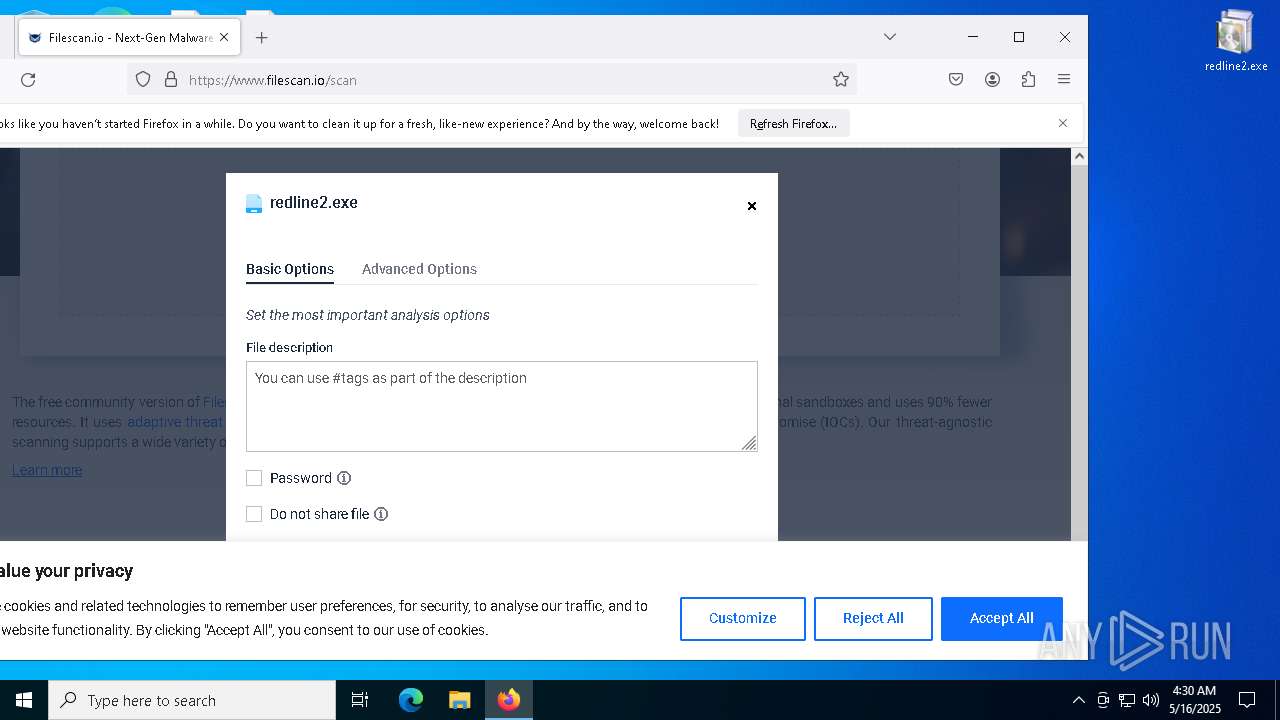
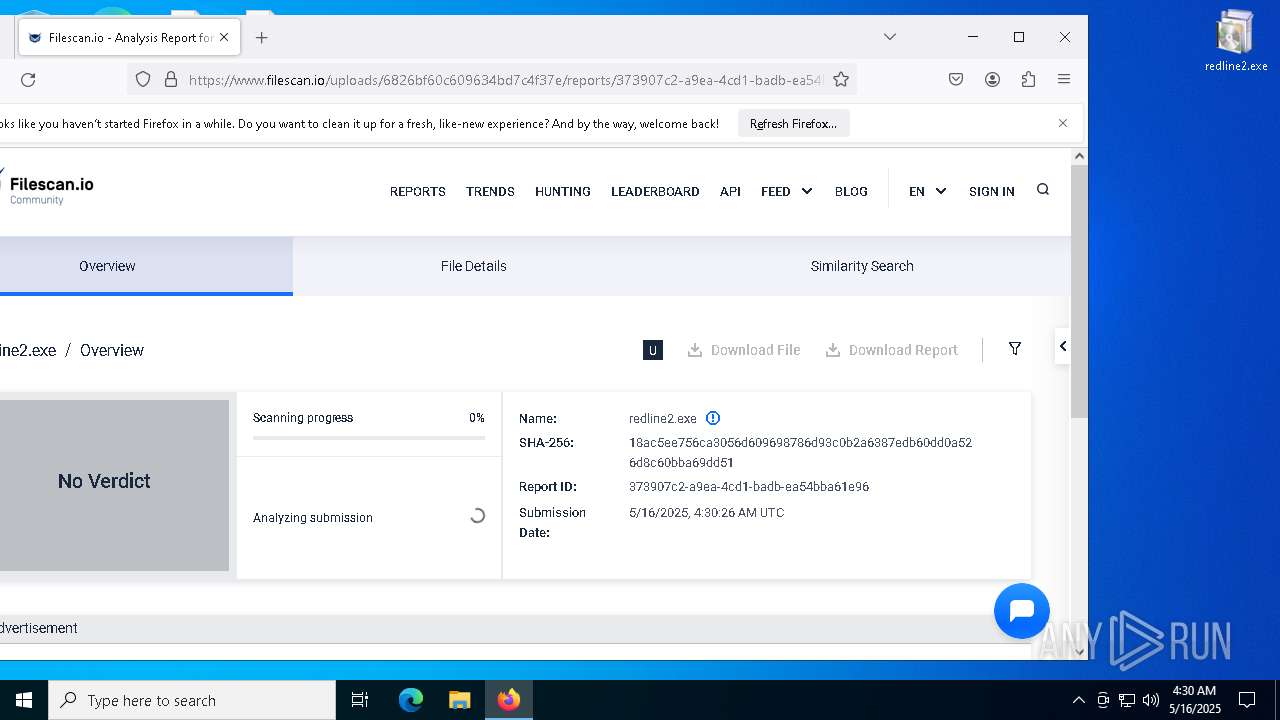
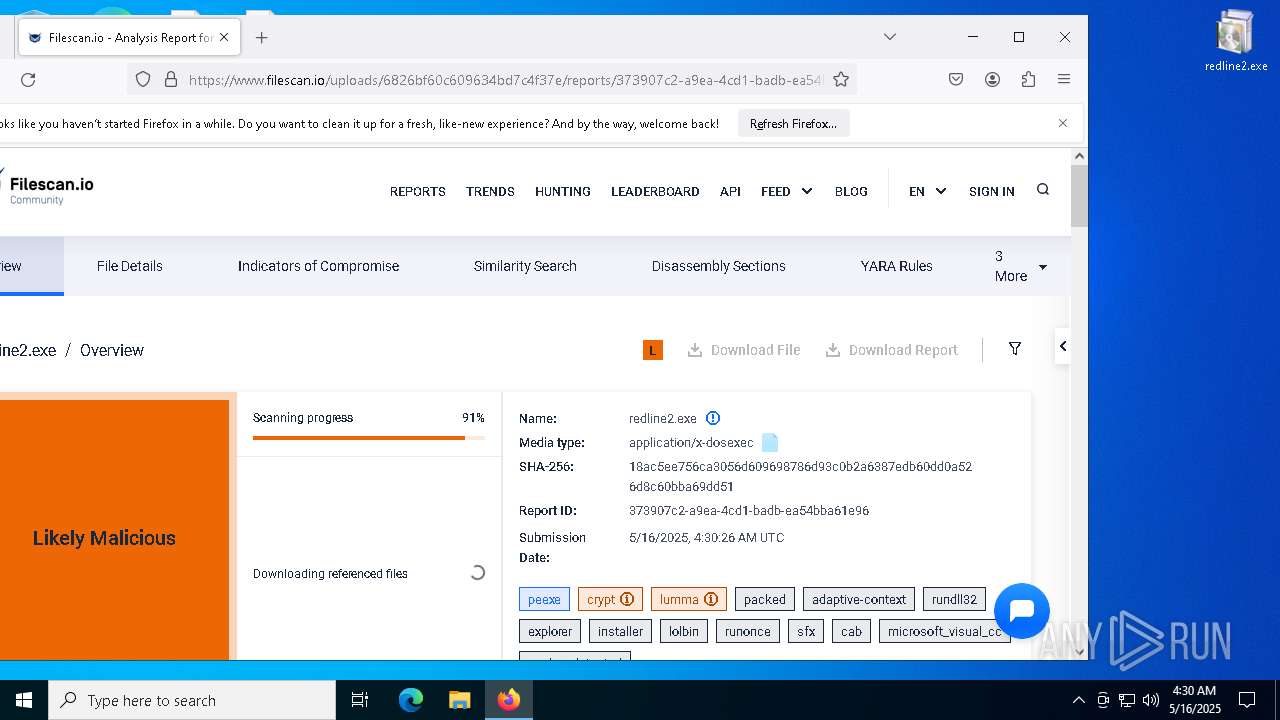
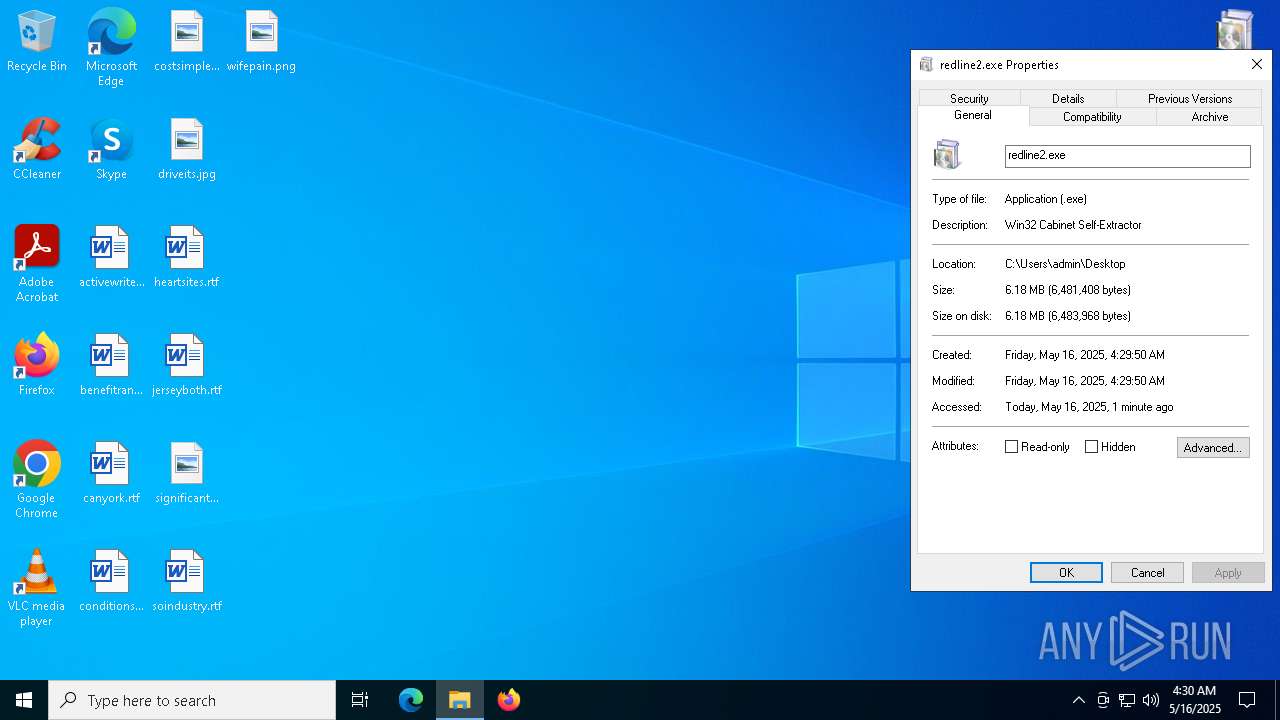
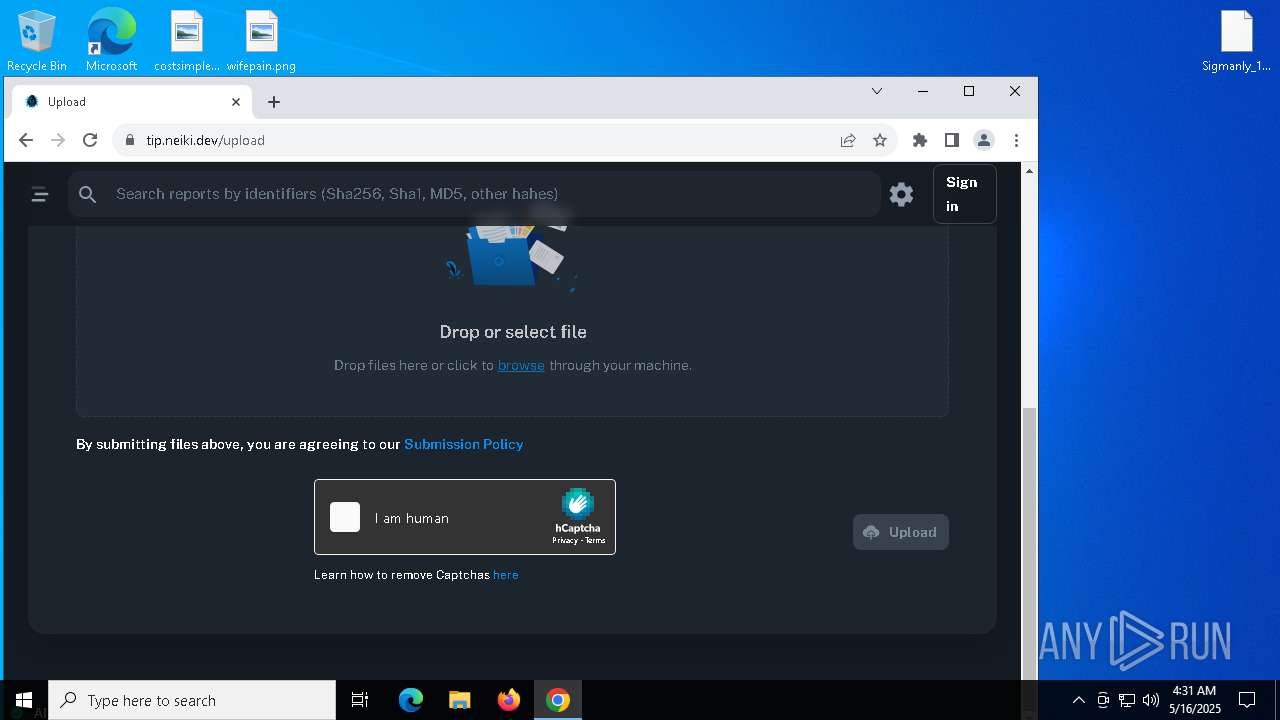
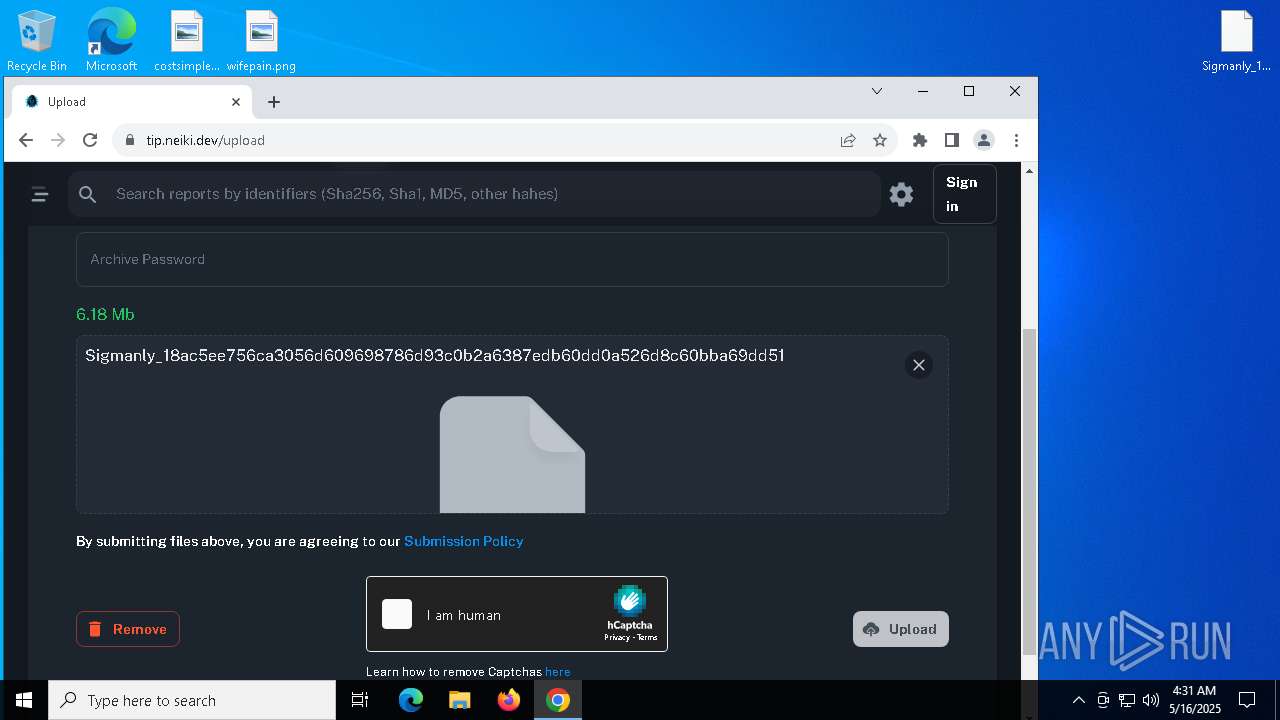
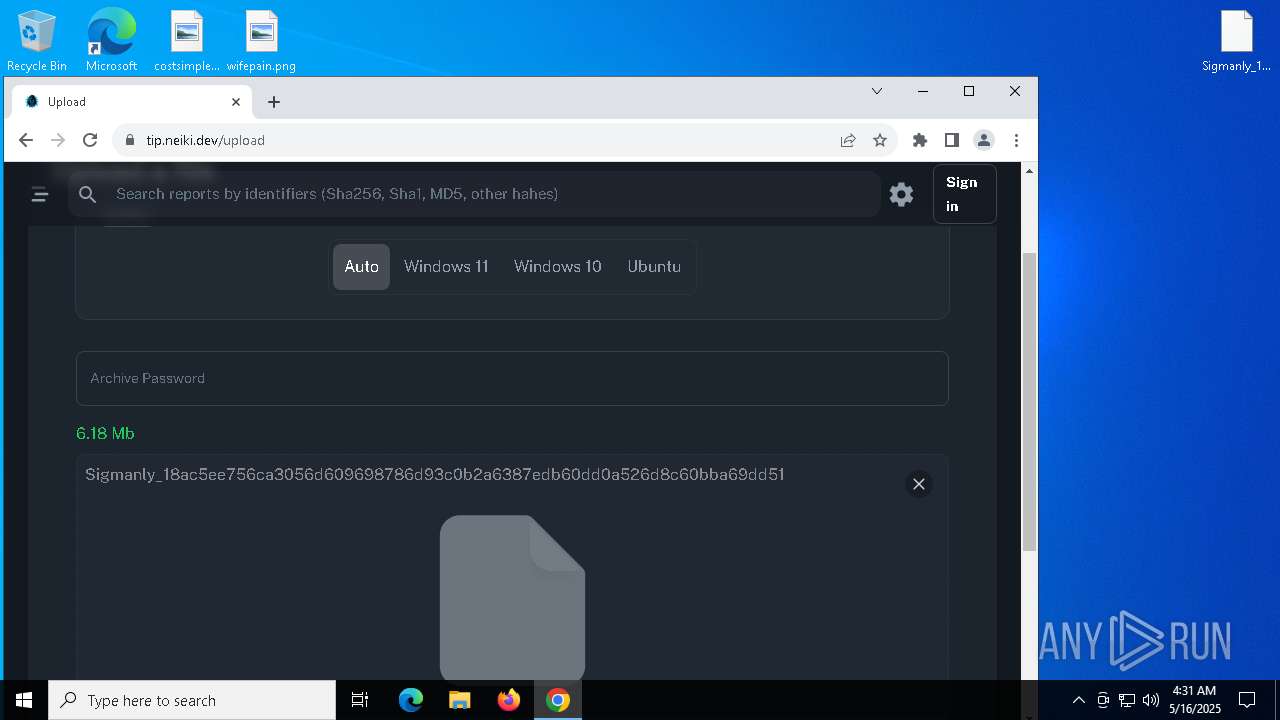
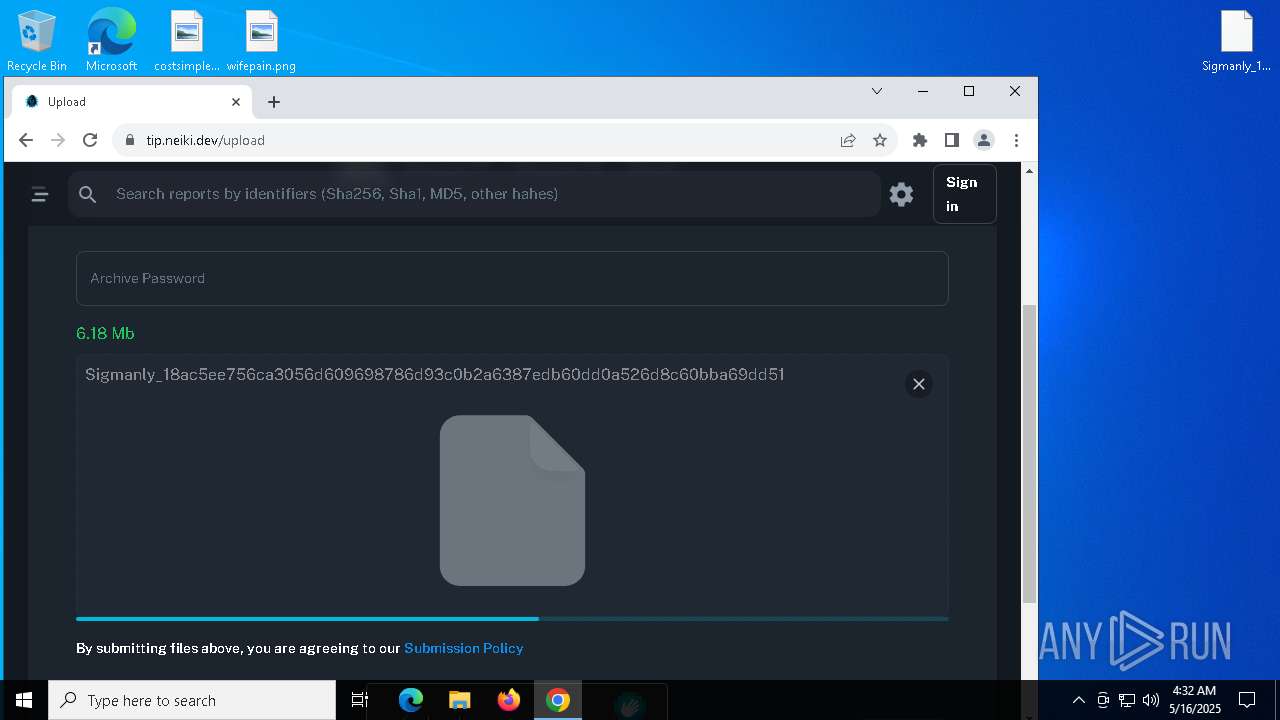
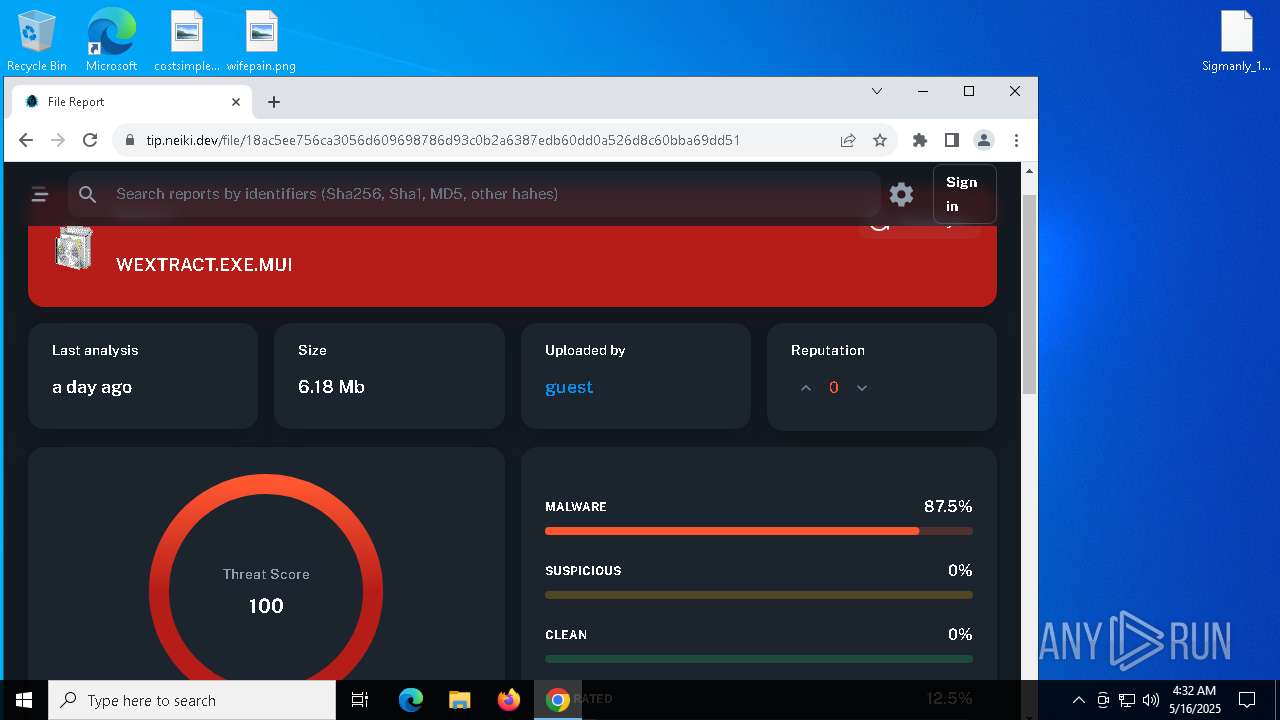
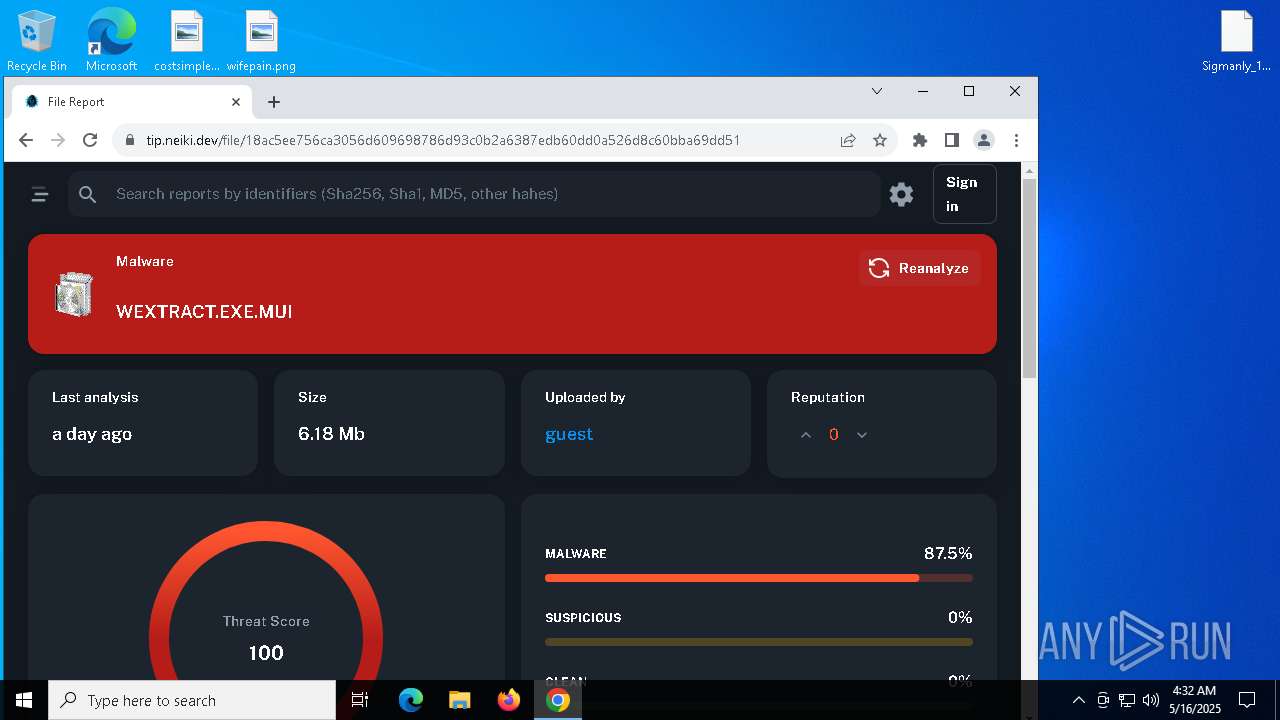
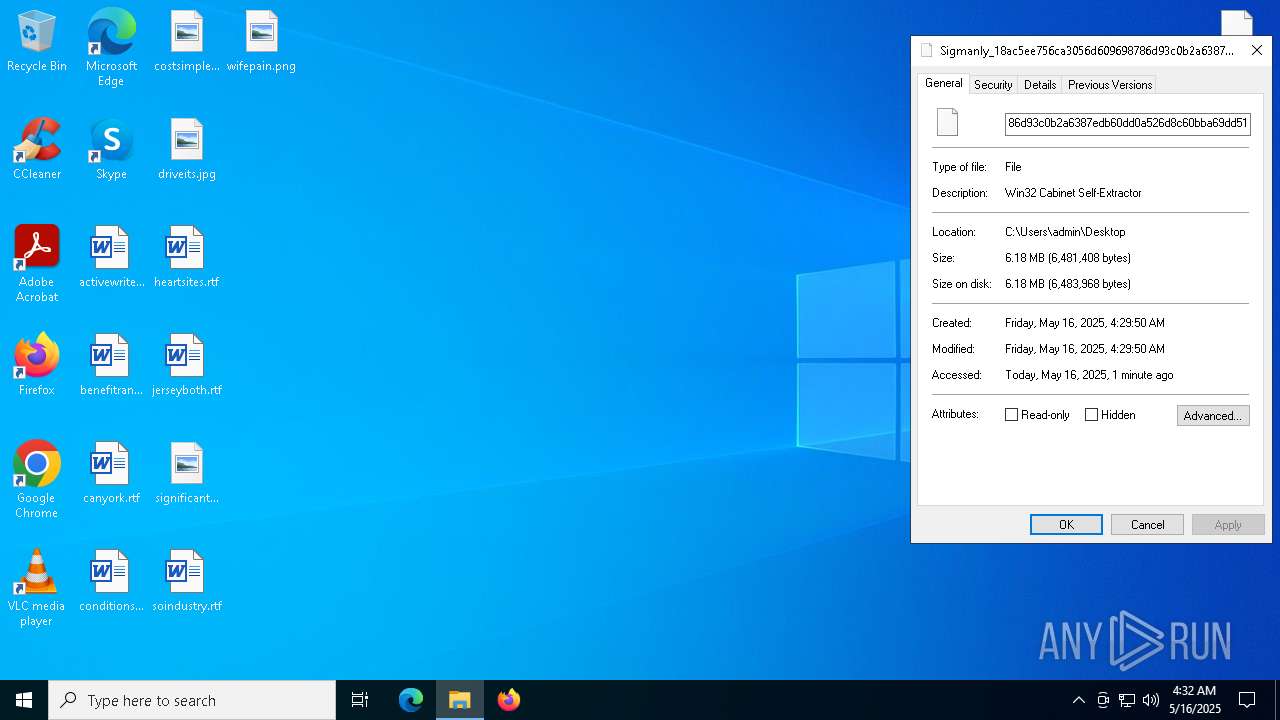
| File name: | redline2.exe |
| Full analysis: | https://app.any.run/tasks/64c6a000-dd93-4cfa-8720-27d35594c6c9 |
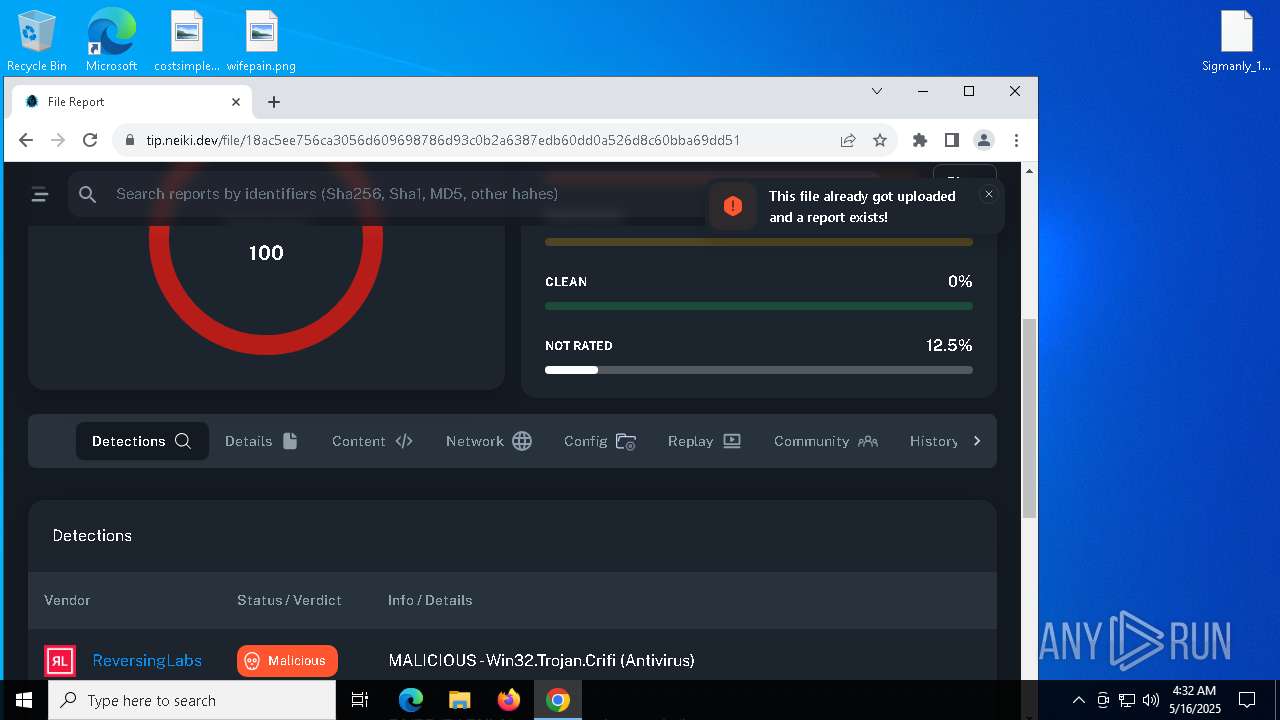
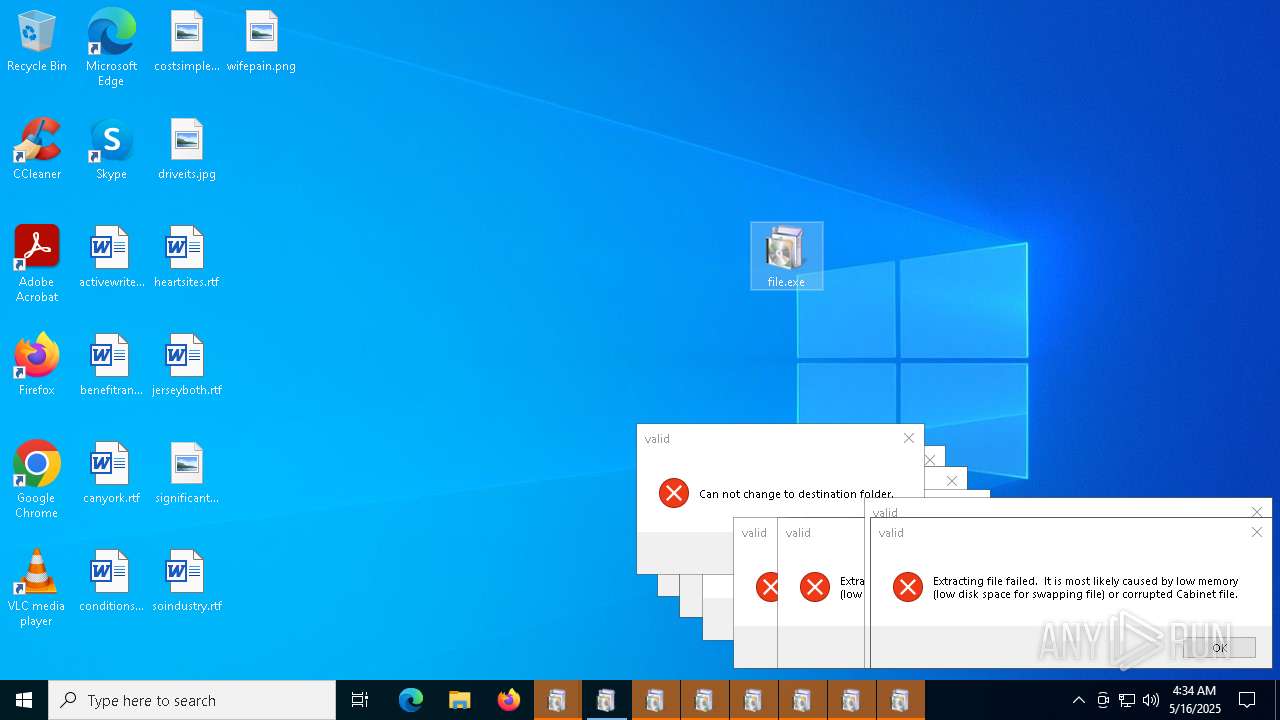
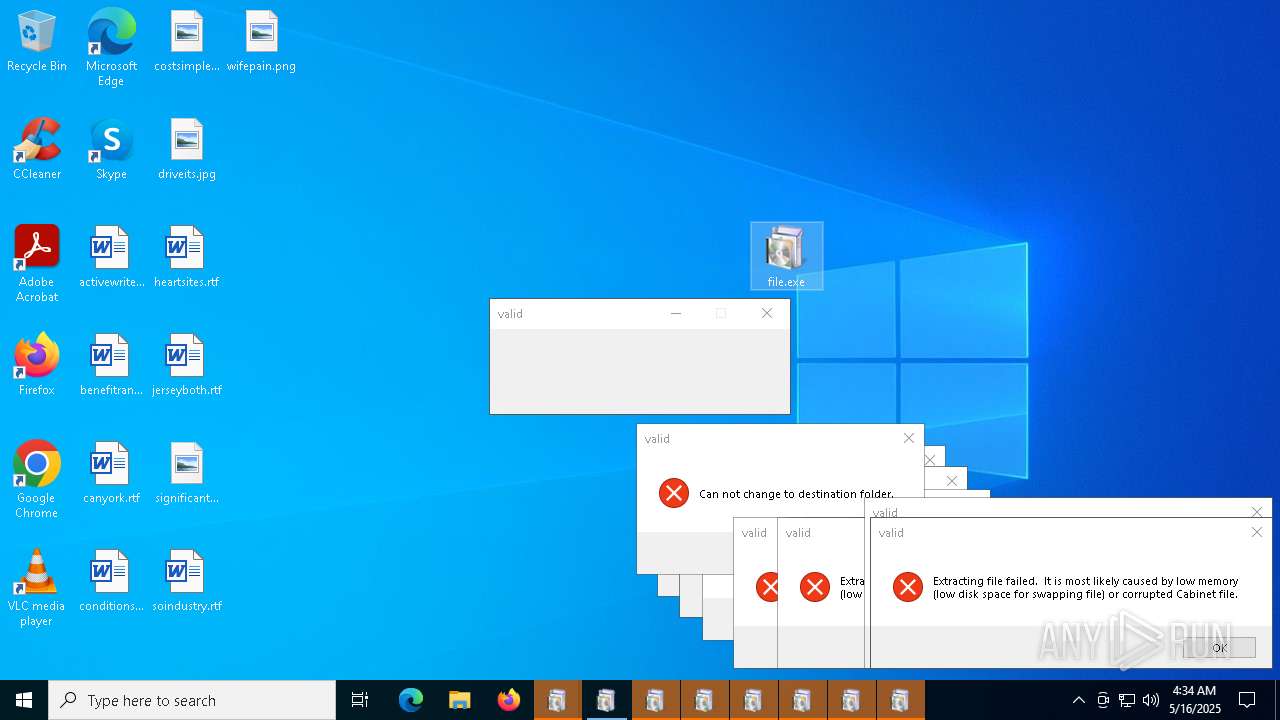
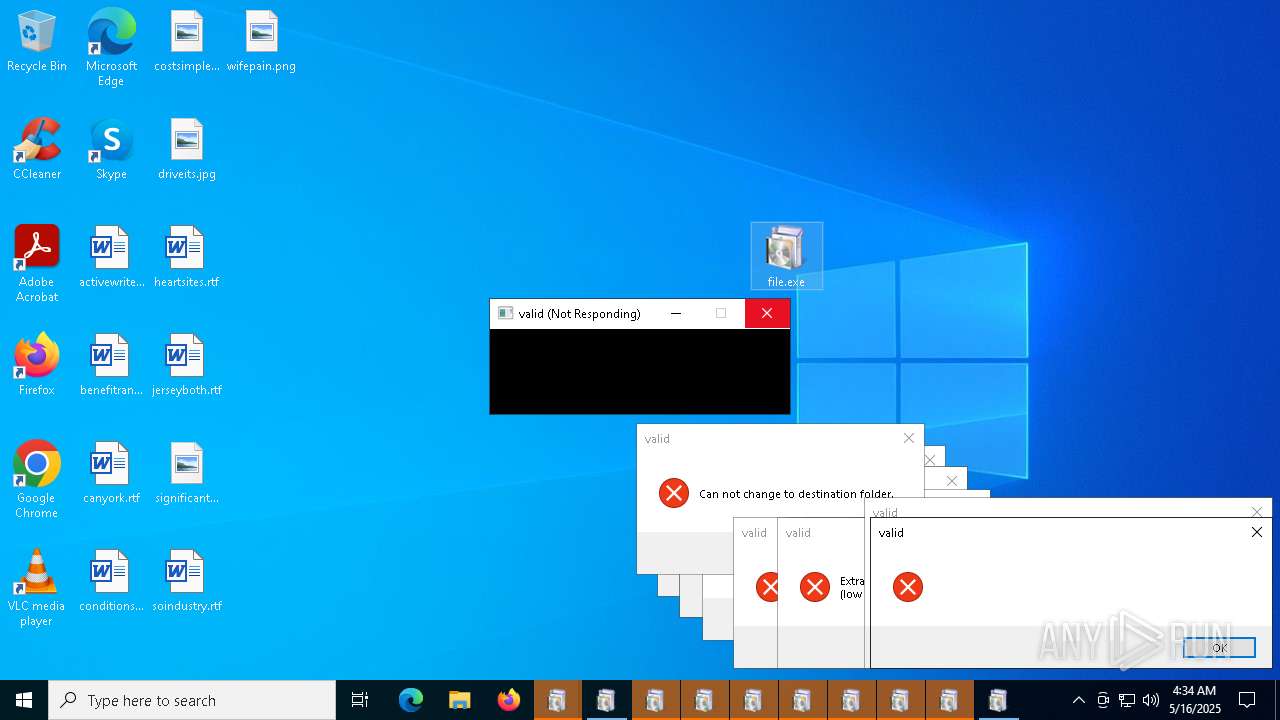
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 16, 2025, 04:29:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 8F8BD202433540AA40F3D7B623645D78 |
| SHA1: | 3DDD36F82DFE14CF66EE5CCBDC038B469FB8CDFC |
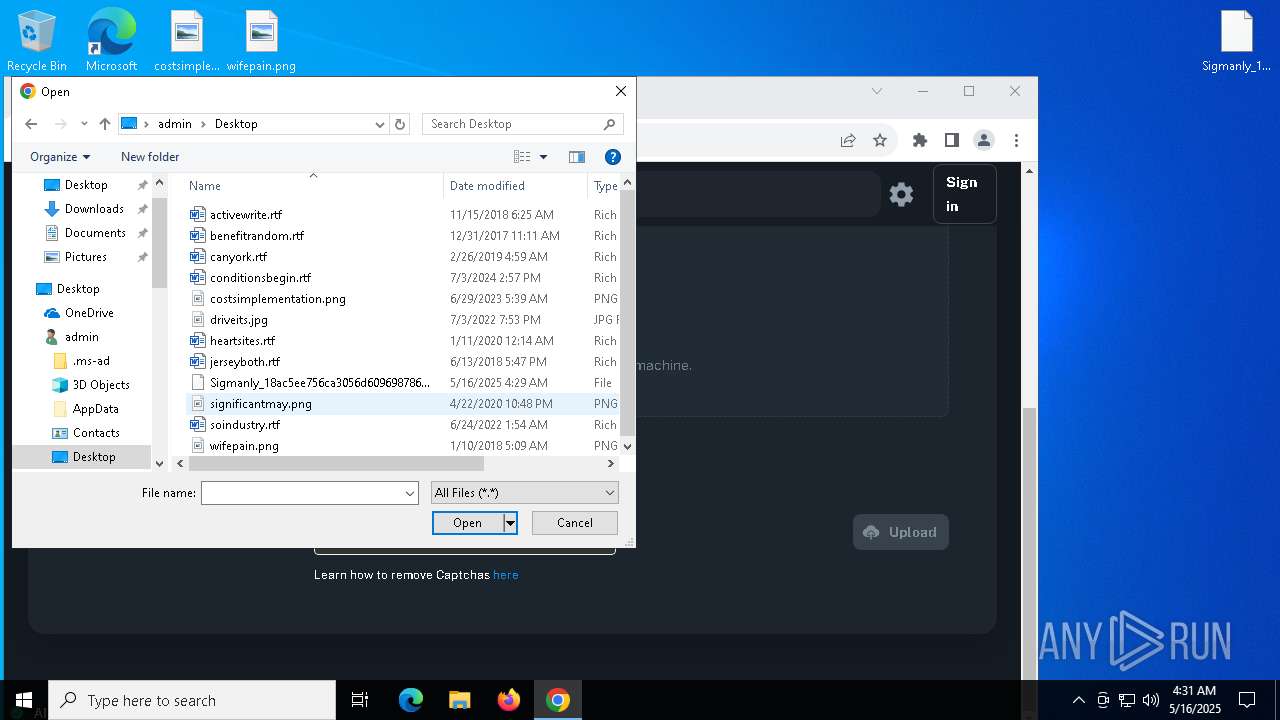
| SHA256: | 18AC5EE756CA3056D609698786D93C0B2A6387EDB60DD0A526D8C60BBA69DD51 |
| SSDEEP: | 98304:sn24Y5kC969FWbbl950ebBSTDBtWVZv+EJQPZ2k68dZnnzRlBVJzKEP1xZp+Z9QI:rRb9JU2i0Vss0q9 |
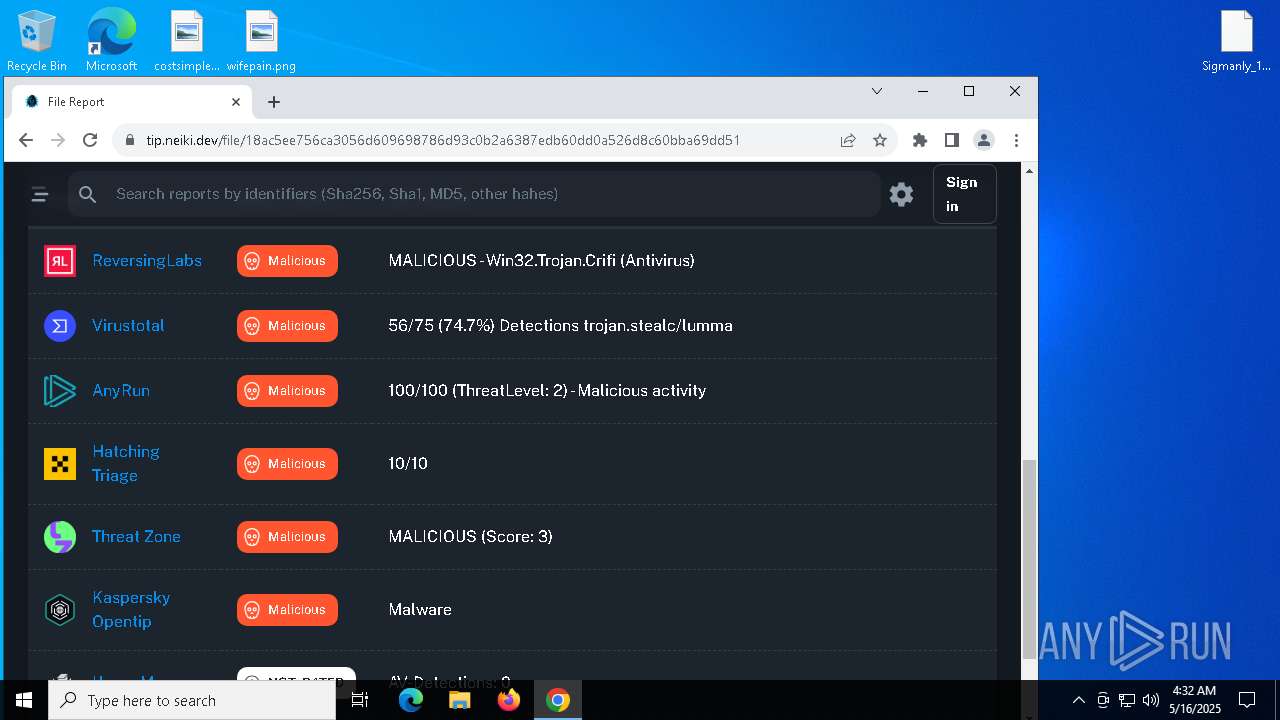
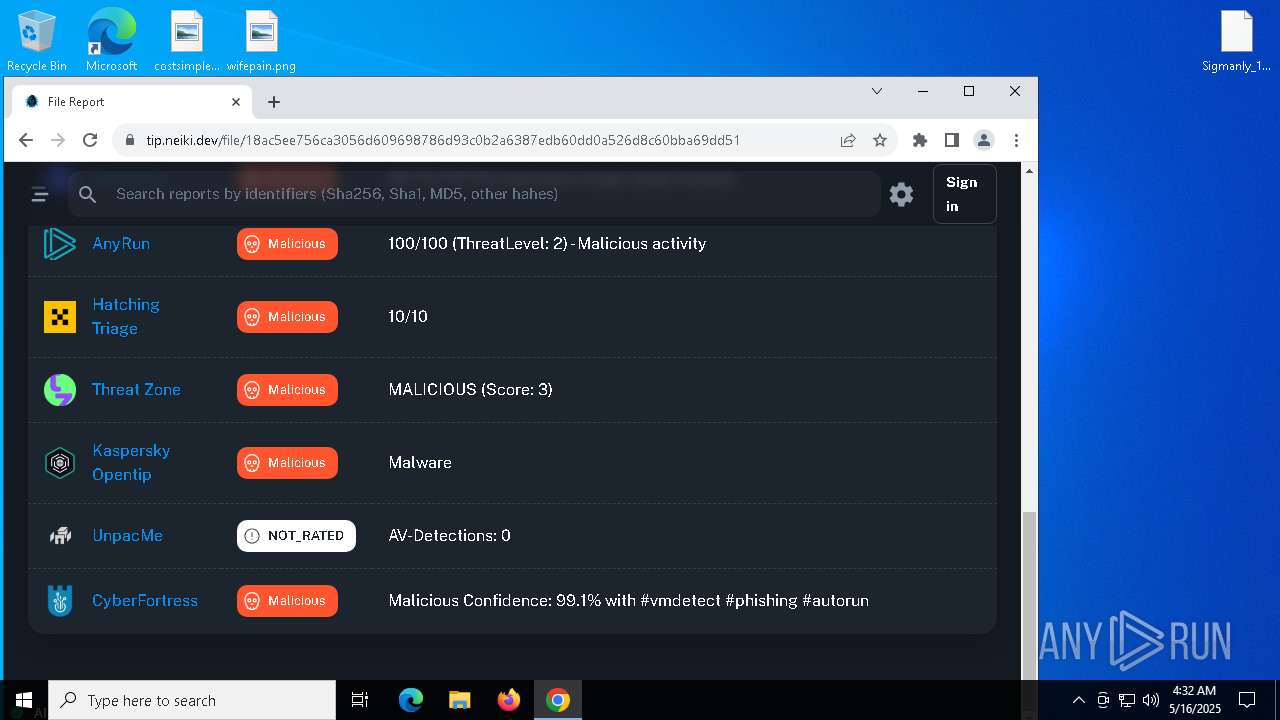
MALICIOUS
STEALC has been found (auto)
- redline2.exe (PID: 4628)
- file.exe (PID: 6404)
- file.exe (PID: 7932)
- file.exe (PID: 4996)
- file.exe (PID: 5544)
- file.exe (PID: 2284)
- file.exe (PID: 6892)
- file.exe (PID: 5324)
- file.exe (PID: 3300)
- file.exe (PID: 2104)
- file.exe (PID: 7480)
- file.exe (PID: 2340)
- file.exe (PID: 4692)
- file.exe (PID: 7520)
- file.exe (PID: 5024)
- file.exe (PID: 7348)
- file.exe (PID: 4012)
- file.exe (PID: 2108)
- file.exe (PID: 7496)
- file.exe (PID: 7936)
- file.exe (PID: 3768)
- file.exe (PID: 4220)
- file.exe (PID: 8088)
- file.exe (PID: 232)
- file.exe (PID: 7884)
- file.exe (PID: 5548)
- file.exe (PID: 5744)
- file.exe (PID: 4424)
- file.exe (PID: 7540)
- file.exe (PID: 6940)
- file.exe (PID: 8312)
- file.exe (PID: 7284)
- file.exe (PID: 6572)
- file.exe (PID: 8328)
- file.exe (PID: 8320)
- file.exe (PID: 8288)
- file.exe (PID: 3620)
- file.exe (PID: 8304)
- file.exe (PID: 7588)
- file.exe (PID: 6300)
- file.exe (PID: 9176)
- file.exe (PID: 7940)
- file.exe (PID: 7720)
- file.exe (PID: 6256)
- file.exe (PID: 7988)
- file.exe (PID: 6044)
- file.exe (PID: 9244)
- file.exe (PID: 11500)
- file.exe (PID: 6372)
- file.exe (PID: 10660)
- file.exe (PID: 11080)
- file.exe (PID: 11116)
- file.exe (PID: 616)
- file.exe (PID: 10544)
- file.exe (PID: 10536)
- file.exe (PID: 10272)
- file.exe (PID: 10652)
- file.exe (PID: 7964)
- file.exe (PID: 11100)
- file.exe (PID: 8724)
- file.exe (PID: 8944)
- file.exe (PID: 968)
- file.exe (PID: 7364)
- file.exe (PID: 11616)
- file.exe (PID: 11604)
- file.exe (PID: 12208)
- file.exe (PID: 12184)
- file.exe (PID: 11372)
- file.exe (PID: 11528)
- file.exe (PID: 11580)
- file.exe (PID: 10852)
- file.exe (PID: 12120)
- file.exe (PID: 11520)
- file.exe (PID: 12100)
- file.exe (PID: 12252)
- file.exe (PID: 12036)
- file.exe (PID: 12152)
- file.exe (PID: 12172)
- file.exe (PID: 12244)
- file.exe (PID: 11628)
- file.exe (PID: 12108)
- file.exe (PID: 12280)
- file.exe (PID: 12052)
- file.exe (PID: 8708)
- file.exe (PID: 12084)
- file.exe (PID: 12500)
- file.exe (PID: 12512)
- file.exe (PID: 12524)
- file.exe (PID: 12856)
- file.exe (PID: 7316)
- file.exe (PID: 12652)
- file.exe (PID: 9140)
- file.exe (PID: 13864)
- file.exe (PID: 12832)
- file.exe (PID: 12608)
- file.exe (PID: 9008)
- file.exe (PID: 13332)
- file.exe (PID: 13028)
- file.exe (PID: 12820)
- file.exe (PID: 12900)
- file.exe (PID: 13800)
- file.exe (PID: 13948)
- file.exe (PID: 14312)
- file.exe (PID: 12364)
- file.exe (PID: 13200)
- file.exe (PID: 12668)
- file.exe (PID: 13680)
- file.exe (PID: 14028)
- file.exe (PID: 9440)
- file.exe (PID: 13740)
- file.exe (PID: 13504)
- file.exe (PID: 14292)
- file.exe (PID: 14832)
- file.exe (PID: 13160)
- file.exe (PID: 13760)
- file.exe (PID: 13576)
- file.exe (PID: 14776)
- file.exe (PID: 8800)
- file.exe (PID: 9096)
- file.exe (PID: 14788)
- file.exe (PID: 13076)
- file.exe (PID: 5044)
- file.exe (PID: 13612)
- file.exe (PID: 13540)
- file.exe (PID: 14304)
- file.exe (PID: 14416)
- file.exe (PID: 9528)
- file.exe (PID: 9372)
- file.exe (PID: 14048)
- file.exe (PID: 11460)
- file.exe (PID: 14180)
- file.exe (PID: 13072)
- file.exe (PID: 9068)
- file.exe (PID: 10632)
- file.exe (PID: 13056)
- file.exe (PID: 9516)
- file.exe (PID: 13664)
- file.exe (PID: 13976)
- file.exe (PID: 14324)
- file.exe (PID: 11884)
- file.exe (PID: 14008)
- file.exe (PID: 13732)
- file.exe (PID: 10916)
- file.exe (PID: 13216)
- file.exe (PID: 13044)
- file.exe (PID: 13548)
- file.exe (PID: 12788)
- file.exe (PID: 8252)
- file.exe (PID: 13772)
- file.exe (PID: 13340)
- file.exe (PID: 9844)
- file.exe (PID: 11560)
- file.exe (PID: 9804)
- file.exe (PID: 14700)
- file.exe (PID: 15144)
- file.exe (PID: 10940)
- file.exe (PID: 14144)
- file.exe (PID: 14152)
- file.exe (PID: 13876)
- file.exe (PID: 8856)
- file.exe (PID: 15116)
- file.exe (PID: 13900)
- file.exe (PID: 9736)
- file.exe (PID: 12980)
- file.exe (PID: 8912)
- file.exe (PID: 13788)
- file.exe (PID: 10904)
- file.exe (PID: 13884)
- file.exe (PID: 14168)
- file.exe (PID: 14272)
- file.exe (PID: 15636)
- file.exe (PID: 5064)
- file.exe (PID: 2596)
- file.exe (PID: 15344)
- file.exe (PID: 18468)
- file.exe (PID: 16904)
- file.exe (PID: 13152)
- file.exe (PID: 9872)
- file.exe (PID: 8096)
- file.exe (PID: 13356)
- file.exe (PID: 9724)
- file.exe (PID: 13252)
- file.exe (PID: 3396)
- file.exe (PID: 18180)
- file.exe (PID: 14280)
- file.exe (PID: 13000)
- file.exe (PID: 10580)
- file.exe (PID: 6112)
- file.exe (PID: 7420)
- file.exe (PID: 13396)
- file.exe (PID: 15608)
- file.exe (PID: 9536)
- file.exe (PID: 13892)
- file.exe (PID: 18828)
- file.exe (PID: 14896)
- file.exe (PID: 9420)
- file.exe (PID: 7412)
- file.exe (PID: 12964)
- file.exe (PID: 13920)
- file.exe (PID: 16456)
- file.exe (PID: 16564)
- file.exe (PID: 14768)
- file.exe (PID: 12372)
- file.exe (PID: 8676)
- file.exe (PID: 14976)
- file.exe (PID: 13176)
- file.exe (PID: 9696)
- file.exe (PID: 14992)
- file.exe (PID: 15624)
- file.exe (PID: 9540)
- file.exe (PID: 17452)
- file.exe (PID: 14440)
- file.exe (PID: 13184)
- file.exe (PID: 18752)
- file.exe (PID: 18184)
- file.exe (PID: 15356)
- file.exe (PID: 12536)
- file.exe (PID: 8892)
- file.exe (PID: 17036)
- file.exe (PID: 10956)
- file.exe (PID: 11624)
- file.exe (PID: 12852)
- file.exe (PID: 9364)
- file.exe (PID: 14256)
- file.exe (PID: 13128)
- file.exe (PID: 9276)
- file.exe (PID: 13376)
- file.exe (PID: 18140)
- file.exe (PID: 8576)
- file.exe (PID: 15012)
- file.exe (PID: 10808)
- file.exe (PID: 10136)
- file.exe (PID: 18356)
- file.exe (PID: 9868)
- file.exe (PID: 18088)
- file.exe (PID: 16572)
- file.exe (PID: 10848)
- file.exe (PID: 13512)
- file.exe (PID: 10872)
- file.exe (PID: 1672)
- file.exe (PID: 11940)
- file.exe (PID: 10648)
- file.exe (PID: 15592)
- file.exe (PID: 13692)
- file.exe (PID: 14952)
- file.exe (PID: 14852)
- file.exe (PID: 13444)
- file.exe (PID: 15220)
- file.exe (PID: 10196)
- file.exe (PID: 9192)
- file.exe (PID: 11716)
- file.exe (PID: 14912)
- file.exe (PID: 13460)
- file.exe (PID: 10072)
- file.exe (PID: 17476)
- file.exe (PID: 10556)
- file.exe (PID: 10528)
- file.exe (PID: 10876)
- file.exe (PID: 15928)
- file.exe (PID: 18804)
- file.exe (PID: 18480)
- file.exe (PID: 15276)
- file.exe (PID: 14464)
- file.exe (PID: 10800)
- file.exe (PID: 17484)
- file.exe (PID: 18532)
- file.exe (PID: 18720)
- file.exe (PID: 17968)
- file.exe (PID: 7396)
- file.exe (PID: 18732)
- file.exe (PID: 18668)
LUMMA has been found (auto)
- g7h64.exe (PID: 3884)
- g7h64.exe (PID: 2692)
- g7h64.exe (PID: 6300)
- g7h64.exe (PID: 7568)
- g7h64.exe (PID: 3992)
- g7h64.exe (PID: 8188)
- g7h64.exe (PID: 8484)
- g7h64.exe (PID: 8492)
- g7h64.exe (PID: 8580)
- g7h64.exe (PID: 8616)
- g7h64.exe (PID: 9160)
- g7h64.exe (PID: 8604)
- g7h64.exe (PID: 8544)
- g7h64.exe (PID: 6980)
- g7h64.exe (PID: 9204)
- g7h64.exe (PID: 7716)
- g7h64.exe (PID: 9212)
- g7h64.exe (PID: 6740)
- g7h64.exe (PID: 8224)
- g7h64.exe (PID: 8212)
- g7h64.exe (PID: 8244)
- g7h64.exe (PID: 3032)
- g7h64.exe (PID: 8076)
- g7h64.exe (PID: 976)
- g7h64.exe (PID: 8204)
- g7h64.exe (PID: 8876)
- g7h64.exe (PID: 8900)
- g7h64.exe (PID: 8524)
- g7h64.exe (PID: 1056)
- g7h64.exe (PID: 668)
- g7h64.exe (PID: 7156)
- g7h64.exe (PID: 1240)
- g7h64.exe (PID: 7924)
- g7h64.exe (PID: 5720)
- g7h64.exe (PID: 10180)
- g7h64.exe (PID: 10168)
- g7h64.exe (PID: 5384)
- g7h64.exe (PID: 11408)
- g7h64.exe (PID: 11464)
- g7h64.exe (PID: 11864)
- g7h64.exe (PID: 11856)
- g7h64.exe (PID: 11472)
- g7h64.exe (PID: 13720)
- g7h64.exe (PID: 18232)
- g7h64.exe (PID: 13604)
- g7h64.exe (PID: 10696)
- g7h64.exe (PID: 12532)
- g7h64.exe (PID: 14928)
- g7h64.exe (PID: 12864)
- g7h64.exe (PID: 8828)
- g7h64.exe (PID: 14816)
- g7h64.exe (PID: 13384)
- g7h64.exe (PID: 17240)
- g7h64.exe (PID: 17160)
- g7h64.exe (PID: 7484)
- g7h64.exe (PID: 14124)
- g7h64.exe (PID: 9484)
- g7h64.exe (PID: 16576)
- g7h64.exe (PID: 17672)
- g7h64.exe (PID: 6168)
- g7h64.exe (PID: 16712)
- g7h64.exe (PID: 15788)
- g7h64.exe (PID: 7480)
- g7h64.exe (PID: 8640)
- g7h64.exe (PID: 9560)
- g7h64.exe (PID: 16704)
- g7h64.exe (PID: 16620)
- g7h64.exe (PID: 13096)
- g7h64.exe (PID: 10592)
- g7h64.exe (PID: 17280)
- g7h64.exe (PID: 13140)
- g7h64.exe (PID: 12440)
- g7h64.exe (PID: 16316)
- g7h64.exe (PID: 12808)
- g7h64.exe (PID: 17636)
- g7h64.exe (PID: 19420)
- g7h64.exe (PID: 13036)
- g7h64.exe (PID: 15240)
- g7h64.exe (PID: 18980)
- g7h64.exe (PID: 5352)
- g7h64.exe (PID: 13368)
- g7h64.exe (PID: 16556)
- g7h64.exe (PID: 16968)
- g7h64.exe (PID: 5212)
- g7h64.exe (PID: 8636)
- g7h64.exe (PID: 18936)
- g7h64.exe (PID: 18756)
- g7h64.exe (PID: 12520)
- g7h64.exe (PID: 9000)
- g7h64.exe (PID: 14224)
- g7h64.exe (PID: 14240)
- g7h64.exe (PID: 9756)
- g7h64.exe (PID: 9744)
- g7h64.exe (PID: 9964)
- g7h64.exe (PID: 10688)
- g7h64.exe (PID: 13492)
- g7h64.exe (PID: 17816)
- g7h64.exe (PID: 9952)
- g7h64.exe (PID: 9896)
- g7h64.exe (PID: 812)
- g7h64.exe (PID: 17116)
- g7h64.exe (PID: 14720)
- g7h64.exe (PID: 13296)
- g7h64.exe (PID: 20008)
- g7h64.exe (PID: 21468)
- g7h64.exe (PID: 7584)
- g7h64.exe (PID: 17600)
- g7h64.exe (PID: 12128)
- g7h64.exe (PID: 16884)
- g7h64.exe (PID: 12076)
- g7h64.exe (PID: 18784)
- g7h64.exe (PID: 14800)
- g7h64.exe (PID: 8528)
- g7h64.exe (PID: 15728)
- g7h64.exe (PID: 18008)
- g7h64.exe (PID: 13288)
- g7h64.exe (PID: 11932)
- g7h64.exe (PID: 13620)
- g7h64.exe (PID: 18000)
- g7h64.exe (PID: 17248)
- g7h64.exe (PID: 16792)
- g7h64.exe (PID: 14936)
- g7h64.exe (PID: 17640)
- g7h64.exe (PID: 18024)
- g7h64.exe (PID: 15388)
- g7h64.exe (PID: 13148)
- g7h64.exe (PID: 20140)
- g7h64.exe (PID: 12068)
- g7h64.exe (PID: 10668)
- g7h64.exe (PID: 9196)
- g7h64.exe (PID: 8848)
- g7h64.exe (PID: 6960)
- g7h64.exe (PID: 17508)
- g7h64.exe (PID: 22976)
- g7h64.exe (PID: 23120)
- g7h64.exe (PID: 23248)
- g7h64.exe (PID: 22880)
- g7h64.exe (PID: 20812)
- g7h64.exe (PID: 23496)
- g7h64.exe (PID: 15752)
- g7h64.exe (PID: 24324)
- g7h64.exe (PID: 16700)
- g7h64.exe (PID: 24172)
- g7h64.exe (PID: 21484)
- g7h64.exe (PID: 21204)
- g7h64.exe (PID: 19948)
- g7h64.exe (PID: 20556)
- g7h64.exe (PID: 21216)
- g7h64.exe (PID: 20548)
- g7h64.exe (PID: 20156)
- g7h64.exe (PID: 19960)
- g7h64.exe (PID: 17780)
- g7h64.exe (PID: 12552)
- g7h64.exe (PID: 16732)
- g7h64.exe (PID: 19980)
- g7h64.exe (PID: 12168)
- g7h64.exe (PID: 16312)
- g7h64.exe (PID: 18748)
- g7h64.exe (PID: 24064)
- g7h64.exe (PID: 20144)
- g7h64.exe (PID: 23680)
- g7h64.exe (PID: 4212)
- g7h64.exe (PID: 16764)
- g7h64.exe (PID: 11984)
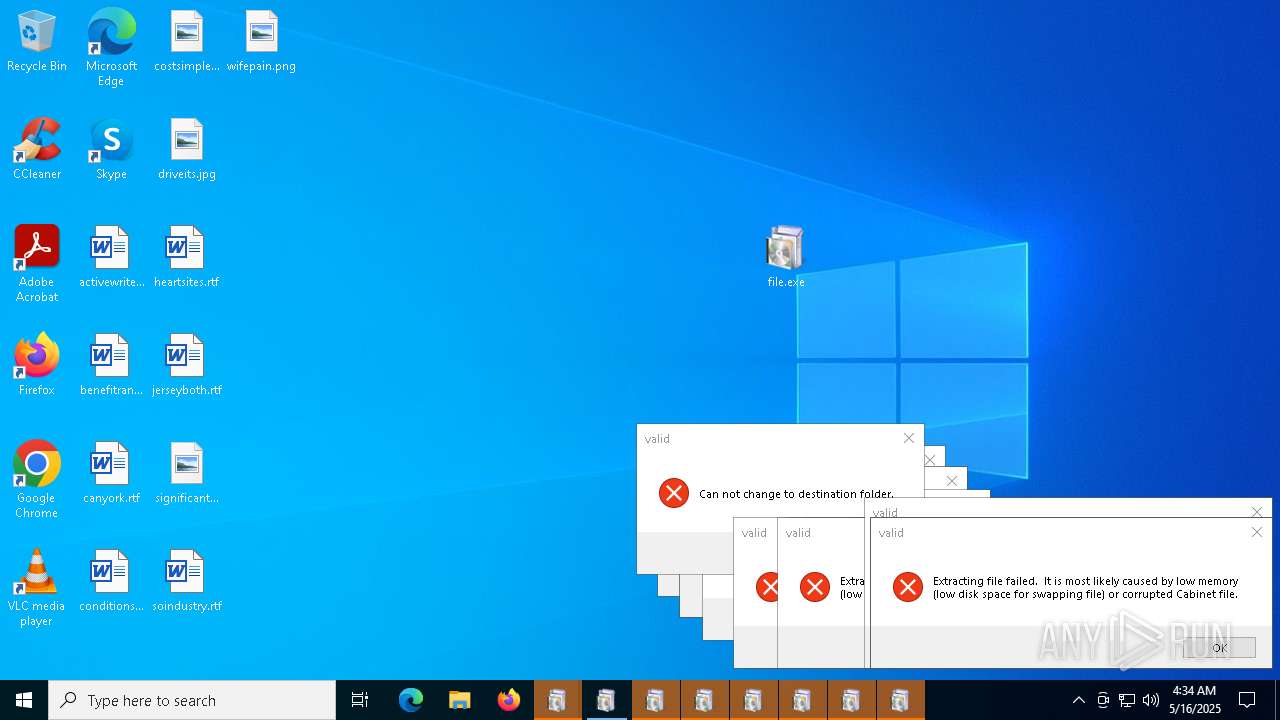
AMADEY mutex has been found
- rapes.exe (PID: 4688)
- 1r80E4.exe (PID: 4756)
- rapes.exe (PID: 7636)
- rapes.exe (PID: 872)
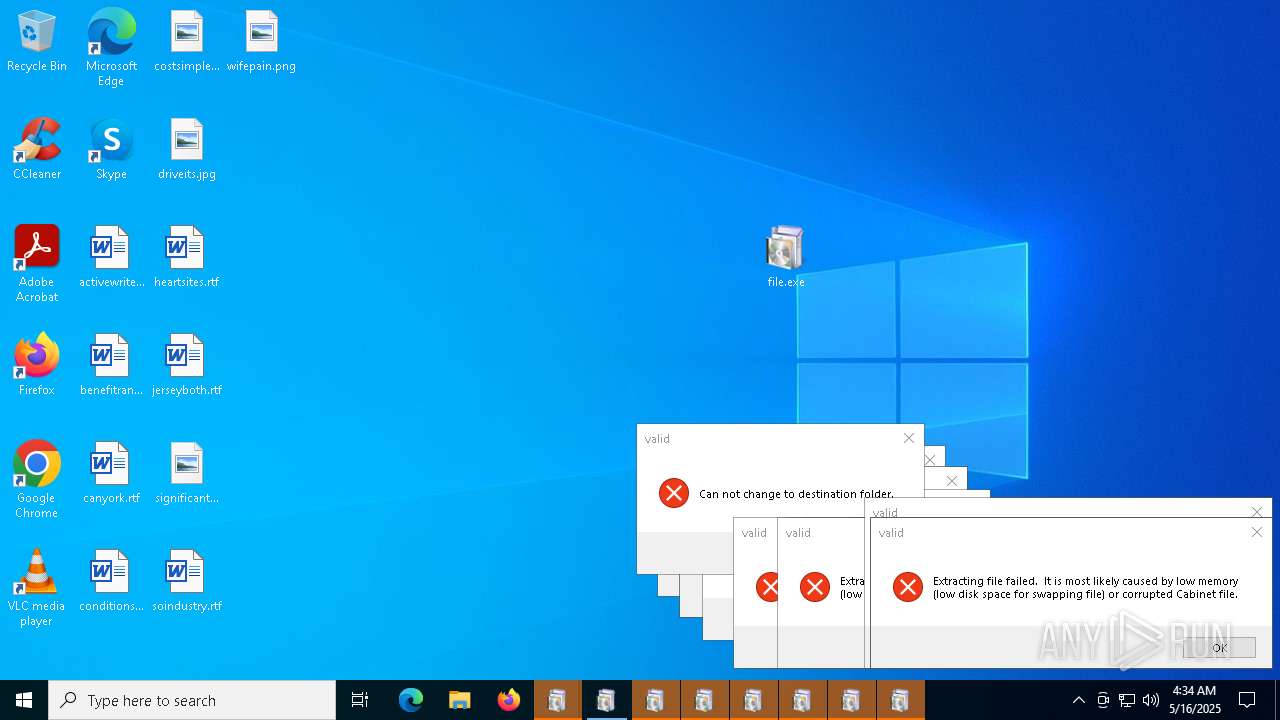
STEALC has been detected
- 3F19T.exe (PID: 7476)
AMADEY has been detected (YARA)
- rapes.exe (PID: 4688)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- msedge.exe (PID: 8028)
Connects to the CnC server
- svchost.exe (PID: 2196)
- msedge.exe (PID: 8028)
Stealers network behavior
- svchost.exe (PID: 2196)
SUSPICIOUS
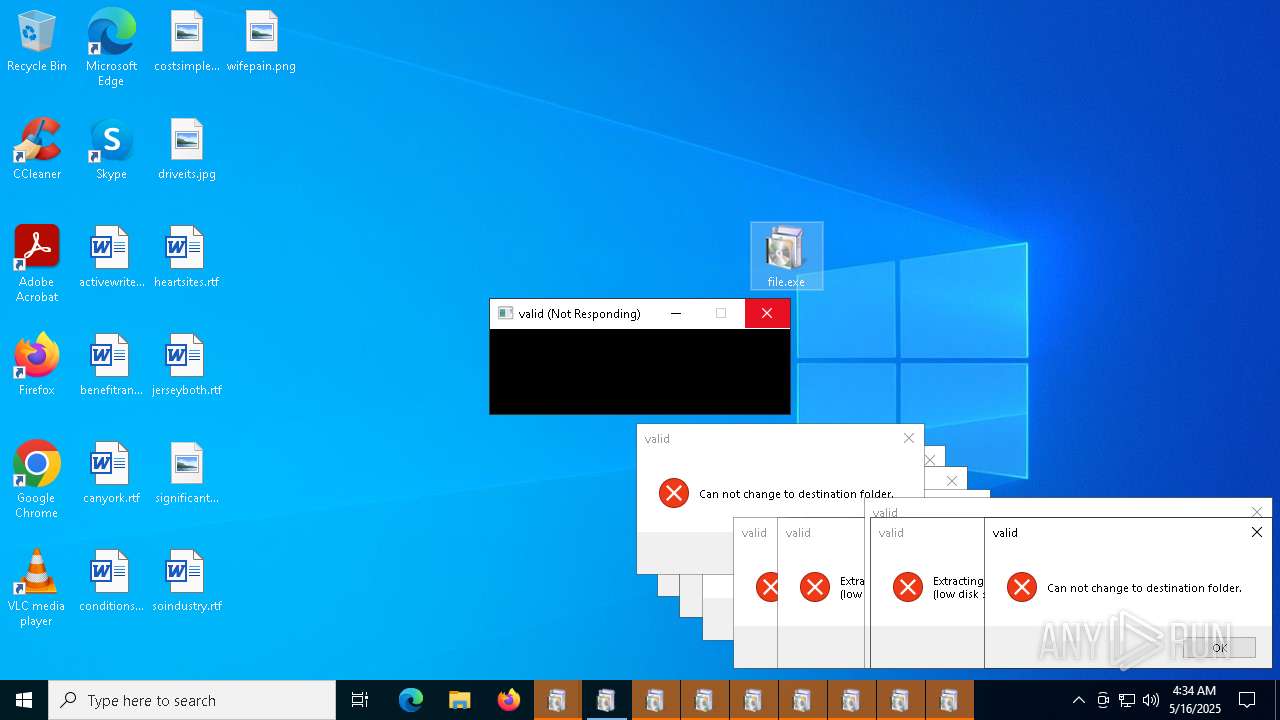
Process drops legitimate windows executable
- redline2.exe (PID: 4628)
- file.exe (PID: 6404)
- file.exe (PID: 7932)
- file.exe (PID: 4996)
- file.exe (PID: 6892)
- file.exe (PID: 5544)
- file.exe (PID: 2284)
- file.exe (PID: 2104)
- file.exe (PID: 5324)
- file.exe (PID: 5024)
- file.exe (PID: 3300)
- file.exe (PID: 7480)
- file.exe (PID: 7348)
- file.exe (PID: 2340)
- file.exe (PID: 7520)
- file.exe (PID: 7496)
- file.exe (PID: 7936)
- file.exe (PID: 8088)
- file.exe (PID: 2108)
- file.exe (PID: 7884)
- file.exe (PID: 232)
- file.exe (PID: 7284)
- file.exe (PID: 4220)
- file.exe (PID: 5548)
- file.exe (PID: 6572)
- file.exe (PID: 5744)
- file.exe (PID: 8312)
- file.exe (PID: 8328)
- file.exe (PID: 7540)
- file.exe (PID: 3620)
- file.exe (PID: 8304)
- file.exe (PID: 8320)
- file.exe (PID: 8288)
- file.exe (PID: 9176)
- file.exe (PID: 6300)
- file.exe (PID: 7588)
- file.exe (PID: 7940)
- file.exe (PID: 6256)
- file.exe (PID: 7720)
- file.exe (PID: 7988)
- file.exe (PID: 6044)
- file.exe (PID: 9244)
- file.exe (PID: 6372)
- file.exe (PID: 10544)
- file.exe (PID: 10660)
- file.exe (PID: 7964)
- file.exe (PID: 616)
- file.exe (PID: 11116)
- file.exe (PID: 11500)
- file.exe (PID: 11100)
- file.exe (PID: 10536)
- file.exe (PID: 10272)
- file.exe (PID: 10652)
- file.exe (PID: 11604)
- file.exe (PID: 8724)
- file.exe (PID: 968)
- file.exe (PID: 7364)
- file.exe (PID: 11372)
- file.exe (PID: 10852)
- file.exe (PID: 11520)
- file.exe (PID: 11528)
- file.exe (PID: 11580)
- file.exe (PID: 12120)
- file.exe (PID: 11616)
- file.exe (PID: 12208)
- file.exe (PID: 8944)
- file.exe (PID: 12184)
- file.exe (PID: 8708)
- file.exe (PID: 12100)
- file.exe (PID: 12172)
- file.exe (PID: 12108)
- file.exe (PID: 12280)
- file.exe (PID: 12244)
- file.exe (PID: 12252)
- file.exe (PID: 12052)
- file.exe (PID: 11628)
- file.exe (PID: 12152)
- file.exe (PID: 12036)
- file.exe (PID: 12084)
- file.exe (PID: 12500)
- file.exe (PID: 9140)
- file.exe (PID: 9008)
- file.exe (PID: 12856)
- file.exe (PID: 12512)
- file.exe (PID: 12524)
- file.exe (PID: 7316)
- file.exe (PID: 12900)
- file.exe (PID: 13864)
- file.exe (PID: 13332)
- file.exe (PID: 12608)
- file.exe (PID: 12668)
- file.exe (PID: 13800)
- file.exe (PID: 12832)
- file.exe (PID: 14312)
- file.exe (PID: 13200)
- file.exe (PID: 13948)
- file.exe (PID: 12364)
- file.exe (PID: 13680)
- file.exe (PID: 14292)
- file.exe (PID: 14028)
- file.exe (PID: 9440)
- file.exe (PID: 14832)
- file.exe (PID: 13504)
- file.exe (PID: 13160)
- file.exe (PID: 13760)
- file.exe (PID: 14776)
- file.exe (PID: 9096)
- file.exe (PID: 8800)
- file.exe (PID: 13576)
- file.exe (PID: 14304)
- file.exe (PID: 13076)
- file.exe (PID: 14788)
- file.exe (PID: 14180)
- file.exe (PID: 5044)
- file.exe (PID: 13540)
- file.exe (PID: 12788)
- file.exe (PID: 13664)
- file.exe (PID: 11460)
- file.exe (PID: 9372)
- file.exe (PID: 14048)
- file.exe (PID: 9068)
- file.exe (PID: 11884)
- file.exe (PID: 14416)
- file.exe (PID: 13072)
- file.exe (PID: 9528)
- file.exe (PID: 9516)
- file.exe (PID: 13976)
- file.exe (PID: 13044)
- file.exe (PID: 13056)
- file.exe (PID: 10632)
- file.exe (PID: 13732)
- file.exe (PID: 14324)
- file.exe (PID: 10916)
- file.exe (PID: 14700)
- file.exe (PID: 13216)
- file.exe (PID: 13548)
- file.exe (PID: 13340)
- file.exe (PID: 14008)
- file.exe (PID: 13772)
- file.exe (PID: 8252)
- file.exe (PID: 15144)
- file.exe (PID: 9844)
- file.exe (PID: 9804)
- file.exe (PID: 10940)
- file.exe (PID: 11560)
- file.exe (PID: 14152)
- file.exe (PID: 14144)
- file.exe (PID: 13692)
- file.exe (PID: 15116)
- file.exe (PID: 13788)
- file.exe (PID: 14272)
- file.exe (PID: 13900)
- file.exe (PID: 8856)
- file.exe (PID: 9736)
- file.exe (PID: 13876)
- file.exe (PID: 14168)
- file.exe (PID: 16904)
- file.exe (PID: 18468)
- file.exe (PID: 8912)
- file.exe (PID: 13252)
- file.exe (PID: 10904)
- file.exe (PID: 15636)
- file.exe (PID: 15344)
- file.exe (PID: 5064)
- file.exe (PID: 2596)
- file.exe (PID: 9872)
- file.exe (PID: 9724)
- file.exe (PID: 13356)
- file.exe (PID: 7420)
- file.exe (PID: 13396)
- file.exe (PID: 12964)
- file.exe (PID: 16456)
- file.exe (PID: 18180)
- file.exe (PID: 13920)
- file.exe (PID: 10580)
- file.exe (PID: 7412)
- file.exe (PID: 14896)
- file.exe (PID: 14768)
- file.exe (PID: 9536)
- file.exe (PID: 13000)
- file.exe (PID: 15608)
- file.exe (PID: 18828)
- file.exe (PID: 16564)
- file.exe (PID: 14280)
- file.exe (PID: 13892)
- file.exe (PID: 12372)
- file.exe (PID: 14992)
- file.exe (PID: 14976)
- file.exe (PID: 9696)
- file.exe (PID: 8676)
- file.exe (PID: 15356)
- file.exe (PID: 14440)
- file.exe (PID: 9540)
- file.exe (PID: 12536)
- file.exe (PID: 18184)
- file.exe (PID: 13184)
- file.exe (PID: 18752)
- file.exe (PID: 14256)
- file.exe (PID: 8576)
- file.exe (PID: 18140)
- file.exe (PID: 13128)
- file.exe (PID: 10808)
- file.exe (PID: 12852)
- file.exe (PID: 8892)
- file.exe (PID: 9364)
- file.exe (PID: 17036)
- file.exe (PID: 11624)
- file.exe (PID: 9276)
- file.exe (PID: 13376)
- file.exe (PID: 15012)
- file.exe (PID: 10136)
- file.exe (PID: 18356)
- file.exe (PID: 9868)
- file.exe (PID: 18088)
- file.exe (PID: 16572)
- file.exe (PID: 10648)
- file.exe (PID: 1672)
- file.exe (PID: 10872)
- file.exe (PID: 14852)
- file.exe (PID: 10848)
- file.exe (PID: 14952)
- file.exe (PID: 13512)
- file.exe (PID: 11940)
- file.exe (PID: 10196)
- file.exe (PID: 11716)
- file.exe (PID: 9192)
- file.exe (PID: 13460)
- file.exe (PID: 14912)
- file.exe (PID: 15220)
- file.exe (PID: 13444)
- file.exe (PID: 10072)
- file.exe (PID: 10556)
- file.exe (PID: 18480)
- file.exe (PID: 17476)
- file.exe (PID: 14464)
- file.exe (PID: 18804)
- file.exe (PID: 15928)
- file.exe (PID: 10528)
- file.exe (PID: 10876)
- file.exe (PID: 9420)
- file.exe (PID: 15276)
- file.exe (PID: 10800)
- file.exe (PID: 17484)
- file.exe (PID: 7396)
- file.exe (PID: 18532)
- file.exe (PID: 18720)
- file.exe (PID: 18732)
- file.exe (PID: 17968)
- file.exe (PID: 18668)
- file.exe (PID: 15624)
- file.exe (PID: 14636)
Starts a Microsoft application from unusual location
- redline2.exe (PID: 4628)
- g7h64.exe (PID: 3884)
- file.exe (PID: 6404)
- g7h64.exe (PID: 2692)
- file.exe (PID: 7932)
- file.exe (PID: 3012)
- file.exe (PID: 6892)
- file.exe (PID: 4996)
- g7h64.exe (PID: 6300)
- file.exe (PID: 5544)
- file.exe (PID: 2284)
- file.exe (PID: 2104)
- file.exe (PID: 5324)
- file.exe (PID: 3300)
- file.exe (PID: 5024)
- file.exe (PID: 7520)
- file.exe (PID: 2340)
- file.exe (PID: 7348)
- file.exe (PID: 7480)
- file.exe (PID: 3396)
- file.exe (PID: 2516)
- file.exe (PID: 7936)
- file.exe (PID: 7496)
- g7h64.exe (PID: 7568)
- g7h64.exe (PID: 8188)
- file.exe (PID: 7884)
- file.exe (PID: 6112)
- file.exe (PID: 5744)
- file.exe (PID: 3620)
- file.exe (PID: 7216)
- file.exe (PID: 4012)
- file.exe (PID: 2108)
- file.exe (PID: 7412)
- file.exe (PID: 4424)
- file.exe (PID: 5548)
- file.exe (PID: 5188)
- g7h64.exe (PID: 3992)
- file.exe (PID: 4692)
- file.exe (PID: 8088)
- file.exe (PID: 7540)
- file.exe (PID: 232)
- file.exe (PID: 6572)
- file.exe (PID: 8000)
- file.exe (PID: 300)
- file.exe (PID: 6940)
- file.exe (PID: 7284)
- file.exe (PID: 3768)
- file.exe (PID: 8096)
- file.exe (PID: 4220)
- file.exe (PID: 8304)
- file.exe (PID: 8288)
- file.exe (PID: 896)
- file.exe (PID: 8296)
- file.exe (PID: 8328)
- file.exe (PID: 8320)
- g7h64.exe (PID: 8360)
- g7h64.exe (PID: 8352)
- file.exe (PID: 8312)
- g7h64.exe (PID: 8492)
- g7h64.exe (PID: 8484)
- g7h64.exe (PID: 8604)
- g7h64.exe (PID: 8580)
- g7h64.exe (PID: 8616)
- g7h64.exe (PID: 8544)
- g7h64.exe (PID: 9160)
- g7h64.exe (PID: 9204)
- g7h64.exe (PID: 6980)
- g7h64.exe (PID: 9212)
- g7h64.exe (PID: 8212)
- g7h64.exe (PID: 8244)
- g7h64.exe (PID: 8224)
- g7h64.exe (PID: 8204)
- g7h64.exe (PID: 1568)
- g7h64.exe (PID: 8076)
- g7h64.exe (PID: 7716)
- g7h64.exe (PID: 6740)
- g7h64.exe (PID: 1240)
- file.exe (PID: 7988)
- file.exe (PID: 9176)
- file.exe (PID: 6044)
- file.exe (PID: 7588)
- file.exe (PID: 6256)
- file.exe (PID: 6300)
- g7h64.exe (PID: 976)
- g7h64.exe (PID: 3032)
- file.exe (PID: 7720)
- file.exe (PID: 7940)
- g7h64.exe (PID: 1056)
- g7h64.exe (PID: 7924)
- g7h64.exe (PID: 7156)
- g7h64.exe (PID: 668)
- g7h64.exe (PID: 5720)
- g7h64.exe (PID: 8264)
- g7h64.exe (PID: 8876)
- g7h64.exe (PID: 8524)
- g7h64.exe (PID: 8900)
- g7h64.exe (PID: 10168)
- g7h64.exe (PID: 10180)
- file.exe (PID: 7964)
- file.exe (PID: 6372)
- file.exe (PID: 9244)
- file.exe (PID: 616)
- file.exe (PID: 968)
- g7h64.exe (PID: 5384)
- file.exe (PID: 10272)
- file.exe (PID: 7364)
- file.exe (PID: 10536)
- file.exe (PID: 10544)
- file.exe (PID: 10660)
- file.exe (PID: 10652)
- file.exe (PID: 11092)
- file.exe (PID: 11100)
- file.exe (PID: 11116)
- file.exe (PID: 11372)
- g7h64.exe (PID: 11408)
- file.exe (PID: 11452)
- file.exe (PID: 10852)
- file.exe (PID: 11080)
- g7h64.exe (PID: 11464)
- g7h64.exe (PID: 11472)
- file.exe (PID: 11500)
- file.exe (PID: 11508)
- file.exe (PID: 11520)
- file.exe (PID: 11528)
- file.exe (PID: 11616)
- file.exe (PID: 11628)
- g7h64.exe (PID: 11856)
- g7h64.exe (PID: 11864)
- file.exe (PID: 12036)
- file.exe (PID: 11596)
- file.exe (PID: 11580)
- file.exe (PID: 11604)
- file.exe (PID: 12052)
- file.exe (PID: 12084)
- file.exe (PID: 12108)
- file.exe (PID: 12100)
- file.exe (PID: 12120)
- file.exe (PID: 12152)
- file.exe (PID: 12172)
- file.exe (PID: 12244)
- file.exe (PID: 12252)
- file.exe (PID: 8708)
- file.exe (PID: 12280)
- file.exe (PID: 8724)
- file.exe (PID: 8944)
- file.exe (PID: 9008)
- file.exe (PID: 12184)
- file.exe (PID: 12208)
- file.exe (PID: 9140)
- file.exe (PID: 2596)
- file.exe (PID: 8800)
- file.exe (PID: 7316)
- file.exe (PID: 12364)
- file.exe (PID: 12384)
- file.exe (PID: 12392)
- file.exe (PID: 12524)
- file.exe (PID: 12536)
- file.exe (PID: 12608)
- file.exe (PID: 12564)
- file.exe (PID: 12572)
- file.exe (PID: 12600)
- file.exe (PID: 12500)
- file.exe (PID: 12512)
- file.exe (PID: 12652)
- file.exe (PID: 12668)
- file.exe (PID: 12676)
- file.exe (PID: 12796)
- file.exe (PID: 12788)
- file.exe (PID: 12812)
- file.exe (PID: 12620)
- file.exe (PID: 12628)
- file.exe (PID: 12644)
- file.exe (PID: 12844)
- file.exe (PID: 12856)
- file.exe (PID: 12868)
- file.exe (PID: 12888)
- file.exe (PID: 12900)
- file.exe (PID: 12908)
- file.exe (PID: 12820)
- file.exe (PID: 12832)
- file.exe (PID: 13056)
- file.exe (PID: 13064)
- g7h64.exe (PID: 13096)
- file.exe (PID: 13016)
- file.exe (PID: 13028)
- file.exe (PID: 13076)
- g7h64.exe (PID: 13140)
- file.exe (PID: 13152)
- file.exe (PID: 13176)
- file.exe (PID: 13164)
- file.exe (PID: 13160)
- file.exe (PID: 13184)
- file.exe (PID: 13200)
- file.exe (PID: 13216)
- file.exe (PID: 13320)
- file.exe (PID: 10528)
- file.exe (PID: 13340)
- file.exe (PID: 13332)
- file.exe (PID: 13192)
- file.exe (PID: 13224)
- g7h64.exe (PID: 13368)
- g7h64.exe (PID: 13384)
- file.exe (PID: 13404)
- file.exe (PID: 13396)
- file.exe (PID: 13360)
- file.exe (PID: 13376)
- file.exe (PID: 13428)
- file.exe (PID: 13416)
- file.exe (PID: 13444)
- file.exe (PID: 13460)
- file.exe (PID: 13512)
- file.exe (PID: 13532)
- file.exe (PID: 13540)
- file.exe (PID: 13552)
- file.exe (PID: 13588)
- file.exe (PID: 13576)
- g7h64.exe (PID: 13492)
- file.exe (PID: 13504)
- g7h64.exe (PID: 13604)
- file.exe (PID: 13612)
- g7h64.exe (PID: 13620)
- file.exe (PID: 13692)
- file.exe (PID: 13740)
- g7h64.exe (PID: 13720)
- file.exe (PID: 13760)
- file.exe (PID: 13788)
- file.exe (PID: 13664)
- file.exe (PID: 13680)
- file.exe (PID: 13732)
- file.exe (PID: 13772)
- file.exe (PID: 13876)
- file.exe (PID: 13884)
- file.exe (PID: 13892)
- file.exe (PID: 13928)
- file.exe (PID: 13900)
- file.exe (PID: 13920)
- file.exe (PID: 13800)
- file.exe (PID: 13824)
- file.exe (PID: 13864)
- file.exe (PID: 13976)
- file.exe (PID: 14008)
- file.exe (PID: 14028)
- file.exe (PID: 14040)
- file.exe (PID: 13948)
- file.exe (PID: 13964)
- file.exe (PID: 14072)
- file.exe (PID: 14116)
- g7h64.exe (PID: 14124)
- file.exe (PID: 14132)
- file.exe (PID: 14144)
- file.exe (PID: 14152)
- file.exe (PID: 14048)
- file.exe (PID: 14180)
- file.exe (PID: 14212)
- g7h64.exe (PID: 14224)
- file.exe (PID: 14168)
- g7h64.exe (PID: 14232)
- g7h64.exe (PID: 14240)
- file.exe (PID: 14256)
- file.exe (PID: 14272)
- file.exe (PID: 14280)
- file.exe (PID: 14304)
- file.exe (PID: 14292)
- file.exe (PID: 14312)
- file.exe (PID: 14324)
- file.exe (PID: 5044)
- file.exe (PID: 11564)
- file.exe (PID: 11460)
- file.exe (PID: 11560)
- file.exe (PID: 11624)
- g7h64.exe (PID: 12068)
- file.exe (PID: 11884)
- file.exe (PID: 12240)
- file.exe (PID: 9096)
- file.exe (PID: 12372)
- g7h64.exe (PID: 12520)
- file.exe (PID: 11232)
- file.exe (PID: 9356)
- file.exe (PID: 9364)
- g7h64.exe (PID: 12532)
- file.exe (PID: 9372)
- file.exe (PID: 9428)
- file.exe (PID: 9440)
- file.exe (PID: 9540)
- file.exe (PID: 9516)
- file.exe (PID: 9528)
- file.exe (PID: 9420)
- file.exe (PID: 8592)
- file.exe (PID: 9068)
- file.exe (PID: 9660)
- file.exe (PID: 9672)
- file.exe (PID: 9696)
- file.exe (PID: 9708)
- file.exe (PID: 9736)
- file.exe (PID: 12852)
- file.exe (PID: 8892)
- g7h64.exe (PID: 12808)
- g7h64.exe (PID: 12864)
- g7h64.exe (PID: 5352)
- g7h64.exe (PID: 9744)
- g7h64.exe (PID: 9756)
- file.exe (PID: 9780)
- file.exe (PID: 9724)
- file.exe (PID: 9828)
- file.exe (PID: 9844)
- file.exe (PID: 9868)
- g7h64.exe (PID: 9896)
- g7h64.exe (PID: 13148)
- file.exe (PID: 9804)
- file.exe (PID: 13252)
- file.exe (PID: 13356)
- file.exe (PID: 13412)
- file.exe (PID: 14416)
- file.exe (PID: 14424)
- g7h64.exe (PID: 13036)
- file.exe (PID: 13072)
- file.exe (PID: 13044)
- g7h64.exe (PID: 14724)
- file.exe (PID: 14768)
- g7h64.exe (PID: 14720)
- file.exe (PID: 14776)
- file.exe (PID: 14788)
- g7h64.exe (PID: 14800)
- g7h64.exe (PID: 14816)
