| File name: | Cat2022DecFile58373.exe |
| Full analysis: | https://app.any.run/tasks/7d3fa157-064c-4ebe-82d4-1f161e7284f7 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | December 05, 2022, 23:12:49 |
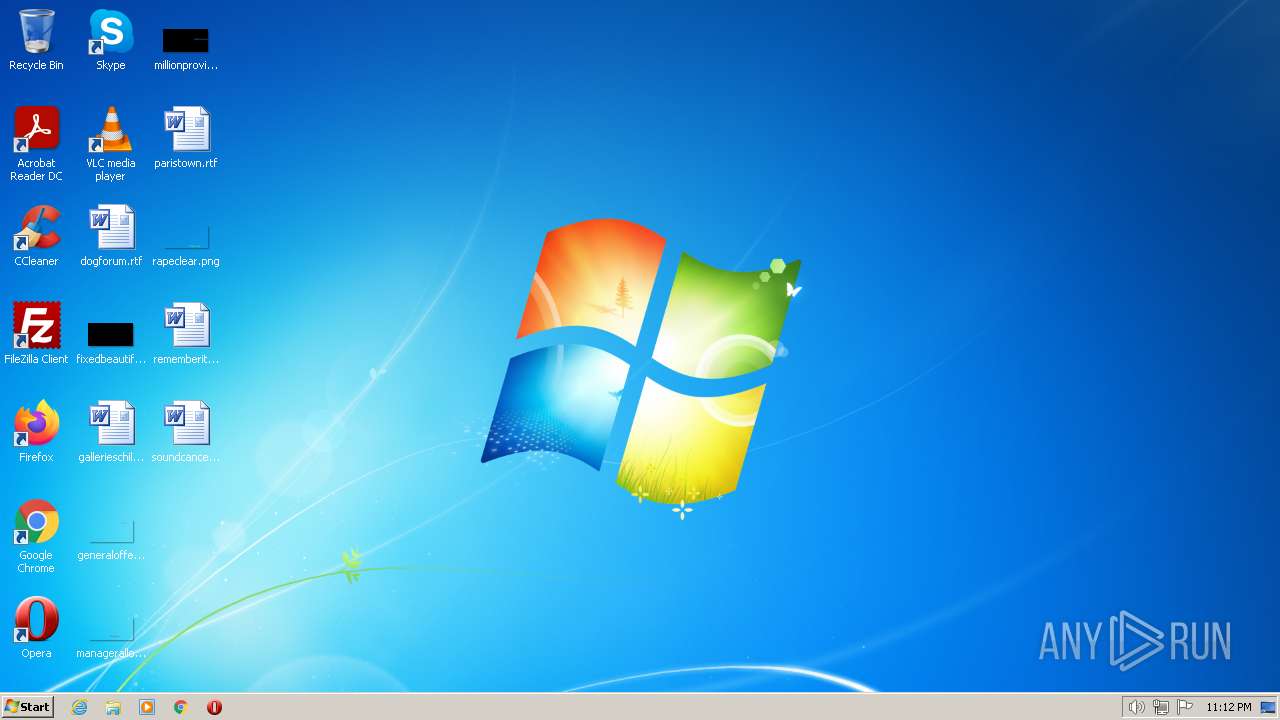
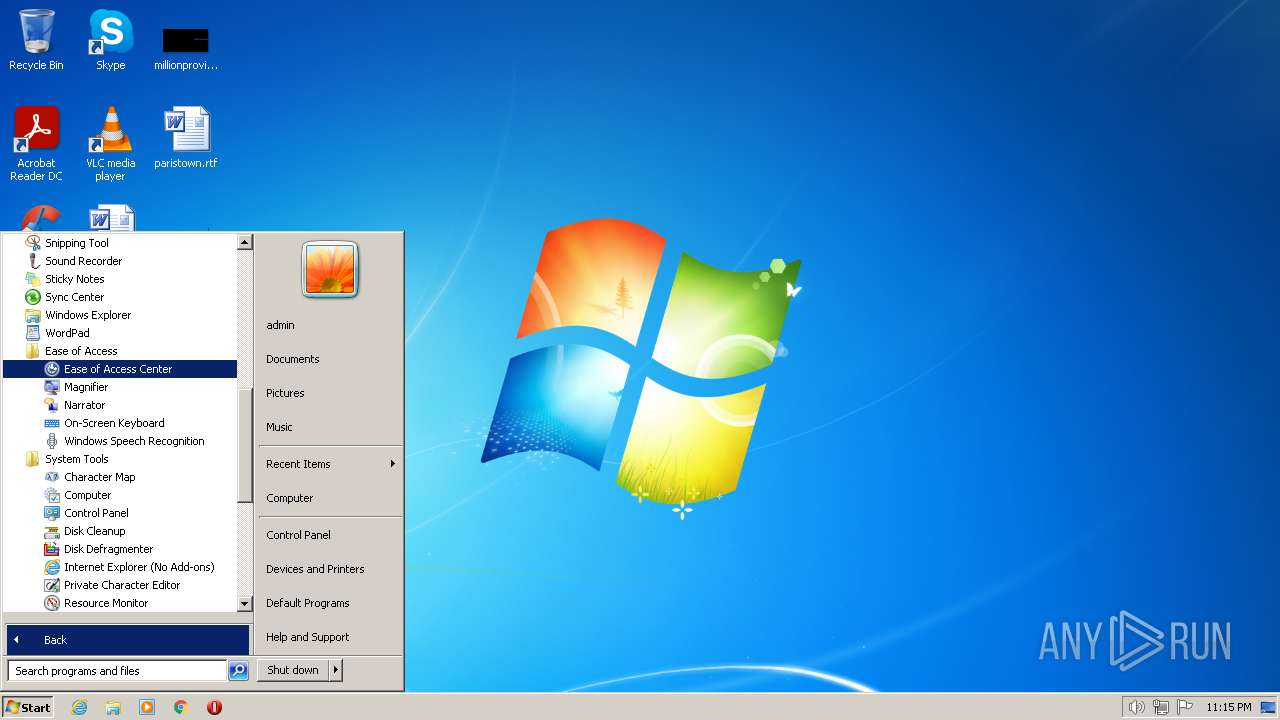
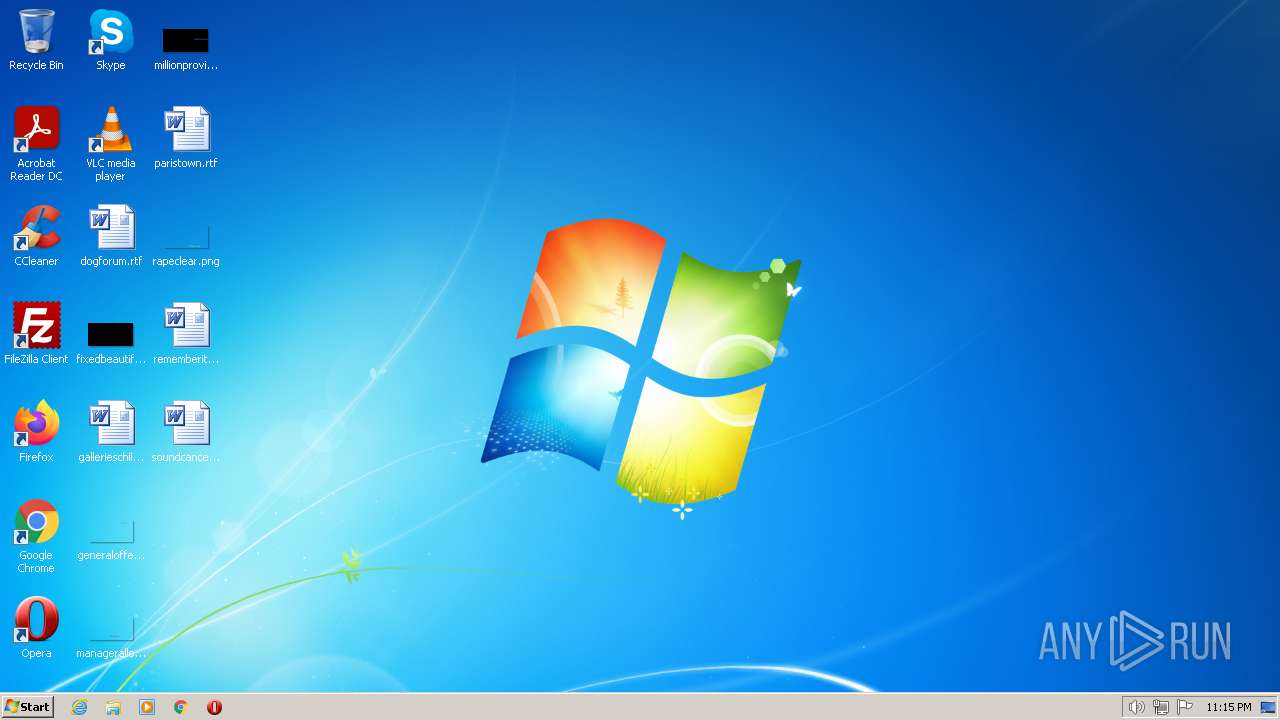
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 59EC68C614CBD08F061B98EE2F7558B6 |
| SHA1: | 518E36C73B44331E89A74C651DDF64E9AD79EE10 |
| SHA256: | 1546E632CB3CD6ABB0497A1E941D7C1AFEFD3D1BC7582B63F49D948241406B80 |
| SSDEEP: | 6144:ptxBKhzEHZ6pqRMVr5PdD1IQnAPJrueL9KEzbIgsfd+O2hht9lKSYS:ptLKhIZ60+VrVR/UJrueL9PbcV8jt9lH |
MALICIOUS
FORMBOOK detected by memory dumps
- cmd.exe (PID: 2872)
Loads dropped or rewritten executable
- cmd.exe (PID: 2872)
FORMBOOK was detected
- Explorer.EXE (PID: 1084)
Connects to the CnC server
- Explorer.EXE (PID: 1084)
Unusual connection from system programs
- Explorer.EXE (PID: 1084)
SUSPICIOUS
Loads DLL from Mozilla Firefox
- cmd.exe (PID: 2872)
Process drops SQLite DLL files
- cmd.exe (PID: 2872)
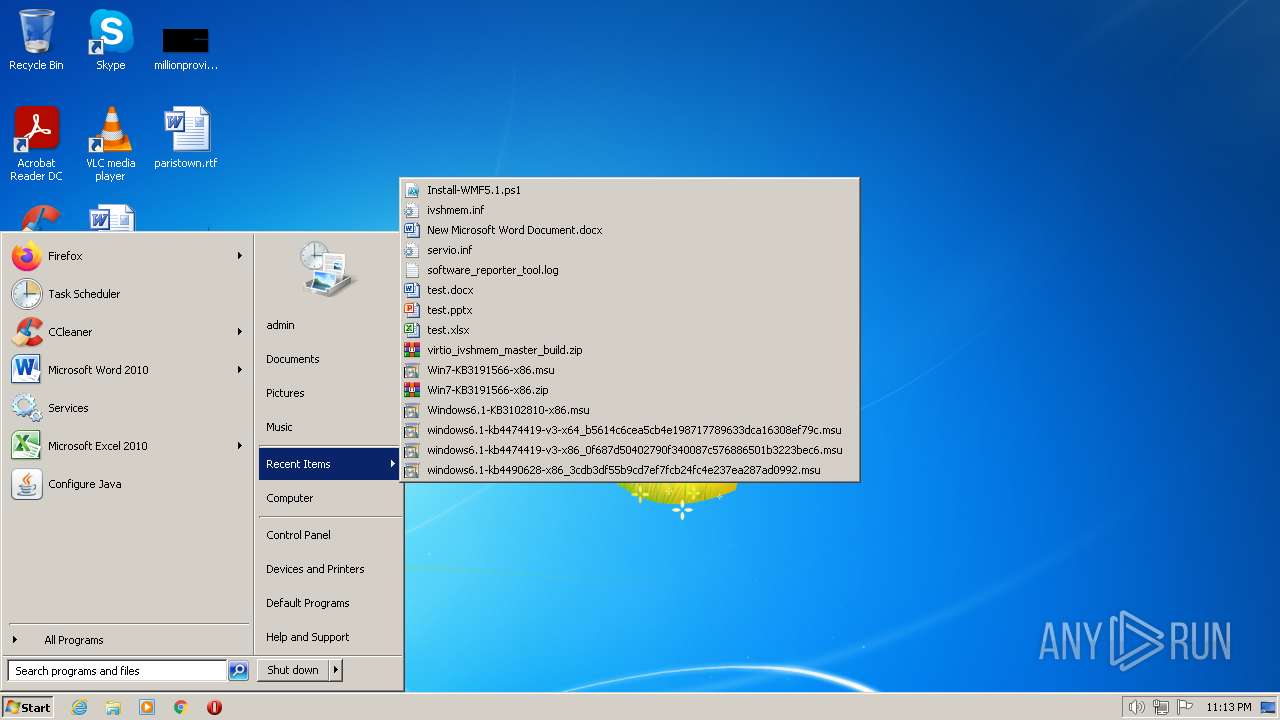
Reads browser cookies
- cmd.exe (PID: 2872)
INFO
Reads the computer name
- Cat2022DecFile58373.exe (PID: 856)
- RegSvcs.exe (PID: 3348)
Checks supported languages
- Cat2022DecFile58373.exe (PID: 856)
- RegSvcs.exe (PID: 3348)
Process checks computer location settings
- RegSvcs.exe (PID: 3348)
Checks proxy server information
- cmd.exe (PID: 2872)
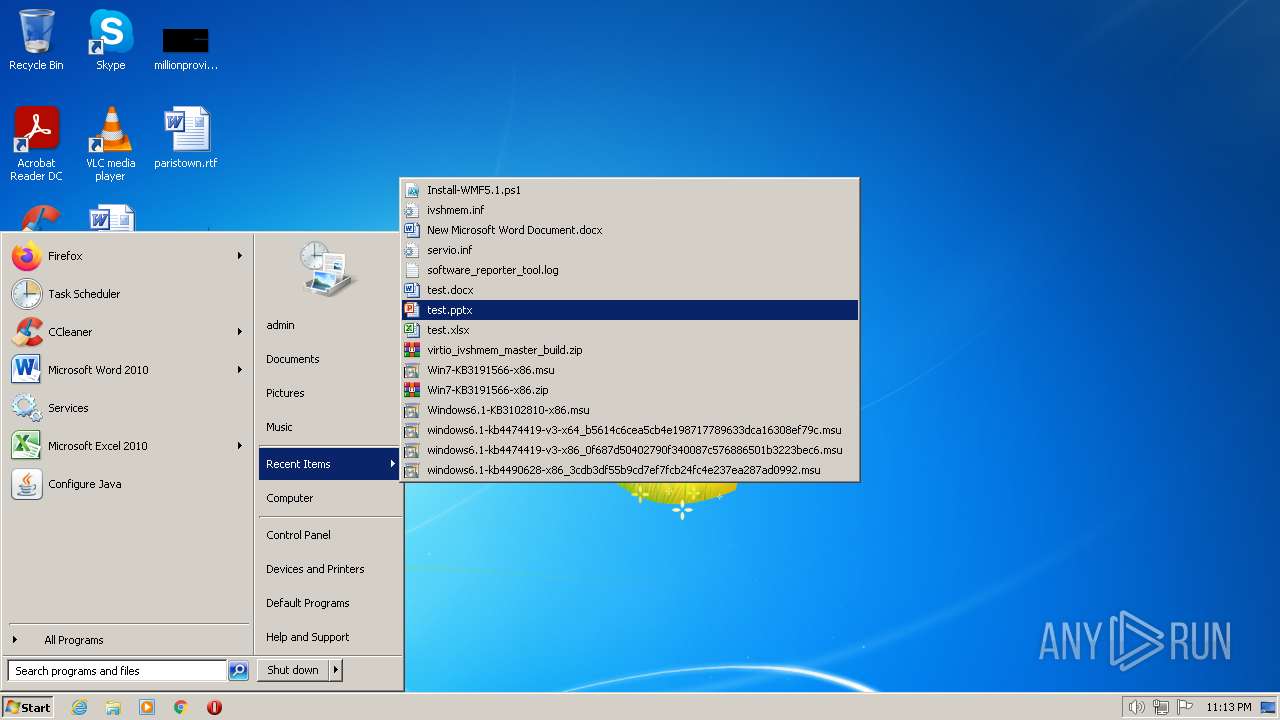
Manual execution by a user
- cmd.exe (PID: 2872)
Executable content was dropped or overwritten
- cmd.exe (PID: 2872)
Drops a file that was compiled in debug mode
- cmd.exe (PID: 2872)
Drops the executable file immediately after the start
- cmd.exe (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(2872) cmd.exe
C2www.needook.com/4u5a/
Strings (75)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Mail\
\Foxmail
\Storage\
\Accounts\Account.rec0
\Data\AccCfg\Accounts.tdat
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)Y9HWoINcPu0r7SSSKt4FCmk7
G/E64auYdhRQM4wZW2bcOaY=
bL57APty/StRpW49a+EdxA==
TppryJ0SoslHe8gJFVc=
