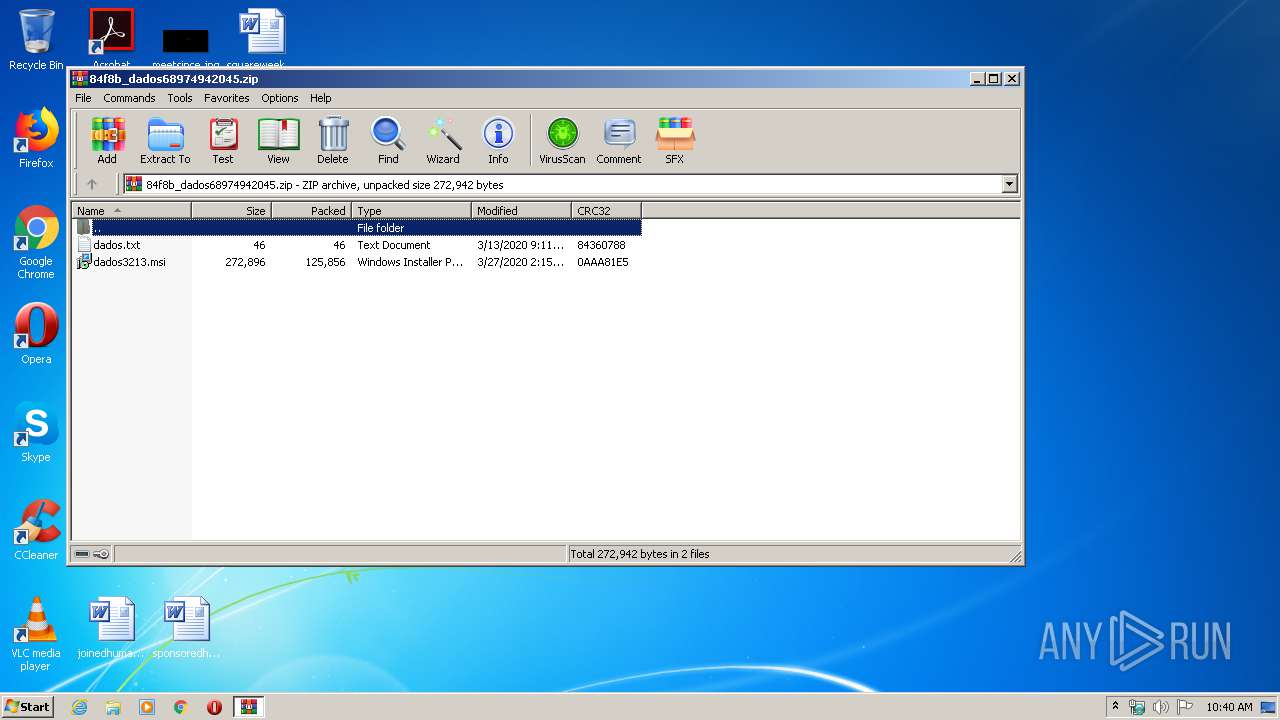
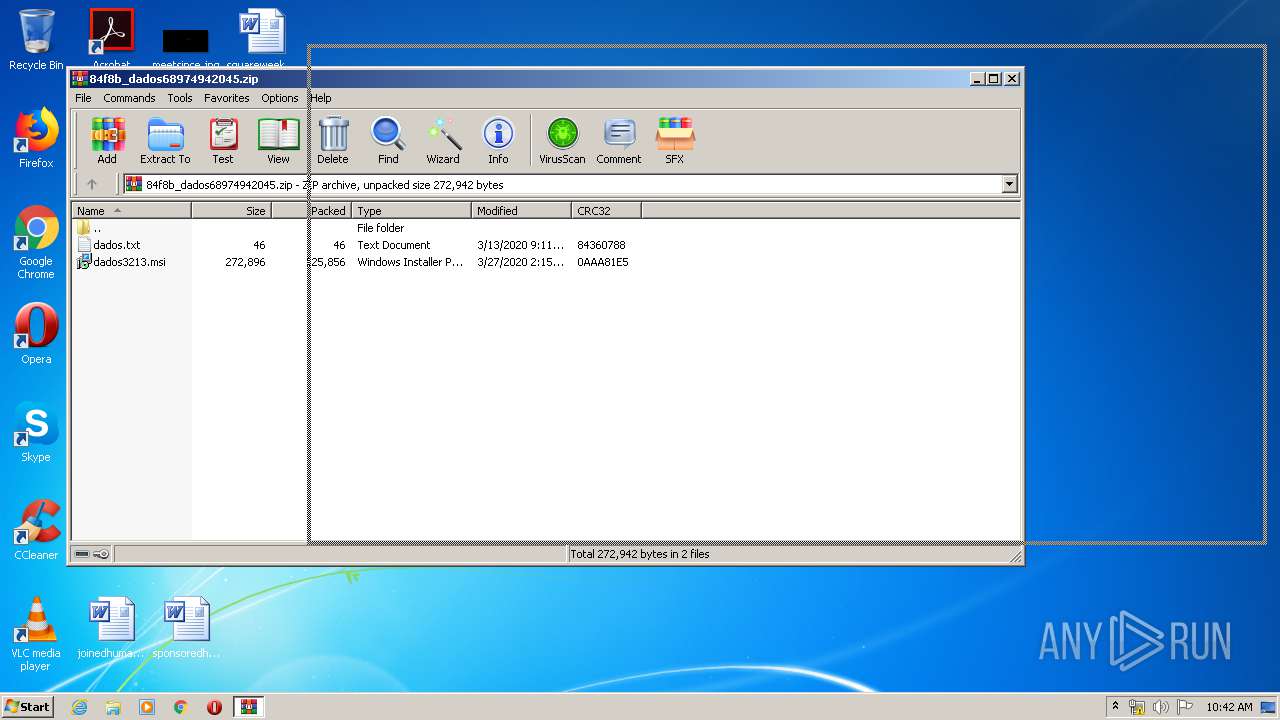
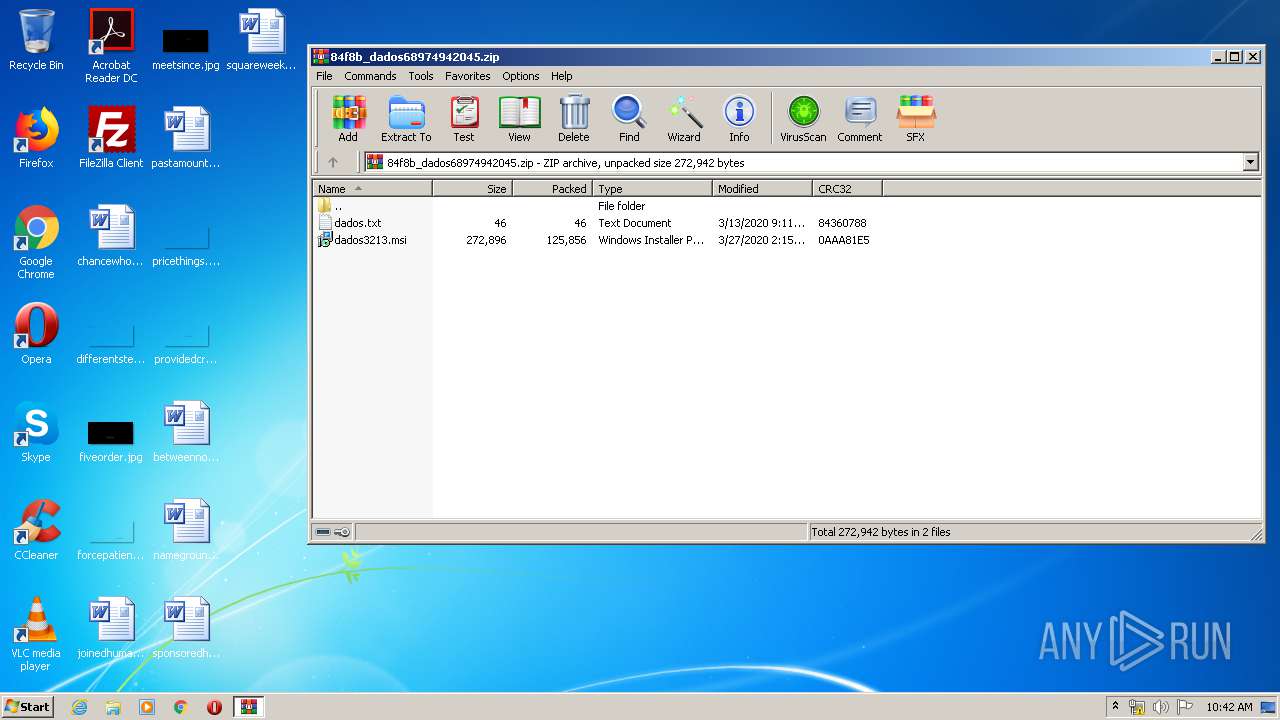
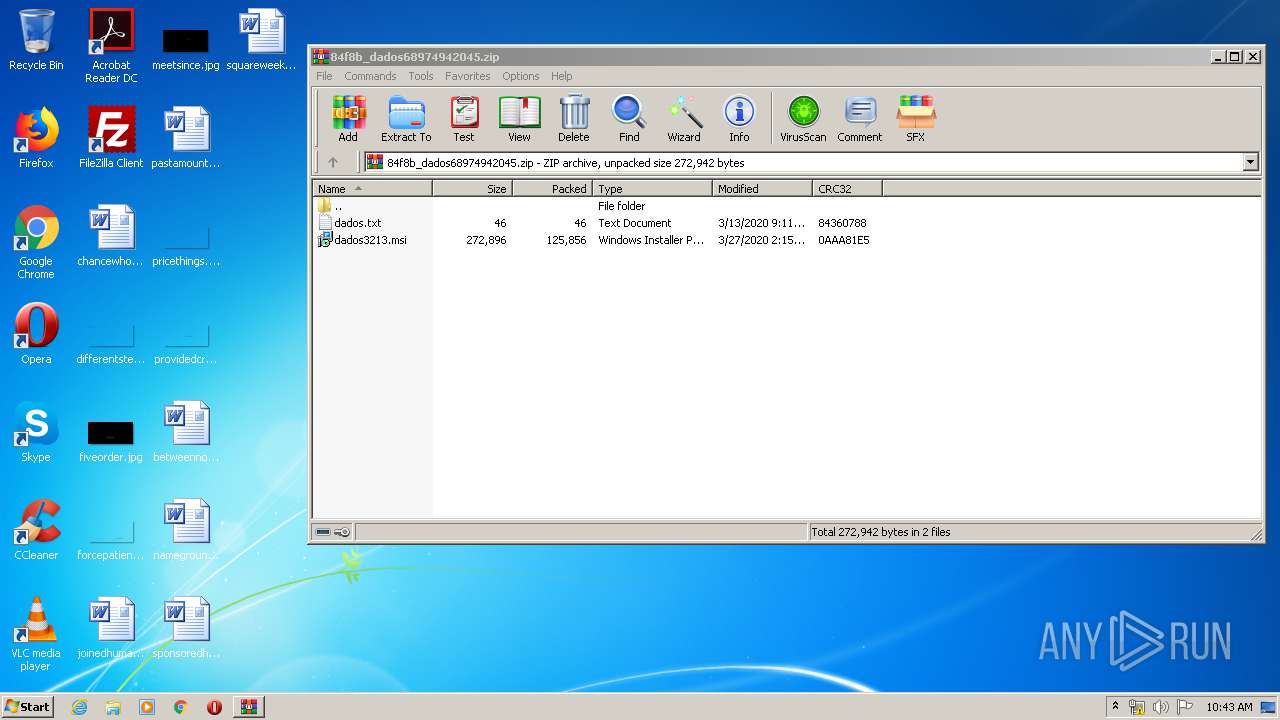
| File name: | 84f8b_dados68974942045.zip |
| Full analysis: | https://app.any.run/tasks/eee8f297-dcc0-40ac-a546-465fd10fafb5 |
| Verdict: | Malicious activity |
| Threats: | Metamorfo is a trojan malware family that has been active since 2018. It remains a top threat, focusing on stealing victims’ financial information, including banking credentials and other data. The malware is known for targeting users in Brazil. |
| Analysis date: | March 31, 2020, 09:40:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
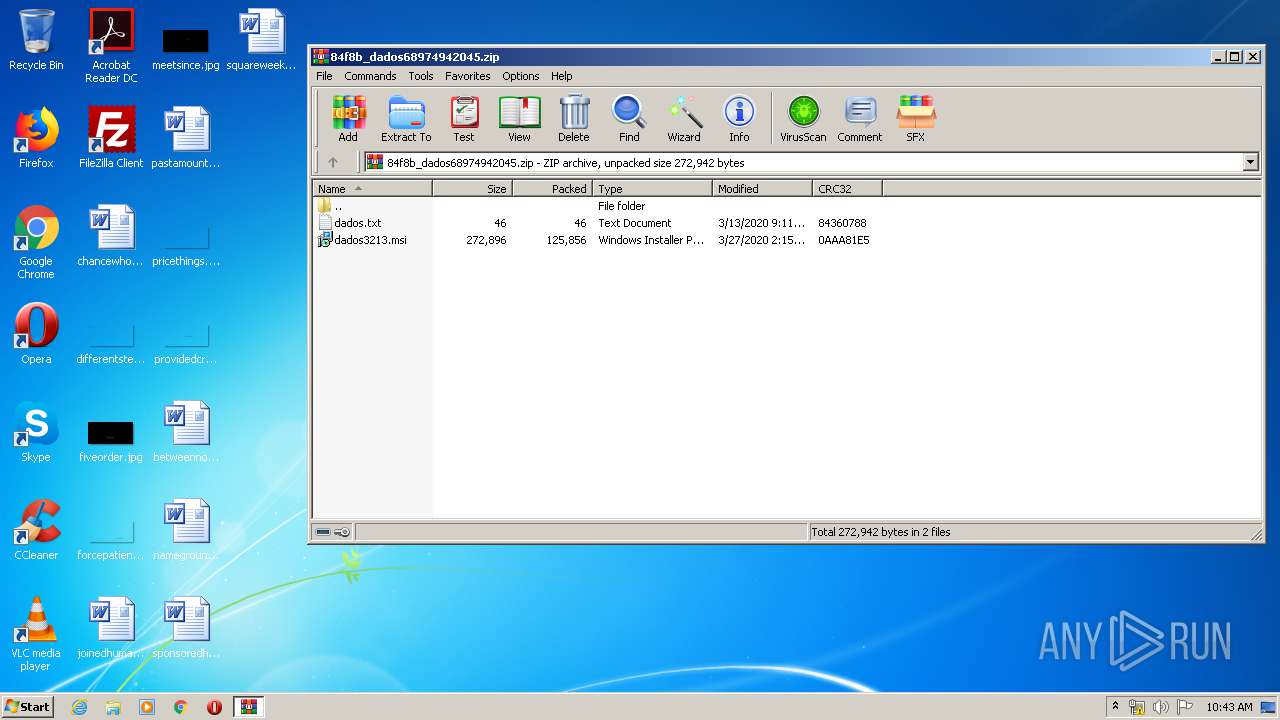
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 84F8BB1AD60607C54EB6AD0C9BAA0404 |
