| File name: | NotePad.exe |
| Full analysis: | https://app.any.run/tasks/8d6c97fd-e94a-478e-b855-586c163c1ad7 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 26, 2023, 17:50:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9B11511D9AD2F52E3693F0E1A25BD83D |
| SHA1: | 7533F73151362F24871AE31E6F8EFDCDFF084A01 |
| SHA256: | 18D1F10B68626C7D8F1D66FA7663D9F9B57C6FD73E9D771FC50C7F3F3350020F |
| SSDEEP: | 1536:oeWUIwxAUYeQsTTiXR7SXE0b0KV4FUvADvc++mWJ:oeWUIwxAUYeih7S00b0KrvccrJ |
MALICIOUS
ASYNCRAT has been detected (YARA)
- notepad.exe (PID: 2016)
Bypass execution policy to execute commands
- powershell.exe (PID: 956)
ASYNCRAT has been detected (SURICATA)
- notepad.exe (PID: 2016)
SUSPICIOUS
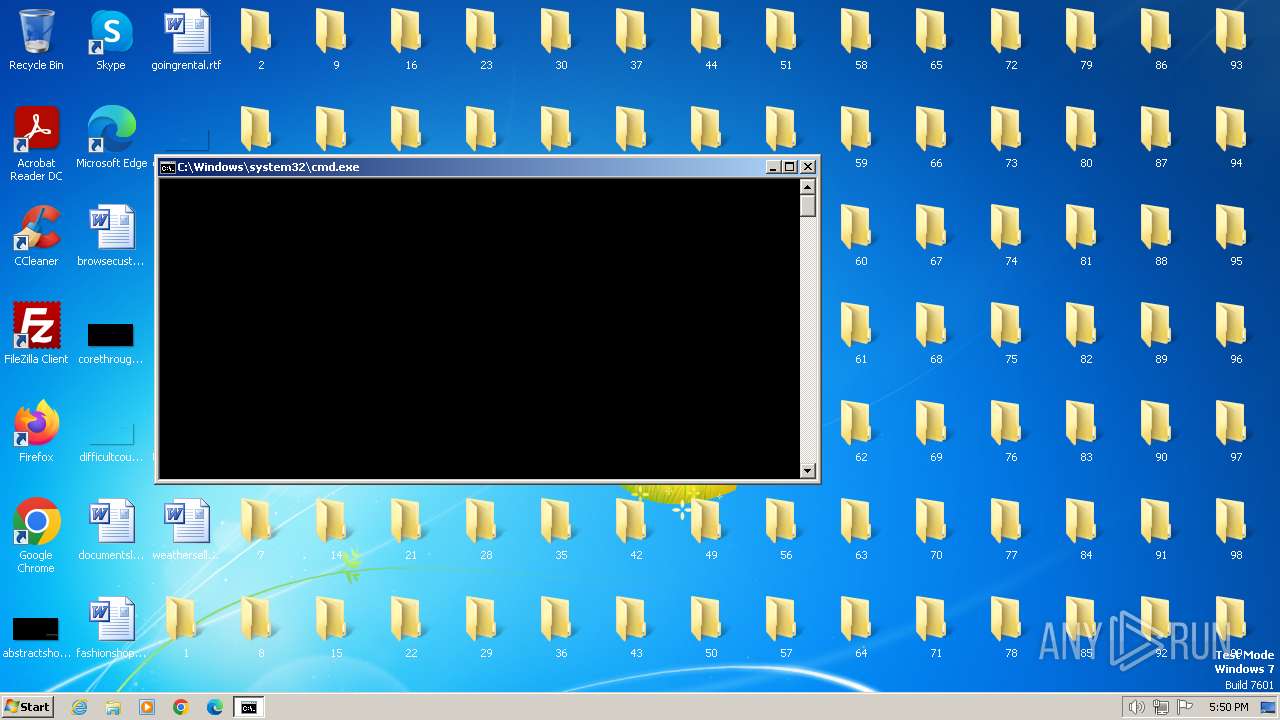
The process creates files with name similar to system file names
- NotePad.exe (PID: 128)
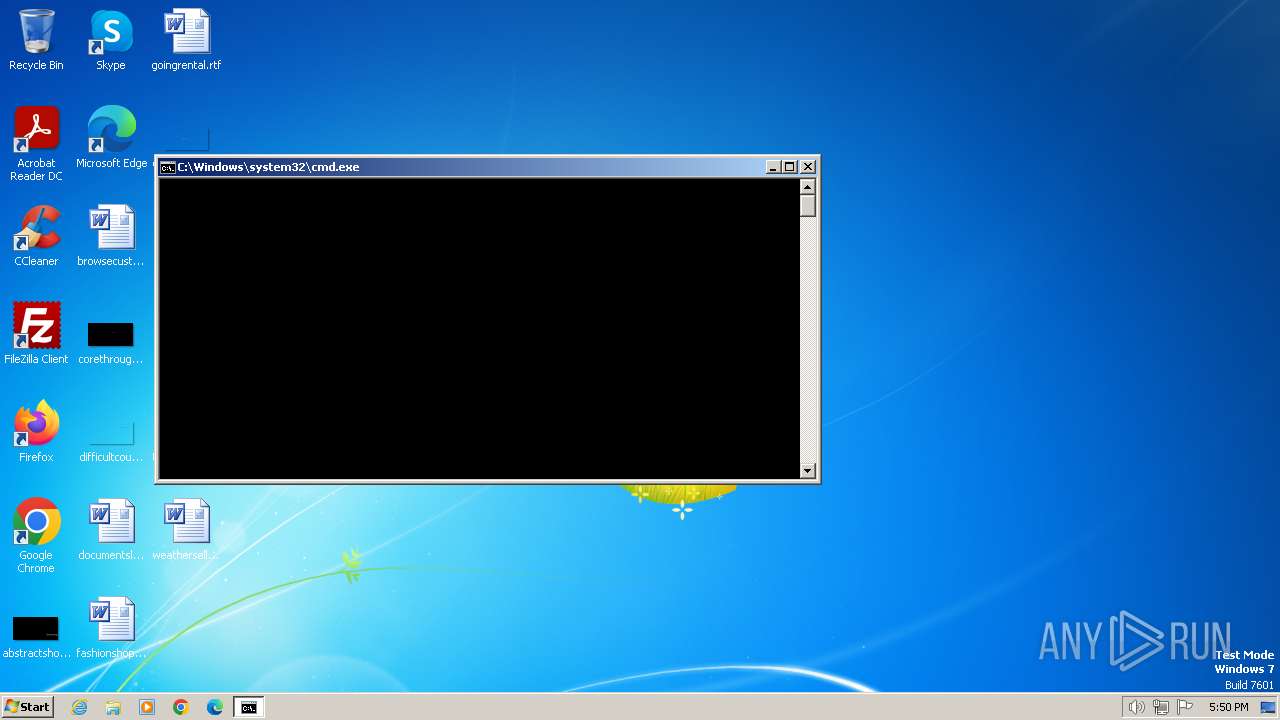
Starts CMD.EXE for commands execution
- NotePad.exe (PID: 128)
- notepad.exe (PID: 2016)
- powershell.exe (PID: 956)
Executing commands from a ".bat" file
- NotePad.exe (PID: 128)
- notepad.exe (PID: 2016)
- powershell.exe (PID: 956)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2624)
Reads settings of System Certificates
- notepad.exe (PID: 2016)
Reads the Internet Settings
- notepad.exe (PID: 2016)
- powershell.exe (PID: 956)
Connects to unusual port
- notepad.exe (PID: 2016)
Powershell scripting: start process
- cmd.exe (PID: 1264)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1264)
INFO
Drops the executable file immediately after the start
- NotePad.exe (PID: 128)
Checks supported languages
- NotePad.exe (PID: 128)
- notepad.exe (PID: 2016)
Process drops legitimate windows executable
- NotePad.exe (PID: 128)
Reads the computer name
- NotePad.exe (PID: 128)
- notepad.exe (PID: 2016)
Create files in a temporary directory
- NotePad.exe (PID: 128)
- notepad.exe (PID: 2016)
Reads the machine GUID from the registry
- NotePad.exe (PID: 128)
- notepad.exe (PID: 2016)
Creates files or folders in the user directory
- NotePad.exe (PID: 128)
The executable file from the user directory is run by the CMD process
- notepad.exe (PID: 2016)
Reads Environment values
- notepad.exe (PID: 2016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(2016) notepad.exe
