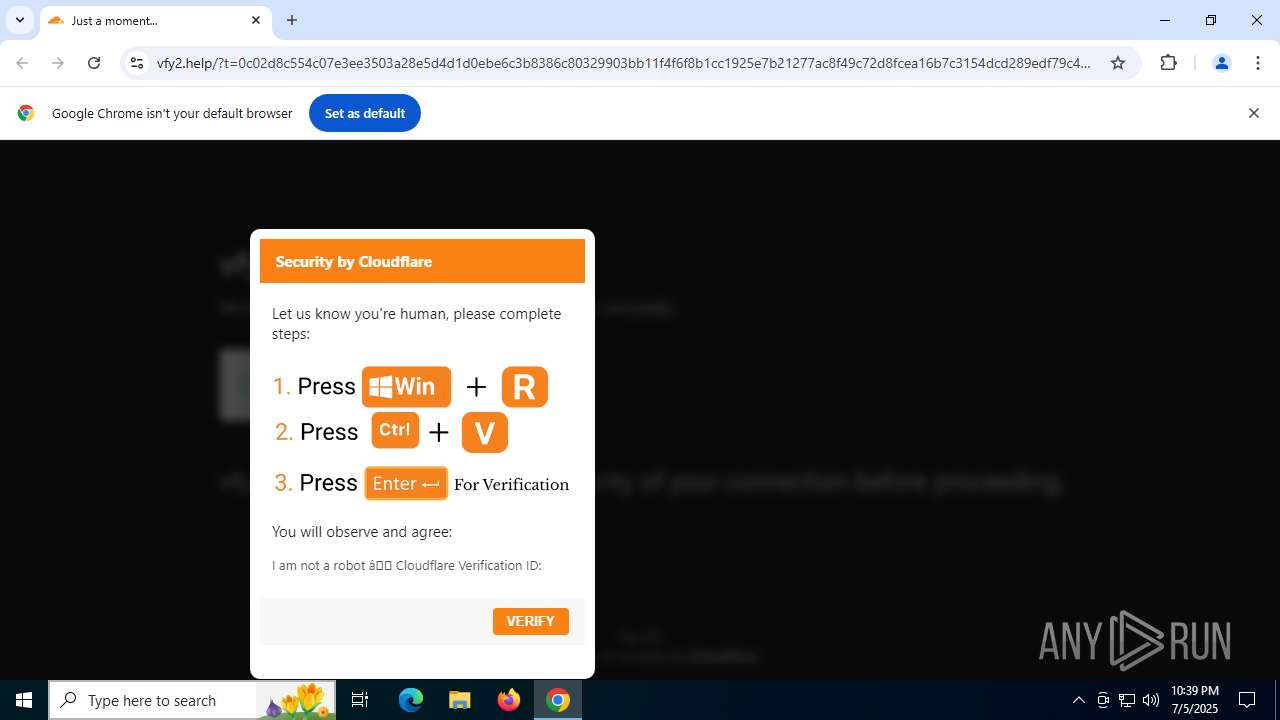
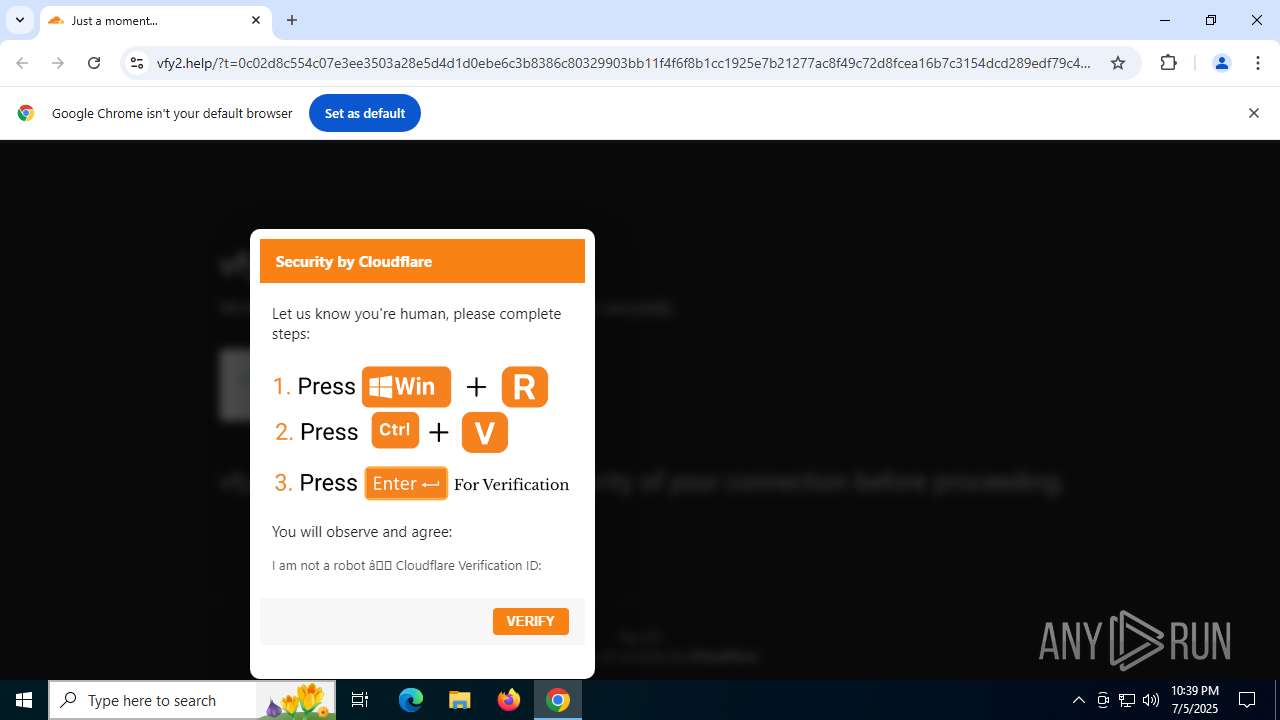
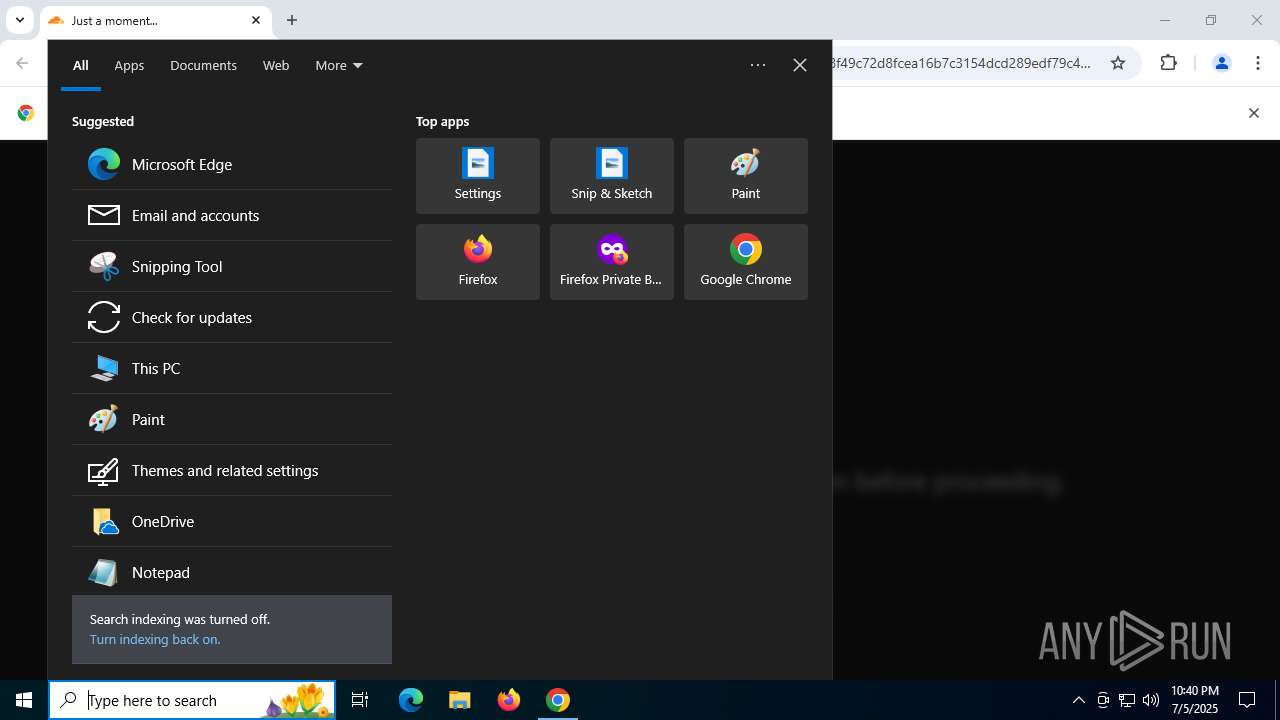
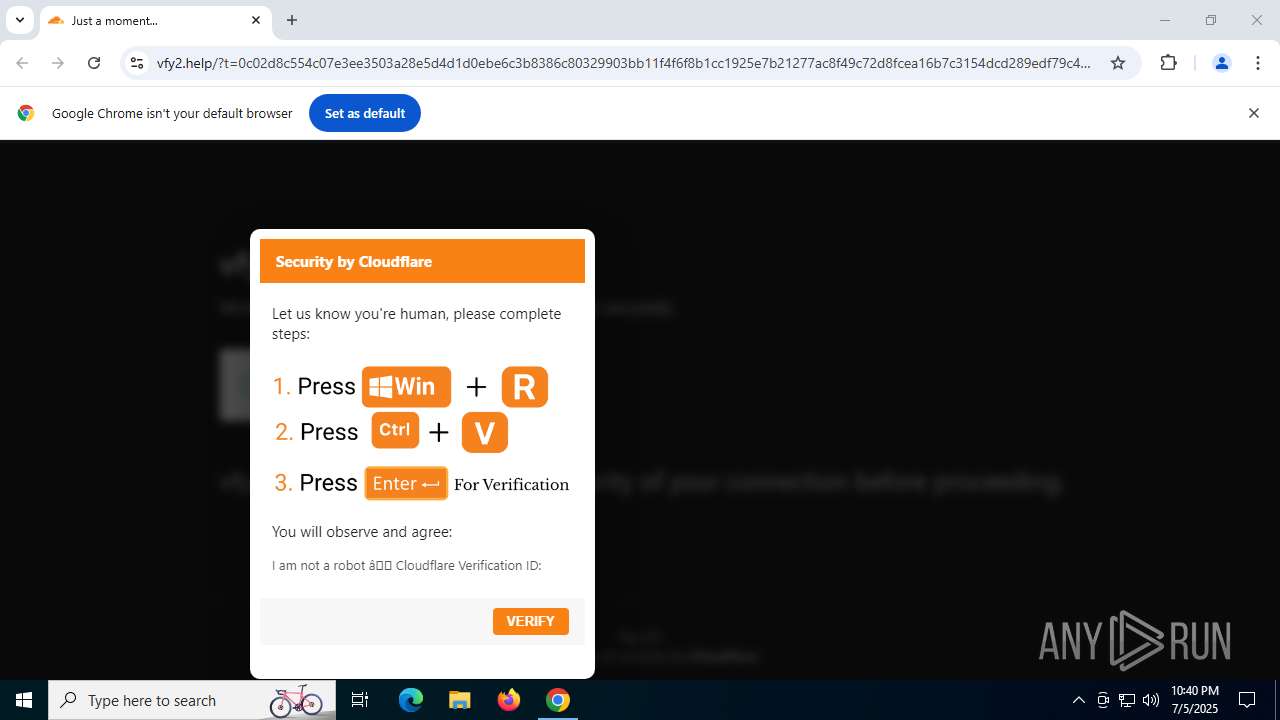
| URL: | vfy2.help |
| Full analysis: | https://app.any.run/tasks/b9ff0842-9848-459e-9f4c-9431c0948199 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | July 05, 2025, 22:39:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 258850B79A092ECFEE582463724208A5 |
| SHA1: | 6013335B7C372A81CB33BAE4F174407C903C920B |
| SHA256: | 15EC7FB1E003B5F899C3F7CC9D430905255442B60C6A3C3057CB7CE468FE315A |
| SSDEEP: | 3:U0n:U0 |
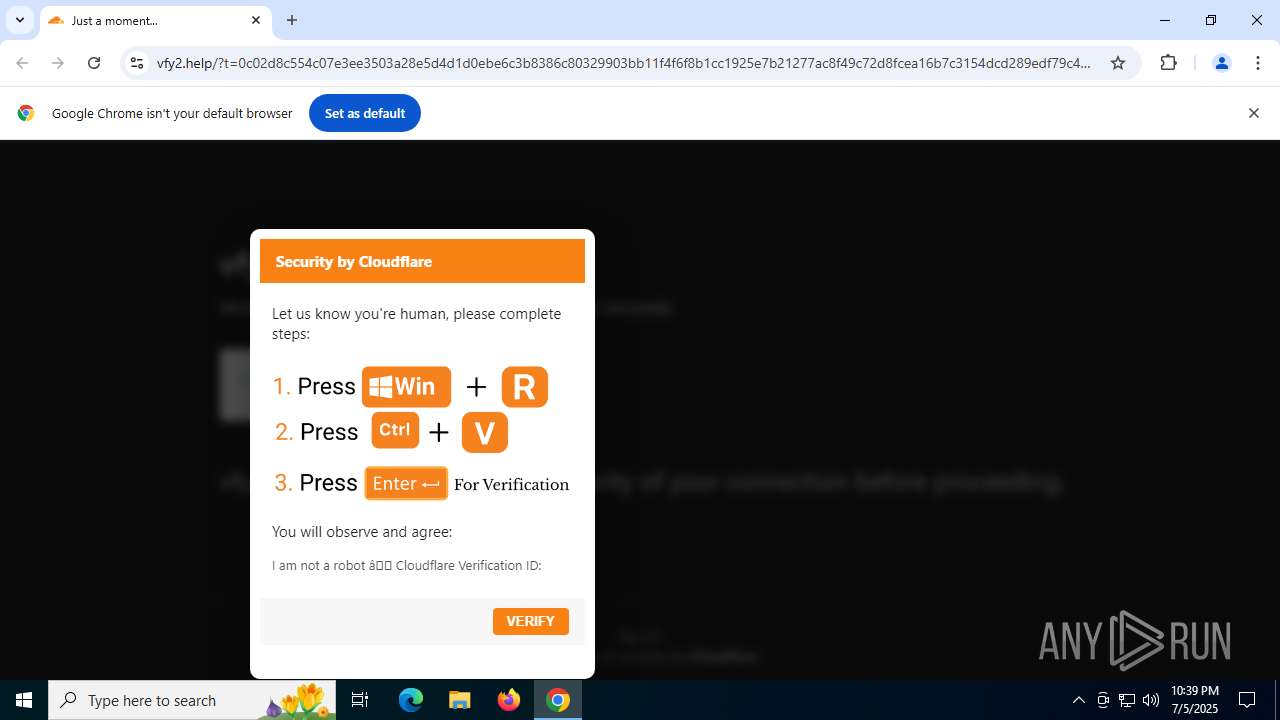
MALICIOUS
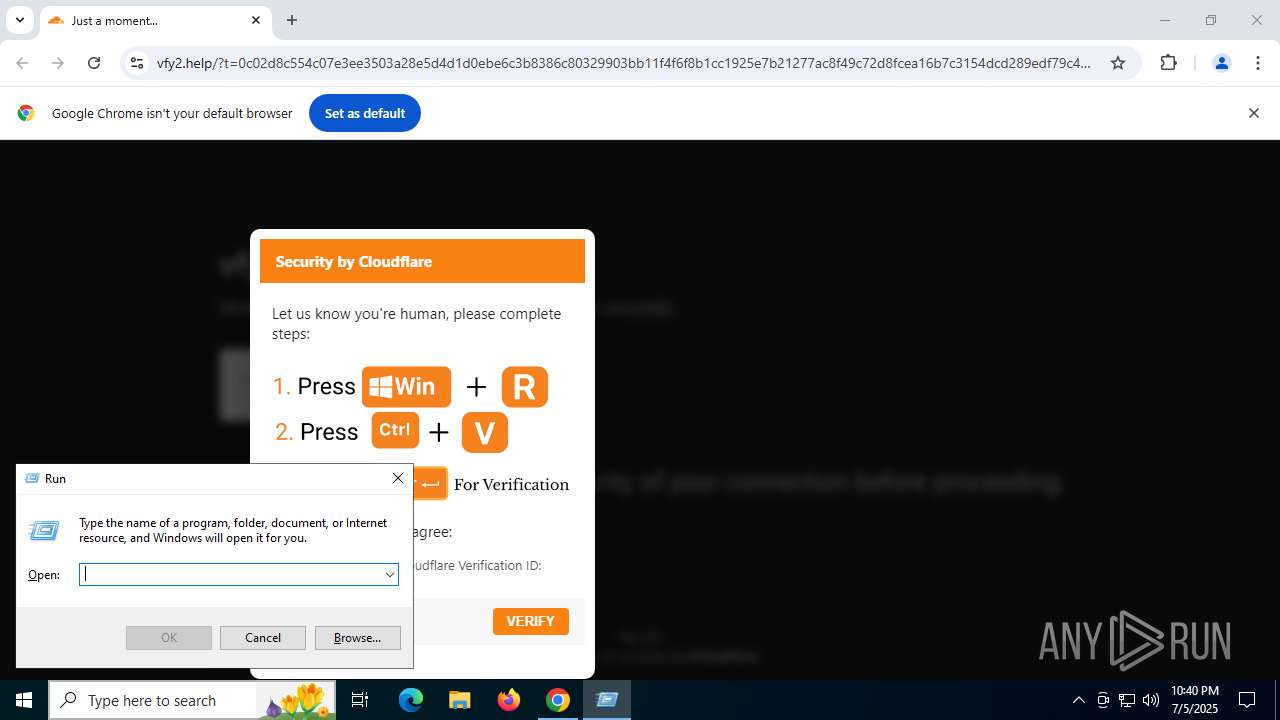
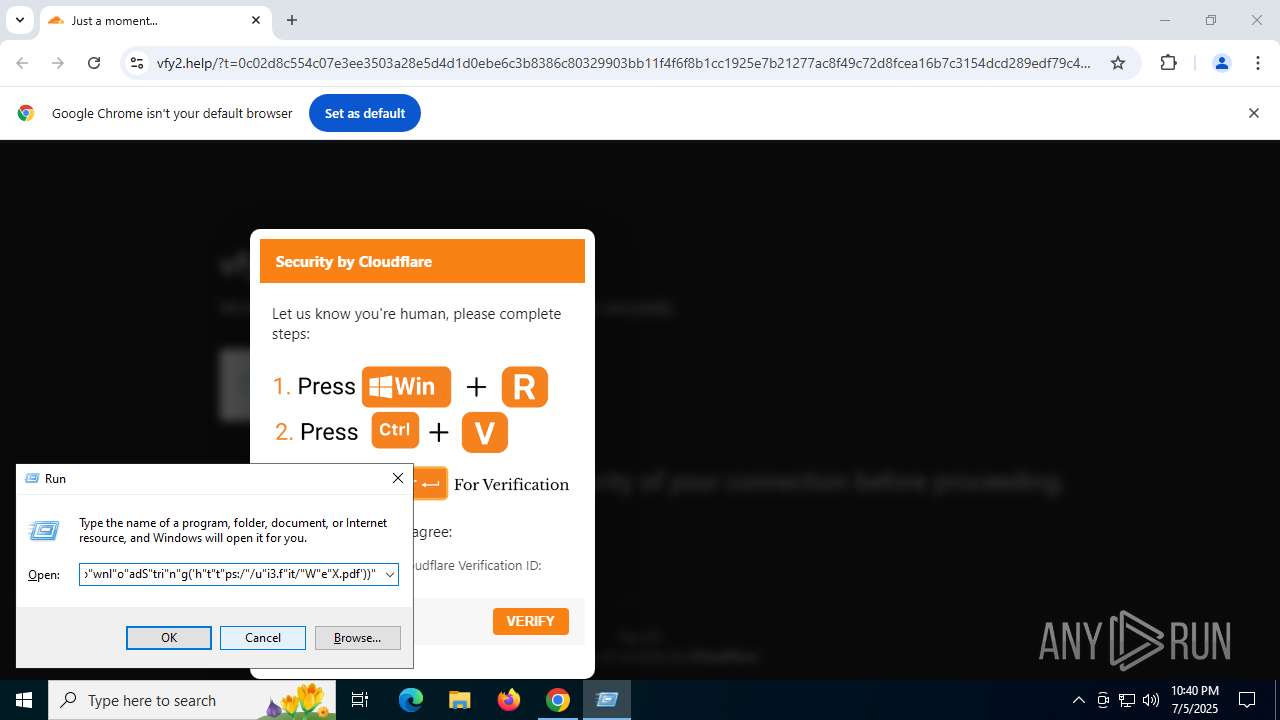
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 4804)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 4804)
Steals credentials from Web Browsers
- explorer.exe (PID: 6240)
Actions looks like stealing of personal data
- explorer.exe (PID: 6240)
LUMMA mutex has been found
- explorer.exe (PID: 6240)
SUSPICIOUS
CSC.EXE is used to compile C# code
- csc.exe (PID: 4400)
- csc.exe (PID: 1300)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4804)
Executable content was dropped or overwritten
- csc.exe (PID: 1300)
- csc.exe (PID: 4400)
Searches for installed software
- explorer.exe (PID: 6240)
INFO
Application launched itself
- chrome.exe (PID: 440)
- msedge.exe (PID: 5716)
- msedge.exe (PID: 7284)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 6140)
- msedge.exe (PID: 7644)
- msedge.exe (PID: 4680)
Disables trace logs
- powershell.exe (PID: 4804)
Checks supported languages
- csc.exe (PID: 4400)
- cvtres.exe (PID: 6572)
- cvtres.exe (PID: 2428)
- csc.exe (PID: 1300)
- identity_helper.exe (PID: 1204)
- identity_helper.exe (PID: 8160)
- identity_helper.exe (PID: 8184)
- identity_helper.exe (PID: 5576)
Reads the machine GUID from the registry
- csc.exe (PID: 4400)
- csc.exe (PID: 1300)
Create files in a temporary directory
- cvtres.exe (PID: 6572)
- csc.exe (PID: 4400)
- cvtres.exe (PID: 2428)
- csc.exe (PID: 1300)
Checks proxy server information
- powershell.exe (PID: 4804)
- slui.exe (PID: 4552)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 4804)
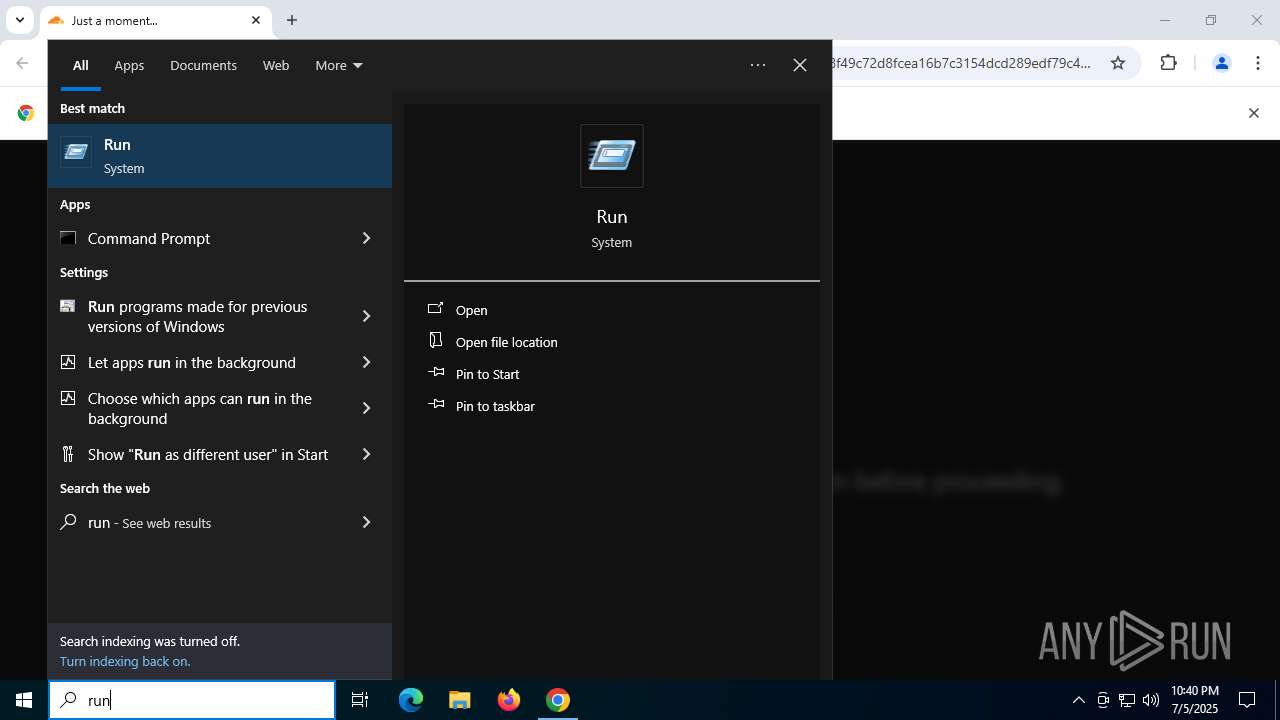
Manual execution by a user
- powershell.exe (PID: 4804)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4804)
Reads Environment values
- identity_helper.exe (PID: 1204)
- identity_helper.exe (PID: 5576)
- identity_helper.exe (PID: 8160)
- identity_helper.exe (PID: 8184)
Reads the computer name
- identity_helper.exe (PID: 1204)
- identity_helper.exe (PID: 5576)
- identity_helper.exe (PID: 8160)
- identity_helper.exe (PID: 8184)
Reads the software policy settings
- explorer.exe (PID: 6240)
- slui.exe (PID: 4552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
260
Monitored processes
118
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1992,i,15186384980782603486,15316460784567006431,262144 --variations-seed-version --mojo-platform-channel-handle=1988 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3136,i,946877258162000409,15987818304795022591,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3620,i,17283660416047604833,933901647379132482,262144 --variations-seed-version --mojo-platform-channel-handle=3600 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
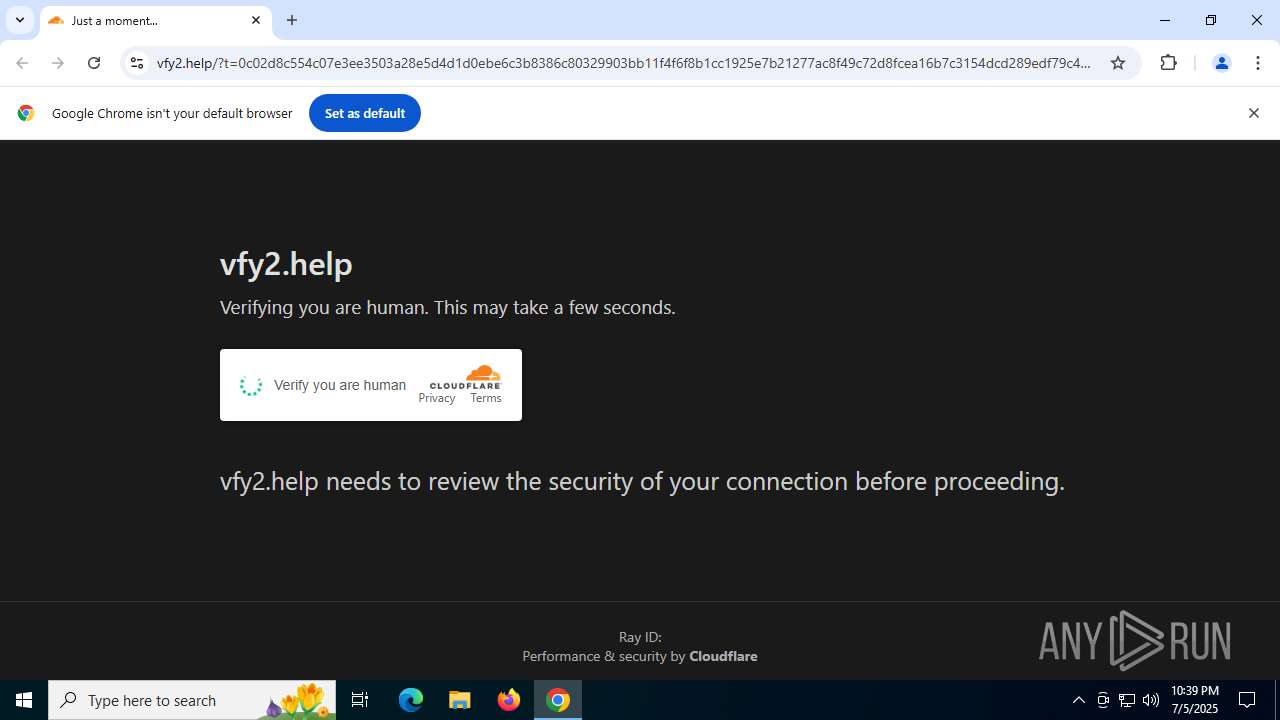
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "vfy2.help" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2204,i,17533932141322755516,17589422014050460705,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2308 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=3232,i,17533932141322755516,17589422014050460705,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2260,i,15186384980782603486,15316460784567006431,262144 --variations-seed-version --mojo-platform-channel-handle=2120 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3176,i,11142338312731492191,18401705732571673907,262144 --variations-seed-version --mojo-platform-channel-handle=3144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6336,i,17283660416047604833,933901647379132482,262144 --variations-seed-version --mojo-platform-channel-handle=6364 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
35 967
Read events
35 878
Write events
89
Delete events
0
Modification events
| (PID) Process: | (440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (440) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
56
Suspicious files
1 188
Text files
404
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF17561f.TMP | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1758de.TMP | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1758de.TMP | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1758de.TMP | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1758de.TMP | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1758de.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
282
DNS requests
260
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1732 | chrome.exe | GET | 200 | 142.250.185.78:80 | http://clients2.google.com/time/1/current?cup2key=8:GcAlyVZVoeetNa-WRCyEuhujVMxyEMQcDYq3abwzYuc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5896 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6128 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6128 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3108 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:V9jo49Vjw1o5pZPCg1Db4WpF983-gHal3JEau2inyug&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.192.153.142:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7132 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1732 | chrome.exe | 142.250.185.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
1732 | chrome.exe | 172.217.23.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
1732 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1732 | chrome.exe | 172.67.162.38:443 | vfy2.help | CLOUDFLARENET | US | unknown |
1732 | chrome.exe | 104.16.124.96:443 | cf-assets.www.cloudflare.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
vfy2.help |
| unknown |
accounts.google.com |
| whitelisted |
cf-assets.www.cloudflare.com |
| whitelisted |
www.cloudflare.com |
| whitelisted |
www.google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6240 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
6240 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
6240 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
6240 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
6240 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
6240 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
6240 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
6240 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |