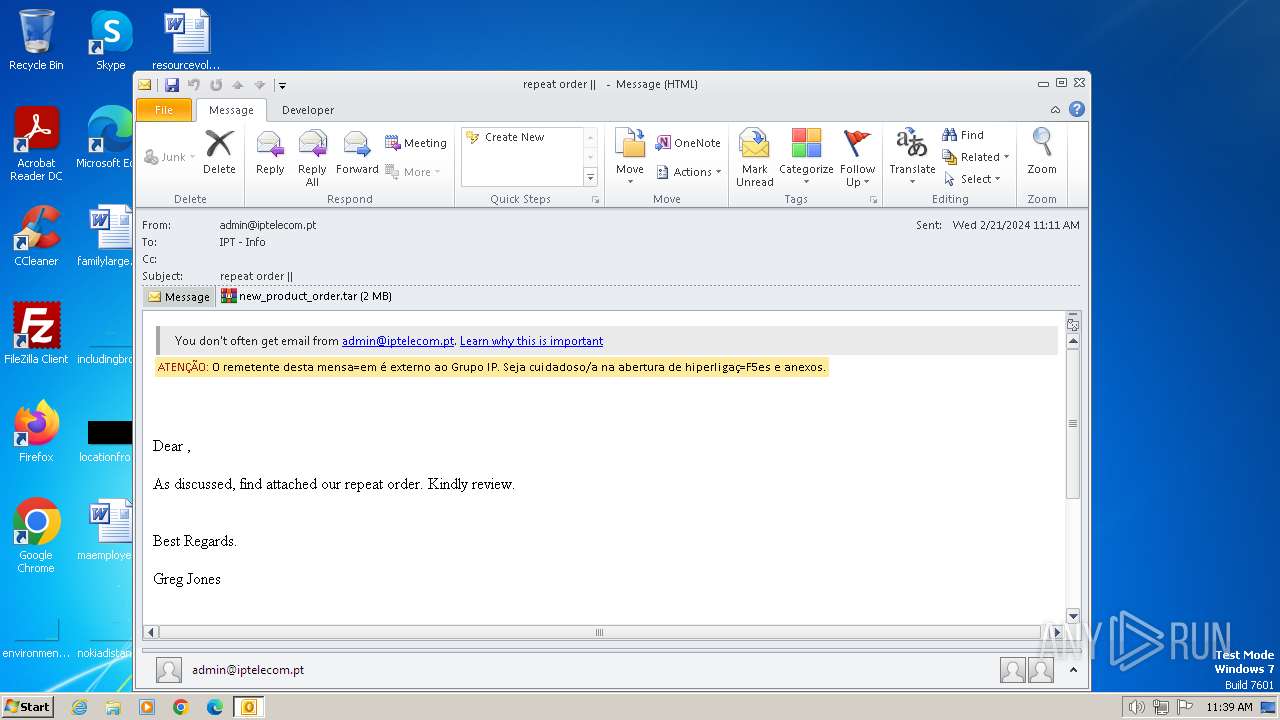
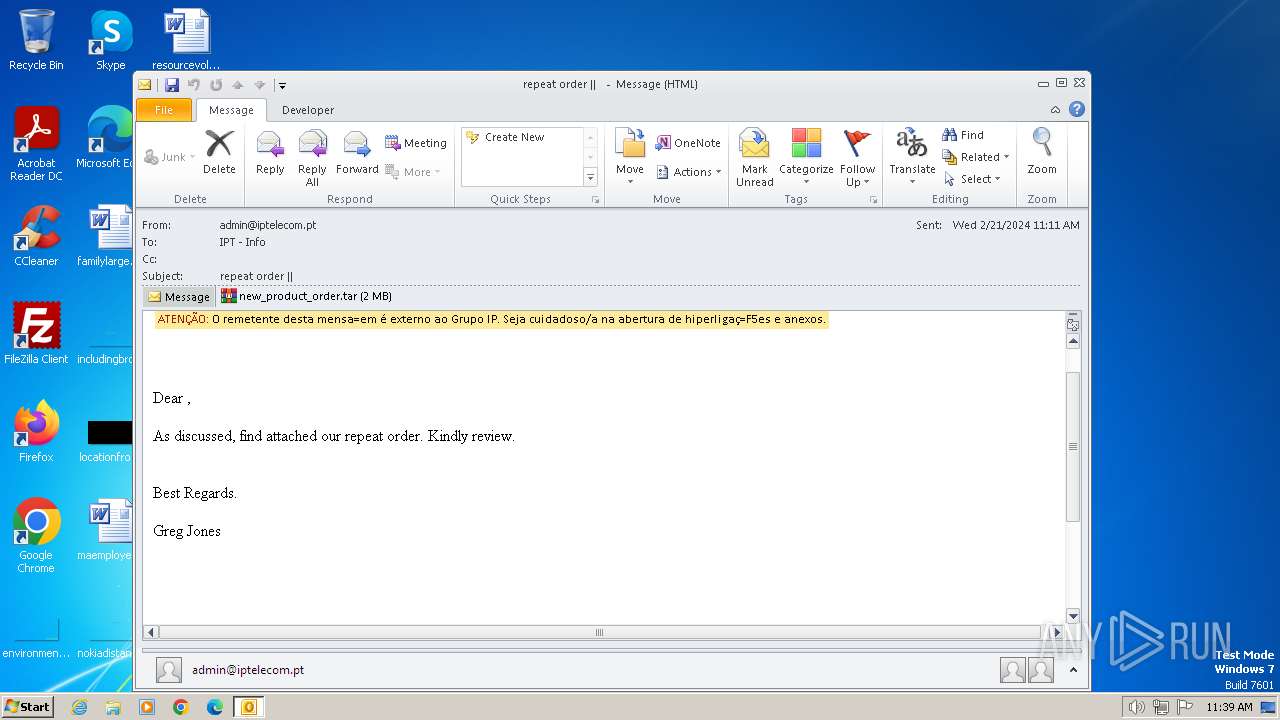
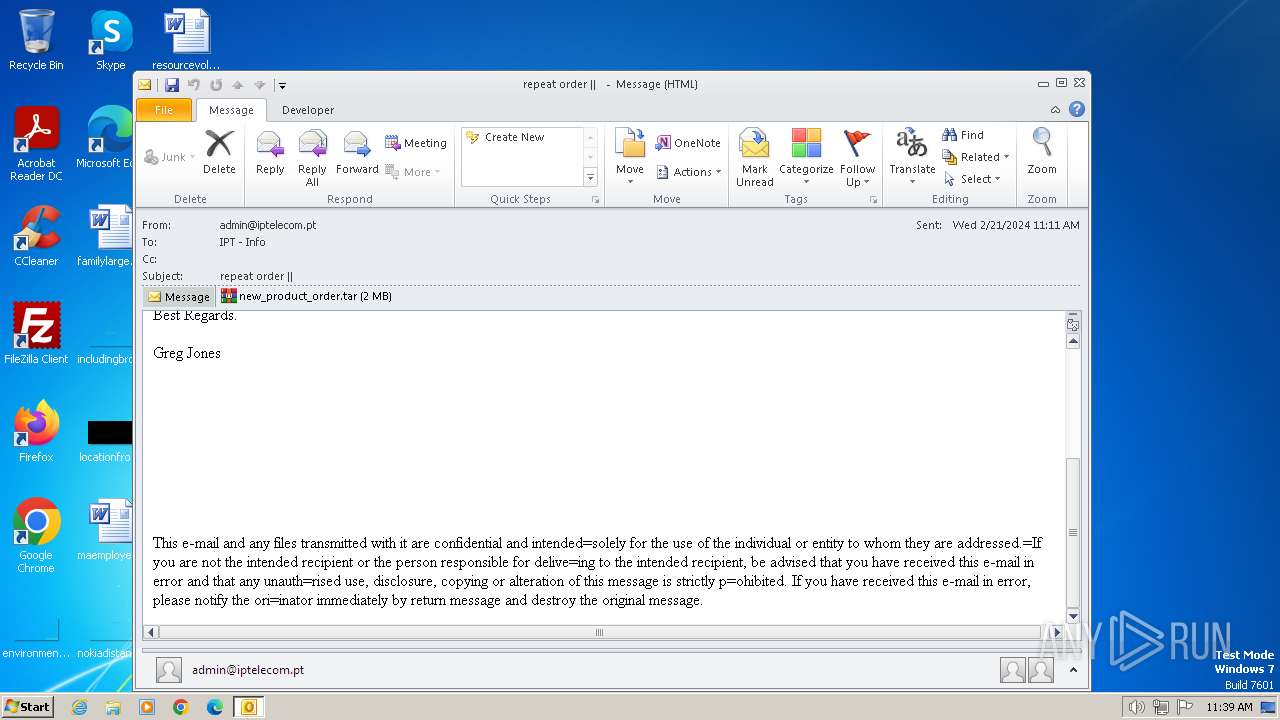
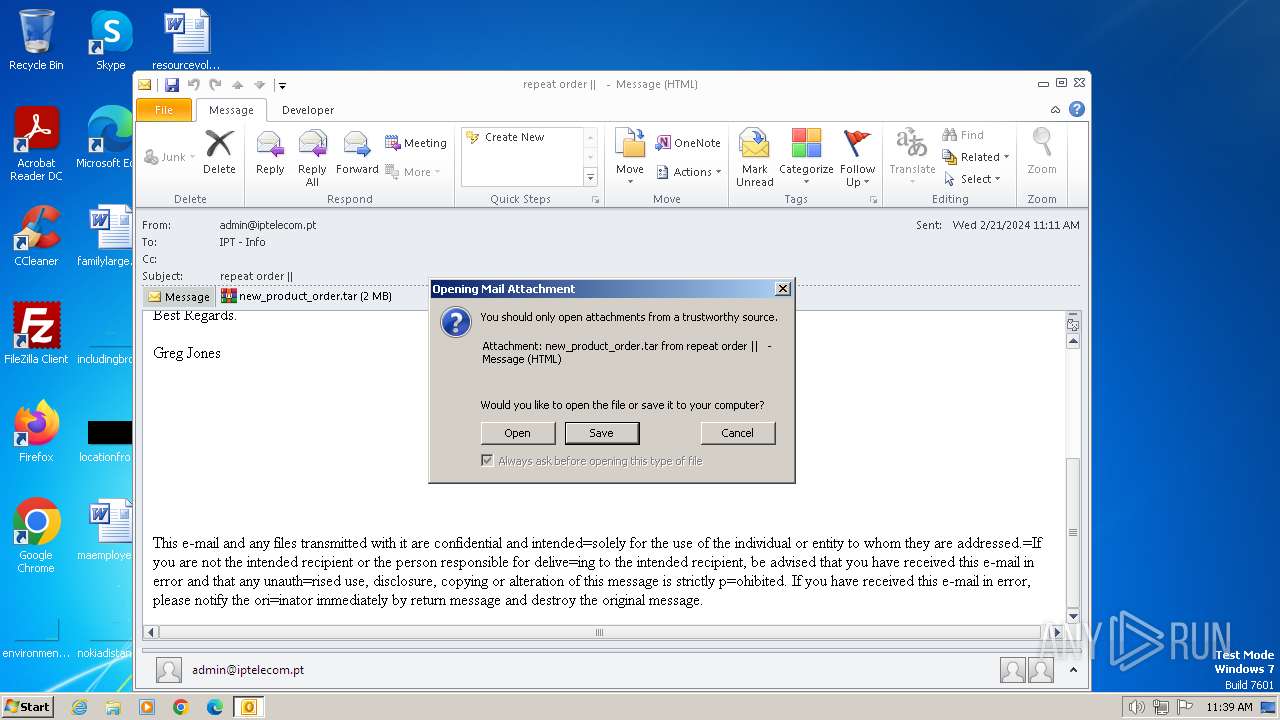
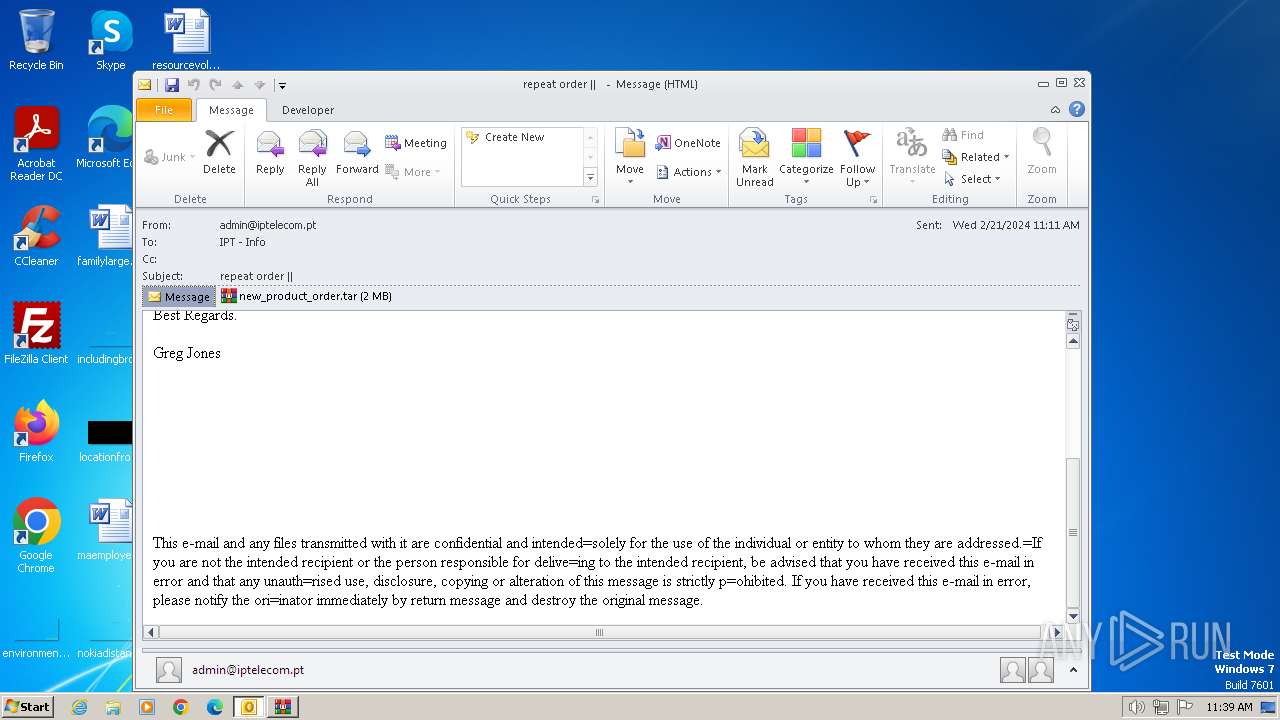
| File name: | repeat order __.eml |
| Full analysis: | https://app.any.run/tasks/cae059f0-73ce-4a26-bd29-5374d1c93dbb |
| Verdict: | Malicious activity |
| Threats: | DBatLoader is a loader malware used for distributing payloads of different types, including WarzoneRAT and Formbook. It is employed in multi-stage attacks that usually start with a phishing email carrying a malicious attachment. |
| Analysis date: | February 21, 2024, 11:39:03 |
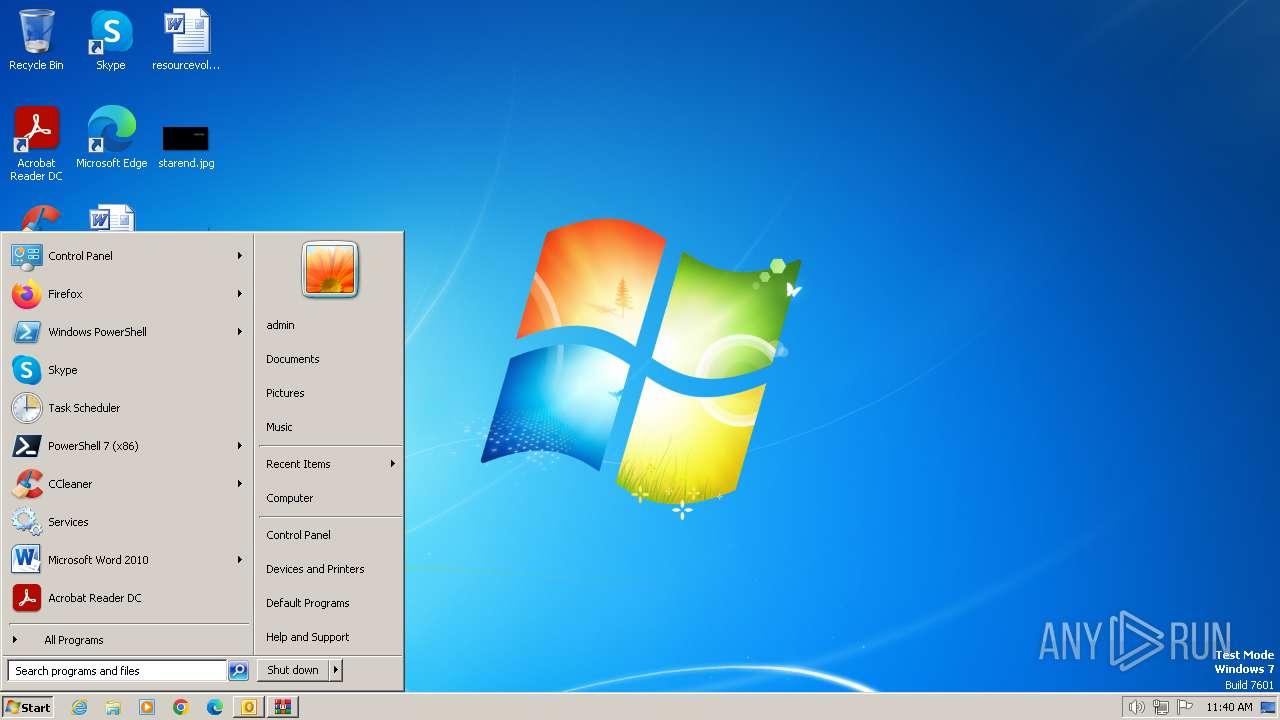
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text |
| MD5: | 7BABE535E3D576BF772B55147798967D |
| SHA1: | 8CFA090D810FCCAF4DB76FB59BA226B49D962A7A |
| SHA256: | 1731EB577BE4D027671EDBDF5F80DE6D8A36D8820825D20227E46004B2C521F3 |
| SSDEEP: | 49152:OwRNPe1zHIIRfxyJSq+jqJHK1jcZemTp9YISy7iIMMgK:F |
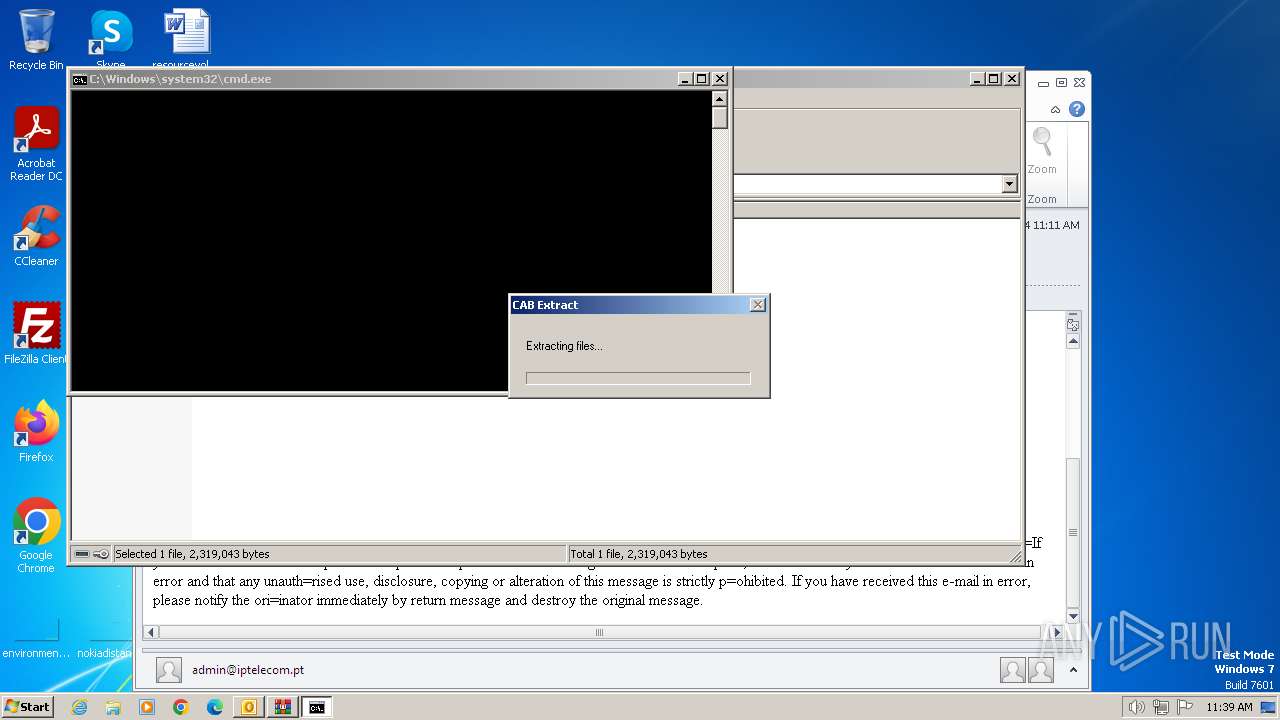