BotnetDefault
Version0.5.7B
Options
AutoRuntrue
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMtrue
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAKoqom07VUgA3r0dl8/c+TANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwMjE5MjEyNTA3WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAM9LVAyiw27Nx3nznTRowgeiULU/Q385Jx6dU0pW+t8UZEk8xroPF8nmdVYbNgtZi/r2C4ky7fNx...
Server_SignatureEGbatw4FmOhuwsTXqfaExEYOqwJQwly4PVLJhct+oNpW82ys8ywujj0MOezXnjCbgp7ilCWPZfLUYeBk373o9I+FyDe/hYSsIc0ngCa1XhHrDdSzJDYXBKgDf99xIgE50qHR32w3jXUvvctQBS8qFTNfPWpB4xRtoSFafXJfQXUnxZ9gNlJi4+oeqCQonk15LoPlIT6BK266zSsYusxNAfZE5rAI0TLlNUGG/H0aqoMoUFNccIKJbqI4VtWukfgK3r3BIXTTEt6c9Ta30y/jmtixA0t1ydOMAC5RtMSVtg3G...
Keys
AES6d9cdb3c47456c1c80c4614f1075381db75ba0be99f449fbcb9552b13d7ee078
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Credentials
Protocolpastebin
URLhttps://pastebin.com/raw/QeEC9AnT
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:10 07:24:51+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 45568 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd0be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.19041.3636 |
| ProductVersionNumber: | 6.2.19041.3636 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Bloco de notas |
| FileVersion: | 6.2.19041.3636 |
| InternalName: | Notepad |
| LegalCopyright: | © Microsoft Corporation. Todos os direitos reservados. |
| LegalTrademarks: | - |
| OriginalFileName: | Notepad |
| ProductName: | Sistema operacional Microsoft® Windows® |
| ProductVersion: | 6.2.19041.3636 |
| AssemblyVersion: | 6.2.19041.3636 |
Total processes
48
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\AppData\Local\Temp\NotePad.exe" | C:\Users\admin\AppData\Local\Temp\NotePad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Bloco de notas Exit code: 0 Version: 6.2.19041.3636 Modules
| |||||||||||||||
