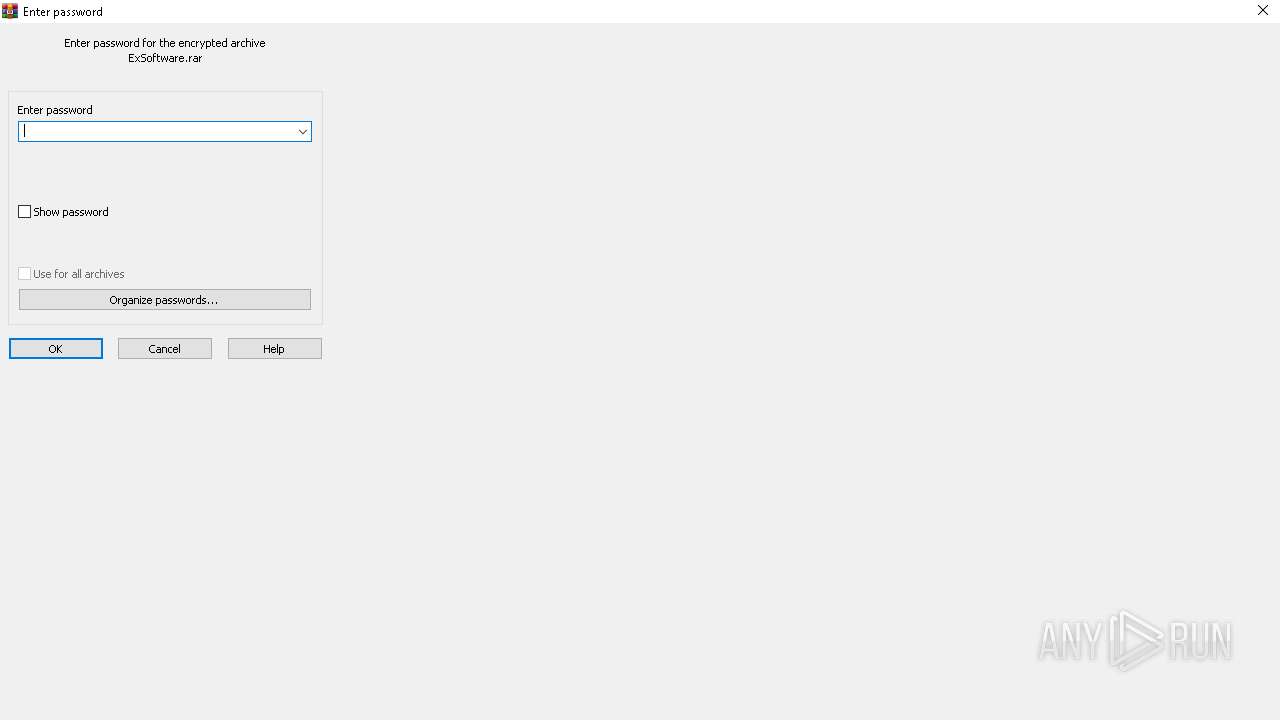
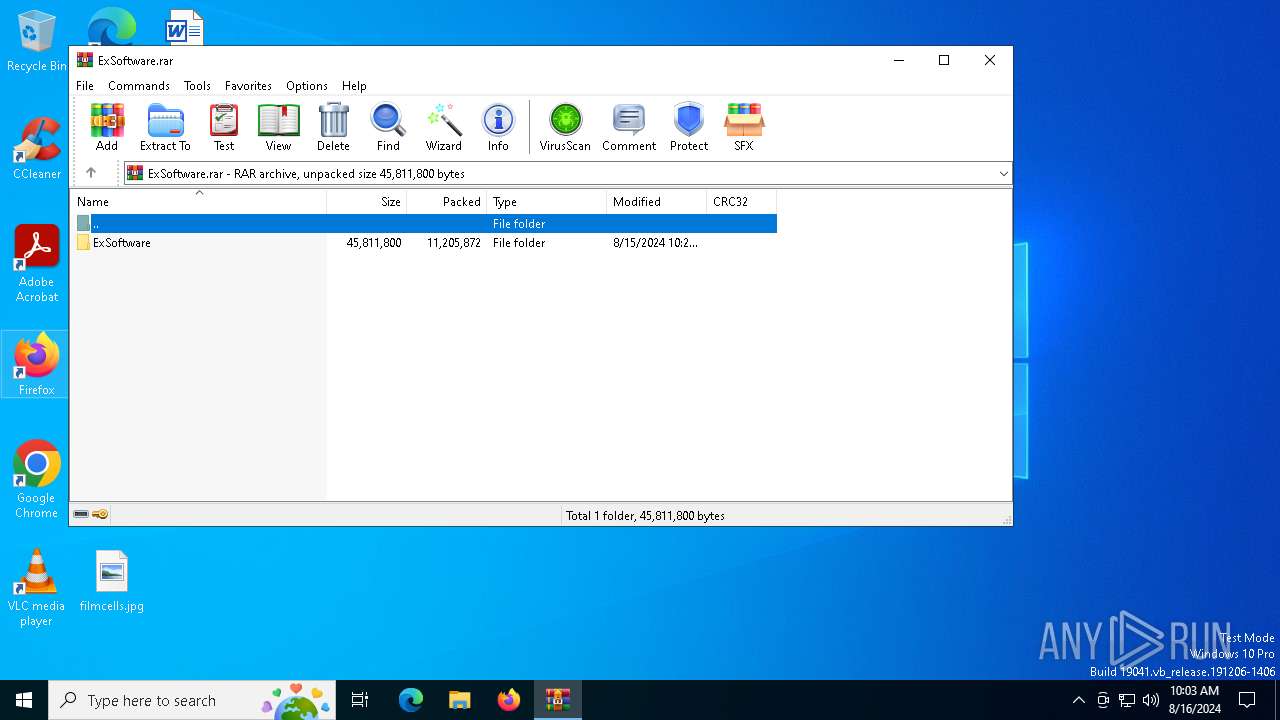
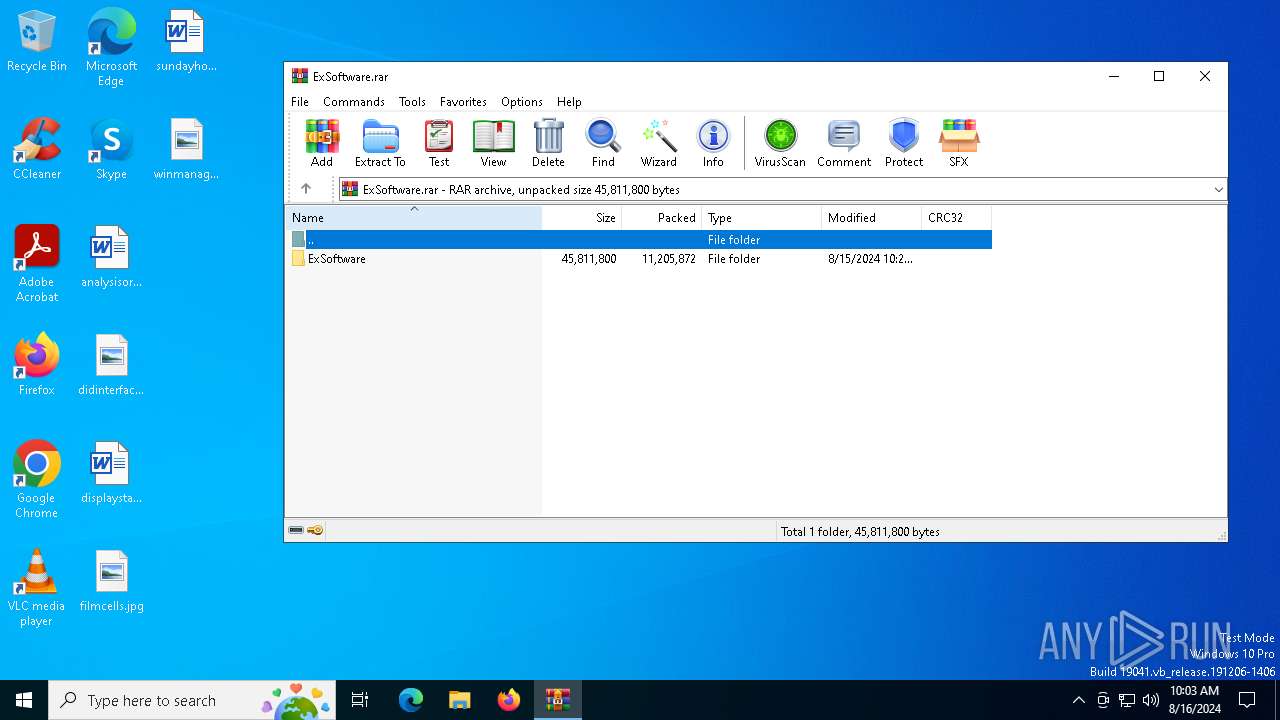
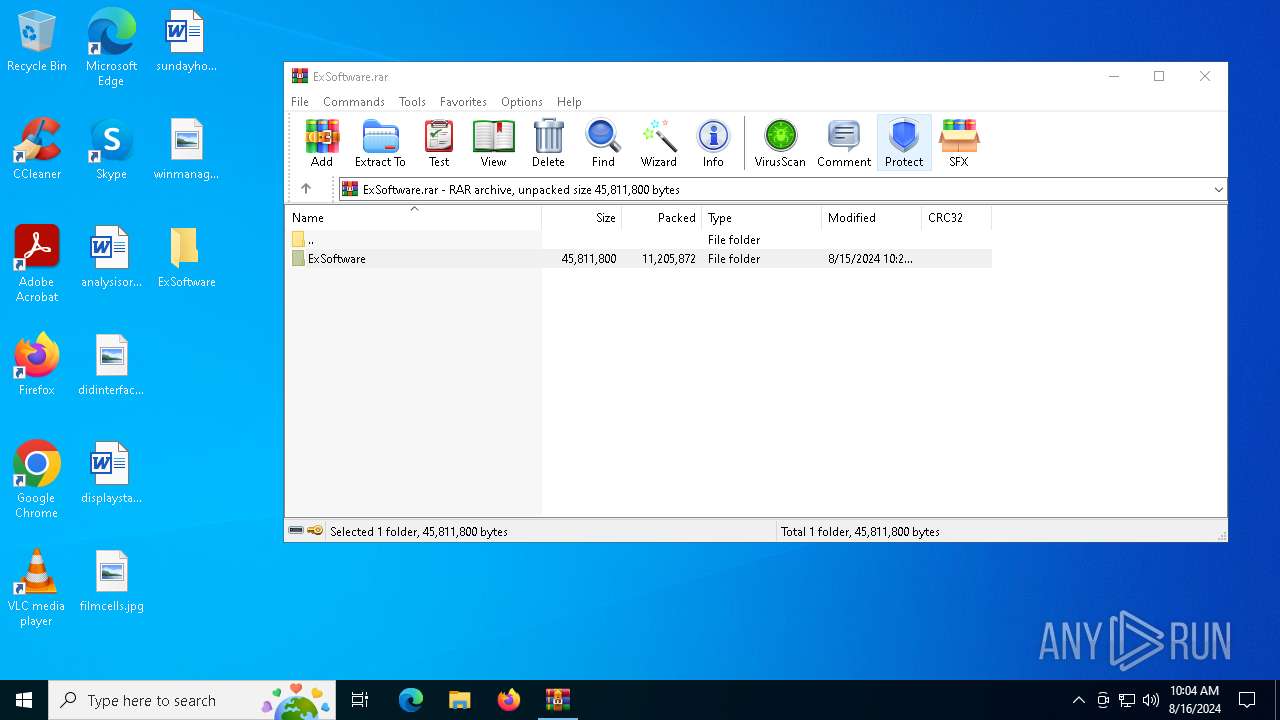
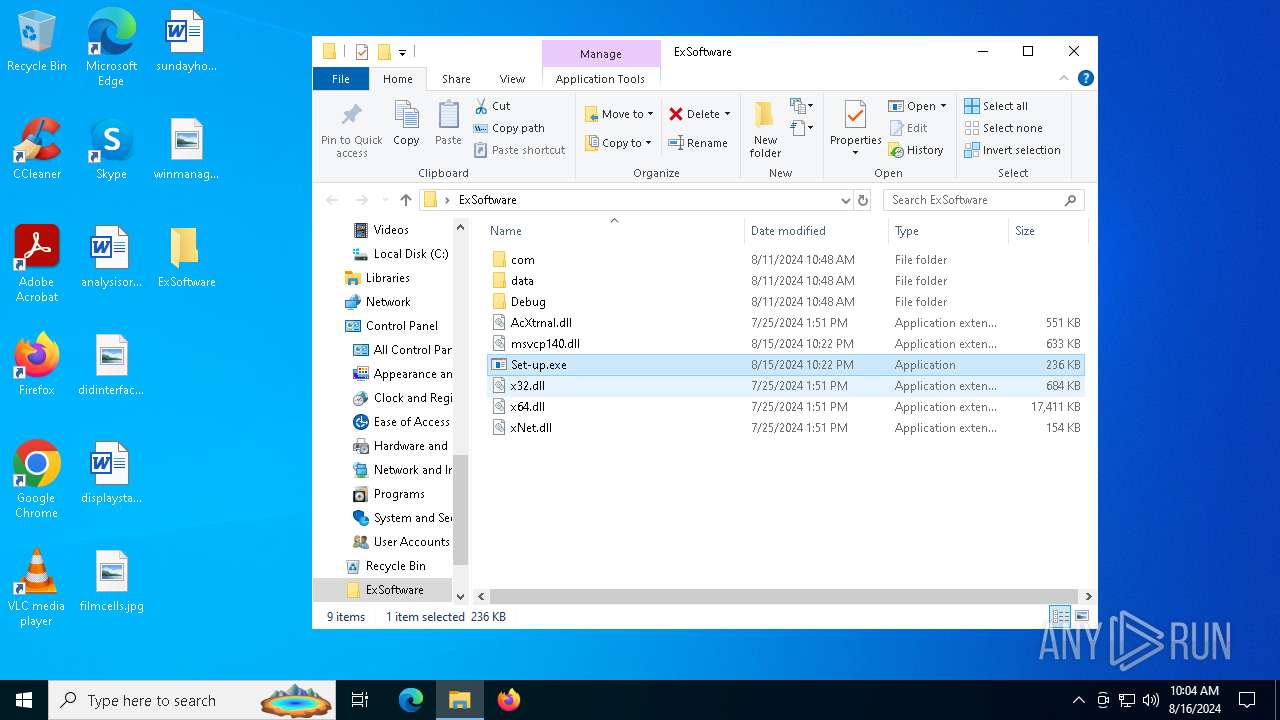
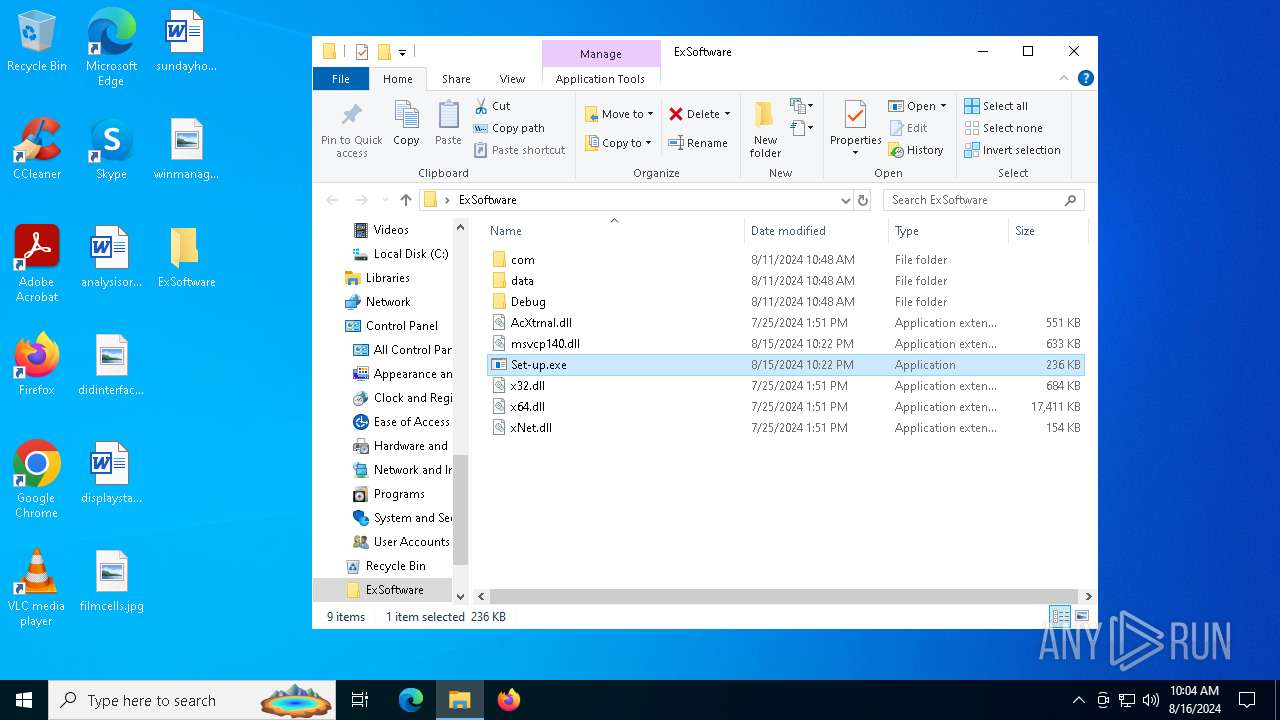
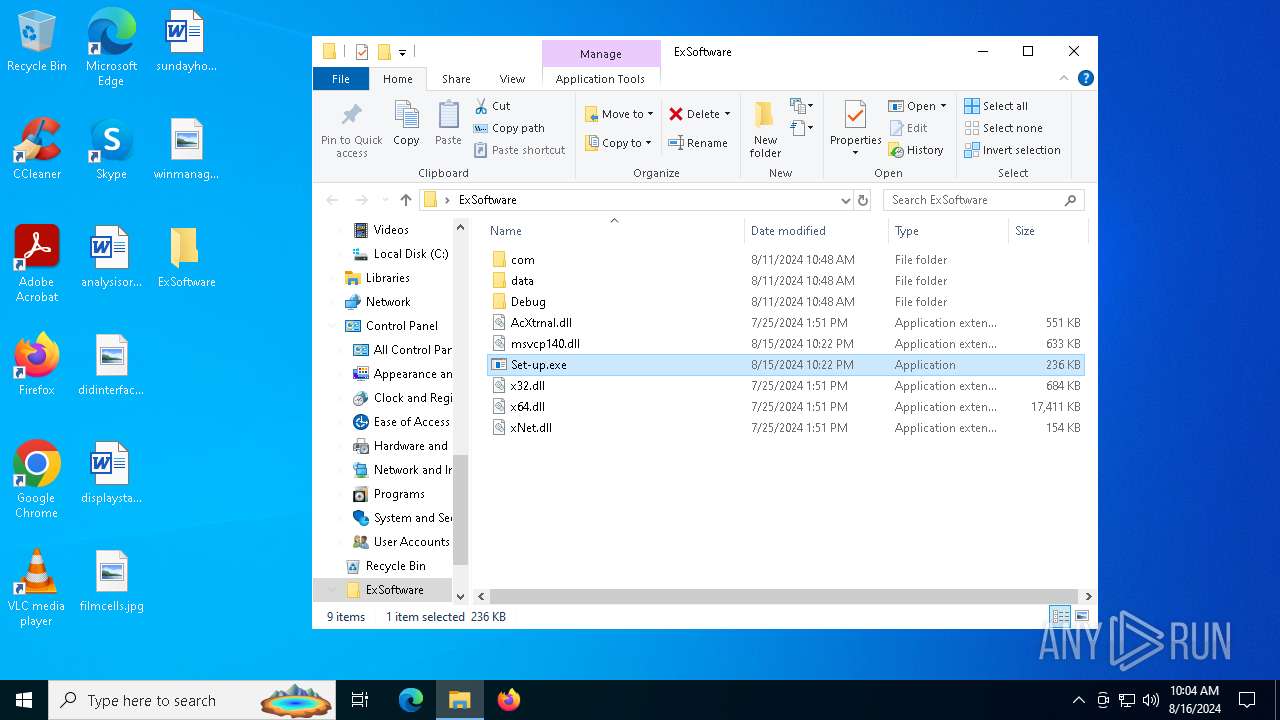
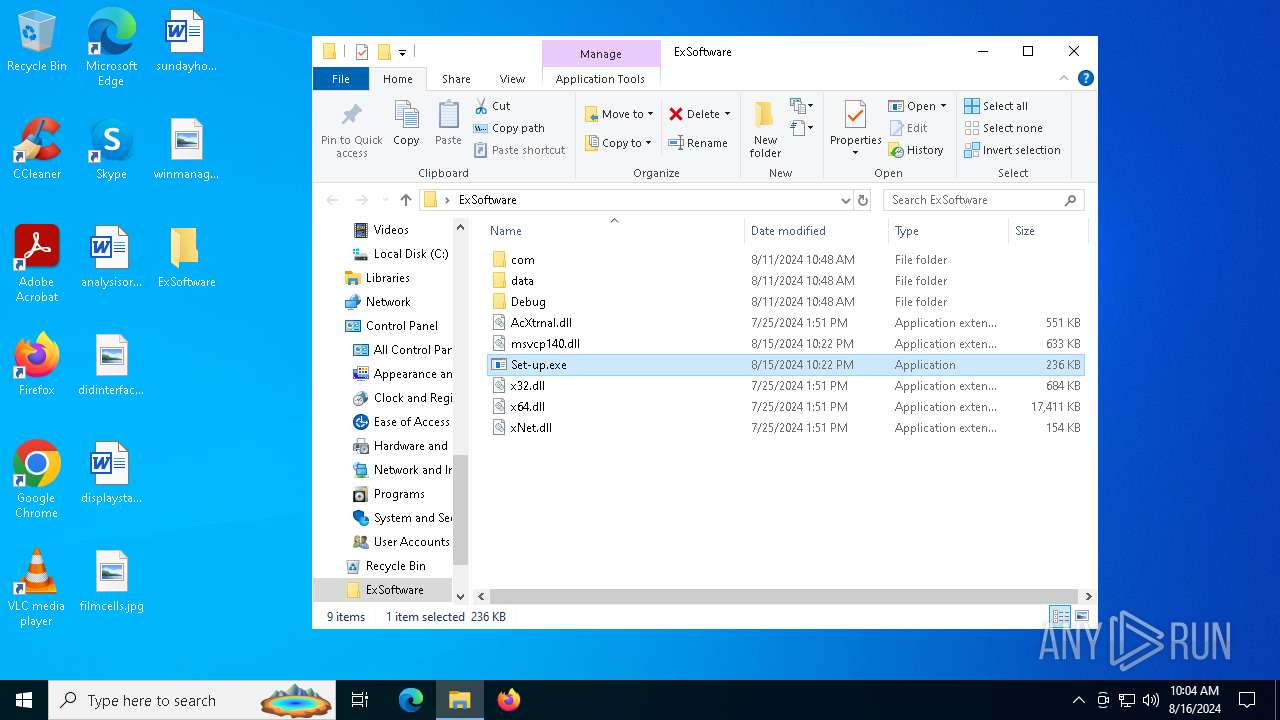
| File name: | ExSoftware.rar |
| Full analysis: | https://app.any.run/tasks/272c0de8-cecb-4af5-968f-931930f98ae2 |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | August 16, 2024, 10:03:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A22A45EA28881626EA0B678B736847C6 |
| SHA1: | 59B6E8F32D24F7F195CC420E5270AA97161395E0 |
| SHA256: | 162233632BAE455D403CEA05B7687E6147D62B7EDB6137F2B874BDD7E3A3611D |
| SSDEEP: | 98304:X6WVCOY3syteaEX9xyVnsHSy4GC0PVGvoN3YqIw4QK2sIUgkPQjq2OGV00ydUn3i:A8n+MbuD6qShDkRyP3kMpQpXr3 |
MALICIOUS
Actions looks like stealing of personal data
- OOBE-Maintenance.exe (PID: 6124)
- OOBE-Maintenance.exe (PID: 6216)
RHADAMANTHYS has been detected (SURICATA)
- OpenWith.exe (PID: 6476)
- OOBE-Maintenance.exe (PID: 6124)
- OpenWith.exe (PID: 6676)
- OOBE-Maintenance.exe (PID: 6216)
- dllhost.exe (PID: 5140)
- dllhost.exe (PID: 7164)
Stealers network behavior
- OOBE-Maintenance.exe (PID: 6124)
- OOBE-Maintenance.exe (PID: 6216)
SUSPICIOUS
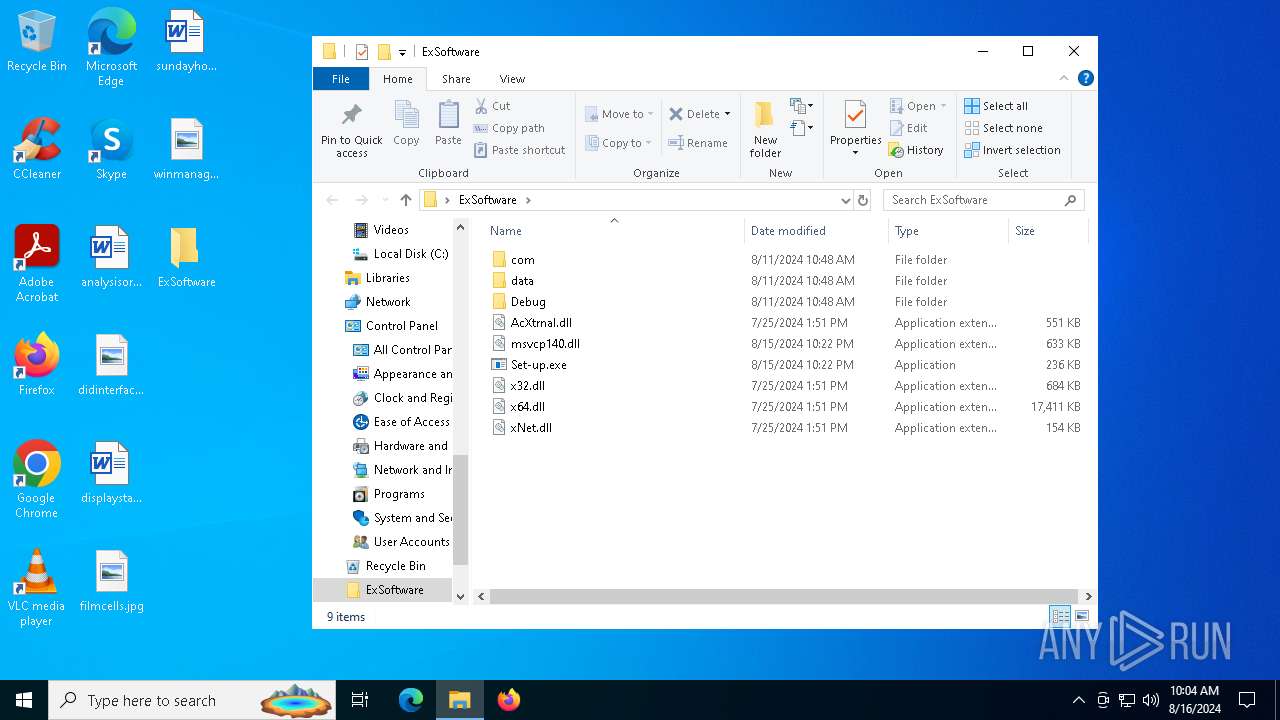
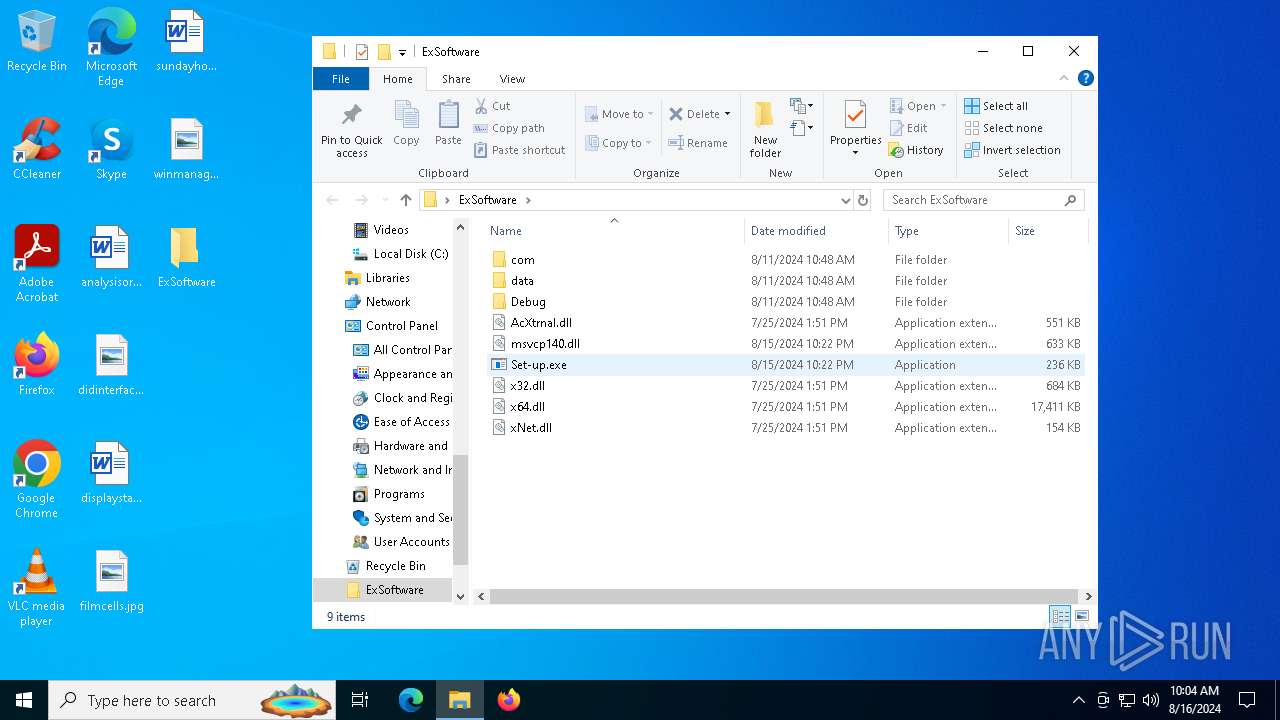
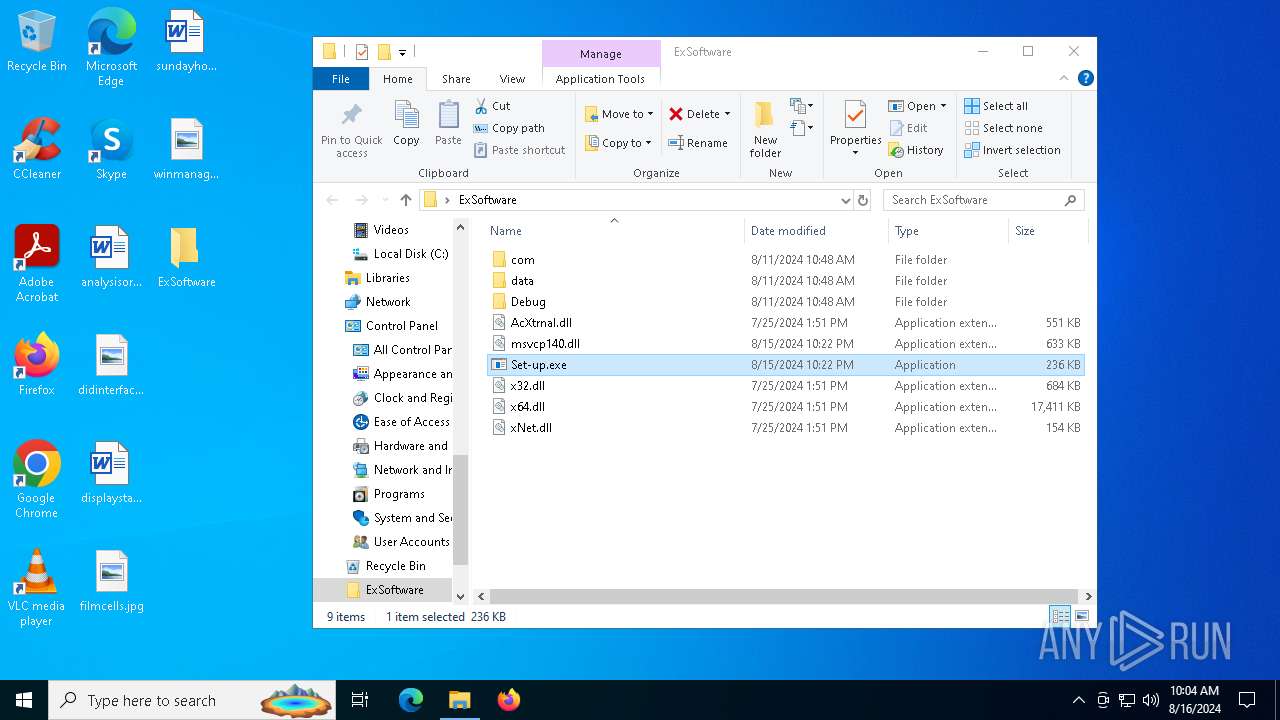
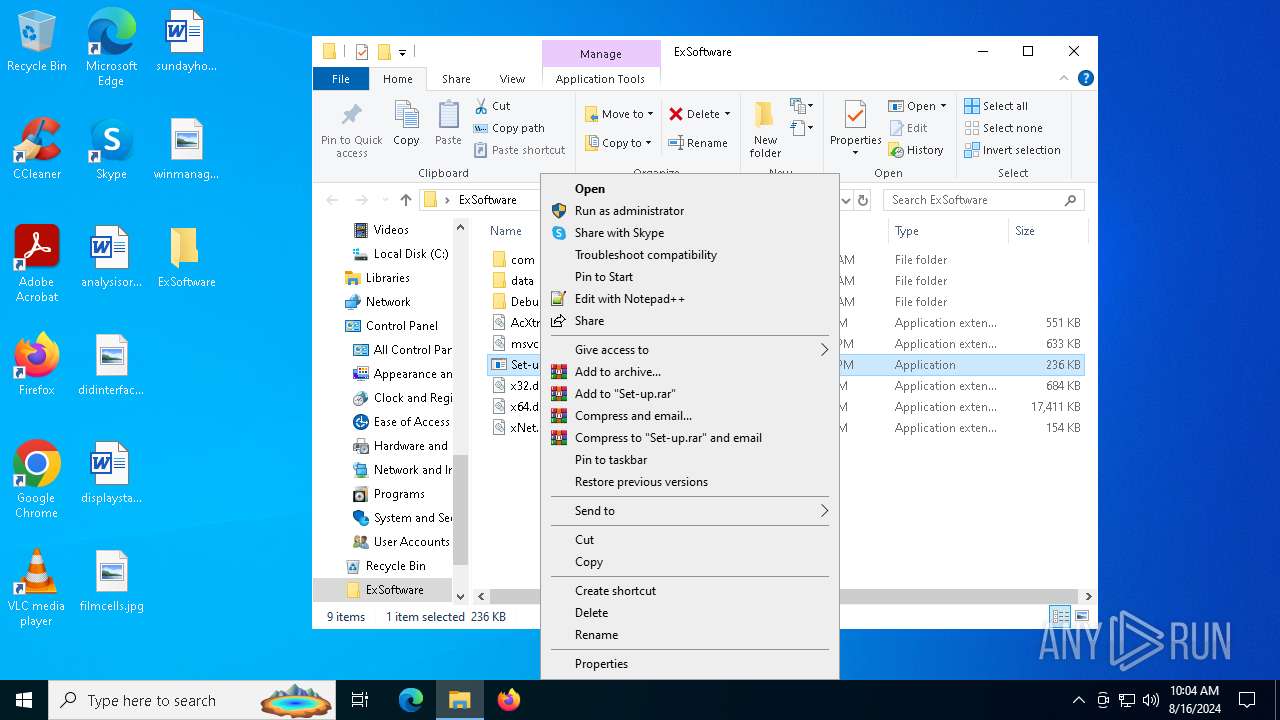
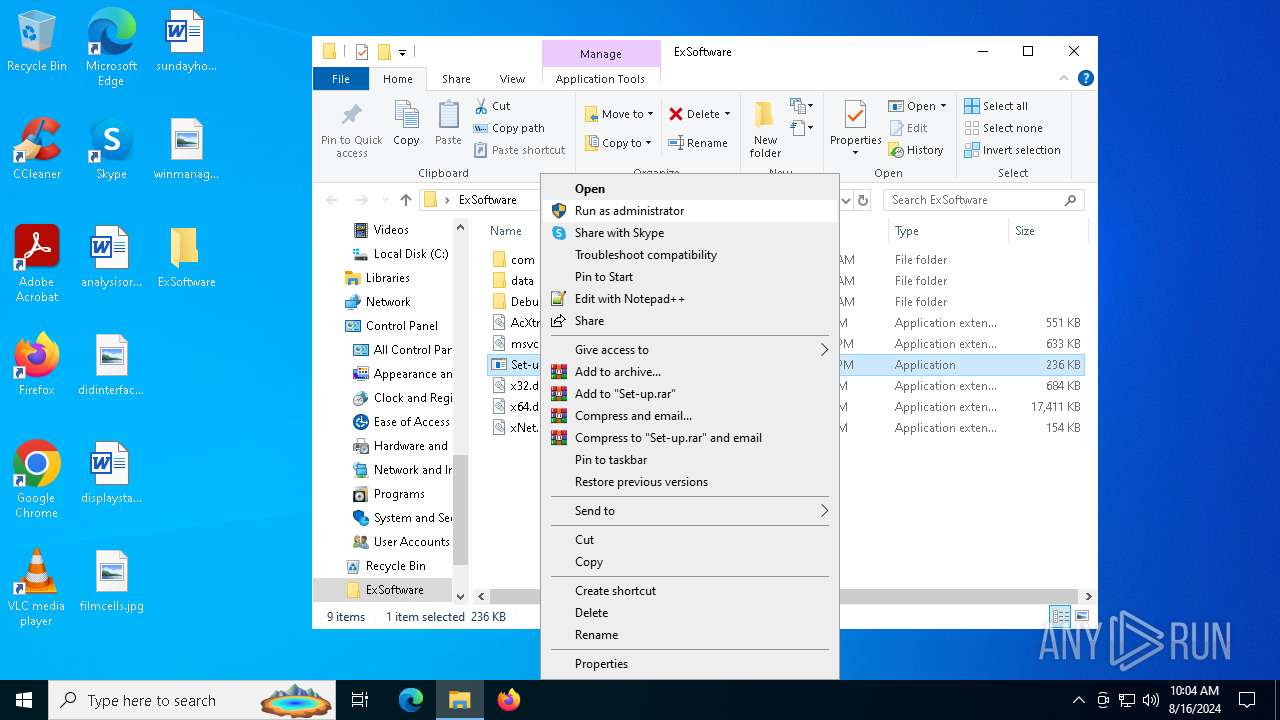
Drops the executable file immediately after the start
- Set-up.exe (PID: 304)
- Set-up.exe (PID: 1432)
Executes application which crashes
- aspnet_regiis.exe (PID: 6328)
- aspnet_regiis.exe (PID: 4132)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 6476)
- OpenWith.exe (PID: 6676)
Executable content was dropped or overwritten
- Set-up.exe (PID: 304)
- Set-up.exe (PID: 1432)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 6124)
- OOBE-Maintenance.exe (PID: 6216)
Searches for installed software
- OOBE-Maintenance.exe (PID: 6124)
- OOBE-Maintenance.exe (PID: 6216)
Contacting a server suspected of hosting an CnC
- OpenWith.exe (PID: 6476)
- OOBE-Maintenance.exe (PID: 6124)
- OpenWith.exe (PID: 6676)
- OOBE-Maintenance.exe (PID: 6216)
- dllhost.exe (PID: 7164)
- dllhost.exe (PID: 5140)
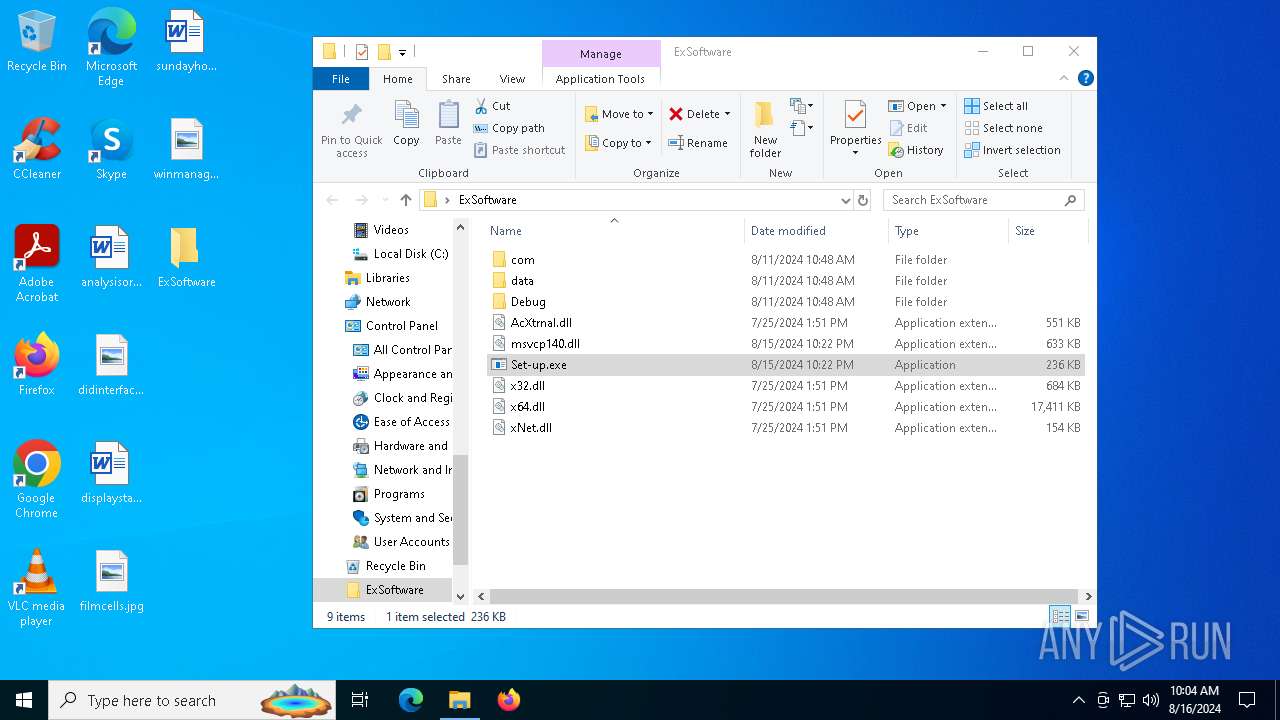
Process drops legitimate windows executable
- WinRAR.exe (PID: 6388)
The process drops Mozilla's DLL files
- WinRAR.exe (PID: 6388)
INFO
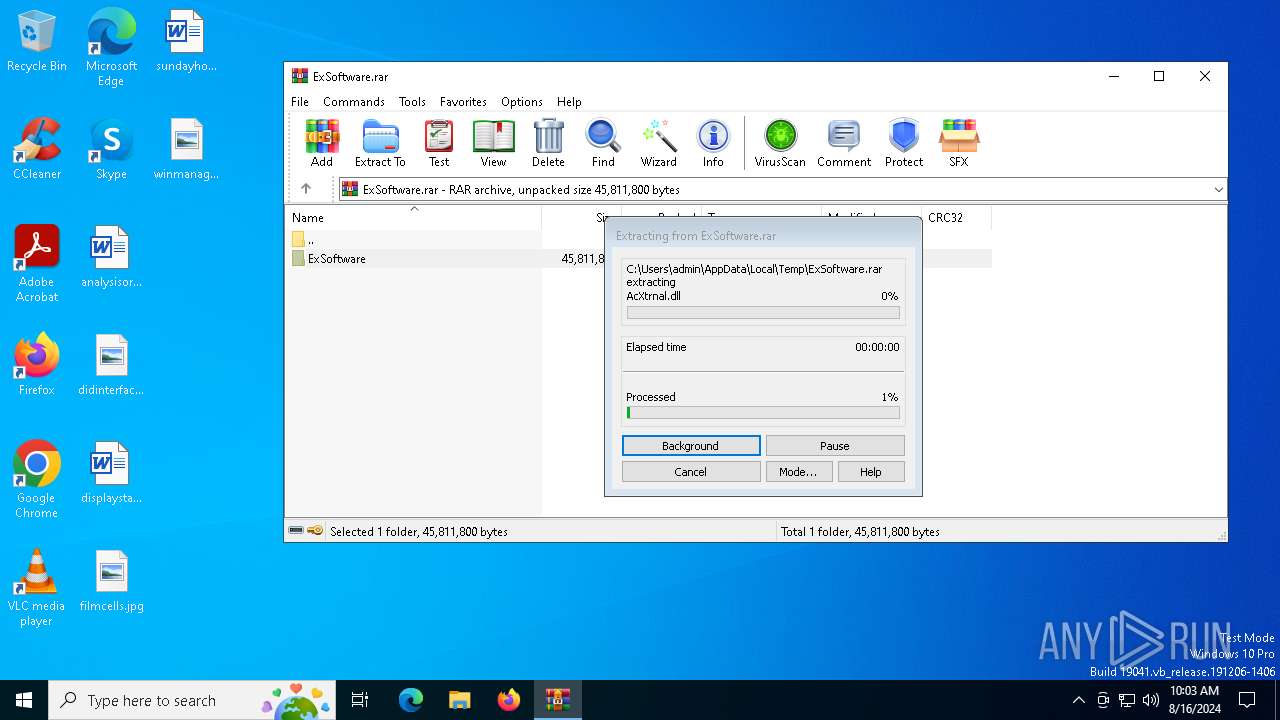
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6388)
Checks supported languages
- aspnet_regiis.exe (PID: 6328)
- Set-up.exe (PID: 1432)
- aspnet_regiis.exe (PID: 4132)
- setup_wm.exe (PID: 2852)
- Set-up.exe (PID: 304)
Manual execution by a user
- OpenWith.exe (PID: 6476)
- OOBE-Maintenance.exe (PID: 6124)
- Set-up.exe (PID: 1432)
- Set-up.exe (PID: 304)
Creates files or folders in the user directory
- Set-up.exe (PID: 304)
- Set-up.exe (PID: 1432)
Reads the computer name
- setup_wm.exe (PID: 2852)
Reads the machine GUID from the registry
- setup_wm.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
159
Monitored processes
21
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
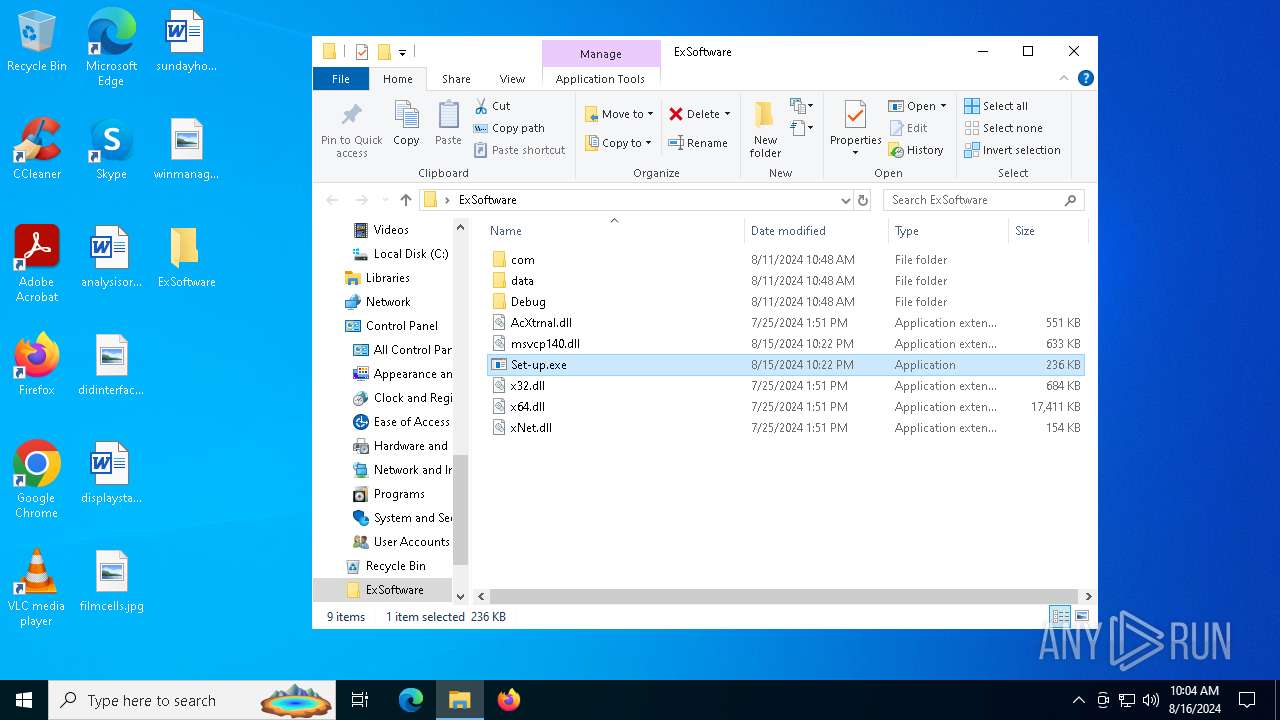
| 304 | "C:\Users\admin\Desktop\ExSoftware\Set-up.exe" | C:\Users\admin\Desktop\ExSoftware\Set-up.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1172 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6328 -s 544 | C:\Windows\SysWOW64\WerFault.exe | — | aspnet_regiis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\Desktop\ExSoftware\Set-up.exe" | C:\Users\admin\Desktop\ExSoftware\Set-up.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2136 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | OOBE-Maintenance.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2396 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6328 -s 564 | C:\Windows\SysWOW64\WerFault.exe | — | aspnet_regiis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Windows Media Player\setup_wm.exe" | C:\Program Files\Windows Media Player\setup_wm.exe | — | OOBE-Maintenance.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Configuration Utility Version: 12.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4132 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regiis.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regiis.exe | Set-up.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: aspnet_regiis.exe Exit code: 3221225477 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4704 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4132 -s 616 | C:\Windows\SysWOW64\WerFault.exe | — | aspnet_regiis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5140 | "C:\WINDOWS\system32\dllhost.exe" | C:\Windows\System32\dllhost.exe | setup_wm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5656 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Set-up.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 431
Read events
9 409
Write events
22
Delete events
0
Modification events
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ExSoftware.rar | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF140100003D000000D404000026020000 | |||
Executable files
55
Suspicious files
9
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\com\ColorManagment.dll | executable | |
MD5:EFF6F115F31539581C175522A578E799 | SHA256:152CBD8148B160B0ED4BAA2ED7CE10B680F45F7E3159D133CD0427575DA42251 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\data\alibabacloud-oss-cpp-sdk.dll | executable | |
MD5:2698F138E8C4D573BB0DAEDC47ACD123 | SHA256:2EE24618C12271B7C9C18DF5F2BEDDF02FD93EE7457707E0A6A54D8D8E88AAA2 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\data\net\FFCore.dll | executable | |
MD5:F8D599C7620A981623302BDBEF6BE1E8 | SHA256:9695408FFAA0EECF13BAF9BF98E67349BA3404130E331DDC3560A73E7460C125 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\data\lekeystore.jks | executable | |
MD5:E8FB6C3324CB66E60900B813B364A5DE | SHA256:742176460AFA2A4ED3642142DFA954E7F53668009A4973459888D5EDF9ED1BDB | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\data\dav2mp4.dll | executable | |
MD5:46DFD88DD581C240556E8F41A629D850 | SHA256:1E566DFB237F01BB9D1A04B8826889D6A5E69171E9EA436B490D10832BBF1209 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\data\net\cloud-disk.dll | executable | |
MD5:D8E7969FB5DB62F81B09E83C157954C3 | SHA256:4EF94BFDB914E87D141A4103E3035DFB7E963B0309B41E1E0675966DFD85137C | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\data\cpr.dll | executable | |
MD5:7A006DC458D9C9BC4666A0F03D354D3D | SHA256:91E513AED4CEFC9CBC8CCD014310E75D5C098C958A23B1AC0780B07170F91F1D | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\data\DemuxMgr.dll | executable | |
MD5:CE2F4A0C39F2FFC2BBD544885AB59175 | SHA256:FCF52E82C1C7AAA94E87E968731AB3CC4CB7390E37FA06546B92AE82EF5CE305 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\Debug\api-ms-win-core-synch-l1-2-0.dll | executable | |
MD5:6E704280D632C2F8F2CADEFCAE25AD85 | SHA256:758A2F9EF6908B51745DB50D89610FE1DE921D93B2DBEA919BFDBA813D5D8893 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6388.44917\ExSoftware\com\cpr.dll | executable | |
MD5:7A006DC458D9C9BC4666A0F03D354D3D | SHA256:91E513AED4CEFC9CBC8CCD014310E75D5C098C958A23B1AC0780B07170F91F1D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
50
DNS requests
16
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6804 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6836 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4708 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1184 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4708 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 104.126.37.144:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6124 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
6124 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
6216 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
6216 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
12 ETPRO signatures available at the full report