MALICIOUS
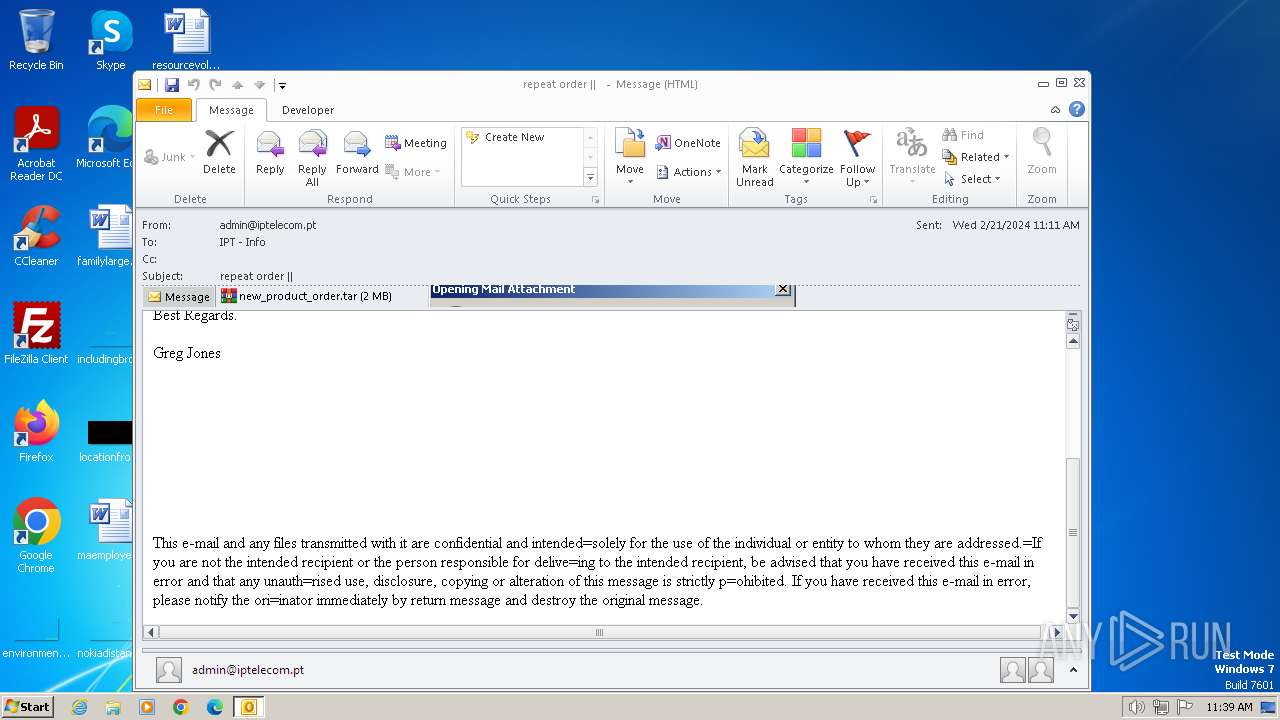
Unusual execution from MS Outlook
- OUTLOOK.EXE (PID: 2472)
DBATLOADER has been detected (YARA)
- x.exe (PID: 1496)
Drops the executable file immediately after the start
- x.exe (PID: 1496)
Changes the autorun value in the registry
- x.exe (PID: 1496)
FORMBOOK has been detected (YARA)
- dwm.exe (PID: 2788)
Actions looks like stealing of personal data
- dwm.exe (PID: 2788)
SUSPICIOUS
Reads security settings of Internet Explorer
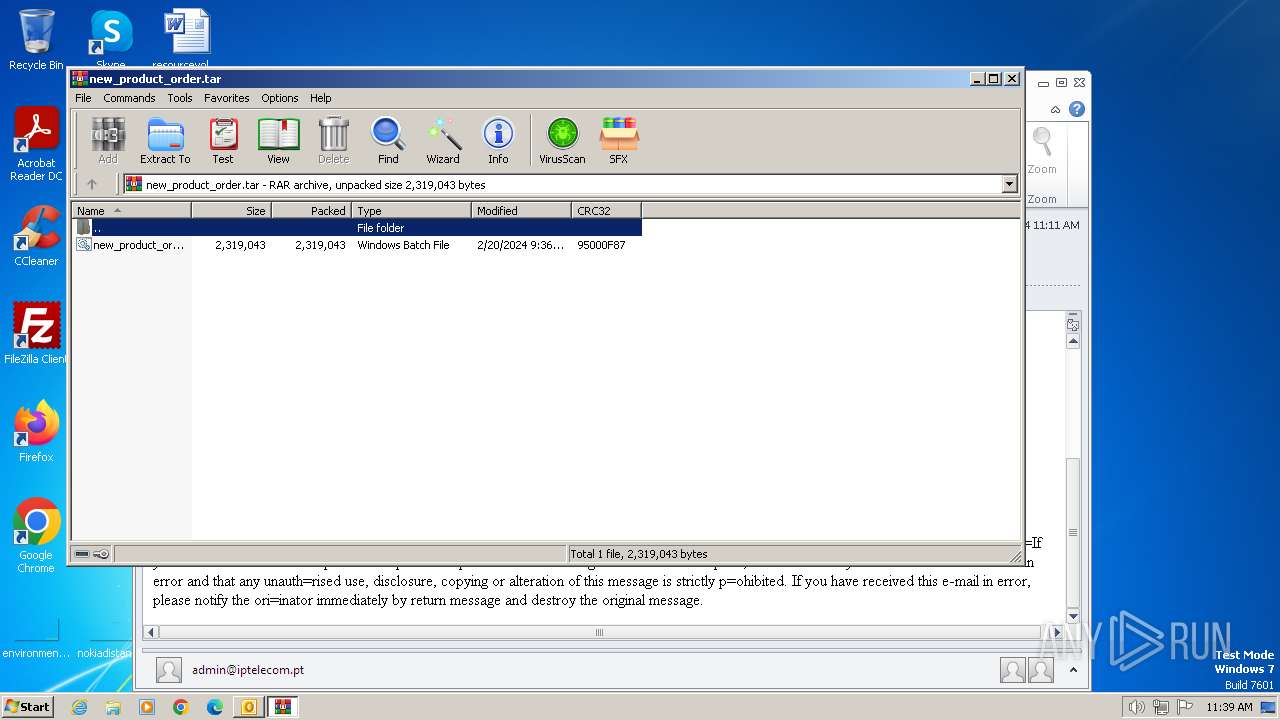
- WinRAR.exe (PID: 116)
Executable content was dropped or overwritten
- extrac32.exe (PID: 3180)
- xcopy.exe (PID: 3508)
- xcopy.exe (PID: 2596)
- x.exe (PID: 1496)
Reads the Internet Settings
- x.exe (PID: 1496)
- dwm.exe (PID: 2788)
Reads settings of System Certificates
- x.exe (PID: 1496)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 116)
- x.exe (PID: 1496)
- cmd.exe (PID: 3516)
The executable file from the user directory is run by the CMD process
- x.exe (PID: 1496)
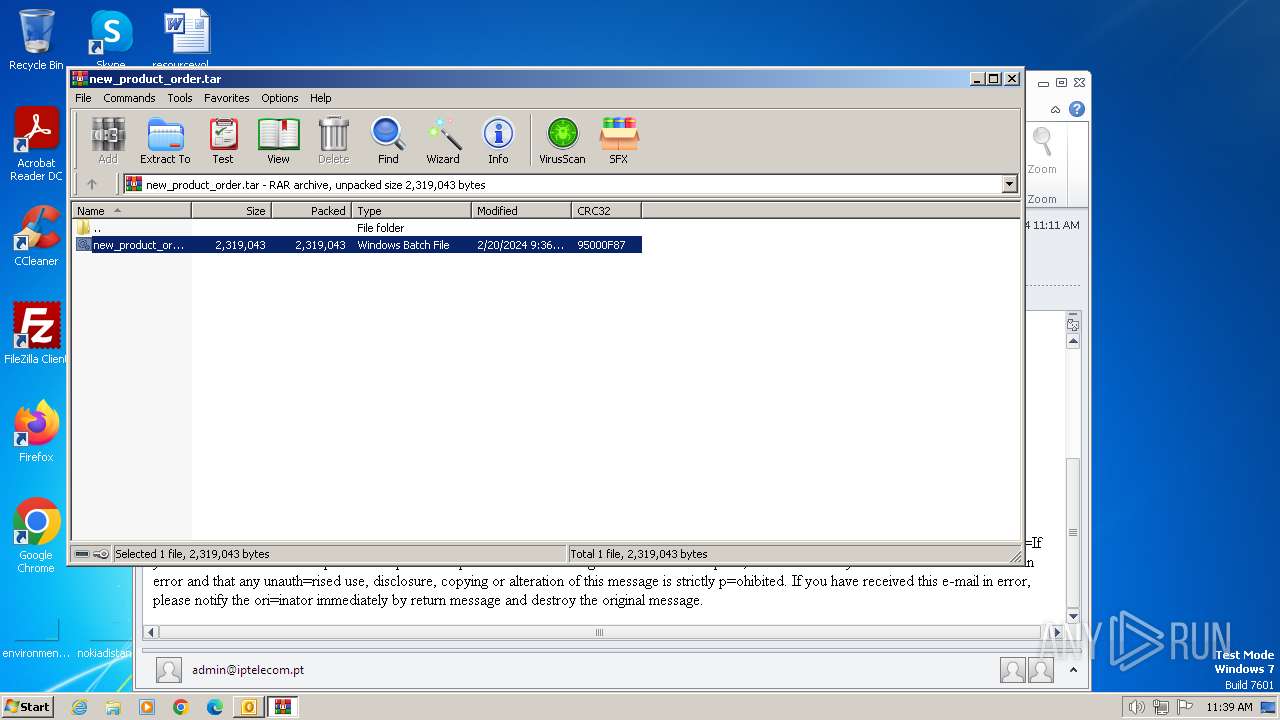
Executing commands from a ".bat" file
- WinRAR.exe (PID: 116)
- x.exe (PID: 1496)
Drops a system driver (possible attempt to evade defenses)
- x.exe (PID: 1496)
Process drops legitimate windows executable
- x.exe (PID: 1496)
- xcopy.exe (PID: 3508)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 3516)
Application launched itself
- cmd.exe (PID: 3516)
Drops a file with a rarely used extension (PIF)
- x.exe (PID: 1496)
Loads DLL from Mozilla Firefox
- dwm.exe (PID: 2788)
INFO
The process uses the downloaded file
- OUTLOOK.EXE (PID: 2472)
- WinRAR.exe (PID: 116)
Checks supported languages
- x.exe (PID: 1496)
Reads the software policy settings
- x.exe (PID: 1496)
Reads the computer name
- x.exe (PID: 1496)
Drops the executable file immediately after the start
- extrac32.exe (PID: 3180)
- xcopy.exe (PID: 3508)
- xcopy.exe (PID: 2596)
Create files in a temporary directory
- extrac32.exe (PID: 3180)
Checks proxy server information
- x.exe (PID: 1496)
Reads the machine GUID from the registry
- x.exe (PID: 1496)
Manual execution by a user
- autofmt.exe (PID: 2320)
- dwm.exe (PID: 2788)
Creates files or folders in the user directory
- dwm.exe (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DBatLoader
(PID) Process(1496) x.exe
C2 (1)https://onedrive.live.com/download?resid=653A5056738F1A02%21173&authkey=!ANQZu5-3y4oDV40
Formbook
(PID) Process(2788) dwm.exe
C2www.938579.top/fd05/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)rancangrumah.com
liposuction-54947.bond
9smp.studio
tranquilos.club
slknb9x4.shop
huidvh.xyz
59638.bet
611422.cc
gurdwarakaramsar.com
level42data.com
remedydx.com
aagmal.pro
aicertifiedpro.com
reeoumcuoarriron.shop
syrianphotographers.com
findasideproject.com
frontierconnects.co
cliphothomnay.top
vbywehjri3.top
hydrogenwaterbottles.co
beauty-bloom.online
flowautomations.info
odakegitimaraclari.xyz
wtevans.com
szkrp.com
vellagroup.dev
eyelearnfrommasters.com
weeklythepaper.com
meineinfacheslernbuch.com
6224narlingtonblvd.com
mcchoi.art
dreamcarsgiveaway.com
singlesmatchmaker.com
fi11cc65.com
myvapbnc.top
greattechinc.com
elevatece.co
dkswl.uno
lindellbank.top
grandmarinaluxuryresidences.com
sulekirkguzellik.net
4second-life.info
realestaterunnerwyo.com
veripost.net
krypto.uno
angelhues.store
avagedin.site
vadym-shapran.com
lovesummitreplay.com
lvdco.com
primeroch.com
loadsong.site
wozel.vip
kenielacouture.com
transmigrationholdings.com
thenemolabs.com
personal-loans-11122.bond
selochrono.com
lemonadeux.com
hiv0851.com
paternina100jahre.com
screehab.com
procyoninnovations.cloud
coachmindchange.com
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
62
Monitored processes
20
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\I1Y32XDS\new_product_order.tar" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | dwm.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1496 | "C:\Users\admin\AppData\Local\Temp\x.exe" | C:\Users\admin\AppData\Local\Temp\x.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
DBatLoader(PID) Process(1496) x.exe C2 (1)https://onedrive.live.com/download?resid=653A5056738F1A02%21173&authkey=!ANQZu5-3y4oDV40 | |||||||||||||||
| 1644 | xcopy "KDECO.bat" "C:\Windows \System32\" /K /D /H /Y | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\cmd.exe /S /D /c" ECHO F" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2320 | "C:\Windows\System32\autofmt.exe" | C:\Windows\System32\autofmt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto File System Format Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | cmd /c mkdir "\\?\C:\Windows " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2472 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\repeat order __.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2488 | C:\Windows\System32\SndVol.exe | C:\Windows\System32\SndVol.exe | — | x.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Volume Mixer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | C:\Windows\system32\cmd.exe /S /D /c" ECHO F" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
18 293
Read events
17 663
Write events
582
Delete events
48
Modification events
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2472) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
7
Suspicious files
6
Text files
10
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF349.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2472 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2472 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpF473.tmp | binary | |
MD5:0036340210290DF500EB75E1E80F6B63 | SHA256:6B046E077850A86303CBB3AAF8F02C5306864F479B6D85F3530457D7F8144771 | |||
| 2472 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\I1Y32XDS\new_product_order (2).tar | compressed | |
MD5:D299AC1C37BB9D94B86DDF5439074E19 | SHA256:A1383E7C1792265D27F29314F059C9D7E04CA8621177F9E6263D7C5B7238B292 | |||
| 3180 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\x.exe | executable | |
MD5:EC585EF88CCD79588D24B84DE9E30F64 | SHA256:089359771A9653653885EE4321BAFBE6EBBE443835118D79F6F33BD56E1B6226 | |||
| 1496 | x.exe | C:\Users\Public\Libraries\KDECO.bat | text | |
MD5:785E8193007BCD7858B9DF41C9D45F89 | SHA256:C8E1912A3328802E98563E32EB053AE3E28249B701054AF227E9F1BA6BFE24D9 | |||
| 2596 | xcopy.exe | C:\Windows \System32\netutils.dll | executable | |
MD5:ECB0B0D16112F27C57E4048A02802FD5 | SHA256:AE33F291A6F2011CA147C2B48035743ABA3C507DCEF86E1FA6ACB4DEE47CBF43 | |||
| 2472 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 2472 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | binary | |
MD5:506A2F28BC9008AC7DB54F5D13109BFC | SHA256:1AE23C625EC84668923037A646EBB58A803B201492C4A62A8468974DD8DAA329 | |||
| 2472 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{F707996E-0579-4771-9941-ECB0CF5154DC}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2472 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1496 | x.exe | 13.107.139.11:443 | onedrive.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1496 | x.exe | 13.107.42.12:443 | zavo9a.sn.files.1drv.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
onedrive.live.com |
| shared |
zavo9a.sn.files.1drv.com |
| unknown |