| File name: | JJSploit_8.10.15_x64_en-US.exe |
| Full analysis: | https://app.any.run/tasks/0237c2ae-8801-4d64-8833-655e430b2893 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
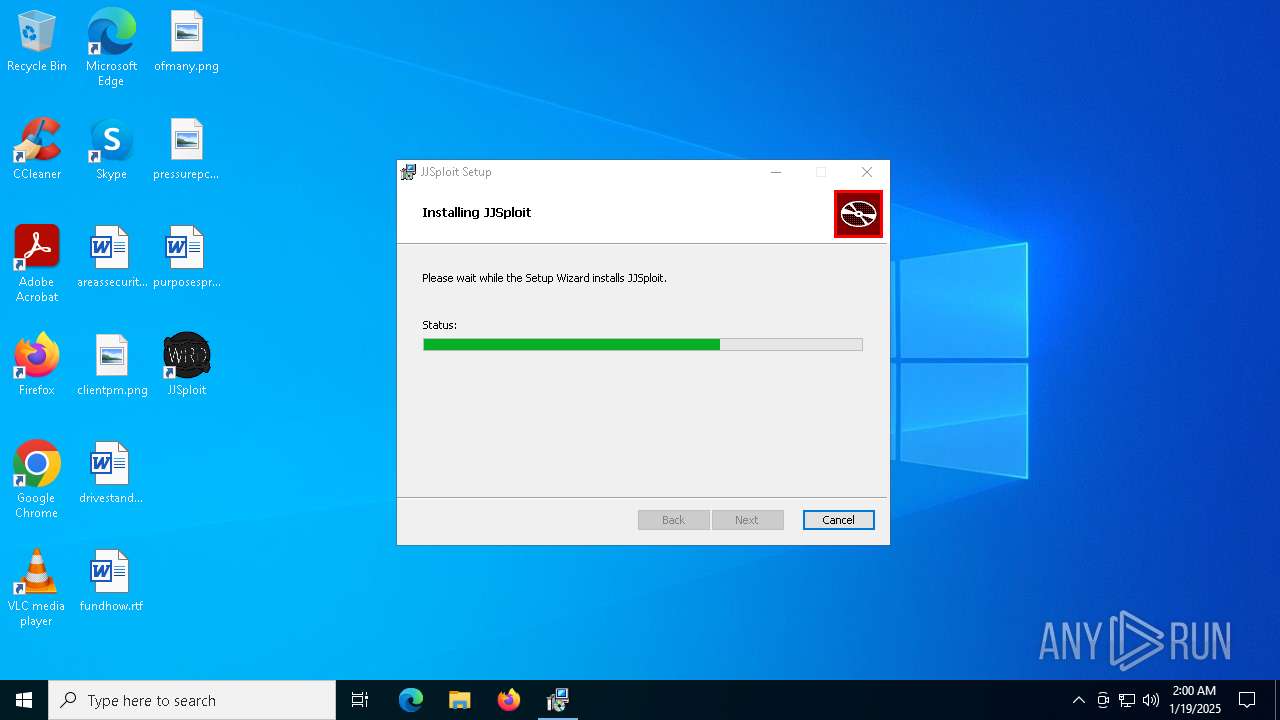
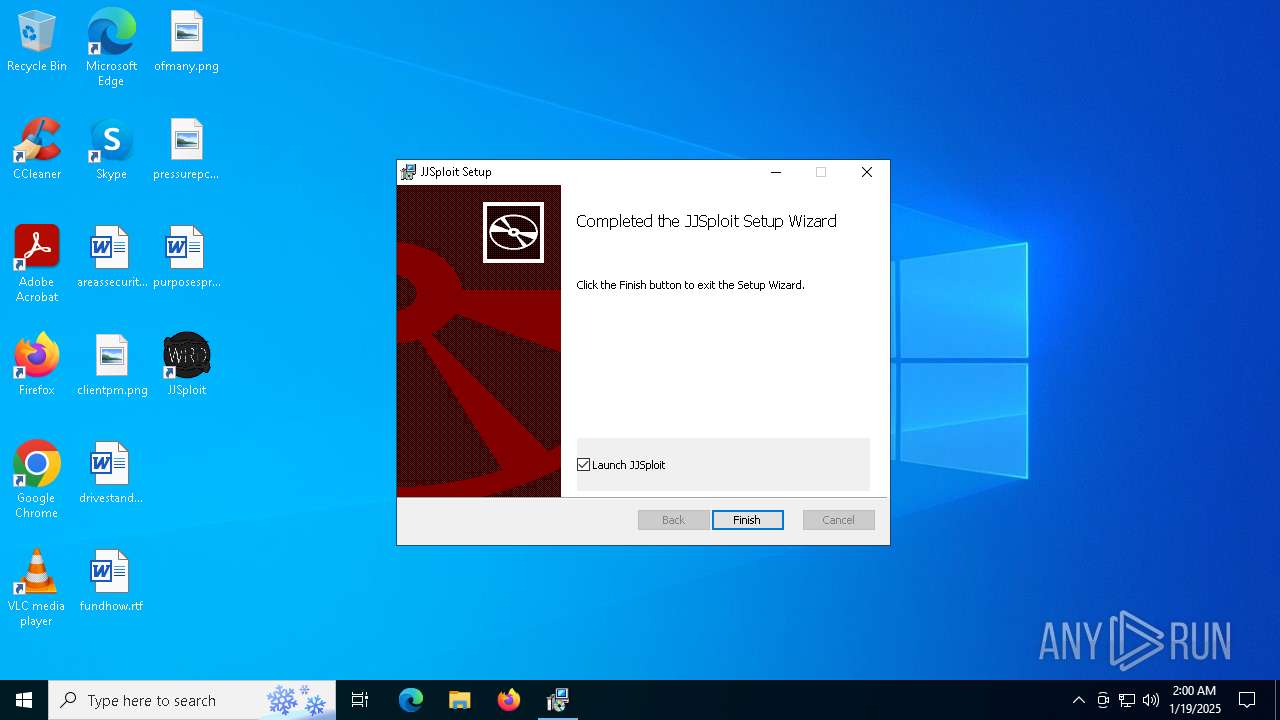
| Analysis date: | January 19, 2025, 01:59:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 8DE4967DFA5AC8CFDB8BB282096FAA33 |
| SHA1: | 8B74C208562AA36D8135411B73E884D0D80AF0C3 |
| SHA256: | 1637408D126C94A8D4C1F85984ADD31B87A782D704748068264D2B7BE742ECDE |
| SSDEEP: | 98304:WVY+YAL1N+Y4NPBWGrJQQKBoYbkDBpw1SpaeXgPuIUyouTMzKjc8q+TT1ELXdBLg:V98pBxlchxLftRKh |
MALICIOUS
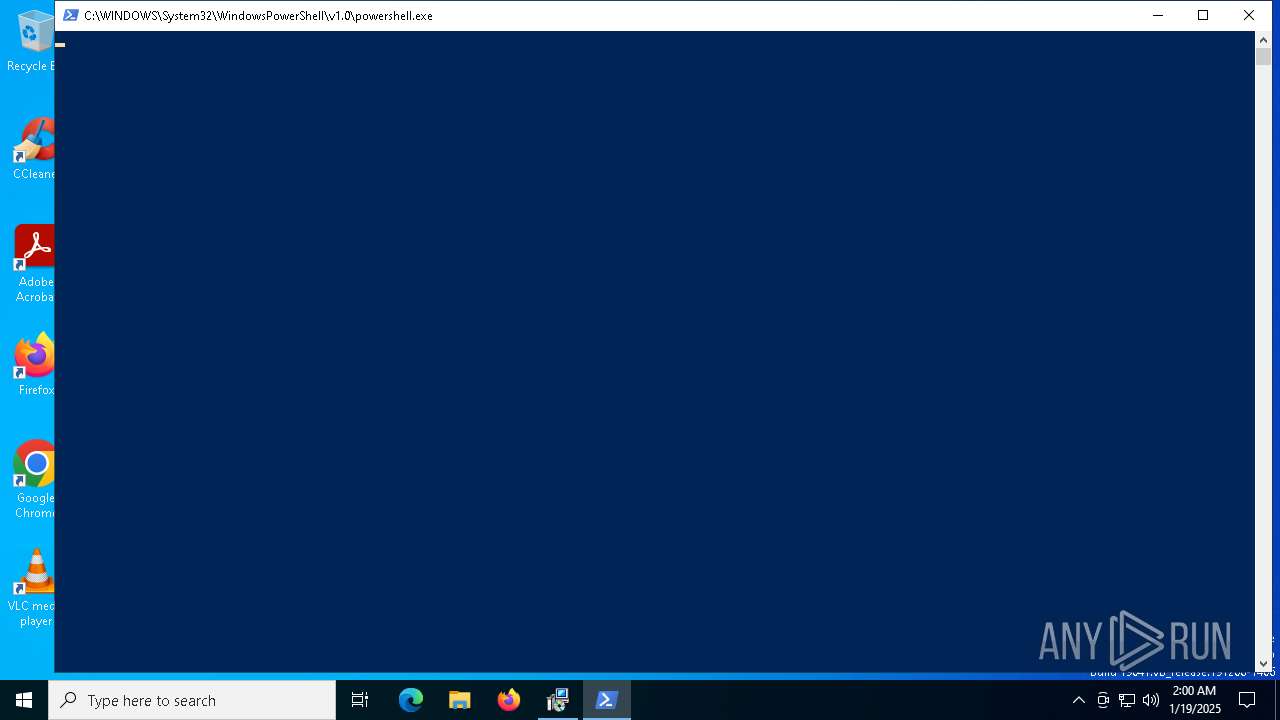
Bypass execution policy to execute commands
- powershell.exe (PID: 6840)
- powershell.exe (PID: 3816)
- powershell.exe (PID: 7520)
Changes powershell execution policy (Bypass)
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- cmd.exe (PID: 6820)
Adds path to the Windows Defender exclusion list
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- AggregatorHost.exe (PID: 6240)
- cmd.exe (PID: 6548)
Executing a file with an untrusted certificate
- AggregatorHost.exe (PID: 5404)
- AggregatorHost.exe (PID: 6240)
BlankGrabber has been detected
- AggregatorHost.exe (PID: 5404)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 4164)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 6736)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6736)
Changes Controlled Folder Access settings
- powershell.exe (PID: 6736)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 6736)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 6736)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 6736)
Changes settings for real-time protection
- powershell.exe (PID: 6736)
Actions looks like stealing of personal data
- AggregatorHost.exe (PID: 6240)
- 123.exe (PID: 720)
Steals credentials from Web Browsers
- AggregatorHost.exe (PID: 6240)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 7148)
SHEETRAT mutex has been found
- 123.exe (PID: 720)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 8144)
Changes the login/logoff helper path in the registry
- 123.exe (PID: 720)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7492)
Changes the autorun value in the registry
- 123.exe (PID: 720)
Changes the AppInit_DLLs value (autorun option)
- 123.exe (PID: 720)
Run PowerShell with an invisible window
- powershell.exe (PID: 4500)
BLANKGRABBER has been detected (SURICATA)
- AggregatorHost.exe (PID: 6240)
Starts CMD.EXE for self-deleting
- AggregatorHost.exe (PID: 6240)
SUSPICIOUS
Reads security settings of Internet Explorer
- JJSploit_8.10.15_x64_en-US.exe (PID: 5684)
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- MicrosoftEdgeUpdate.exe (PID: 6016)
- msiexec.exe (PID: 7164)
Reads the date of Windows installation
- JJSploit_8.10.15_x64_en-US.exe (PID: 5684)
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- SearchApp.exe (PID: 6772)
