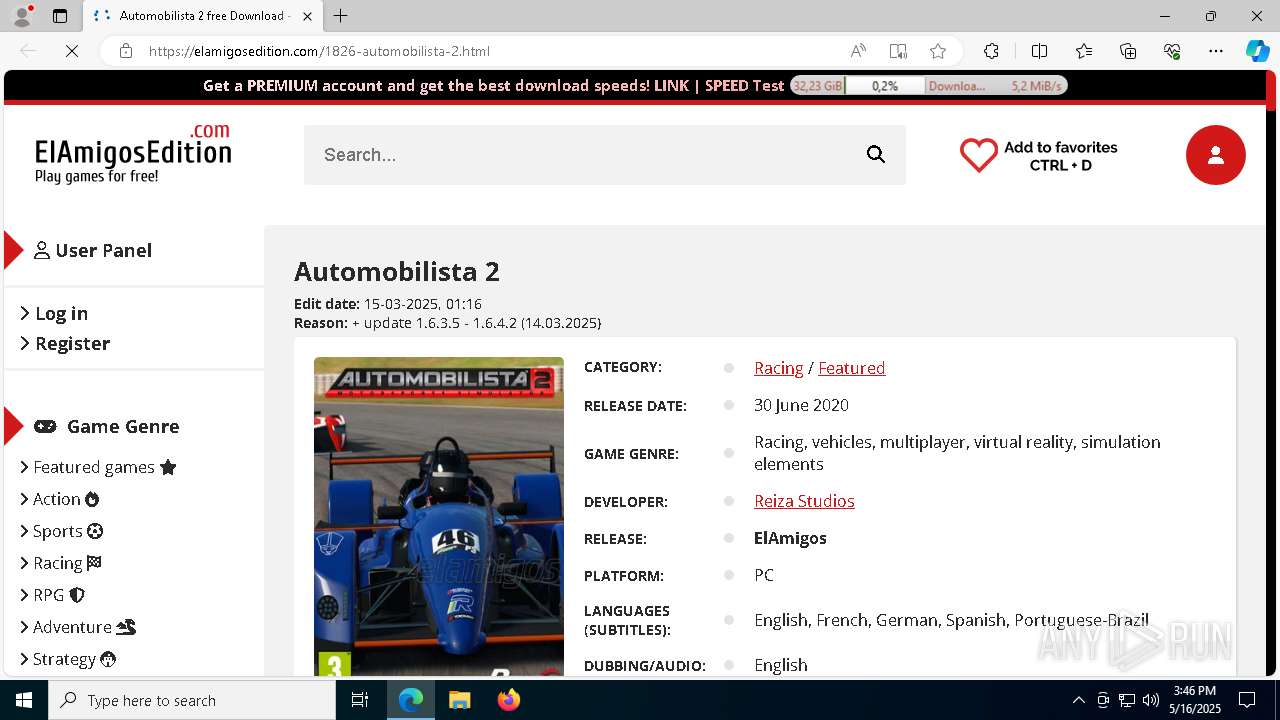
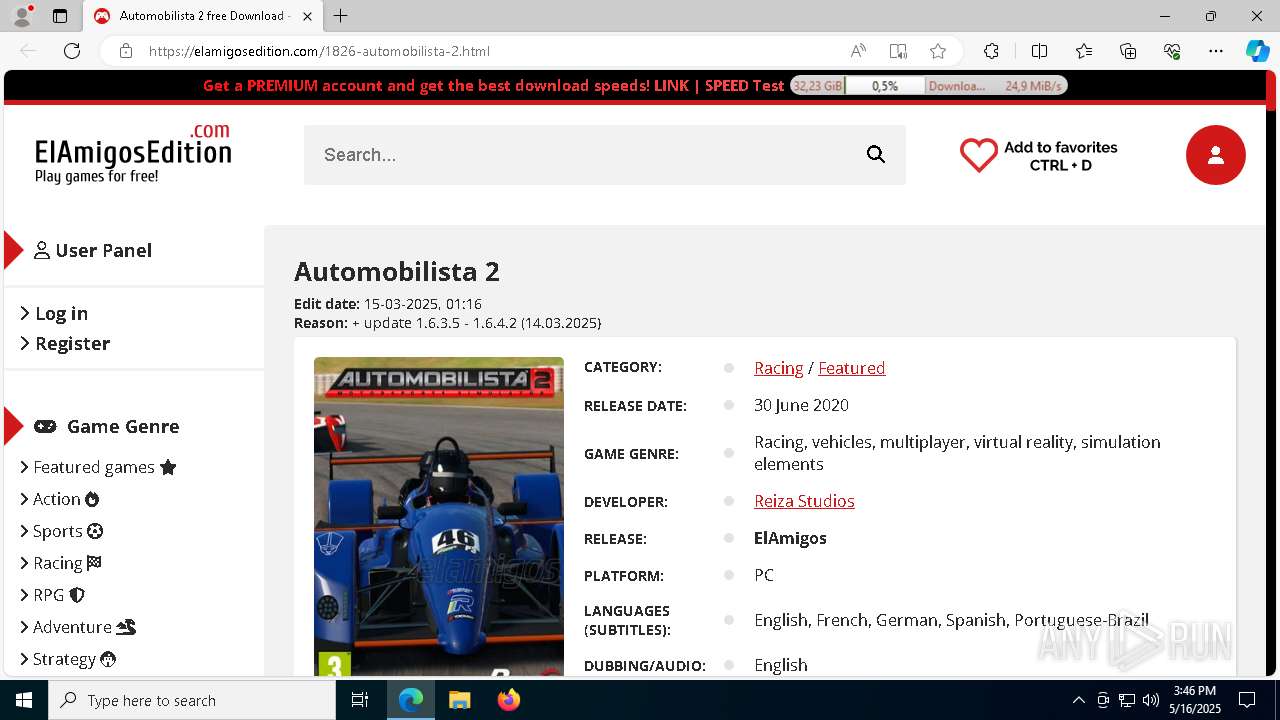
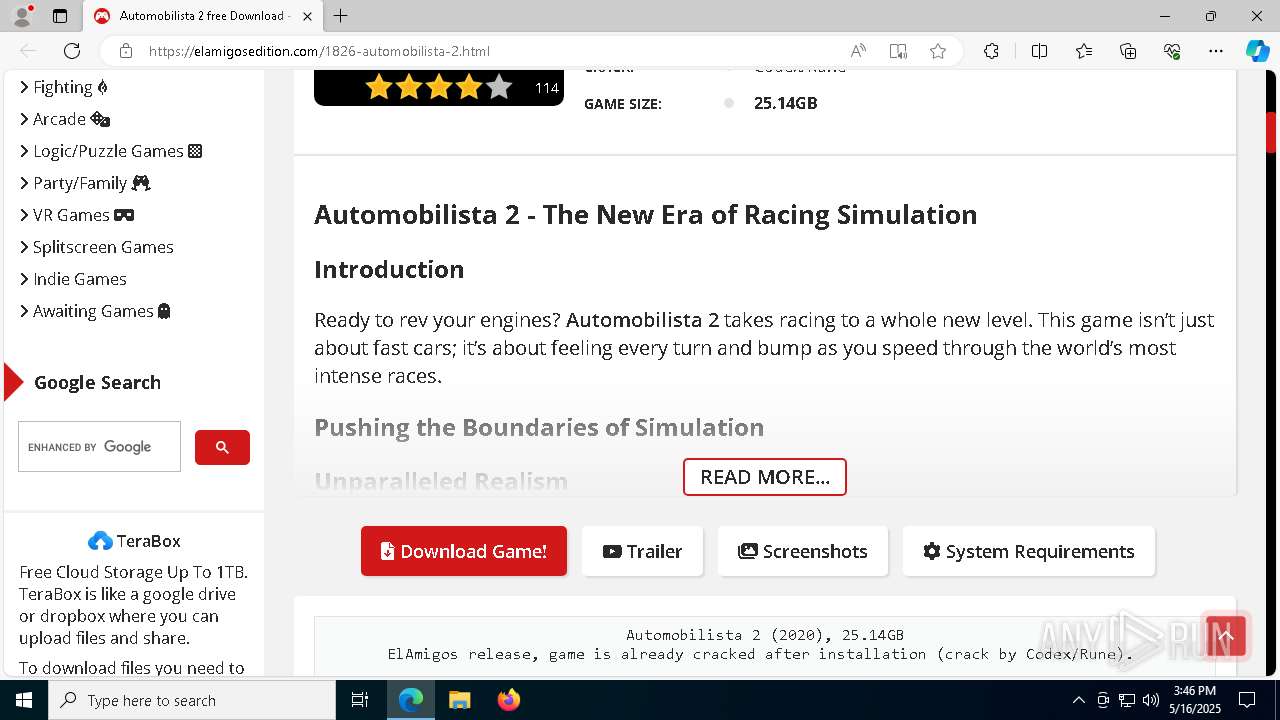
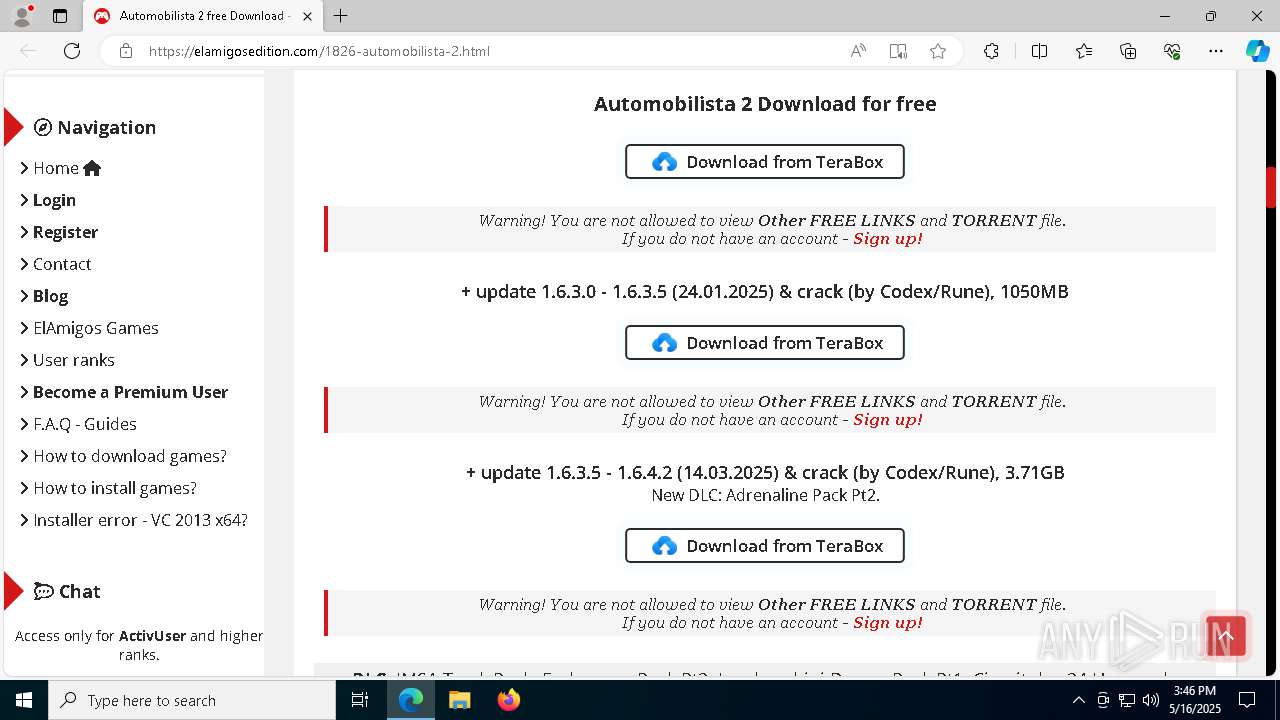
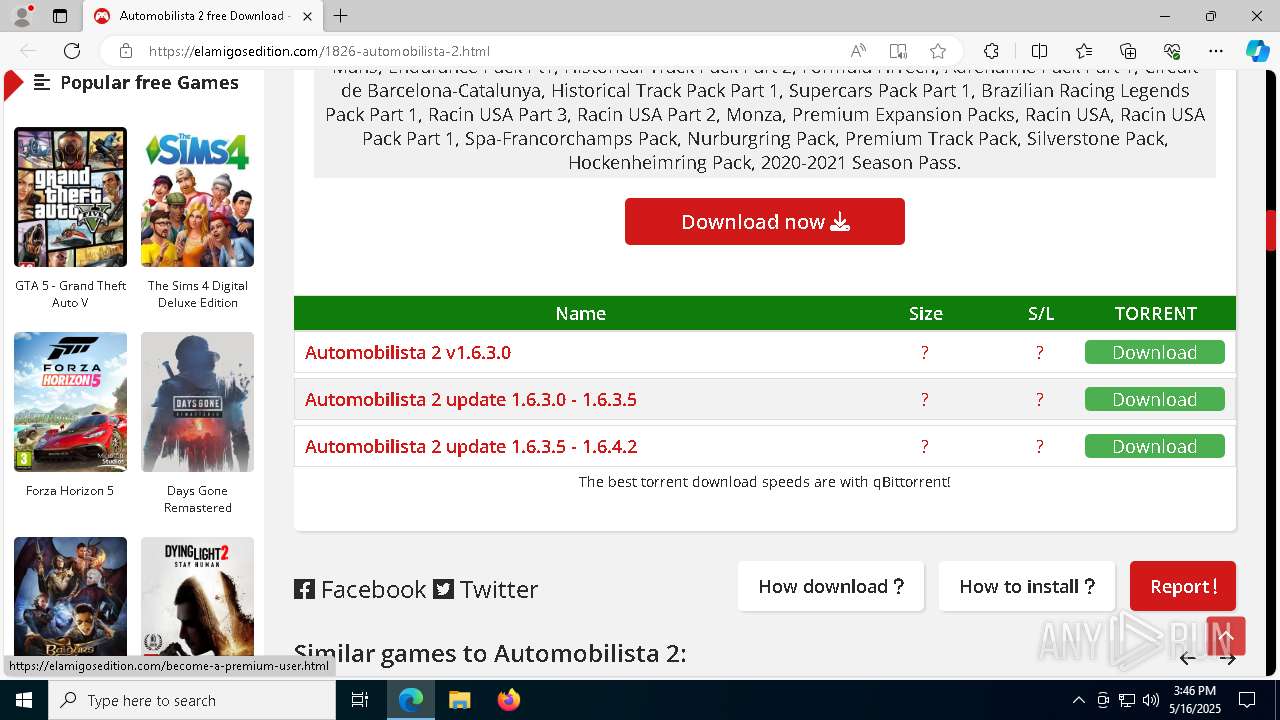
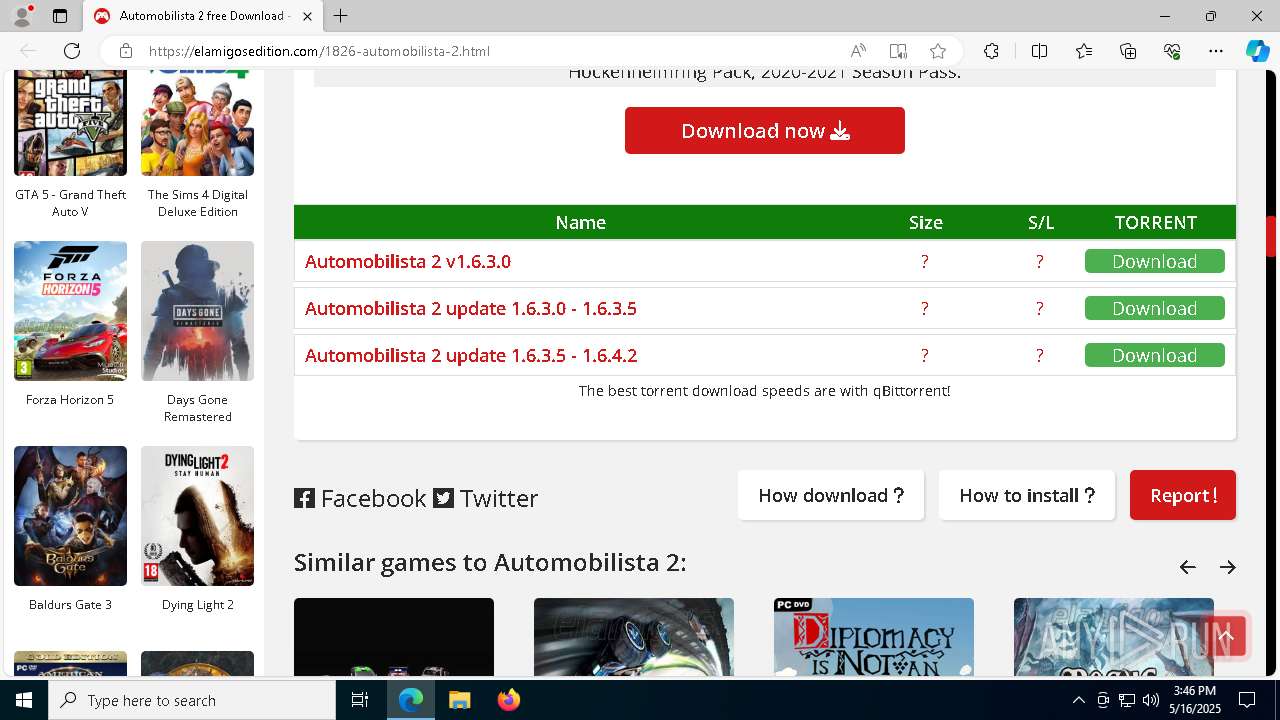
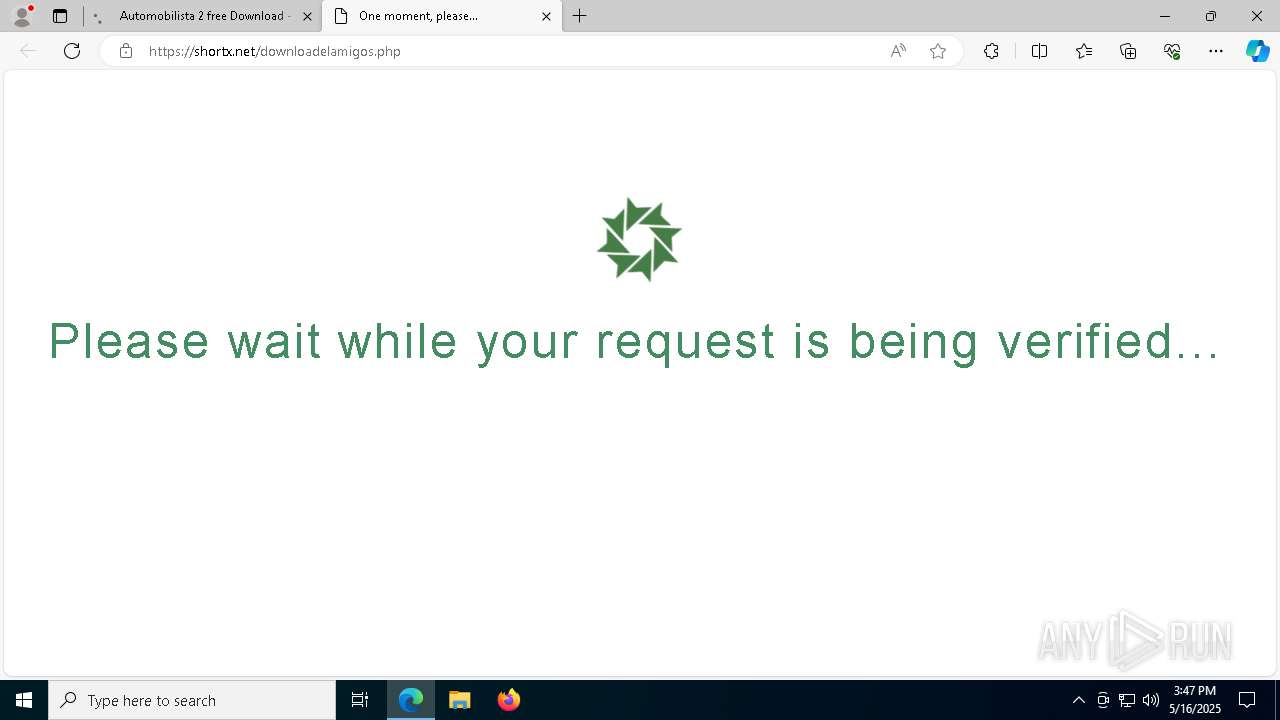
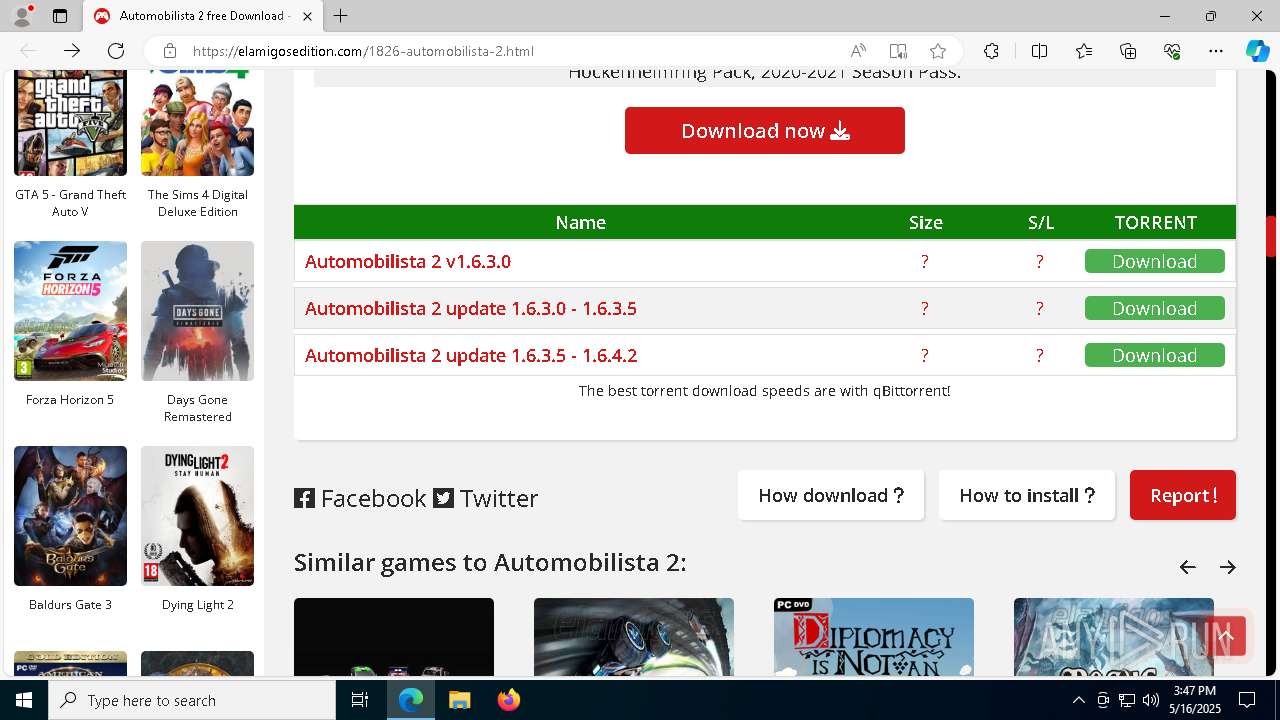
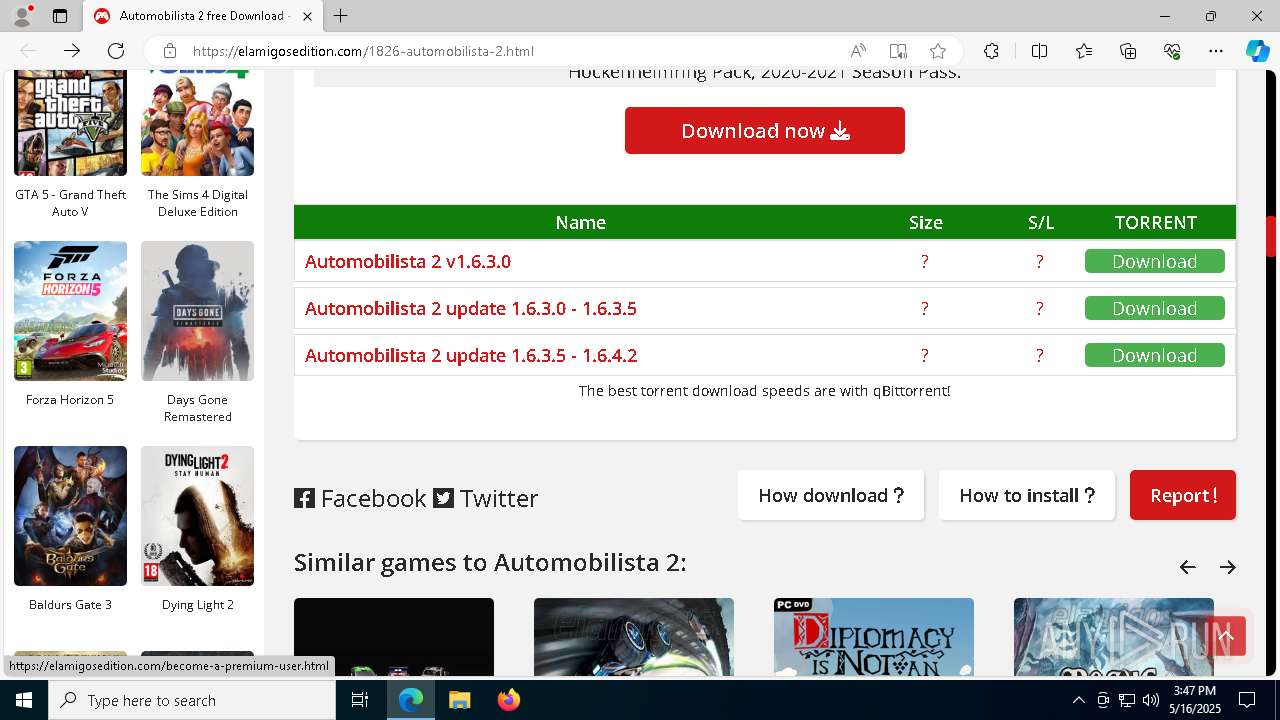
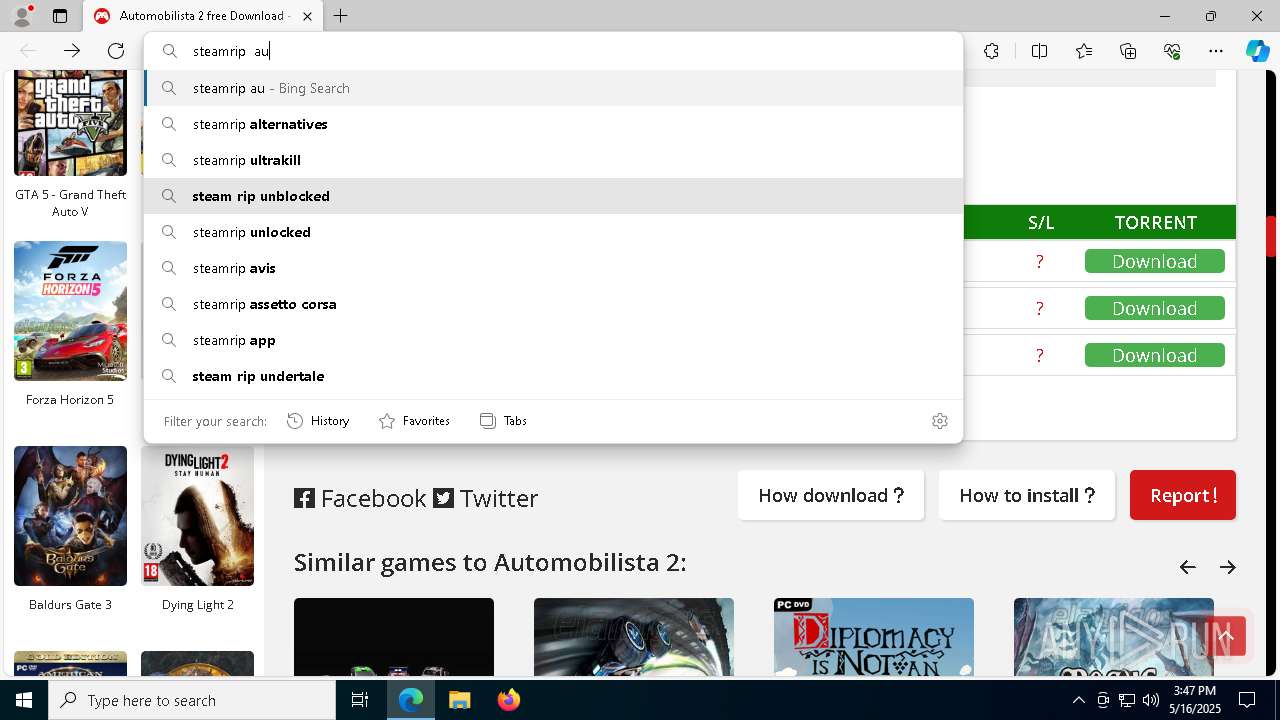
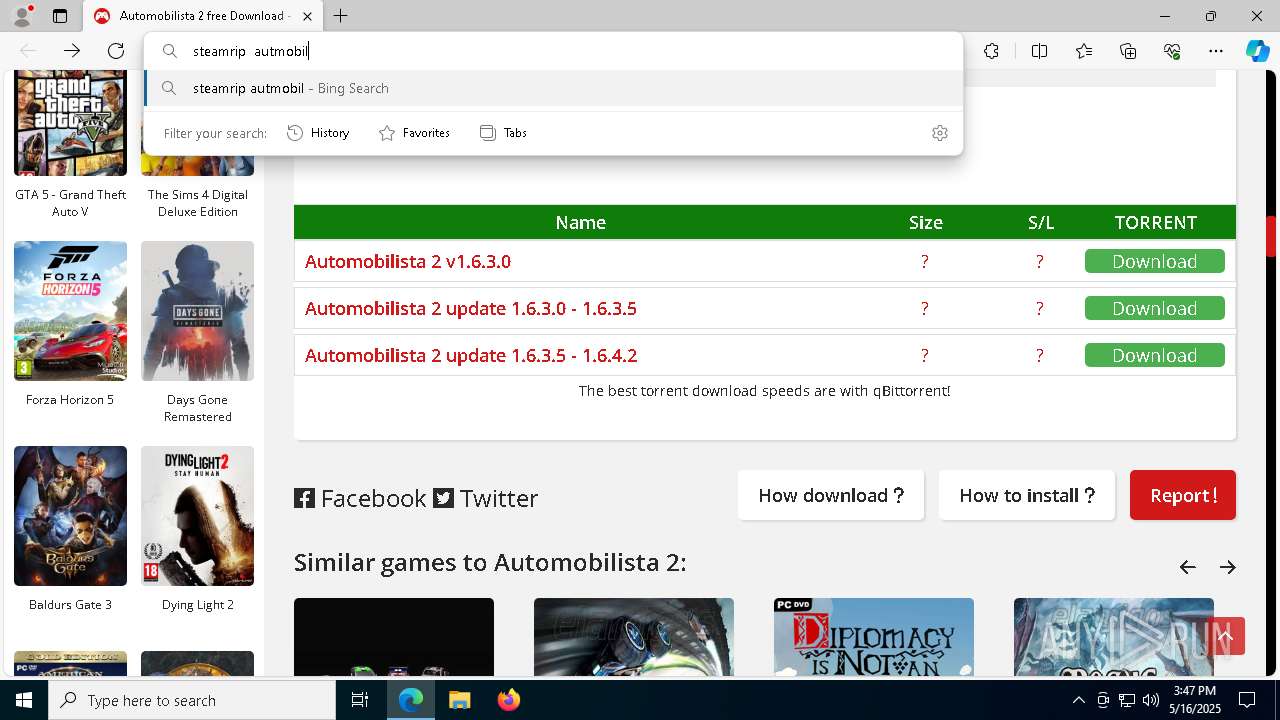
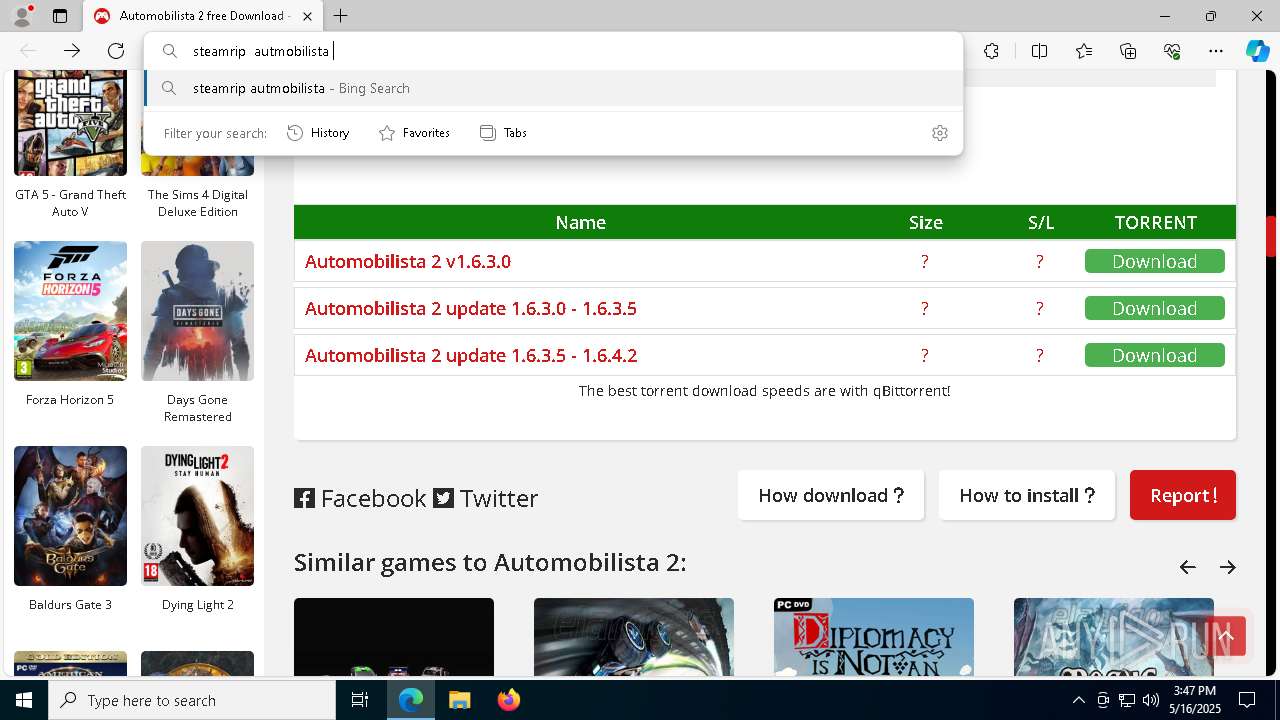
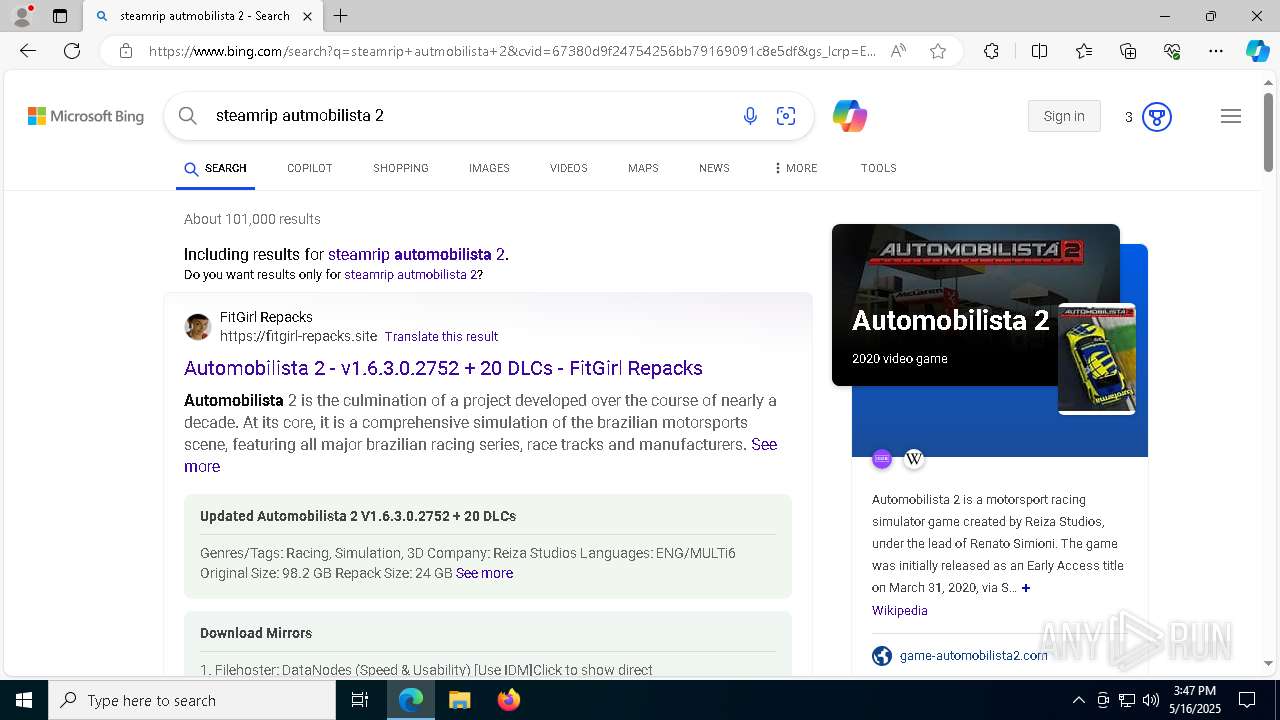
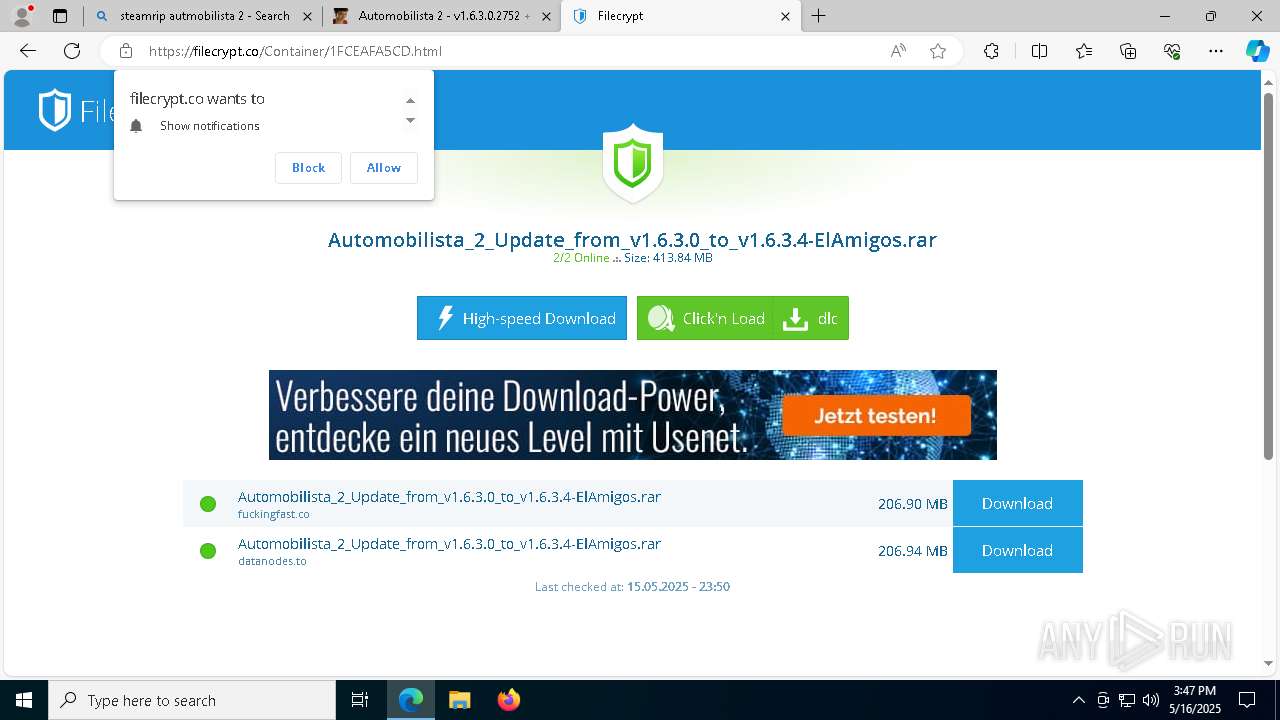
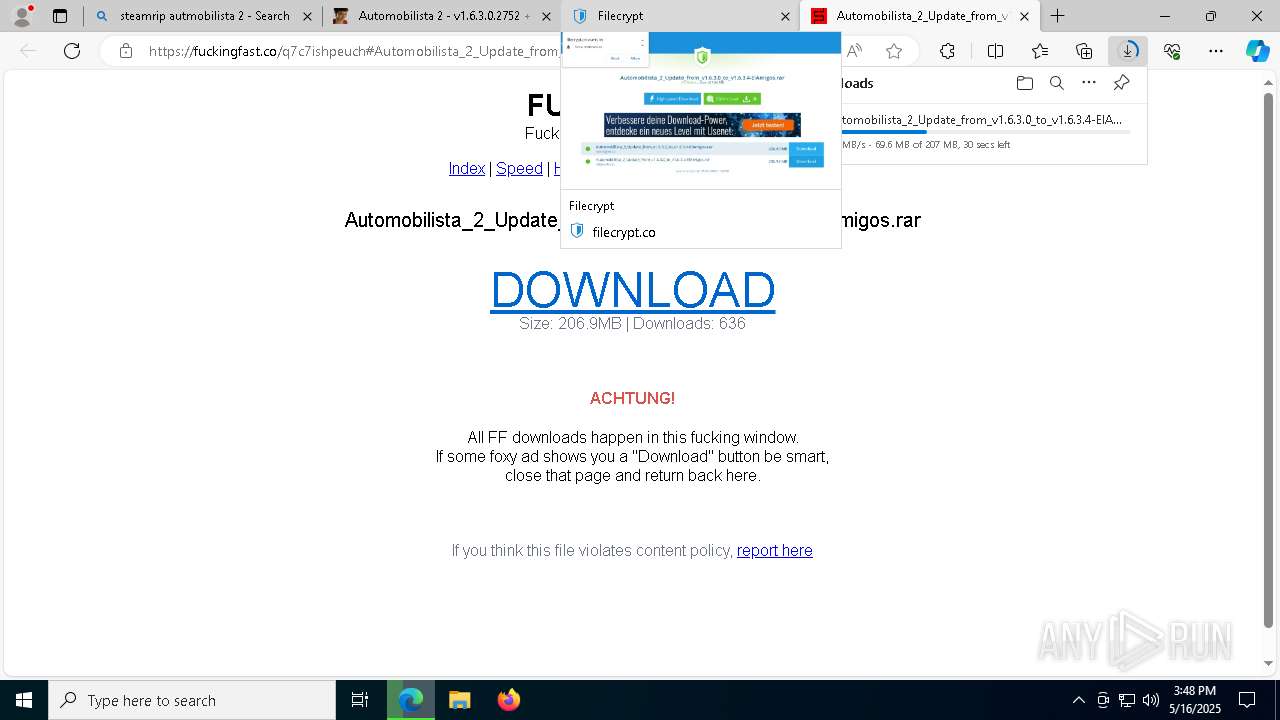
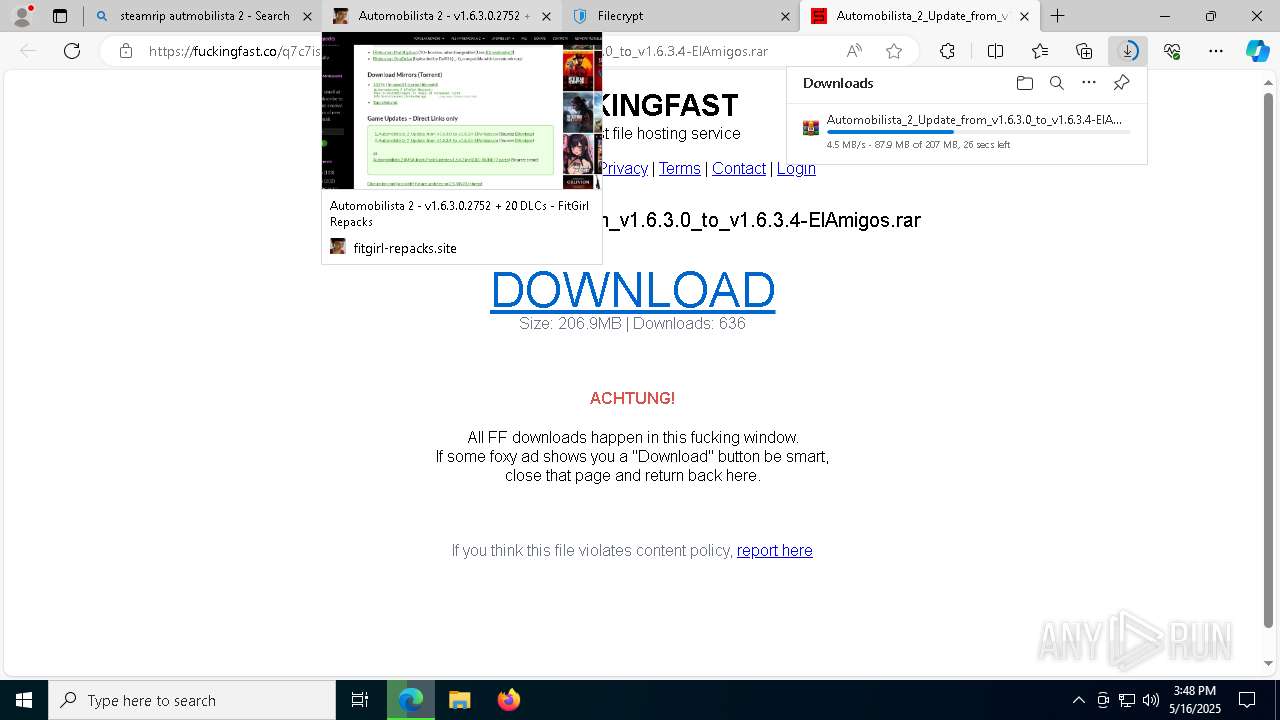
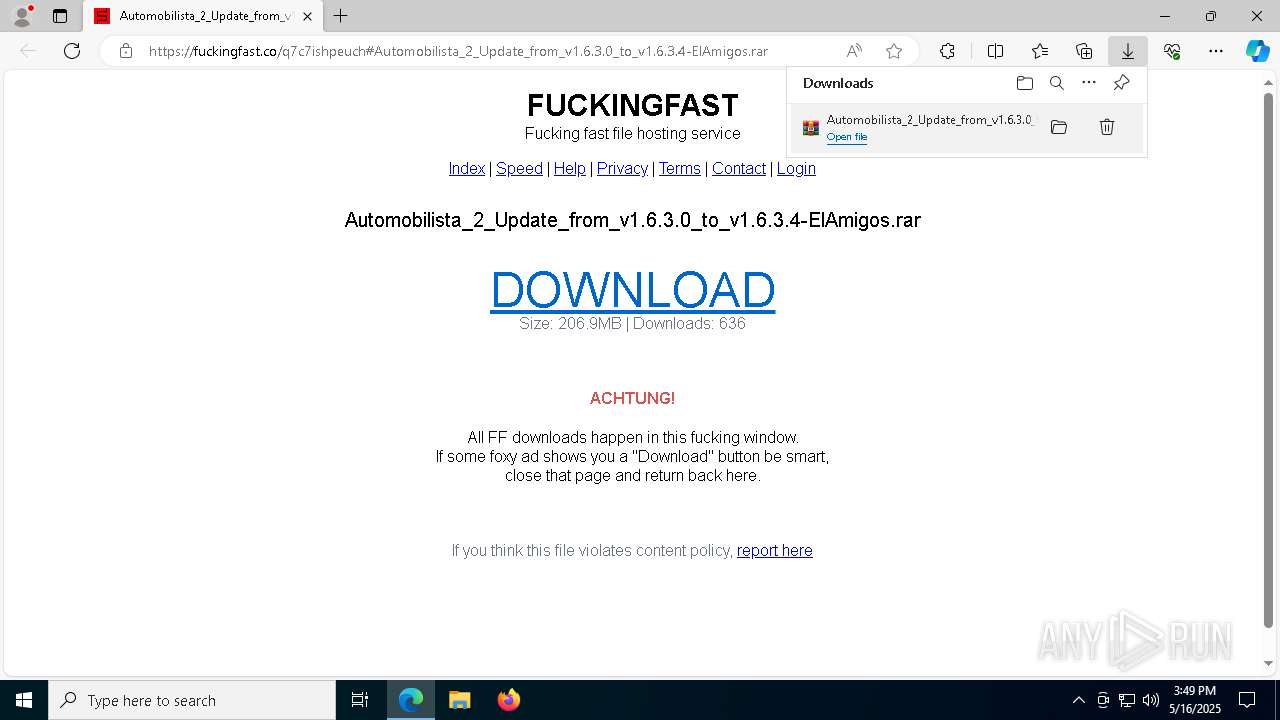
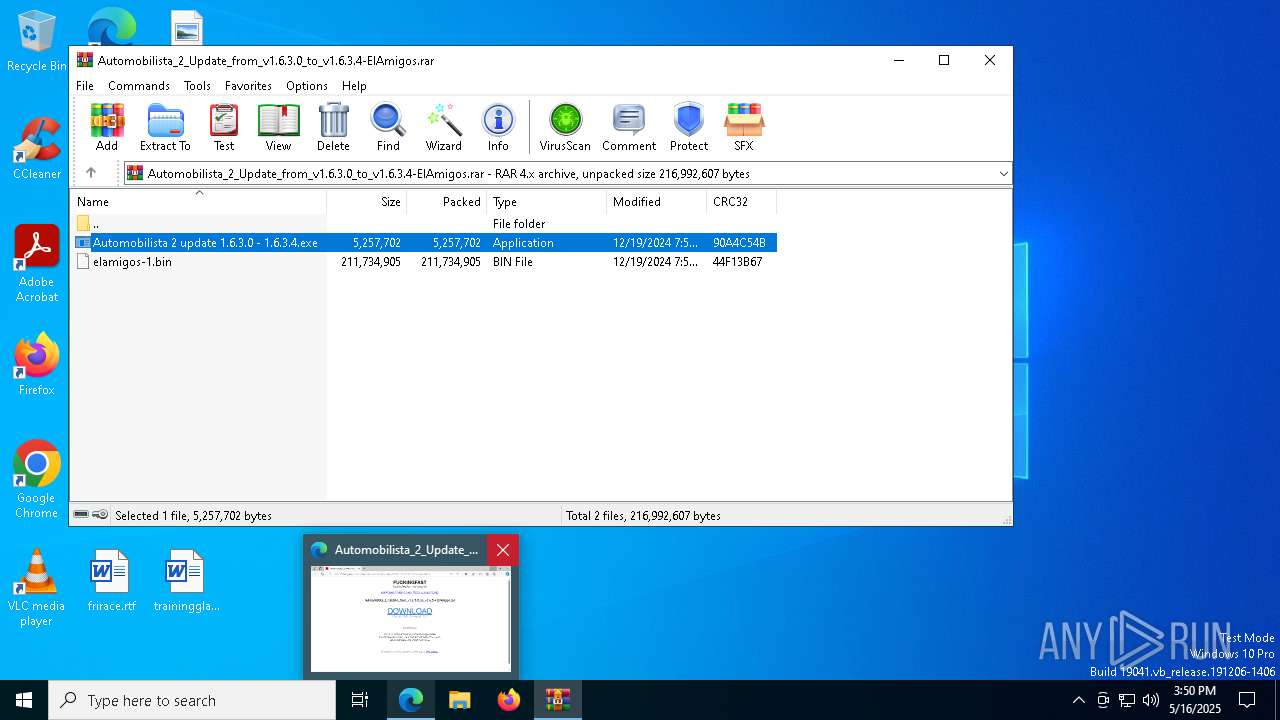
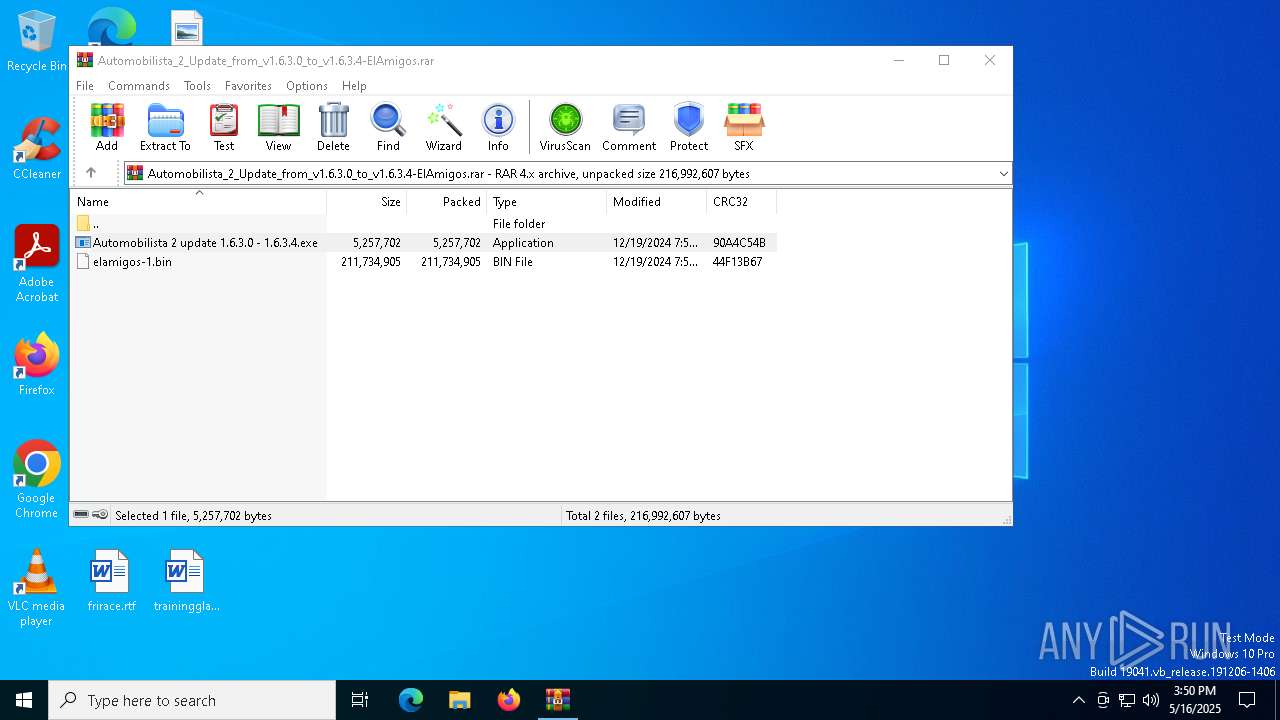
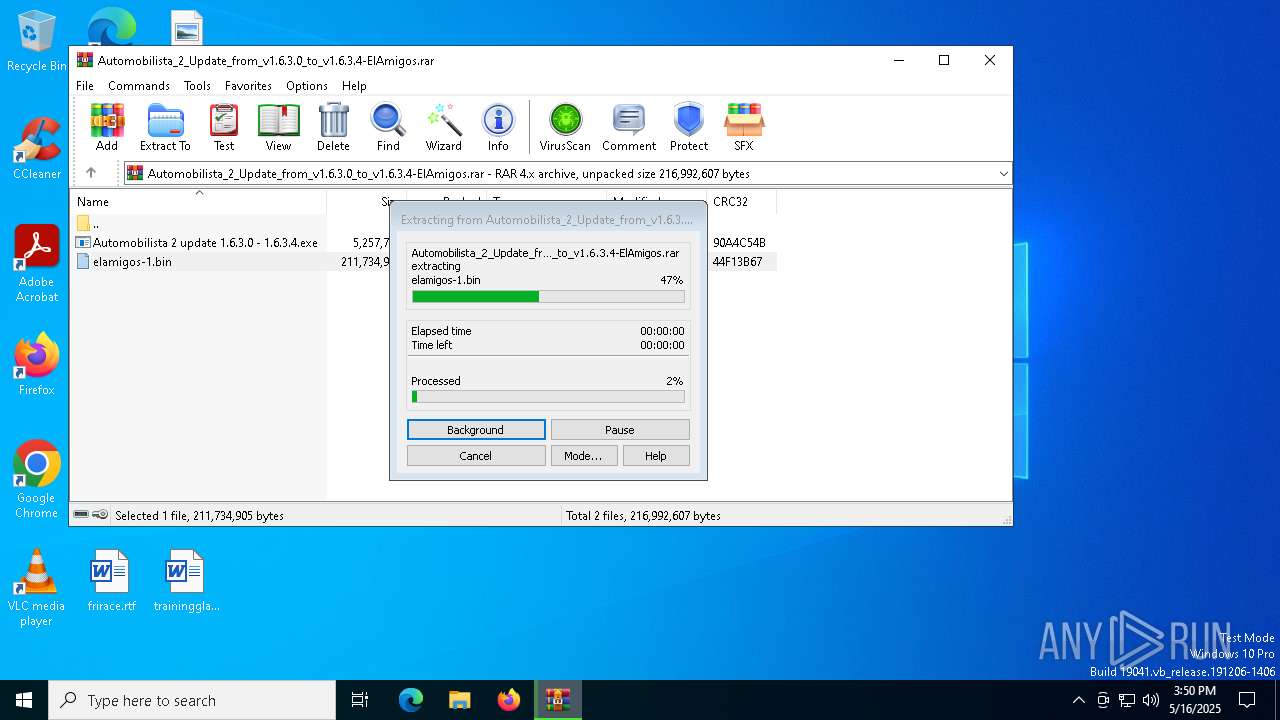
| URL: | https://elamigosedition.com/1826-automobilista-2.html |
| Full analysis: | https://app.any.run/tasks/11bb6eed-3076-4327-bc81-9444d6c17fb9 |
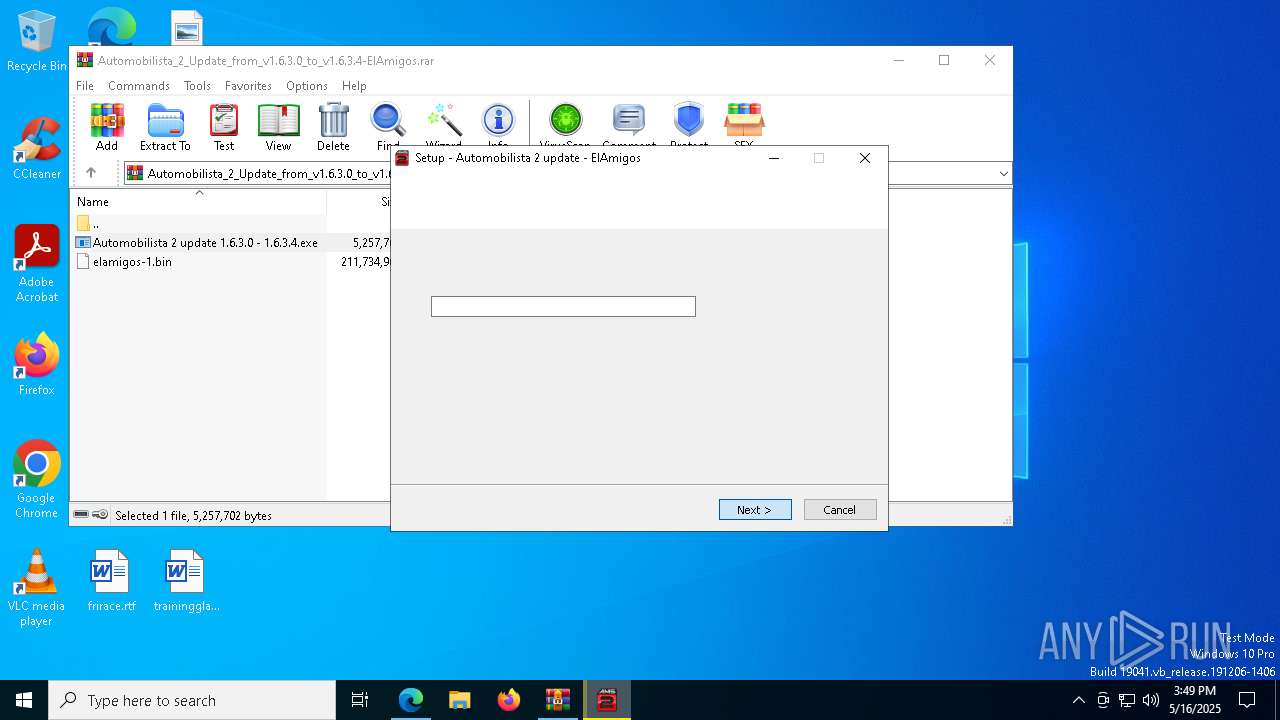
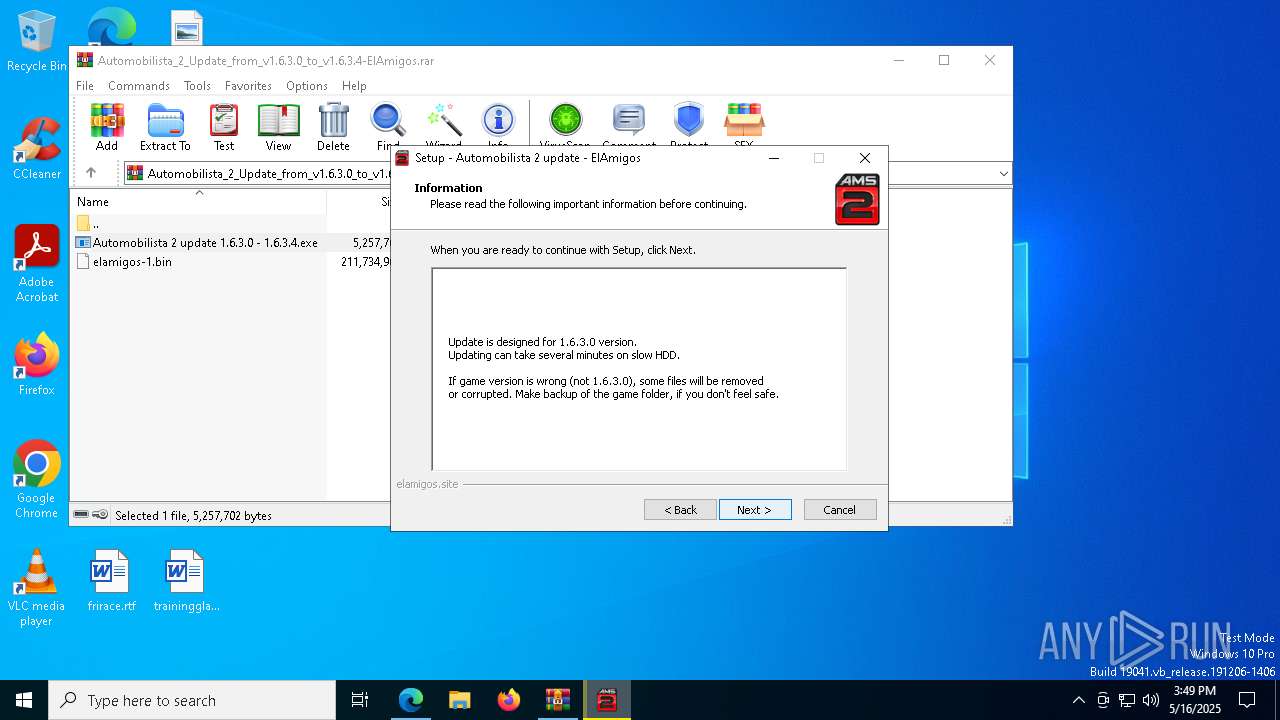
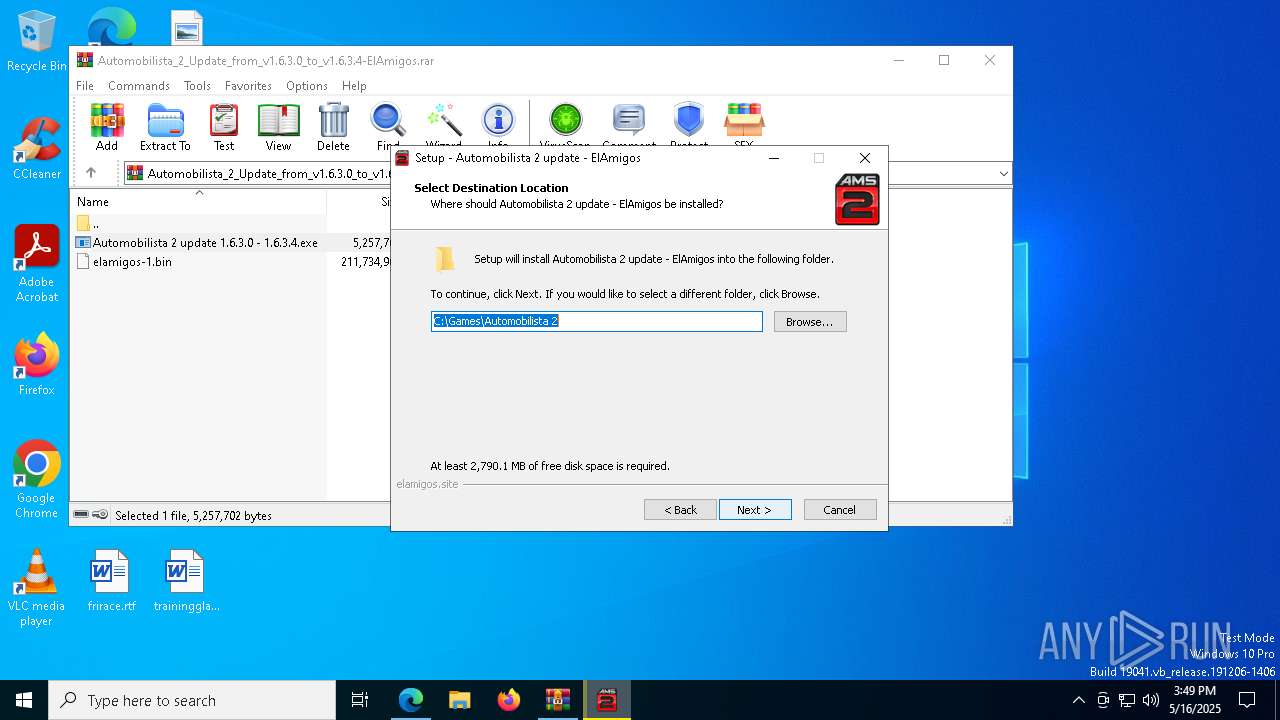
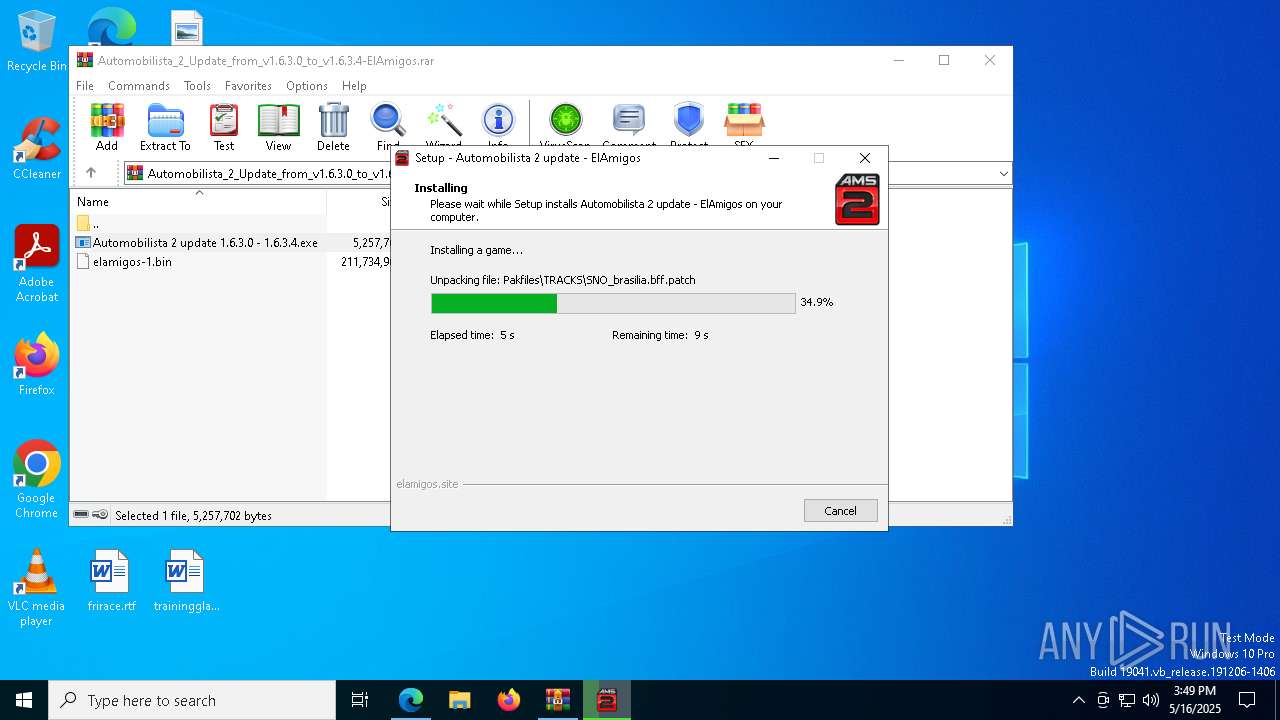
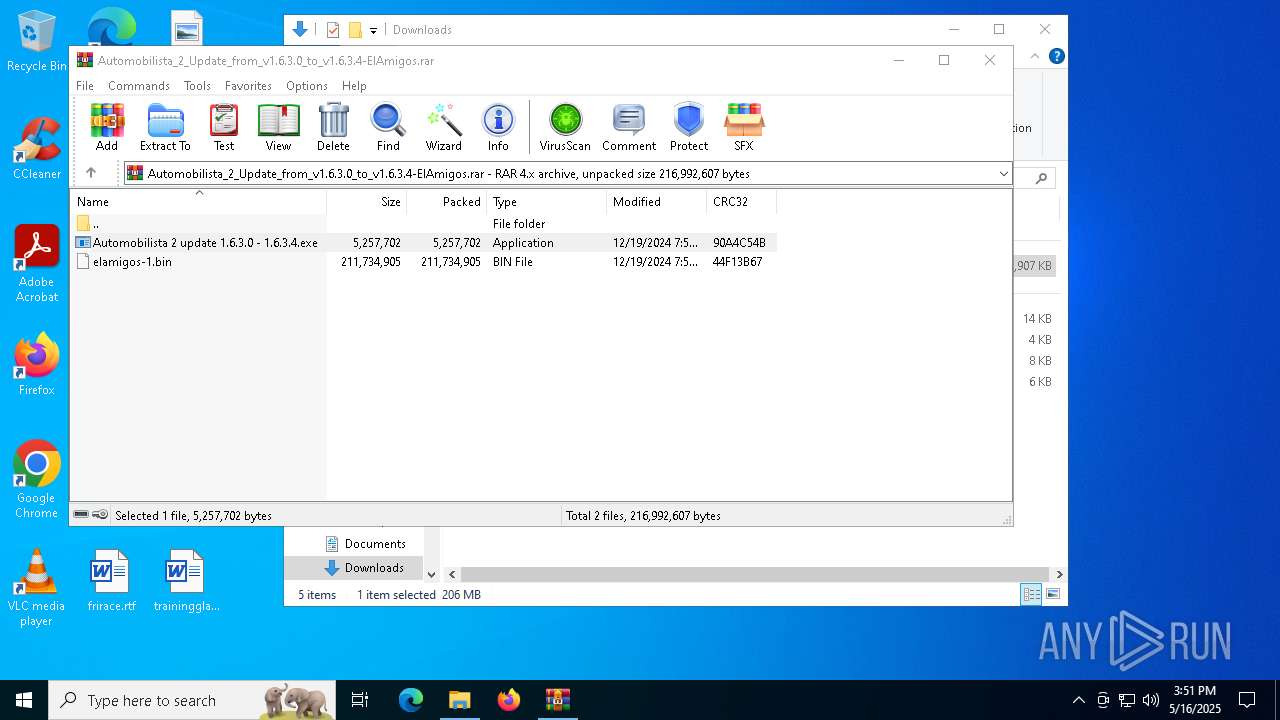
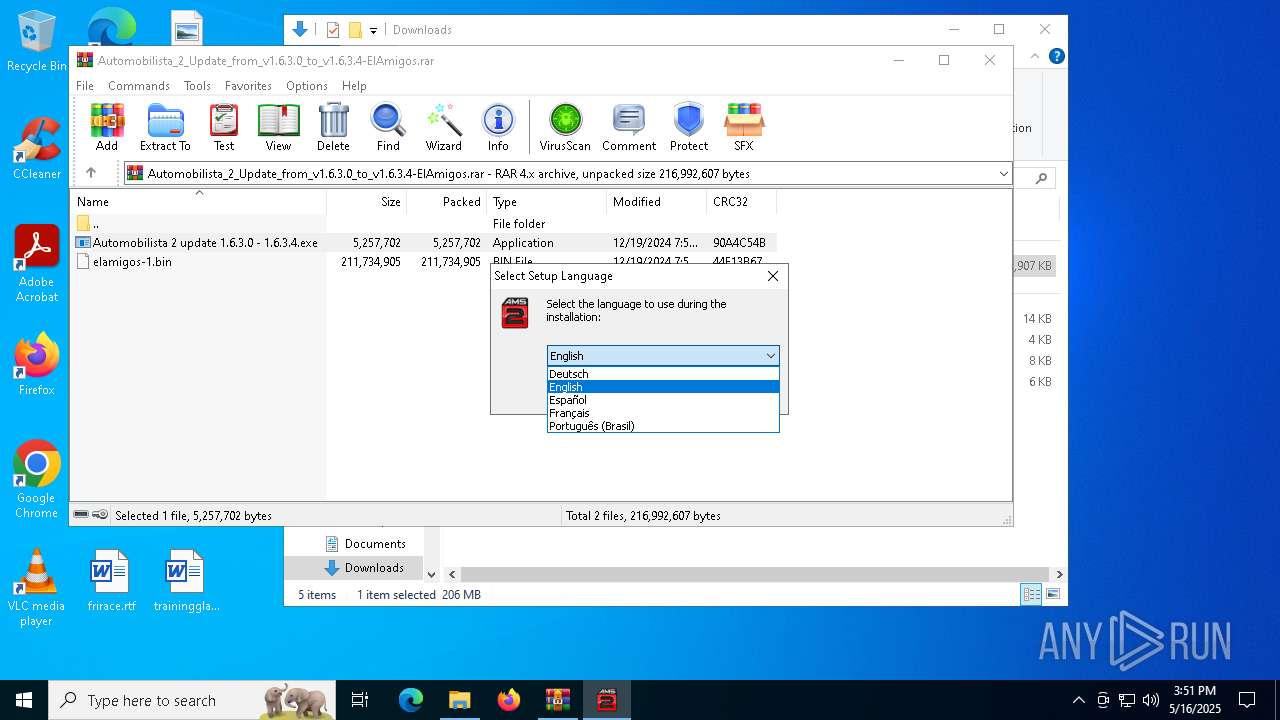
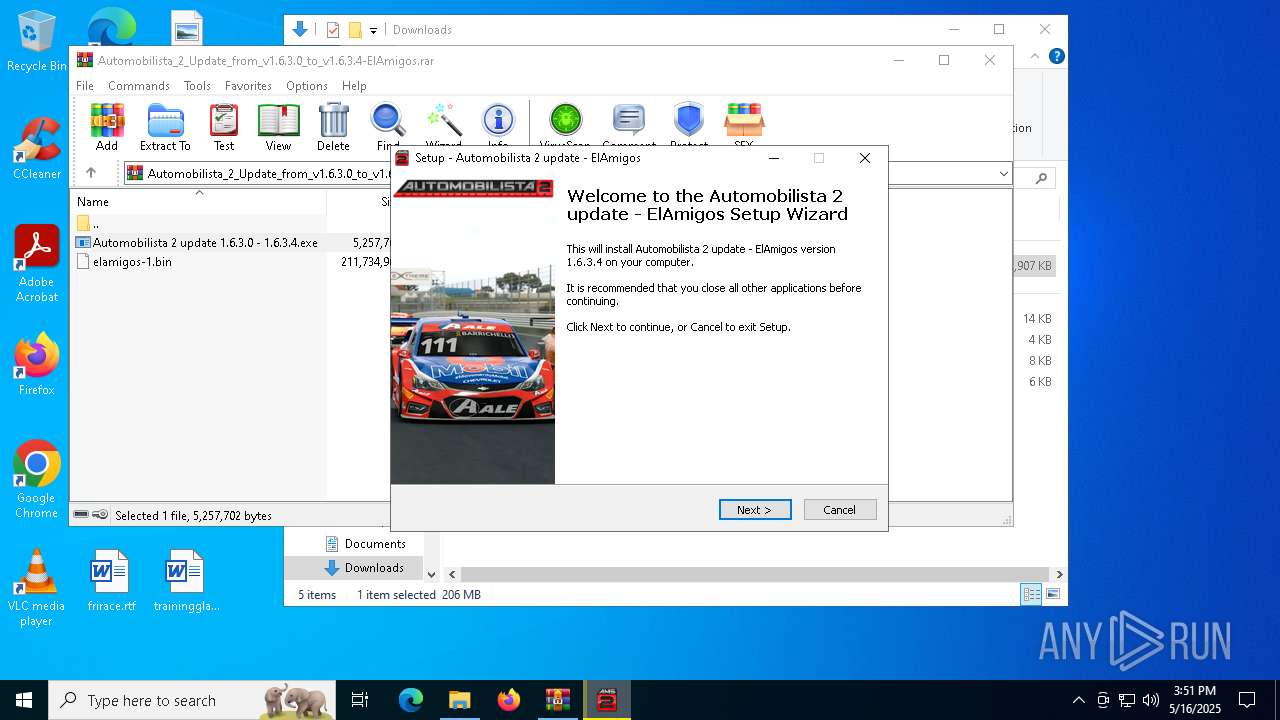
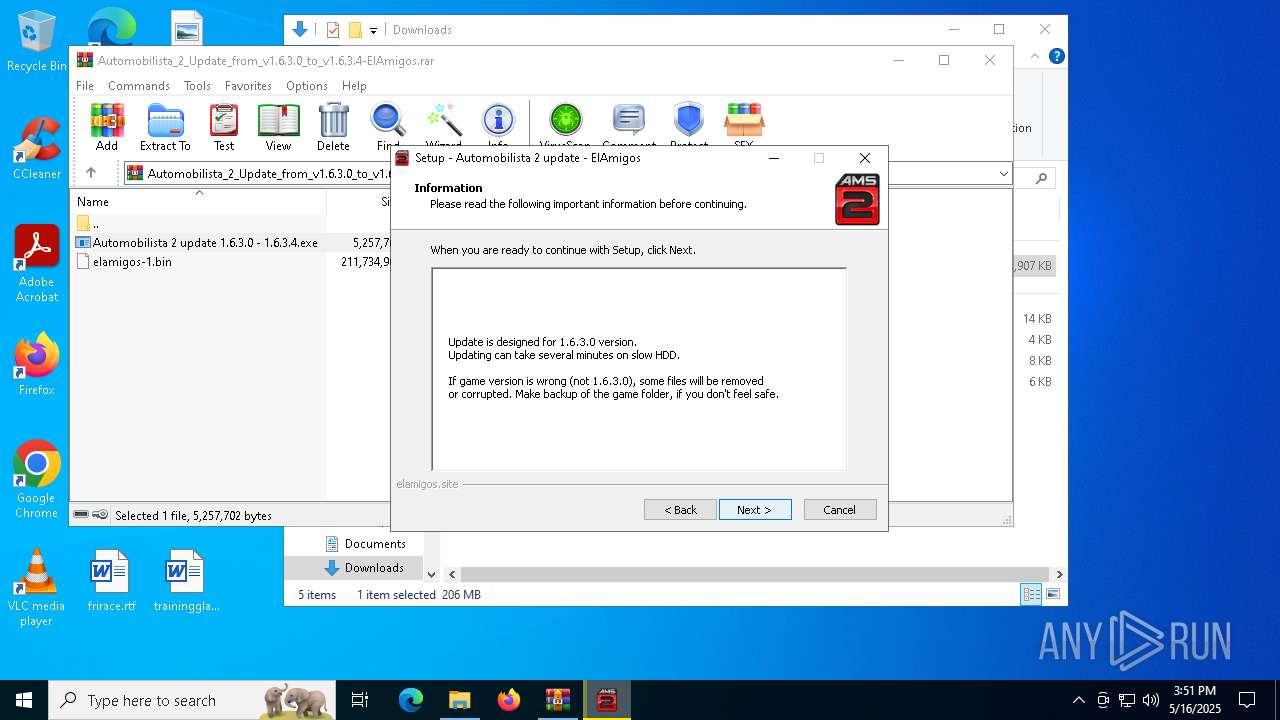
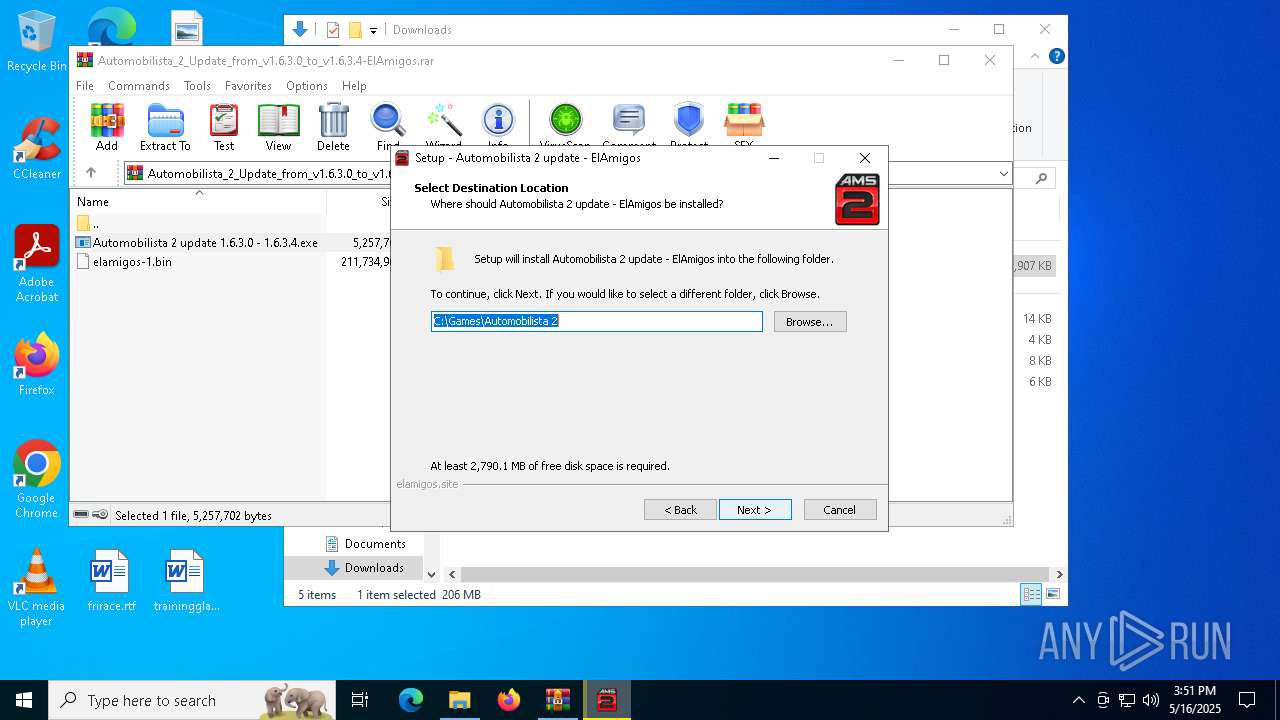
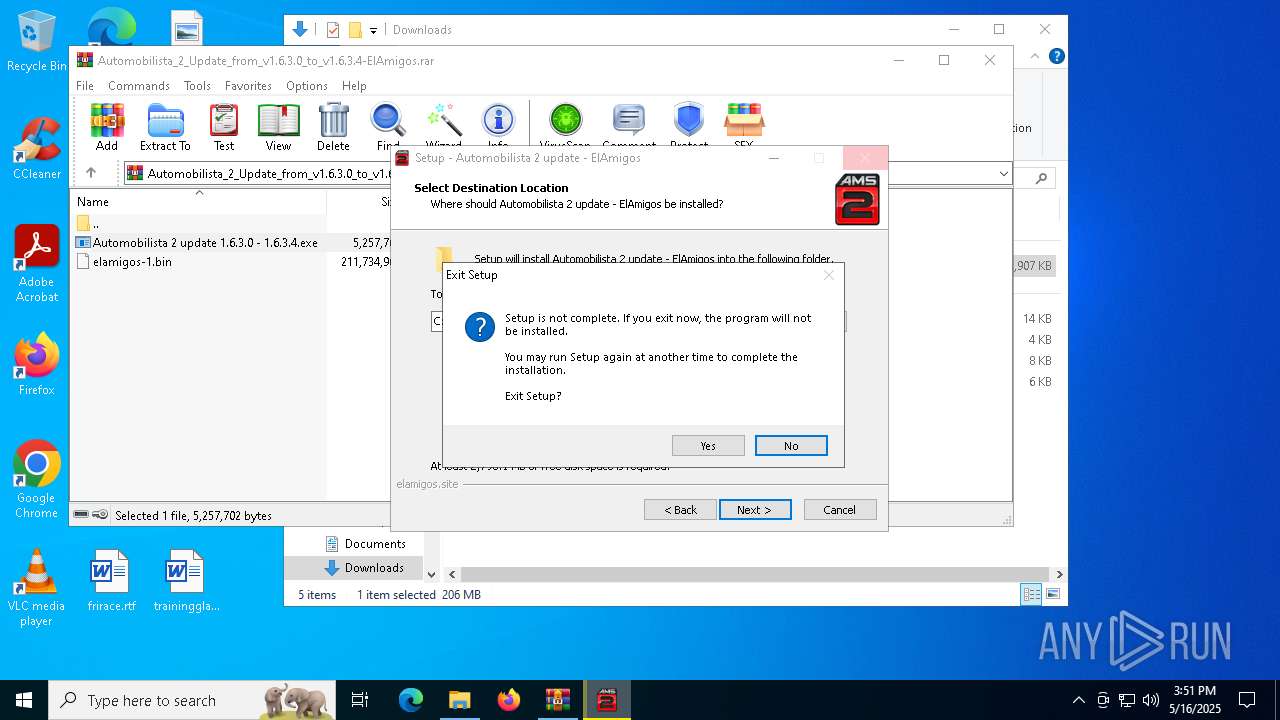
| Verdict: | Malicious activity |
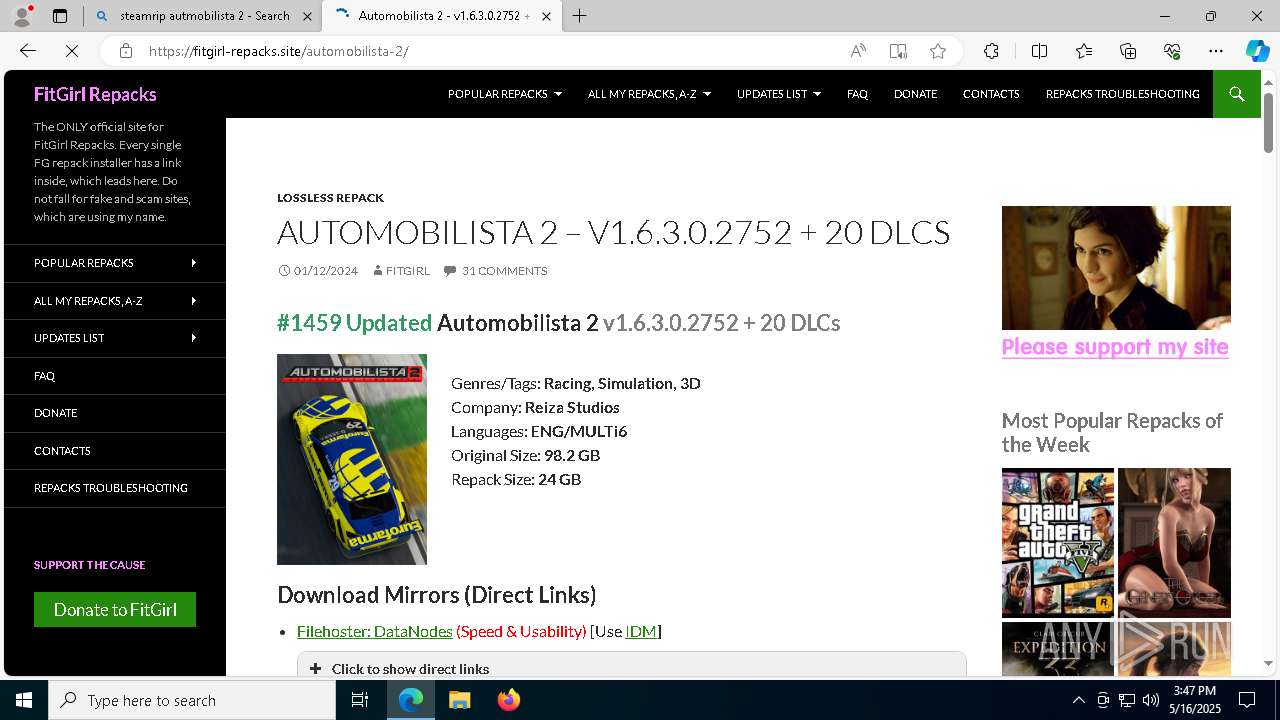
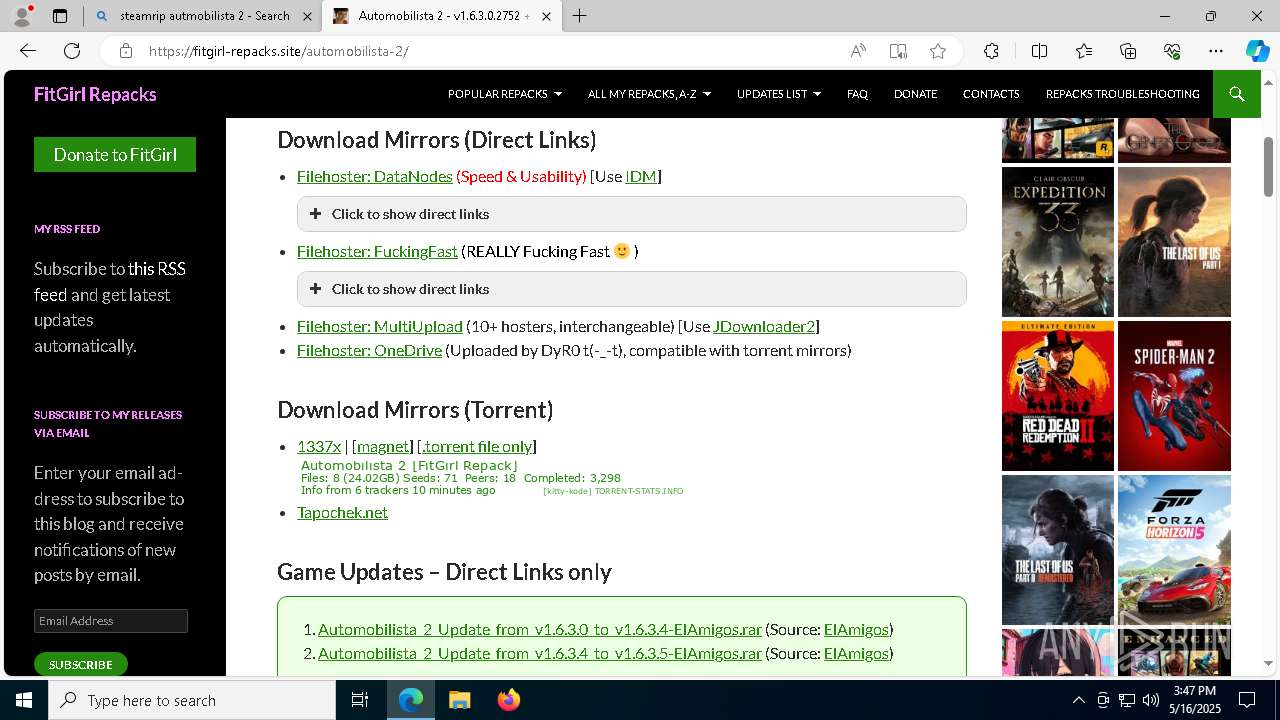
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
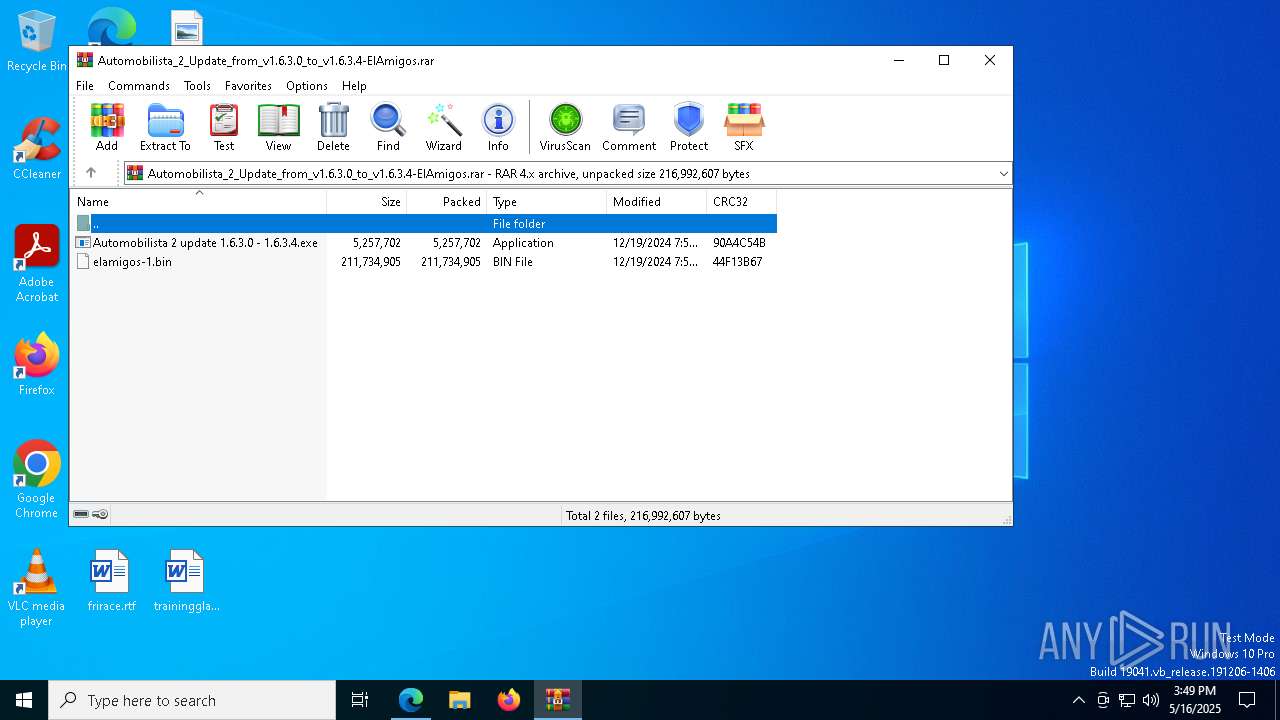
| Analysis date: | May 16, 2025, 15:46:40 |
