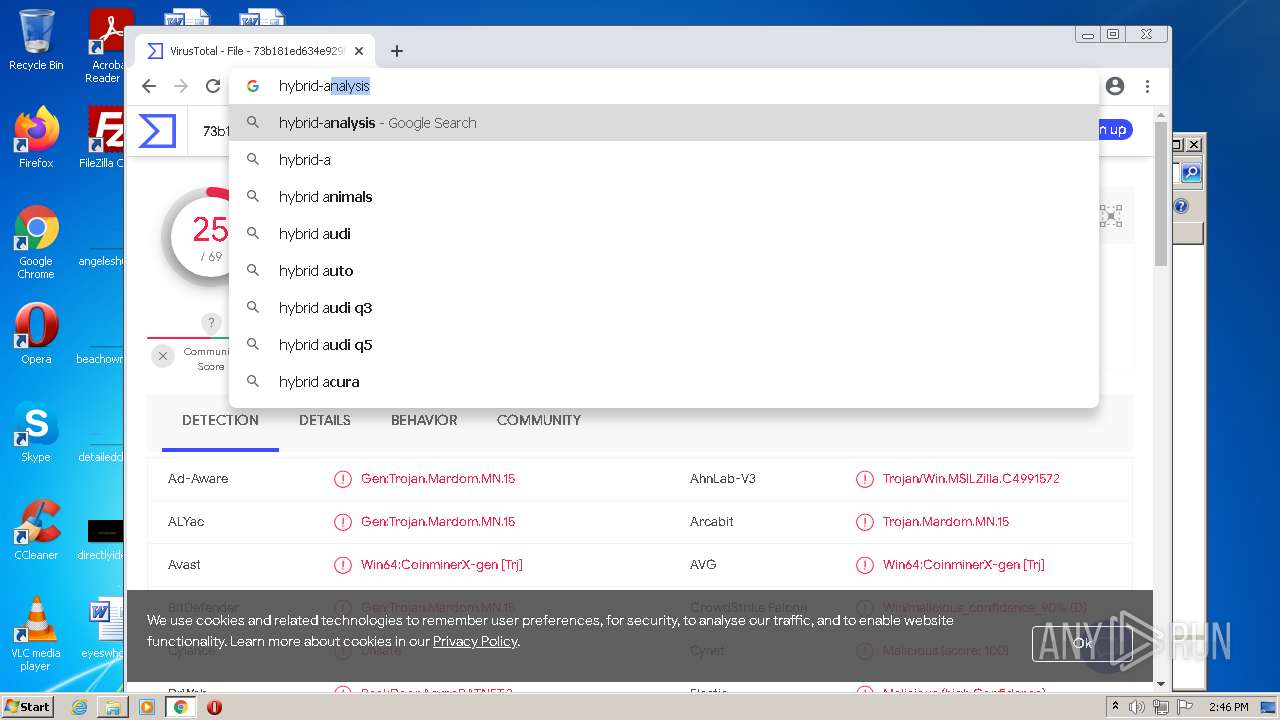
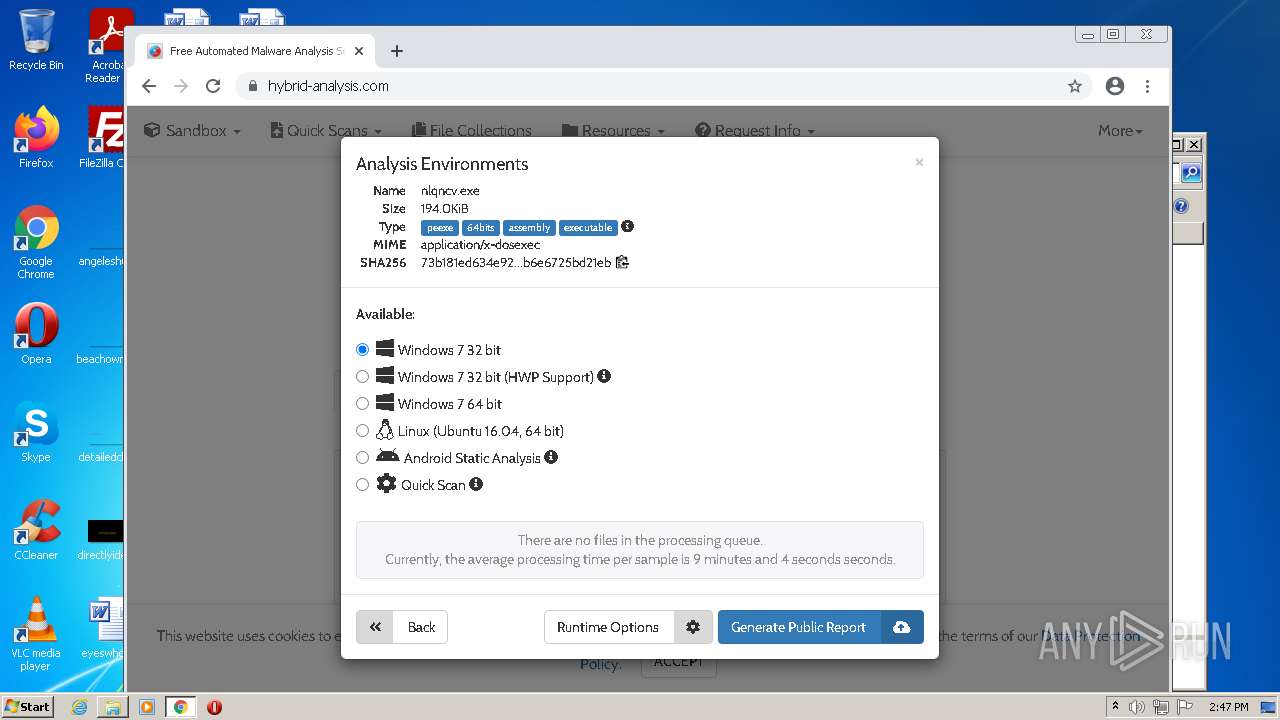
| File name: | C:\Users\admin\Downloads\888 RAT 1.2.5\888 RAT 1.2.5\888 RAT 1.2.5.exe |
| Full analysis: | https://app.any.run/tasks/77dbda4e-716f-4cb7-8df0-bf757100963b |
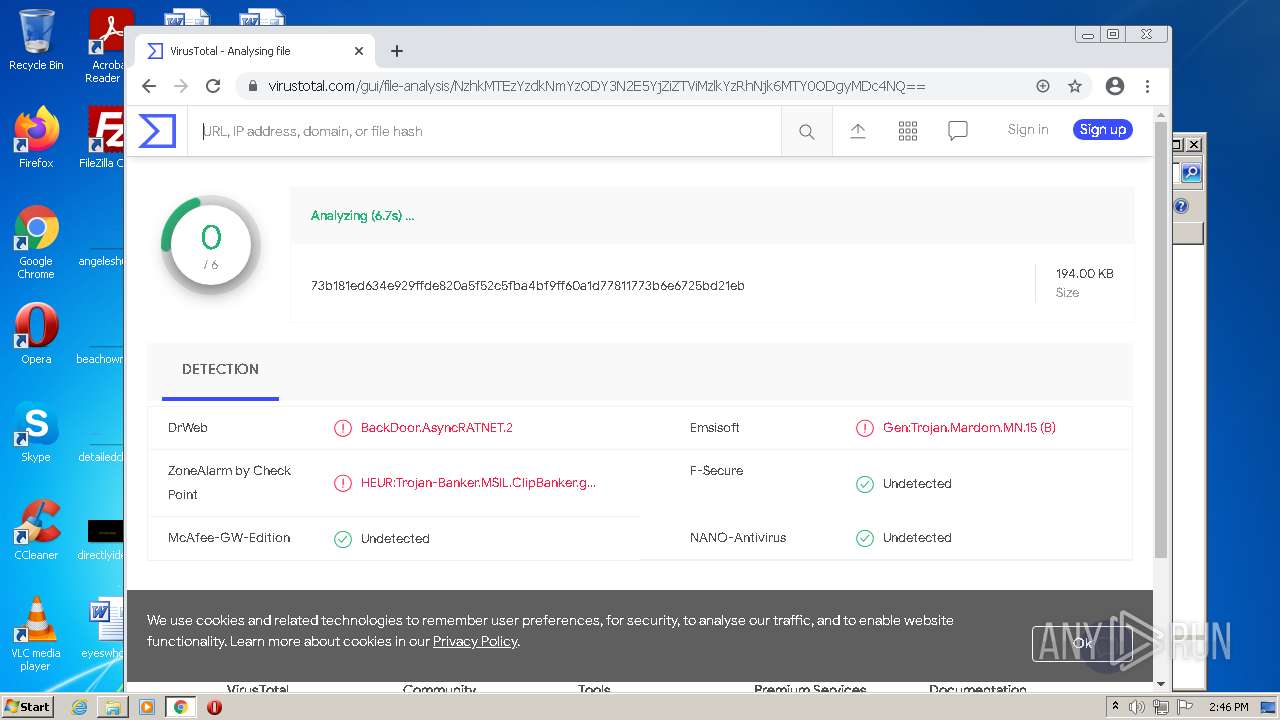
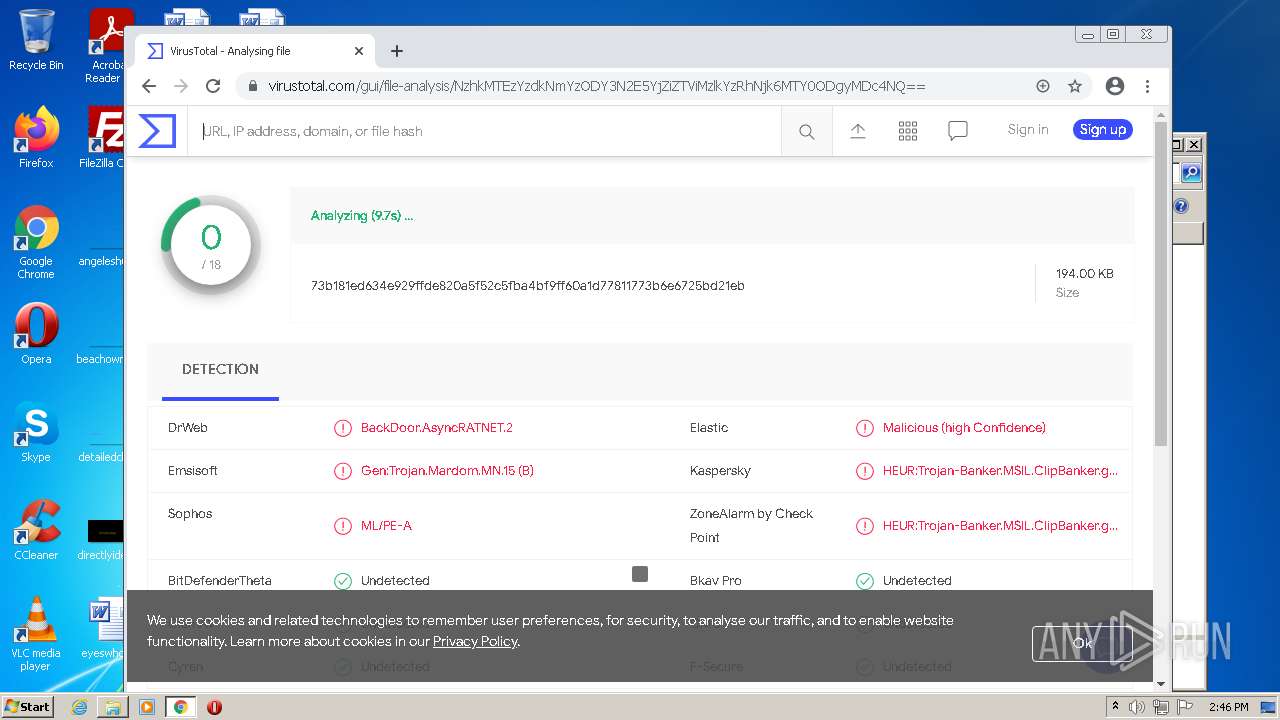
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 01, 2022, 13:44:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
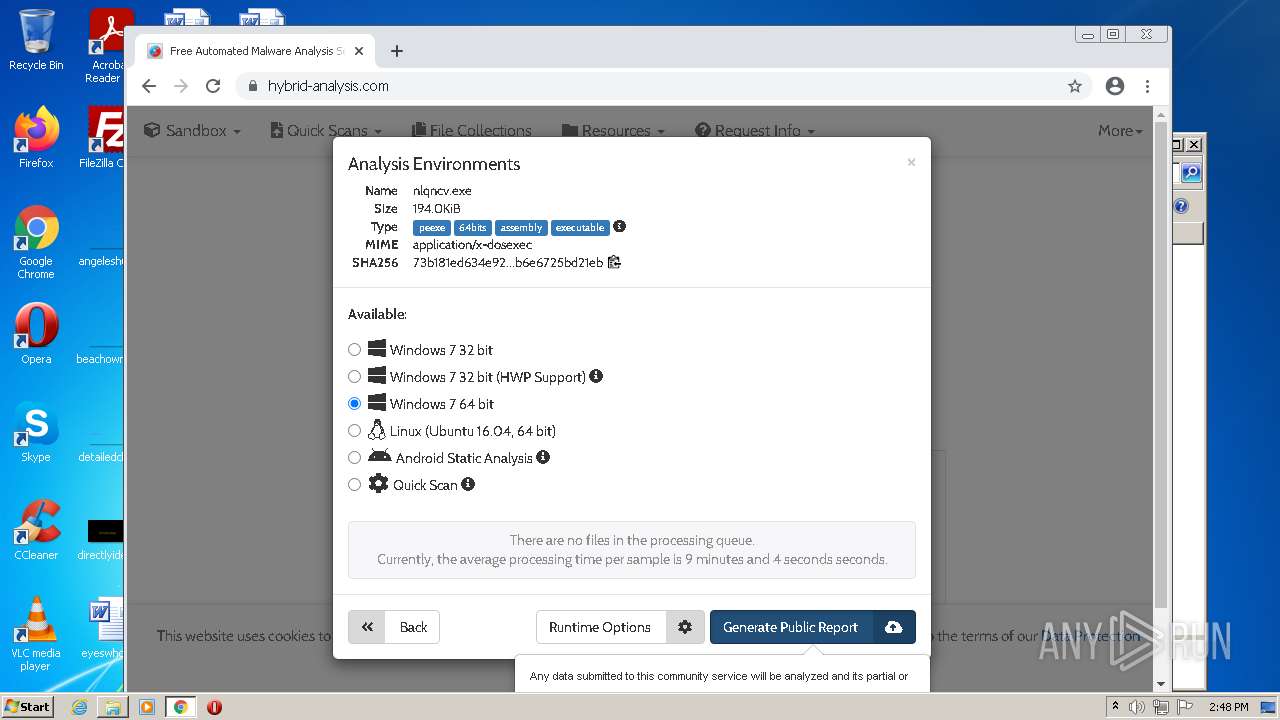
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
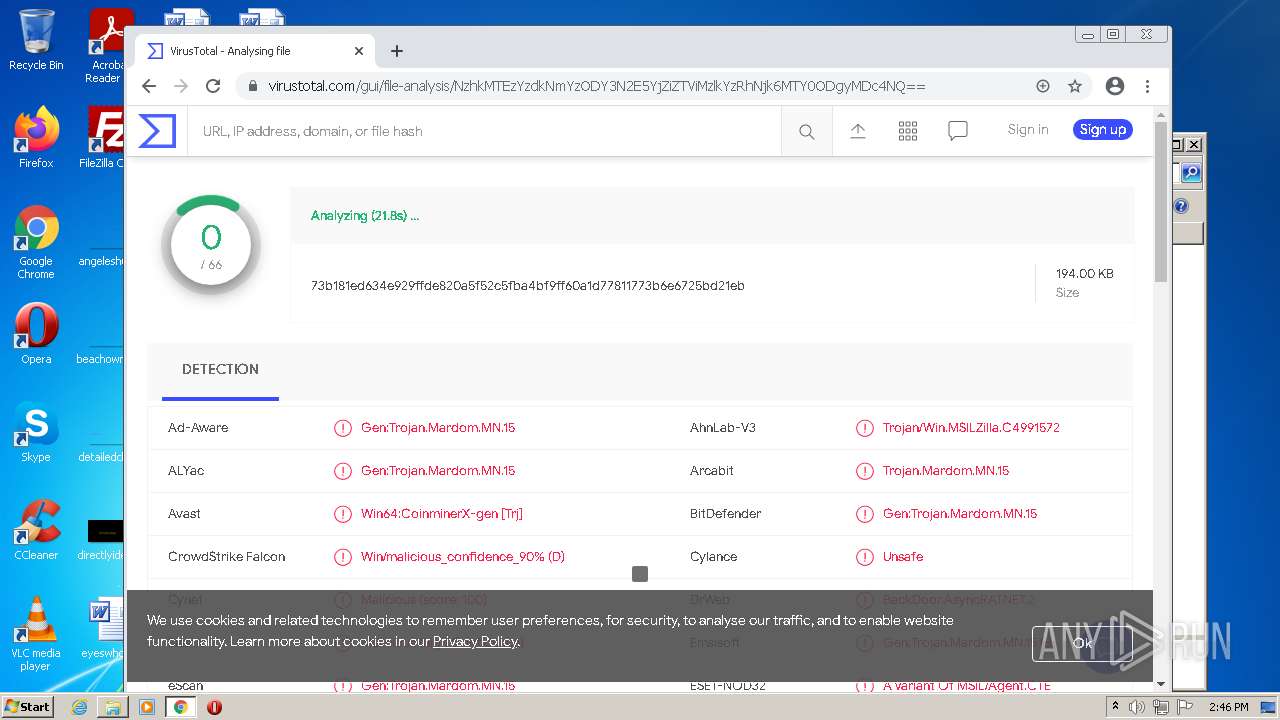
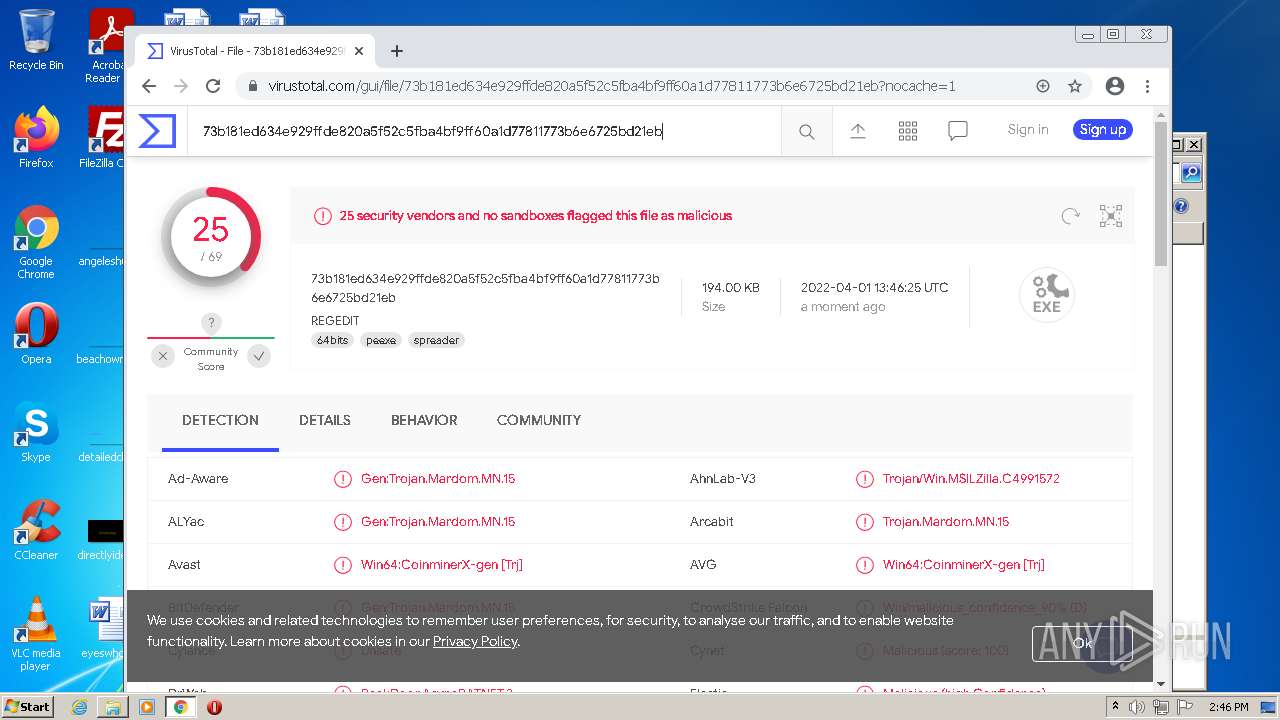
| MD5: | A6A36115E072D7EF31B40277E4695E2C |
| SHA1: | 7FC7F195266C8E362551C8FB6564CA97CE26DAD8 |
| SHA256: | 162C17601F3F2D8EDA02546E6EE08CABED5F01267FB75224073A3AC21F0CA3DC |
| SSDEEP: | 12288:CxnFyb6EQr8EBJufwbtUCnvohuDvm4z3idUuiAJ9S:CDyjQgEBXxnt |
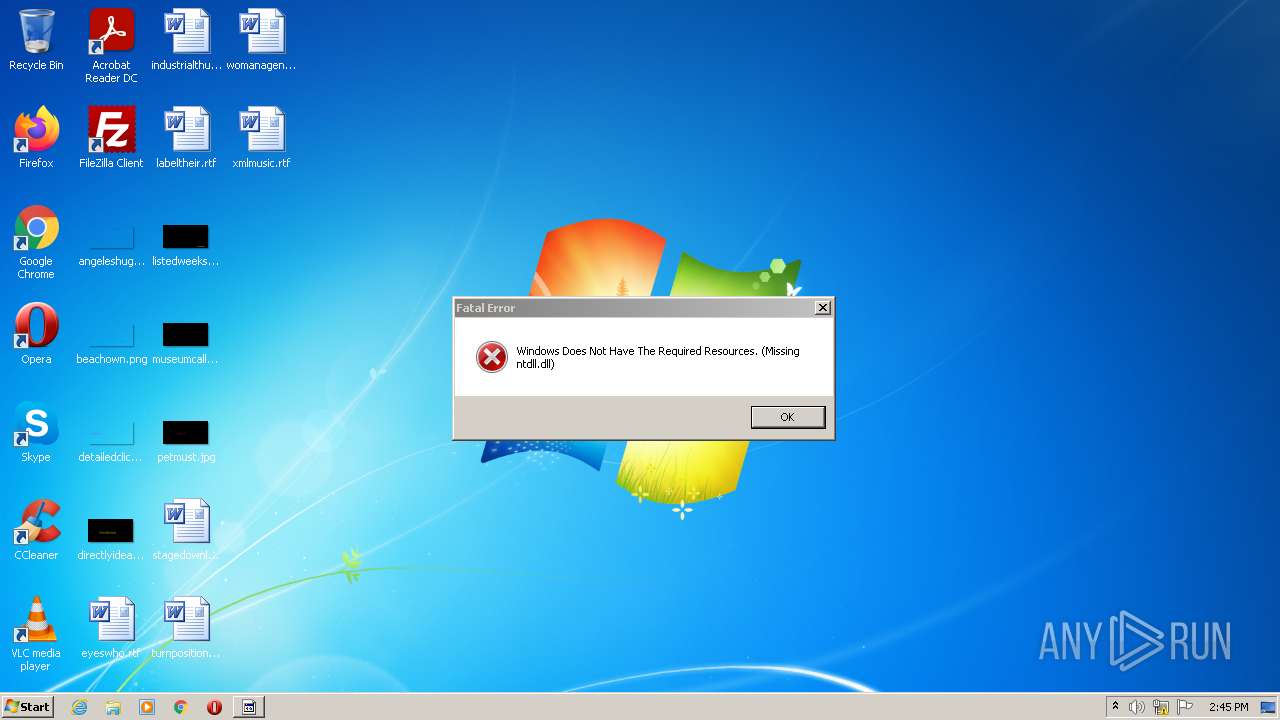
MALICIOUS
ASYNCRAT was detected
- 888 RAT 1.2.5.exe (PID: 3380)
Executes PowerShell scripts
- cmd.exe (PID: 3100)
ASYNCRAT detected by memory dumps
- 888 RAT 1.2.5.exe (PID: 3380)
SUSPICIOUS
Checks supported languages
- 888 RAT 1.2.5.exe (PID: 3380)
- 888 RAT 1.2.5.exe (PID: 3548)
- powershell.exe (PID: 1792)
- cmd.exe (PID: 3100)
Reads the computer name
- 888 RAT 1.2.5.exe (PID: 3380)
- 888 RAT 1.2.5.exe (PID: 3548)
- powershell.exe (PID: 1792)
Application launched itself
- 888 RAT 1.2.5.exe (PID: 3548)
Reads Environment values
- 888 RAT 1.2.5.exe (PID: 3380)
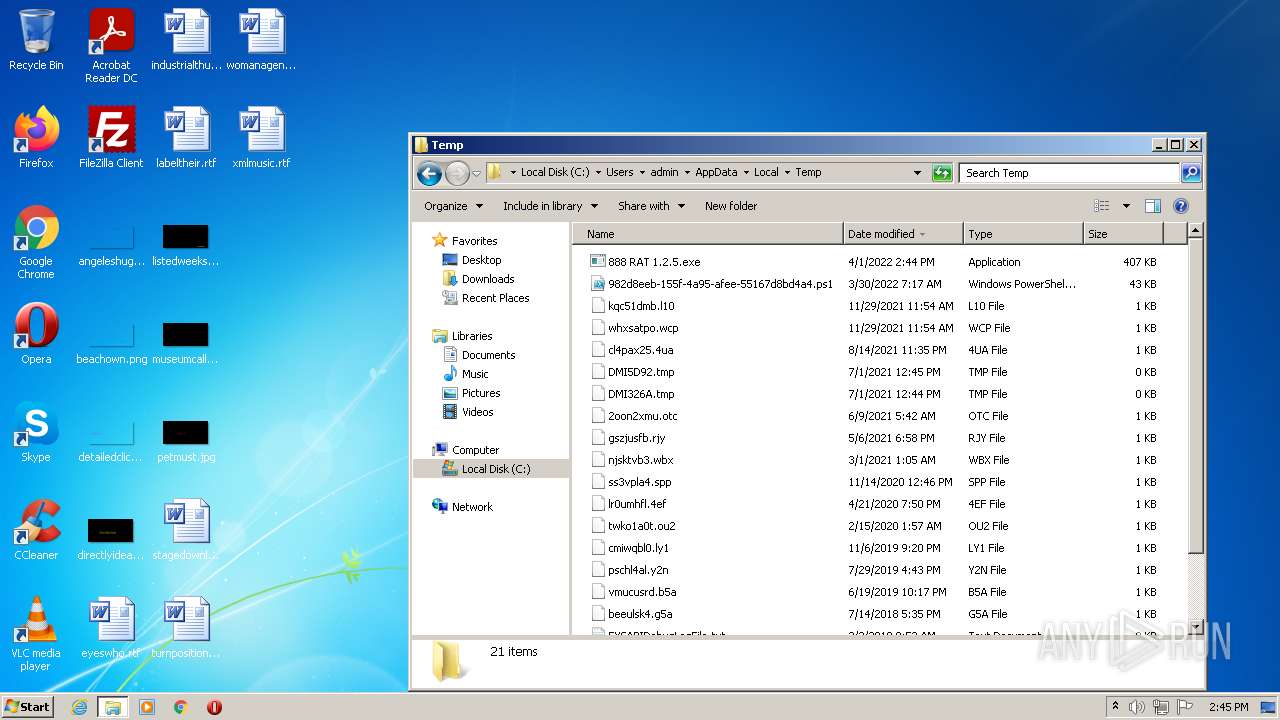
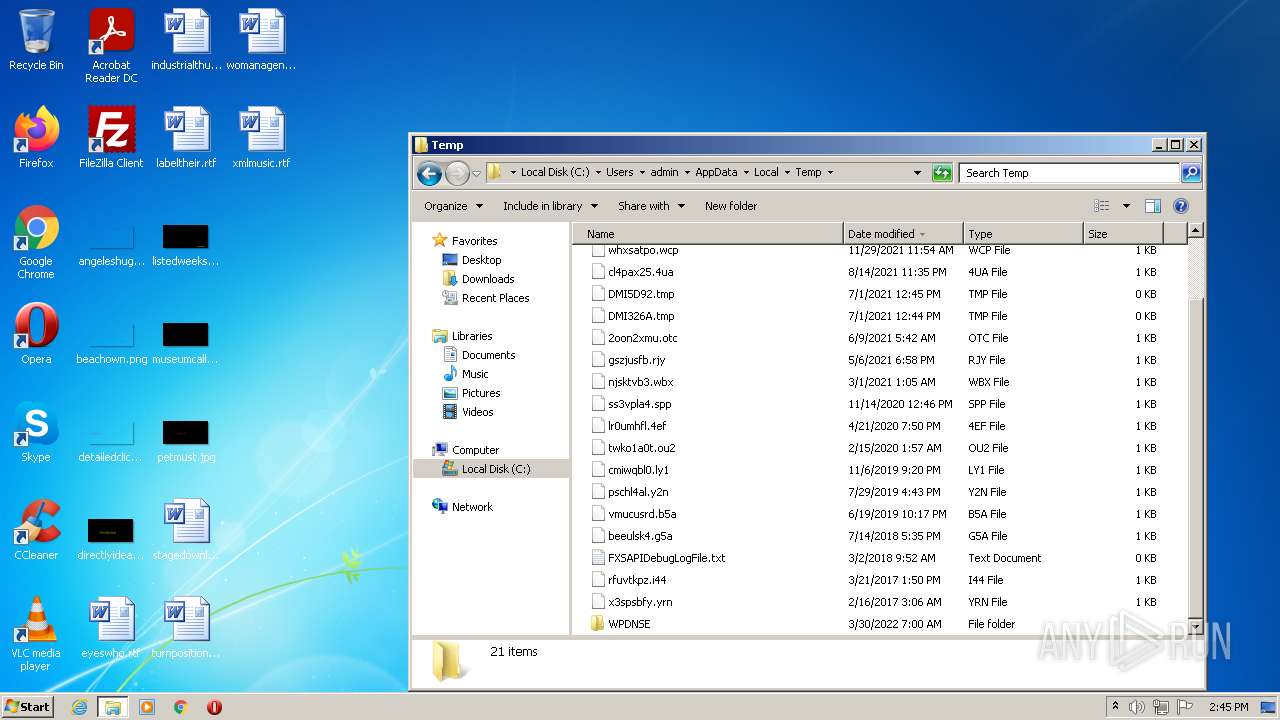
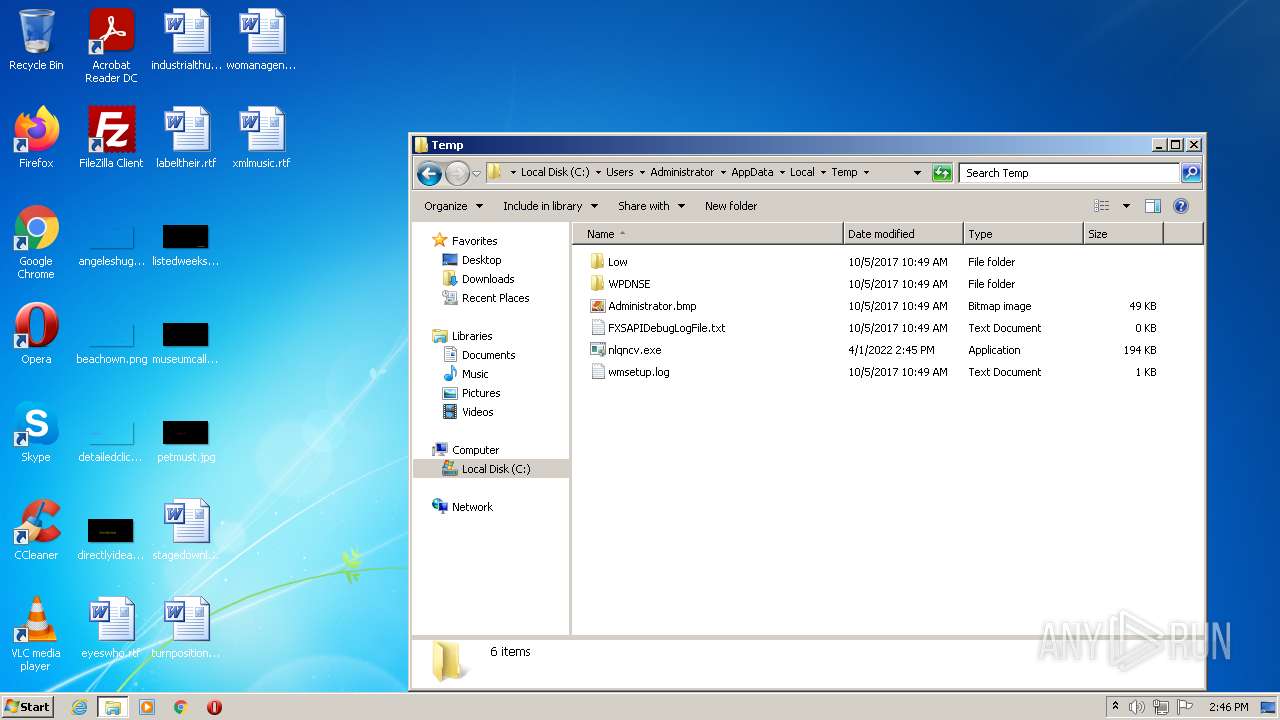
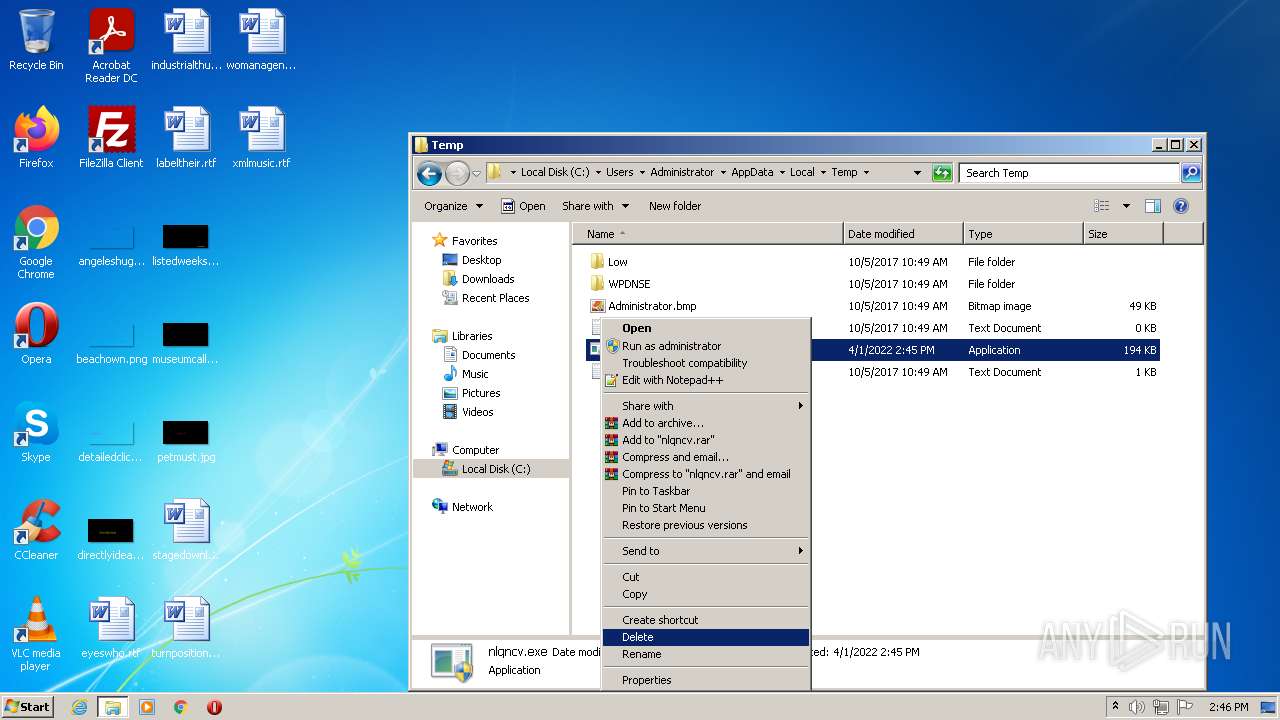
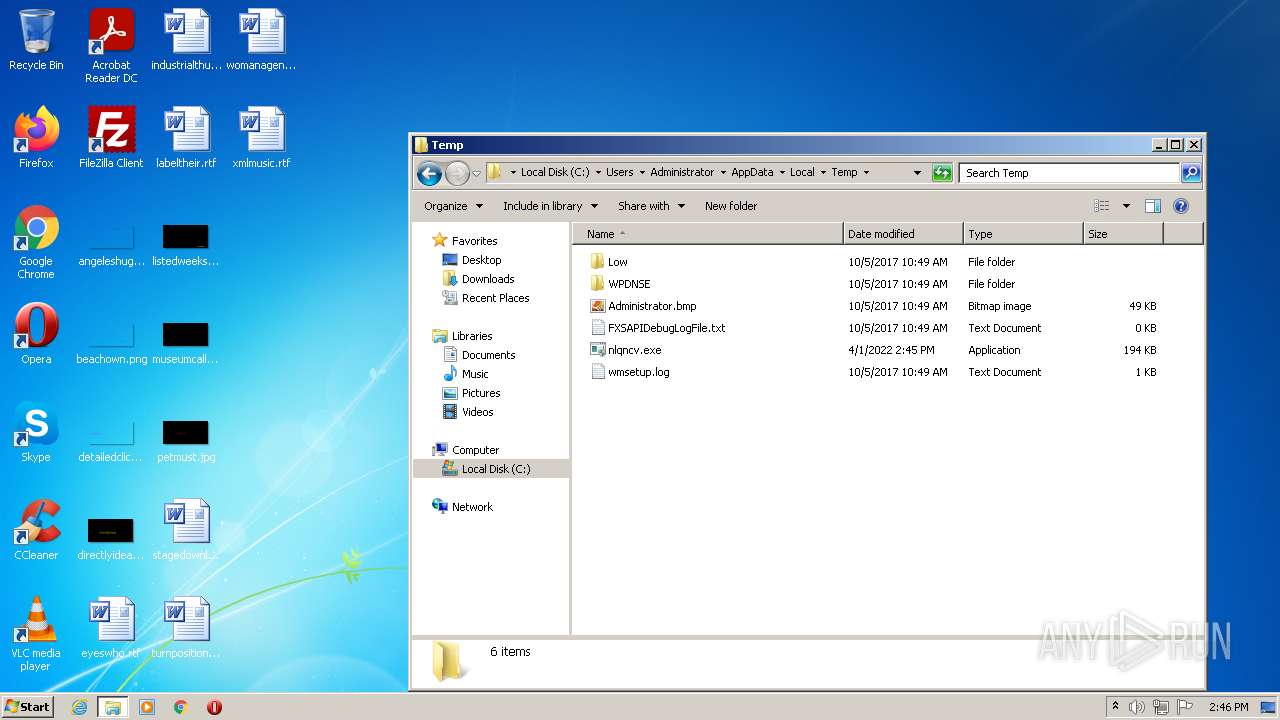
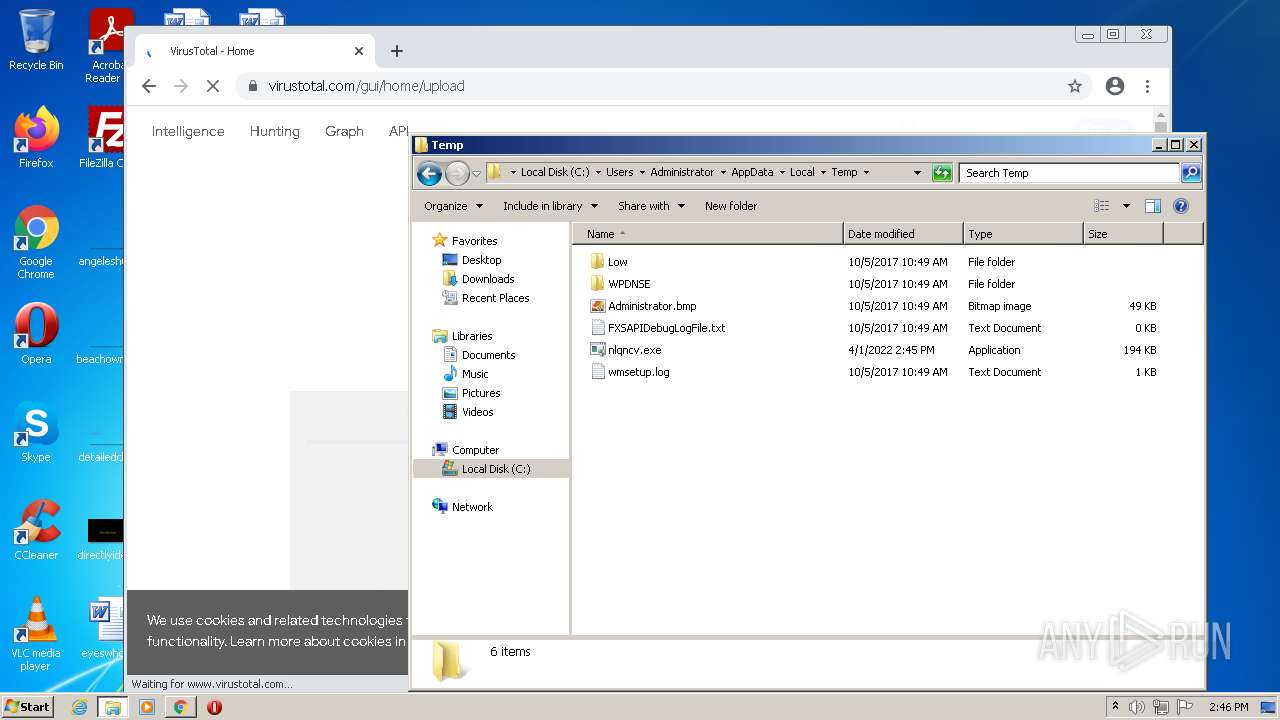
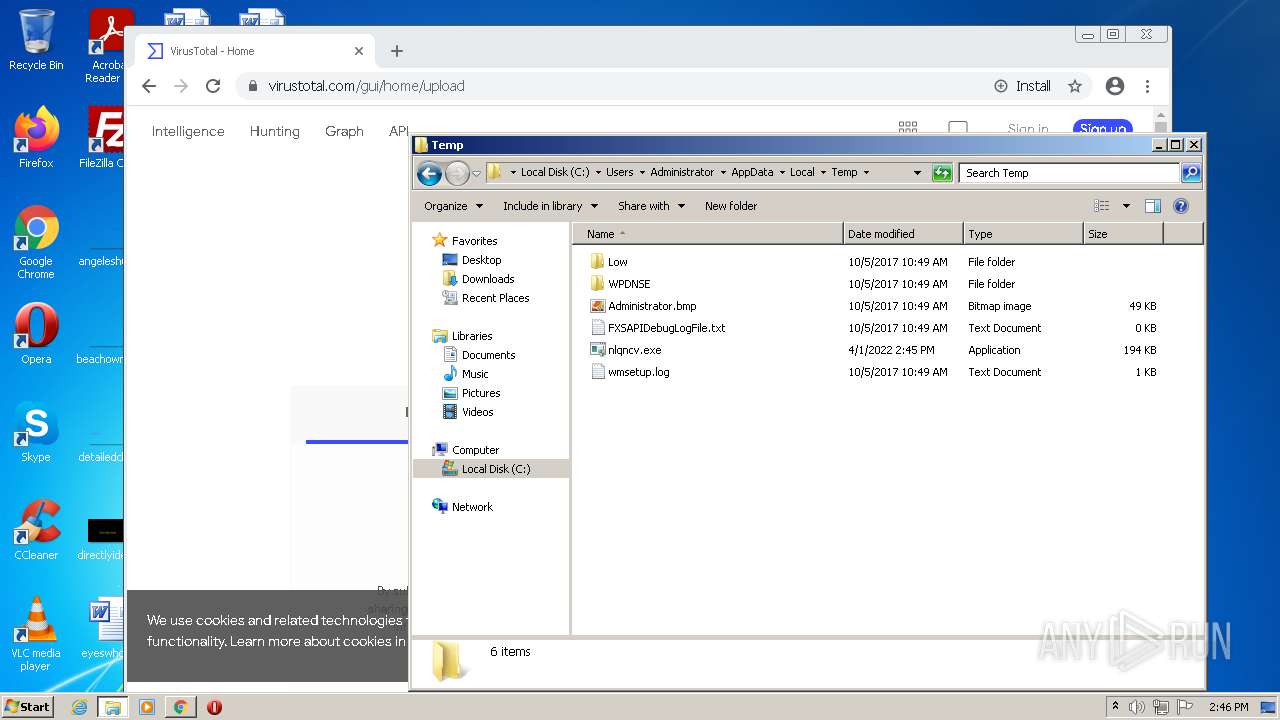
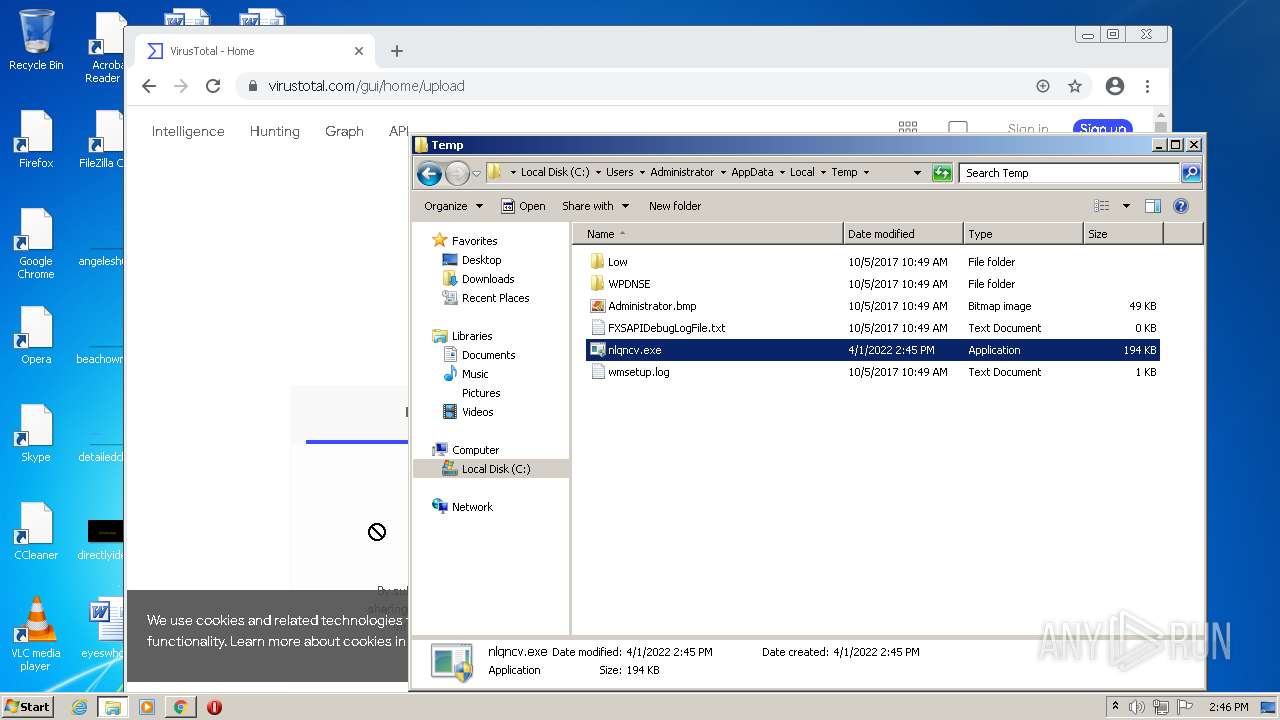