- file.exe (PID: 14832)
- file.exe (PID: 14448)
- file.exe (PID: 14464)
- file.exe (PID: 14912)
- g7h64.exe (PID: 14936)
- g7h64.exe (PID: 14928)
- file.exe (PID: 14952)
- g7h64.exe (PID: 14960)
- file.exe (PID: 14992)
- file.exe (PID: 14852)
- file.exe (PID: 14896)
- file.exe (PID: 15012)
- file.exe (PID: 15056)
- file.exe (PID: 15080)
- file.exe (PID: 15116)
- file.exe (PID: 15144)
- file.exe (PID: 15220)
- file.exe (PID: 15344)
- file.exe (PID: 15020)
- file.exe (PID: 13528)
- g7h64.exe (PID: 10668)
- g7h64.exe (PID: 10688)
- g7h64.exe (PID: 10696)
- file.exe (PID: 10704)
- file.exe (PID: 10756)
- file.exe (PID: 5064)
- g7h64.exe (PID: 9952)
- file.exe (PID: 9460)
- file.exe (PID: 9276)
- file.exe (PID: 1672)
- g7h64.exe (PID: 9964)
- file.exe (PID: 10876)
- file.exe (PID: 10904)
- file.exe (PID: 10916)
- file.exe (PID: 10940)
- file.exe (PID: 10956)
- file.exe (PID: 10196)
- file.exe (PID: 14976)
- file.exe (PID: 11724)
- file.exe (PID: 11716)
- file.exe (PID: 10072)
- file.exe (PID: 10136)
- file.exe (PID: 10160)
- file.exe (PID: 13548)
- file.exe (PID: 13712)
- g7h64.exe (PID: 8848)
- file.exe (PID: 8856)
- file.exe (PID: 9192)
- file.exe (PID: 8252)
- file.exe (PID: 14700)
- file.exe (PID: 10556)
- file.exe (PID: 10580)
- file.exe (PID: 10648)
- file.exe (PID: 10632)
- g7h64.exe (PID: 9196)
- g7h64.exe (PID: 9000)
- g7h64.exe (PID: 9560)
- g7h64.exe (PID: 15388)
- g7h64.exe (PID: 16576)
- g7h64.exe (PID: 16816)
- g7h64.exe (PID: 17116)
- g7h64.exe (PID: 17160)
- g7h64.exe (PID: 17232)
- g7h64.exe (PID: 17240)
- g7h64.exe (PID: 17280)
- g7h64.exe (PID: 17248)
- g7h64.exe (PID: 812)
- g7h64.exe (PID: 16792)
- g7h64.exe (PID: 9484)
- g7h64.exe (PID: 10592)
- g7h64.exe (PID: 10936)
- g7h64.exe (PID: 13716)
- g7h64.exe (PID: 17816)
- g7h64.exe (PID: 17672)
- g7h64.exe (PID: 18232)
- g7h64.exe (PID: 7484)
- g7h64.exe (PID: 17600)
- g7h64.exe (PID: 17640)
- g7h64.exe (PID: 19420)
- g7h64.exe (PID: 8828)
- g7h64.exe (PID: 8640)
- g7h64.exe (PID: 8636)
- g7h64.exe (PID: 14196)
- file.exe (PID: 14440)
- g7h64.exe (PID: 6168)
- g7h64.exe (PID: 12440)
- g7h64.exe (PID: 16976)
- g7h64.exe (PID: 7480)
- g7h64.exe (PID: 16704)
- g7h64.exe (PID: 16712)
- g7h64.exe (PID: 16756)
- g7h64.exe (PID: 15240)
- g7h64.exe (PID: 17636)
- g7h64.exe (PID: 16316)
- g7h64.exe (PID: 14208)
- g7h64.exe (PID: 13272)
- g7h64.exe (PID: 13288)
- g7h64.exe (PID: 13296)
- g7h64.exe (PID: 16548)
- g7h64.exe (PID: 16556)
- g7h64.exe (PID: 13264)
- file.exe (PID: 16572)
- file.exe (PID: 15880)
- file.exe (PID: 16904)
- file.exe (PID: 16564)
- g7h64.exe (PID: 5212)
- file.exe (PID: 18468)
- g7h64.exe (PID: 16628)
- file.exe (PID: 15592)
- file.exe (PID: 15608)
- file.exe (PID: 15624)
- file.exe (PID: 8912)
- file.exe (PID: 15636)
- file.exe (PID: 15644)
- g7h64.exe (PID: 16620)
- file.exe (PID: 7428)
- file.exe (PID: 18656)
- file.exe (PID: 12964)
- file.exe (PID: 12980)
- file.exe (PID: 13000)
- file.exe (PID: 8676)
- file.exe (PID: 8644)
- file.exe (PID: 16456)
- file.exe (PID: 9872)
- file.exe (PID: 19156)
- file.exe (PID: 8196)
- g7h64.exe (PID: 17724)
- file.exe (PID: 17036)
- file.exe (PID: 9572)
- file.exe (PID: 18532)
- g7h64.exe (PID: 17760)
- g7h64.exe (PID: 17772)
- g7h64.exe (PID: 17780)
- g7h64.exe (PID: 17740)
- g7h64.exe (PID: 18936)
- file.exe (PID: 18140)
- file.exe (PID: 18184)
- g7h64.exe (PID: 18980)
- g7h64.exe (PID: 18000)
- g7h64.exe (PID: 18008)
- file.exe (PID: 15356)
- file.exe (PID: 10348)
- file.exe (PID: 19264)
- file.exe (PID: 18180)
- file.exe (PID: 17968)
- file.exe (PID: 16640)
- file.exe (PID: 8576)
- file.exe (PID: 18480)
- file.exe (PID: 15276)
- file.exe (PID: 12700)
- file.exe (PID: 9536)
- file.exe (PID: 12692)
- file.exe (PID: 7380)
- file.exe (PID: 12432)
- file.exe (PID: 9208)
- file.exe (PID: 17428)
- file.exe (PID: 18304)
- file.exe (PID: 18292)
- file.exe (PID: 17436)
- file.exe (PID: 12712)
- file.exe (PID: 7420)
- file.exe (PID: 12744)
- file.exe (PID: 17444)
- file.exe (PID: 17452)
- file.exe (PID: 17460)
- file.exe (PID: 17476)
- file.exe (PID: 17492)
- file.exe (PID: 17484)
- g7h64.exe (PID: 18756)
- file.exe (PID: 11940)
- file.exe (PID: 11948)
- file.exe (PID: 11956)
- file.exe (PID: 15928)
- g7h64.exe (PID: 11984)
- file.exe (PID: 18668)
- file.exe (PID: 18752)
- file.exe (PID: 18696)
- g7h64.exe (PID: 13780)
- g7h64.exe (PID: 6960)
- file.exe (PID: 10816)
- file.exe (PID: 10824)
- file.exe (PID: 10840)
- file.exe (PID: 10848)
- file.exe (PID: 7396)
- file.exe (PID: 10800)
- file.exe (PID: 10808)
- file.exe (PID: 10872)
- file.exe (PID: 13052)
- file.exe (PID: 18828)
- file.exe (PID: 18720)
- file.exe (PID: 18804)
- file.exe (PID: 10860)
- file.exe (PID: 13128)
- file.exe (PID: 10328)
- file.exe (PID: 18732)
- g7h64.exe (PID: 16700)
- file.exe (PID: 18356)
- file.exe (PID: 14636)
- file.exe (PID: 18088)
- g7h64.exe (PID: 15788)
- g7h64.exe (PID: 18784)
- g7h64.exe (PID: 16860)
- g7h64.exe (PID: 16884)
- g7h64.exe (PID: 18024)
- g7h64.exe (PID: 4152)
- g7h64.exe (PID: 10284)
- g7h64.exe (PID: 16968)
- g7h64.exe (PID: 16312)
- g7h64.exe (PID: 5592)
- g7h64.exe (PID: 15088)
- g7h64.exe (PID: 16732)
- g7h64.exe (PID: 19932)
- g7h64.exe (PID: 19948)
- g7h64.exe (PID: 19960)
- g7h64.exe (PID: 19992)
- g7h64.exe (PID: 19980)
- g7h64.exe (PID: 20008)
- g7h64.exe (PID: 21180)
- g7h64.exe (PID: 21192)
- g7h64.exe (PID: 21204)
- g7h64.exe (PID: 21244)
- g7h64.exe (PID: 21468)
- g7h64.exe (PID: 21484)
- g7h64.exe (PID: 18868)
- g7h64.exe (PID: 11932)
- g7h64.exe (PID: 7584)
- g7h64.exe (PID: 9104)
- g7h64.exe (PID: 19968)
- g7h64.exe (PID: 8448)
- g7h64.exe (PID: 8528)
- g7h64.exe (PID: 13124)
- g7h64.exe (PID: 16764)
- g7h64.exe (PID: 15752)
- g7h64.exe (PID: 20812)
- g7h64.exe (PID: 15728)
- g7h64.exe (PID: 20556)
- g7h64.exe (PID: 20564)
- g7h64.exe (PID: 18748)
- g7h64.exe (PID: 17508)
- g7h64.exe (PID: 20800)
- g7h64.exe (PID: 8692)
- g7h64.exe (PID: 20264)
- g7h64.exe (PID: 20272)
- g7h64.exe (PID: 20308)
- g7h64.exe (PID: 20316)
- g7h64.exe (PID: 20324)
- g7h64.exe (PID: 20332)
- g7h64.exe (PID: 20156)
- g7h64.exe (PID: 20144)
- g7h64.exe (PID: 20140)
- g7h64.exe (PID: 20048)
- g7h64.exe (PID: 22880)
- g7h64.exe (PID: 22892)
- g7h64.exe (PID: 22900)
- g7h64.exe (PID: 22948)
- g7h64.exe (PID: 22976)
- g7h64.exe (PID: 22932)
- g7h64.exe (PID: 22940)
- g7h64.exe (PID: 23000)
- g7h64.exe (PID: 23028)
- g7h64.exe (PID: 23040)
- g7h64.exe (PID: 23248)
- g7h64.exe (PID: 23276)
- g7h64.exe (PID: 23440)
- g7h64.exe (PID: 23448)
- g7h64.exe (PID: 11268)
- g7h64.exe (PID: 23468)
- g7h64.exe (PID: 23484)
- g7h64.exe (PID: 23496)
- g7h64.exe (PID: 11368)
- g7h64.exe (PID: 3768)
- g7h64.exe (PID: 12076)
- g7h64.exe (PID: 12128)
- g7h64.exe (PID: 12160)
- g7h64.exe (PID: 12216)
- g7h64.exe (PID: 12168)
- g7h64.exe (PID: 12204)
- g7h64.exe (PID: 12220)
- g7h64.exe (PID: 9136)
- g7h64.exe (PID: 8748)
- g7h64.exe (PID: 4212)
- g7h64.exe (PID: 12552)
- g7h64.exe (PID: 23104)
- g7h64.exe (PID: 23120)
- g7h64.exe (PID: 23128)
- g7h64.exe (PID: 23632)
- g7h64.exe (PID: 23680)
- g7h64.exe (PID: 23840)
- g7h64.exe (PID: 24032)
- g7h64.exe (PID: 24064)
- g7h64.exe (PID: 24164)
- g7h64.exe (PID: 24172)
- g7h64.exe (PID: 24324)
- g7h64.exe (PID: 24436)
- g7h64.exe (PID: 20532)
- g7h64.exe (PID: 20548)
- g7h64.exe (PID: 7212)
- g7h64.exe (PID: 9236)
- g7h64.exe (PID: 7920)
- g7h64.exe (PID: 10204)
- g7h64.exe (PID: 10248)
- g7h64.exe (PID: 236)
- g7h64.exe (PID: 3268)
- g7h64.exe (PID: 21832)
- g7h64.exe (PID: 21224)
- g7h64.exe (PID: 24964)
- g7h64.exe (PID: 24972)
- g7h64.exe (PID: 25012)
- g7h64.exe (PID: 25020)
- g7h64.exe (PID: 21216)
- g7h64.exe (PID: 25068)
- g7h64.exe (PID: 25192)
- g7h64.exe (PID: 25504)
- g7h64.exe (PID: 21476)
- g7h64.exe (PID: 18940)
- g7h64.exe (PID: 26432)
- g7h64.exe (PID: 26500)
- g7h64.exe (PID: 26492)
- g7h64.exe (PID: 26508)
- g7h64.exe (PID: 26468)
- g7h64.exe (PID: 26476)
- g7h64.exe (PID: 26548)
- g7h64.exe (PID: 26516)
- g7h64.exe (PID: 26524)
- g7h64.exe (PID: 1240)
- g7h64.exe (PID: 12424)
- g7h64.exe (PID: 16204)
- g7h64.exe (PID: 1056)
- g7h64.exe (PID: 26640)
- g7h64.exe (PID: 26648)
- g7h64.exe (PID: 26684)
- g7h64.exe (PID: 26692)
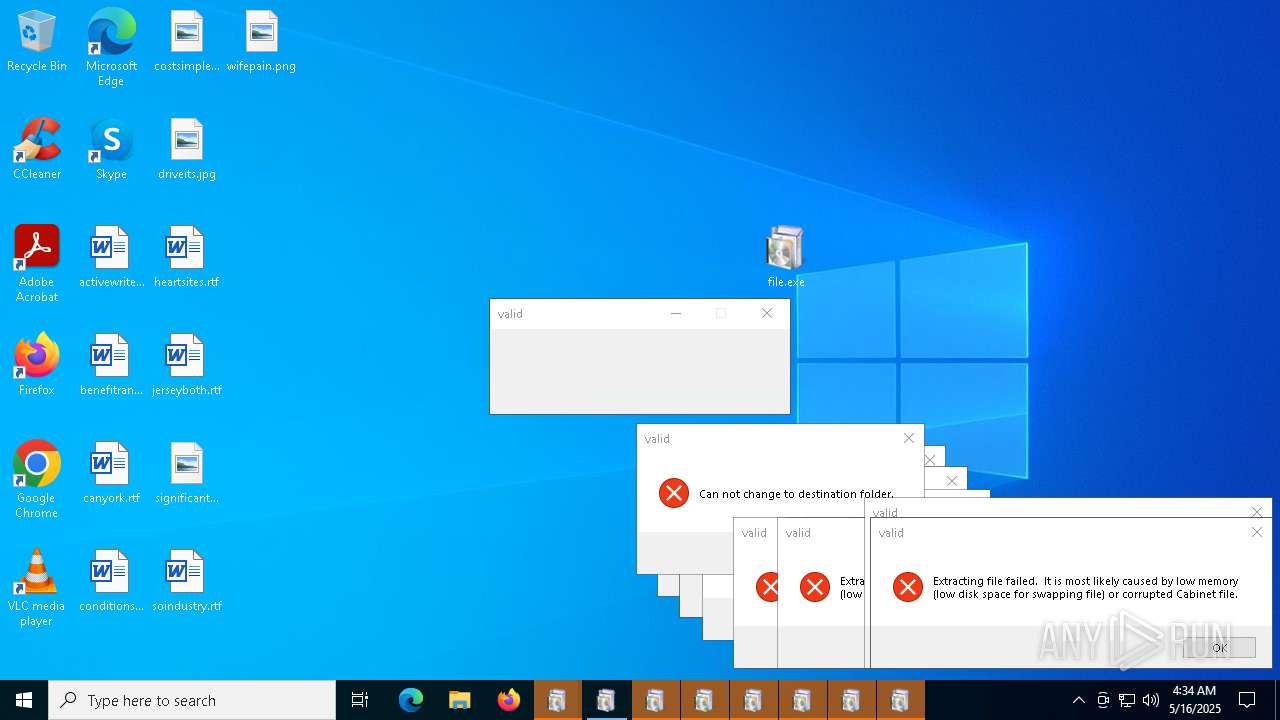
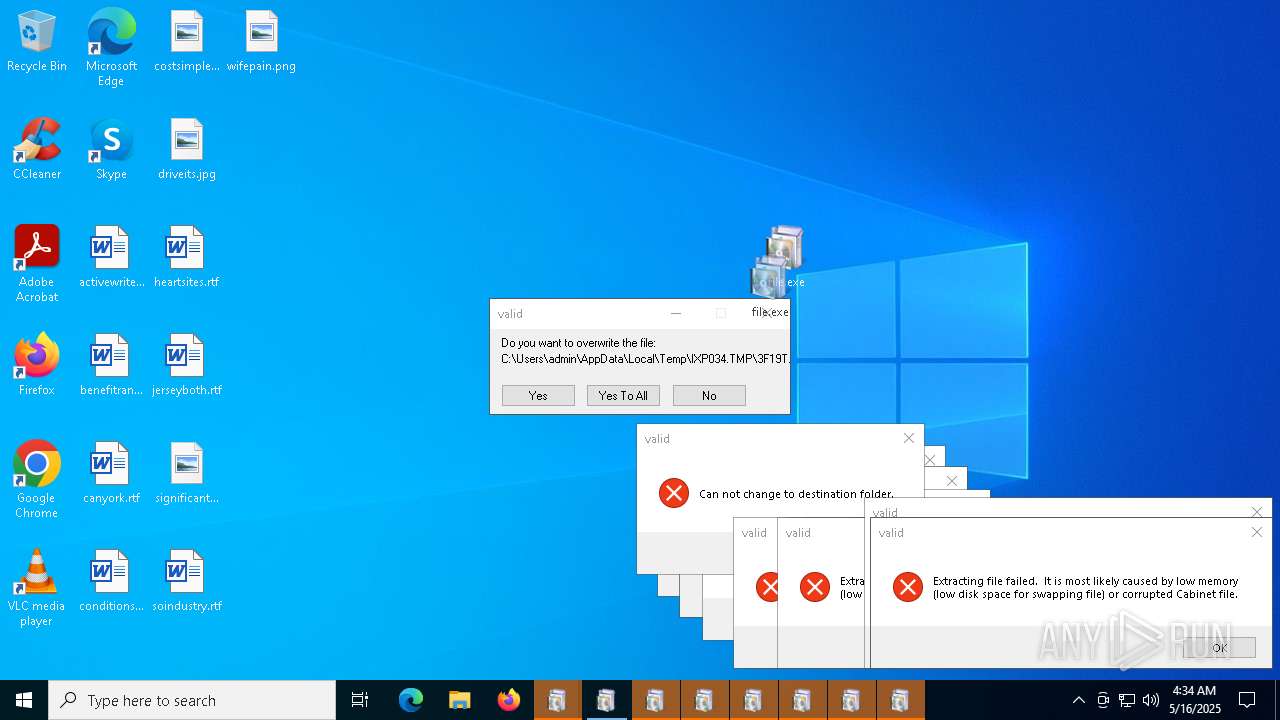
Executable content was dropped or overwritten
- redline2.exe (PID: 4628)
- g7h64.exe (PID: 3884)
- 1r80E4.exe (PID: 4756)
- file.exe (PID: 6404)
- g7h64.exe (PID: 2692)
- file.exe (PID: 7932)
- file.exe (PID: 2284)
- g7h64.exe (PID: 6300)
- file.exe (PID: 4996)
- file.exe (PID: 5544)
- file.exe (PID: 5324)
- file.exe (PID: 5024)
- file.exe (PID: 3300)
- file.exe (PID: 2340)
- file.exe (PID: 7348)
- file.exe (PID: 7412)
- file.exe (PID: 7480)
- file.exe (PID: 7520)
- g7h64.exe (PID: 7568)
