| File name: | PO.doc |
| Full analysis: | https://app.any.run/tasks/991d0a69-ae7a-4fe7-bc04-d679247d02e5 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | May 20, 2019, 11:58:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 162699F4F1AD38EF4E538F72DBBEA609 |
| SHA1: | A5388724227BD4679CB9AE16ED4D142032D0968D |
| SHA256: | 18F9405DF1C40772A5C91C753D0283C7FE434B5F2C5C15C457D71A15B061DE58 |
| SSDEEP: | 3072:oH3XciTuHeaUNlpdXciTuHeaUNlpdXciTuHeaUNlpdXciTuHeaUNlpdXciTuHeaz:UIbUjzIbUjzIbUjzIbUjzIbUjYHIS |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2312)
- EXCEL.EXE (PID: 3028)
- EXCEL.EXE (PID: 2900)
- EXCEL.EXE (PID: 1736)
- EXCEL.EXE (PID: 2356)
- WINWORD.EXE (PID: 3532)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 3028)
- EXCEL.EXE (PID: 2900)
- EXCEL.EXE (PID: 1736)
- EXCEL.EXE (PID: 2356)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2312)
- EXCEL.EXE (PID: 3028)
- EXCEL.EXE (PID: 2900)
- EXCEL.EXE (PID: 1736)
- EXCEL.EXE (PID: 2356)
Requests a remote executable file from MS Office
- EXCEL.EXE (PID: 2312)
- EXCEL.EXE (PID: 3028)
- EXCEL.EXE (PID: 2900)
- EXCEL.EXE (PID: 1736)
- EXCEL.EXE (PID: 2356)
Application was dropped or rewritten from another process
- j18587.exe (PID: 3696)
- j18587.exe (PID: 916)
- j18587.exe (PID: 2736)
- j18587.exe (PID: 1752)
- j18587.exe (PID: 3164)
- j18587.exe (PID: 300)
- j18587.exe (PID: 2084)
- j18587.exe (PID: 2456)
- j18587.exe (PID: 3796)
- j18587.exe (PID: 3592)
- j18587.exe (PID: 2744)
- j18587.exe (PID: 2844)
FORMBOOK was detected
- explorer.exe (PID: 116)
Connects to CnC server
- explorer.exe (PID: 116)
Changes the autorun value in the registry
- services.exe (PID: 2452)
Formbook was detected
- services.exe (PID: 2452)
- Firefox.exe (PID: 968)
Actions looks like stealing of personal data
- services.exe (PID: 2452)
Stealing of credential data
- services.exe (PID: 2452)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 3028)
- EXCEL.EXE (PID: 2312)
- EXCEL.EXE (PID: 2900)
- EXCEL.EXE (PID: 1736)
- EXCEL.EXE (PID: 2356)
- excelcnv.exe (PID: 2468)
Executable content was dropped or overwritten
- cmd.exe (PID: 2356)
- cmd.exe (PID: 3644)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 3412)
- cmd.exe (PID: 2244)
Starts CMD.EXE for commands execution
- j18587.exe (PID: 916)
- j18587.exe (PID: 2736)
- j18587.exe (PID: 3696)
- j18587.exe (PID: 1752)
- j18587.exe (PID: 3164)
- services.exe (PID: 2452)
Application launched itself
- j18587.exe (PID: 916)
- j18587.exe (PID: 3696)
- j18587.exe (PID: 2736)
- j18587.exe (PID: 1752)
- j18587.exe (PID: 3164)
Reads Internet Cache Settings
- explorer.exe (PID: 116)
- WINWORD.EXE (PID: 3532)
Creates files in the user directory
- services.exe (PID: 2452)
- explorer.exe (PID: 116)
Loads DLL from Mozilla Firefox
- services.exe (PID: 2452)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 116)
Creates files in the user directory
- WINWORD.EXE (PID: 3532)
- Firefox.exe (PID: 968)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2312)
- WINWORD.EXE (PID: 3532)
- EXCEL.EXE (PID: 3028)
- EXCEL.EXE (PID: 2900)
- EXCEL.EXE (PID: 1736)
- EXCEL.EXE (PID: 2356)
- excelcnv.exe (PID: 2468)
- WINWORD.EXE (PID: 1808)
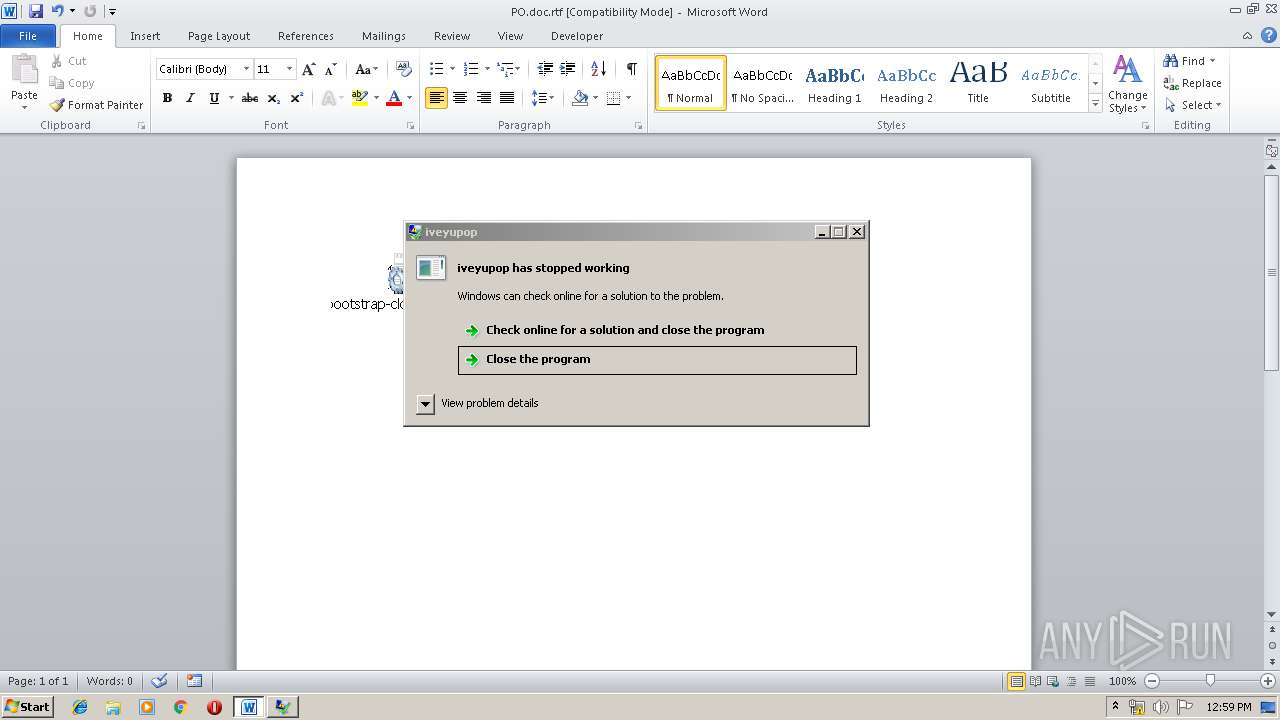
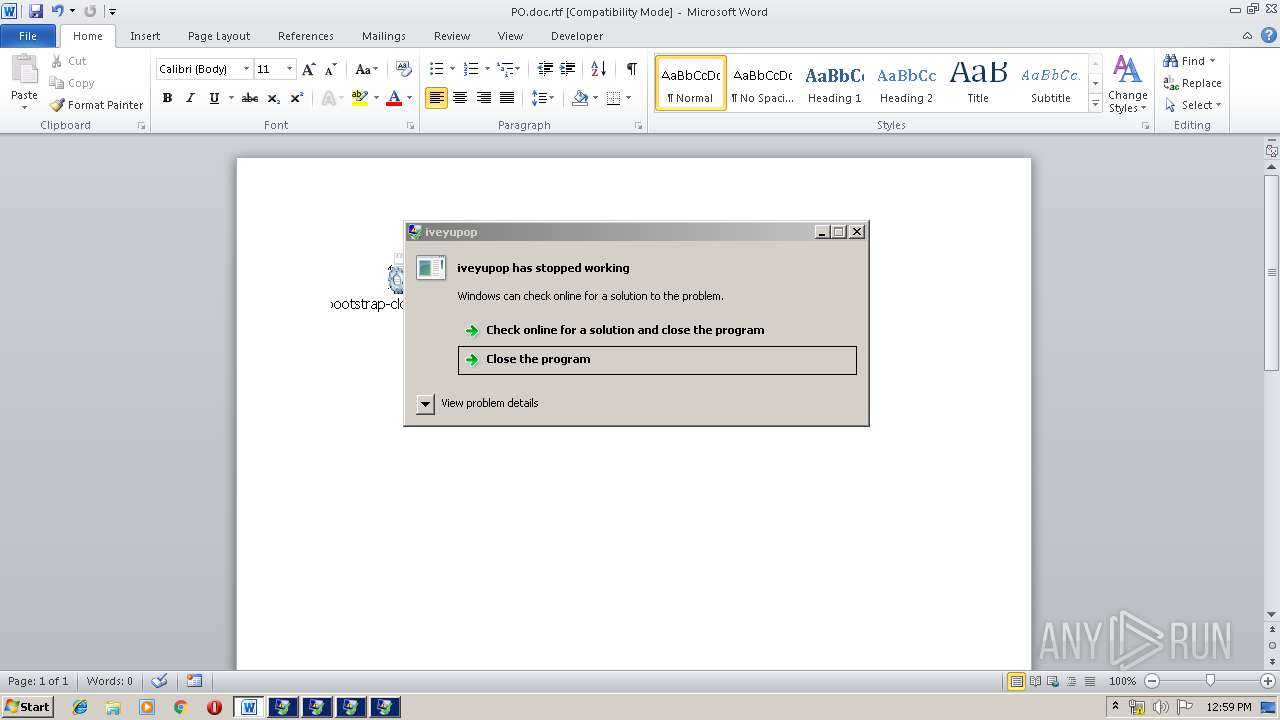
Application was crashed
- j18587.exe (PID: 916)
- j18587.exe (PID: 3696)
- j18587.exe (PID: 2736)
- j18587.exe (PID: 1752)
- j18587.exe (PID: 3164)
Manual execution by user
- services.exe (PID: 2452)
- wininit.exe (PID: 2336)
- autofmt.exe (PID: 2124)
- wlanext.exe (PID: 3284)
- autochk.exe (PID: 1872)
- lsass.exe (PID: 3184)
- wlanext.exe (PID: 2756)
- WINWORD.EXE (PID: 1808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Admin |
|---|---|
| LastModifiedBy: | Admin |
| CreateDate: | 2019:01:07 23:54:00 |
| ModifyDate: | 2019:01:07 23:54:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 4 |
| CharactersWithSpaces: | 4 |
| InternalVersionNumber: | 57435 |
Total processes
101
Monitored processes
46
Malicious processes
13
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 300 | "C:\Users\admin\AppData\Local\Temp\j18587.exe" | C:\Users\admin\AppData\Local\Temp\j18587.exe | — | j18587.exe | |||||||||||
User: admin Company: amitanuhum Integrity Level: MEDIUM Description: iveyupop Exit code: 0 Version: 6.9.11.14 Modules
| |||||||||||||||
| 916 | "C:\Users\admin\AppData\Local\Temp\j18587.exe" | C:\Users\admin\AppData\Local\Temp\j18587.exe | cmd.exe | ||||||||||||
User: admin Company: amitanuhum Integrity Level: MEDIUM Description: iveyupop Exit code: 3762504530 Version: 6.9.11.14 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | services.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1088 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\AppData\Local\Temp\j18587.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | j18587.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1752 | "C:\Users\admin\AppData\Local\Temp\j18587.exe" | C:\Users\admin\AppData\Local\Temp\j18587.exe | cmd.exe | ||||||||||||
User: admin Company: amitanuhum Integrity Level: MEDIUM Description: iveyupop Exit code: 3762504530 Version: 6.9.11.14 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\costfurther.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1872 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\AppData\Local\Temp\j18587.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | j18587.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1872 | "C:\Windows\System32\autochk.exe" | C:\Windows\System32\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 403
