| File name: | RFQOCEAN5645457788.lzh |
| Full analysis: | https://app.any.run/tasks/3b8a4ddf-f721-4969-a577-839132199ad2 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | September 02, 2024, 07:09:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
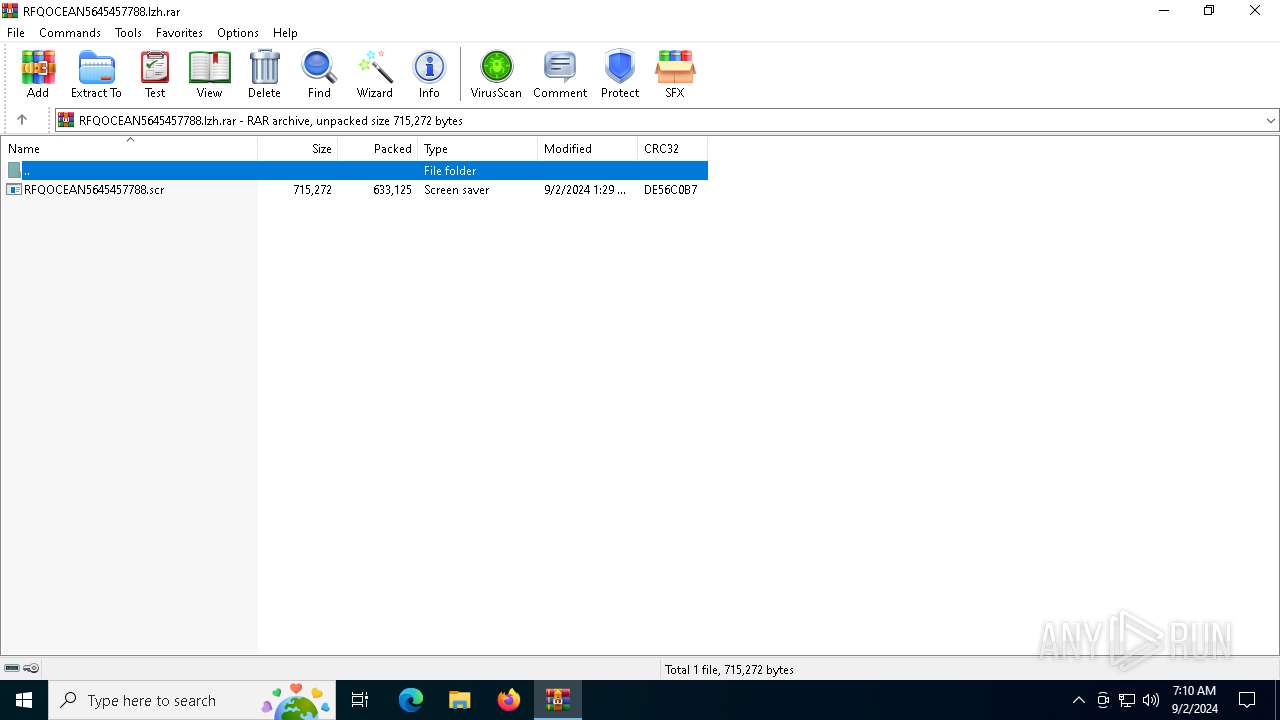
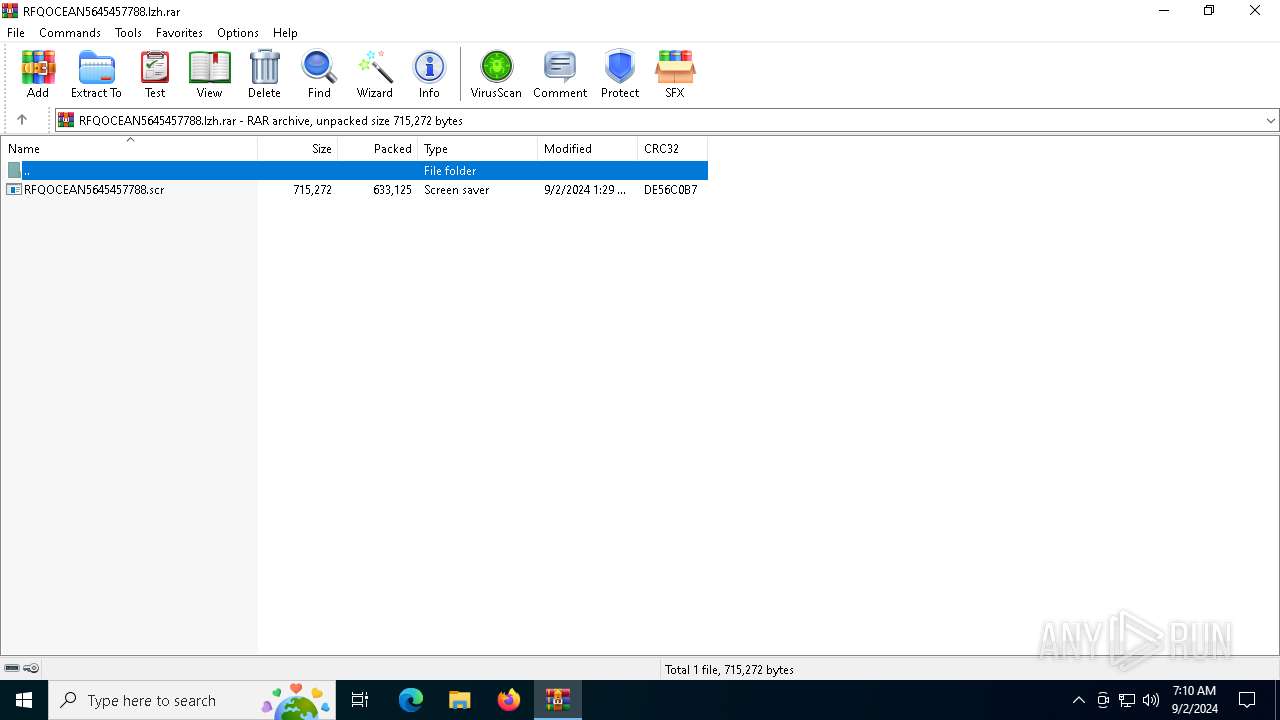
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | EAF1FD361980FCD3BD0C46C1F67080B7 |
| SHA1: | D2E162F3CDFD695A844A834E5C55FB5D6071B993 |
| SHA256: | 151A928481EA398F50D2154CB27527B5CBEB88C49F589E16C035BC8E18D9F9E3 |
| SSDEEP: | 24576:g99hiGC9irJaTt7kjuYhVuqpU4s7o5MquDiiKqpIZWYm0ApHc3DiX2:gHUGC9oJaTt7kjuYhVuqe4sU5MquDii0 |
MALICIOUS
FORMBOOK has been detected (YARA)
- svchost.exe (PID: 2576)
SUSPICIOUS
Deletes system .NET executable
- cmd.exe (PID: 2112)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 2576)
INFO
Reads the computer name
- RegSvcs.exe (PID: 6556)
- RFQOCEAN5645457788.scr (PID: 4064)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6792)
The process uses the downloaded file
- WinRAR.exe (PID: 6792)
Checks supported languages
- RFQOCEAN5645457788.scr (PID: 4064)
- RegSvcs.exe (PID: 6556)
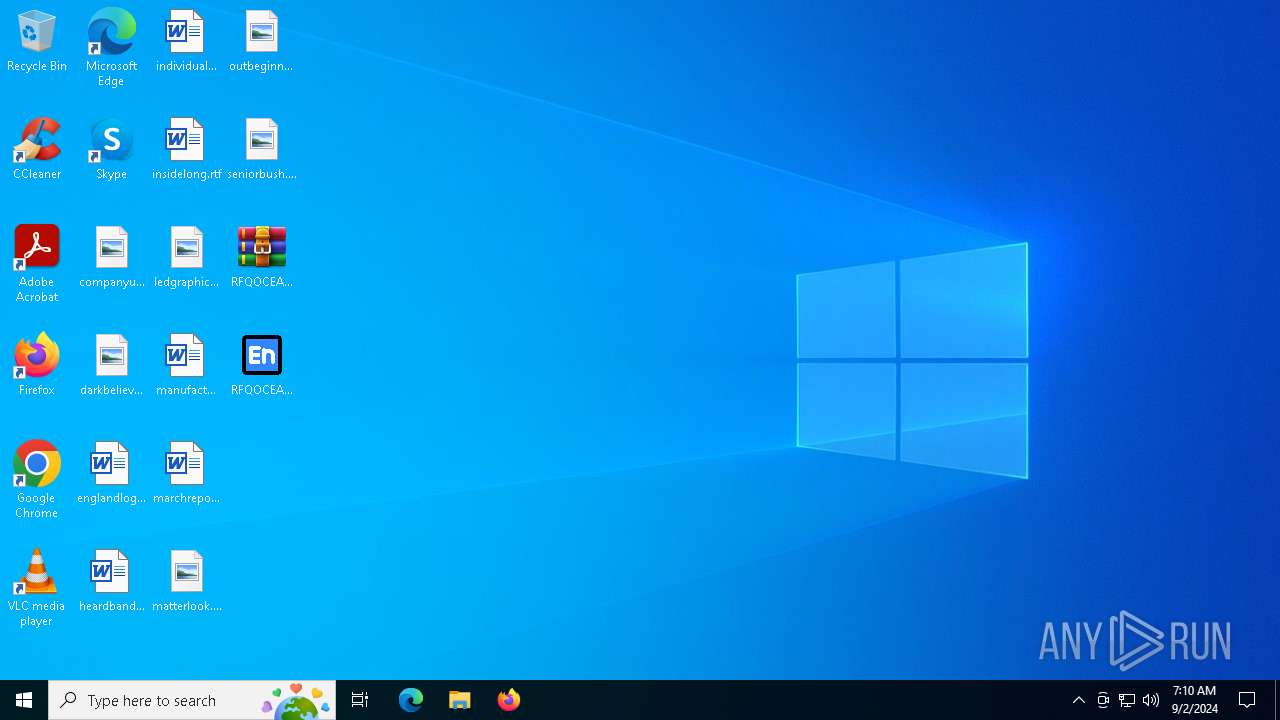
Manual execution by a user
- RFQOCEAN5645457788.scr (PID: 4064)
- svchost.exe (PID: 2576)
Reads the machine GUID from the registry
- RFQOCEAN5645457788.scr (PID: 4064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(2576) svchost.exe
C2www.ysticastrospain.online/m49z/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)ormswarm.xyz
awn-care-63587.bond
uymetanail5.online
mergencyloan007.xyz
545.top
eiliao596.pro
ackersandmoverschennai.net
ehdiahmadvandmusicbest.click
tlgxmb2024.cloud
ulfcoastharborhopper.pro
rohns-disease-early-signs.today
oldenhorizonsbgcl.click
weetindulgencepro.xyz
yexoiup.xyz
yself-solar.net
kfirsatimla.online
bropub3.online
ouljourney.online
usvf76f.shop
onnaberich.online
erminia.net
nline-advertising-91281.bond
pt-23.live
ayhentai.vip
ockyjapan.net
est-mortgage-loan-2507.today
uikfox.click
870077.vip
hzjjys88.vip
hayrain.shop
63638d.xyz
ines.cafe
oomed.shop
addy-cazino.online
ellybharat.net
razeonthego.net
ickbrady.dev
872277.vip
nwoebz.shop
udatoga.xyz
j10j.xyz
utogongcom.net
14oz957dd.autos
sgarasjeport.online
xrmxfh150.xyz
3win2.top
alrv9s8.christmas
0847.photo
aturally-canadian.beauty
artnelide.top
ropertiesforrentfr.bond
j11j.xyz
otaislifexd.xyz
zesuteta.shop
avaburrn.rest
azavivianonline.tech
ealthcare-software-96535.bond
atrixdon.online
group.tech
ertiberiaterra.net
pneesxw.christmas
assaporteapn.shop
hangwuyi.cfd
ounter-courses.world
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
136
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2112 | /c del "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\SysWOW64\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2576 | "C:\Windows\SysWOW64\svchost.exe" | C:\Windows\SysWOW64\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
Formbook(PID) Process(2576) svchost.exe C2www.ysticastrospain.online/m49z/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)ormswarm.xyz awn-care-63587.bond uymetanail5.online mergencyloan007.xyz 545.top eiliao596.pro ackersandmoverschennai.net ehdiahmadvandmusicbest.click tlgxmb2024.cloud ulfcoastharborhopper.pro rohns-disease-early-signs.today oldenhorizonsbgcl.click weetindulgencepro.xyz yexoiup.xyz yself-solar.net kfirsatimla.online bropub3.online ouljourney.online usvf76f.shop onnaberich.online erminia.net nline-advertising-91281.bond pt-23.live ayhentai.vip ockyjapan.net est-mortgage-loan-2507.today uikfox.click 870077.vip hzjjys88.vip hayrain.shop 63638d.xyz ines.cafe oomed.shop addy-cazino.online ellybharat.net razeonthego.net ickbrady.dev 872277.vip nwoebz.shop udatoga.xyz j10j.xyz utogongcom.net 14oz957dd.autos sgarasjeport.online xrmxfh150.xyz 3win2.top alrv9s8.christmas 0847.photo aturally-canadian.beauty artnelide.top ropertiesforrentfr.bond j11j.xyz otaislifexd.xyz zesuteta.shop avaburrn.rest azavivianonline.tech ealthcare-software-96535.bond atrixdon.online group.tech ertiberiaterra.net pneesxw.christmas assaporteapn.shop hangwuyi.cfd ounter-courses.world | |||||||||||||||
| 2868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4064 | "C:\Users\admin\Desktop\RFQOCEAN5645457788.scr" /S | C:\Users\admin\Desktop\RFQOCEAN5645457788.scr | — | explorer.exe | |||||||||||
User: admin Company: 767556767 Integrity Level: MEDIUM Description: 778yugh Exit code: 0 Version: 13.13.13.13 Modules
| |||||||||||||||
| 6556 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | RFQOCEAN5645457788.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
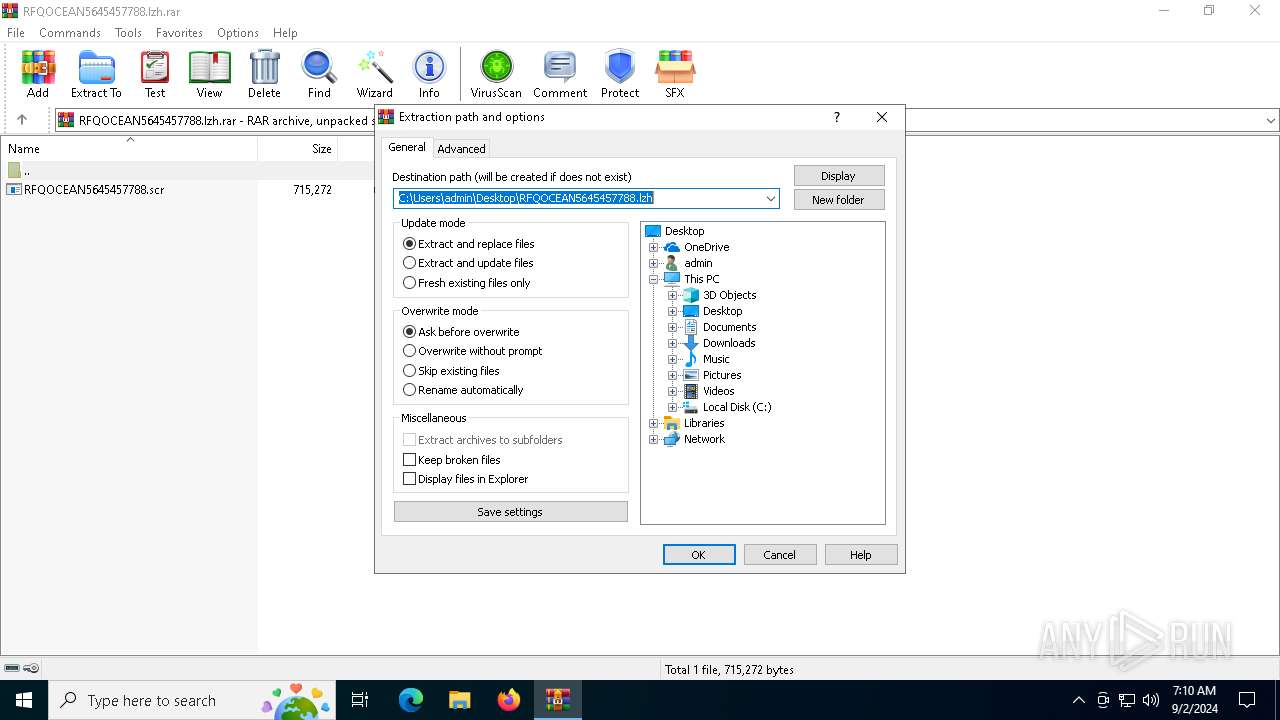
| 6792 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\RFQOCEAN5645457788.lzh.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
4 367
Read events
4 346
Write events
21
Delete events
0
Modification events
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\RFQOCEAN5645457788.lzh.rar | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @shell32,-10162 |
Value: Screen saver | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\RFQOCEAN5645457788.scr | executable | |
MD5:37DEB8C1285C7787FE88A51B5064A435 | SHA256:C8500ADF5318AA42E5CFE9D6EFE18D328538A6D8B36765D68820D2B99C3C9626 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
33
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2036 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4040 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4040 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6164 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4276 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6164 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2036 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2036 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.uikfox.click |
| unknown |
www.ormswarm.xyz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |