| File name: | 3.exe |
| Full analysis: | https://app.any.run/tasks/2e0f3b3f-48a4-4777-857e-0d53b056e576 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | February 09, 2019, 19:47:46 |
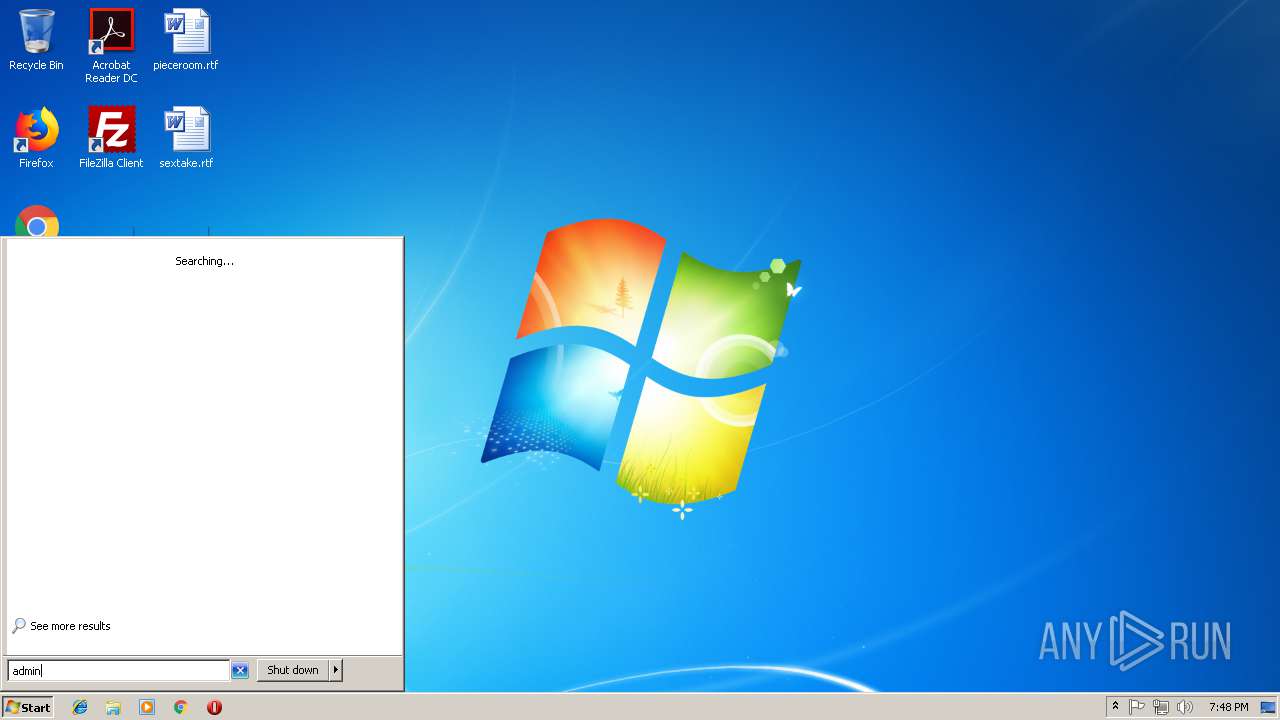
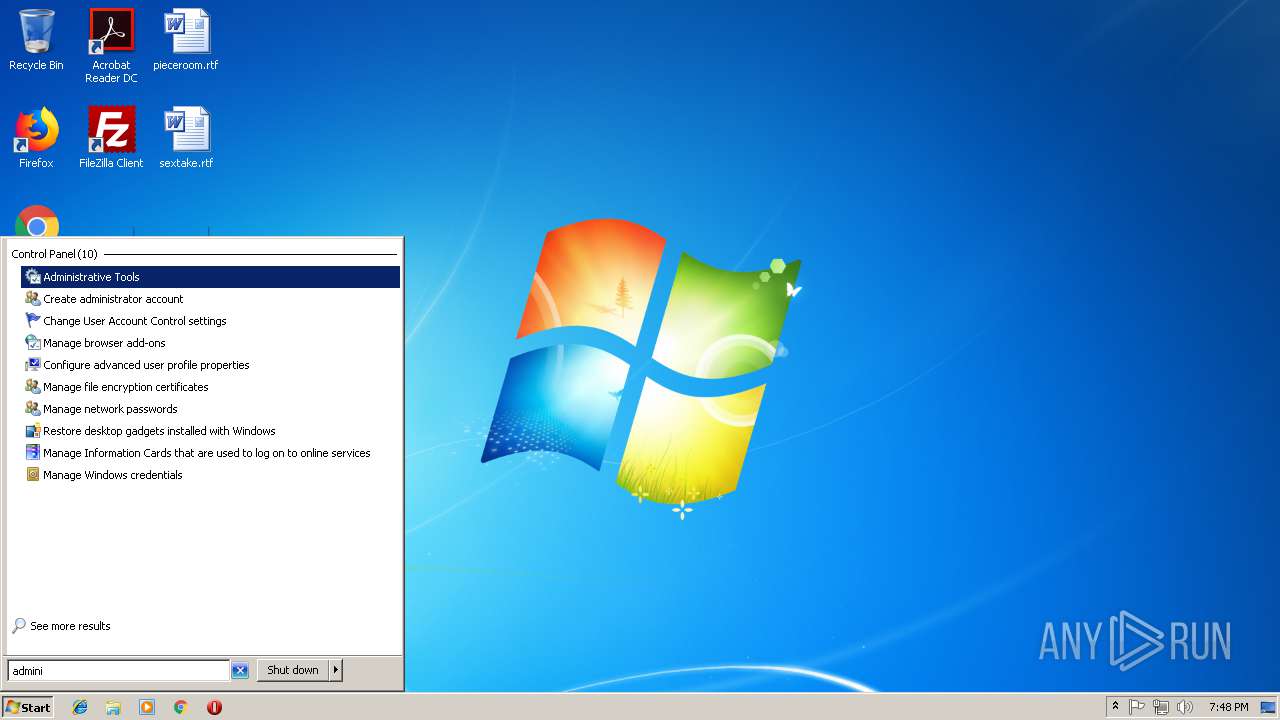
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E0D79B152EA769D876973D8CD8BF733B |
| SHA1: | CF04B36638E1967C3DFCE61EC1114E7A793F5415 |
| SHA256: | 1636776894F20E41EF1C87D1028517416DA5B8FFD2B5404DAE1ADBDAFA9EF136 |
| SSDEEP: | 98304:+I9+6qF8B0kJ2yd8grunMIPeIarp7fH2RS:CF6Ay6grNp |
MALICIOUS
Changes the autorun value in the registry
- 3.exe (PID: 3312)
Loads dropped or rewritten executable
- vbc.exe (PID: 3088)
Writes to a start menu file
- vbc.exe (PID: 3088)
MINER was detected
- calc.exe (PID: 2452)
Connects to CnC server
- calc.exe (PID: 2452)
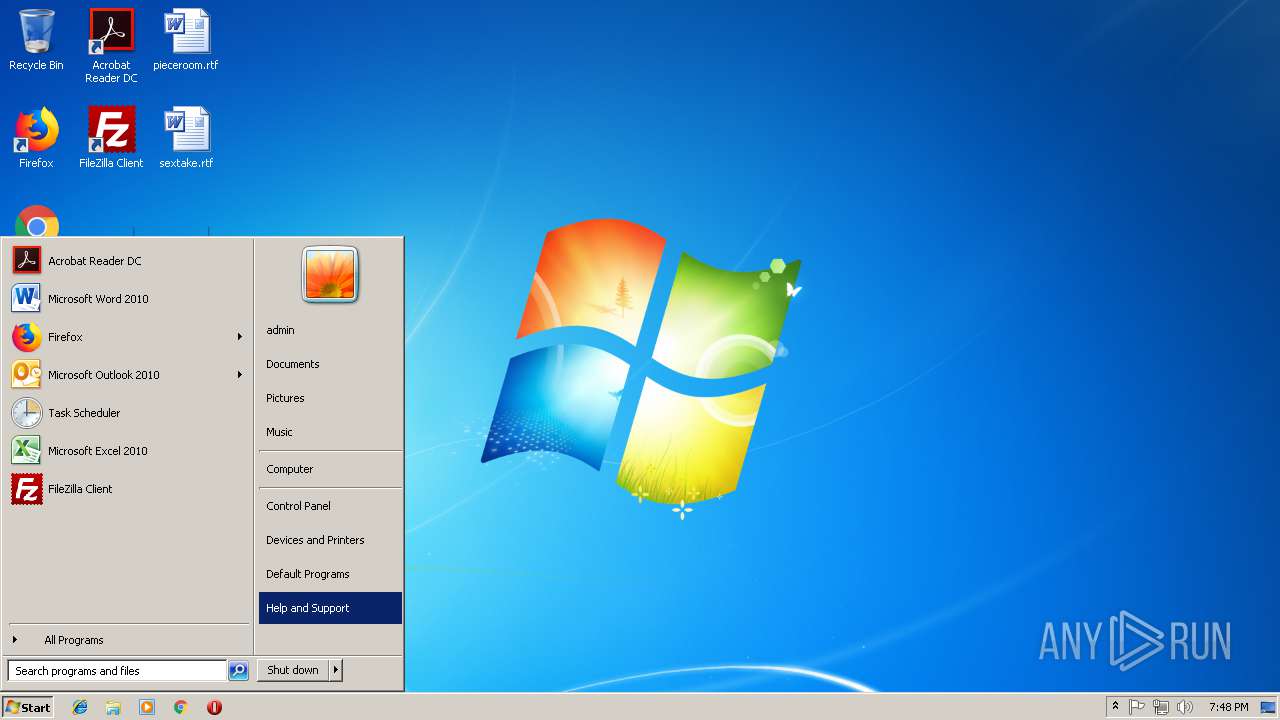
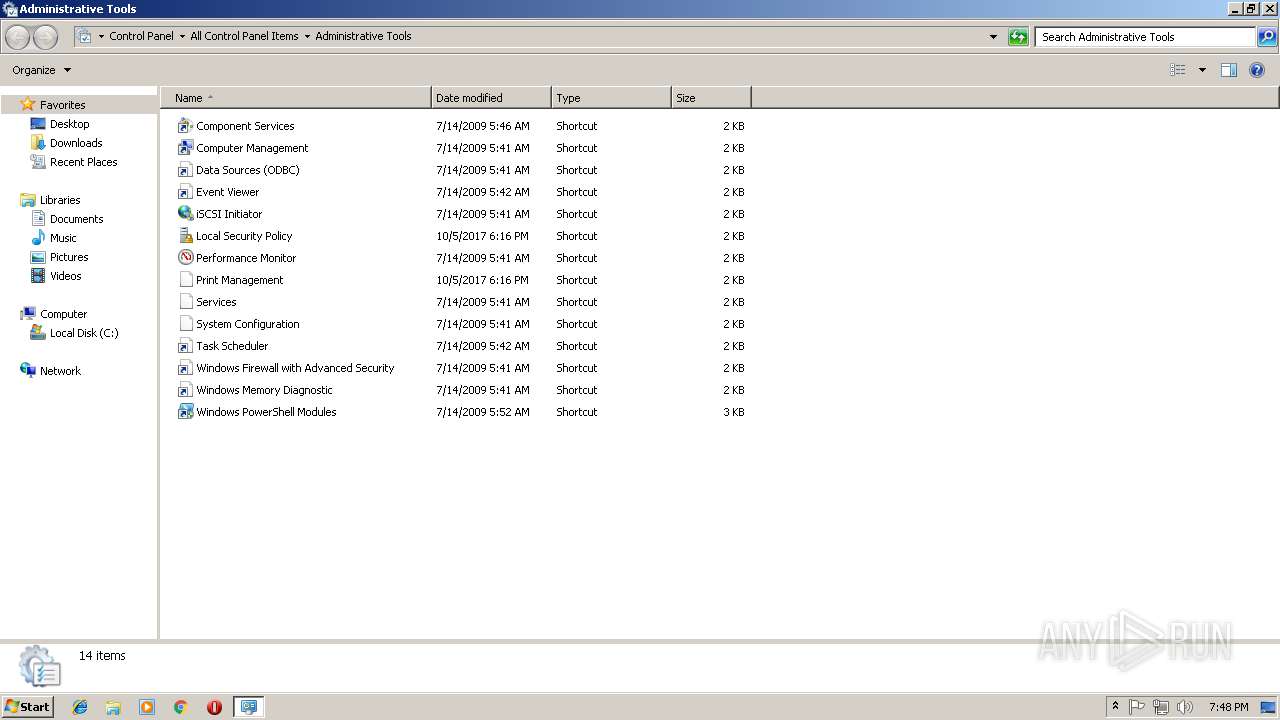
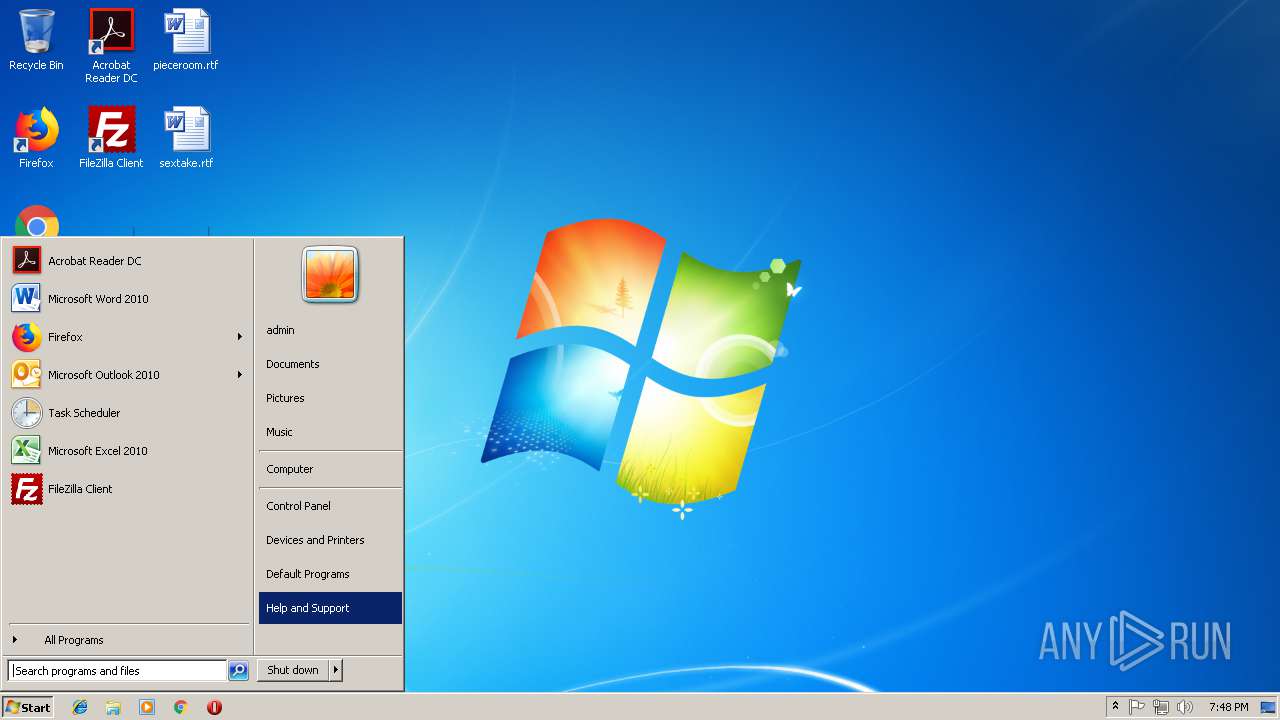
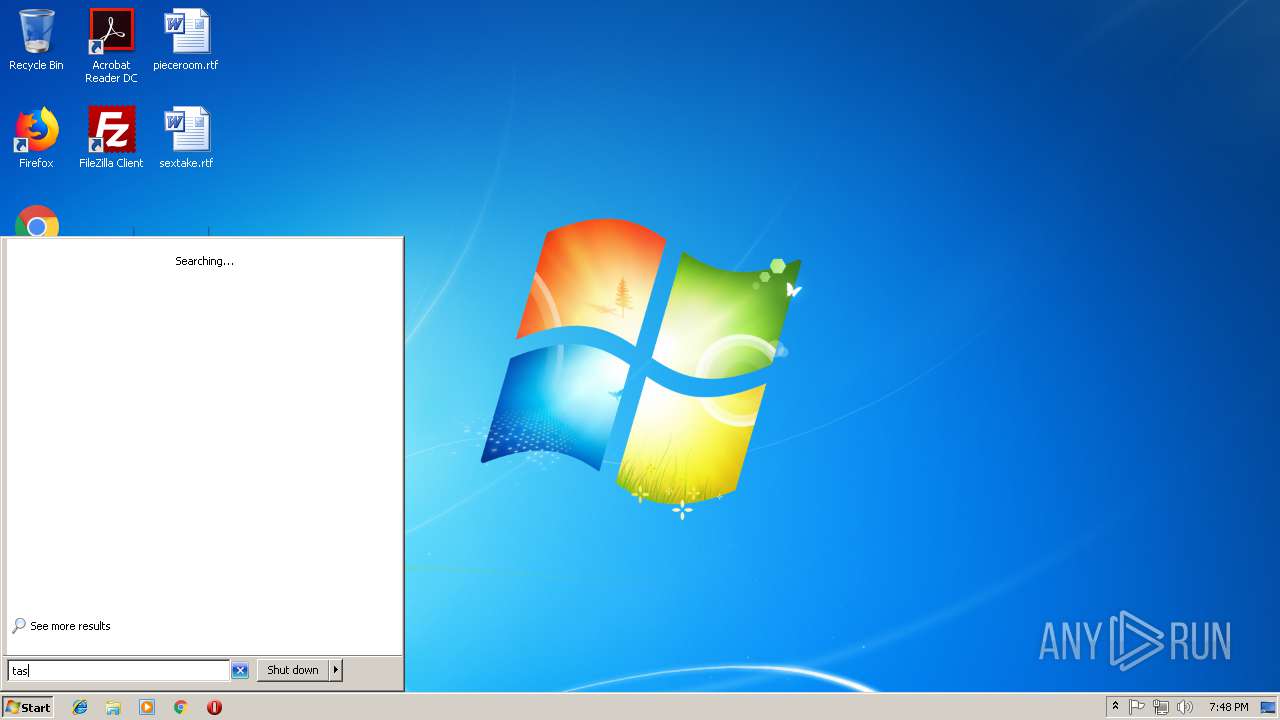
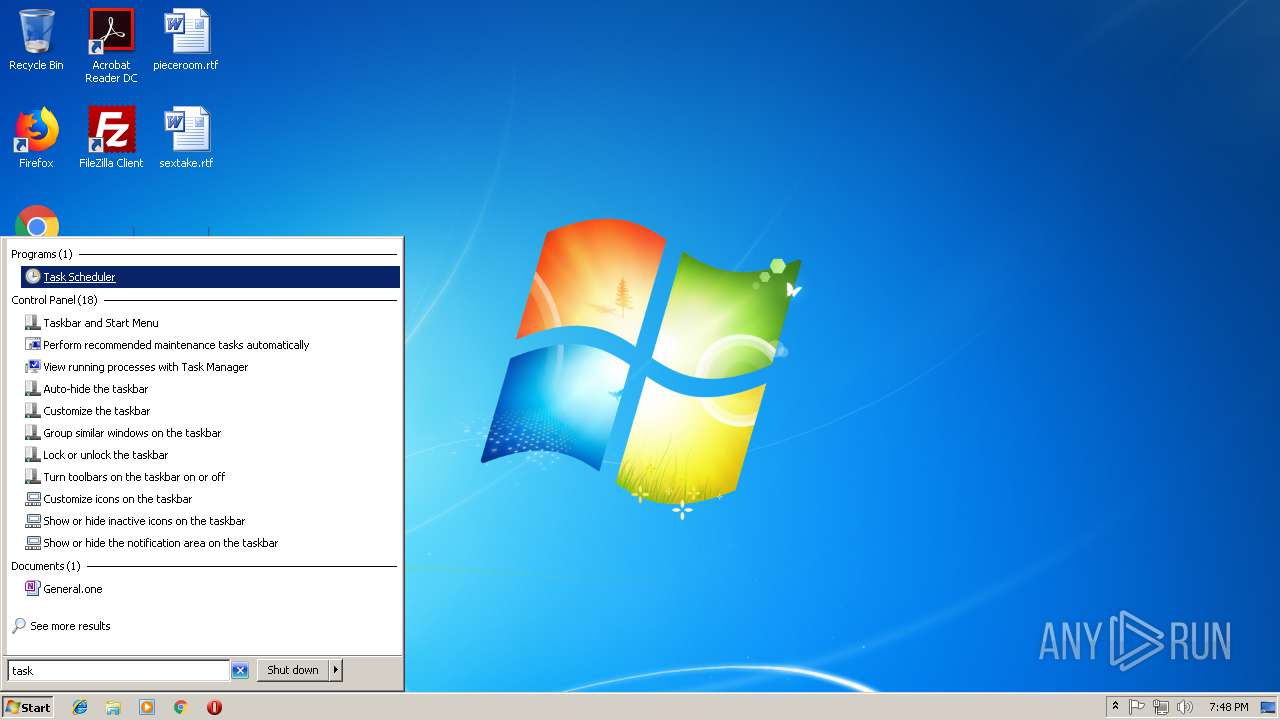
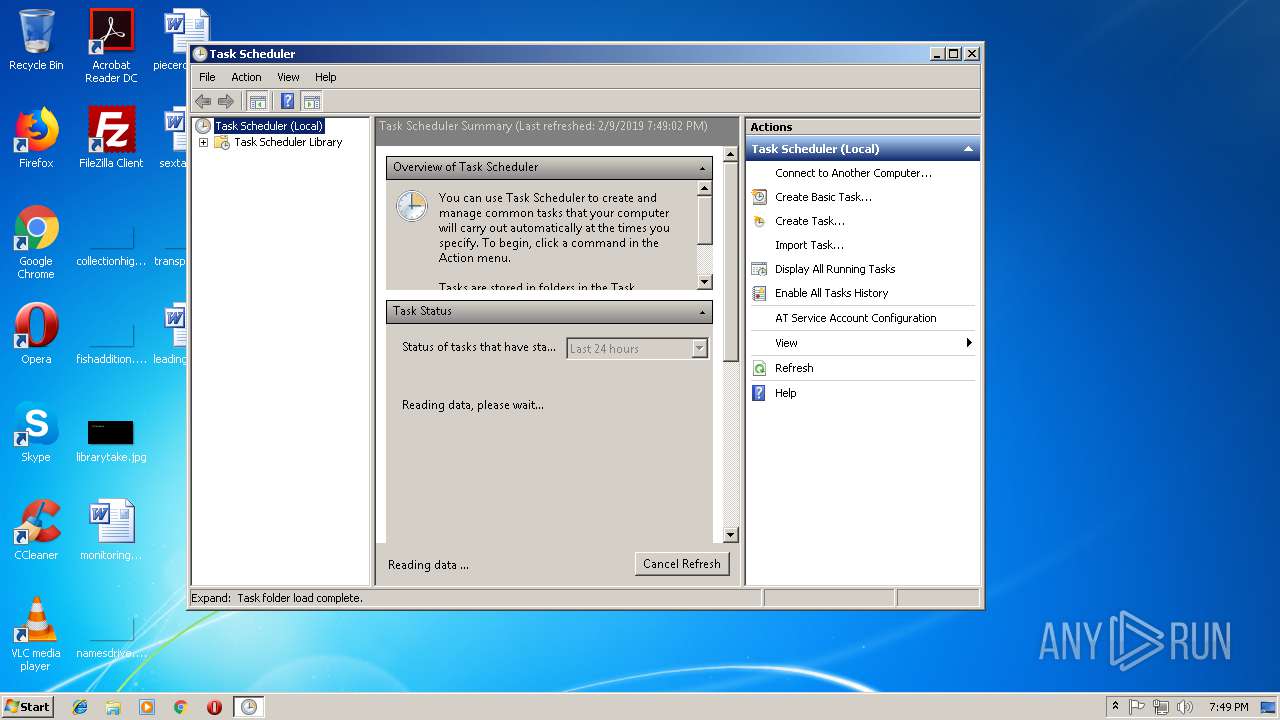
Loads the Task Scheduler COM API
- mmc.exe (PID: 2800)
SUSPICIOUS
Executable content was dropped or overwritten
- 3.exe (PID: 3312)
- vbc.exe (PID: 3088)
Creates files in the user directory
- vbc.exe (PID: 3088)
- 3.exe (PID: 3312)
Executes scripts
- 3.exe (PID: 3312)
Connects to unusual port
- calc.exe (PID: 2452)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (81) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.2) |
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.2) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:09 19:49:12+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 10258944 |
| InitializedDataSize: | 16896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9ca98e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | ABYyWpxEhIDiXOSzm.exe |
| LegalCopyright: | |
| OriginalFileName: | ABYyWpxEhIDiXOSzm.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 792 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | -o xmrpool.xmrminingpool.net:3333 -u GuyFawkesMiner-admin -p xxxx -k --max-cpu-usage=50 | C:\Windows\system32\calc.exe | vbc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2800 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3088 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | 3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3312 | "C:\Users\admin\AppData\Local\Temp\3.exe" | C:\Users\admin\AppData\Local\Temp\3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
258
Read events
251
Write events
6
Delete events
1
Modification events
| (PID) Process: | (3312) 3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | startupname |
Value: C:\Users\admin\AppData\Roaming\filename.exe | |||
| (PID) Process: | (2800) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | HelpTopic |
Value: C:\Windows\Help\taskscheduler.chm | |||
| (PID) Process: | (2800) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | LinkedHelpTopics |
Value: C:\Windows\Help\taskscheduler.chm | |||
| (PID) Process: | (2800) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2800) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File1 |
Value: C:\Windows\system32\taskschd.msc | |||
| (PID) Process: | (2800) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File2 |
Value: C:\Windows\system32\wf.msc | |||
| (PID) Process: | (2800) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File3 |
Value: C:\Windows\System32\services.msc | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | vbc.exe | C:\Users\admin\AppData\Local\Temp\LZMA.DLL | executable | |
MD5:— | SHA256:— | |||
| 3088 | vbc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Notepad.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3312 | 3.exe | C:\Users\admin\AppData\Roaming\filename.exe | executable | |
MD5:— | SHA256:— | |||
| 2800 | mmc.exe | C:\Users\admin\AppData\Roaming\Microsoft\MMC\taskschd | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
8
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2452 | calc.exe | 83.47.188.156:3333 | xmrpool.xmrminingpool.net | Telefonica De Espana | ES | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xmrpool.xmrminingpool.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2452 | calc.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
2452 | calc.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2452 | calc.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
2452 | calc.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |
2452 | calc.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
2452 | calc.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
2452 | calc.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |
2452 | calc.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight algo JSON_RPC server Response |
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|