- g7h64.exe (PID: 8188)
- file.exe (PID: 6892)
- file.exe (PID: 7496)
- file.exe (PID: 7936)
- file.exe (PID: 8096)
- file.exe (PID: 6112)
- file.exe (PID: 2104)
- file.exe (PID: 8088)
- file.exe (PID: 2108)
- g7h64.exe (PID: 3992)
- file.exe (PID: 4692)
- file.exe (PID: 7884)
- file.exe (PID: 232)
- file.exe (PID: 896)
- file.exe (PID: 5744)
- file.exe (PID: 7284)
- file.exe (PID: 4220)
- file.exe (PID: 8000)
- g7h64.exe (PID: 8492)
- file.exe (PID: 6572)
- file.exe (PID: 4012)
- file.exe (PID: 3768)
- file.exe (PID: 8312)
- file.exe (PID: 8328)
- g7h64.exe (PID: 8544)
- g7h64.exe (PID: 8580)
- file.exe (PID: 3620)
- file.exe (PID: 8304)
- file.exe (PID: 8320)
- g7h64.exe (PID: 9160)
- g7h64.exe (PID: 8616)
- g7h64.exe (PID: 8604)
- file.exe (PID: 5548)
- file.exe (PID: 4424)
- file.exe (PID: 7540)
- g7h64.exe (PID: 8484)
- file.exe (PID: 8288)
- file.exe (PID: 6940)
- g7h64.exe (PID: 6980)
- g7h64.exe (PID: 6740)
- g7h64.exe (PID: 8244)
- g7h64.exe (PID: 7924)
- g7h64.exe (PID: 1240)
- g7h64.exe (PID: 3032)
- g7h64.exe (PID: 9204)
- g7h64.exe (PID: 8264)
- g7h64.exe (PID: 8212)
- g7h64.exe (PID: 7716)
- g7h64.exe (PID: 9212)
- g7h64.exe (PID: 8204)
- g7h64.exe (PID: 8224)
- g7h64.exe (PID: 8524)
- g7h64.exe (PID: 8076)
- g7h64.exe (PID: 976)
- g7h64.exe (PID: 5720)
- g7h64.exe (PID: 1056)
- g7h64.exe (PID: 8900)
- g7h64.exe (PID: 7156)
- file.exe (PID: 9176)
- file.exe (PID: 7940)
- g7h64.exe (PID: 8876)
- g7h64.exe (PID: 668)
- file.exe (PID: 6300)
- file.exe (PID: 7588)
- file.exe (PID: 6256)
- g7h64.exe (PID: 10180)
- file.exe (PID: 7720)
- file.exe (PID: 9244)
- g7h64.exe (PID: 10168)
- file.exe (PID: 6044)
- file.exe (PID: 11092)
- file.exe (PID: 6372)
- file.exe (PID: 7988)
- file.exe (PID: 10544)
- file.exe (PID: 10660)
- g7h64.exe (PID: 5384)
- g7h64.exe (PID: 11464)
- file.exe (PID: 7964)
- file.exe (PID: 616)
- file.exe (PID: 11500)
- g7h64.exe (PID: 11408)
- file.exe (PID: 11100)
- file.exe (PID: 10536)
- file.exe (PID: 10652)
- file.exe (PID: 11080)
- file.exe (PID: 10272)
- file.exe (PID: 11604)
- file.exe (PID: 11116)
- file.exe (PID: 7364)
- file.exe (PID: 8724)
- file.exe (PID: 968)
- file.exe (PID: 10852)
- file.exe (PID: 11372)
- file.exe (PID: 11520)
- file.exe (PID: 11528)
- file.exe (PID: 11580)
- g7h64.exe (PID: 11864)
- file.exe (PID: 11616)
- g7h64.exe (PID: 11856)
- file.exe (PID: 12120)
- file.exe (PID: 8944)
- file.exe (PID: 12184)
- file.exe (PID: 12208)
- file.exe (PID: 12172)
- file.exe (PID: 8708)
- file.exe (PID: 12100)
- file.exe (PID: 12108)
- file.exe (PID: 12252)
- file.exe (PID: 12244)
- file.exe (PID: 12280)
- file.exe (PID: 12052)
- file.exe (PID: 11628)
- file.exe (PID: 12084)
- file.exe (PID: 12036)
- file.exe (PID: 12152)
- g7h64.exe (PID: 11472)
- file.exe (PID: 12512)
- file.exe (PID: 12500)
- file.exe (PID: 9140)
- file.exe (PID: 9008)
- file.exe (PID: 12524)
- file.exe (PID: 7316)
- g7h64.exe (PID: 13720)
- file.exe (PID: 12900)
- file.exe (PID: 13864)
- file.exe (PID: 13016)
- file.exe (PID: 13332)
- file.exe (PID: 12888)
- file.exe (PID: 12856)
- file.exe (PID: 12676)
- file.exe (PID: 12608)
- file.exe (PID: 13028)
- file.exe (PID: 12668)
- file.exe (PID: 12652)
- file.exe (PID: 13800)
- file.exe (PID: 14312)
- file.exe (PID: 12832)
- file.exe (PID: 12820)
- file.exe (PID: 13200)
- file.exe (PID: 12364)
- file.exe (PID: 14028)
- file.exe (PID: 13948)
- file.exe (PID: 13680)
- g7h64.exe (PID: 10696)
- file.exe (PID: 13192)
- g7h64.exe (PID: 13604)
- file.exe (PID: 13504)
- file.exe (PID: 14776)
- file.exe (PID: 14832)
- g7h64.exe (PID: 18232)
- file.exe (PID: 9440)
- file.exe (PID: 13740)
- file.exe (PID: 13160)
- file.exe (PID: 13760)
- file.exe (PID: 13576)
- file.exe (PID: 14292)
- file.exe (PID: 8800)
- file.exe (PID: 9096)
- g7h64.exe (PID: 12532)
- file.exe (PID: 13076)
- file.exe (PID: 11724)
- file.exe (PID: 14304)
- g7h64.exe (PID: 8828)
- g7h64.exe (PID: 13384)
- file.exe (PID: 14788)
- file.exe (PID: 14180)
- file.exe (PID: 5044)
- g7h64.exe (PID: 12864)
- g7h64.exe (PID: 14816)
- file.exe (PID: 13540)
- file.exe (PID: 12788)
- g7h64.exe (PID: 17240)
- file.exe (PID: 13664)
- file.exe (PID: 11460)
- g7h64.exe (PID: 14928)
- g7h64.exe (PID: 17160)
- file.exe (PID: 9372)
- file.exe (PID: 9068)
- g7h64.exe (PID: 7484)
- file.exe (PID: 13612)
- file.exe (PID: 11884)
- file.exe (PID: 14416)
- file.exe (PID: 13976)
- file.exe (PID: 9516)
- file.exe (PID: 13072)
- file.exe (PID: 13056)
- file.exe (PID: 13044)
- file.exe (PID: 13732)
- g7h64.exe (PID: 14124)
- file.exe (PID: 10632)
- file.exe (PID: 13216)
- file.exe (PID: 13548)
- file.exe (PID: 10916)
- file.exe (PID: 14700)
- g7h64.exe (PID: 9484)
- file.exe (PID: 14324)
- file.exe (PID: 14008)
- file.exe (PID: 13340)
- g7h64.exe (PID: 13096)
- g7h64.exe (PID: 7480)
- file.exe (PID: 9528)
- g7h64.exe (PID: 16576)
- file.exe (PID: 14048)
- file.exe (PID: 13772)
- g7h64.exe (PID: 17672)
- g7h64.exe (PID: 15788)
- g7h64.exe (PID: 16712)
- file.exe (PID: 8252)
- file.exe (PID: 15144)
- file.exe (PID: 9844)
- g7h64.exe (PID: 6168)
- g7h64.exe (PID: 14232)
- g7h64.exe (PID: 9560)
- g7h64.exe (PID: 12808)
- file.exe (PID: 9804)
- file.exe (PID: 14152)
- file.exe (PID: 11560)
- file.exe (PID: 14116)
- g7h64.exe (PID: 17280)
- g7h64.exe (PID: 13140)
- file.exe (PID: 14144)
- file.exe (PID: 9660)
- g7h64.exe (PID: 16704)
- g7h64.exe (PID: 14196)
- g7h64.exe (PID: 16620)
- g7h64.exe (PID: 17636)
- file.exe (PID: 15116)
- file.exe (PID: 13692)
- g7h64.exe (PID: 10592)
- g7h64.exe (PID: 13036)
- g7h64.exe (PID: 12440)
- g7h64.exe (PID: 8640)
- file.exe (PID: 13900)
- file.exe (PID: 10940)
- file.exe (PID: 13876)
- g7h64.exe (PID: 5352)
- file.exe (PID: 14272)
- file.exe (PID: 13788)
- file.exe (PID: 8856)
- file.exe (PID: 9736)
- file.exe (PID: 14168)
- file.exe (PID: 16904)
- file.exe (PID: 18468)
- file.exe (PID: 10904)
- g7h64.exe (PID: 16316)
- file.exe (PID: 15636)
- file.exe (PID: 13252)
- file.exe (PID: 8912)
- file.exe (PID: 15344)
- file.exe (PID: 8196)
- file.exe (PID: 5064)
- file.exe (PID: 2596)
- g7h64.exe (PID: 8636)
- g7h64.exe (PID: 5212)
- g7h64.exe (PID: 18756)
- g7h64.exe (PID: 16968)
- g7h64.exe (PID: 18980)
- file.exe (PID: 13356)
- file.exe (PID: 9872)
- g7h64.exe (PID: 15240)
- g7h64.exe (PID: 18936)
- file.exe (PID: 12980)
- file.exe (PID: 7420)
- g7h64.exe (PID: 9000)
- file.exe (PID: 13884)
- file.exe (PID: 9724)
- file.exe (PID: 12964)
- file.exe (PID: 16456)
- file.exe (PID: 13396)
- file.exe (PID: 18180)
- g7h64.exe (PID: 9744)
- g7h64.exe (PID: 14240)
- g7h64.exe (PID: 19420)
- file.exe (PID: 14768)
- file.exe (PID: 13920)
- g7h64.exe (PID: 16756)
- file.exe (PID: 10580)
- file.exe (PID: 14896)
- file.exe (PID: 13152)
- file.exe (PID: 9536)
- file.exe (PID: 13000)
- file.exe (PID: 15608)
- file.exe (PID: 18828)
- file.exe (PID: 14280)
- g7h64.exe (PID: 13492)
- g7h64.exe (PID: 9756)
- g7h64.exe (PID: 12520)
- g7h64.exe (PID: 10688)
- g7h64.exe (PID: 13368)
- g7h64.exe (PID: 9896)
- g7h64.exe (PID: 16556)
- file.exe (PID: 3396)
- file.exe (PID: 14992)
- file.exe (PID: 14976)
- g7h64.exe (PID: 9952)
- g7h64.exe (PID: 14224)
- file.exe (PID: 13892)
- file.exe (PID: 9696)
- file.exe (PID: 8676)
- file.exe (PID: 16564)
- file.exe (PID: 15356)
- file.exe (PID: 15624)
- g7h64.exe (PID: 17816)
- file.exe (PID: 14424)
- file.exe (PID: 14440)
- g7h64.exe (PID: 9964)
- file.exe (PID: 12372)
- file.exe (PID: 12536)
- file.exe (PID: 9540)
- file.exe (PID: 18184)
- file.exe (PID: 18752)
- file.exe (PID: 13184)
- file.exe (PID: 8576)
- g7h64.exe (PID: 17116)
- g7h64.exe (PID: 20008)
- file.exe (PID: 7428)
- file.exe (PID: 12240)
- file.exe (PID: 14256)
- file.exe (PID: 13176)
- file.exe (PID: 18140)
- g7h64.exe (PID: 812)
- g7h64.exe (PID: 14720)
- g7h64.exe (PID: 7584)
- g7h64.exe (PID: 13296)
- file.exe (PID: 12852)
- file.exe (PID: 10808)
- file.exe (PID: 13128)
- file.exe (PID: 17452)
- file.exe (PID: 8892)
- file.exe (PID: 17036)
- file.exe (PID: 9364)
- file.exe (PID: 9276)
- file.exe (PID: 11624)
- file.exe (PID: 13376)
- g7h64.exe (PID: 21468)
- file.exe (PID: 15012)
- file.exe (PID: 10136)
- file.exe (PID: 18356)
- file.exe (PID: 10956)
- file.exe (PID: 9868)
- file.exe (PID: 16572)
- g7h64.exe (PID: 17600)
- file.exe (PID: 18088)
- g7h64.exe (PID: 12076)
- file.exe (PID: 10648)
- g7h64.exe (PID: 18784)
- g7h64.exe (PID: 12128)
- file.exe (PID: 10872)
- file.exe (PID: 10848)
- file.exe (PID: 14952)
- file.exe (PID: 1672)
- g7h64.exe (PID: 16884)
- file.exe (PID: 10824)
- g7h64.exe (PID: 18000)
- g7h64.exe (PID: 18008)
- g7h64.exe (PID: 13288)
- g7h64.exe (PID: 11932)
- g7h64.exe (PID: 17248)
- file.exe (PID: 10196)
- file.exe (PID: 11716)
- g7h64.exe (PID: 12068)
- file.exe (PID: 13512)
- file.exe (PID: 13460)
- file.exe (PID: 9192)
- file.exe (PID: 14912)
- g7h64.exe (PID: 13148)
- g7h64.exe (PID: 13620)
- g7h64.exe (PID: 20140)
- file.exe (PID: 11940)
- g7h64.exe (PID: 16792)
- g7h64.exe (PID: 15388)
- file.exe (PID: 15220)
- file.exe (PID: 15592)
- g7h64.exe (PID: 8528)
- file.exe (PID: 14852)
- g7h64.exe (PID: 14800)
- g7h64.exe (PID: 13716)
- g7h64.exe (PID: 18024)
- file.exe (PID: 13444)
- g7h64.exe (PID: 15728)
- g7h64.exe (PID: 17640)
- g7h64.exe (PID: 10668)
- file.exe (PID: 10072)
- g7h64.exe (PID: 20812)
- g7h64.exe (PID: 14936)
- file.exe (PID: 10556)
- file.exe (PID: 18480)
- file.exe (PID: 17476)
- file.exe (PID: 14464)
- g7h64.exe (PID: 9196)
- g7h64.exe (PID: 8848)
- file.exe (PID: 18804)
- g7h64.exe (PID: 23248)
- file.exe (PID: 15928)
- file.exe (PID: 10528)
- file.exe (PID: 10876)
- g7h64.exe (PID: 22880)
- file.exe (PID: 9420)
- g7h64.exe (PID: 17508)
- g7h64.exe (PID: 23496)
- file.exe (PID: 15276)
- file.exe (PID: 10800)
- g7h64.exe (PID: 21204)
- g7h64.exe (PID: 15752)
- g7h64.exe (PID: 6960)
- g7h64.exe (PID: 20548)
- g7h64.exe (PID: 17780)
- g7h64.exe (PID: 23276)
- g7h64.exe (PID: 12552)
- g7h64.exe (PID: 16860)
- file.exe (PID: 17484)
- g7h64.exe (PID: 22976)
- file.exe (PID: 7396)
- g7h64.exe (PID: 24324)
- g7h64.exe (PID: 23120)
- g7h64.exe (PID: 24172)
- file.exe (PID: 18532)
- g7h64.exe (PID: 19948)
- g7h64.exe (PID: 21216)
- g7h64.exe (PID: 16732)
- g7h64.exe (PID: 19960)
- g7h64.exe (PID: 23680)
- g7h64.exe (PID: 4212)
- file.exe (PID: 18720)
- g7h64.exe (PID: 19980)
- g7h64.exe (PID: 20156)
- file.exe (PID: 18668)
- file.exe (PID: 17968)
- file.exe (PID: 18732)
- g7h64.exe (PID: 16700)
- g7h64.exe (PID: 20556)
- g7h64.exe (PID: 18748)
- g7h64.exe (PID: 24064)
- g7h64.exe (PID: 16312)
- g7h64.exe (PID: 20144)
- g7h64.exe (PID: 21484)
- g7h64.exe (PID: 12168)
- g7h64.exe (PID: 16764)
- g7h64.exe (PID: 11984)
- g7h64.exe (PID: 23840)
- g7h64.exe (PID: 20332)
- g7h64.exe (PID: 19968)
- g7h64.exe (PID: 25192)
- g7h64.exe (PID: 16628)
- file.exe (PID: 14636)
Reads the BIOS version
- 1r80E4.exe (PID: 4756)
- rapes.exe (PID: 4688)
- 2Z1366.exe (PID: 1672)
- 3F19T.exe (PID: 7476)
- rapes.exe (PID: 7636)
- rapes.exe (PID: 872)
Starts itself from another location
- 1r80E4.exe (PID: 4756)
Reads security settings of Internet Explorer
- 1r80E4.exe (PID: 4756)
- rapes.exe (PID: 4688)
The process executes via Task Scheduler
- rapes.exe (PID: 7636)
- rapes.exe (PID: 872)
- rapes.exe (PID: 4284)
- rapes.exe (PID: 8732)
- rapes.exe (PID: 24072)
There is functionality for enable RDP (YARA)
- rapes.exe (PID: 4688)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- msedge.exe (PID: 8028)
INFO
Create files in a temporary directory
- redline2.exe (PID: 4628)
- g7h64.exe (PID: 3884)
- 1r80E4.exe (PID: 4756)
The sample compiled with english language support
- redline2.exe (PID: 4628)
- file.exe (PID: 6404)
- file.exe (PID: 7932)
- file.exe (PID: 4996)
- file.exe (PID: 6892)
- file.exe (PID: 5544)
- file.exe (PID: 2284)
- file.exe (PID: 2104)
- file.exe (PID: 5324)
- file.exe (PID: 5024)
- file.exe (PID: 3300)
- file.exe (PID: 7480)
- file.exe (PID: 7348)
- file.exe (PID: 2340)
- file.exe (PID: 7520)
- file.exe (PID: 7496)
- file.exe (PID: 8088)
- file.exe (PID: 2108)
- file.exe (PID: 7936)
- file.exe (PID: 7884)
- file.exe (PID: 232)
- file.exe (PID: 5744)
- file.exe (PID: 7284)
- file.exe (PID: 4220)
- file.exe (PID: 6572)
- file.exe (PID: 5548)
- file.exe (PID: 8312)
- file.exe (PID: 8328)
- file.exe (PID: 7540)
- file.exe (PID: 3620)
- file.exe (PID: 8304)
- file.exe (PID: 8320)
- file.exe (PID: 8288)
- file.exe (PID: 9176)
- file.exe (PID: 6300)
- file.exe (PID: 7588)
- file.exe (PID: 6256)
- file.exe (PID: 7940)
- file.exe (PID: 7720)
- file.exe (PID: 6044)
- file.exe (PID: 7988)
- file.exe (PID: 9244)
- file.exe (PID: 6372)
- file.exe (PID: 10544)
- file.exe (PID: 10660)
- file.exe (PID: 7964)
- file.exe (PID: 11116)
- file.exe (PID: 616)
- file.exe (PID: 11500)
- file.exe (PID: 11100)
- file.exe (PID: 10536)
- file.exe (PID: 10272)
- file.exe (PID: 10652)
- file.exe (PID: 11604)
- file.exe (PID: 7364)
- file.exe (PID: 8724)
- file.exe (PID: 968)
- file.exe (PID: 10852)
- file.exe (PID: 11372)
- file.exe (PID: 11520)
- file.exe (PID: 11528)
- file.exe (PID: 11580)
- file.exe (PID: 11616)
- file.exe (PID: 12120)
- file.exe (PID: 8944)
- file.exe (PID: 12208)
- file.exe (PID: 12184)
- file.exe (PID: 8708)
- file.exe (PID: 12100)
- file.exe (PID: 12172)
- file.exe (PID: 12252)
- file.exe (PID: 12108)
- file.exe (PID: 12244)
- file.exe (PID: 11628)
- file.exe (PID: 12052)
- file.exe (PID: 12152)
- file.exe (PID: 12280)
- file.exe (PID: 12036)
- file.exe (PID: 12084)
- file.exe (PID: 12500)
- file.exe (PID: 12512)
- file.exe (PID: 9140)
- file.exe (PID: 9008)
- file.exe (PID: 12524)
- file.exe (PID: 7316)
- file.exe (PID: 12900)
- file.exe (PID: 12856)
- file.exe (PID: 13864)
- file.exe (PID: 13332)
- file.exe (PID: 12608)
- file.exe (PID: 12668)
- file.exe (PID: 13800)
- file.exe (PID: 12832)
- file.exe (PID: 14312)
- file.exe (PID: 13200)
- file.exe (PID: 12364)
- file.exe (PID: 13948)
- file.exe (PID: 14028)
- file.exe (PID: 13680)
- file.exe (PID: 9440)
- file.exe (PID: 14776)
- file.exe (PID: 14832)
- file.exe (PID: 13160)
- file.exe (PID: 14292)
- file.exe (PID: 13504)
- file.exe (PID: 13576)
- file.exe (PID: 8800)
- file.exe (PID: 13760)
- file.exe (PID: 9096)
- file.exe (PID: 13076)
- file.exe (PID: 14304)
- file.exe (PID: 14788)
- file.exe (PID: 14180)
- file.exe (PID: 5044)
- file.exe (PID: 13540)
- file.exe (PID: 11460)
- file.exe (PID: 12788)
- file.exe (PID: 13664)
- file.exe (PID: 11884)
- file.exe (PID: 9372)
- file.exe (PID: 14048)
- file.exe (PID: 9068)
- file.exe (PID: 14416)
- file.exe (PID: 13976)
- file.exe (PID: 9516)
- file.exe (PID: 13072)
- file.exe (PID: 9528)
- file.exe (PID: 13044)
- file.exe (PID: 10632)
- file.exe (PID: 13216)
- file.exe (PID: 13056)
- file.exe (PID: 10916)
- file.exe (PID: 14700)
- file.exe (PID: 13732)
- file.exe (PID: 13548)
- file.exe (PID: 14008)
- file.exe (PID: 13340)
- file.exe (PID: 13772)
- file.exe (PID: 8252)
- file.exe (PID: 15144)
- file.exe (PID: 9844)
- file.exe (PID: 9804)
- file.exe (PID: 11560)
- file.exe (PID: 10940)
- file.exe (PID: 14152)
- file.exe (PID: 14144)
- file.exe (PID: 13692)
- file.exe (PID: 15116)
- file.exe (PID: 13788)
- file.exe (PID: 13900)
- file.exe (PID: 8856)
- file.exe (PID: 14272)
- file.exe (PID: 16904)
- file.exe (PID: 13876)
- file.exe (PID: 9736)
- file.exe (PID: 14168)
- file.exe (PID: 8912)
- file.exe (PID: 18468)
- file.exe (PID: 13252)
- file.exe (PID: 10904)
- file.exe (PID: 2596)
- file.exe (PID: 15344)
- file.exe (PID: 15636)
- file.exe (PID: 5064)
- file.exe (PID: 9872)
- file.exe (PID: 9724)
- file.exe (PID: 7420)
- file.exe (PID: 13356)
- file.exe (PID: 18180)
- file.exe (PID: 16456)
- file.exe (PID: 12964)
- file.exe (PID: 13396)
- file.exe (PID: 14324)
- file.exe (PID: 10580)
- file.exe (PID: 7412)
- file.exe (PID: 14896)
- file.exe (PID: 13920)
- file.exe (PID: 14768)
- file.exe (PID: 9536)
- file.exe (PID: 9420)
- file.exe (PID: 15608)
- file.exe (PID: 18828)
- file.exe (PID: 16564)
- file.exe (PID: 14280)
- file.exe (PID: 13892)
- file.exe (PID: 12372)
- file.exe (PID: 14992)
- file.exe (PID: 14976)
- file.exe (PID: 9696)
- file.exe (PID: 8676)
- file.exe (PID: 15356)
- file.exe (PID: 15624)
- file.exe (PID: 14440)
- file.exe (PID: 18184)
- file.exe (PID: 9540)
- file.exe (PID: 12536)
- file.exe (PID: 13184)
- file.exe (PID: 18752)
- file.exe (PID: 14256)
- file.exe (PID: 8576)
- file.exe (PID: 18140)
- file.exe (PID: 13128)
- file.exe (PID: 12852)
- file.exe (PID: 10808)
- file.exe (PID: 8892)
- file.exe (PID: 9364)
- file.exe (PID: 17036)
- file.exe (PID: 11624)
- file.exe (PID: 9276)
- file.exe (PID: 13376)
- file.exe (PID: 15012)
- file.exe (PID: 10136)
- file.exe (PID: 18356)
- file.exe (PID: 9868)
- file.exe (PID: 18088)
- file.exe (PID: 16572)
- file.exe (PID: 10648)
- file.exe (PID: 10872)
- file.exe (PID: 14952)
- file.exe (PID: 14852)
- file.exe (PID: 10848)
- file.exe (PID: 1672)
- file.exe (PID: 13512)
- file.exe (PID: 11940)
- file.exe (PID: 10196)
- file.exe (PID: 11716)
- file.exe (PID: 9192)
- file.exe (PID: 13460)
- file.exe (PID: 14912)
- file.exe (PID: 15220)
- file.exe (PID: 13444)
- file.exe (PID: 10072)
- file.exe (PID: 10556)
- file.exe (PID: 18480)
- file.exe (PID: 17476)
- file.exe (PID: 14464)
- file.exe (PID: 18804)
- file.exe (PID: 15928)
- file.exe (PID: 10528)
- file.exe (PID: 10876)
- file.exe (PID: 13000)
- file.exe (PID: 15276)
- file.exe (PID: 10800)
- file.exe (PID: 17484)
- file.exe (PID: 7396)
- file.exe (PID: 18532)
- file.exe (PID: 18668)
- file.exe (PID: 18732)
- file.exe (PID: 17968)
- file.exe (PID: 18720)
- file.exe (PID: 14636)
Checks supported languages
- redline2.exe (PID: 4628)
- g7h64.exe (PID: 3884)
- rapes.exe (PID: 4688)
- 2Z1366.exe (PID: 1672)
- 1r80E4.exe (PID: 4756)
- rapes.exe (PID: 7636)
- 3F19T.exe (PID: 7476)
- rapes.exe (PID: 872)
Reads the computer name
- 2Z1366.exe (PID: 1672)
- rapes.exe (PID: 4688)
- 1r80E4.exe (PID: 4756)
- 3F19T.exe (PID: 7476)
Reads the software policy settings
- 2Z1366.exe (PID: 1672)
- slui.exe (PID: 1020)
Process checks computer location settings
- 1r80E4.exe (PID: 4756)
Checks proxy server information
- rapes.exe (PID: 4688)
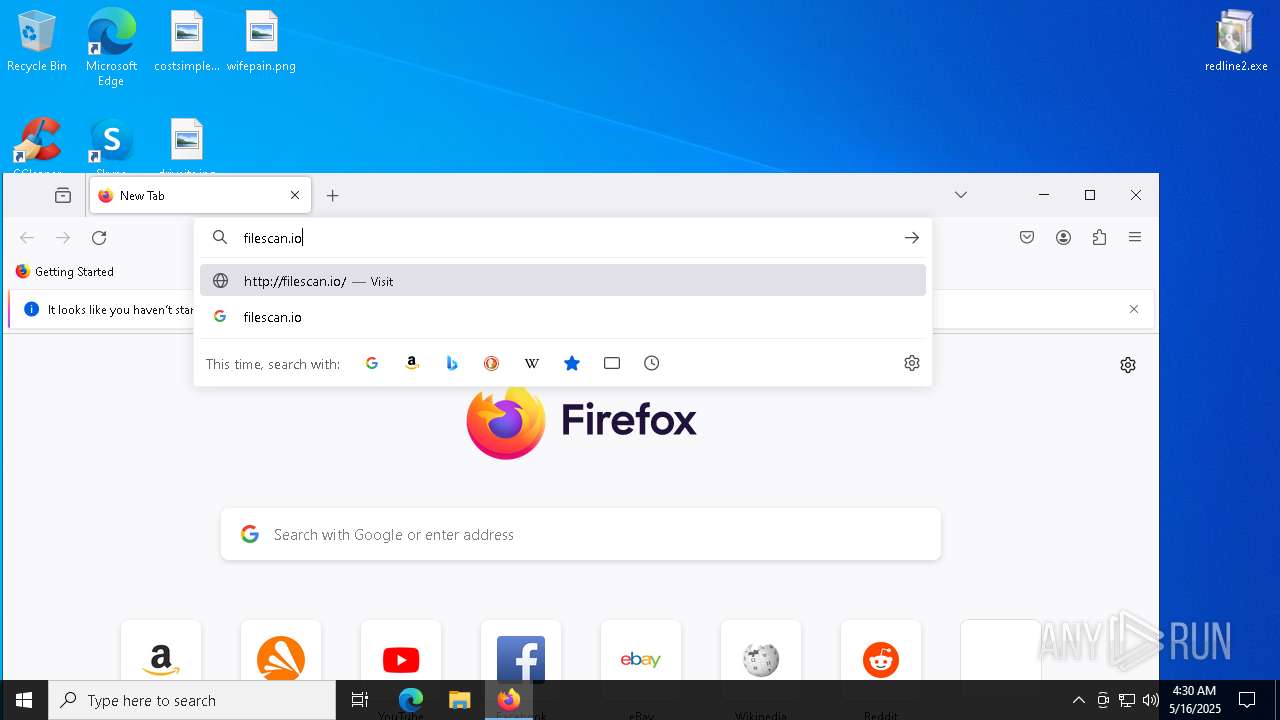
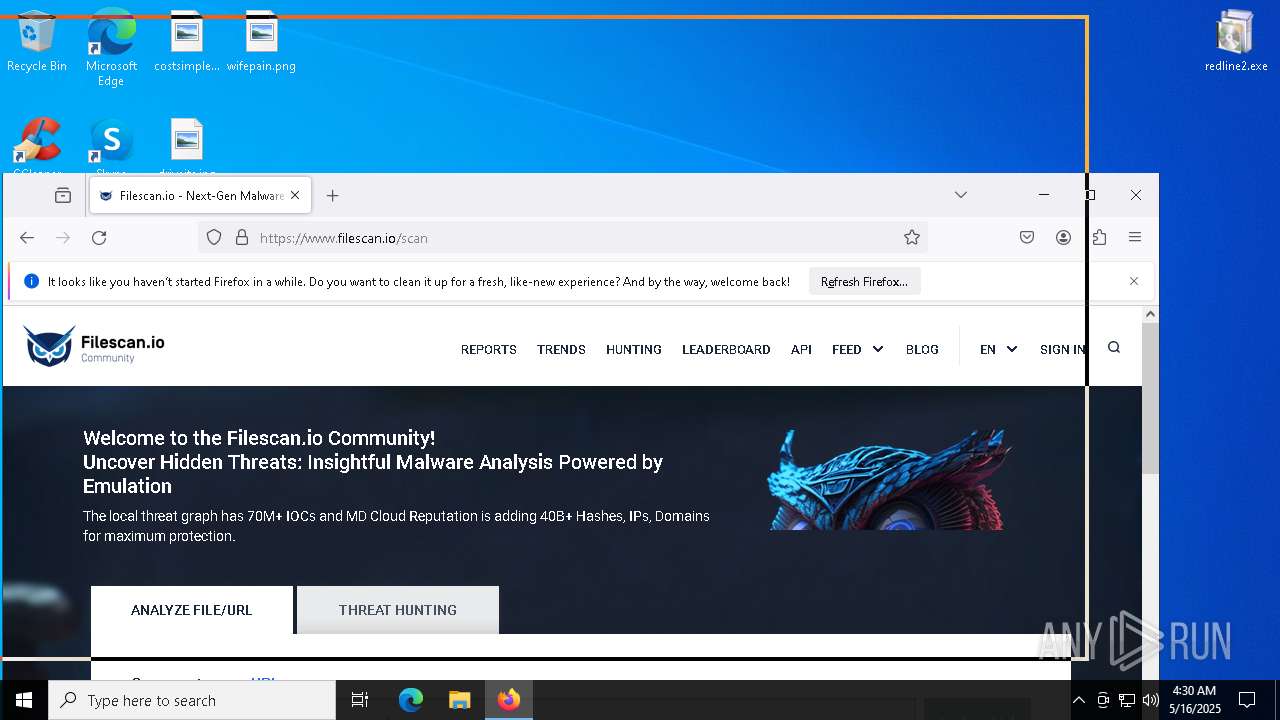
Manual execution by a user
- firefox.exe (PID: 7776)
- firefox.exe (PID: 5720)
- msedge.exe (PID: 7904)
- chrome.exe (PID: 2664)
- file.exe (PID: 6404)
- file.exe (PID: 3012)
- file.exe (PID: 7932)
- file.exe (PID: 6892)
- file.exe (PID: 4996)
- file.exe (PID: 5544)
- file.exe (PID: 2284)
- file.exe (PID: 2104)
- file.exe (PID: 5324)
- file.exe (PID: 3300)
- file.exe (PID: 5024)
- file.exe (PID: 7520)
- file.exe (PID: 2340)
- file.exe (PID: 7348)
- file.exe (PID: 7480)
- file.exe (PID: 3396)
- file.exe (PID: 7936)
- file.exe (PID: 2516)
- file.exe (PID: 7496)
- file.exe (PID: 7884)
- file.exe (PID: 7412)
- file.exe (PID: 3620)
- file.exe (PID: 4012)
- file.exe (PID: 300)
- file.exe (PID: 2108)
- file.exe (PID: 6112)
- file.exe (PID: 4424)
- file.exe (PID: 7216)
- file.exe (PID: 5744)
- file.exe (PID: 5548)
- file.exe (PID: 5188)
- file.exe (PID: 8088)
- file.exe (PID: 7540)
- file.exe (PID: 4692)
- file.exe (PID: 232)
- file.exe (PID: 6572)
- file.exe (PID: 4220)
- file.exe (PID: 6940)
- file.exe (PID: 7284)
- file.exe (PID: 3768)
- file.exe (PID: 8096)
- file.exe (PID: 8000)
- file.exe (PID: 896)
- file.exe (PID: 8288)
- file.exe (PID: 8296)
- file.exe (PID: 8304)
- file.exe (PID: 8312)
- file.exe (PID: 8328)
- file.exe (PID: 8320)
- file.exe (PID: 9176)
- file.exe (PID: 7588)
- file.exe (PID: 7988)
- file.exe (PID: 6256)
- file.exe (PID: 6044)
- file.exe (PID: 6300)
- file.exe (PID: 7720)
- file.exe (PID: 7940)
- file.exe (PID: 6372)
- file.exe (PID: 7964)
- file.exe (PID: 7364)
- file.exe (PID: 616)
- file.exe (PID: 10272)
- file.exe (PID: 9244)
- file.exe (PID: 968)
- file.exe (PID: 10544)
- file.exe (PID: 10536)
- file.exe (PID: 10652)
- file.exe (PID: 10660)
- file.exe (PID: 10852)
- file.exe (PID: 11092)
- file.exe (PID: 11372)
- file.exe (PID: 11116)
- file.exe (PID: 11452)
- file.exe (PID: 11080)
- file.exe (PID: 11100)
- file.exe (PID: 11500)
- file.exe (PID: 11508)
- file.exe (PID: 11520)
- file.exe (PID: 11528)
- file.exe (PID: 11616)
- file.exe (PID: 11628)
- file.exe (PID: 12036)
- file.exe (PID: 11596)
- file.exe (PID: 11580)
- file.exe (PID: 11604)
- file.exe (PID: 12084)
- file.exe (PID: 12052)
- file.exe (PID: 12100)
- file.exe (PID: 12152)
- file.exe (PID: 12108)
- file.exe (PID: 12120)
- file.exe (PID: 12244)
- file.exe (PID: 12252)
- file.exe (PID: 8708)
- file.exe (PID: 8724)
- file.exe (PID: 12172)
- file.exe (PID: 12184)
- file.exe (PID: 12208)
- file.exe (PID: 12280)
- file.exe (PID: 8800)
- file.exe (PID: 2596)
- file.exe (PID: 7316)
- file.exe (PID: 12384)
- file.exe (PID: 12364)
- file.exe (PID: 9008)
- file.exe (PID: 8944)
- file.exe (PID: 9140)
- file.exe (PID: 12392)
- file.exe (PID: 12524)
- file.exe (PID: 12536)
- file.exe (PID: 12564)
- file.exe (PID: 12572)
- file.exe (PID: 12600)
- file.exe (PID: 12608)
- file.exe (PID: 12620)
- file.exe (PID: 12500)
- file.exe (PID: 12512)
- file.exe (PID: 12644)
- file.exe (PID: 12652)
- file.exe (PID: 12812)
- file.exe (PID: 12668)
- file.exe (PID: 12788)
- file.exe (PID: 12676)
- file.exe (PID: 12796)
- file.exe (PID: 12628)
- file.exe (PID: 12832)
- file.exe (PID: 12844)
- file.exe (PID: 12900)
- file.exe (PID: 12856)
- file.exe (PID: 12888)
- file.exe (PID: 12908)
- file.exe (PID: 12820)
- file.exe (PID: 12868)
- file.exe (PID: 13056)
- file.exe (PID: 13064)
- file.exe (PID: 13076)
- file.exe (PID: 13016)
- file.exe (PID: 13028)
- file.exe (PID: 13152)
- file.exe (PID: 13160)
- file.exe (PID: 13164)
- file.exe (PID: 13176)
- file.exe (PID: 13200)
- file.exe (PID: 13216)
- file.exe (PID: 13224)
- file.exe (PID: 10528)
- file.exe (PID: 13320)
- file.exe (PID: 13332)
- file.exe (PID: 13340)
- file.exe (PID: 13192)
- file.exe (PID: 13184)
- file.exe (PID: 13376)
- file.exe (PID: 13360)
- file.exe (PID: 13396)
- file.exe (PID: 13428)
- file.exe (PID: 13444)
- file.exe (PID: 13460)
- file.exe (PID: 13404)
- file.exe (PID: 13416)
- file.exe (PID: 13512)
- file.exe (PID: 13532)
- file.exe (PID: 13552)
- file.exe (PID: 13576)
- file.exe (PID: 13588)
- file.exe (PID: 13504)
- file.exe (PID: 13540)
- file.exe (PID: 13612)
- file.exe (PID: 13692)
- file.exe (PID: 13732)
- file.exe (PID: 13788)
- file.exe (PID: 13740)
- file.exe (PID: 13760)
- file.exe (PID: 13772)
- file.exe (PID: 13800)
- file.exe (PID: 13664)
- file.exe (PID: 13680)
- file.exe (PID: 13864)
- file.exe (PID: 13876)
- file.exe (PID: 13892)
- file.exe (PID: 13900)
- file.exe (PID: 13928)
- file.exe (PID: 13920)
- file.exe (PID: 13948)
- file.exe (PID: 13824)
- file.exe (PID: 13884)
- file.exe (PID: 13964)
- file.exe (PID: 13976)
- file.exe (PID: 14008)
- file.exe (PID: 14028)
- file.exe (PID: 14072)
- file.exe (PID: 14116)
- file.exe (PID: 14132)
- file.exe (PID: 14144)
- file.exe (PID: 14152)
- file.exe (PID: 14040)
- file.exe (PID: 14048)
- file.exe (PID: 14168)
- file.exe (PID: 14180)
- file.exe (PID: 14212)
- file.exe (PID: 14272)
- file.exe (PID: 14256)
- file.exe (PID: 14280)
- file.exe (PID: 14292)
- file.exe (PID: 14304)
- file.exe (PID: 5044)
- file.exe (PID: 11460)
- file.exe (PID: 11564)
- file.exe (PID: 11560)
- file.exe (PID: 11624)
- file.exe (PID: 14312)
- file.exe (PID: 14324)
- file.exe (PID: 12240)
- file.exe (PID: 11884)
- file.exe (PID: 9096)
- file.exe (PID: 11232)
- file.exe (PID: 12372)
- file.exe (PID: 9364)
- file.exe (PID: 9356)
- file.exe (PID: 9372)
- file.exe (PID: 9428)
- file.exe (PID: 9440)
- file.exe (PID: 9516)
- file.exe (PID: 9528)
- file.exe (PID: 9540)
- file.exe (PID: 9420)
- file.exe (PID: 9660)
- file.exe (PID: 9068)
- file.exe (PID: 9672)
- file.exe (PID: 8592)
- file.exe (PID: 9696)
- file.exe (PID: 9708)
- file.exe (PID: 9736)
- file.exe (PID: 8892)
- file.exe (PID: 12852)
- file.exe (PID: 9780)
- file.exe (PID: 9804)
- file.exe (PID: 9724)
- file.exe (PID: 9844)
- file.exe (PID: 9868)
- file.exe (PID: 9828)
- file.exe (PID: 13044)
- file.exe (PID: 13252)
- file.exe (PID: 13356)
- file.exe (PID: 13412)
- file.exe (PID: 14424)
- file.exe (PID: 14440)
- file.exe (PID: 13072)
- file.exe (PID: 14416)
- file.exe (PID: 14464)
- file.exe (PID: 14776)
- file.exe (PID: 14788)
- file.exe (PID: 14448)
- file.exe (PID: 14768)
- file.exe (PID: 14852)
- file.exe (PID: 14896)
- file.exe (PID: 14912)
- file.exe (PID: 14952)
- file.exe (PID: 14832)
- file.exe (PID: 15020)
- file.exe (PID: 15056)
- file.exe (PID: 15012)
- file.exe (PID: 15080)
- file.exe (PID: 15220)
- file.exe (PID: 15116)
- file.exe (PID: 15144)
- file.exe (PID: 15344)
- file.exe (PID: 14992)
- file.exe (PID: 13528)
- file.exe (PID: 10756)
- file.exe (PID: 10704)
- file.exe (PID: 9460)
- file.exe (PID: 5064)
- file.exe (PID: 1672)
- file.exe (PID: 9276)
- file.exe (PID: 10876)
- file.exe (PID: 10904)
- file.exe (PID: 10916)
- file.exe (PID: 10940)
- file.exe (PID: 10956)
- file.exe (PID: 10072)
- file.exe (PID: 10196)
- file.exe (PID: 14976)
- file.exe (PID: 13712)
- file.exe (PID: 11716)
- file.exe (PID: 11724)
- file.exe (PID: 10136)
- file.exe (PID: 10160)
- file.exe (PID: 13548)
- file.exe (PID: 8856)
- file.exe (PID: 9192)
- file.exe (PID: 10556)
- file.exe (PID: 8252)
- file.exe (PID: 14700)
- file.exe (PID: 10632)
- file.exe (PID: 10580)
- file.exe (PID: 10648)
- file.exe (PID: 16564)
- file.exe (PID: 18468)
- file.exe (PID: 15880)
- file.exe (PID: 16904)
- file.exe (PID: 16572)
- file.exe (PID: 15624)
- file.exe (PID: 15608)
- file.exe (PID: 15636)
- file.exe (PID: 15644)
- file.exe (PID: 8912)
- file.exe (PID: 8676)
- file.exe (PID: 15592)
- file.exe (PID: 13000)
- file.exe (PID: 9872)
- file.exe (PID: 12964)
- file.exe (PID: 7428)
- file.exe (PID: 12980)
- file.exe (PID: 8644)
- file.exe (PID: 16456)
- file.exe (PID: 18656)
- file.exe (PID: 9572)
- file.exe (PID: 8196)
- file.exe (PID: 17036)
- file.exe (PID: 18532)
- file.exe (PID: 19156)
- file.exe (PID: 18184)
- file.exe (PID: 18140)
- file.exe (PID: 18180)
- file.exe (PID: 15356)
- file.exe (PID: 16640)
- file.exe (PID: 8576)
- file.exe (PID: 19264)
- file.exe (PID: 17968)
- file.exe (PID: 10348)
- file.exe (PID: 18480)
- file.exe (PID: 15276)
- file.exe (PID: 9536)
- file.exe (PID: 12700)
- file.exe (PID: 12692)
- file.exe (PID: 12712)
- file.exe (PID: 7380)
- file.exe (PID: 9208)
- file.exe (PID: 18292)
- file.exe (PID: 18304)
- file.exe (PID: 17428)
- file.exe (PID: 12744)
- file.exe (PID: 7420)
- file.exe (PID: 12432)
- file.exe (PID: 17484)
- file.exe (PID: 17492)
- file.exe (PID: 17436)
- file.exe (PID: 17444)
- file.exe (PID: 17452)
- file.exe (PID: 17460)
- file.exe (PID: 17476)
- file.exe (PID: 15928)
- file.exe (PID: 11956)
- file.exe (PID: 11948)
- file.exe (PID: 11940)
- file.exe (PID: 18752)
- file.exe (PID: 18668)
- file.exe (PID: 18696)
- file.exe (PID: 7396)
- file.exe (PID: 10808)
- file.exe (PID: 10840)
- file.exe (PID: 10816)
- file.exe (PID: 10824)
- file.exe (PID: 10872)
- file.exe (PID: 10800)
- file.exe (PID: 10848)
- file.exe (PID: 13052)
- file.exe (PID: 18804)
- file.exe (PID: 10860)
- file.exe (PID: 13128)
- file.exe (PID: 18828)
- file.exe (PID: 18720)
- file.exe (PID: 10328)
- file.exe (PID: 18732)
- file.exe (PID: 18356)
- file.exe (PID: 14636)
- file.exe (PID: 18088)
Application launched itself
- firefox.exe (PID: 7776)
- firefox.exe (PID: 7796)
- firefox.exe (PID: 5720)
- msedge.exe (PID: 7904)
- firefox.exe (PID: 5024)
- msedge.exe (PID: 4652)
- chrome.exe (PID: 2664)
Themida protector has been detected
- rapes.exe (PID: 4688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
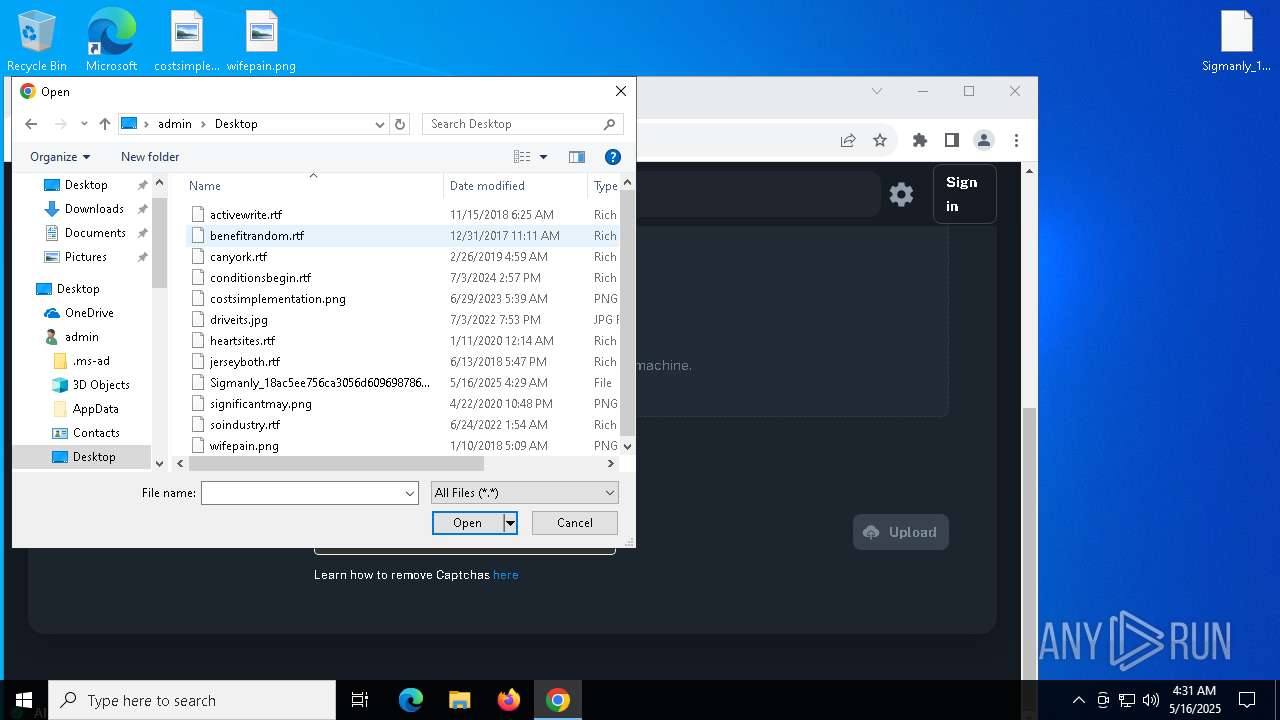
Amadey
(PID) Process(4688) rapes.exe
C2176.113.115.6
URLhttp://176.113.115.6/Ni9kiput/index.php
Version5.21
Options
Drop directorybb556cff4a
Drop namerapes.exe
Strings (125)lv:
msi
Kaspersky Lab
av:
|
#
"
\App
00000422
dm:
Powershell.exe
ProgramData\
ps1
rundll32
http://
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
5.21
dll
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
id:
VideoID
cred.dll|clip.dll|
0000043f
cmd
00000423
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
-executionpolicy remotesigned -File "
2022
------
2016
og:
\0000
CurrentBuild
2019
:::
S-%lu-
" && timeout 1 && del
ProductName
Panda Security
ESET
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/k
+++
?scr=1
Doctor Web
GET
SYSTEM\ControlSet001\Services\BasicDisplay\Video
/quiet
.jpg
vs:
sd:
rundll32.exe
"taskkill /f /im "
pc:
random
=
bb556cff4a
360TotalSecurity
<d>
wb
Content-Type: multipart/form-data; boundary=----
Startup
rapes.exe
Norton
176.113.115.6
&& Exit"
os:
https://
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
2025
Avira
%-lu
zip
POST
"
Content-Type: application/octet-stream
Rem
------
<c>
clip.dll
AVAST Software
\
shell32.dll
" && ren
e3
kernel32.dll
DefaultSettings.XResolution
d1
DefaultSettings.YResolution
r=
cred.dll
--
GetNativeSystemInfo
-%lu
ComputerName
&unit=
Keyboard Layout\Preload
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
ar:
Sophos
%USERPROFILE%
exe
e1
e2
st=s
Programs
0123456789
/Ni9kiput/index.php
un:
rb
bi:
abcdefghijklmnopqrstuvwxyz0123456789-_
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
cmd /C RMDIR /s/q
Bitdefender
-unicode-
AVG
WinDefender
&&
shutdown -s -t 0
Comodo
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
Main
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:24 22:49:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 25600 |
| InitializedDataSize: | 6454784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a60 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.17763.1 |
| ProductVersionNumber: | 11.0.17763.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.17763.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.17763.1 |
Total processes
1 174
Monitored processes
1 034
Malicious processes
444
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc88acdc40,0x7ffc88acdc4c,0x7ffc88acdc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 232 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | C:\Users\admin\AppData\Local\Temp\IXP208.TMP\g7h64.exe | C:\Users\admin\AppData\Local\Temp\IXP208.TMP\g7h64.exe | — | file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\2Z1366.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\2Z1366.exe | g7h64.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 300 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4236 -childID 2 -isForBrowser -prefsHandle 4300 -prefMapHandle 2732 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {99eecbf5-6d8a-4854-a7f2-8c91cfa8fc82} 7796 "\\.\pipe\gecko-crash-server-pipe.7796" 22b8f6c5bd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 616 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | C:\Users\admin\AppData\Local\Temp\IXP65A3.tmp\g7h64.exe | C:\Users\admin\AppData\Local\Temp\IXP65A3.tmp\g7h64.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3172 --field-trial-handle=1972,i,5754144898451523069,3380617734235286348,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 800 | C:\Users\admin\AppData\Local\Temp\IXP133.TMP\2Z1366.exe | C:\Users\admin\AppData\Local\Temp\IXP133.TMP\2Z1366.exe | — | g7h64.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
70 832
Read events
70 721
Write events
105
Delete events
6
Modification events
| (PID) Process: | (4688) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4688) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4688) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7796) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5024) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7904) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7904) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7904) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7904) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7904) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D0306089CF932F00 | |||
Executable files
906
Suspicious files
827
Text files
163
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7796 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4756 | 1r80E4.exe | C:\Windows\Tasks\rapes.job | binary | |
MD5:C1078DCEDDD17FB489C4DA4BA1A60AB4 | SHA256:20BF88CB113C7FC53BD3BED5D3AA2F4670B6F92FF2BB1957B07343D6772F30A9 | |||
| 7796 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 4628 | redline2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\g7h64.exe | executable | |
MD5:CB1B5CBE9E13F3FE4E7EDB1954B074C0 | SHA256:2901C7B24AB0294CC12782630E66CCB35FEFC505DBE3658FE68C1324CD485EDC | |||
| 3884 | g7h64.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\2Z1366.exe | executable | |
MD5:D186C703E85FA3F4DFEEAAA48B1A83C7 | SHA256:0FAC62C7BB069712650BDF37777E91E080A9D011EC241EE25F601ECB862B2247 | |||
| 4628 | redline2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\3F19T.exe | executable | |
MD5:0D40B55E1F552DB81C2B8400E1F25558 | SHA256:0B921636568EE3E1F8CE71FF9C931DA5675089BA796B65A6B212440425D63C8C | |||
| 3884 | g7h64.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\1r80E4.exe | executable | |
MD5:4AFAE939B4028412A49667D82BFD12E6 | SHA256:678FAA5C47726719F8483E7B74DFE48BCA64BA8202C1160C4AD097BA413461A8 | |||
| 7796 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7796 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7796 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
75
TCP/UDP connections
302
DNS requests
471
Threats
205
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7796 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7796 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7796 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7796 | firefox.exe | POST | 200 | 216.58.206.67:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
7796 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7796 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7796 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1672 | 2Z1366.exe | 104.102.49.106:443 | steamcommunity.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4688 | rapes.exe | 176.113.115.6:80 | — | Red Bytes LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
pepperiop.digital |
| unknown |
jrxsafer.top |
| unknown |
plantainklj.run |
| unknown |
puerrogfh.live |
| unknown |
quavabvc.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (jrxsafer .top) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (pepperiop .digital) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (jrxsafer .top) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (ywmedici .top) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (advennture .top) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (plantainklj .run) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (rambutanvcx .run) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (quavabvc .top) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (puerrogfh .live) |