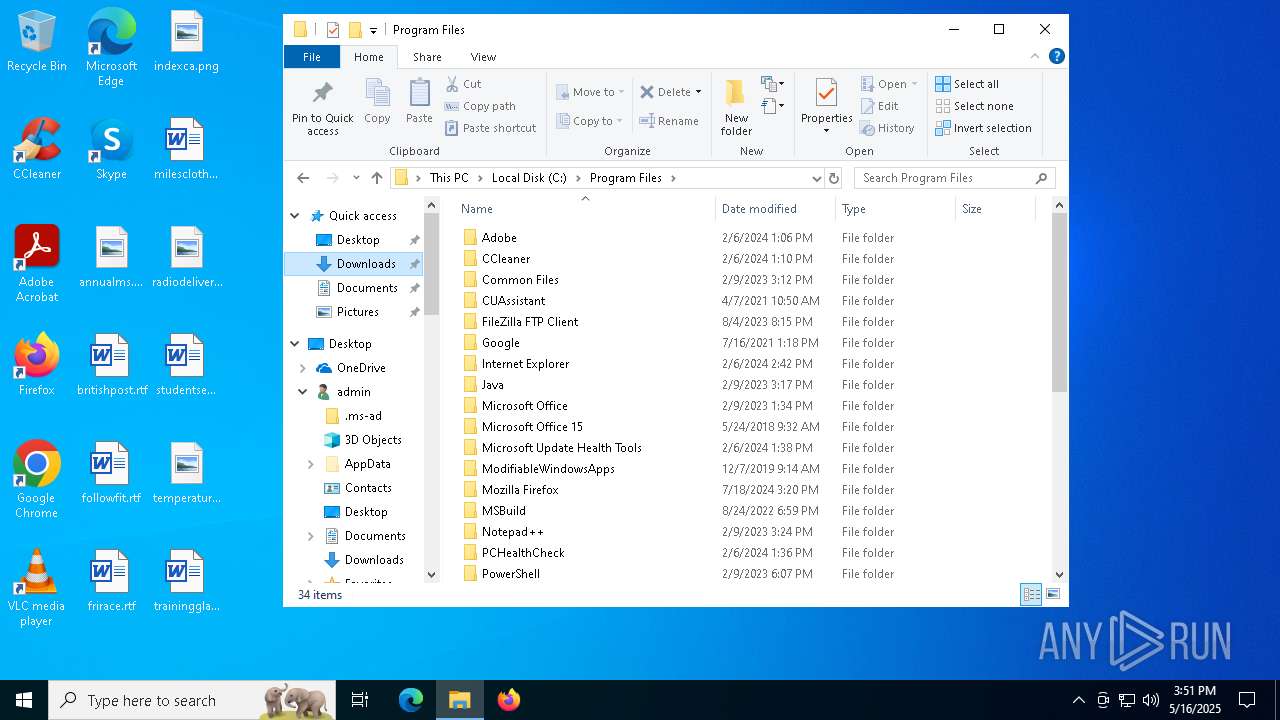
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
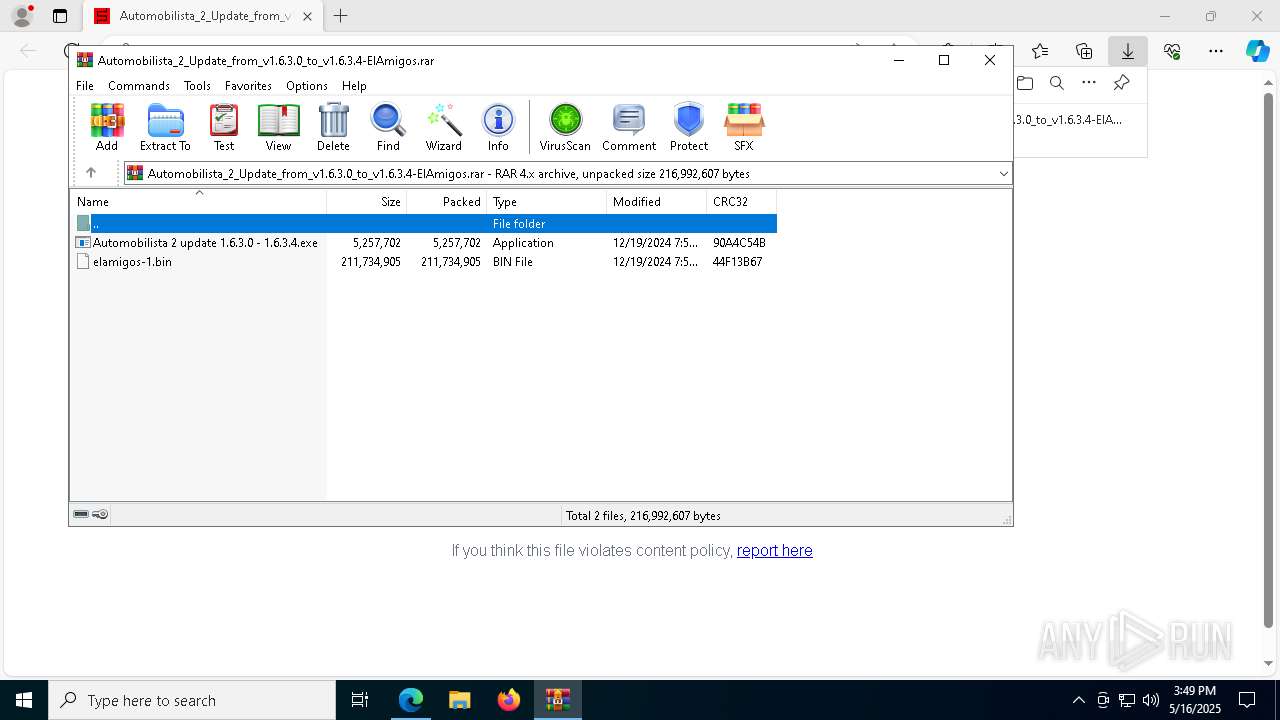
| MD5: | 0E745B74B54DD02104A1B05F7CFC46F0 |
| SHA1: | BFC7A1B8CEA87E1263F9E83261DA294C3DE60588 |
| SHA256: | 18FF2A597929556F59FCC03FB0174FD7CDD4456E7A9E5DAFC0A48F3F762A1204 |
| SSDEEP: | 3:N8EDyMRBIlDIEEKIKRWrpRIJ:2hMRBIldzapR0 |
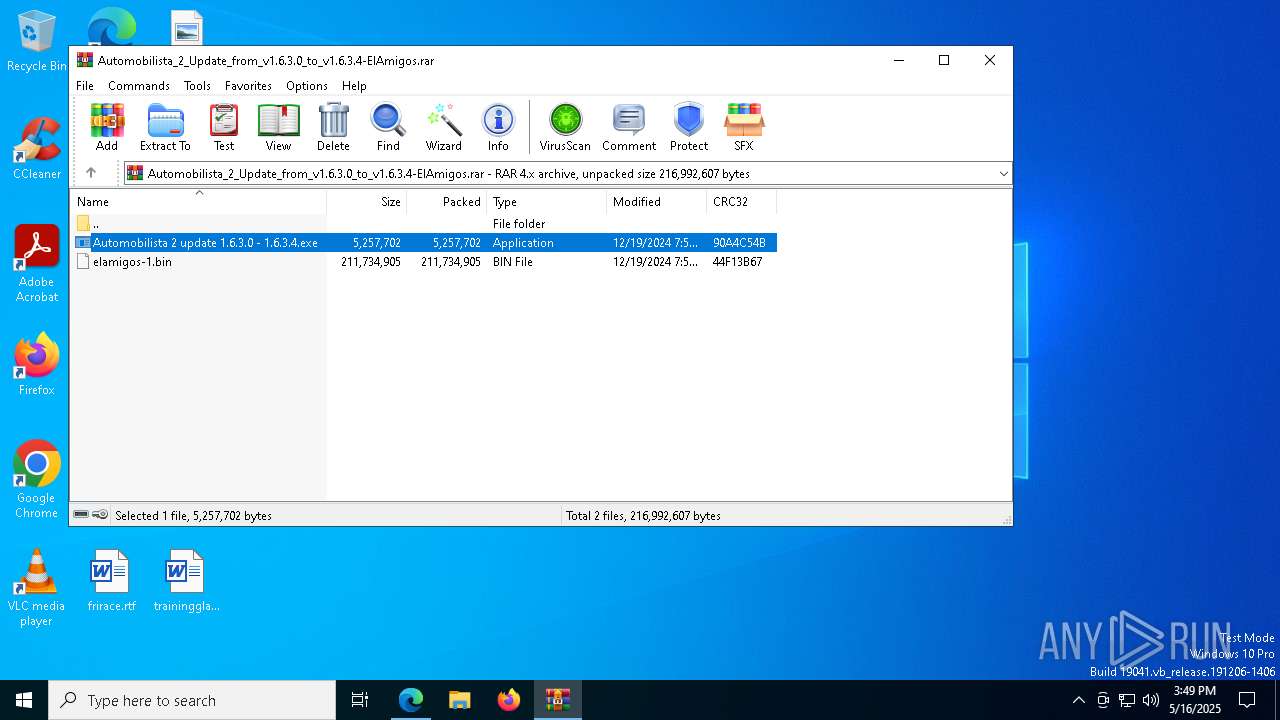
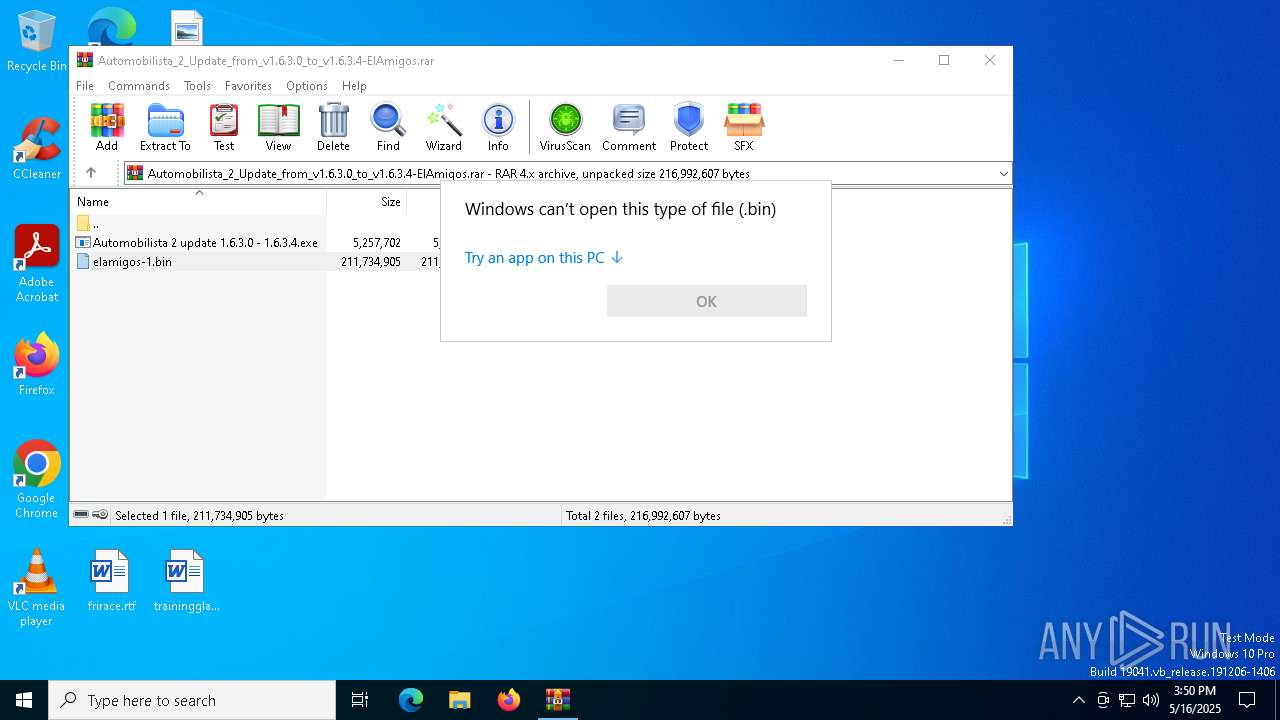
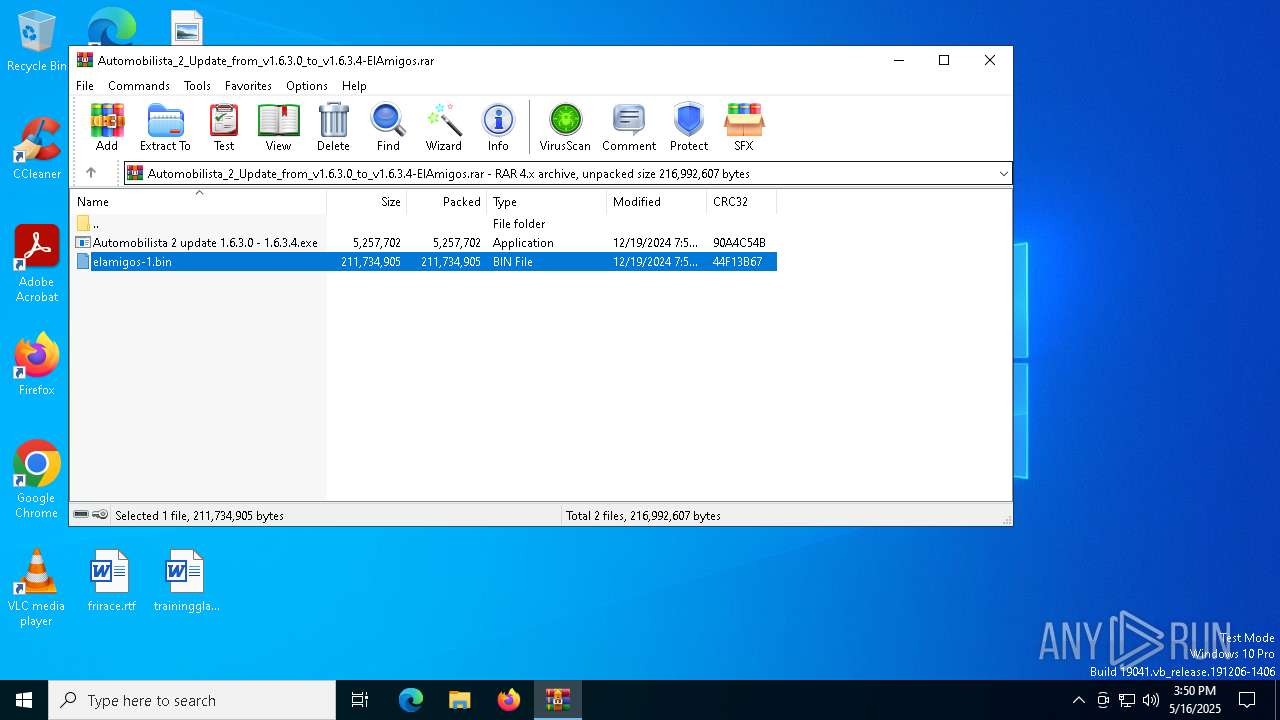
MALICIOUS
LUMMA has been detected (SURICATA)
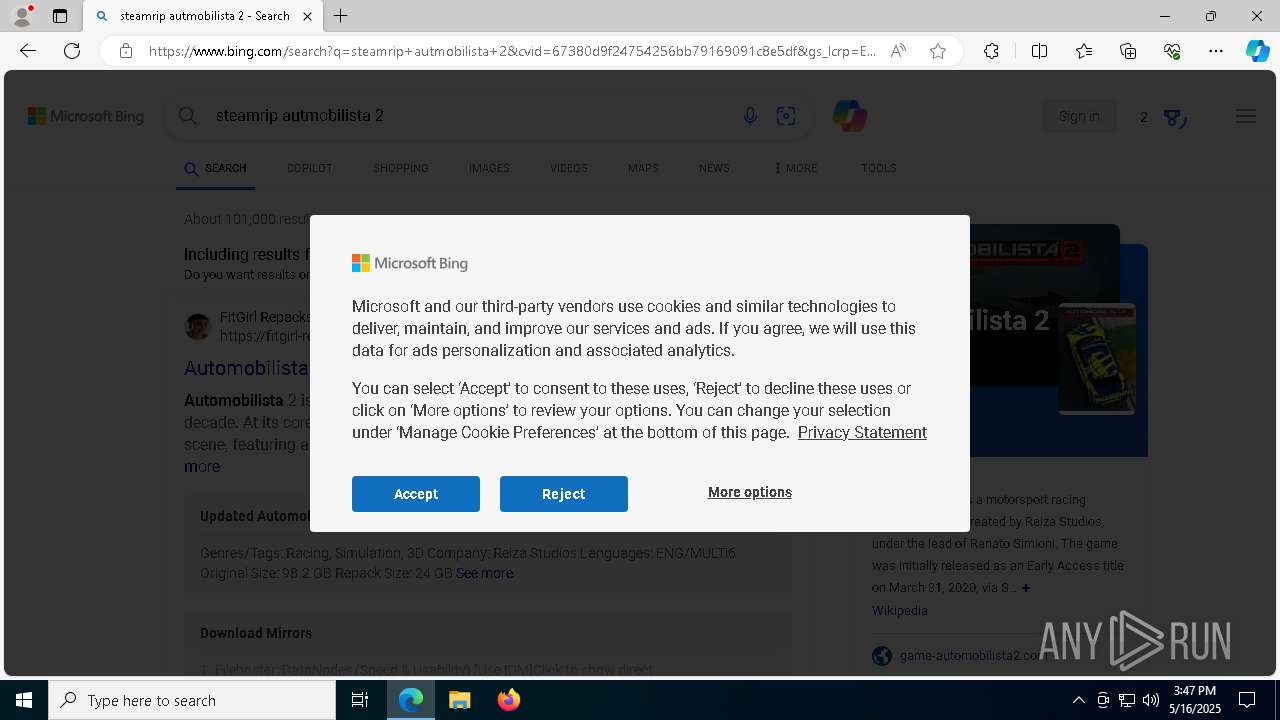
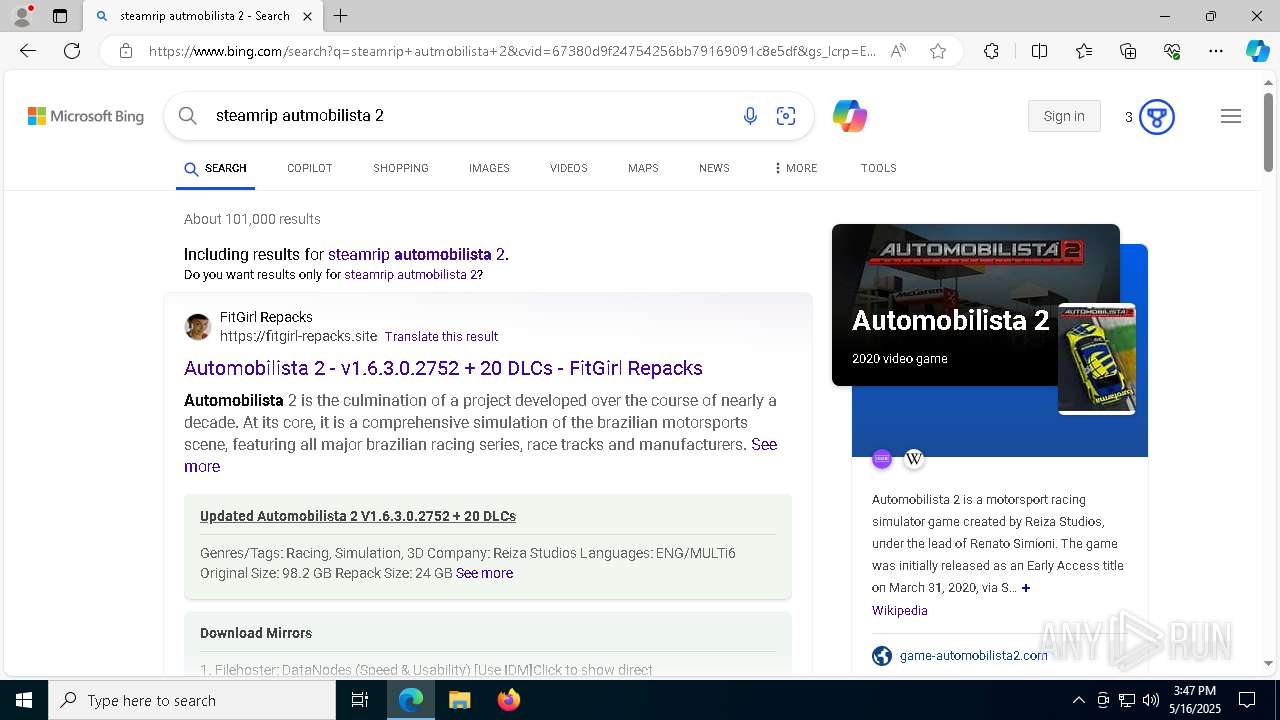
- msedge.exe (PID: 7356)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 7356)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2344)
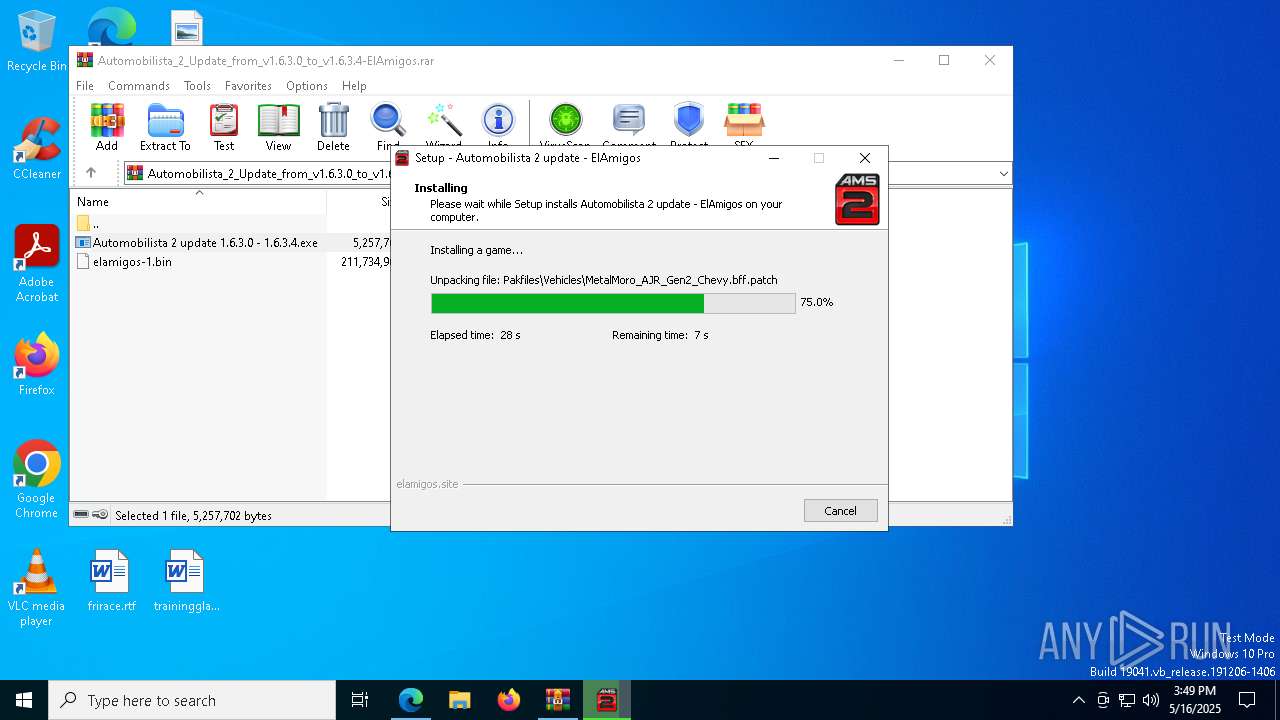
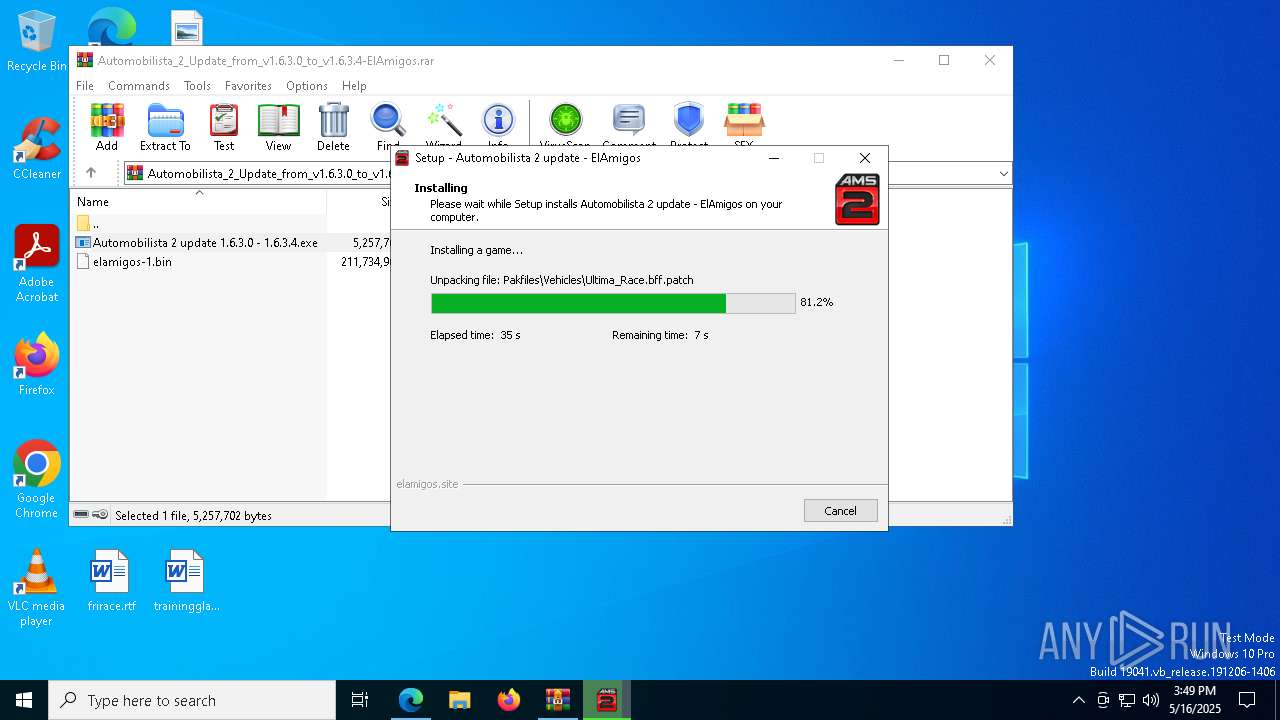
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 6852)
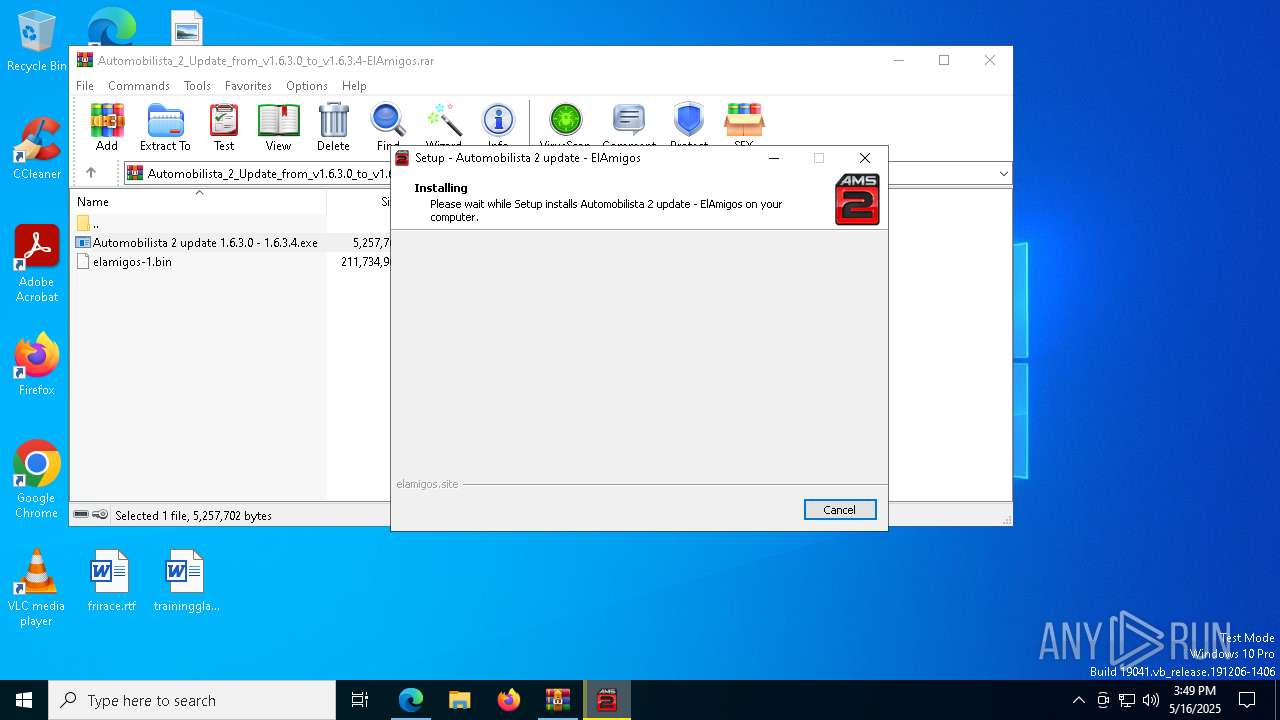
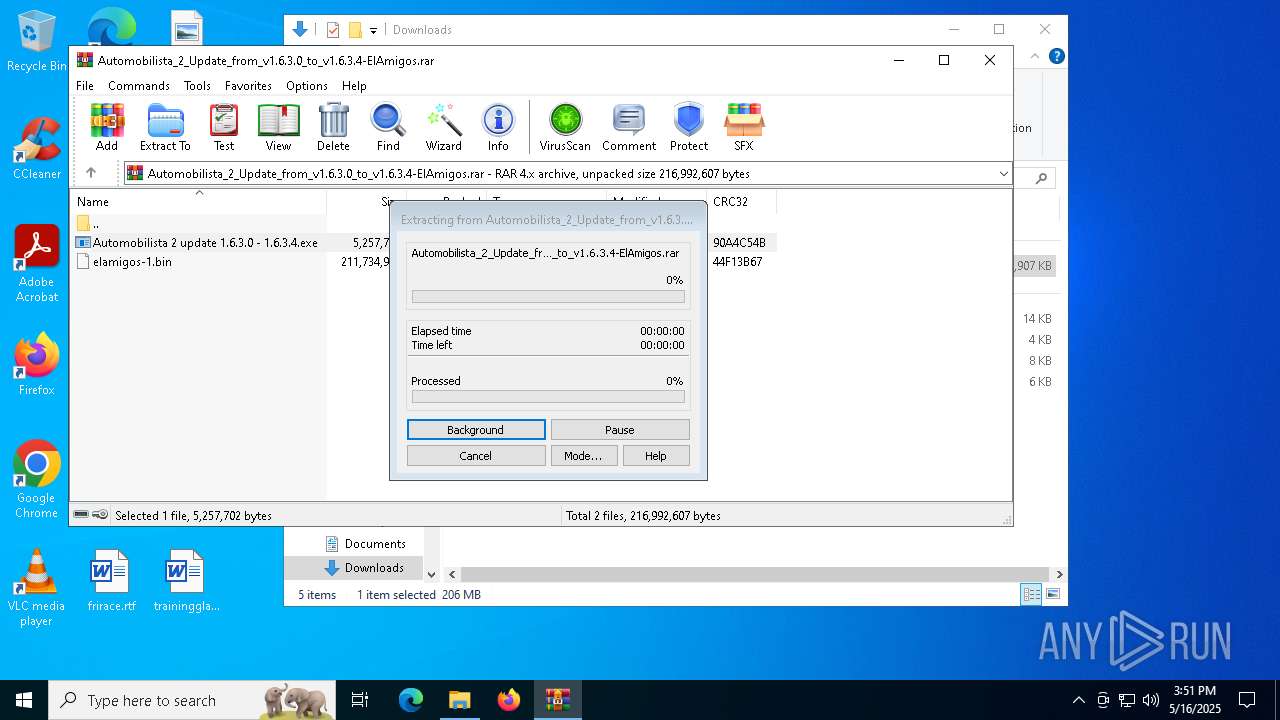
Executable content was dropped or overwritten
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 6272)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 5156)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 7296)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 7704)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 7204)
Process drops legitimate windows executable
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 7204)
Reads the Windows owner or organization settings
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
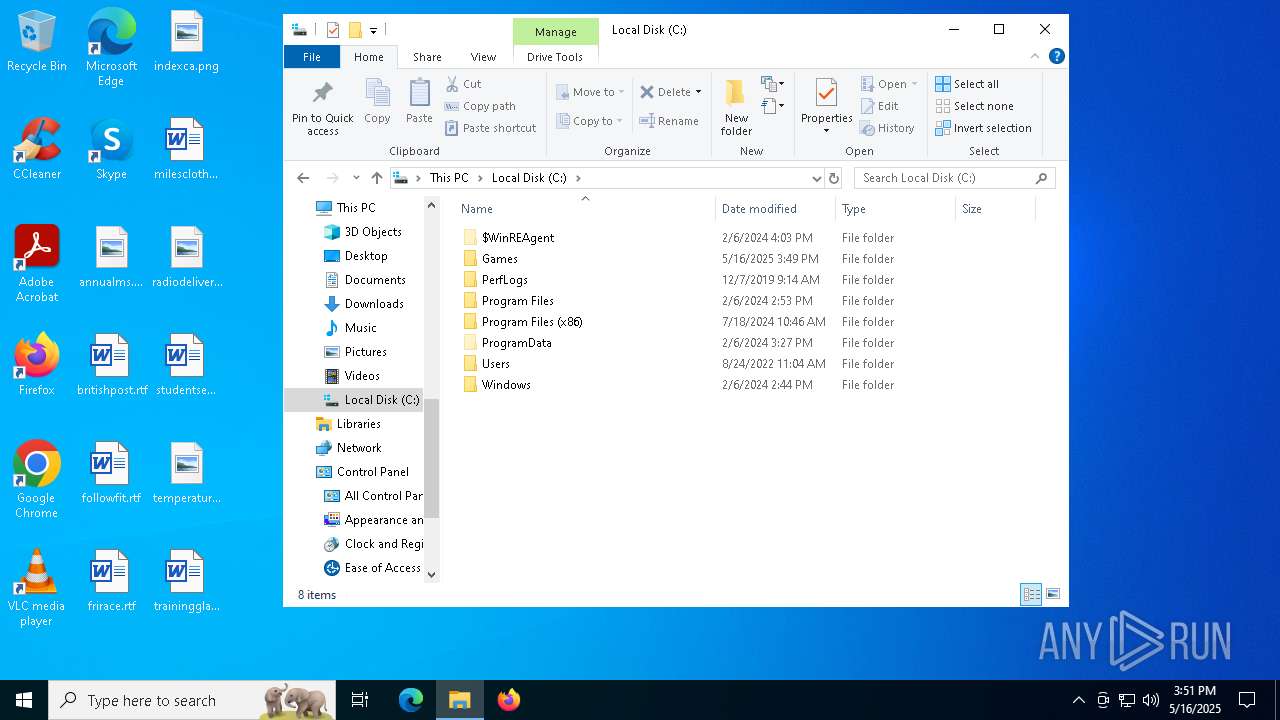
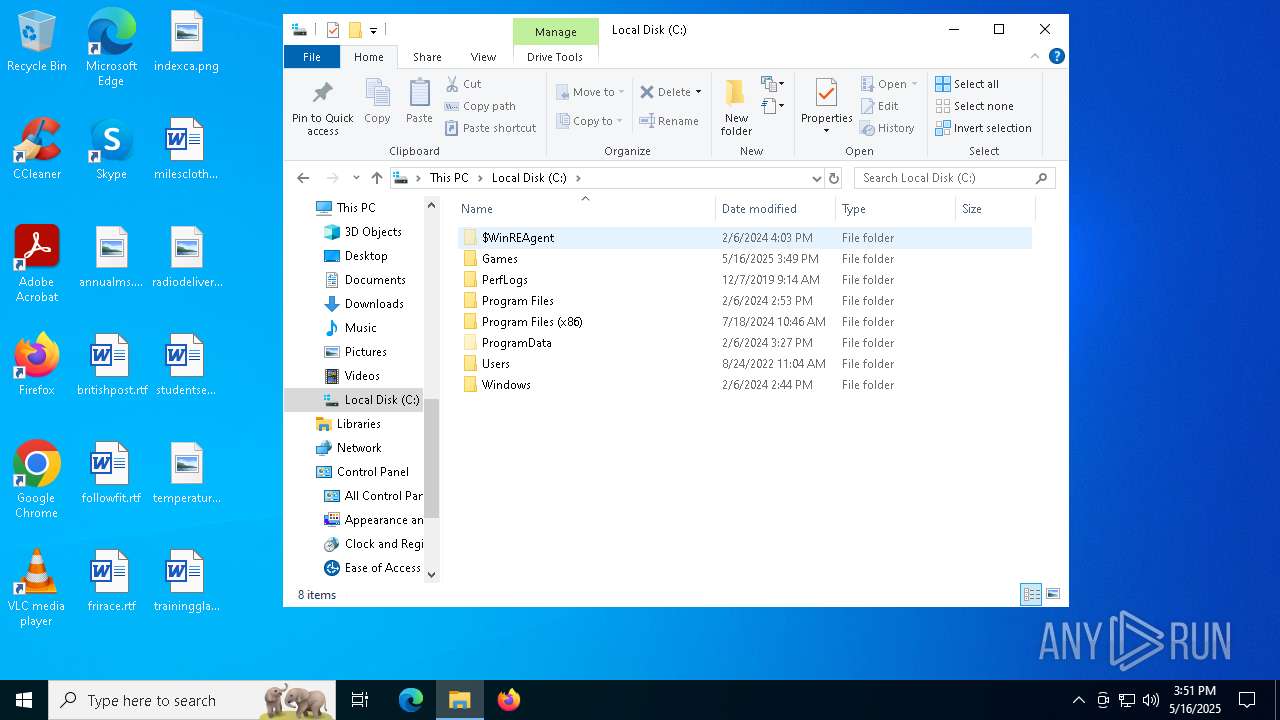
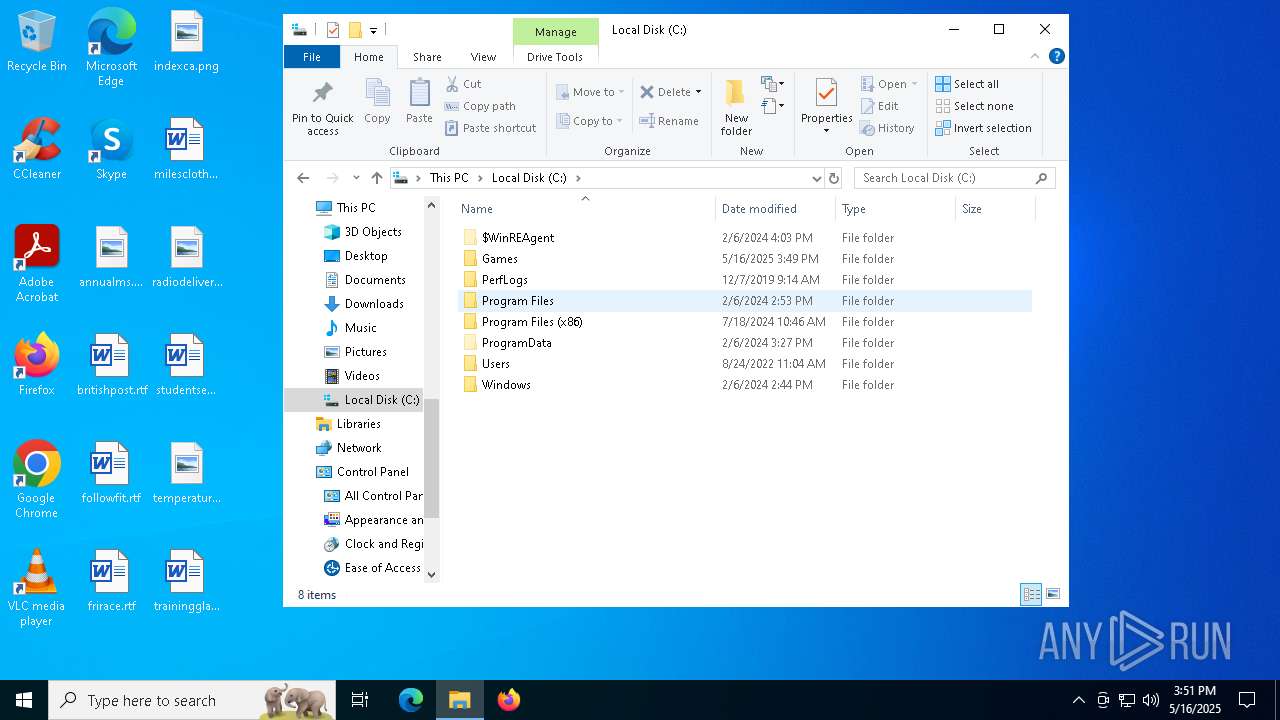
Creates file in the systems drive root
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
There is functionality for taking screenshot (YARA)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
Executing commands from a ".bat" file
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
Starts CMD.EXE for commands execution
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
INFO
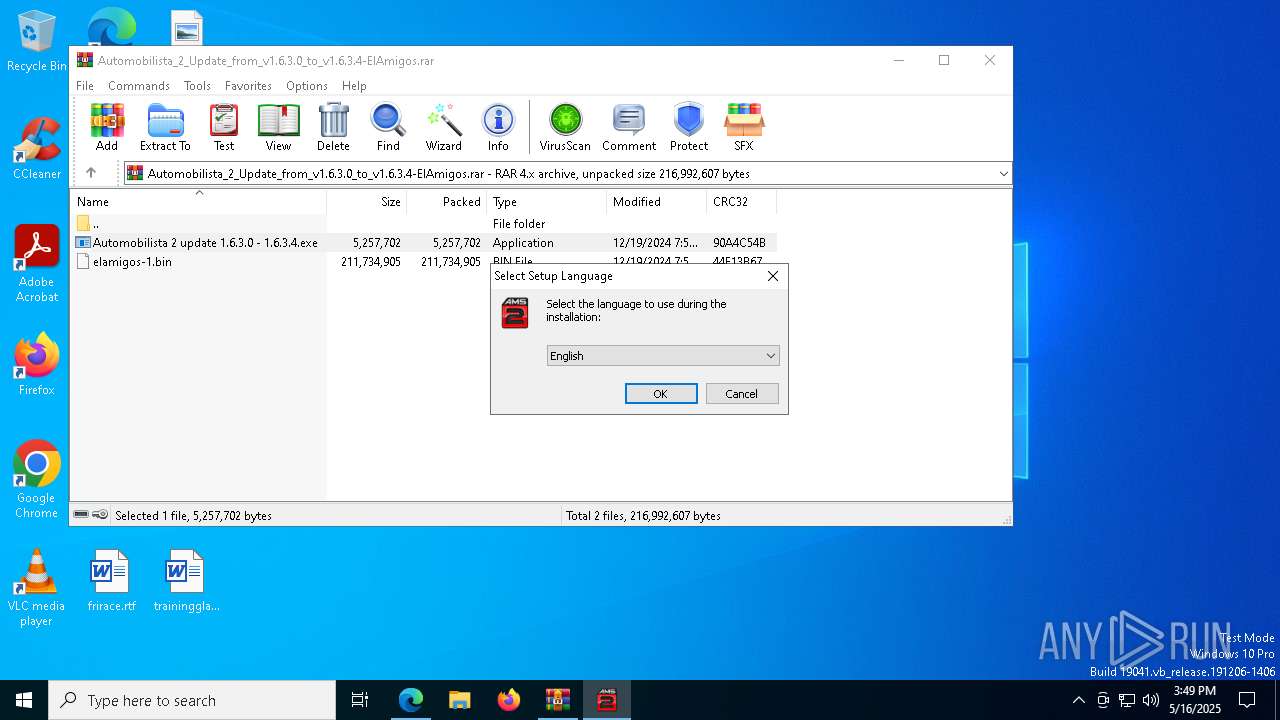
Checks supported languages
- identity_helper.exe (PID: 8160)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 6272)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 6852)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 5156)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
- srep64.exe (PID: 8040)
- hpatchz.exe (PID: 8092)
- hpatchz.exe (PID: 6576)
- hpatchz.exe (PID: 1040)
- hpatchz.exe (PID: 6752)
- hpatchz.exe (PID: 2984)
- hpatchz.exe (PID: 3620)
- hpatchz.exe (PID: 6592)
- hpatchz.exe (PID: 2104)
- hpatchz.exe (PID: 8068)
- hpatchz.exe (PID: 7628)
- hpatchz.exe (PID: 2152)
- hpatchz.exe (PID: 5968)
- hpatchz.exe (PID: 6264)
- hpatchz.exe (PID: 8148)
- hpatchz.exe (PID: 2980)
- hpatchz.exe (PID: 5332)
- hpatchz.exe (PID: 7888)
- hpatchz.exe (PID: 7920)
- hpatchz.exe (PID: 7932)
- hpatchz.exe (PID: 8168)
- hpatchz.exe (PID: 1912)
- hpatchz.exe (PID: 7720)
- hpatchz.exe (PID: 5116)
- hpatchz.exe (PID: 6228)
- hpatchz.exe (PID: 7844)
- hpatchz.exe (PID: 5964)
- hpatchz.exe (PID: 7796)
- hpatchz.exe (PID: 6656)
- hpatchz.exe (PID: 5008)
- hpatchz.exe (PID: 7852)
- hpatchz.exe (PID: 7712)
- hpatchz.exe (PID: 7940)
- hpatchz.exe (PID: 5172)
- hpatchz.exe (PID: 5796)
- hpatchz.exe (PID: 1616)
- hpatchz.exe (PID: 5548)