HXxDShYIEcUJDahdv2nvl5Hlbp4=
EKaq5c6w0nV3WWlEqM4Www==
VM+YjE8XS1OLcH1roYF4zA==
OwK0wxmBGnq2Fg==
B1zy4bulyfY9tj9DK2eIkeYArpTt
Avj5JeA8m9girqfQ4+cZxA==
AOY4dmDFkCdX8HUJMw==
5cQUw3pPMYr07V8=
P7ZsN4/zt63AEw==
FYyVCOpB8Vl//kSkDLPo91Yy
jxwZTBp+5gcsccPxDF+K4bDG2Rpp0A==
iGx9AO58DRhZbXX9
prwVyLkAtlhSU6irmansg8wArpTt
uqa8ZPl+FFObOkdFNg==
tL4OhF22EDaEOkdFNg==
6exH76Z9o7eu/n86vgPE
rJfvmmO0I0KSOkdFNg==
fWeyPQpzFxdBSlPuAlA=
imNhpGXCQjOgCw==
KOLqYk7Qy278+j3g
A4mLyKgkynW7jZZt0F8=
380eDrCm3ApZbXX9
1k6VTs/04X8=
6yQgD+RiKrbnhr77i60lI/gyAQ==
rST4Evf891bSukI=
wYh6yzBy3wDSOkdFNg==
i0j/88JPuMOz
1t8w27cIepbAIqSh0G5dsiUnCw==
uI6hQB6EIE+bFW1woYF4zA==
BPL0Pin+82dmW/OhB0Fr5JHlbp4=
XC5/ZktMXzEnk+xGrPFSE+st
srT4c1/AacoX8F0=
zJeU2qIZ2VCSOkdFNg==
j4a8RbuBvuFZbXX9
asVC+9b7w7eu
L6UfqgNtQjOgCw==
yTgIJt0+qNUilvojOWqqBypDFg==
Ie006MzYHidZbXX9
fbVjId1kpfdZbXX9
w7z+dzqeJEZq2/A6vgPE
bkyOQjI+MYr07V8=
EODzbkTAOSJZbXX9
sZXWleMz4n7HrUI=
YuK38tZjKZ3eQJnC3jxvdM7D2Rpp0A==
VTJSAfJU7tISaHT/
d/gIXE8qLIr07V8=
F3XypWdIKor07V8=
uQaJTBhc8R4kr/I6vgPE
1T8ENSkKJLudaZZt0F8=
uc4eyKuvBidZbXX9
txCp1rM0oc4LhQHpKYJQUKKktIT3GWoNJw==
RMLQh/ZpQjOgCw==
0+Qt17zBCyNZbXX9
JC6jMCHmB77Eu/EFdap62w==
t4XGRQqC3kSB9Tpds2j0Wrg=
T7hCMhTkzX2mf4lVAQjjJOgz
DQ6VYEicGU+NFio7Lw==
PCpjzoTZU3Ol9T1coYF4zA==
DxVl5Jum/t5orqfQ4+cZxA==
OaM0F9KunPxoQUk/Nw==
C2www.needook.com/4u5a/
Strings (75)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Mail\
\Foxmail
\Storage\
\Accounts\Account.rec0
\Data\AccCfg\Accounts.tdat
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)wp-operator.online
openhardware.farm
nu2uresale.store
tefalito.store
maximumercrefund.com
bestcolonia.club
zhuanxiandai.com
www460.vip
smartturflawncare.com
pollicino.online
re-curve.tech
michari.com
33344.cyou
marketmall.digital
estacatemucocautin.com
dersameh.com
fangzizhuangxiu47.com
lee-perez.com
nekutenti.com
medhatkouta.com
jhfgroups.com
shopcheap.club
bjrkfw.com
tommy57.shop
anniistore.com
ope-cctv.com
05hc.com
y31jaihdb6zm87.buzz
easydaw.app
www659123.com
suppq.top
thebrotherhood.shop
videosrunman.com
powerscoumembers.com
lodehewulan.yachts
festpay.pro
zhukojobs.com
www64421.com
jxily.com
700544.com
skechersofferte.com
uloggers.com
yt82ra5c.com
kaylastjean.com
nyameci.com
talisian.com
api2022.top
darkchocolatebliss.com
mcarmen.info
kasslot.com
stublan.com
uknowmarket.com
cpitherapy.com
agikdnjs.com
canadianlocalbusiness.com
dkc010.com
cardgloo.com
fuzulyapigyo.xyz
steves.properties
guaiguaimao188.com
cityasset.net
burcinyilmaz.com
inhibit09.online
olanger.email
C2www.needook.com/4u5a/
Strings (75)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Mail\
\Foxmail
\Storage\
\Accounts\Account.rec0
\Data\AccCfg\Accounts.tdat
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)Y9HWoINcPu0r7SSSKt4FCmk7
G/E64auYdhRQM4wZW2bcOaY=
bL57APty/StRpW49a+EdxA==
TppryJ0SoslHe8gJFVc=
HXxDShYIEcUJDahdv2nvl5Hlbp4=
EKaq5c6w0nV3WWlEqM4Www==
VM+YjE8XS1OLcH1roYF4zA==
OwK0wxmBGnq2Fg==
B1zy4bulyfY9tj9DK2eIkeYArpTt
Avj5JeA8m9girqfQ4+cZxA==
AOY4dmDFkCdX8HUJMw==
5cQUw3pPMYr07V8=
P7ZsN4/zt63AEw==
FYyVCOpB8Vl//kSkDLPo91Yy
jxwZTBp+5gcsccPxDF+K4bDG2Rpp0A==
iGx9AO58DRhZbXX9
prwVyLkAtlhSU6irmansg8wArpTt
uqa8ZPl+FFObOkdFNg==
tL4OhF22EDaEOkdFNg==
6exH76Z9o7eu/n86vgPE
rJfvmmO0I0KSOkdFNg==
fWeyPQpzFxdBSlPuAlA=
imNhpGXCQjOgCw==
KOLqYk7Qy278+j3g
A4mLyKgkynW7jZZt0F8=
380eDrCm3ApZbXX9
1k6VTs/04X8=
6yQgD+RiKrbnhr77i60lI/gyAQ==
rST4Evf891bSukI=
wYh6yzBy3wDSOkdFNg==
i0j/88JPuMOz
1t8w27cIepbAIqSh0G5dsiUnCw==
uI6hQB6EIE+bFW1woYF4zA==
BPL0Pin+82dmW/OhB0Fr5JHlbp4=
XC5/ZktMXzEnk+xGrPFSE+st
srT4c1/AacoX8F0=
zJeU2qIZ2VCSOkdFNg==
j4a8RbuBvuFZbXX9
asVC+9b7w7eu
L6UfqgNtQjOgCw==
yTgIJt0+qNUilvojOWqqBypDFg==
Ie006MzYHidZbXX9
fbVjId1kpfdZbXX9
w7z+dzqeJEZq2/A6vgPE
bkyOQjI+MYr07V8=
EODzbkTAOSJZbXX9
sZXWleMz4n7HrUI=
YuK38tZjKZ3eQJnC3jxvdM7D2Rpp0A==
VTJSAfJU7tISaHT/
d/gIXE8qLIr07V8=
F3XypWdIKor07V8=
uQaJTBhc8R4kr/I6vgPE
1T8ENSkKJLudaZZt0F8=
uc4eyKuvBidZbXX9
txCp1rM0oc4LhQHpKYJQUKKktIT3GWoNJw==
RMLQh/ZpQjOgCw==
0+Qt17zBCyNZbXX9
JC6jMCHmB77Eu/EFdap62w==
t4XGRQqC3kSB9Tpds2j0Wrg=
T7hCMhTkzX2mf4lVAQjjJOgz
DQ6VYEicGU+NFio7Lw==
PCpjzoTZU3Ol9T1coYF4zA==
DxVl5Jum/t5orqfQ4+cZxA==
OaM0F9KunPxoQUk/Nw==
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2103-Nov-18 21:46:25 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | HNIOPLN |
| FileVersion: | 1.0.0.0 |
| InternalName: | HNIOPLN.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | - |
| OriginalFilename: | HNIOPLN.exe |
| ProductName: | HNIOPLN |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 5 |
| TimeDateStamp: | 2103-Nov-18 21:46:25 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
X\x166F)"#\x19 | 8192 | 285236 | 285696 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99936 |
.text | 294912 | 42028 | 42496 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06849 |
.rsrc | 344064 | 5858 | 6144 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.35264 |
Section_4 | 352256 | 16 | 512 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.122276 |
.reloc | 360448 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.15503 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 1.7815 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 3.27039 | 780 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#3) | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
38
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Users\admin\AppData\Local\Temp\Cat2022DecFile58373.exe" | C:\Users\admin\AppData\Local\Temp\Cat2022DecFile58373.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: HNIOPLN Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1084 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | — | cmd.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2872 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
Formbook(PID) Process(2872) cmd.exe C2www.needook.com/4u5a/ Strings (75)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Mail\ \Foxmail \Storage\ \Accounts\Account.rec0 \Data\AccCfg\Accounts.tdat \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)Y9HWoINcPu0r7SSSKt4FCmk7 G/E64auYdhRQM4wZW2bcOaY= bL57APty/StRpW49a+EdxA== TppryJ0SoslHe8gJFVc= HXxDShYIEcUJDahdv2nvl5Hlbp4= EKaq5c6w0nV3WWlEqM4Www== VM+YjE8XS1OLcH1roYF4zA== OwK0wxmBGnq2Fg== B1zy4bulyfY9tj9DK2eIkeYArpTt Avj5JeA8m9girqfQ4+cZxA== AOY4dmDFkCdX8HUJMw== 5cQUw3pPMYr07V8= P7ZsN4/zt63AEw== FYyVCOpB8Vl//kSkDLPo91Yy jxwZTBp+5gcsccPxDF+K4bDG2Rpp0A== iGx9AO58DRhZbXX9 prwVyLkAtlhSU6irmansg8wArpTt uqa8ZPl+FFObOkdFNg== tL4OhF22EDaEOkdFNg== 6exH76Z9o7eu/n86vgPE rJfvmmO0I0KSOkdFNg== fWeyPQpzFxdBSlPuAlA= imNhpGXCQjOgCw== KOLqYk7Qy278+j3g A4mLyKgkynW7jZZt0F8= 380eDrCm3ApZbXX9 1k6VTs/04X8= 6yQgD+RiKrbnhr77i60lI/gyAQ== rST4Evf891bSukI= wYh6yzBy3wDSOkdFNg== i0j/88JPuMOz 1t8w27cIepbAIqSh0G5dsiUnCw== uI6hQB6EIE+bFW1woYF4zA== BPL0Pin+82dmW/OhB0Fr5JHlbp4= XC5/ZktMXzEnk+xGrPFSE+st srT4c1/AacoX8F0= zJeU2qIZ2VCSOkdFNg== j4a8RbuBvuFZbXX9 asVC+9b7w7eu L6UfqgNtQjOgCw== yTgIJt0+qNUilvojOWqqBypDFg== Ie006MzYHidZbXX9 fbVjId1kpfdZbXX9 w7z+dzqeJEZq2/A6vgPE bkyOQjI+MYr07V8= EODzbkTAOSJZbXX9 sZXWleMz4n7HrUI= YuK38tZjKZ3eQJnC3jxvdM7D2Rpp0A== VTJSAfJU7tISaHT/ d/gIXE8qLIr07V8= F3XypWdIKor07V8= uQaJTBhc8R4kr/I6vgPE 1T8ENSkKJLudaZZt0F8= uc4eyKuvBidZbXX9 txCp1rM0oc4LhQHpKYJQUKKktIT3GWoNJw== RMLQh/ZpQjOgCw== 0+Qt17zBCyNZbXX9 JC6jMCHmB77Eu/EFdap62w== t4XGRQqC3kSB9Tpds2j0Wrg= T7hCMhTkzX2mf4lVAQjjJOgz DQ6VYEicGU+NFio7Lw== PCpjzoTZU3Ol9T1coYF4zA== DxVl5Jum/t5orqfQ4+cZxA== OaM0F9KunPxoQUk/Nw== (PID) Process(2872) cmd.exe C2www.needook.com/4u5a/ Strings (75)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Mail\ \Foxmail \Storage\ \Accounts\Account.rec0 \Data\AccCfg\Accounts.tdat \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)wp-operator.online openhardware.farm nu2uresale.store tefalito.store maximumercrefund.com bestcolonia.club zhuanxiandai.com www460.vip smartturflawncare.com pollicino.online re-curve.tech michari.com 33344.cyou marketmall.digital estacatemucocautin.com dersameh.com fangzizhuangxiu47.com lee-perez.com nekutenti.com medhatkouta.com jhfgroups.com shopcheap.club bjrkfw.com tommy57.shop anniistore.com ope-cctv.com 05hc.com y31jaihdb6zm87.buzz easydaw.app www659123.com suppq.top thebrotherhood.shop videosrunman.com powerscoumembers.com lodehewulan.yachts festpay.pro zhukojobs.com www64421.com jxily.com 700544.com skechersofferte.com uloggers.com yt82ra5c.com kaylastjean.com nyameci.com talisian.com api2022.top darkchocolatebliss.com mcarmen.info kasslot.com stublan.com uknowmarket.com cpitherapy.com agikdnjs.com canadianlocalbusiness.com dkc010.com cardgloo.com fuzulyapigyo.xyz steves.properties guaiguaimao188.com cityasset.net burcinyilmaz.com inhibit09.online olanger.email (PID) Process(2872) cmd.exe C2www.needook.com/4u5a/ Strings (75)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Mail\ \Foxmail \Storage\ \Accounts\Account.rec0 \Data\AccCfg\Accounts.tdat \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)Y9HWoINcPu0r7SSSKt4FCmk7 G/E64auYdhRQM4wZW2bcOaY= bL57APty/StRpW49a+EdxA== TppryJ0SoslHe8gJFVc= HXxDShYIEcUJDahdv2nvl5Hlbp4= EKaq5c6w0nV3WWlEqM4Www== VM+YjE8XS1OLcH1roYF4zA== OwK0wxmBGnq2Fg== B1zy4bulyfY9tj9DK2eIkeYArpTt Avj5JeA8m9girqfQ4+cZxA== AOY4dmDFkCdX8HUJMw== 5cQUw3pPMYr07V8= P7ZsN4/zt63AEw== FYyVCOpB8Vl//kSkDLPo91Yy jxwZTBp+5gcsccPxDF+K4bDG2Rpp0A== iGx9AO58DRhZbXX9 prwVyLkAtlhSU6irmansg8wArpTt uqa8ZPl+FFObOkdFNg== tL4OhF22EDaEOkdFNg== 6exH76Z9o7eu/n86vgPE rJfvmmO0I0KSOkdFNg== fWeyPQpzFxdBSlPuAlA= imNhpGXCQjOgCw== KOLqYk7Qy278+j3g A4mLyKgkynW7jZZt0F8= 380eDrCm3ApZbXX9 1k6VTs/04X8= 6yQgD+RiKrbnhr77i60lI/gyAQ== rST4Evf891bSukI= wYh6yzBy3wDSOkdFNg== i0j/88JPuMOz 1t8w27cIepbAIqSh0G5dsiUnCw== uI6hQB6EIE+bFW1woYF4zA== BPL0Pin+82dmW/OhB0Fr5JHlbp4= XC5/ZktMXzEnk+xGrPFSE+st srT4c1/AacoX8F0= zJeU2qIZ2VCSOkdFNg== j4a8RbuBvuFZbXX9 asVC+9b7w7eu L6UfqgNtQjOgCw== yTgIJt0+qNUilvojOWqqBypDFg== Ie006MzYHidZbXX9 fbVjId1kpfdZbXX9 w7z+dzqeJEZq2/A6vgPE bkyOQjI+MYr07V8= EODzbkTAOSJZbXX9 sZXWleMz4n7HrUI= YuK38tZjKZ3eQJnC3jxvdM7D2Rpp0A== VTJSAfJU7tISaHT/ d/gIXE8qLIr07V8= F3XypWdIKor07V8= uQaJTBhc8R4kr/I6vgPE 1T8ENSkKJLudaZZt0F8= uc4eyKuvBidZbXX9 txCp1rM0oc4LhQHpKYJQUKKktIT3GWoNJw== RMLQh/ZpQjOgCw== 0+Qt17zBCyNZbXX9 JC6jMCHmB77Eu/EFdap62w== t4XGRQqC3kSB9Tpds2j0Wrg= T7hCMhTkzX2mf4lVAQjjJOgz DQ6VYEicGU+NFio7Lw== PCpjzoTZU3Ol9T1coYF4zA== DxVl5Jum/t5orqfQ4+cZxA== OaM0F9KunPxoQUk/Nw== | |||||||||||||||
| 3348 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | Cat2022DecFile58373.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
Total events
4 618
Read events
4 217
Write events
400
Delete events
1
Modification events
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2872) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | cmd.exe | C:\Users\admin\AppData\Local\Temp\sqlite3.def | text | |
MD5:88B78A6F643D3341AE9BF96D5816F1C2 | SHA256:8CA12E8B973A1974E160AE2E55F2B59870314DF159BA2DC54C7349ACEE176EBE | |||
| 2872 | cmd.exe | C:\Users\admin\AppData\Local\Temp\lhylq.zip | compressed | |
MD5:A9A3B70ADCF65BE80C9B00E65D158669 | SHA256:BDCD90D909C708EFF9A829C01B428C2B24FAFC15F63DECCD064C2BB12B0A49E3 | |||
| 2872 | cmd.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\sqlite-dll-win32-x86-3360000[1].zip | compressed | |
MD5:A9A3B70ADCF65BE80C9B00E65D158669 | SHA256:BDCD90D909C708EFF9A829C01B428C2B24FAFC15F63DECCD064C2BB12B0A49E3 | |||
| 2872 | cmd.exe | C:\Users\admin\AppData\Local\Temp\1--Lt08NN | sqlite | |
MD5:CC104C4E4E904C3AD7AD5C45FBFA7087 | SHA256:321BE844CECC903EF1E7F875B729C96BB3ED0D4986314384CD5944A29A670C9B | |||
| 2872 | cmd.exe | C:\Users\admin\AppData\Local\Temp\sqlite3.dll | executable | |
MD5:CE5C15B5092877974D5B6476AD1CB2D7 | SHA256:1F1A186EA26BD2462EA2A9CF35A816B92CAF0897FDF332AF3A61569E0BA97B24 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
39
DNS requests
11
Threats
76
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1084 | Explorer.EXE | POST | — | 94.23.162.163:80 | http://www.darkchocolatebliss.com/4u5a/ | DE | — | — | malicious |
1084 | Explorer.EXE | POST | — | 94.23.162.163:80 | http://www.darkchocolatebliss.com/4u5a/ | DE | — | — | malicious |
1084 | Explorer.EXE | POST | — | 94.23.162.163:80 | http://www.darkchocolatebliss.com/4u5a/ | DE | — | — | malicious |
1084 | Explorer.EXE | POST | — | 94.23.162.163:80 | http://www.darkchocolatebliss.com/4u5a/ | DE | — | — | malicious |
1084 | Explorer.EXE | POST | — | 94.23.162.163:80 | http://www.darkchocolatebliss.com/4u5a/ | DE | — | — | malicious |
1084 | Explorer.EXE | POST | 405 | 89.31.143.1:80 | http://www.dersameh.com/4u5a/ | DE | html | 150 b | malicious |
2872 | cmd.exe | GET | 200 | 45.33.6.223:80 | http://www.sqlite.org/2021/sqlite-dll-win32-x86-3360000.zip | US | compressed | 542 Kb | whitelisted |
1084 | Explorer.EXE | POST | 405 | 89.31.143.1:80 | http://www.dersameh.com/4u5a/ | DE | html | 150 b | malicious |
1084 | Explorer.EXE | POST | 405 | 89.31.143.1:80 | http://www.dersameh.com/4u5a/ | DE | html | 150 b | malicious |
1084 | Explorer.EXE | POST | 405 | 89.31.143.1:80 | http://www.dersameh.com/4u5a/ | DE | html | 150 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1084 | Explorer.EXE | 38.55.236.89:80 | www.ope-cctv.com | STARCLOUD GLOBAL PTE., LTD. | US | malicious |
2872 | cmd.exe | 45.33.6.223:80 | www.sqlite.org | Linode, LLC | US | suspicious |
1084 | Explorer.EXE | 89.31.143.1:80 | www.dersameh.com | IP Exchange GmbH | DE | malicious |
— | — | 89.31.143.1:80 | www.dersameh.com | IP Exchange GmbH | DE | malicious |
1084 | Explorer.EXE | 94.23.162.163:80 | www.darkchocolatebliss.com | OVH SAS | DE | malicious |
— | — | 94.23.162.163:80 | www.darkchocolatebliss.com | OVH SAS | DE | malicious |
1084 | Explorer.EXE | 154.209.6.241:80 | www.y31jaihdb6zm87.buzz | YISU CLOUD LTD | HK | malicious |
2872 | cmd.exe | 154.209.6.241:80 | www.y31jaihdb6zm87.buzz | YISU CLOUD LTD | HK | malicious |
1084 | Explorer.EXE | 162.213.255.142:80 | www.marketmall.digital | NAMECHEAP-NET | US | malicious |
1084 | Explorer.EXE | 172.67.148.132:80 | www.canadianlocalbusiness.com | CLOUDFLARENET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ope-cctv.com |
| malicious |
www.sqlite.org |
| whitelisted |
www.dersameh.com |
| malicious |
www.darkchocolatebliss.com |
| malicious |
www.y31jaihdb6zm87.buzz |
| malicious |
dns.msftncsi.com |
| shared |
www.marketmall.digital |
| malicious |
www.canadianlocalbusiness.com |
| malicious |
www.fuzulyapigyo.xyz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1084 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1084 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1084 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1084 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1084 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1084 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1084 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1084 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1084 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1084 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (POST) M2 |
11 ETPRO signatures available at the full report