| 848 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\brtsjq.bat" " | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | powershell –ExecutionPolicy Bypass Start-Process -FilePath '"C:\Users\admin\AppData\Local\Temp\brtsjq.bat"' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1264 | "C:\Windows\System32\cmd.exe" /c start /b powershell –ExecutionPolicy Bypass Start-Process -FilePath '"C:\Users\admin\AppData\Local\Temp\brtsjq.bat"' & exit | C:\Windows\System32\cmd.exe | — | notepad.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1924 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2016 | "C:\Users\admin\AppData\Roaming\notepad.exe" | C:\Users\admin\AppData\Roaming\notepad.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Bloco de notas Exit code: 0 Version: 6.2.19041.3636 Modules
AsyncRat(PID) Process(2016) notepad.exe BotnetDefault Version0.5.7B Options AutoRuntrue MutexAsyncMutex_6SI8OkPnk InstallFolder%AppData% BSoDfalse AntiVMtrue Certificates Cert1MIIE8jCCAtqgAwIBAgIQAKoqom07VUgA3r0dl8/c+TANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwMjE5MjEyNTA3WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAM9LVAyiw27Nx3nznTRowgeiULU/Q385Jx6dU0pW+t8UZEk8xroPF8nmdVYbNgtZi/r2C4ky7fNx... Server_SignatureEGbatw4FmOhuwsTXqfaExEYOqwJQwly4PVLJhct+oNpW82ys8ywujj0MOezXnjCbgp7ilCWPZfLUYeBk373o9I+FyDe/hYSsIc0ngCa1XhHrDdSzJDYXBKgDf99xIgE50qHR32w3jXUvvctQBS8qFTNfPWpB4xRtoSFafXJfQXUnxZ9gNlJi4+oeqCQonk15LoPlIT6BK266zSsYusxNAfZE5rAI0TLlNUGG/H0aqoMoUFNccIKJbqI4VtWukfgK3r3BIXTTEt6c9Ta30y/jmtixA0t1ydOMAC5RtMSVtg3G... Keys AES6d9cdb3c47456c1c80c4614f1075381db75ba0be99f449fbcb9552b13d7ee078 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 Credentials Protocolpastebin URLhttps://pastebin.com/raw/QeEC9AnT | |||||||||||||||
| 2084 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmpD3A.tmp.bat"" | C:\Windows\System32\cmd.exe | — | NotePad.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2416 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp39D5.tmp.bat"" | C:\Windows\System32\cmd.exe | — | notepad.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
6 194
Read events
6 148
Write events
44
Delete events
2
Modification events
| (PID) Process: | (128) NotePad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2016) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2016) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2016) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2016) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2016) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
7
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2016 | notepad.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:E78854AE25AE8BBCFF1A42AA51AE5846 | SHA256:EDE6E0217C72DFD074BA7DE0D54FE84C4DA863878C98C4371013E78FB7C19313 | |||
| 2016 | notepad.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Local\Temp\iwmcfz4v.f4h.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2016 | notepad.exe | C:\Users\admin\AppData\Local\Temp\Tar4C38.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 128 | NotePad.exe | C:\Users\admin\AppData\Local\Temp\tmpD3A.tmp.bat | text | |
MD5:65CBC548A5F69692AC95BB45D0725FAA | SHA256:1F06B9004E2C7871A65CDB08F85BA81103816282F105C15AF80D23E6C5D75CC4 | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Local\Temp\nbs4dhfq.o15.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2016 | notepad.exe | C:\Users\admin\AppData\Local\Temp\tmp39D5.tmp.bat | text | |
MD5:0B3E2AA09B93B921982AC511E7645C5A | SHA256:A5468D53B42167F8611B746AC08D9A229495FEE2CC2E7A34D462120F654F7929 | |||
| 2016 | notepad.exe | C:\Users\admin\AppData\Local\Temp\Cab4C37.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2016 | notepad.exe | C:\Users\admin\AppData\Local\Temp\brtsjq.bat | text | |
MD5:93BA68D3E97B7F56093A87132E7393AC | SHA256:2D11E2B4C8CEE1EF0F848284FD9E850DDC07307A1017F598A6BE54C66D1F9EBD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2016 | notepad.exe | GET | 200 | 2.16.100.169:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7c5cced82a00ccfd | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2016 | notepad.exe | 104.20.68.143:443 | pastebin.com | CLOUDFLARENET | — | unknown |
2016 | notepad.exe | 3.142.81.166:11917 | 8.tcp.ngrok.io | AMAZON-02 | US | unknown |
2016 | notepad.exe | 2.16.100.169:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| shared |
8.tcp.ngrok.io |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
1080 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
2016 | notepad.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2016 | notepad.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
2016 | notepad.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
2016 | notepad.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |