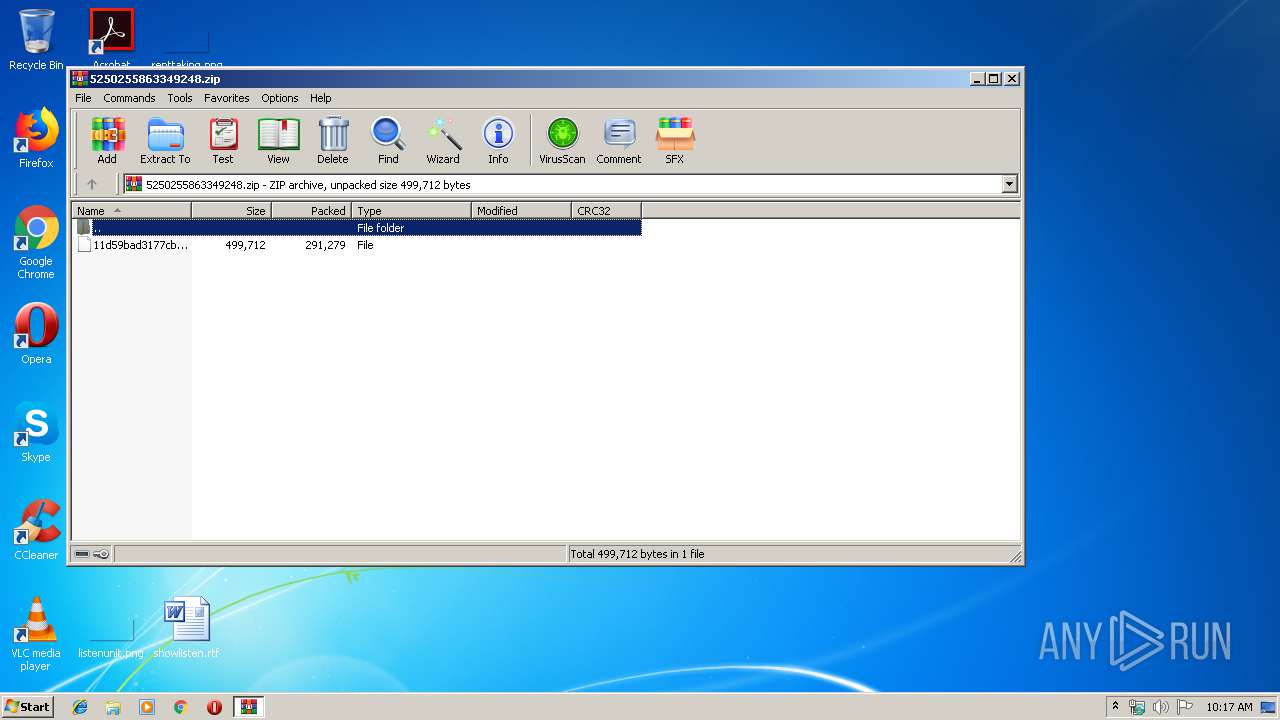
| File name: | 5250255863349248.zip |
| Full analysis: | https://app.any.run/tasks/0a7652e3-098c-496b-8615-d76753923b59 |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | August 25, 2019, 09:17:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | FD5946F2085CD379B53DE567E709E3D6 |
| SHA1: | 4C029A72EEBEFF5FA97E682542E3AFD5AB4DD12D |
| SHA256: | 18E07E4292B5A0FAAC0DC1CCE366F7744025BF91ADBA3BFDCA99EA770A2B704A |
| SSDEEP: | 6144:pi0cK+SfJvrEv6iZip+Le9qkU2cl1X0nadpc9l7c4JZ08UUCgPz+:U0cFwvIvy9Yjl1kazc9hNJZn7+ |
MALICIOUS
Application was dropped or rewritten from another process
- ПАКсЕыЦолИс.exe (PID: 3796)
- 123.exe (PID: 2840)
- ПАКсЕыЦолИс.exe (PID: 3852)
- ПАКсЕыЦолИс.exe (PID: 184)
Known privilege escalation attack
- DllHost.exe (PID: 2772)
Loads the Task Scheduler COM API
- ПАКсЕыЦолИс.exe (PID: 3796)
- ПАКсЕыЦолИс.exe (PID: 184)
Connects to CnC server
- ПАКсЕыЦолИс.exe (PID: 184)
TRICKBOT was detected
- ПАКсЕыЦолИс.exe (PID: 184)
SUSPICIOUS
Creates files in the user directory
- ПАКсЕыЦолИс.exe (PID: 3852)
- ПАКсЕыЦолИс.exe (PID: 184)
Creates files in the program directory
- ПАКсЕыЦолИс.exe (PID: 184)
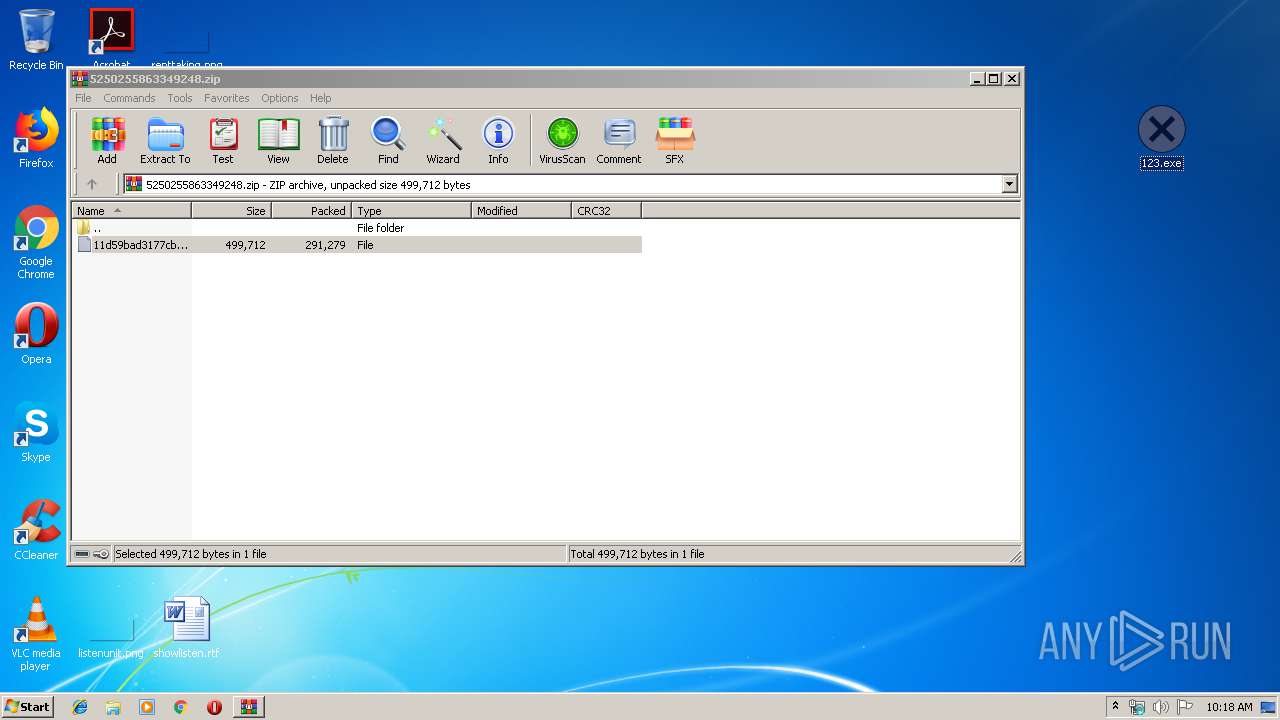
- 123.exe (PID: 2840)
Executed via Task Scheduler
- ПАКсЕыЦолИс.exe (PID: 184)
Starts itself from another location
- 123.exe (PID: 2840)
Executable content was dropped or overwritten
- 123.exe (PID: 2840)
- ПАКсЕыЦолИс.exe (PID: 3852)
Executed via COM
- DllHost.exe (PID: 2772)
Removes files from Windows directory
- ПАКсЕыЦолИс.exe (PID: 184)
Creates files in the Windows directory
- ПАКсЕыЦолИс.exe (PID: 184)
Checks for external IP
- ПАКсЕыЦолИс.exe (PID: 184)
INFO
Manual execution by user
- 123.exe (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 291279 |
| ZipUncompressedSize: | 499712 |
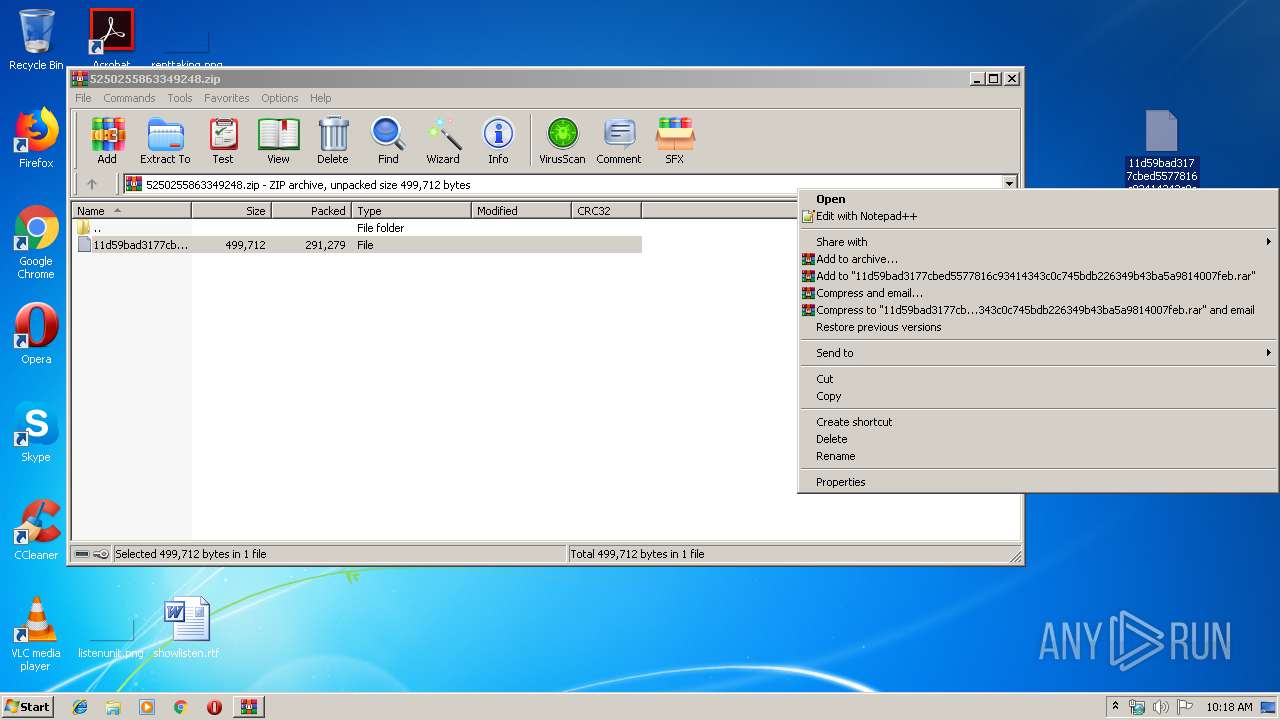
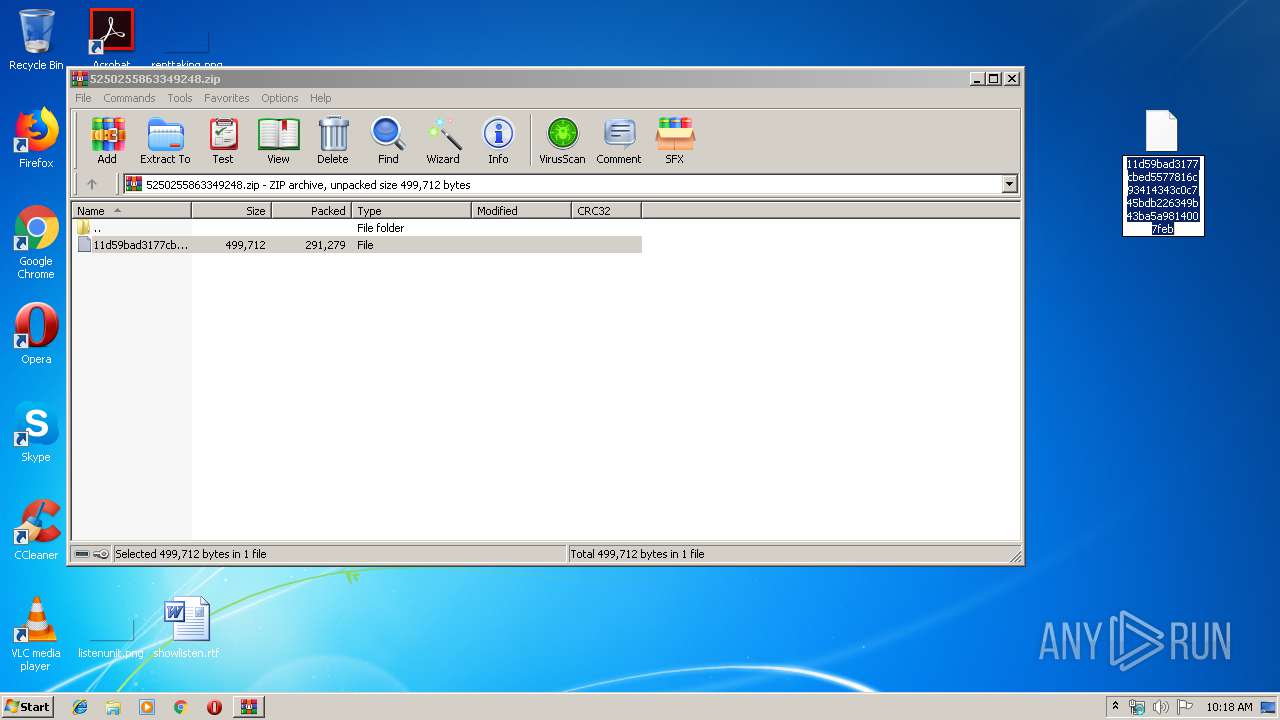
| ZipFileName: | 11d59bad3177cbed5577816c93414343c0c745bdb226349b43ba5a9814007feb |
Total processes
41
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | C:\Users\admin\AppData\Roaming\speedlink\ПАКсЕыЦолИс.exe | C:\Users\admin\AppData\Roaming\speedlink\ПАКсЕыЦолИс.exe | taskeng.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Win32 API DLL Exit code: 0 Version: 6.1.7601.17887 (win7sp1_gdr.120704-0720) Modules
| |||||||||||||||
| 2772 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | "C:\Users\admin\Desktop\123.exe" | C:\Users\admin\Desktop\123.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Win32 API DLL Exit code: 0 Version: 6.1.7601.17887 (win7sp1_gdr.120704-0720) Modules
| |||||||||||||||
| 3408 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\5250255863349248.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3796 | "C:\Users\admin\AppData\Roaming\speedlink\ПАКсЕыЦолИс.exe" | C:\Users\admin\AppData\Roaming\speedlink\ПАКсЕыЦолИс.exe | — | DllHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Win32 API DLL Exit code: 0 Version: 6.1.7601.17887 (win7sp1_gdr.120704-0720) Modules
| |||||||||||||||
| 3852 | "C:\ProgramData\ПАКсЕыЦолИс.exe" | C:\ProgramData\ПАКсЕыЦолИс.exe | 123.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Win32 API DLL Exit code: 0 Version: 6.1.7601.17887 (win7sp1_gdr.120704-0720) Modules
| |||||||||||||||
Total events
854
Read events
827
Write events
27
Delete events
0
Modification events
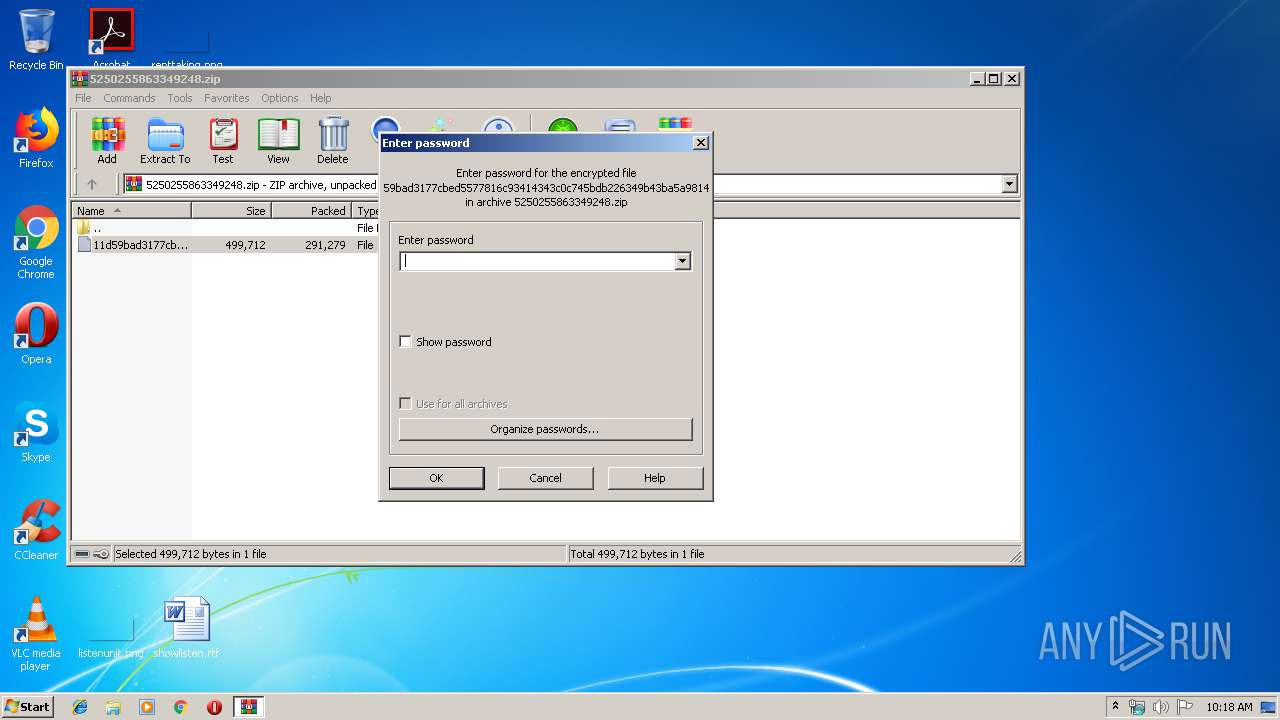
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5250255863349248.zip | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2840) 123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
8
Text files
1
Unknown types
0
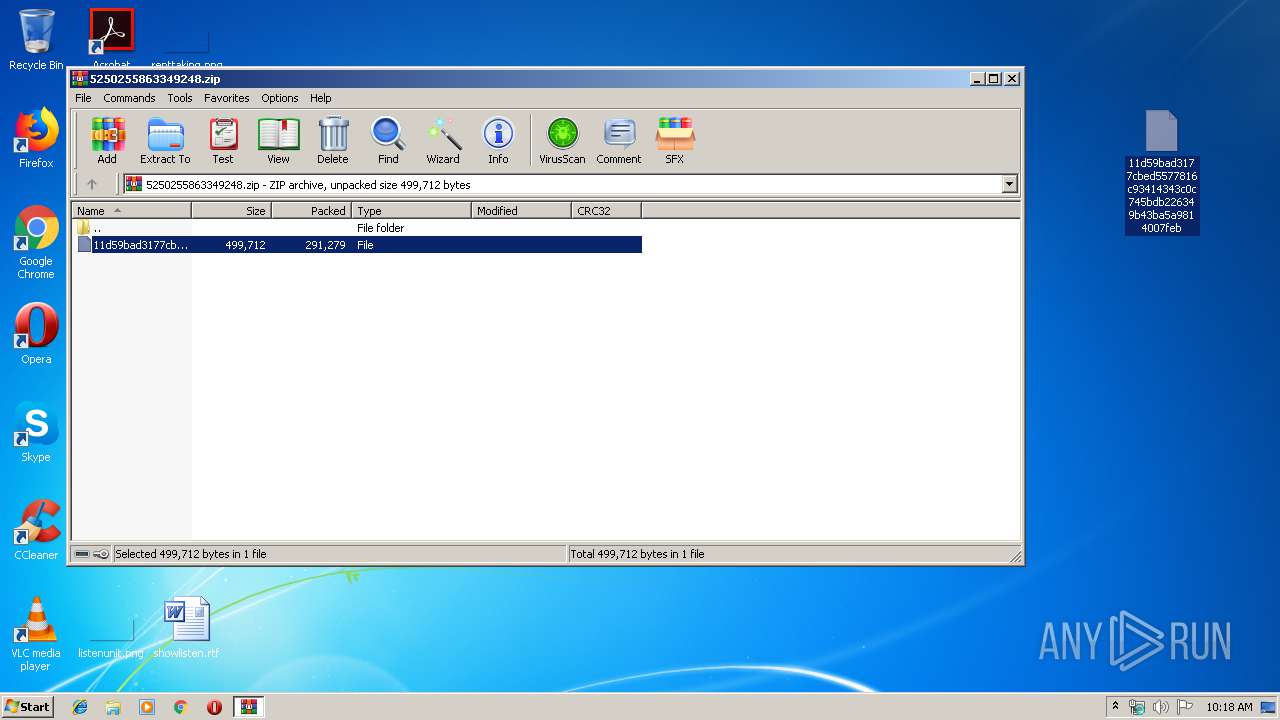
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3408 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3408.19244\11d59bad3177cbed5577816c93414343c0c745bdb226349b43ba5a9814007feb | — | |
MD5:— | SHA256:— | |||
| 184 | ПАКсЕыЦолИс.exe | C:\Windows\TEMP\CabF075.tmp | — | |
MD5:— | SHA256:— | |||
| 184 | ПАКсЕыЦолИс.exe | C:\Windows\TEMP\TarF076.tmp | — | |
MD5:— | SHA256:— | |||
| 184 | ПАКсЕыЦолИс.exe | C:\Windows\TEMP\CabF097.tmp | — | |
MD5:— | SHA256:— | |||
| 184 | ПАКсЕыЦолИс.exe | C:\Windows\TEMP\TarF098.tmp | — | |
MD5:— | SHA256:— | |||
| 184 | ПАКсЕыЦолИс.exe | C:\Windows\TEMP\Cab569.tmp | — | |
MD5:— | SHA256:— | |||
| 184 | ПАКсЕыЦолИс.exe | C:\Windows\TEMP\Tar56A.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | 123.exe | C:\ProgramData\ПАКсЕыЦолИс.exe | executable | |
MD5:— | SHA256:— | |||
| 184 | ПАКсЕыЦолИс.exe | C:\Users\admin\AppData\Roaming\speedlink\settings.ini | text | |
MD5:— | SHA256:— | |||
| 184 | ПАКсЕыЦолИс.exe | C:\ProgramData\Microsoft\Crypto\RSA\S-1-5-18\6d14e4b1d8ca773bab785d1be032546e_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
4
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
184 | ПАКсЕыЦолИс.exe | GET | 200 | 23.23.243.154:80 | http://api.ipify.org/ | US | text | 12 b | shared |
184 | ПАКсЕыЦолИс.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
184 | ПАКсЕыЦолИс.exe | 178.157.82.90:443 | — | Nav Communications Srl | RO | suspicious |
184 | ПАКсЕыЦолИс.exe | 31.184.253.6:443 | — | — | RU | malicious |
184 | ПАКсЕыЦолИс.exe | 23.23.243.154:80 | api.ipify.org | Amazon.com, Inc. | US | malicious |
184 | ПАКсЕыЦолИс.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
api.ipify.org |
| shared |
116.82.254.5.zen.spamhaus.org |
| unknown |
116.82.254.5.cbl.abuseat.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
184 | ПАКсЕыЦолИс.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
184 | ПАКсЕыЦолИс.exe | A Network Trojan was detected | ET TROJAN ABUSE.CH SSL Blacklist Malicious SSL certificate detected (Dridex/Trickbot CnC) |
184 | ПАКсЕыЦолИс.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
184 | ПАКсЕыЦолИс.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
184 | ПАКсЕыЦолИс.exe | A Network Trojan was detected | MALWARE [PTsecurity] Dyre/Trickbot/Dridex SSL connection |
2 ETPRO signatures available at the full report