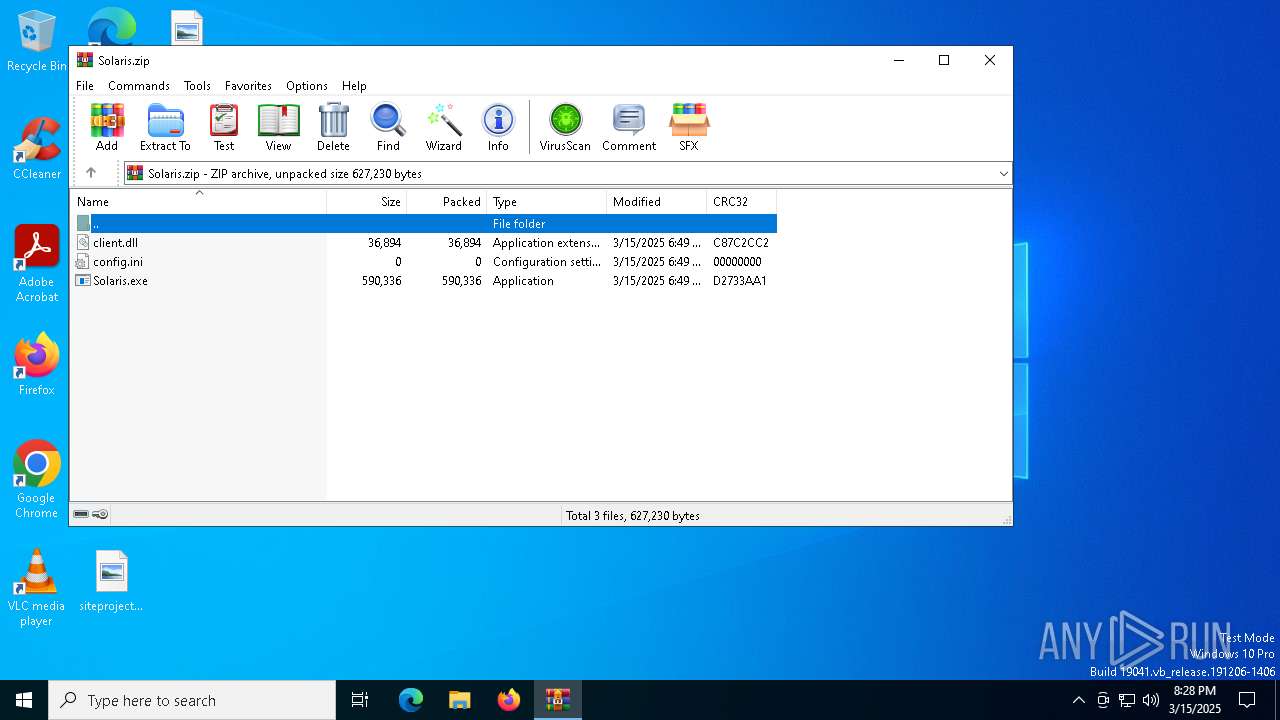
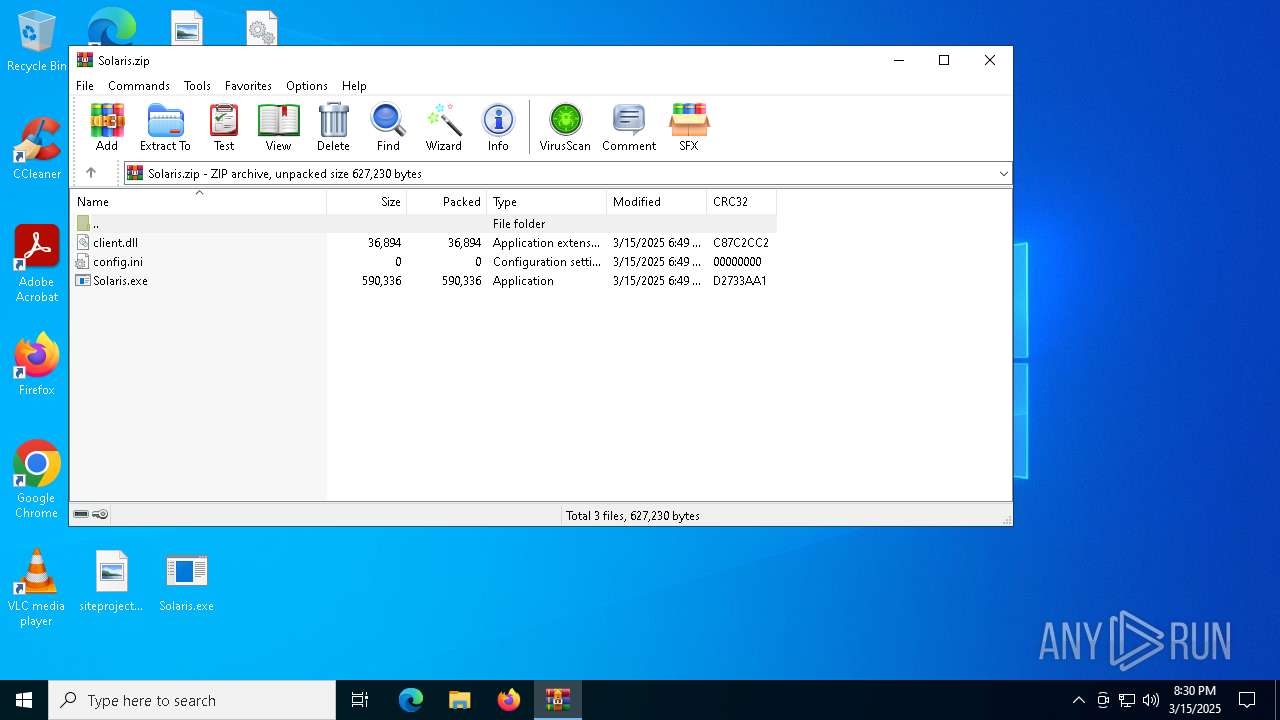
| File name: | Solaris.zip |
| Full analysis: | https://app.any.run/tasks/dc895a57-2c3b-4536-bf67-a3141e4bb06e |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 15, 2025, 20:28:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 24014AC73891E8E62B5B04CD58D84EF1 |
| SHA1: | 3FF8047BFDAAE0DDCE4D7FFF76DD23E1E89EC21D |
| SHA256: | 183E966BA1AF89D0F24A302FF327C46DAB10B6BDE24D692D8CF7610AE2055711 |
| SSDEEP: | 24576:N1tbHtPJ9f4FOcrb0IvFV38k2/g4HfJAJlmqO3O3:NfbHtPJ9f48crb0IvFV38k2/g4/Jolmc |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7728)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 7912)
LUMMA mutex has been found
- MSBuild.exe (PID: 7912)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 7912)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 7912)
Multiple wallet extension IDs have been found
- MSBuild.exe (PID: 7912)
Searches for installed software
- MSBuild.exe (PID: 7912)
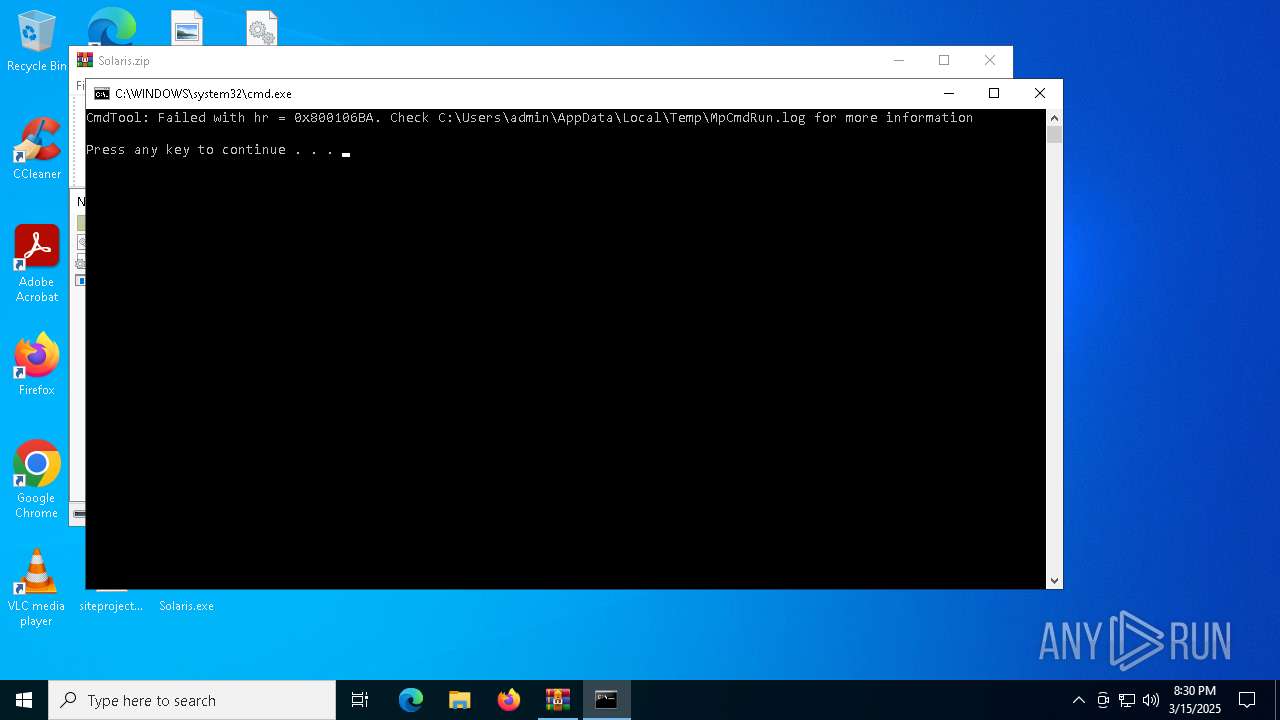
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7728)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7728)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7728)
INFO
Reads the computer name
- MSBuild.exe (PID: 7912)
- MpCmdRun.exe (PID: 2284)
Manual execution by a user
- Solaris.exe (PID: 7848)
Checks supported languages
- Solaris.exe (PID: 7848)
- MSBuild.exe (PID: 7912)
- MpCmdRun.exe (PID: 2284)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 7912)
Reads the software policy settings
- MSBuild.exe (PID: 7912)
- slui.exe (PID: 4784)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7728)
Create files in a temporary directory
- MpCmdRun.exe (PID: 2284)
Checks proxy server information
- slui.exe (PID: 4784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:03:15 18:49:50 |
| ZipCRC: | 0xc87c2cc2 |
| ZipCompressedSize: | 36894 |
| ZipUncompressedSize: | 36894 |
| ZipFileName: | client.dll |
Total processes
128
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
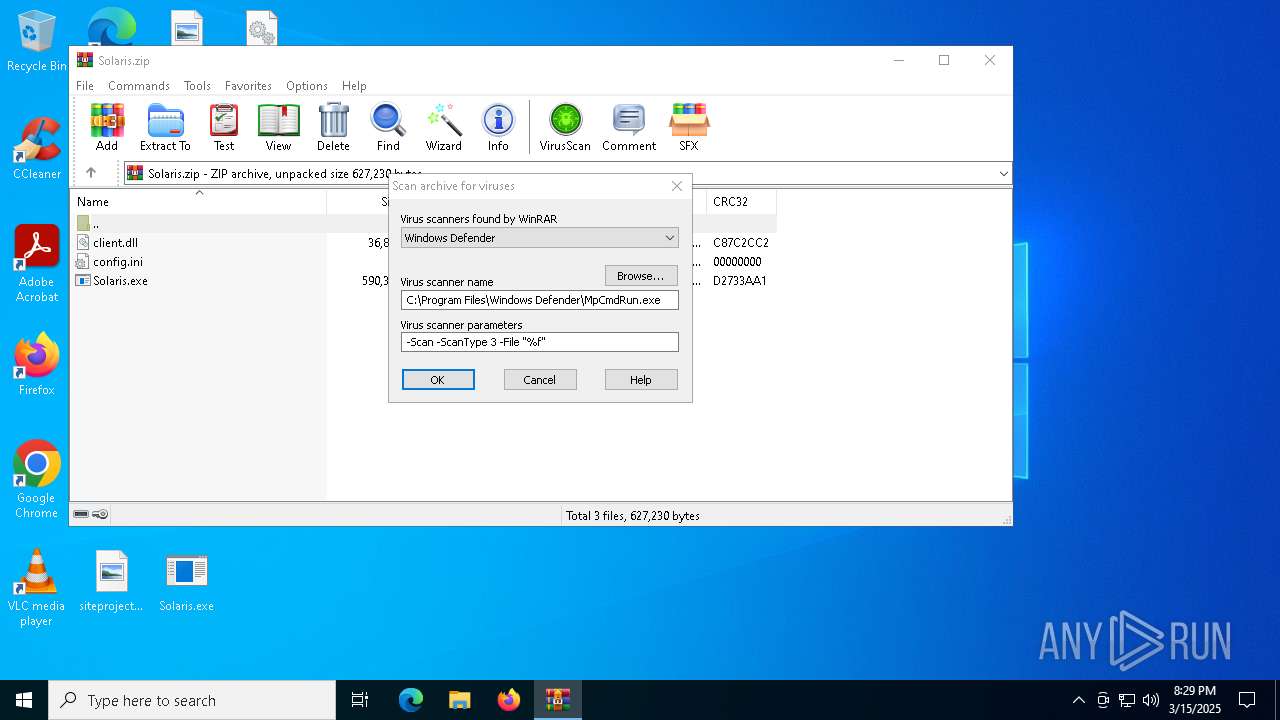
| 2284 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR7728.42296" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4784 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR7728.42296\Rar$Scan101646.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7728 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Solaris.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7848 | "C:\Users\admin\Desktop\Solaris.exe" | C:\Users\admin\Desktop\Solaris.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Solaris.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7912 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | Solaris.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
8 459
Read events
8 450
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Solaris.zip | |||
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7728) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
1
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7728 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7728.42296\Rar$Scan101646.bat | text | |
MD5:91BB0142EC3530EC6648FD4F4C5115D7 | SHA256:DB012E93DF9AA7979434EAE41BA0BAB631C831ADF4D7C70E0507804B7F7F0C00 | |||
| 7728 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7728.42296\Solaris.zip\client.dll | text | |
MD5:702348A3919A13F056AB52A8085C5B5B | SHA256:8C5F289D8817F1FF725DCCA44B93A0A9BEBDBB933750EBE81E91C33C561C875C | |||
| 7728 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7728.42296\Solaris.zip\Solaris.exe | executable | |
MD5:E8A106AAC815C1AB3C61ECFB6EB4C1BE | SHA256:2A5318F97E44EABD95CAF1F188207912FF86283B2F0B895BECE994FF9D980160 | |||
| 2284 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:53F7F09C54974ECF8737E0794F737ED1 | SHA256:C1301381606093165D6EC01EB32E7005BAEC7A451EB9F83AAE900D3B0B616090 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
25
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 188.114.96.3:443 | https://loadoutle.life/kpLsOAm | unknown | binary | 60 b | unknown |
— | — | POST | 200 | 188.114.97.3:443 | https://loadoutle.life/kpLsOAm | unknown | binary | 60 b | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 200 | 188.114.96.3:443 | https://loadoutle.life/kpLsOAm | unknown | binary | 10.2 Kb | unknown |
— | — | POST | 200 | 188.114.96.3:443 | https://loadoutle.life/kpLsOAm | unknown | binary | 60 b | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 200 | 188.114.97.3:443 | https://loadoutle.life/kpLsOAm | unknown | binary | 60 b | unknown |
— | — | POST | 200 | 188.114.97.3:443 | https://loadoutle.life/kpLsOAm | unknown | binary | 60 b | unknown |
— | — | POST | 200 | 188.114.96.3:443 | https://loadoutle.life/kpLsOAm | unknown | binary | 13.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
7912 | MSBuild.exe | 188.114.96.3:443 | loadoutle.life | CLOUDFLARENET | NL | unknown |
7412 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4784 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| whitelisted |
loadoutle.life |
| unknown |
activation-v2.sls.microsoft.com |
| unknown |