| SHA1: | D15A559494EB253671C33BB5613CE7134C30B442 |
| SHA256: | 17EC2AC96AFF11AFCCBC5E2654EE47788C5D01A26BE231C88EC23447601A79A4 |
| SSDEEP: | 3072:BXi47x7Emf2s7r3a9oSbUY1ZI4SsSwPawtYvUA7y5NUSb79:BXi4j2gpSbUY1Q3wPRtZsAeIp |
MALICIOUS
Application was dropped or rewritten from another process
- NPIE.EXE (PID: 3860)
Connects to CnC server
- NPIE.EXE (PID: 3860)
Changes the autorun value in the registry
- NPIE.EXE (PID: 3860)
- reg.exe (PID: 2860)
Loads dropped or rewritten executable
- NPIE.EXE (PID: 3860)
- SearchProtocolHost.exe (PID: 3548)
METAMORFO was detected
- NPIE.EXE (PID: 3860)
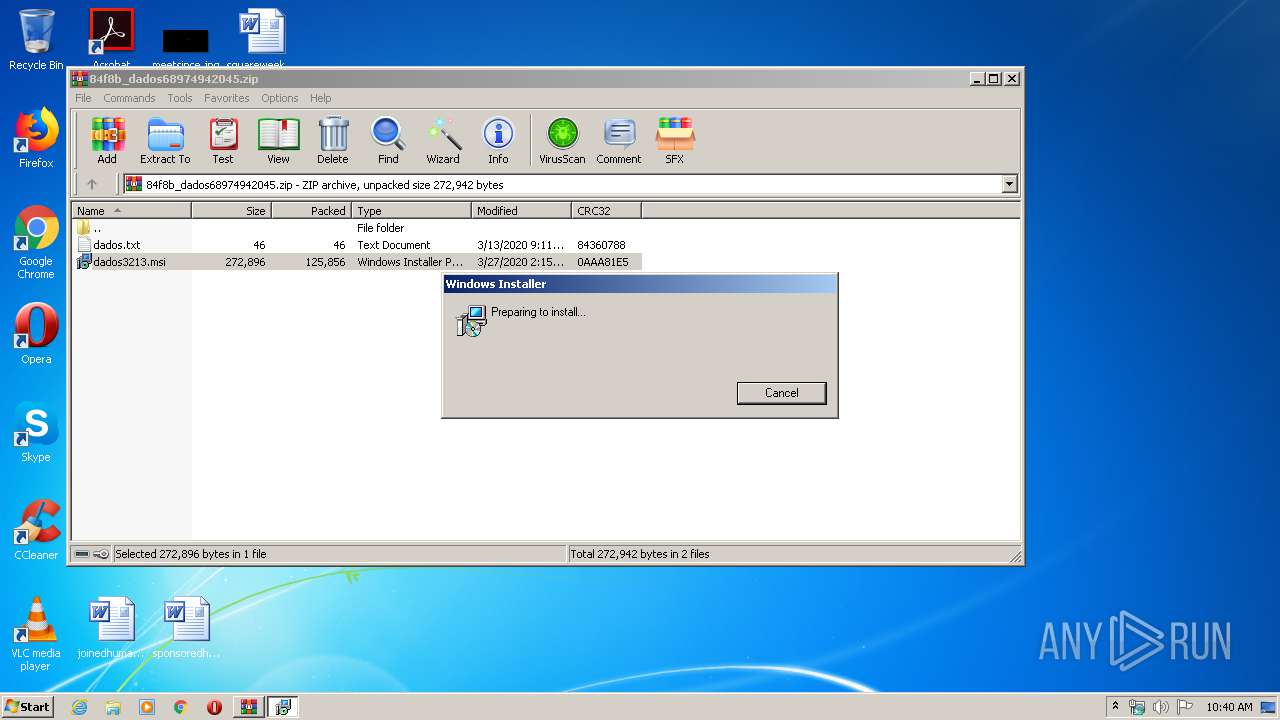
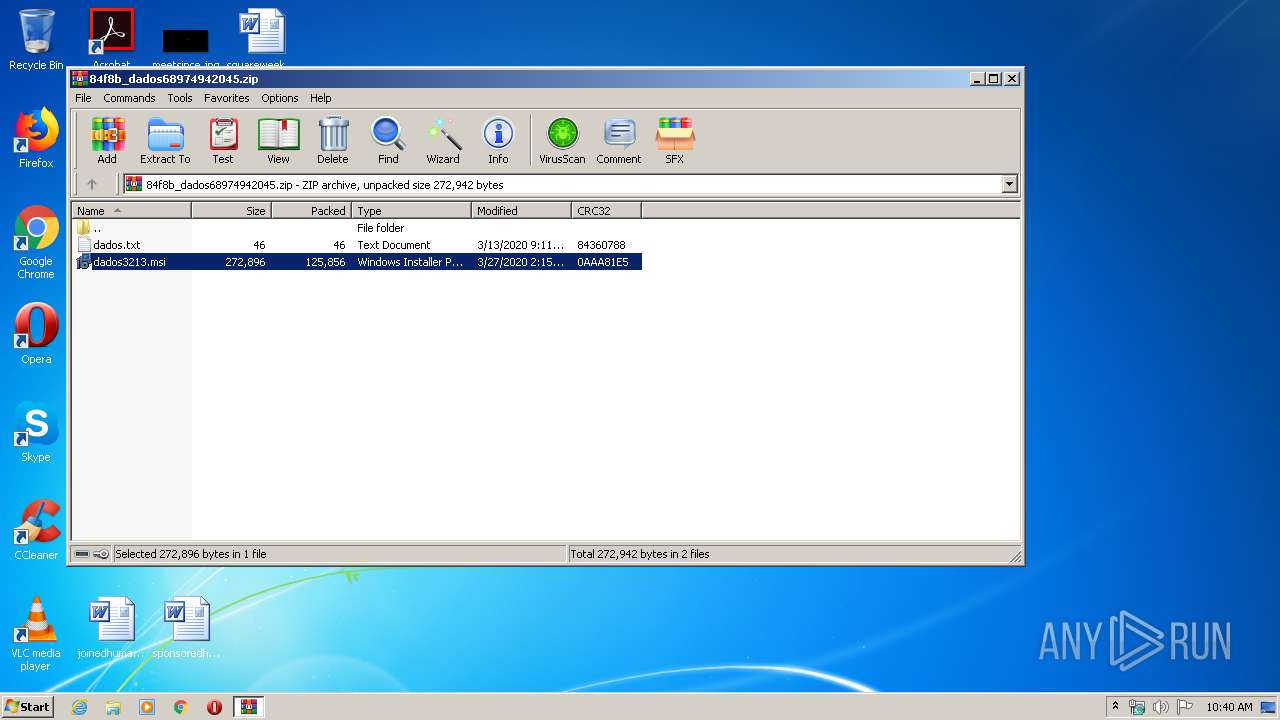
SUSPICIOUS
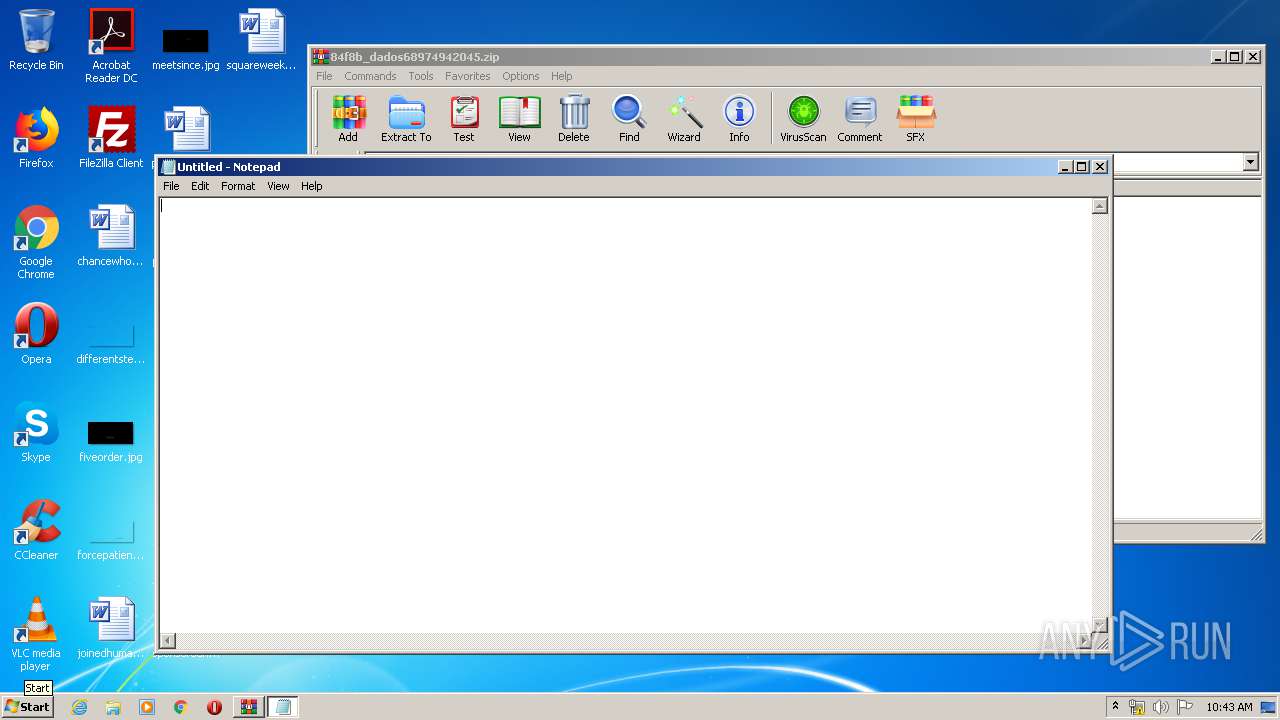
Starts Microsoft Installer
- WinRAR.exe (PID: 2956)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2956)
- MsiExec.exe (PID: 3324)
- msiexec.exe (PID: 1712)
Reads Internet Cache Settings
- MsiExec.exe (PID: 3324)
Reads Environment values
- NPIE.EXE (PID: 3860)
Uses REG.EXE to modify Windows registry
- MsiExec.exe (PID: 3324)
INFO
Application launched itself
- msiexec.exe (PID: 1712)
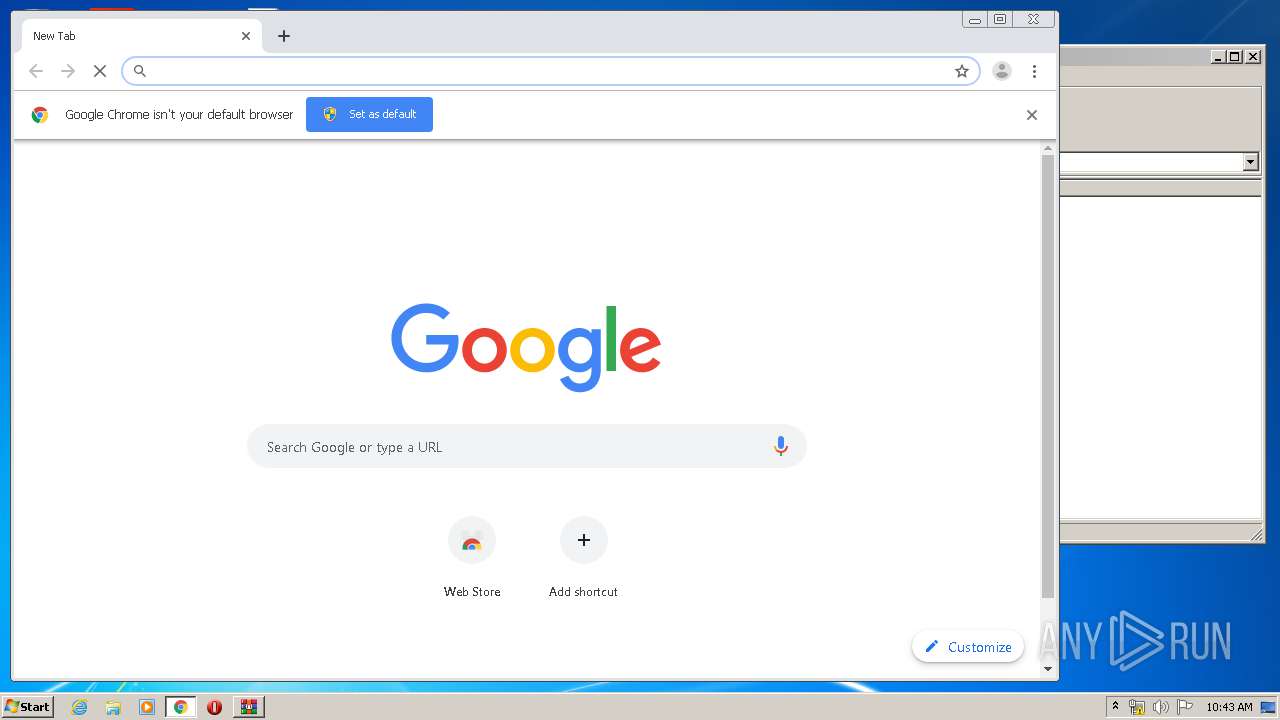
- chrome.exe (PID: 1016)
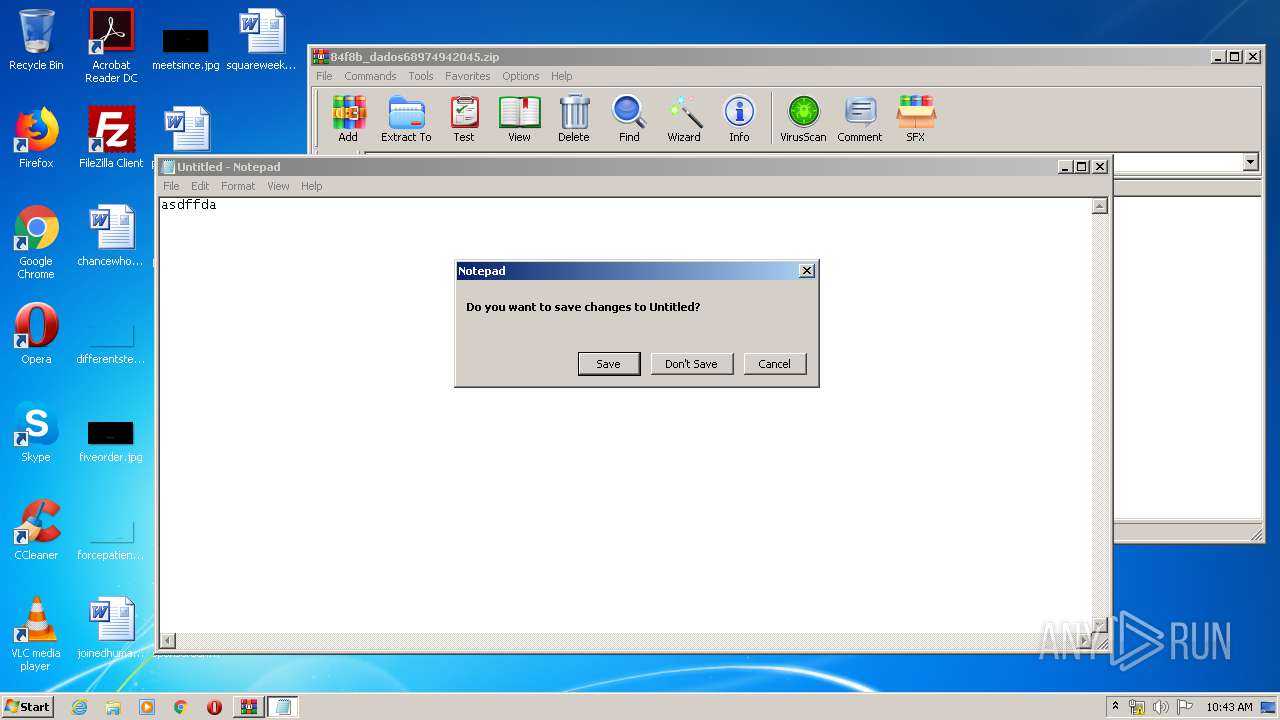
Manual execution by user
- chrome.exe (PID: 1016)
- notepad.exe (PID: 880)
Reads the hosts file
- chrome.exe (PID: 2144)
- chrome.exe (PID: 1016)
Reads settings of System Certificates
- chrome.exe (PID: 2144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:03:26 23:15:18 |
| ZipCRC: | 0x0aaa81e5 |
| ZipCompressedSize: | 125856 |
| ZipUncompressedSize: | 272896 |
| ZipFileName: | dados3213.msi |
Total processes
54
Monitored processes
20