Read events
3 833
Write events
533
Delete events
37
Modification events
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2r> |
Value: 32723E00CC0D0000010000000000000000000000 | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419472 | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419473 | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: CC0D00005829E85C030FD50100000000 | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | &t> |
Value: 26743E00CC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | &t> |
Value: 26743E00CC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
9
Suspicious files
73
Text files
4
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREEA3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2312 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRF9CE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2312 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\j18587.png | — | |
MD5:— | SHA256:— | |||
| 3028 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR3B1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2900 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9AD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1736 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRF98.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2356 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR1620.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2468 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\CVR1FF4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2468 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\~DFA730388AC896955E.TMP | — | |
MD5:— | SHA256:— | |||
| 3532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFEBC44357640B5E80.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
22
DNS requests
11
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | explorer.exe | GET | — | 154.220.64.238:80 | http://www.edmov.com/sa/?BZ=VFosjuBCN5EUWjKveFNzek6pIBmrEIqfGEoqa6hcC5zLROLzG37LjDPVuE49C4TU2r26Jg==&CtbL8=4hiHZl | US | — | — | malicious |
116 | explorer.exe | GET | — | 192.64.115.176:80 | http://www.skylod.com/sa/?BZ=SM5LhZrjIDszq8dWOR01LJjTq42xusFjlyDX+xwSOXHFKXRdwY68gAObCx9XlQsiARbQ5A==&CtbL8=4hiHZl | US | — | — | malicious |
2900 | EXCEL.EXE | GET | 200 | 46.105.57.169:80 | http://mpctunisia.com/wp-content/themes/POOI.exe | FR | executable | 393 Kb | malicious |
116 | explorer.exe | GET | — | 198.49.23.144:80 | http://www.kaseyandersonmusic.com/sa/?BZ=xwlUphGcljDq4VdtMAIAXu1Aucpda0PK6WggYWQEY7PXIJ0kGq340WR1Xy/xH723DlRDpA==&CtbL8=4hiHZl | US | — | — | malicious |
116 | explorer.exe | GET | — | 68.65.122.35:80 | http://www.platinumpowerplanet.com/sa/?BZ=FMNZ+0IdmlbWClhIRL1zH4ioMZAu2cNWWZdSVvCo/W0rMf8qfMIhQ09QKucyhlyjNaLzUA==&CtbL8=4hiHZl&sql=1 | US | — | — | malicious |
116 | explorer.exe | POST | — | 194.156.114.28:80 | http://www.ih73.com/sa/ | unknown | — | — | malicious |
116 | explorer.exe | POST | — | 194.156.114.28:80 | http://www.ih73.com/sa/ | unknown | — | — | malicious |
2312 | EXCEL.EXE | GET | 200 | 46.105.57.169:80 | http://mpctunisia.com/wp-content/themes/POOI.exe | FR | executable | 393 Kb | malicious |
116 | explorer.exe | POST | 404 | 192.64.115.176:80 | http://www.skylod.com/sa/ | US | html | 290 b | malicious |
116 | explorer.exe | POST | — | 192.64.115.176:80 | http://www.skylod.com/sa/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2312 | EXCEL.EXE | 46.105.57.169:80 | mpctunisia.com | OVH SAS | FR | malicious |
3028 | EXCEL.EXE | 46.105.57.169:80 | mpctunisia.com | OVH SAS | FR | malicious |
116 | explorer.exe | 192.64.115.176:80 | www.skylod.com | Namecheap, Inc. | US | malicious |
116 | explorer.exe | 154.220.64.238:80 | www.edmov.com | MULTACOM CORPORATION | US | malicious |
116 | explorer.exe | 68.65.122.35:80 | www.platinumpowerplanet.com | Namecheap, Inc. | US | malicious |
116 | explorer.exe | 198.49.23.144:80 | www.kaseyandersonmusic.com | Squarespace, Inc. | US | malicious |
2900 | EXCEL.EXE | 46.105.57.169:80 | mpctunisia.com | OVH SAS | FR | malicious |
1736 | EXCEL.EXE | 46.105.57.169:80 | mpctunisia.com | OVH SAS | FR | malicious |
116 | explorer.exe | 194.156.114.28:80 | www.ih73.com | — | — | malicious |
2356 | EXCEL.EXE | 46.105.57.169:80 | mpctunisia.com | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mpctunisia.com |
| malicious |
www.hsctsu.com |
| unknown |
www.edmov.com |
| malicious |
www.reclaimingmyprime.com |
| malicious |
www.kdmarke.com |
| unknown |
www.ih73.com |
| malicious |
www.platinumpowerplanet.com |
| malicious |
www.wescoch.life |
| unknown |
www.skylod.com |
| malicious |
www.jonstats.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2312 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
2312 | EXCEL.EXE | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
2312 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3028 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3028 | EXCEL.EXE | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
3028 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2900 | EXCEL.EXE | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
2900 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1736 | EXCEL.EXE | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
1736 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
18 ETPRO signatures available at the full report