Executable content was dropped or overwritten
- 888 RAT 1.2.5.exe (PID: 3380)
Drops a file with a compile date too recent
- 888 RAT 1.2.5.exe (PID: 3380)
Starts CMD.EXE for commands execution
- 888 RAT 1.2.5.exe (PID: 3380)
Executed via COM
- DllHost.exe (PID: 2776)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2536)
INFO
Reads the computer name
- runas.exe (PID: 2984)
- explorer.exe (PID: 280)
- DllHost.exe (PID: 2776)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 1912)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 2348)
Checks supported languages
- runas.exe (PID: 2984)
- explorer.exe (PID: 280)
- DllHost.exe (PID: 2776)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 296)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 1912)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 620)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 3276)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 1660)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 448)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 1780)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 644)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 1020)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 2348)
Reads settings of System Certificates
- 888 RAT 1.2.5.exe (PID: 3380)
- chrome.exe (PID: 3384)
Checks Windows Trust Settings
- powershell.exe (PID: 1792)
Manual execution by user
- explorer.exe (PID: 280)
- chrome.exe (PID: 2536)
Application launched itself
- chrome.exe (PID: 2536)
Reads the hosts file
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3384)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2536)
Reads the date of Windows installation
- chrome.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(3380) 888 RAT 1.2.5.exe
Server107.182.237.14:58453
Version0.5.7B
Autorunfalse
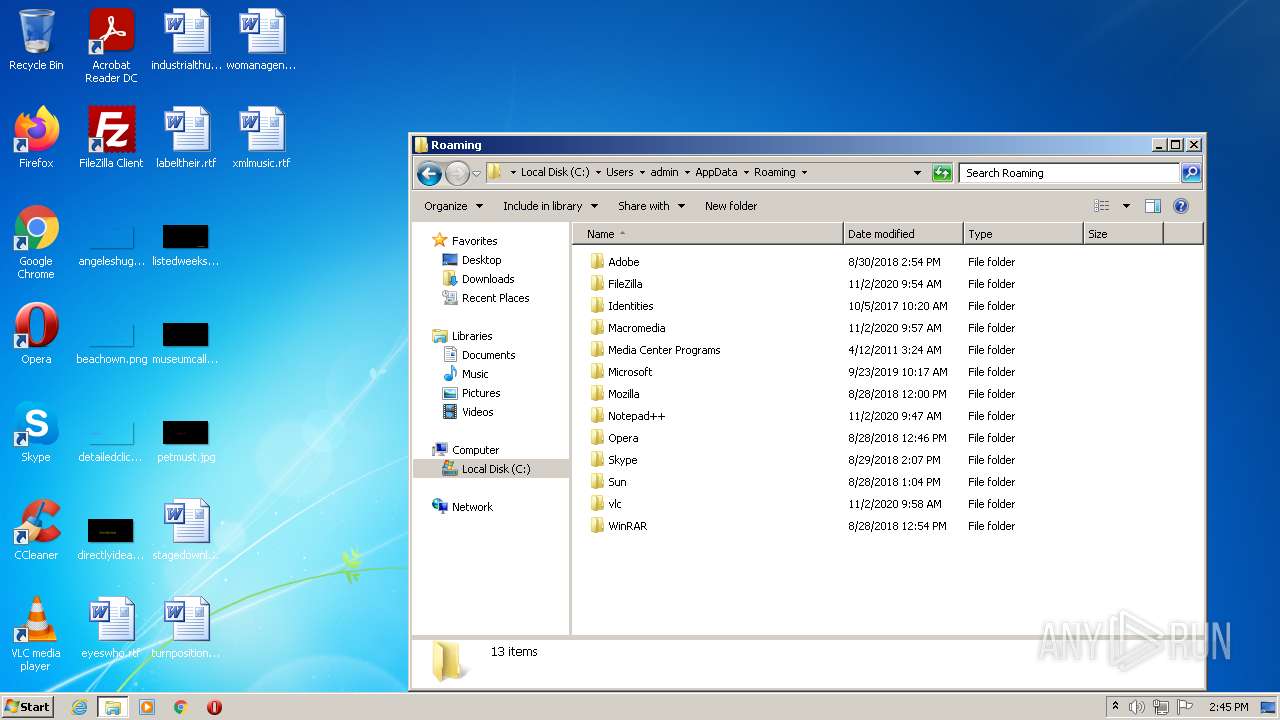
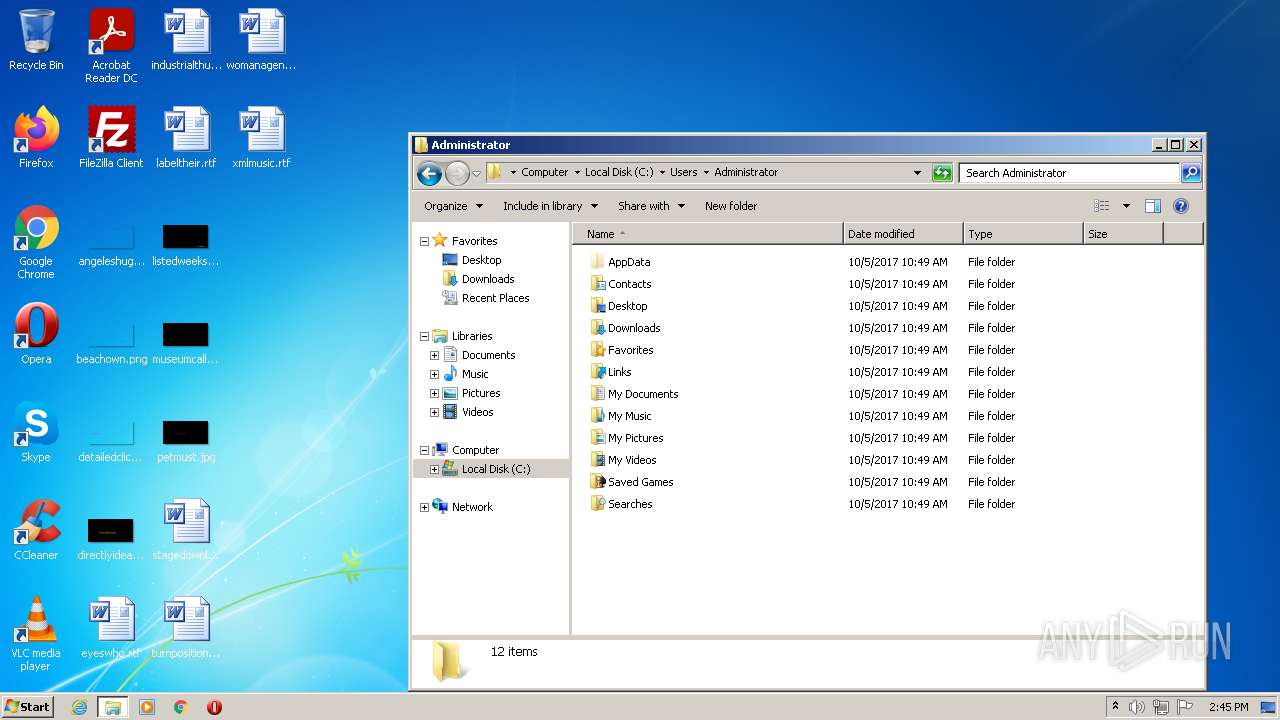
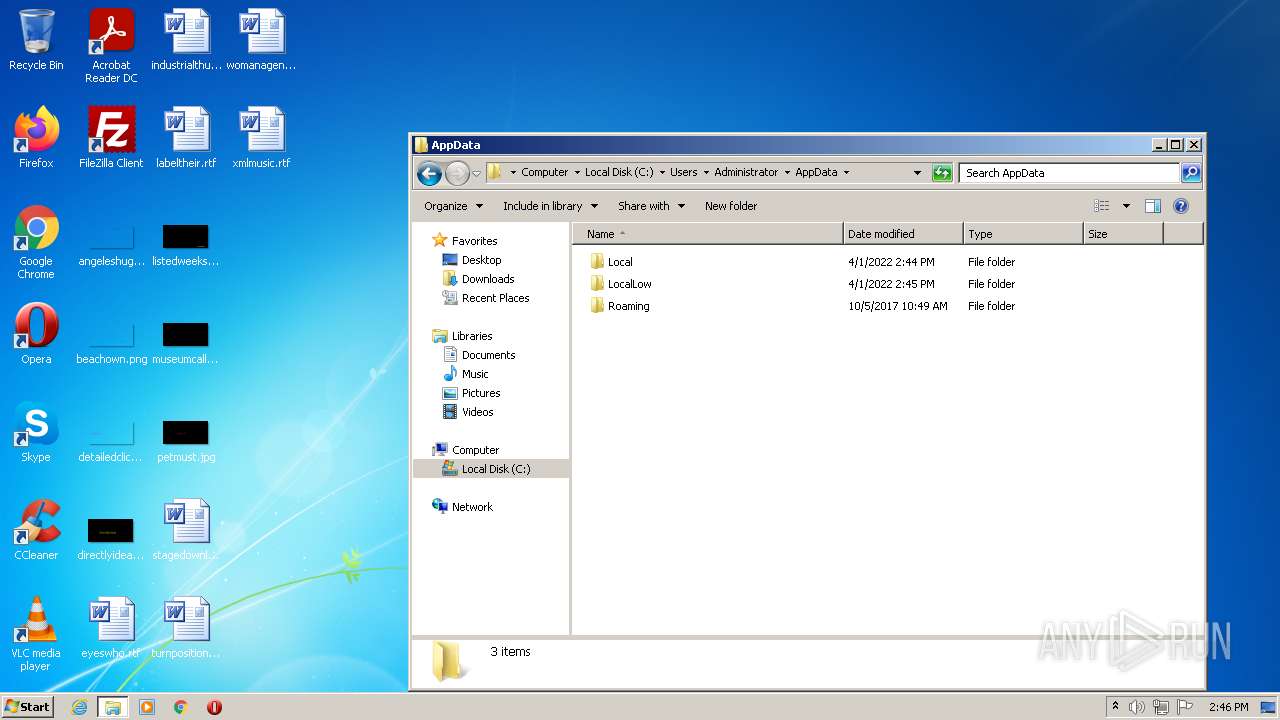
Install_folder%AppData%
Install_name
AES_keyc2e9cd50b361b7c674861998b299a96da9c6230c967d2116a2174d52a82d446e
Master_KeyxDFtehsPUQK7KtOxsih2eEjxKpuVWEmj
MutexAsyncMutex_6SI8OkPnk
CertificateMIIFEjCCAvqgAwIBAgIQANXQK3BKcW2UaY1IuHx6GTANBgkqhkiG9w0BAQ0FADAqMSgwJgYDVQQDDB9Bc3luY1JBVCBTZXJ2ZXIxMDFnYWdlMTAxMjAyMzAzMCAXDTIyMDEyNTIwNTkyNloYDzk5OTkxMjMxMjM1OTU5WjAqMSgwJgYDVQQDDB9Bc3luY1JBVCBTZXJ2ZXIxMDFnYWdlMTAxMjAyMzAzMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAgtUz5BoPZZP40lEpdu5IxYOOPgoc6M2a...
Server_SignaturebCnavONR3CAGg8c/7bujeInli6dJw2TuK28+DbCE2mEZ0/AS8jE6OMFsxiZw7U1BU0n0LtGL7ZebbVU+RZWbURGpac7s1k5C6iUJzapoEugIJ8hfJYduP4QQ9LXxz0pu3ZtPJjtW8j4iK5ysL6dGzr3qrPgGj73qi/mCotlWv2tivWrtkxOBDOm7bPu2LlOtXYF747LM/K8CY5rawhfNAC8YHFQXTK+IoCyTg4LZ8PggPy0fSfzXGPBlxJ/IbzJoJcdDLDWq8xAbTkFTlJt7jYXh7YfNrsyJzb3GF26Mk7F7...
Anti_VMfalse
Pastebin_Confignull
BSODfalse
Startup_delay3
GroupDefault
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:04:01 09:57:32+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 414208 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x671ee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Coin Toss |
| FileVersion: | 1.0.0.0 |
| InternalName: | zJ8BU.exe |
| LegalCopyright: | Copyright © 2016 |
| LegalTrademarks: | - |
| OriginalFileName: | zJ8BU.exe |
| ProductName: | Coin Toss |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2022 07:57:32 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Coin Toss |
| FileVersion: | 1.0.0.0 |
| InternalName: | zJ8BU.exe |
| LegalCopyright: | Copyright © 2016 |
| LegalTrademarks: | - |
| OriginalFilename: | zJ8BU.exe |
| ProductName: | Coin Toss |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Apr-2022 07:57:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000651F4 | 0x00065200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.0998 |
.rsrc | 0x00068000 | 0x00000598 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.06115 |
.reloc | 0x0006A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
98
Monitored processes
53
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1712 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3116 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2908 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,11451624927190370499,16878971235950674332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3288 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
20 641
Read events
20 475
Write events
154
Delete events
12
Modification events
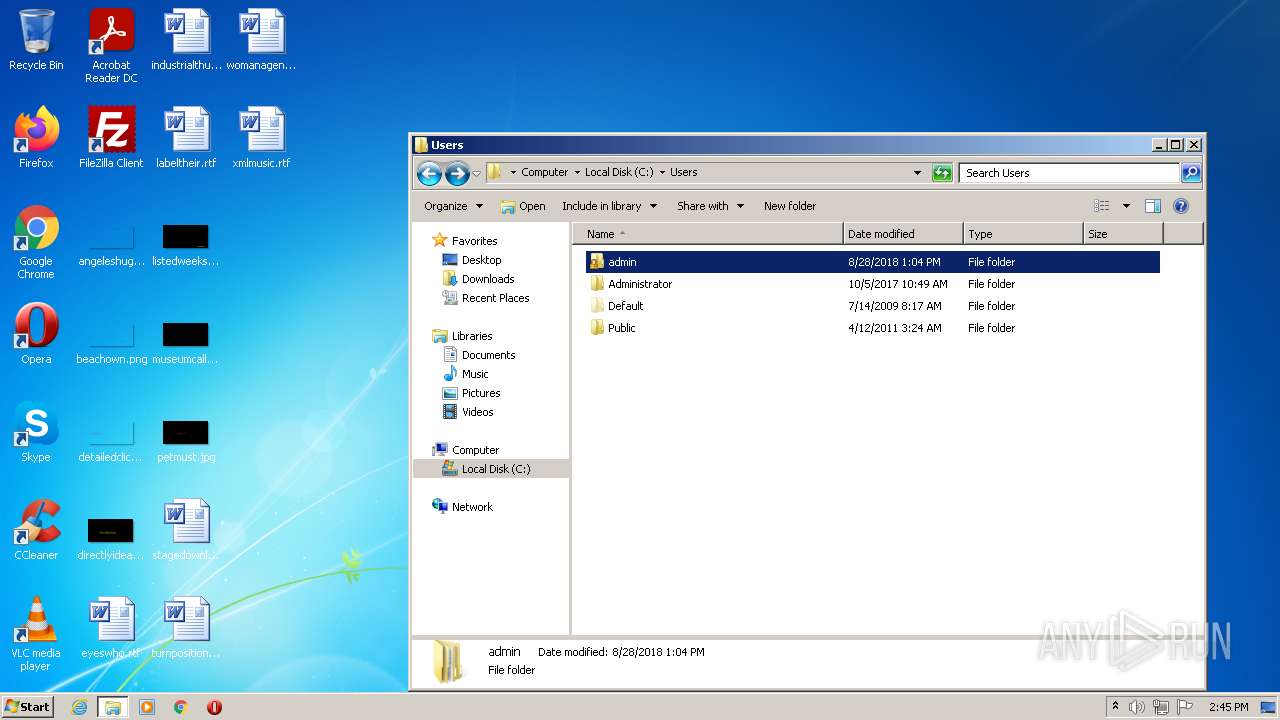
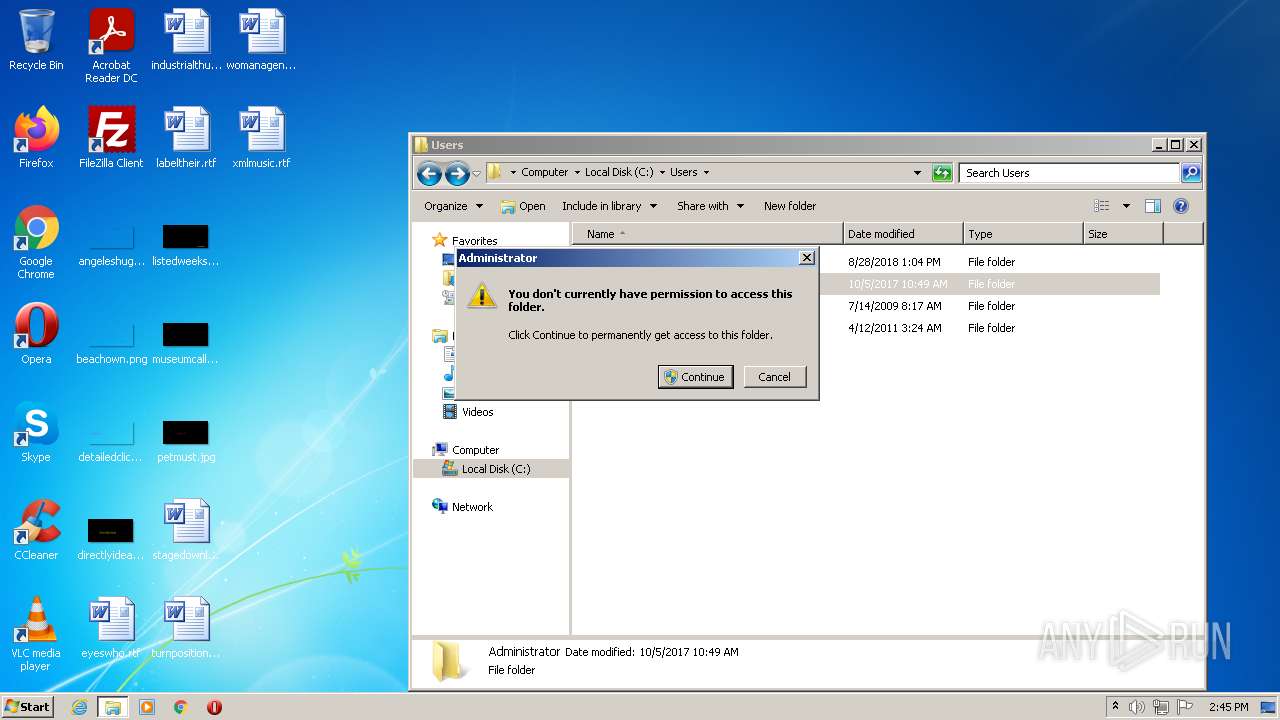
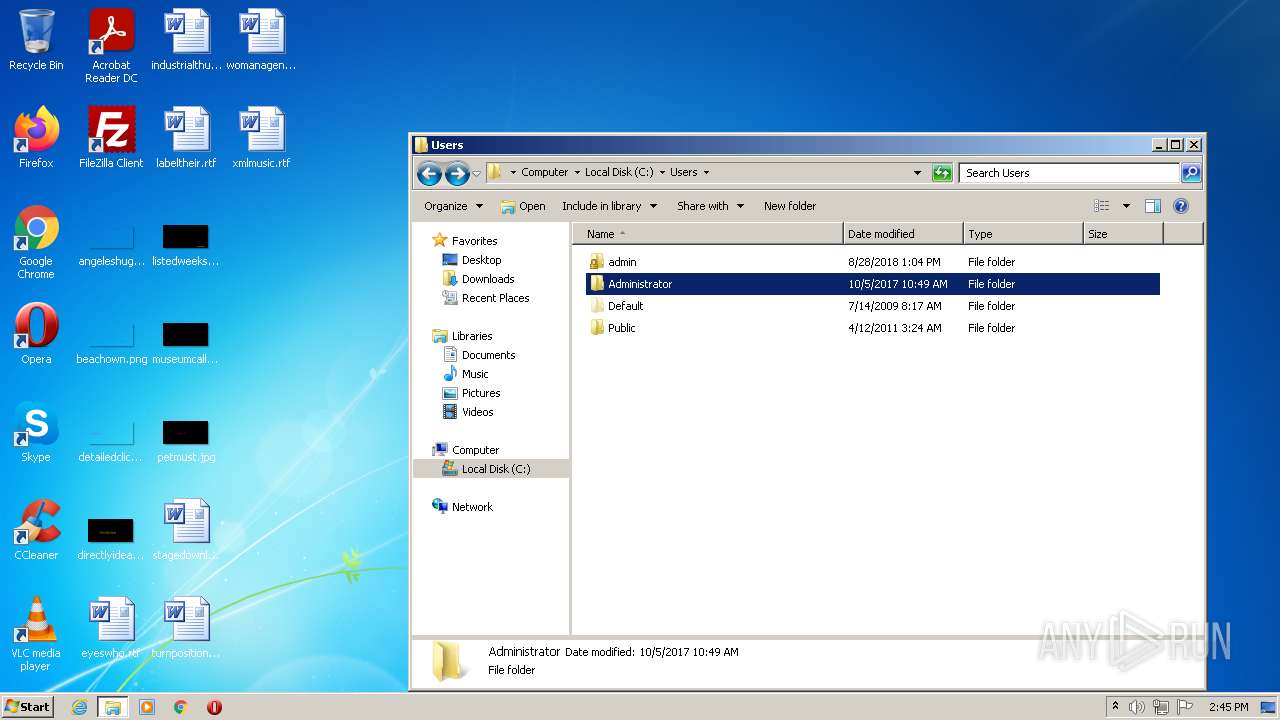
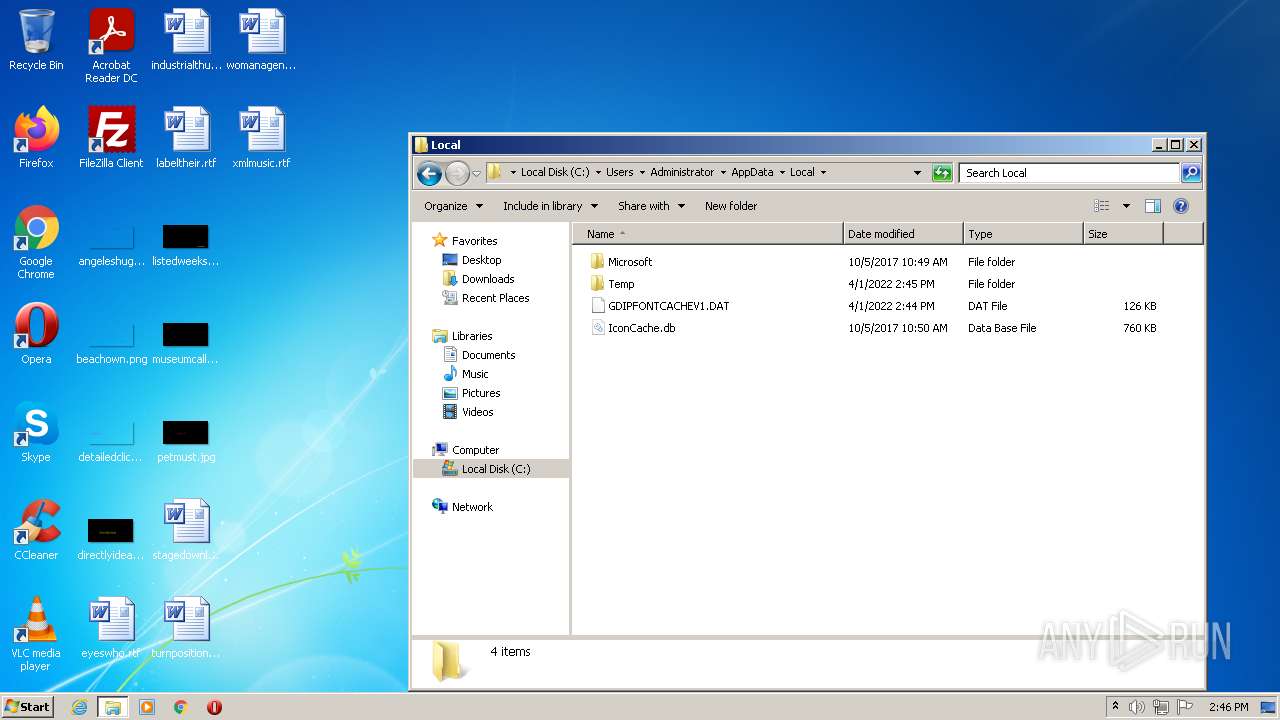
| (PID) Process: | (3548) 888 RAT 1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\GDIPlus |
| Operation: | write | Name: | FontCachePath |
Value: C:\Users\Administrator\AppData\Local | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (3380) 888 RAT 1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wuaueng.dll,-400 |
Value: Windows Update | |||
Executable files
1
Suspicious files
229
Text files
163
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62470220-9E8.pma | — | |
MD5:— | SHA256:— | |||
| 3380 | 888 RAT 1.2.5.exe | C:\Users\ADMINI~1\AppData\Local\Temp\Cab1AC8.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3380 | 888 RAT 1.2.5.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3380 | 888 RAT 1.2.5.exe | C:\Users\ADMINI~1\AppData\Local\Temp\Tar1AC9.tmp | cat | |
MD5:— | SHA256:— | |||
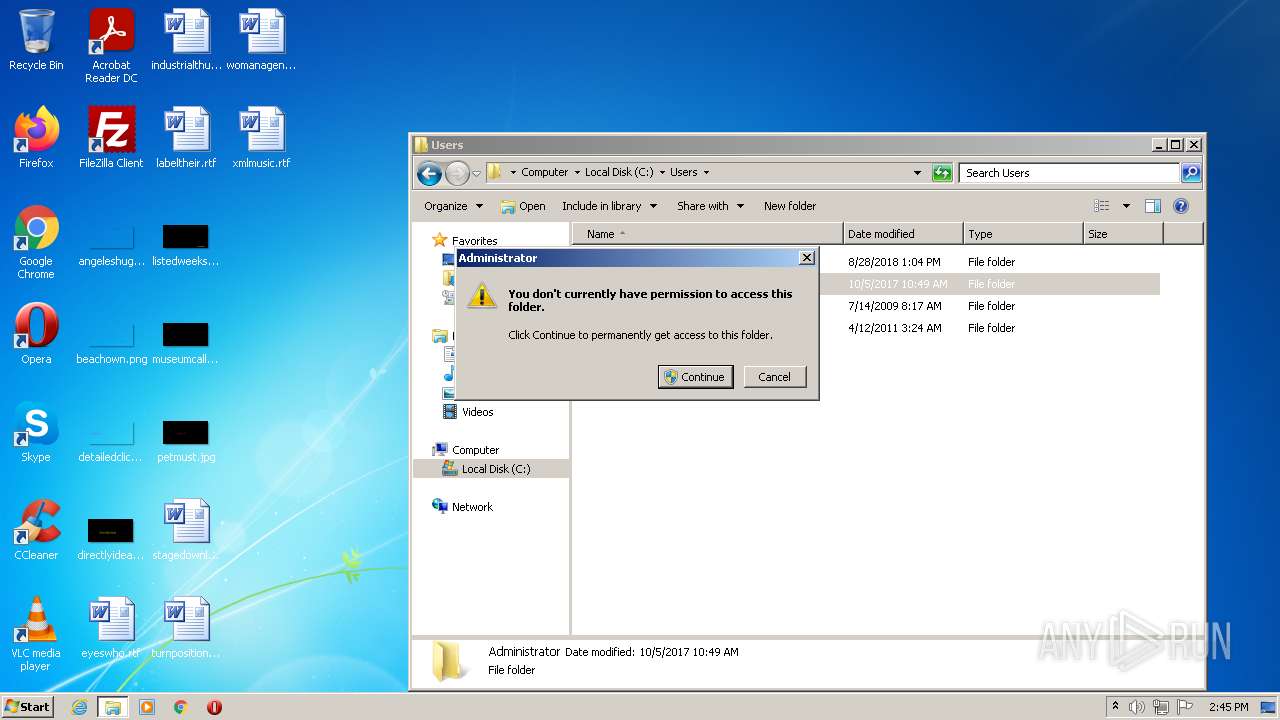
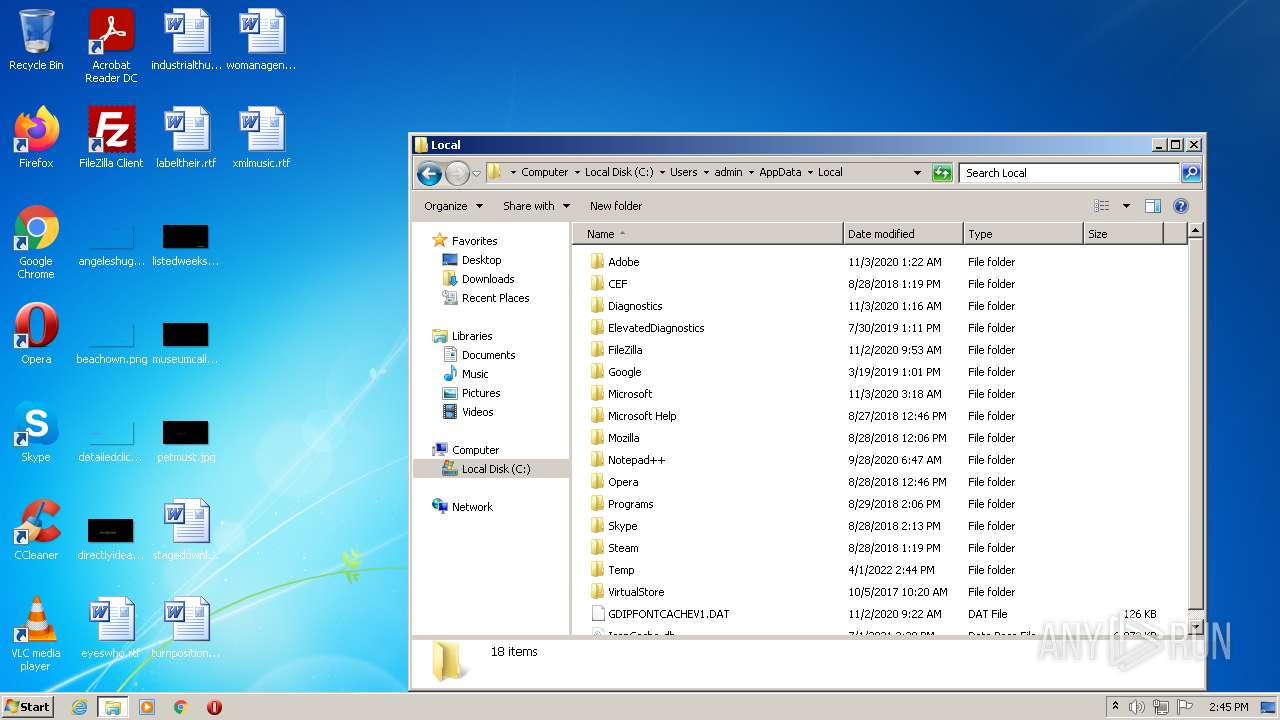
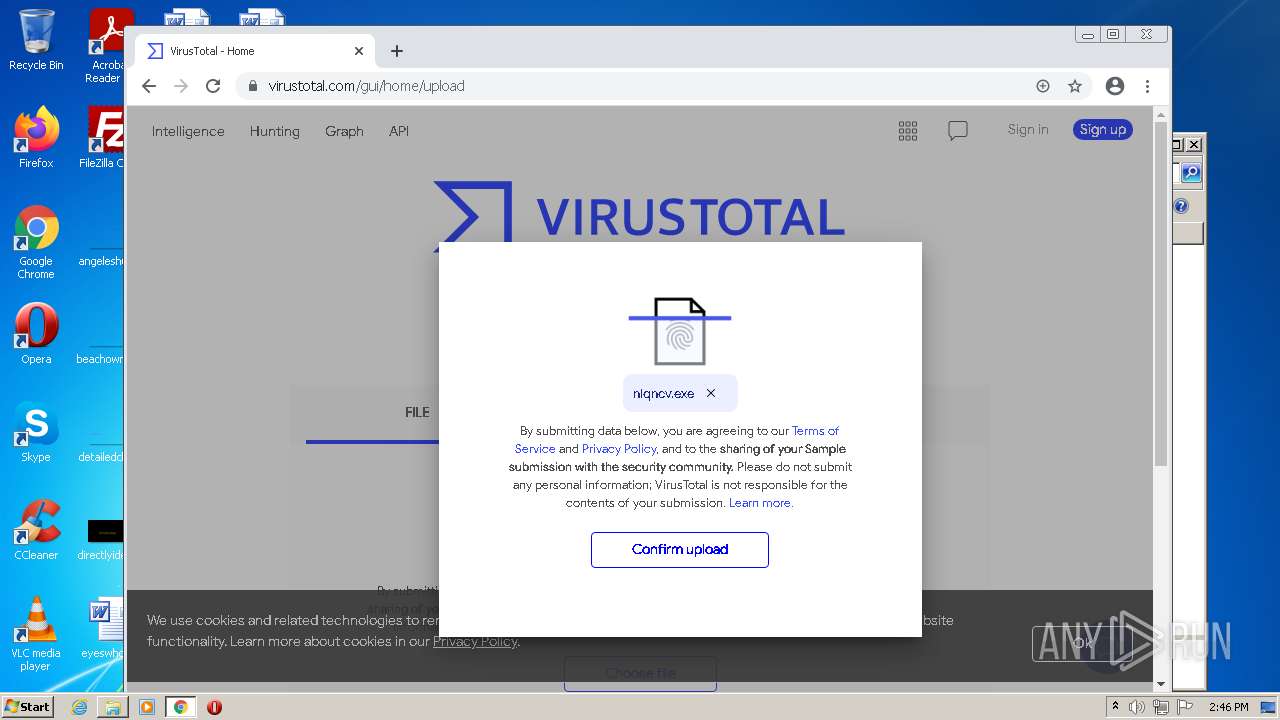
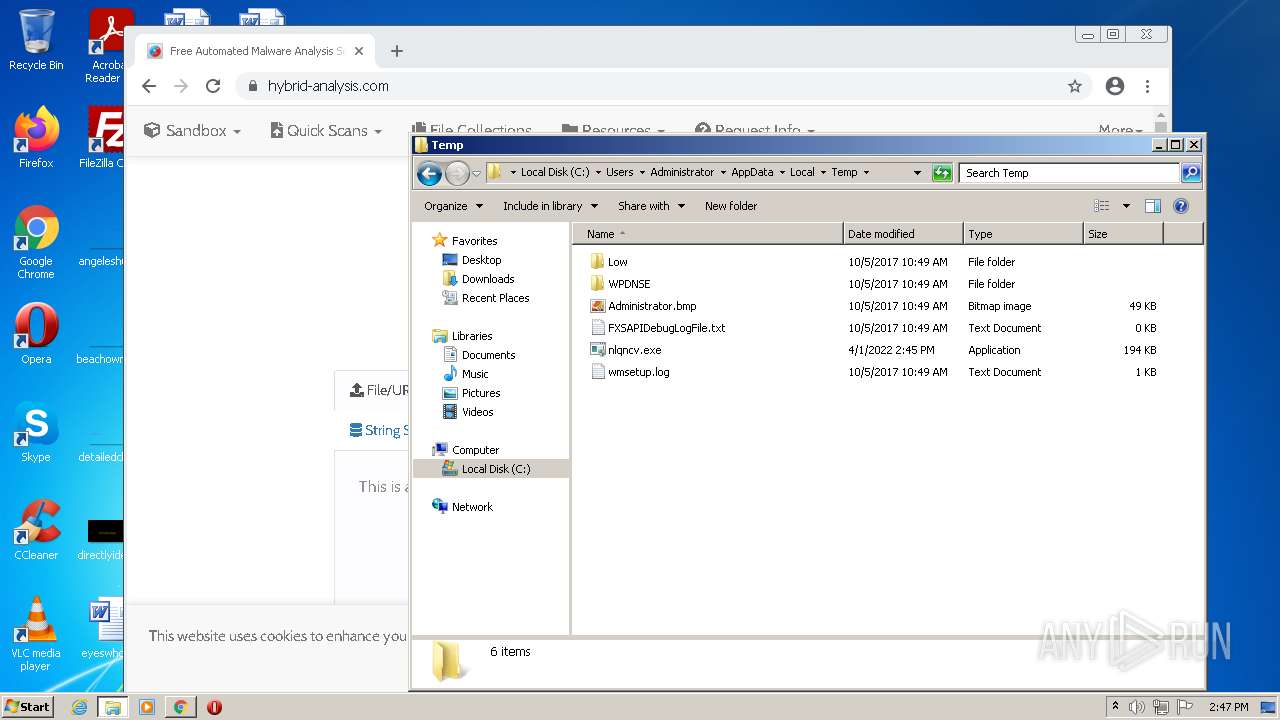
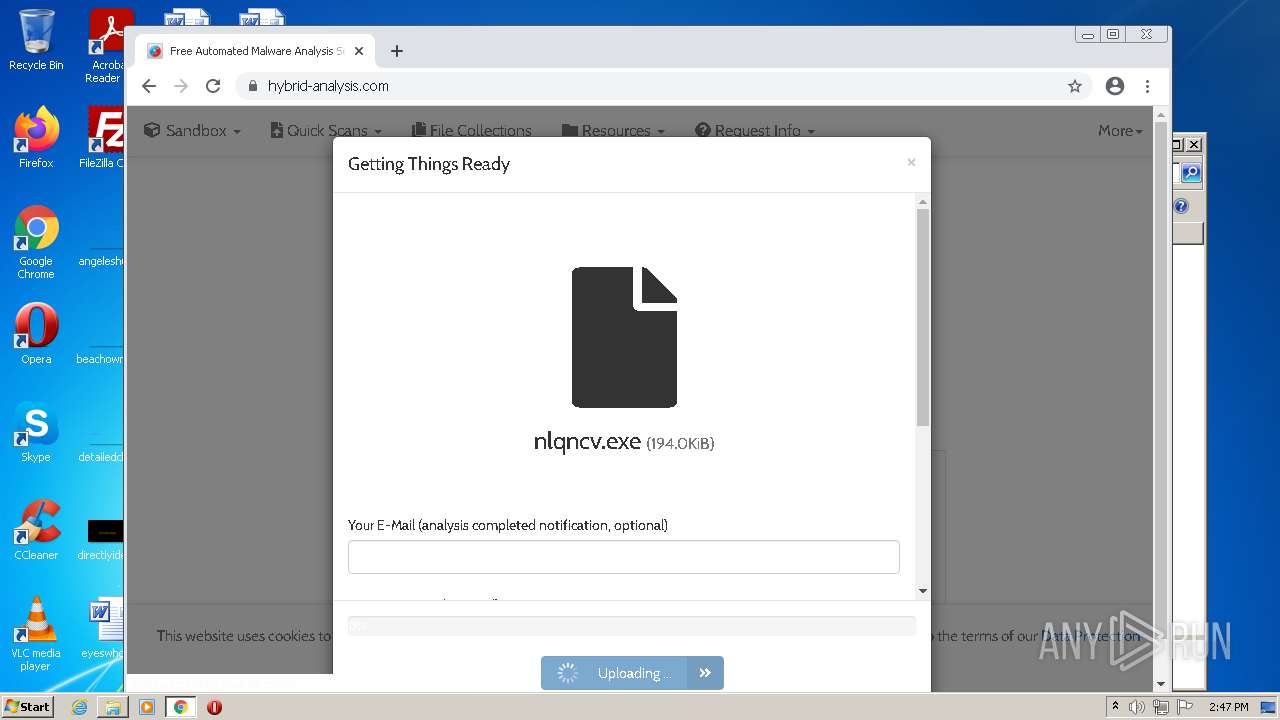
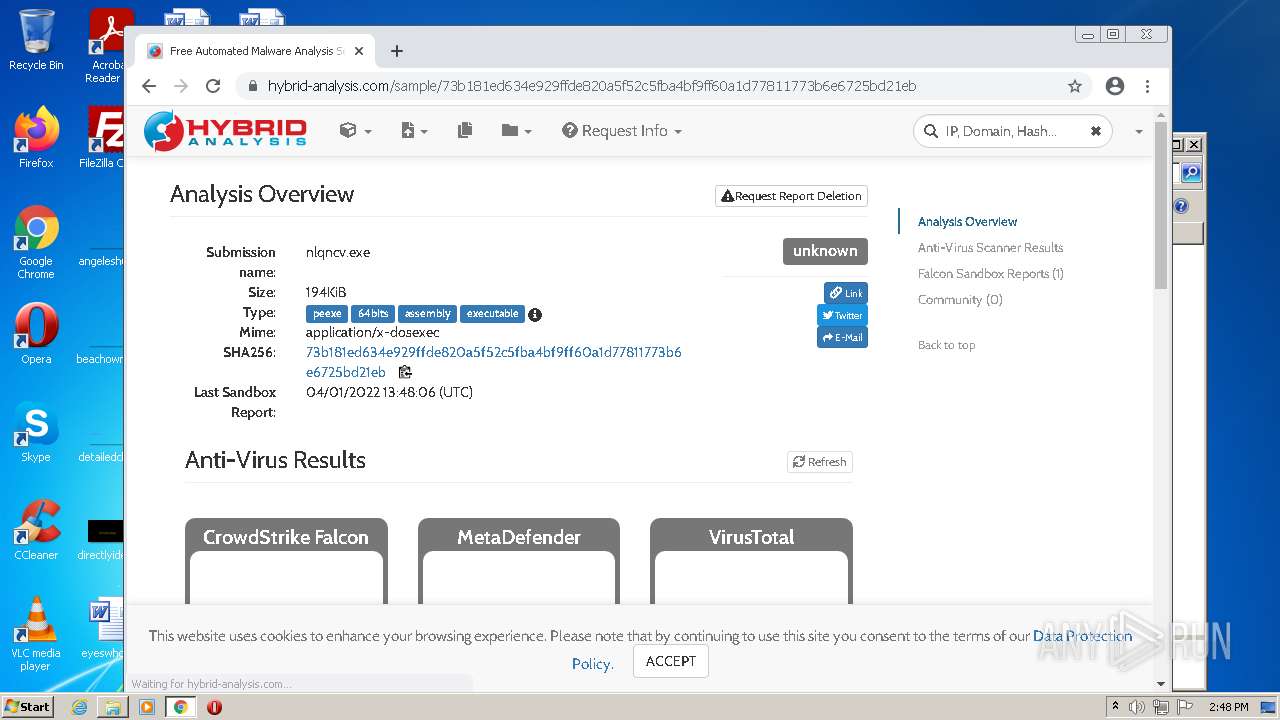
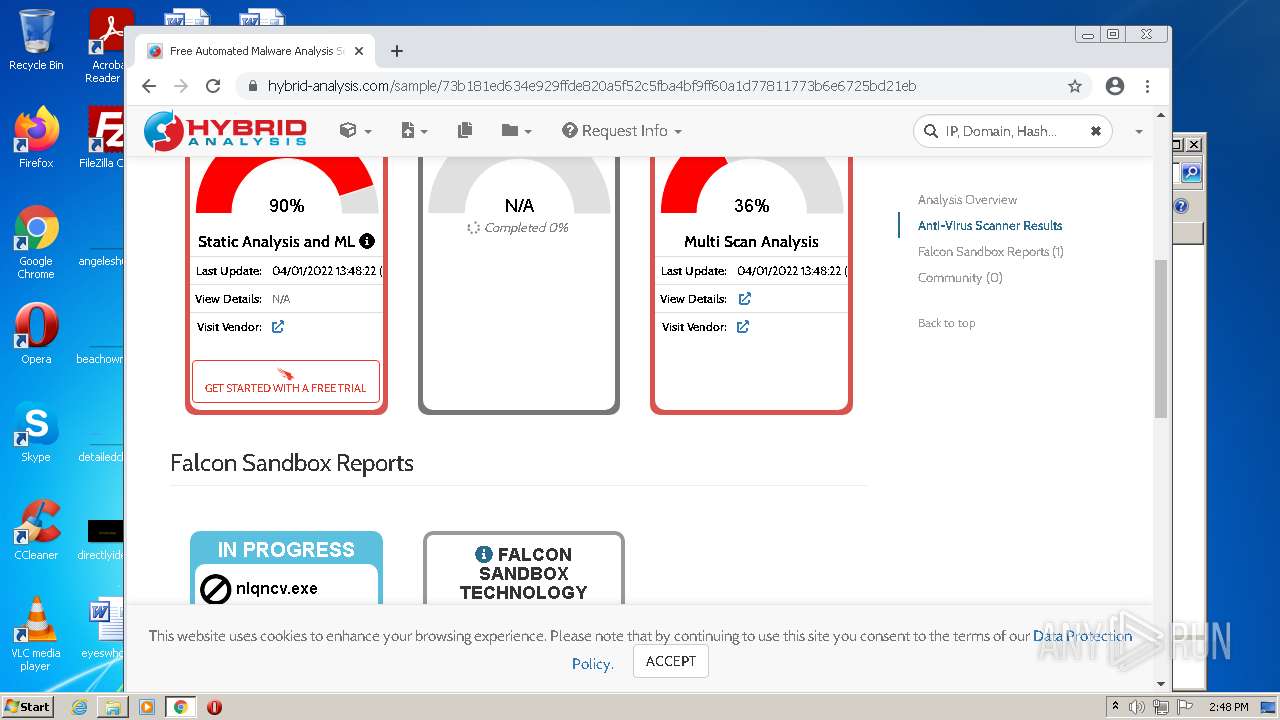
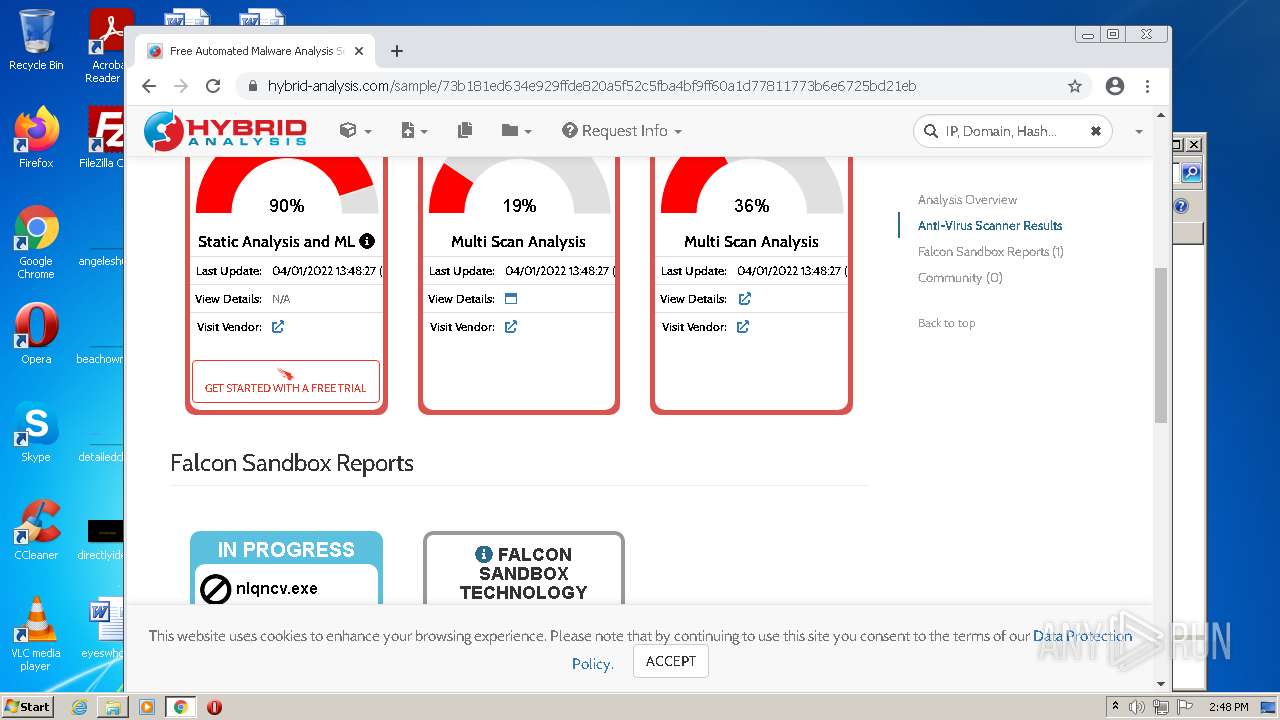
| 3380 | 888 RAT 1.2.5.exe | C:\Users\Administrator\AppData\Local\Temp\nlqncv.exe | executable | |
MD5:— | SHA256:— | |||
| 3380 | 888 RAT 1.2.5.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2776 | DllHost.exe | C:\Users\Administrator\ntuser.dat | hiv | |
MD5:— | SHA256:— | |||
| 1792 | powershell.exe | C:\Users\Administrator\AppData\Local\Temp\zvt4ipbs.25s.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1792 | powershell.exe | C:\Users\Administrator\AppData\Local\Temp\y5ygcupk.knx.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1792 | powershell.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
42
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | chrome.exe | GET | 302 | 216.239.34.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
3384 | chrome.exe | GET | 301 | 172.66.40.54:80 | http://hybrid-analysis.com/ | US | — | — | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/anhvlng3efkhijm4zc33nftnny_7250/hfnkpimlhhgieaddgfemjhofmfblmnib_7250_all_idpguze2vrtp7yzqdybzdwjxd4.crx3 | US | — | — | whitelisted |
— | — | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad4t5gyopw4e6ilqvowclo6tma_50/khaoiebndkojlmppeemjhbpbandiljpe_50_win_acsga3m25g3ggyskzfftlfgdr7aq.crx3 | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/anhvlng3efkhijm4zc33nftnny_7250/hfnkpimlhhgieaddgfemjhofmfblmnib_7250_all_idpguze2vrtp7yzqdybzdwjxd4.crx3 | US | binary | 5.67 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/anhvlng3efkhijm4zc33nftnny_7250/hfnkpimlhhgieaddgfemjhofmfblmnib_7250_all_idpguze2vrtp7yzqdybzdwjxd4.crx3 | US | binary | 9.28 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6ioqohe4v2uzgmdk4cg6iwyq6q_2022.3.28.1141/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.3.28.1141_all_ad2642qicjxpnvhlrxrsgp77tika.crx3 | US | binary | 429 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 718 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 358 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 429 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | 888 RAT 1.2.5.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3380 | 888 RAT 1.2.5.exe | 107.182.237.14:58453 | — | Hosting Services, Inc. | US | malicious |
3384 | chrome.exe | 142.250.186.36:443 | www.google.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 142.250.184.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
3384 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 142.250.186.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 142.250.184.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 142.250.185.195:443 | update.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3380 | 888 RAT 1.2.5.exe | A Network Trojan was detected | ET TROJAN Observed Malicious SSL Cert (AsyncRAT Server) |
3380 | 888 RAT 1.2.5.exe | A Network Trojan was detected | ET TROJAN Generic AsyncRAT Style SSL Cert |