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,12984254752713025087,1943802331145468718,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4477631998404979259 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Windows\system32\notepad.exe" | C:\Windows\system32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d50a9d0,0x6d50a9e0,0x6d50a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12984254752713025087,1943802331145468718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9516435437890803456 --mojo-platform-channel-handle=3676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12984254752713025087,1943802331145468718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3742360811564050249 --mojo-platform-channel-handle=3304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12984254752713025087,1943802331145468718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15274855470390273818 --mojo-platform-channel-handle=1656 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2388 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,12984254752713025087,1943802331145468718,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14840638175037167162 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 988
Read events
1 892
Write events
81
Delete events
15
Modification events
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\84f8b_dados68974942045.zip | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msimsg.dll,-34 |
Value: Windows Installer Package | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
31
Text files
83
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1712 | msiexec.exe | C:\Windows\Installer\MSI8E4E.tmp | — | |
MD5:— | SHA256:— | |||
| 1712 | msiexec.exe | C:\Windows\Installer\MSI8EAD.tmp | — | |
MD5:— | SHA256:— | |||
| 1712 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF6EBE22DC933AB958.TMP | — | |
MD5:— | SHA256:— | |||
| 3324 | MsiExec.exe | C:\Users\admin\Documents\NPIE\Avira.OE.NativeCore.dll | — | |
MD5:— | SHA256:— | |||
| 2956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2956.45241\dados.txt | text | |
MD5:— | SHA256:— | |||
| 3324 | MsiExec.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\video2[1].tar | compressed | |
MD5:— | SHA256:— | |||
| 1712 | msiexec.exe | C:\Windows\Installer\a68da2.msi | executable | |
MD5:— | SHA256:— | |||
| 1712 | msiexec.exe | C:\Windows\Installer\a68da4.ipi | binary | |
MD5:— | SHA256:— | |||
| 3324 | MsiExec.exe | C:\Users\admin\Documents\NPIE\Celuer um Gri (1).png | image | |
MD5:964E31FA1C594025C66950F6B9C58A5D | SHA256:369AA5F4AF0E964A93820DBE3A4DB9F7D0C0024F941E68D593D66E9DEEDBDE4B | |||
| 3324 | MsiExec.exe | C:\Users\admin\Documents\NPIE\Birinb (2).ico | image | |
MD5:16D7B3E48B2051D1935A11514AB72FB1 | SHA256:F1BA32CCD49B26CE88B2708A11075C866A02D6DD8B767C8F4446FB037B1E315C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
15
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3860 | NPIE.EXE | POST | — | 5.57.226.202:80 | http://novamultimidea.webcindario.com/covid19/ | ES | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2144 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3324 | MsiExec.exe | 187.17.111.35:80 | moggiempilhadeiras.com.br | Universo Online S.A. | BR | malicious |
2144 | chrome.exe | 172.217.23.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2144 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2144 | chrome.exe | 172.217.22.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2144 | chrome.exe | 172.217.21.206:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2144 | chrome.exe | 172.217.23.163:443 | www.google.it | Google Inc. | US | whitelisted |
2144 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2144 | chrome.exe | 172.217.21.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2144 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
moggiempilhadeiras.com.br |
| malicious |
novamultimidea.webcindario.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3860 | NPIE.EXE | Potentially Bad Traffic | ET INFO Suspicious POST Request with Possible COVID-19 URI M1 |
1 ETPRO signatures available at the full report