Application launched itself
- JJSploit_8.10.15_x64_en-US.exe (PID: 5684)
- AggregatorHost.exe (PID: 5404)
Script adds exclusion path to Windows Defender
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- cmd.exe (PID: 6548)
Starts POWERSHELL.EXE for commands execution
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- cmd.exe (PID: 6548)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 3988)
- cmd.exe (PID: 6820)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 3836)
- msiexec.exe (PID: 6964)
- cmd.exe (PID: 7788)
Executable content was dropped or overwritten
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- AggregatorHost.exe (PID: 5404)
- csc.exe (PID: 3620)
- 123.exe (PID: 720)
- powershell.exe (PID: 4500)
- MicrosoftEdgeWebview2Setup.exe (PID: 5632)
Executes as Windows Service
- VSSVC.exe (PID: 5872)
The process creates files with name similar to system file names
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- 123.exe (PID: 720)
Process drops legitimate windows executable
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- AggregatorHost.exe (PID: 5404)
- powershell.exe (PID: 4500)
- MicrosoftEdgeWebview2Setup.exe (PID: 5632)
- MicrosoftEdgeUpdate.exe (PID: 6016)
Starts a Microsoft application from unusual location
- AggregatorHost.exe (PID: 5404)
- AggregatorHost.exe (PID: 6240)
- MicrosoftEdgeWebview2Setup.exe (PID: 5632)
- MicrosoftEdgeUpdate.exe (PID: 6016)
Process drops python dynamic module
- AggregatorHost.exe (PID: 5404)
Loads Python modules
- AggregatorHost.exe (PID: 6240)
Starts CMD.EXE for commands execution
- AggregatorHost.exe (PID: 6240)
- 123.exe (PID: 720)
Found strings related to reading or modifying Windows Defender settings
- AggregatorHost.exe (PID: 6240)
Script disables Windows Defender's IPS
- cmd.exe (PID: 4164)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 4164)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5092)
Get information on the list of running processes
- AggregatorHost.exe (PID: 6240)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6992)
- cmd.exe (PID: 4804)
Starts application with an unusual extension
- cmd.exe (PID: 4132)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 8100)
- cmd.exe (PID: 7828)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4764)
- cmd.exe (PID: 8036)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 2072)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 4076)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 6820)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6820)
- msiexec.exe (PID: 6964)
Base64-obfuscated command line is found
- cmd.exe (PID: 6820)
The process drops C-runtime libraries
- AggregatorHost.exe (PID: 5404)
CSC.EXE is used to compile C# code
- csc.exe (PID: 3620)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 7432)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 7520)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 7468)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4648)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 4328)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7852)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7888)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 8112)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 6520)
Connects to unusual port
- 123.exe (PID: 720)
Checks for external IP
- svchost.exe (PID: 2192)
- AggregatorHost.exe (PID: 6240)
Starts process via Powershell
- powershell.exe (PID: 4500)
Manipulates environment variables
- powershell.exe (PID: 4500)
Downloads file from URI via Powershell
- powershell.exe (PID: 4500)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6964)
Hides command output
- cmd.exe (PID: 3988)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3988)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4500)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 6016)
INFO
Reads the computer name
- JJSploit_8.10.15_x64_en-US.exe (PID: 5684)
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- msiexec.exe (PID: 6964)
- msiexec.exe (PID: 7164)
- 123.exe (PID: 720)
- AggregatorHost.exe (PID: 6240)
- AggregatorHost.exe (PID: 5404)
- MpCmdRun.exe (PID: 7148)
- SearchApp.exe (PID: 6772)
- JJSploit.exe (PID: 6172)
- JJSploit.exe (PID: 6168)
- MicrosoftEdgeUpdate.exe (PID: 6016)
Process checks computer location settings
- JJSploit_8.10.15_x64_en-US.exe (PID: 5684)
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- SearchApp.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 6016)
- msiexec.exe (PID: 7164)
The process uses the downloaded file
- JJSploit_8.10.15_x64_en-US.exe (PID: 5684)
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- powershell.exe (PID: 4500)
Reads Microsoft Office registry keys
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
Reads the machine GUID from the registry
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- 123.exe (PID: 720)
- csc.exe (PID: 3620)
- rar.exe (PID: 7468)
- SearchApp.exe (PID: 6772)
Checks supported languages
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- msiexec.exe (PID: 6964)
- msiexec.exe (PID: 7164)
- 123.exe (PID: 720)
- AggregatorHost.exe (PID: 5404)
- AggregatorHost.exe (PID: 6240)
- JJSploit_8.10.15_x64_en-US.exe (PID: 5684)
- tree.com (PID: 6796)
- tree.com (PID: 7672)
- tree.com (PID: 7860)
- tree.com (PID: 7336)
- tree.com (PID: 8008)
- tree.com (PID: 7408)
- cvtres.exe (PID: 7792)
- MpCmdRun.exe (PID: 7148)
- csc.exe (PID: 3620)
- rar.exe (PID: 7468)
- SearchApp.exe (PID: 6772)
- MicrosoftEdgeWebview2Setup.exe (PID: 5632)
- MicrosoftEdgeUpdate.exe (PID: 6016)
- JJSploit.exe (PID: 6172)
- JJSploit.exe (PID: 6168)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6840)
- powershell.exe (PID: 3816)
- powershell.exe (PID: 6736)
- powershell.exe (PID: 6884)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6840)
- powershell.exe (PID: 3816)
- powershell.exe (PID: 6884)
- powershell.exe (PID: 6736)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 7508)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6832)
- msiexec.exe (PID: 6964)
The sample compiled with english language support
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- AggregatorHost.exe (PID: 5404)
- powershell.exe (PID: 4500)
- MicrosoftEdgeWebview2Setup.exe (PID: 5632)
- MicrosoftEdgeUpdate.exe (PID: 6016)
Create files in a temporary directory
- JJSploit_8.10.15_x64_en-US.exe (PID: 6444)
- AggregatorHost.exe (PID: 5404)
- AggregatorHost.exe (PID: 6240)
- csc.exe (PID: 3620)
- cvtres.exe (PID: 7792)
- MpCmdRun.exe (PID: 7148)
Checks the directory tree
- tree.com (PID: 6796)
- tree.com (PID: 7672)
- tree.com (PID: 7860)
- tree.com (PID: 8008)
- tree.com (PID: 7408)
- tree.com (PID: 7336)
The Powershell gets current clipboard
- powershell.exe (PID: 7512)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7432)
- WMIC.exe (PID: 4328)
- WMIC.exe (PID: 6636)
- WMIC.exe (PID: 7888)
- WMIC.exe (PID: 6520)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 6724)
Drops encrypted VBS script (Microsoft Script Encoder)
- 123.exe (PID: 720)
Reads Environment values
- 123.exe (PID: 720)
- SearchApp.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 6016)
Disables trace logs
- 123.exe (PID: 720)
- powershell.exe (PID: 4500)
Checks proxy server information
- 123.exe (PID: 720)
- SearchApp.exe (PID: 6772)
- powershell.exe (PID: 4500)
- MicrosoftEdgeUpdate.exe (PID: 6016)
- wermgr.exe (PID: 7356)
Creates files or folders in the user directory
- 123.exe (PID: 720)
Reads the software policy settings
- 123.exe (PID: 720)
- SearchApp.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 6016)
- wermgr.exe (PID: 7356)
Manages system restore points
- SrTasks.exe (PID: 7240)
Creates a software uninstall entry
- msiexec.exe (PID: 6964)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 5632)
Creates files in the program directory
- MicrosoftEdgeWebview2Setup.exe (PID: 5632)
Manual execution by a user
- JJSploit.exe (PID: 6168)
Sends debugging messages
- JJSploit.exe (PID: 6172)
- JJSploit.exe (PID: 6168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:01:12 20:52:21+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 13238272 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xca1fee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | JJSploit_8.10.15_x64_en-US.exe |
| LegalCopyright: | |
| OriginalFileName: | JJSploit_8.10.15_x64_en-US.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
254
Monitored processes
121
Malicious processes
11
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\Users\admin\AppData\Local\Temp\123.exe" | C:\Users\admin\AppData\Local\Temp\123.exe | JJSploit_8.10.15_x64_en-US.exe | ||||||||||||
User: admin Company: Bloxstrap Integrity Level: HIGH Description: Bloxstrap Version: 2.8.1.0 Modules
| |||||||||||||||
| 2072 | C:\WINDOWS\system32\cmd.exe /c "systeminfo" | C:\Windows\System32\cmd.exe | — | AggregatorHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2736 | attrib +h +s "C:\Users\admin\AppData\Local\Temp\AggregatorHost.exe" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2956 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3260 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\4dr35pbu\4dr35pbu.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3620 | C:\WINDOWS\system32\cmd.exe /c "powershell Get-ItemPropertyValue -Path 'HKLM:System\CurrentControlSet\Control\Session Manager\Environment' -Name PROCESSOR_IDENTIFIER" | C:\Windows\System32\cmd.exe | — | AggregatorHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3816 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\AggregatorHost.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | JJSploit_8.10.15_x64_en-US.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
86 917
Read events
86 440
Write events
454
Delete events
23
Modification events
| (PID) Process: | (6444) JJSploit_8.10.15_x64_en-US.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
| (PID) Process: | (6964) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000005BB0B3DF156ADB01341B00009C160000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6964) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000005BB0B3DF156ADB01341B00009C160000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6964) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000A0E2ECDF156ADB01341B00009C160000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6964) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000A0E2ECDF156ADB01341B00009C160000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6964) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000019A9F1DF156ADB01341B00009C160000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6964) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000D845EFDF156ADB01341B00009C160000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (720) 123.exe | Key: | HKEY_CURRENT_USER\SOFTWARE |
| Operation: | write | Name: | hwid |
Value: MUFFQ0EyRTVDODhDMzgzNkJFQkZBM0M= | |||
| (PID) Process: | (6964) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6964) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000909D5AE0156ADB01341B00009C160000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
271
Suspicious files
104
Text files
188
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6444 | JJSploit_8.10.15_x64_en-US.exe | C:\Users\admin\AppData\Local\Temp\JJSploit_8.10.15_x64_en-US.msi | — | |
MD5:— | SHA256:— | |||
| 6840 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_debu1xja.gqd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3816 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pismd1mm.l1a.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5404 | AggregatorHost.exe | C:\Users\admin\AppData\Local\Temp\_MEI54042\_decimal.pyd | executable | |
MD5:7BA541DEFE3739A888BE466C999C9787 | SHA256:F90EFA10D90D940CDE48AAFE02C13A0FC0A1F0BE7F3714856B7A1435F5DECF29 | |||
| 3816 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wwp5cnln.l4s.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5404 | AggregatorHost.exe | C:\Users\admin\AppData\Local\Temp\_MEI54042\_queue.pyd | executable | |
MD5:FBBBFBCDCF0A7C1611E27F4B3B71079E | SHA256:699C1F0F0387511EF543C0DF7EF81A13A1CFFDE4CE4CD43A1BAF47A893B99163 | |||
| 6444 | JJSploit_8.10.15_x64_en-US.exe | C:\Users\admin\AppData\Local\Temp\AggregatorHost.exe | executable | |
MD5:AA23AE6F2FBE0056ACE9B2786B12FFB2 | SHA256:8077797EBDD88706933EF5837CA1565E6A6BBF0C9165732F0C455AAC69B5D1D7 | |||
| 6444 | JJSploit_8.10.15_x64_en-US.exe | C:\Users\admin\AppData\Local\Temp\123.exe | executable | |
MD5:2381DBB16A86A7AB1504B63513DD3B58 | SHA256:CDD3A4A0BB5BD37585CBBC19DD63B680871EEEA88C6B58791E5CD596B5CF59BA | |||
| 5404 | AggregatorHost.exe | C:\Users\admin\AppData\Local\Temp\_MEI54042\_hashlib.pyd | executable | |
MD5:596DF8ADA4B8BC4AE2C2E5BBB41A6C2E | SHA256:54348CFBF95FD818D74014C16343D9134282D2CF238329EEC2CDA1E2591565EC | |||
| 5404 | AggregatorHost.exe | C:\Users\admin\AppData\Local\Temp\_MEI54042\VCRUNTIME140.dll | executable | |
MD5:F12681A472B9DD04A812E16096514974 | SHA256:D66C3B47091CEB3F8D3CC165A43D285AE919211A0C0FCB74491EE574D8D464F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
55
DNS requests
31
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
188 | svchost.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
188 | svchost.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
968 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7720 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7720 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7356 | wermgr.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6240 | AggregatorHost.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | shared |
7356 | wermgr.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
188 | svchost.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
188 | svchost.exe | 23.209.214.100:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.19.122.26:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1076 | svchost.exe | 2.18.97.227:443 | go.microsoft.com | Akamai International B.V. | FR | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
gstatic.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2192 | svchost.exe | Misc activity | ET INFO Tunneling Service in DNS Lookup (* .ply .gg) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6240 | AggregatorHost.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6240 | AggregatorHost.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |
6240 | AggregatorHost.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
Process | Message |
|---|---|
JJSploit.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
JJSploit.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|