- hpatchz.exe (PID: 6192)
- hpatchz.exe (PID: 3008)
- hpatchz.exe (PID: 8124)
- hpatchz.exe (PID: 6876)
- hpatchz.exe (PID: 660)
- hpatchz.exe (PID: 5392)
- hpatchz.exe (PID: 1672)
- hpatchz.exe (PID: 1180)
- hpatchz.exe (PID: 6988)
- hpatchz.exe (PID: 5680)
- hpatchz.exe (PID: 8108)
- hpatchz.exe (PID: 7692)
- hpatchz.exe (PID: 1812)
- hpatchz.exe (PID: 7268)
- hpatchz.exe (PID: 7780)
- hpatchz.exe (PID: 4400)
- hpatchz.exe (PID: 2420)
- hpatchz.exe (PID: 8088)
- hpatchz.exe (PID: 456)
- hpatchz.exe (PID: 8156)
- hpatchz.exe (PID: 6044)
- hpatchz.exe (PID: 4724)
- hpatchz.exe (PID: 4892)
- hpatchz.exe (PID: 4220)
- hpatchz.exe (PID: 7676)
- hpatchz.exe (PID: 3304)
Reads Environment values
- identity_helper.exe (PID: 8160)
Reads the computer name
- identity_helper.exe (PID: 8160)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 6852)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
Application launched itself
- msedge.exe (PID: 5048)
- msedge.exe (PID: 5360)
Reads the software policy settings
- slui.exe (PID: 8144)
- slui.exe (PID: 6944)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5048)
Create files in a temporary directory
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 6272)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 5156)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
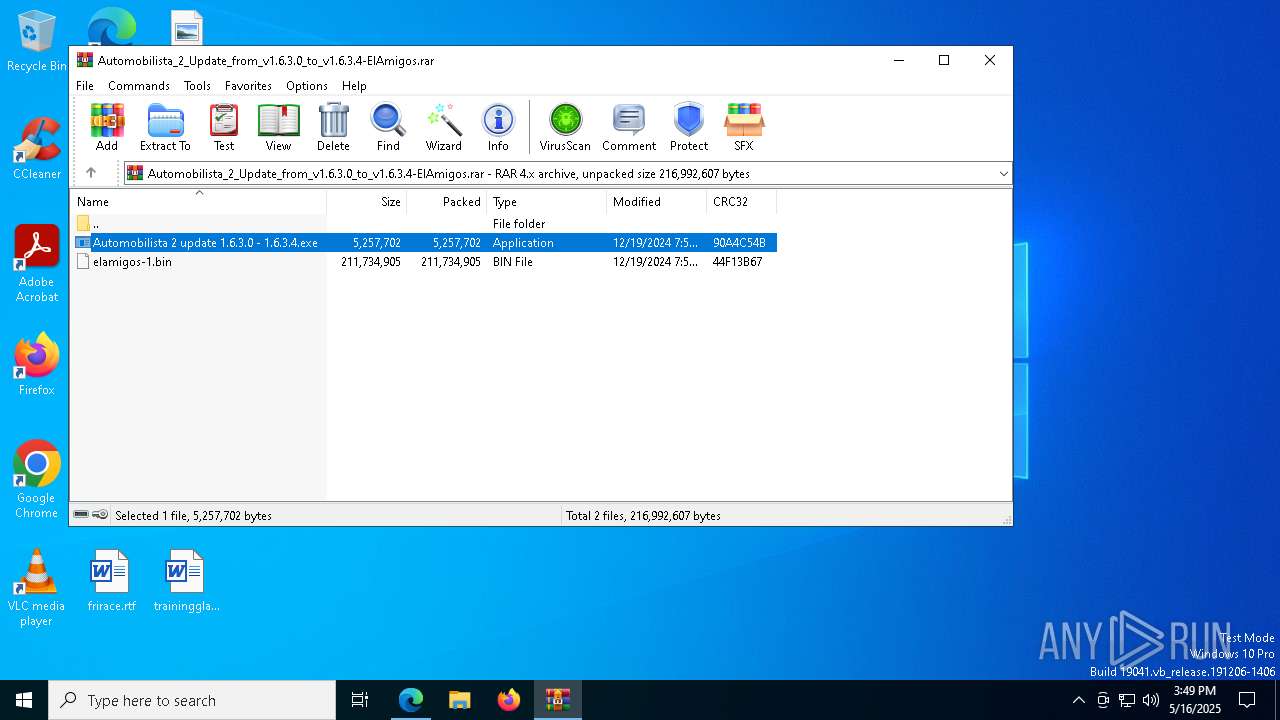
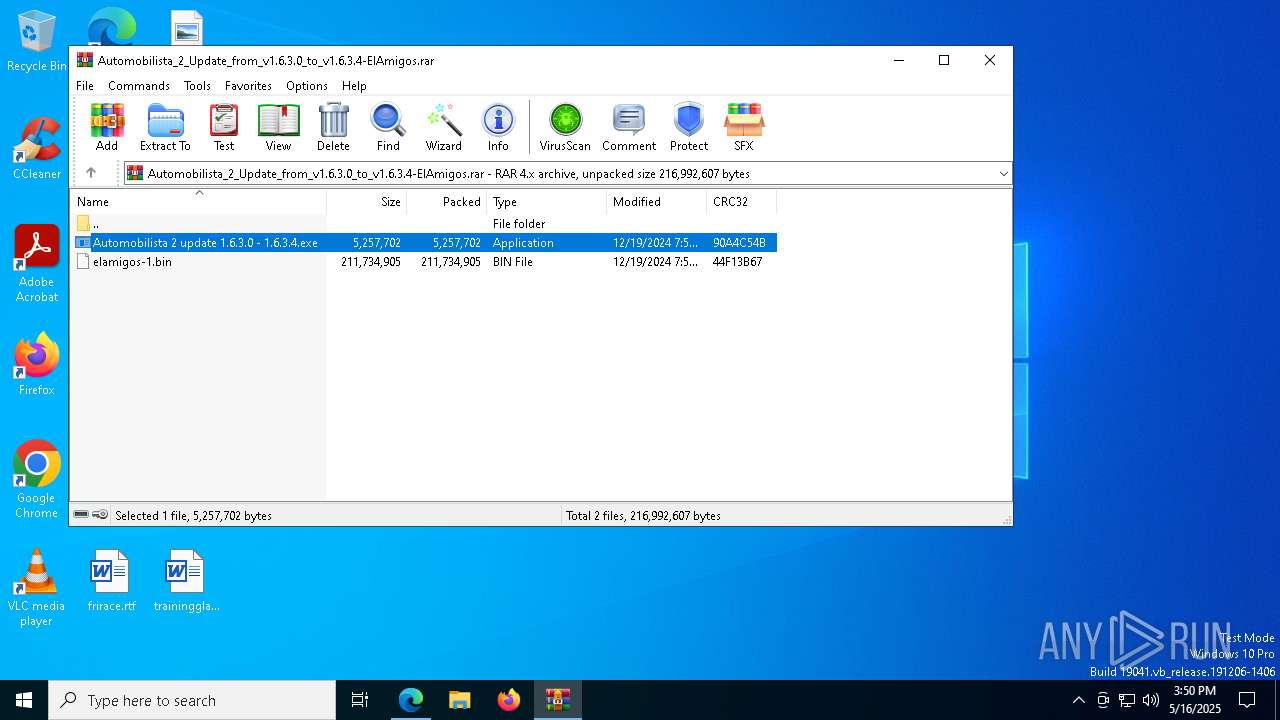
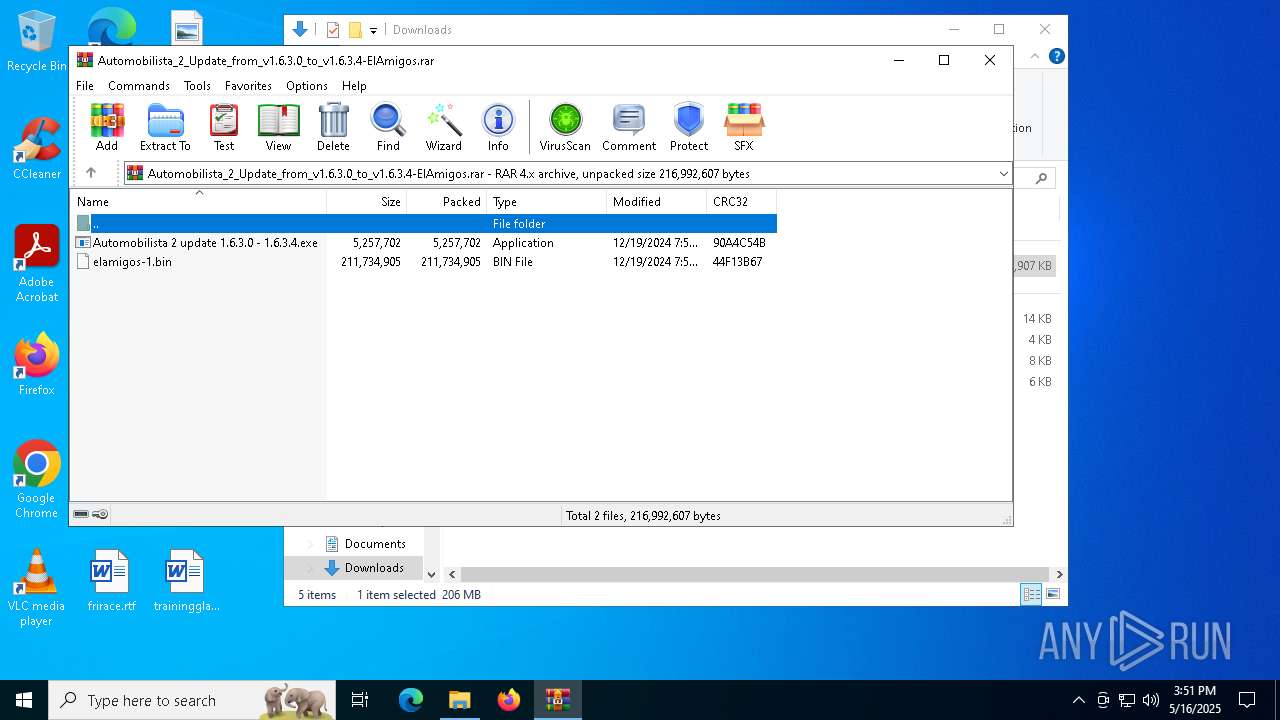
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2344)
- WinRAR.exe (PID: 3156)
Checks proxy server information
- slui.exe (PID: 6944)
Process checks computer location settings
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 6852)
The sample compiled with russian language support
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 7204)
The sample compiled with english language support
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 7204)
The sample compiled with chinese language support
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 7204)
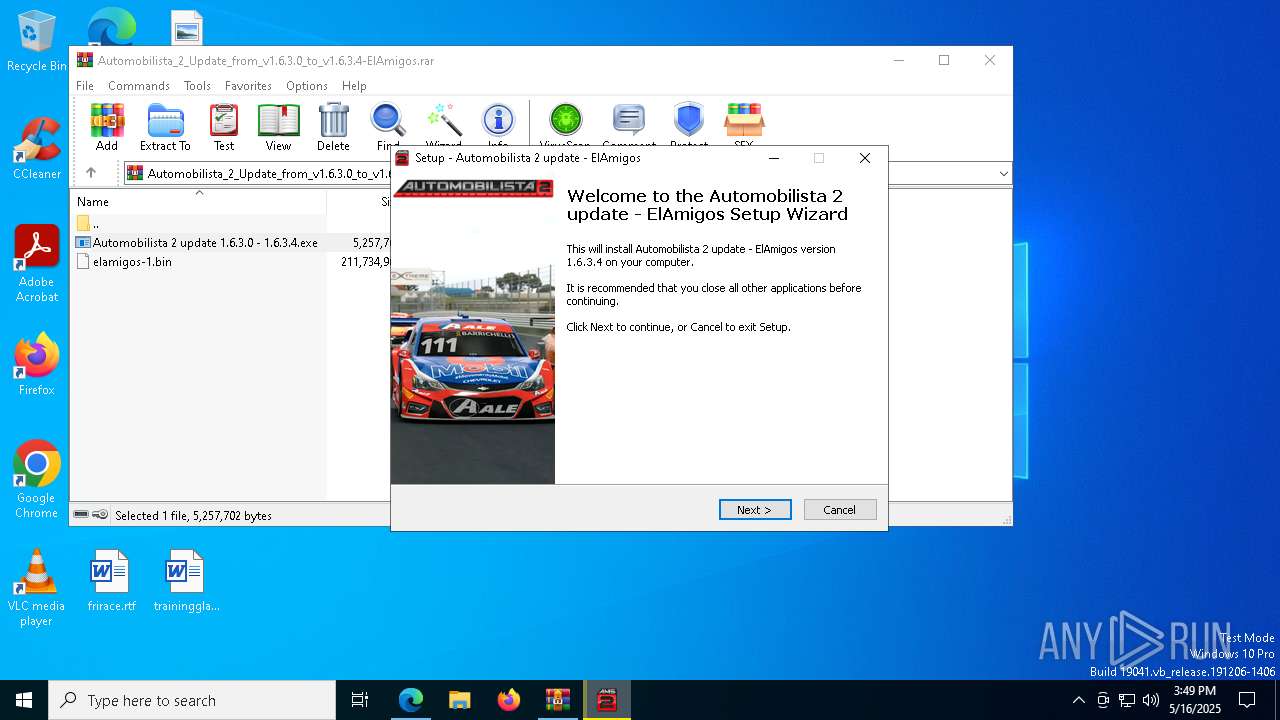
Compiled with Borland Delphi (YARA)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 6272)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 6852)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 5156)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
Detects InnoSetup installer (YARA)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 6272)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.exe (PID: 5156)
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 6852)
The sample compiled with german language support
- Automobilista 2 update 1.6.3.0 - 1.6.3.4.tmp (PID: 3784)
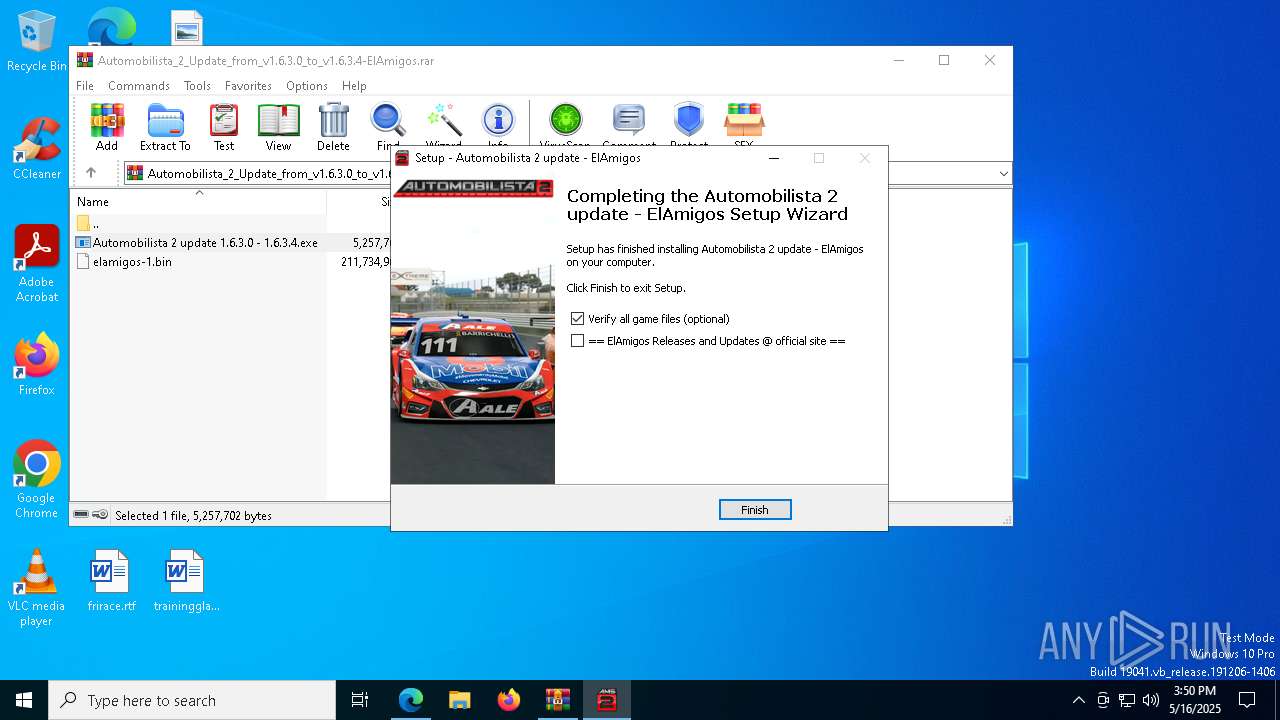
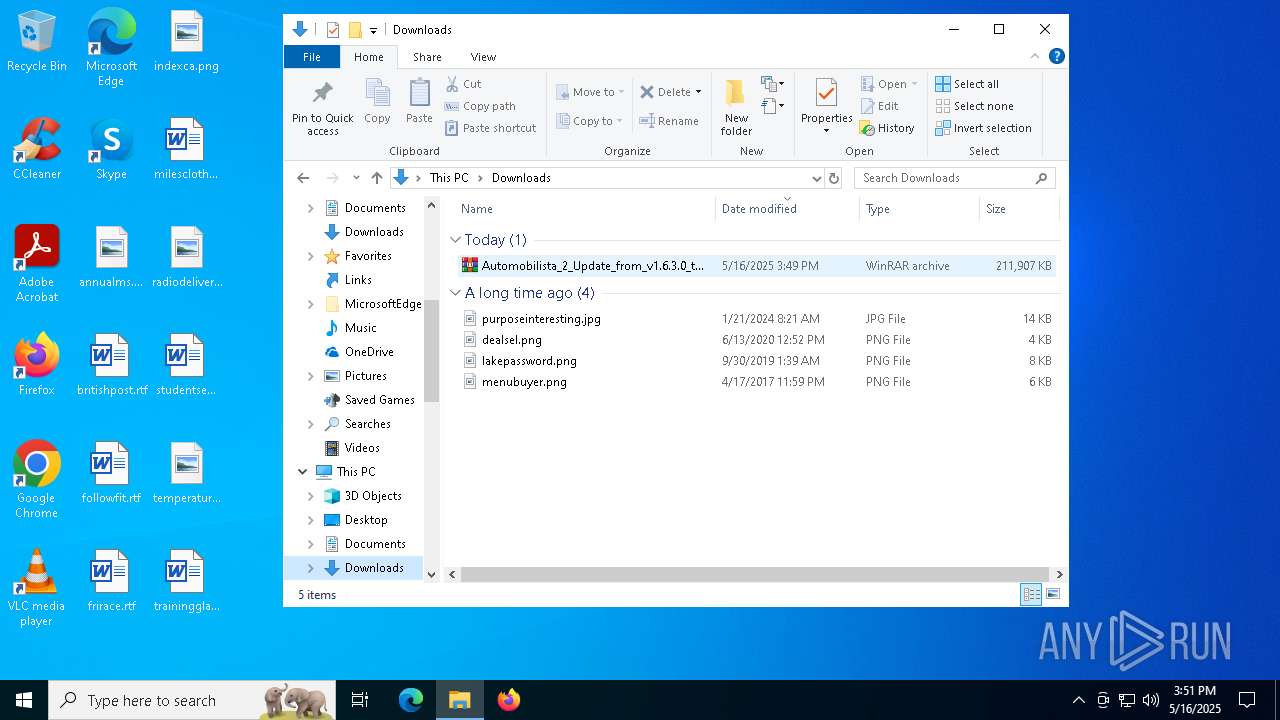
Manual execution by a user
- WinRAR.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
687
Monitored processes
546
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | hpatchz.exe "Pakfiles\Vehicles\McLaren_MP47.bff.tmp" "Pakfiles\Vehicles\McLaren_MP47.bff.patch" "Pakfiles\Vehicles\McLaren_MP47.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 132 | hpatchz.exe "Pakfiles\Vehicles\Formula_Retro_G3_TE.bff.tmp" "Pakfiles\Vehicles\Formula_Retro_G3_TE.bff.patch" "Pakfiles\Vehicles\Formula_Retro_G3_TE.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 132 | hpatchz.exe "Pakfiles\Vehicles\McLaren_F1_LM.bff.tmp" "Pakfiles\Vehicles\McLaren_F1_LM.bff.patch" "Pakfiles\Vehicles\McLaren_F1_LM.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 208 | hpatchz.exe "Pakfiles\TRACKS\OultonParkFosters_Physics.bff.tmp" "Pakfiles\TRACKS\OultonParkFosters_Physics.bff.patch" "Pakfiles\TRACKS\OultonParkFosters_Physics.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 236 | hpatchz.exe "Pakfiles\Vehicles\CART_Lola_B2K00_Ford.bff.tmp" "Pakfiles\Vehicles\CART_Lola_B2K00_Ford.bff.patch" "Pakfiles\Vehicles\CART_Lola_B2K00_Ford.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 236 | hpatchz.exe "Pakfiles\TRACKS\SPR_GoianiaOuter.bff.tmp" "Pakfiles\TRACKS\SPR_GoianiaOuter.bff.patch" "Pakfiles\TRACKS\SPR_GoianiaOuter.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 240 | hpatchz.exe "Pakfiles\Vehicles\CART_Reynard_98i_Toyota_SO.bff.tmp" "Pakfiles\Vehicles\CART_Reynard_98i_Toyota_SO.bff.patch" "Pakfiles\Vehicles\CART_Reynard_98i_Toyota_SO.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 240 | hpatchz.exe "Pakfiles\Vehicles\Mercedes_AMG_GT3.bff.tmp" "Pakfiles\Vehicles\Mercedes_AMG_GT3.bff.patch" "Pakfiles\Vehicles\Mercedes_AMG_GT3.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 300 | hpatchz.exe "Pakfiles\Vehicles\Formula_Classic_G1M1.bff.tmp" "Pakfiles\Vehicles\Formula_Classic_G1M1.bff.patch" "Pakfiles\Vehicles\Formula_Classic_G1M1.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
| 300 | hpatchz.exe "Pakfiles\Vehicles\Formula_Classic_G3M4.bff.tmp" "Pakfiles\Vehicles\Formula_Classic_G3M4.bff.patch" "Pakfiles\Vehicles\Formula_Classic_G3M4.bff" | C:\Games\Automobilista 2\hpatchz.exe | — | cmd.exe | |||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||
Total events
19 881
Read events
19 772
Write events
109
Delete events
0
Modification events
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 59C42EF9D8932F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6C8A38F9D8932F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AC962FA4-B30C-44E1-ADED-4F95B661AA03} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7B232187-F876-4E6F-9154-54C680C61FFE} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3B832C74-FD6A-4C4D-B8DC-72880B544F6D} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CDAB35C6-314F-4BAC-90F0-69F798C16B26} | |||
Executable files
89
Suspicious files
999
Text files
200
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bfe7.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bfe7.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bff6.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bff6.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c016.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
322
DNS requests
329
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4608 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7356 | msedge.exe | GET | 301 | 172.67.150.141:80 | http://s01.riotpixels.net/data/b6/a3/b6a3c056-96d2-4449-9180-dac905904351.jpg.240p.jpg | unknown | — | — | unknown |
632 | svchost.exe | HEAD | 200 | 23.50.131.90:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747705107&P2=404&P3=2&P4=j7cE5y9pVax3qVC9G4tfU16OICiLNao4qwzzN4ZhtnNgCAjmApw096EbFv%2buYxSiAu%2bb83RfBDTvU9vcjCb2tw%3d%3d | unknown | — | — | whitelisted |
7356 | msedge.exe | GET | 301 | 172.67.150.141:80 | http://s01.riotpixels.net/data/5e/b0/5eb0b8f7-9f3c-45b2-ab58-a9ddbfd2083d.jpg.240p.jpg | unknown | — | — | unknown |
632 | svchost.exe | GET | 206 | 23.50.131.90:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747705107&P2=404&P3=2&P4=j7cE5y9pVax3qVC9G4tfU16OICiLNao4qwzzN4ZhtnNgCAjmApw096EbFv%2buYxSiAu%2bb83RfBDTvU9vcjCb2tw%3d%3d | unknown | — | — | whitelisted |
7356 | msedge.exe | GET | 301 | 190.115.31.179:80 | http://fitgirl-repacks.site/wp-content/uploads/2016/08/cropped-icon-192x192.jpg | unknown | — | — | unknown |
632 | svchost.exe | GET | 206 | 23.50.131.90:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747705107&P2=404&P3=2&P4=j7cE5y9pVax3qVC9G4tfU16OICiLNao4qwzzN4ZhtnNgCAjmApw096EbFv%2buYxSiAu%2bb83RfBDTvU9vcjCb2tw%3d%3d | unknown | — | — | whitelisted |
632 | svchost.exe | GET | 206 | 23.50.131.90:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747705107&P2=404&P3=2&P4=j7cE5y9pVax3qVC9G4tfU16OICiLNao4qwzzN4ZhtnNgCAjmApw096EbFv%2buYxSiAu%2bb83RfBDTvU9vcjCb2tw%3d%3d | unknown | — | — | whitelisted |
7356 | msedge.exe | GET | 301 | 172.67.150.141:80 | http://s01.riotpixels.net/data/94/c3/94c3b33d-92cc-450b-baf2-a103c446c974.jpg.240p.jpg | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7356 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5048 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7356 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
elamigosedition.com |
| unknown |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7356 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7356 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |