| File name: | doingCTIrocks_crypted_LAB.exe |
| Full analysis: | https://app.any.run/tasks/179359dc-ea4e-475d-ae4b-4d6db02682ec |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 21, 2025, 23:08:29 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 9 sections |
| MD5: | 9F3423FECD5476CD566F4D81000E5EFA |
| SHA1: | E7757C365BD1D0E5CF99A1204949AAC56CE930B7 |
| SHA256: | 15EBCDD4EFDBB9EB97760516EC8FD18A0AF15502E4FCD63B99FAF7A0095ABAE6 |
| SSDEEP: | 49152:cres2xH5fDvPWRLfA3SLT1OMjql9p5aoku0frf9fOf4vQZCOr28w:UexHZDveRLfAMjqlr5aoku0r9GgcLi8w |
MALICIOUS
Steals credentials from Web Browsers
- MSBuild.exe (PID: 1076)
LUMMA mutex has been found
- MSBuild.exe (PID: 1076)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 1076)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 1076)
SUSPICIOUS
Reads settings of System Certificates
- MSBuild.exe (PID: 1076)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 1076)
Reads the Internet Settings
- MSBuild.exe (PID: 1076)
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 1076)
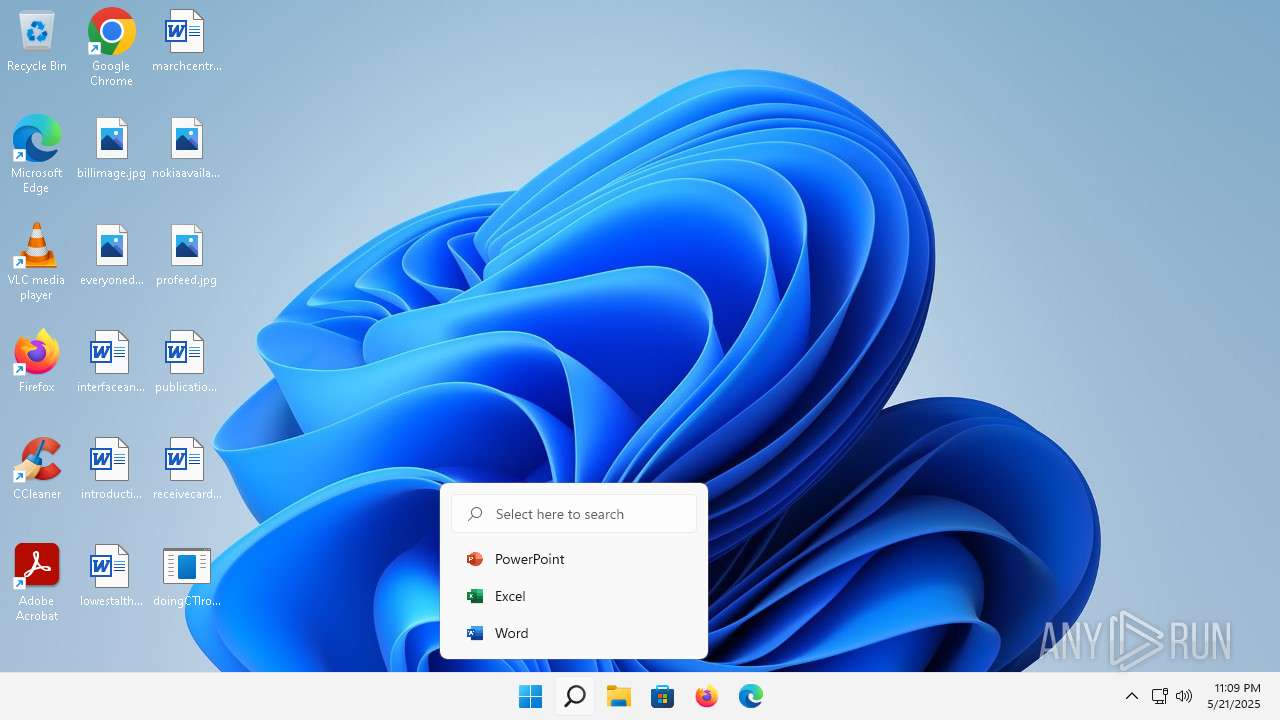
Searches for installed software
- MSBuild.exe (PID: 1076)
INFO
Checks supported languages
- doingCTIrocks_crypted_LAB.exe (PID: 5088)
- MSBuild.exe (PID: 1076)
- MiniSearchHost.exe (PID: 2188)
Reads the software policy settings
- MSBuild.exe (PID: 1076)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 1076)
Reads the computer name
- MSBuild.exe (PID: 1076)
- MiniSearchHost.exe (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(1076) MSBuild.exe
C2 (10)escczlv.top/bufi
phoucc.digital/pxa
https://t.me/sdassdadasda
korxddl.top/qidz
localixbiw.top/zlpa
bogtkr.top/zhyk
diecam.top/laur
citellcagt.top/gjtu
narrathfpt.top/tekq
ordntx.top/pxla
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:21 17:29:56+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 532480 |
| InitializedDataSize: | 97280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5f000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
106
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | doingCTIrocks_crypted_LAB.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
Lumma(PID) Process(1076) MSBuild.exe C2 (10)escczlv.top/bufi phoucc.digital/pxa https://t.me/sdassdadasda korxddl.top/qidz localixbiw.top/zlpa bogtkr.top/zhyk diecam.top/laur citellcagt.top/gjtu narrathfpt.top/tekq ordntx.top/pxla | |||||||||||||||
| 2188 | "C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\MiniSearchHost.exe" -ServerName:MiniSearchUI.AppXj3y73at8fy1htwztzxs68sxx1v7cksp7.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\MiniSearchHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 421.22500.3595.0 Modules
| |||||||||||||||
| 2356 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | doingCTIrocks_crypted_LAB.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5088 | "C:\Users\admin\Desktop\doingCTIrocks_crypted_LAB.exe" | C:\Users\admin\Desktop\doingCTIrocks_crypted_LAB.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
5 696
Read events
5 696
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
12
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1748 | smartscreen.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5c8a309e71e826fe | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 2.18.64.200:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?30c27d0b0183e869 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?6e74c5411d5b84cd | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?95ffe5009287b7a1 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?1e08fe46a221a123 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 2.18.64.212:80 | — | Administracion Nacional de Telecomunicaciones | UY | unknown |
1748 | smartscreen.exe | 48.209.144.71:443 | checkappexec.microsoft.com | — | US | whitelisted |
1748 | smartscreen.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3560 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | MSBuild.exe | 149.154.167.99:443 | t.me | Telegram Messenger Inc | GB | whitelisted |
1076 | MSBuild.exe | 172.67.156.189:443 | phoucc.digital | CLOUDFLARENET | US | unknown |
1352 | svchost.exe | 2.18.64.200:80 | — | Administracion Nacional de Telecomunicaciones | UY | unknown |
3640 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2776 | svchost.exe | 13.89.179.13:443 | v10.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
t.me |
| whitelisted |
phoucc.digital |
| unknown |
login.live.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1076 | MSBuild.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |