| File name: | 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe |
| Full analysis: | https://app.any.run/tasks/10838cbf-d0c3-4e68-8ae2-912e06d866cd |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 19, 2025, 02:22:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | CE3077867DB91FEFAD34E156837C4375 |
| SHA1: | 555FA235E6FB16D7E461D1DCE39B29A76E0A27CE |
| SHA256: | 1634057CC5FF967579FD610822628B576227875E5287A59DD76D7258B72BD20C |
| SSDEEP: | 98304:5cSigcN+m1Dju8PUMN8dPkekFdKqOeCN+cNZSj46s15IP78OjNPsk3hJxEQKURC4:/M |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
Actions looks like stealing of personal data
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
Steals credentials from Web Browsers
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
SUSPICIOUS
Reads the BIOS version
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
Searches for installed software
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
INFO
Reads the computer name
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
Reads the machine GUID from the registry
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
Reads the software policy settings
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
- slui.exe (PID: 5548)
Checks supported languages
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
Themida protector has been detected
- 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe (PID: 2236)
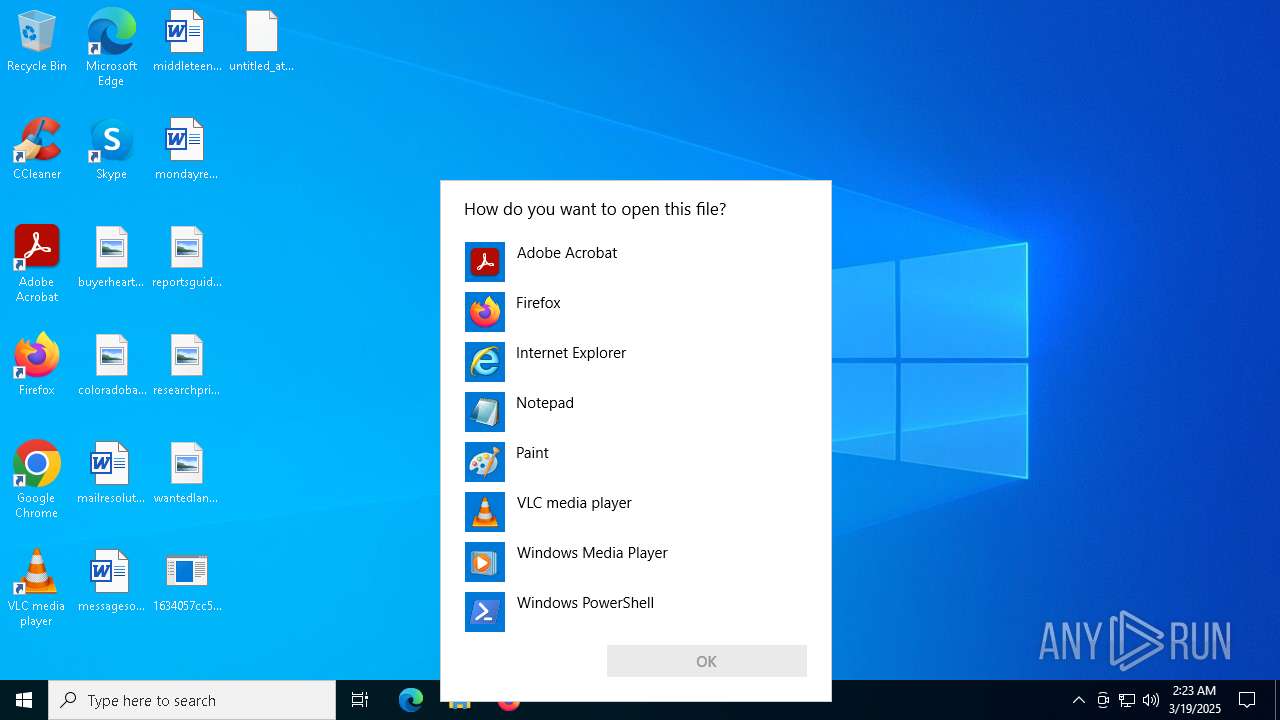
Manual execution by a user
- OpenWith.exe (PID: 3156)
Checks proxy server information
- slui.exe (PID: 5548)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:11 12:57:56+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 313856 |
| InitializedDataSize: | 46592 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4b3000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
123
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\Desktop\1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe" | C:\Users\admin\Desktop\1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3156 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\untitled_attachment_0 | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 412
Read events
7 412
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
27
DNS requests
15
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.212.216.106:443 | https://steamcommunity.com/profiles/76561199822375128 | unknown | html | 35.2 Kb | whitelisted |
— | — | POST | 200 | 104.21.32.1:443 | https://pupmeholk.bet/pLoska | unknown | binary | 13.8 Kb | malicious |
— | — | GET | 200 | 23.212.216.106:443 | https://steamcommunity.com/profiles/76561199822375128 | unknown | html | 35.2 Kb | whitelisted |
— | — | GET | 200 | 23.212.216.106:443 | https://steamcommunity.com/profiles/76561199822375128 | unknown | html | 35.2 Kb | whitelisted |
— | — | GET | 200 | 23.212.216.106:443 | https://steamcommunity.com/profiles/76561199822375128 | unknown | html | 35.2 Kb | whitelisted |
— | — | POST | 200 | 104.21.16.1:443 | https://pupmeholk.bet/pLoska | unknown | binary | 70 b | malicious |
— | — | POST | 200 | 104.21.32.1:443 | https://pupmeholk.bet/pLoska | unknown | binary | 70 b | malicious |
— | — | POST | — | 104.21.96.1:443 | https://pupmeholk.bet/pLoska | unknown | — | — | malicious |
— | — | GET | 200 | 23.212.216.106:443 | https://steamcommunity.com/profiles/76561199822375128 | unknown | html | 35.2 Kb | whitelisted |
— | — | POST | 200 | 104.21.112.1:443 | https://pupmeholk.bet/pLoska | unknown | binary | 70 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2236 | 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe | 104.73.234.102:443 | steamcommunity.com | AKAMAI-AS | DE | whitelisted |
2236 | 1634057cc5ff967579fd610822628b576227875e5287a59dd76d7258b72bd20c.exe | 104.21.64.1:443 | pupmeholk.bet | CLOUDFLARENET | — | malicious |
5556 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5548 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
kbracketba.shop |
| malicious |
featureccus.shop |
| malicious |
mrodularmall.top |
| malicious |
jowinjoinery.icu |
| malicious |
legenassedk.top |
| malicious |
htardwarehu.icu |
| malicious |
cjlaspcorne.icu |
| malicious |
bugildbett.top |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (bugildbett .top) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (mrodularmall .top) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (jowinjoinery .icu) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (legenassedk .top) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (htardwarehu .icu) |