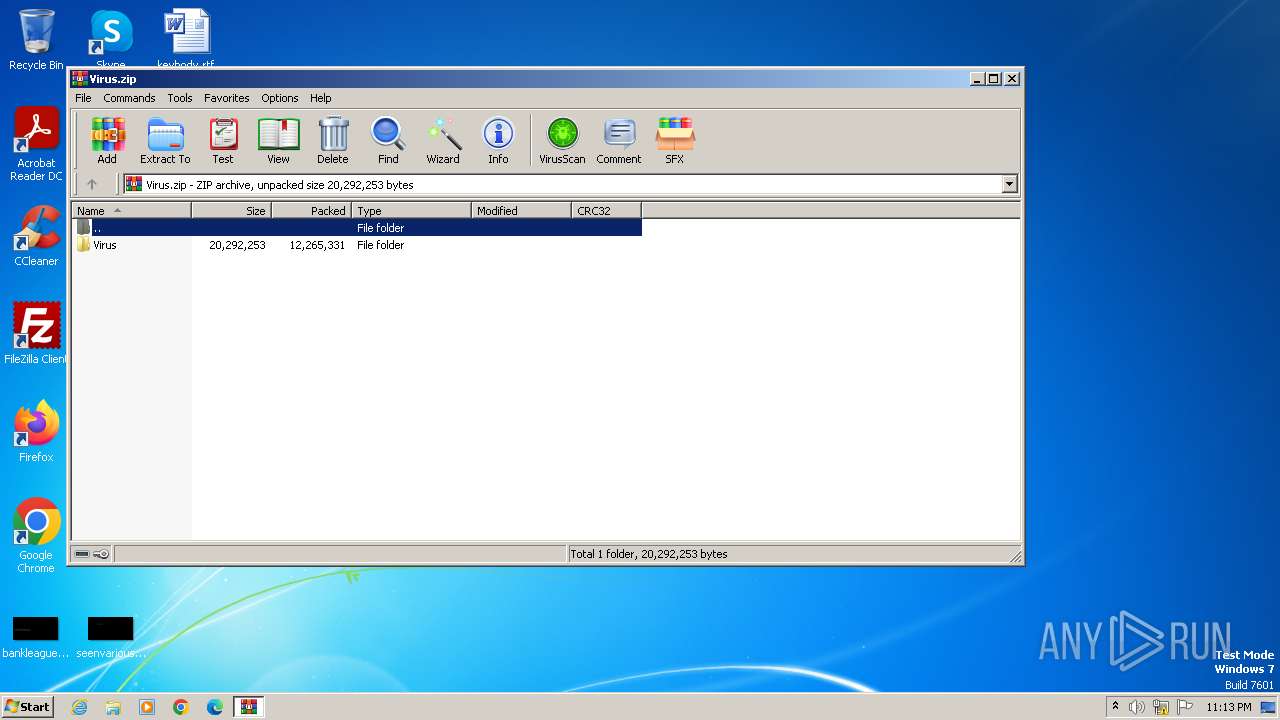
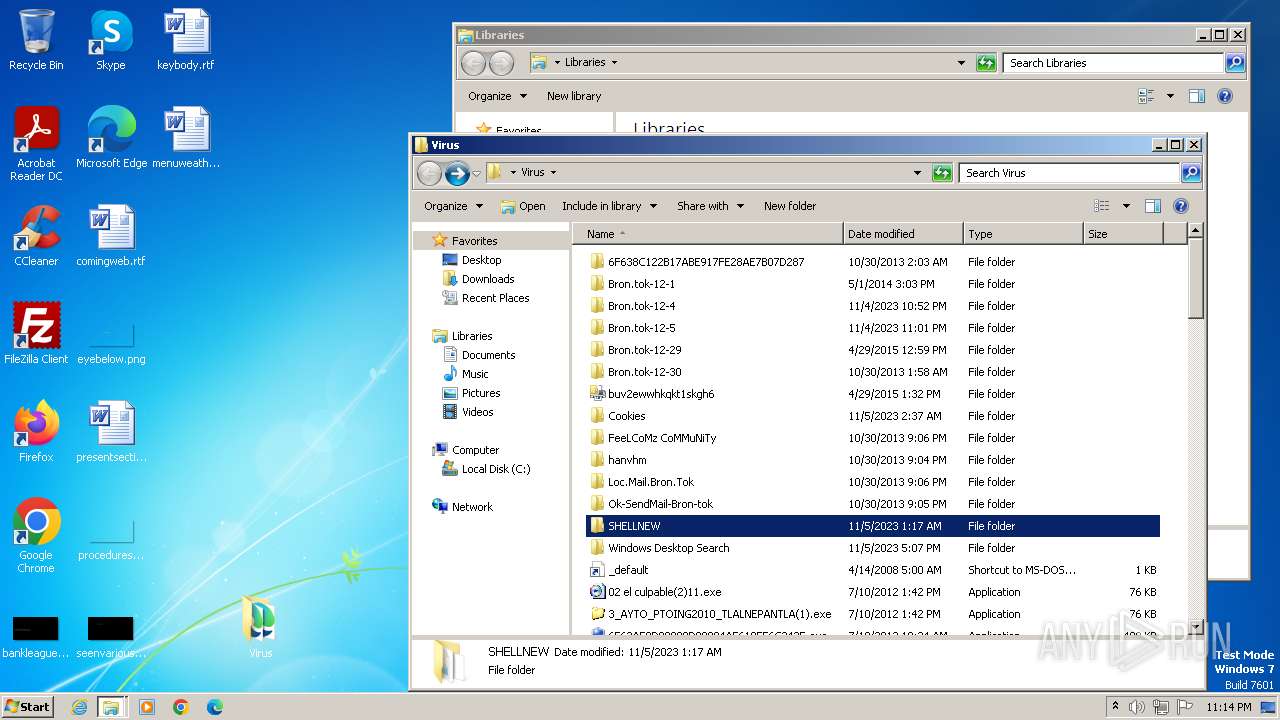
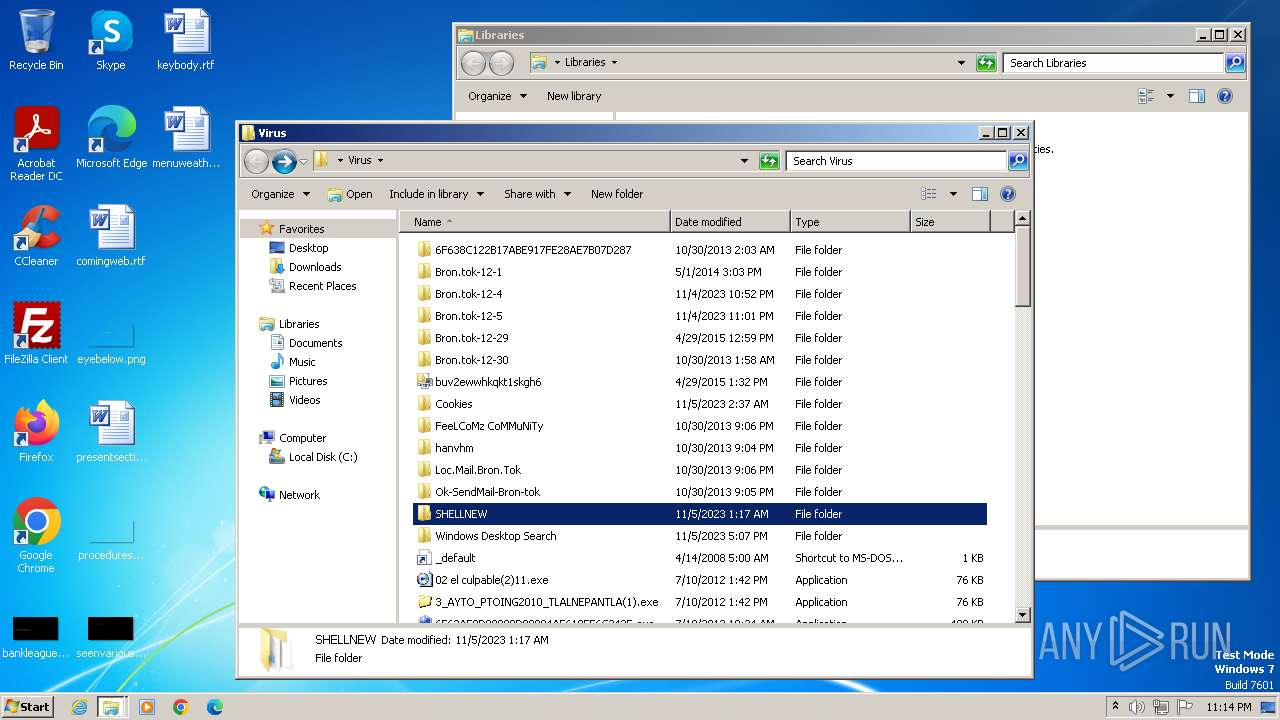
| File name: | Virus.zip |
| Full analysis: | https://app.any.run/tasks/237448ed-5d33-4565-84d9-599fa3acf5de |
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | November 06, 2023, 23:13:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3CA9B55E573DCC977BB1167D5A3D6FD0 |
| SHA1: | 50AE8AFE81B62BBB170523E6A3E6404F5460C1D7 |
| SHA256: | 15016FB331CEF2F2CE4FEDA5CE61B5560E7BE4CA031D0759531C9A639229FB06 |
| SSDEEP: | 98304:/dOmsMV7Q1TpfJd5DkBhMwHeqnBHAJ0wOqwHeqnBHAJ0wORXauNeeGhmXc8KH1Zs:mdgaLJLP8PGACaLOxpJQ |
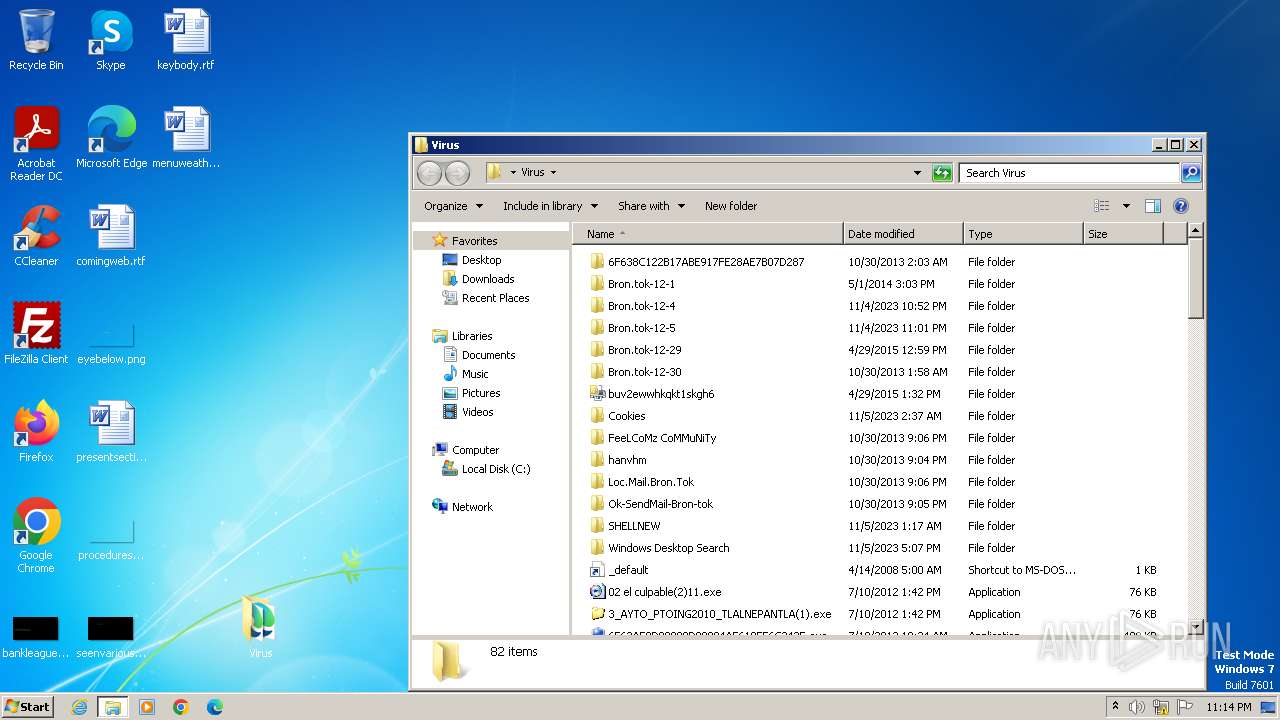
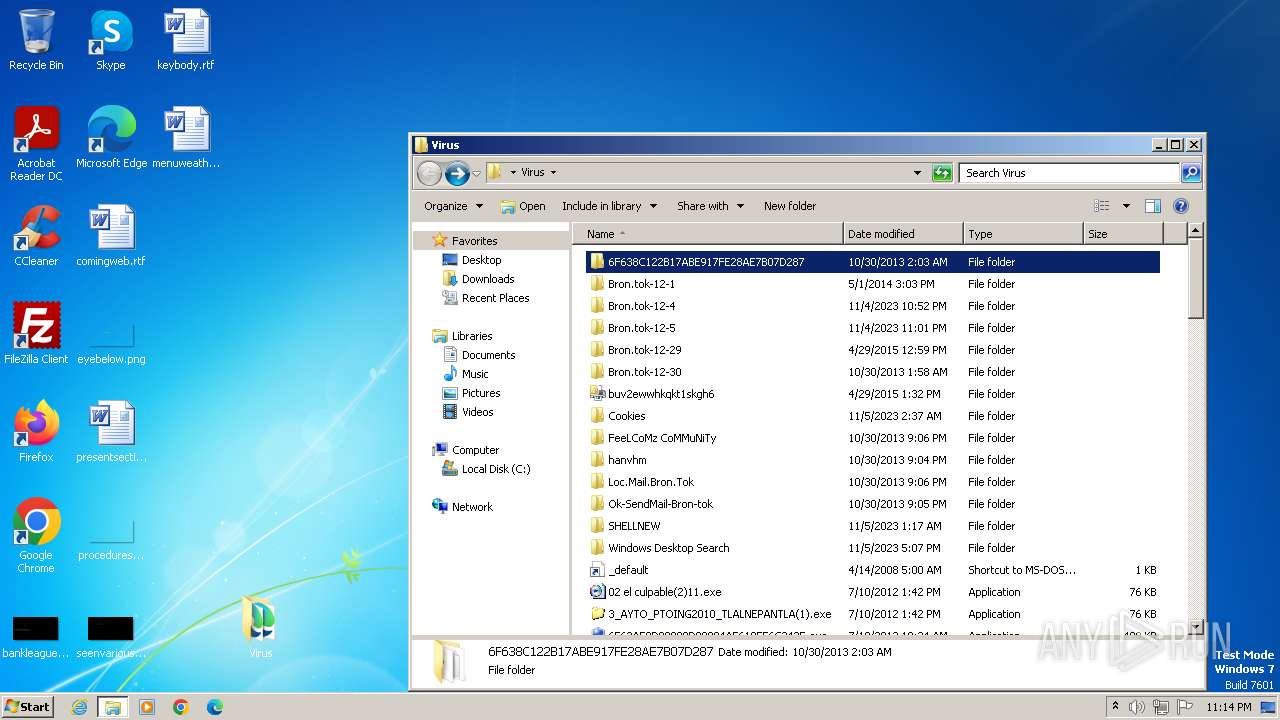
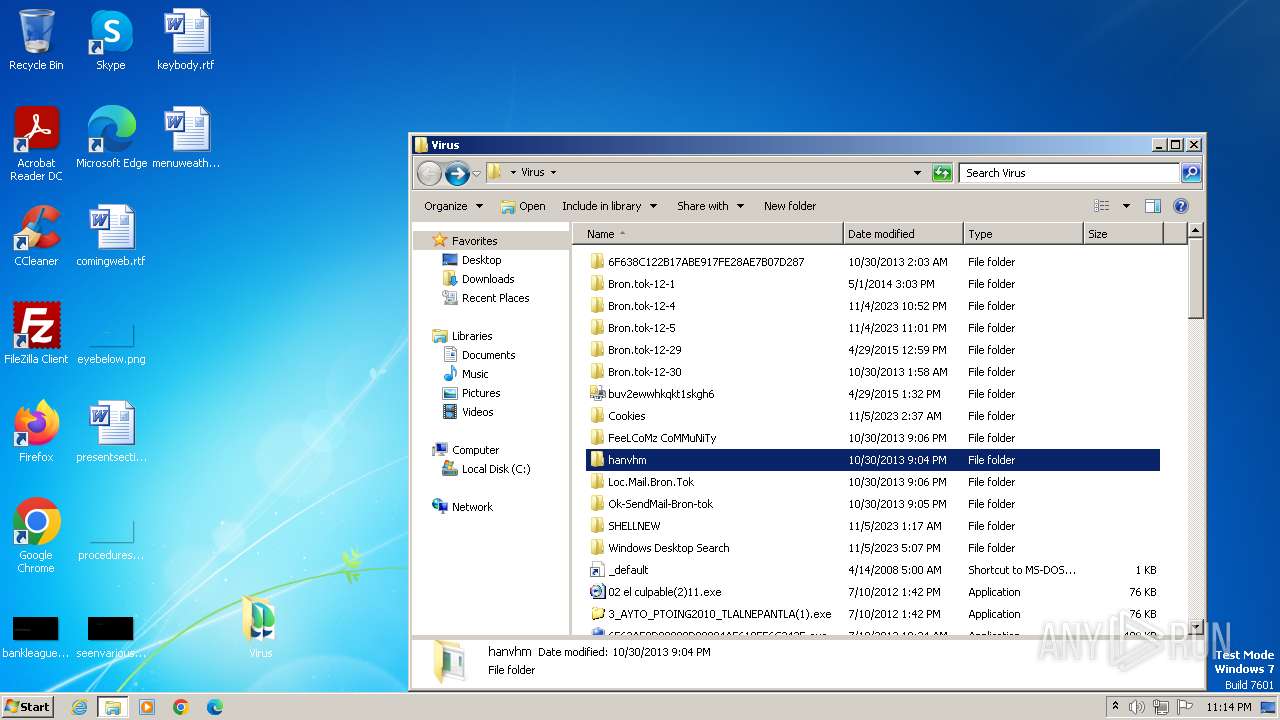
MALICIOUS
WINWEBSEC has been detected (SURICATA)
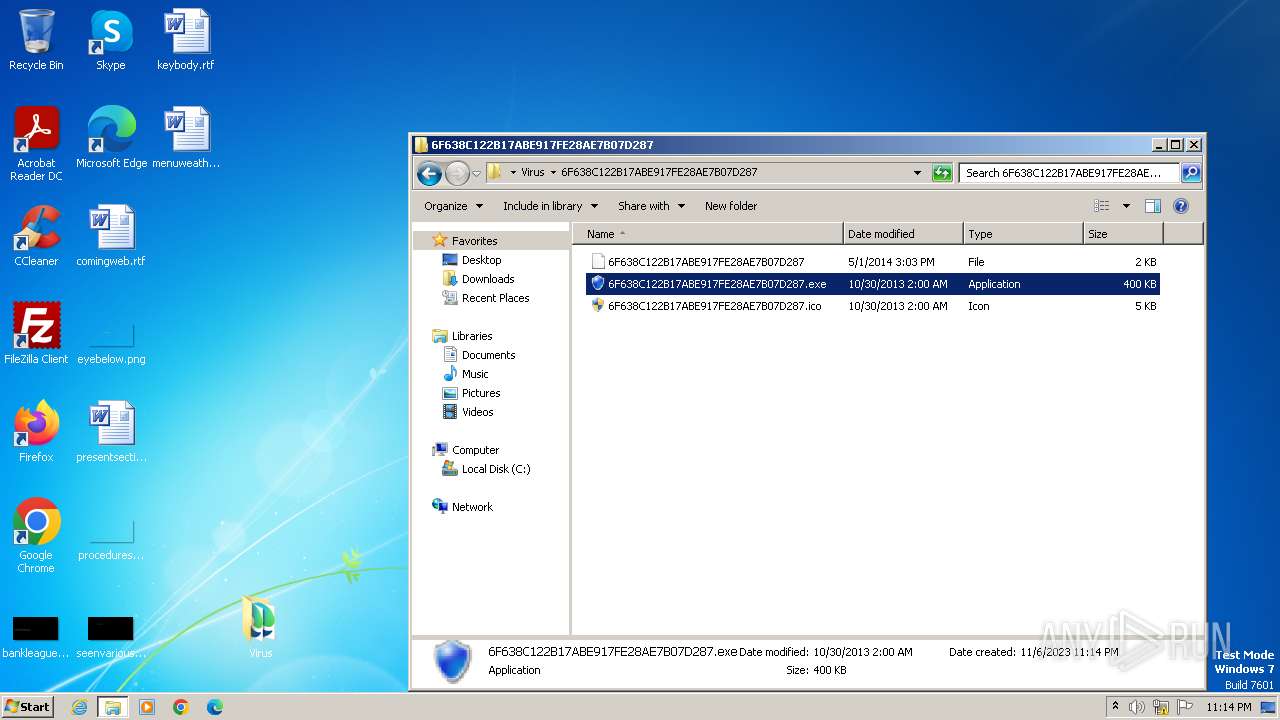
- 6F638C122B17ABE917FE28AE7B07D287.exe (PID: 3632)
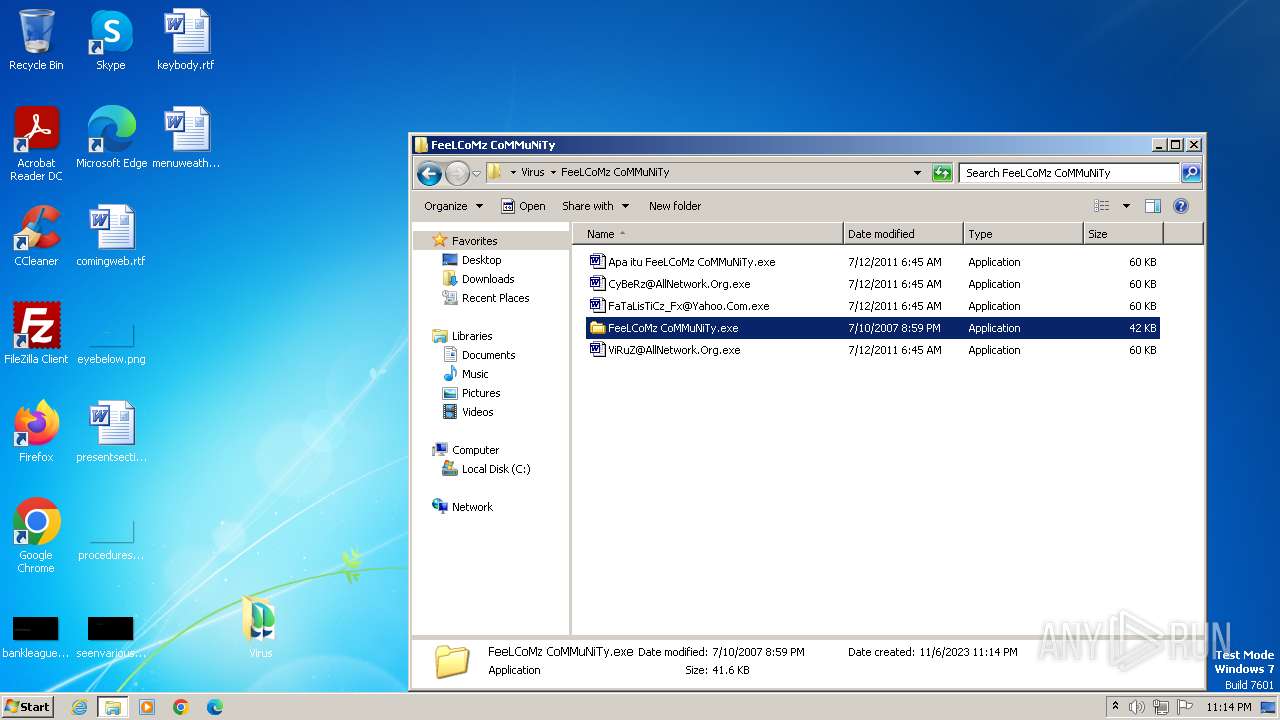
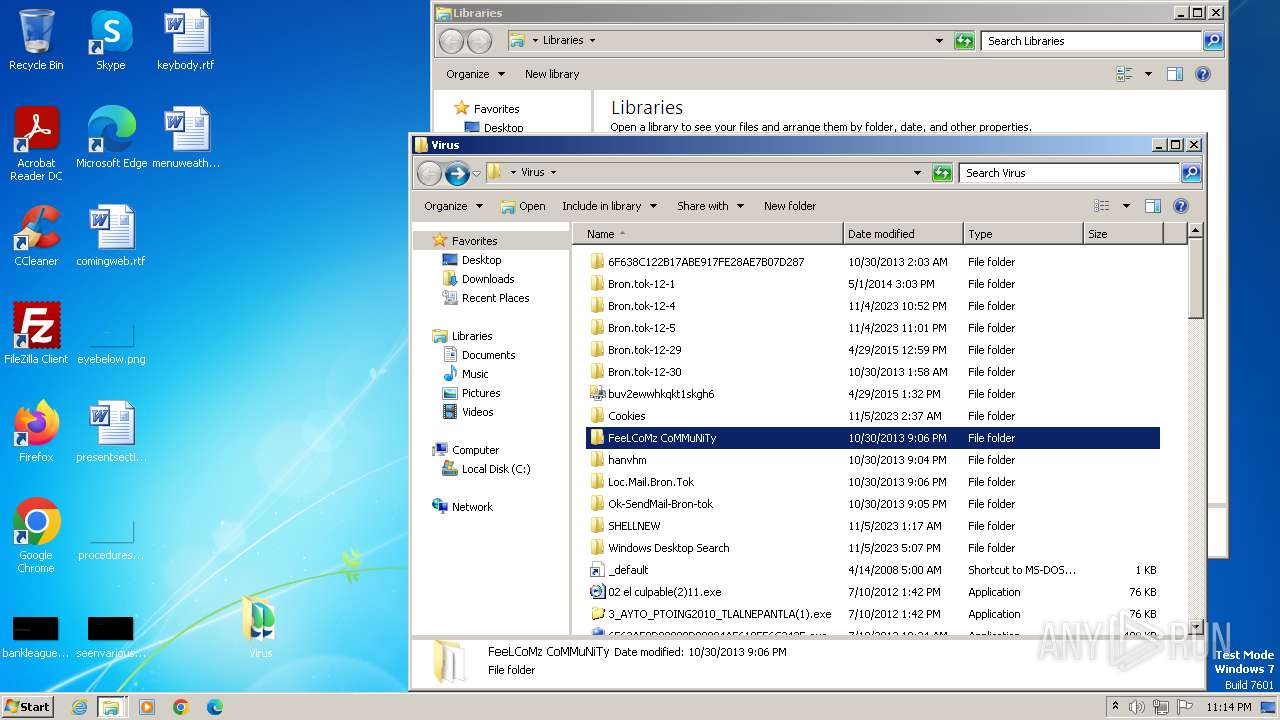
Drops the executable file immediately after the start
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- smss.exe (PID: 3616)
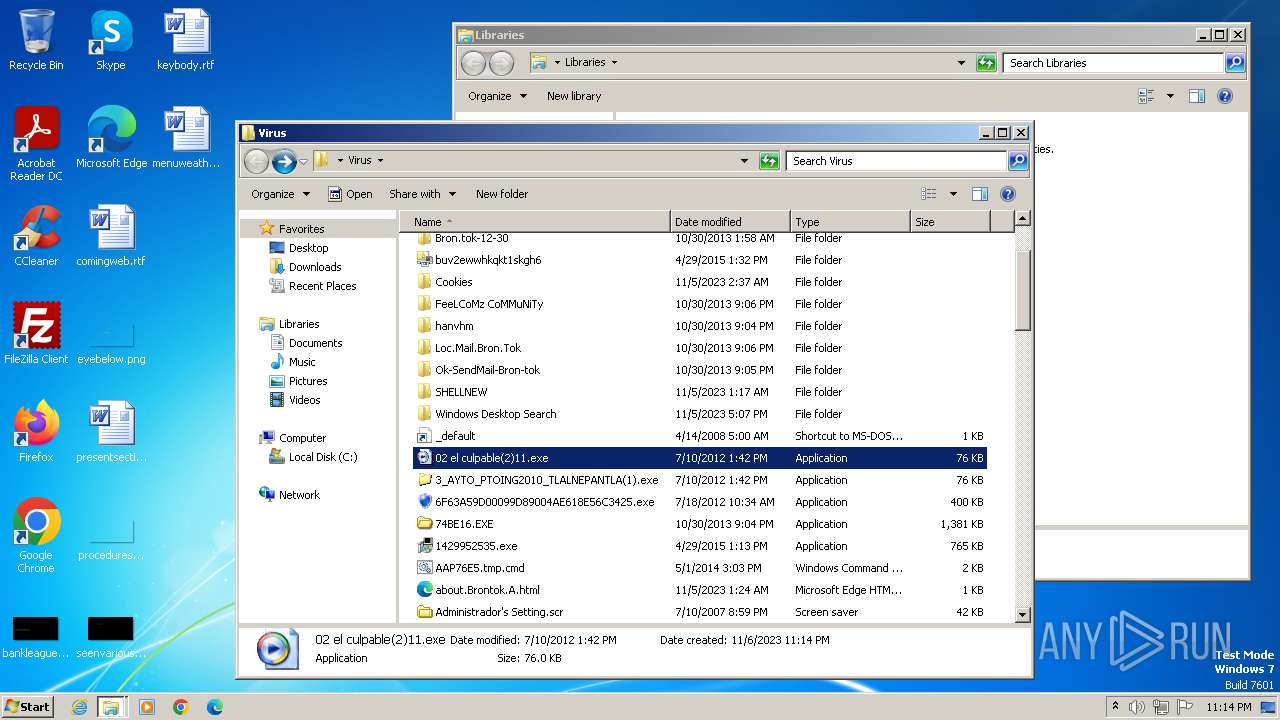
- 02 el culpable(2)11.exe (PID: 2856)
- 3_AYTO_PTOING2010_TLALNEPANTLA(1).exe (PID: 2132)
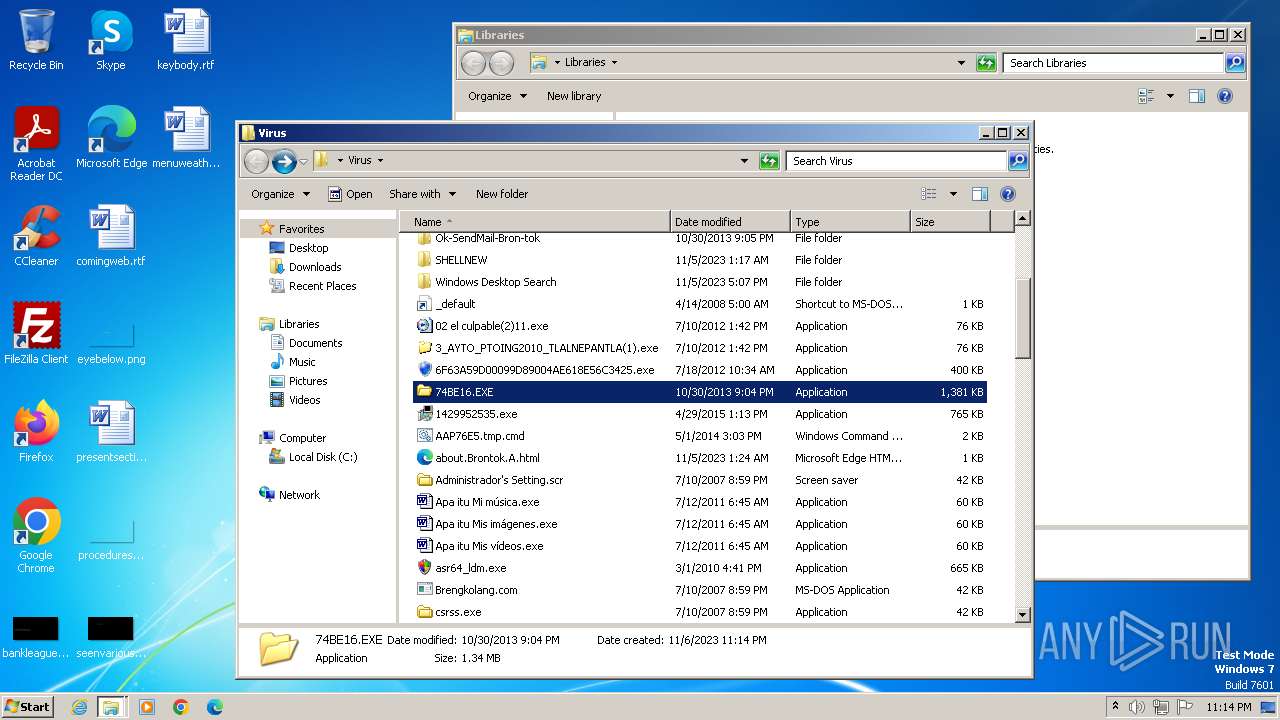
- 74BE16.EXE (PID: 2516)
Changes appearance of the Explorer extensions
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- smss.exe (PID: 3616)
- services.exe (PID: 1924)
- winlogon.exe (PID: 3820)
- lsass.exe (PID: 2260)
- inetinfo.exe (PID: 2428)
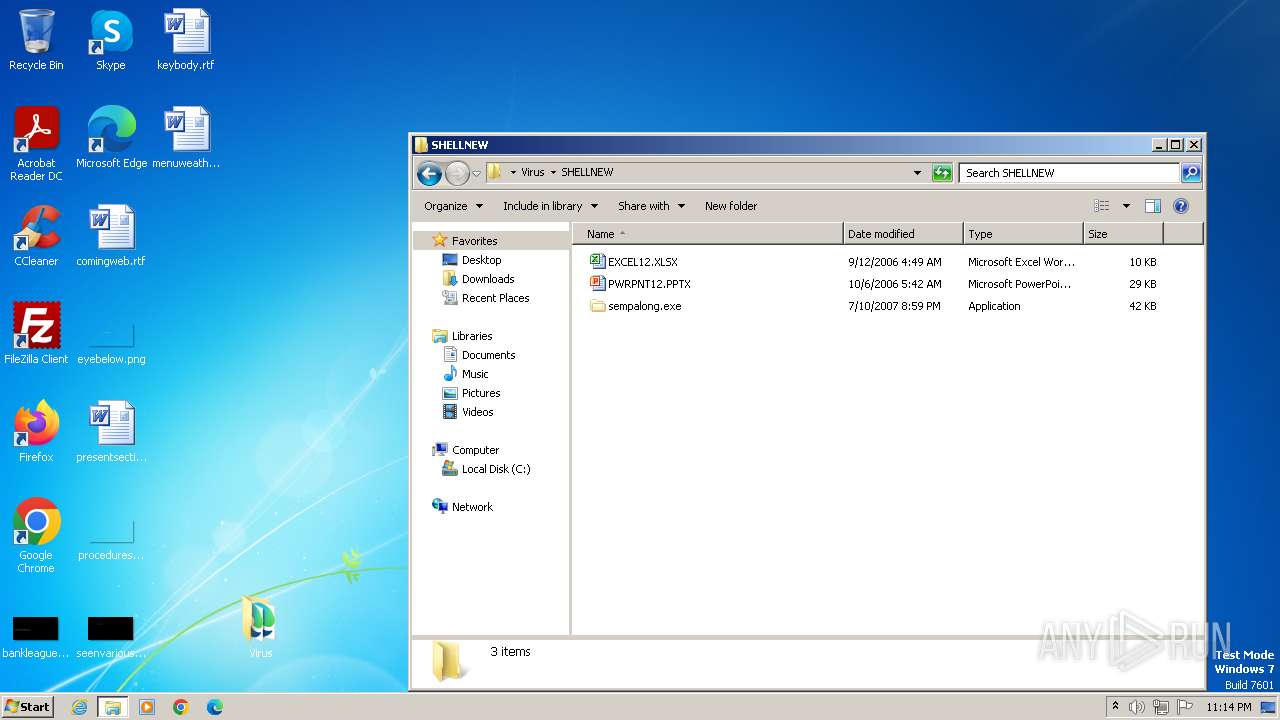
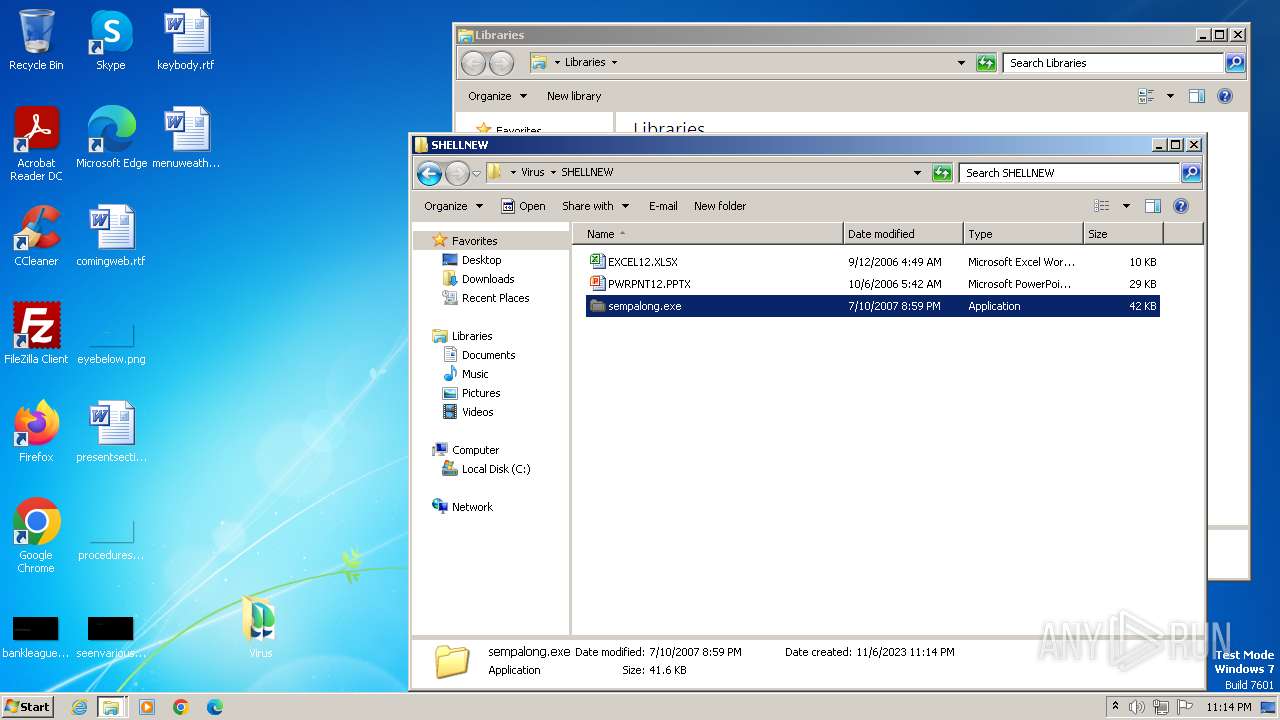
- sempalong.exe (PID: 3780)
- smss.exe (PID: 2120)
- 02 el culpable(2)11.exe (PID: 2856)
- 3_AYTO_PTOING2010_TLALNEPANTLA(1).exe (PID: 2132)
- xoaixo.exe (PID: 2988)
Changes the autorun value in the registry
- smss.exe (PID: 3616)
- services.exe (PID: 1924)
- winlogon.exe (PID: 3820)
- lsass.exe (PID: 2260)
- inetinfo.exe (PID: 2428)
- sempalong.exe (PID: 3780)
- smss.exe (PID: 2120)
- xoaixo.exe (PID: 2988)
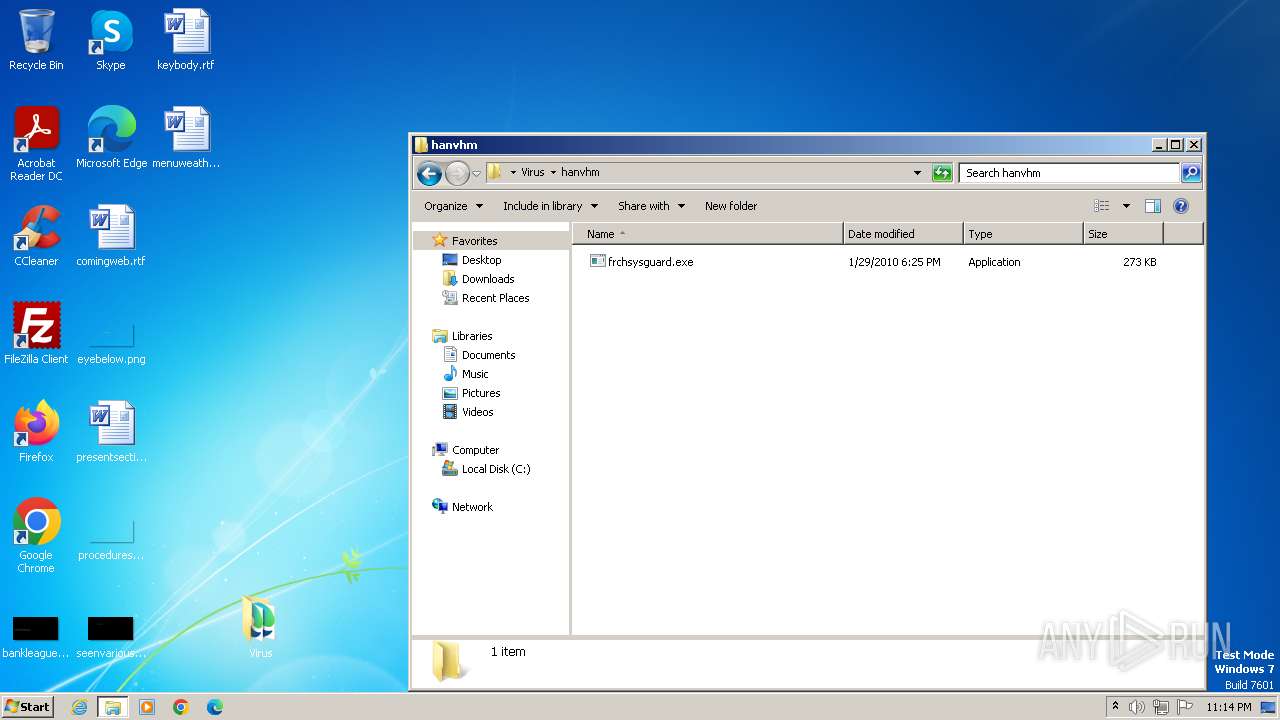
Gets startup folder path (SCRIPT)
- frchsysguard.exe (PID: 1356)
Gets path to any of the special folders (SCRIPT)
- frchsysguard.exe (PID: 1356)
Create files in the Startup directory
- smss.exe (PID: 3616)
Accesses system services(Win32_Service) via WMI (SCRIPT)
- frchsysguard.exe (PID: 1356)
Reads the value of a key from the registry (SCRIPT)
- frchsysguard.exe (PID: 1356)
Registers / Runs the DLL via REGSVR32.EXE
- frchsysguard.exe (PID: 1356)
Connects to the CnC server
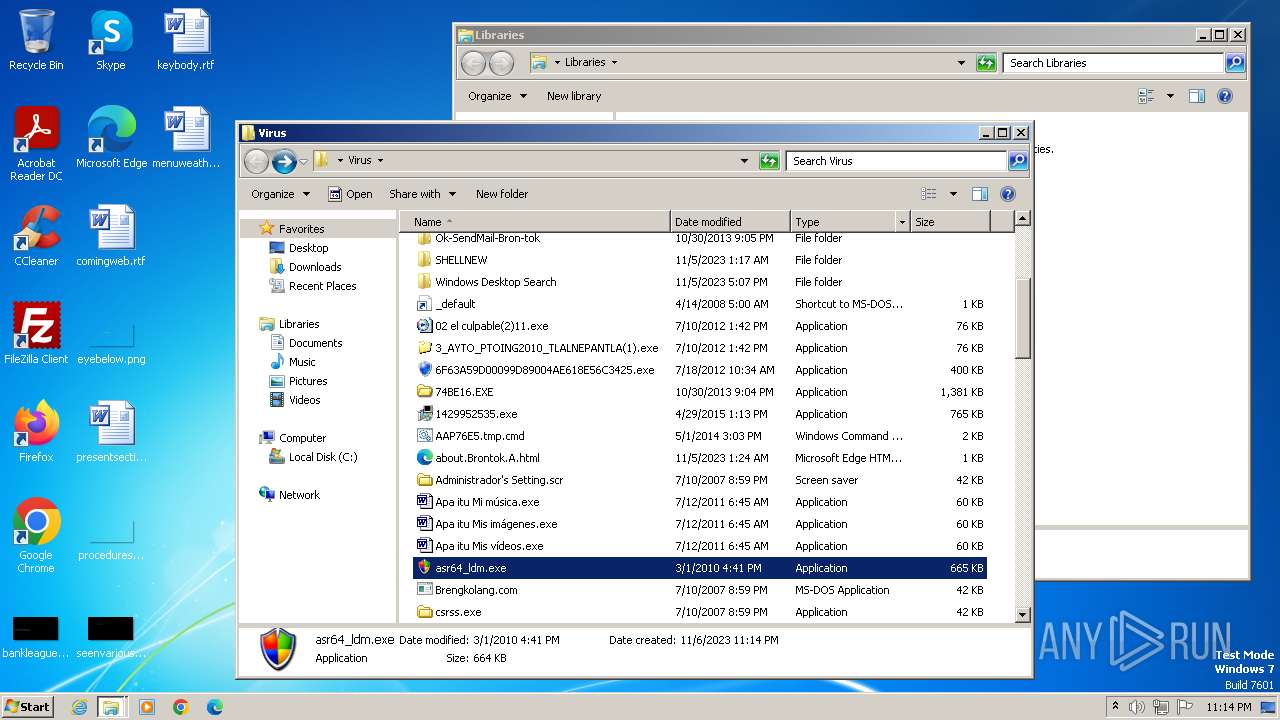
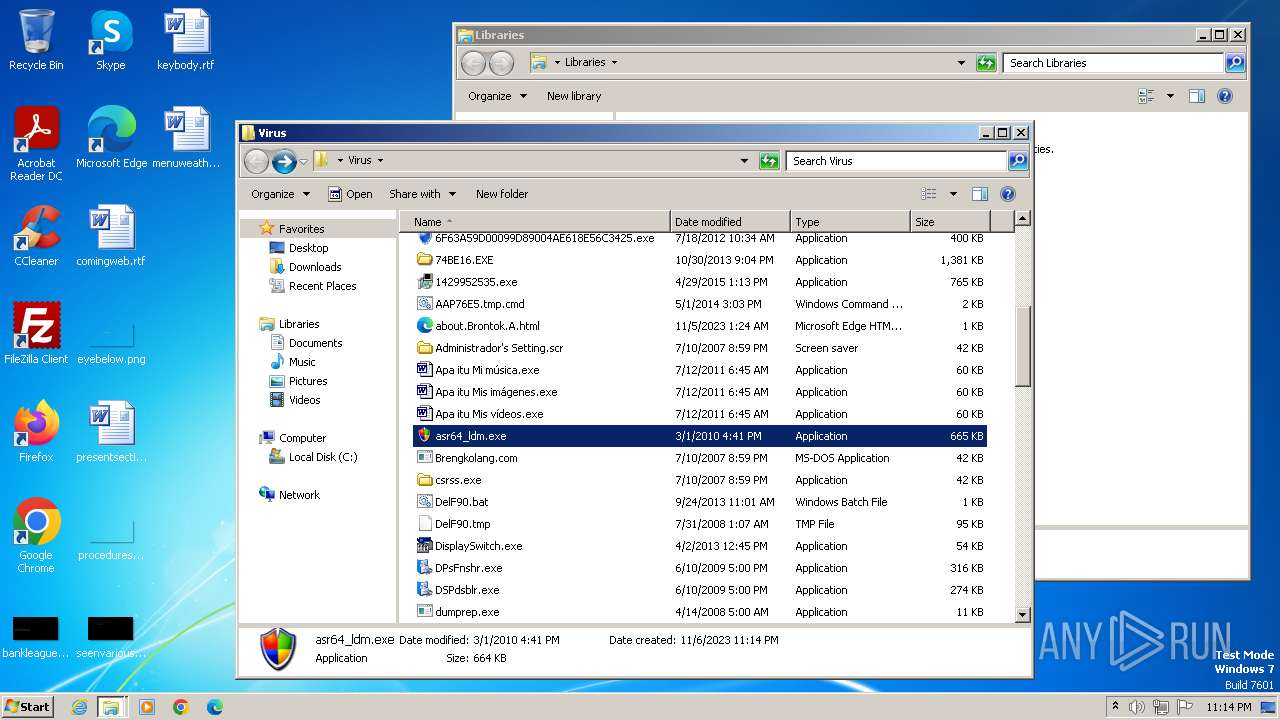
- asr64_ldm.exe (PID: 3676)
BRONTOK has been detected (SURICATA)
- inetinfo.exe (PID: 2428)
SUSPICIOUS
The process creates files with name similar to system file names
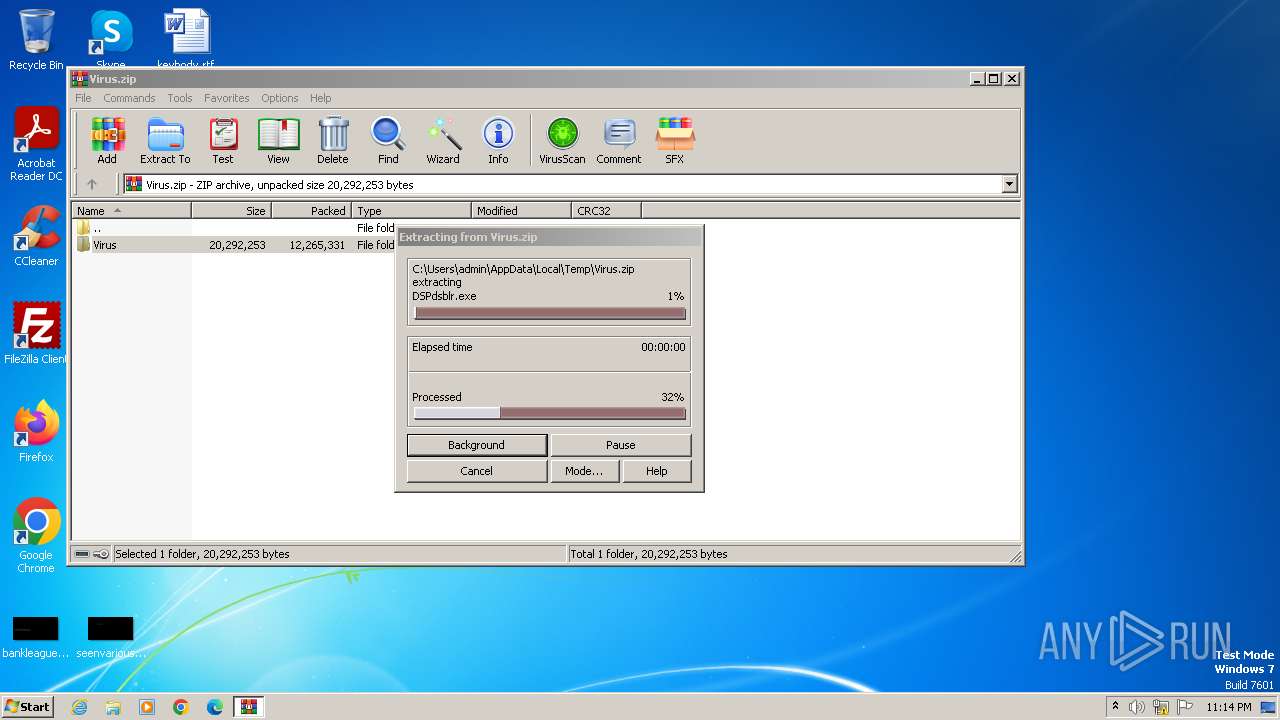
- WinRAR.exe (PID: 3440)
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3440)
Creates executable files that already exist in Windows
- WinRAR.exe (PID: 3440)
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
Connects to the server without a host name
- 6F638C122B17ABE917FE28AE7B07D287.exe (PID: 3632)
Starts itself from another location
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- smss.exe (PID: 3616)
- sempalong.exe (PID: 3780)
Creates FileSystem object to access computer's file system (SCRIPT)
- frchsysguard.exe (PID: 1356)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- frchsysguard.exe (PID: 1356)
Creates a Folder object (SCRIPT)
- frchsysguard.exe (PID: 1356)
Runs shell command (SCRIPT)
- frchsysguard.exe (PID: 1356)
Executes WMI query (SCRIPT)
- frchsysguard.exe (PID: 1356)
Reads the Internet Settings
- frchsysguard.exe (PID: 1356)
- 74BE16.EXE (PID: 2516)
- 02 el culpable(2)11.exe (PID: 2856)
- 3_AYTO_PTOING2010_TLALNEPANTLA(1).exe (PID: 2132)
- WMIC.exe (PID: 3240)
- WMIC.exe (PID: 3124)
- WMIC.exe (PID: 3584)
- WMIC.exe (PID: 3840)
- inetinfo.exe (PID: 2428)
- WMIC.exe (PID: 2824)
- asr64_ldm.exe (PID: 3676)
Uses WMIC.EXE to obtain BIOS management information
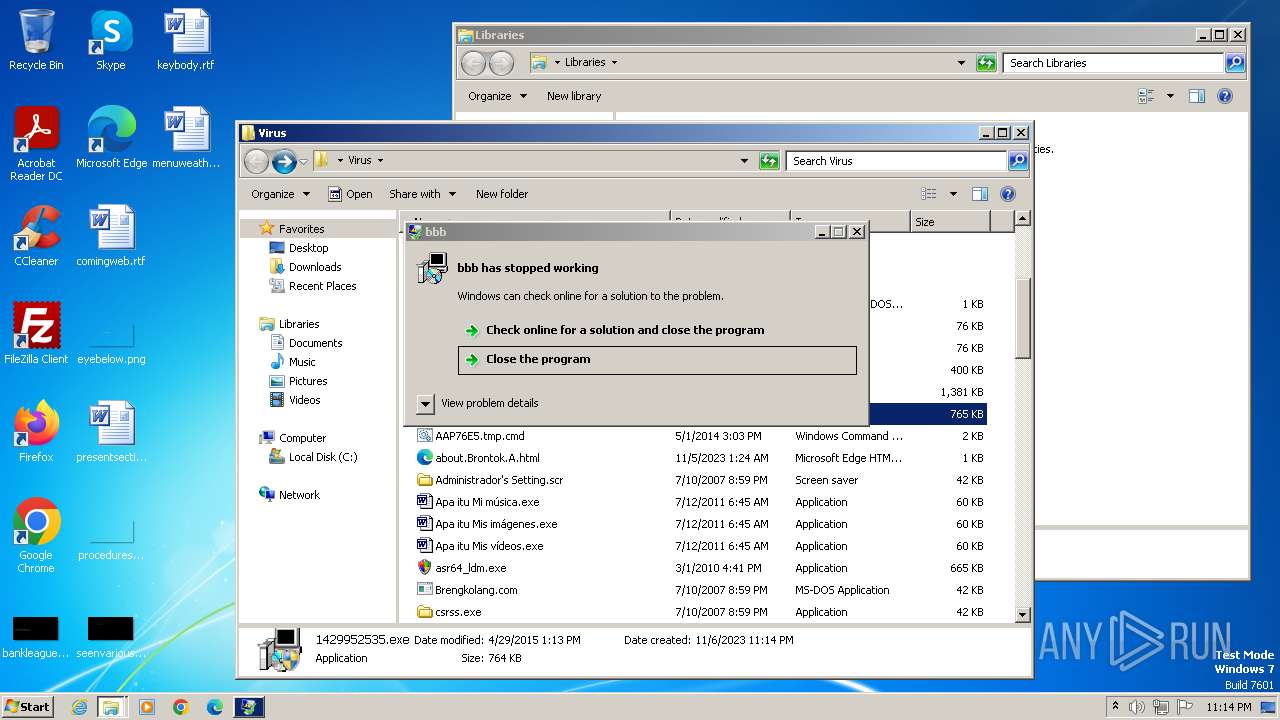
- 1429952535.exe (PID: 3200)
Connects to unusual port
- 02 el culpable(2)11.exe (PID: 2856)
- 3_AYTO_PTOING2010_TLALNEPANTLA(1).exe (PID: 2132)
Reads security settings of Internet Explorer
- asr64_ldm.exe (PID: 3676)
Checks Windows Trust Settings
- asr64_ldm.exe (PID: 3676)
Reads settings of System Certificates
- asr64_ldm.exe (PID: 3676)
INFO
Checks supported languages
- 6F638C122B17ABE917FE28AE7B07D287.exe (PID: 3632)
- wmpnscfg.exe (PID: 3828)
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- smss.exe (PID: 3616)
- winlogon.exe (PID: 3820)
- frchsysguard.exe (PID: 1356)
- services.exe (PID: 1924)
- lsass.exe (PID: 2260)
- inetinfo.exe (PID: 2428)
- sempalong.exe (PID: 3780)
- smss.exe (PID: 2120)
- 3_AYTO_PTOING2010_TLALNEPANTLA(1).exe (PID: 2132)
- 02 el culpable(2)11.exe (PID: 2856)
- 74BE16.EXE (PID: 2516)
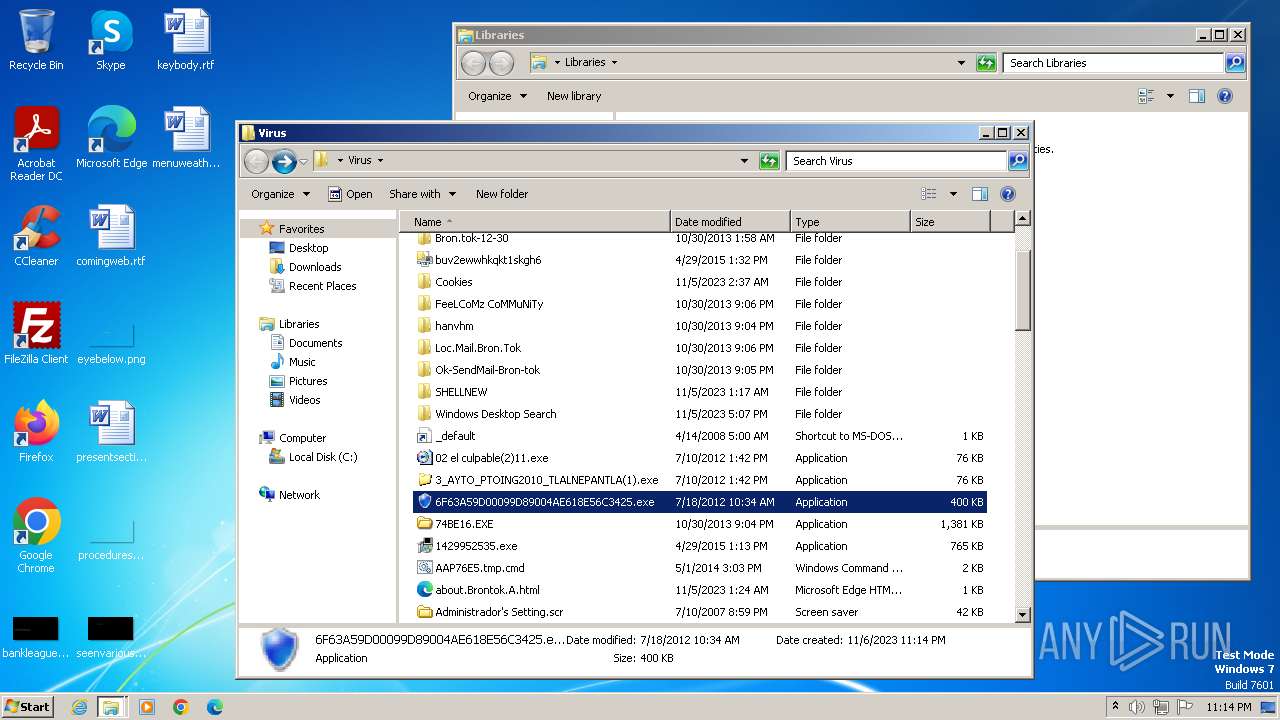
- 6F63A59D00099D89004AE618E56C3425.exe (PID: 2940)
- xoaixo.exe (PID: 2988)
- xuazue.exe (PID: 2908)
- 1429952535.exe (PID: 3200)
- asr64_ldm.exe (PID: 3676)
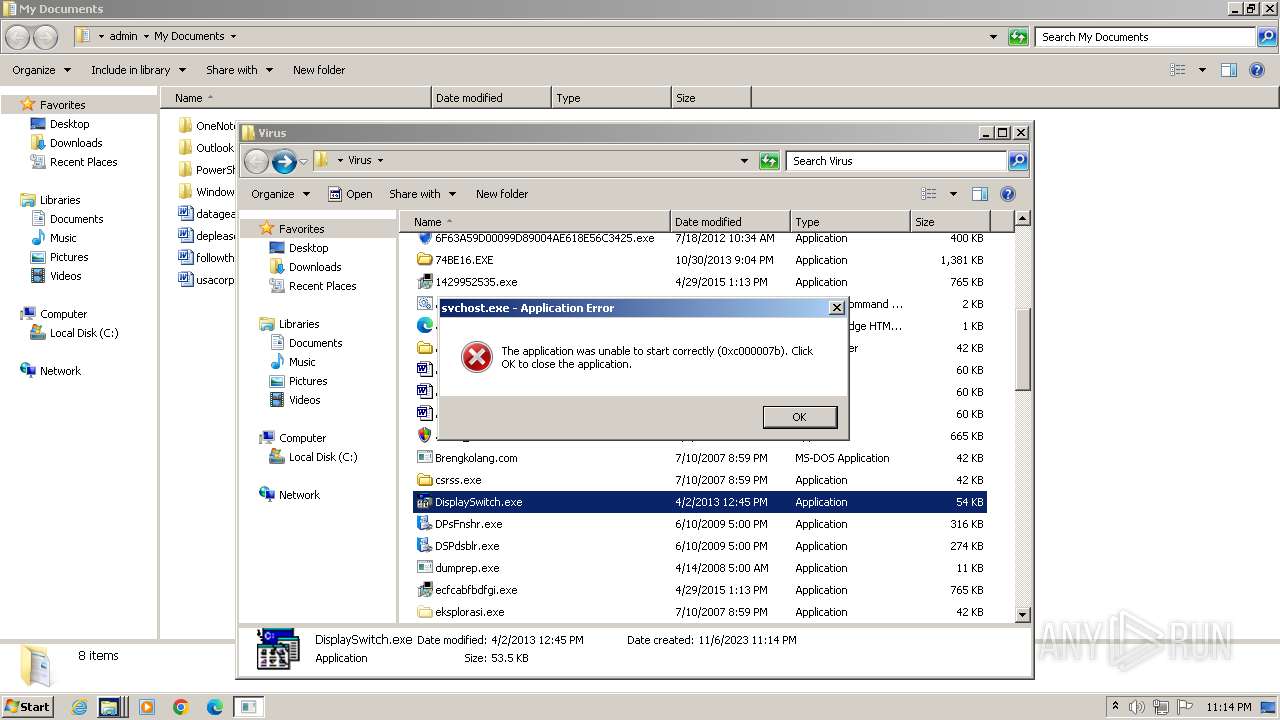
- DisplaySwitch.exe (PID: 1856)
Reads the computer name
- 6F638C122B17ABE917FE28AE7B07D287.exe (PID: 3632)
- wmpnscfg.exe (PID: 3828)
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- winlogon.exe (PID: 3820)
- smss.exe (PID: 3616)
- services.exe (PID: 1924)
- frchsysguard.exe (PID: 1356)
- lsass.exe (PID: 2260)
- inetinfo.exe (PID: 2428)
- sempalong.exe (PID: 3780)
- 02 el culpable(2)11.exe (PID: 2856)
- smss.exe (PID: 2120)
- 6F63A59D00099D89004AE618E56C3425.exe (PID: 2940)
- 74BE16.EXE (PID: 2516)
- xoaixo.exe (PID: 2988)
- 3_AYTO_PTOING2010_TLALNEPANTLA(1).exe (PID: 2132)
- xuazue.exe (PID: 2908)
- 1429952535.exe (PID: 3200)
- asr64_ldm.exe (PID: 3676)
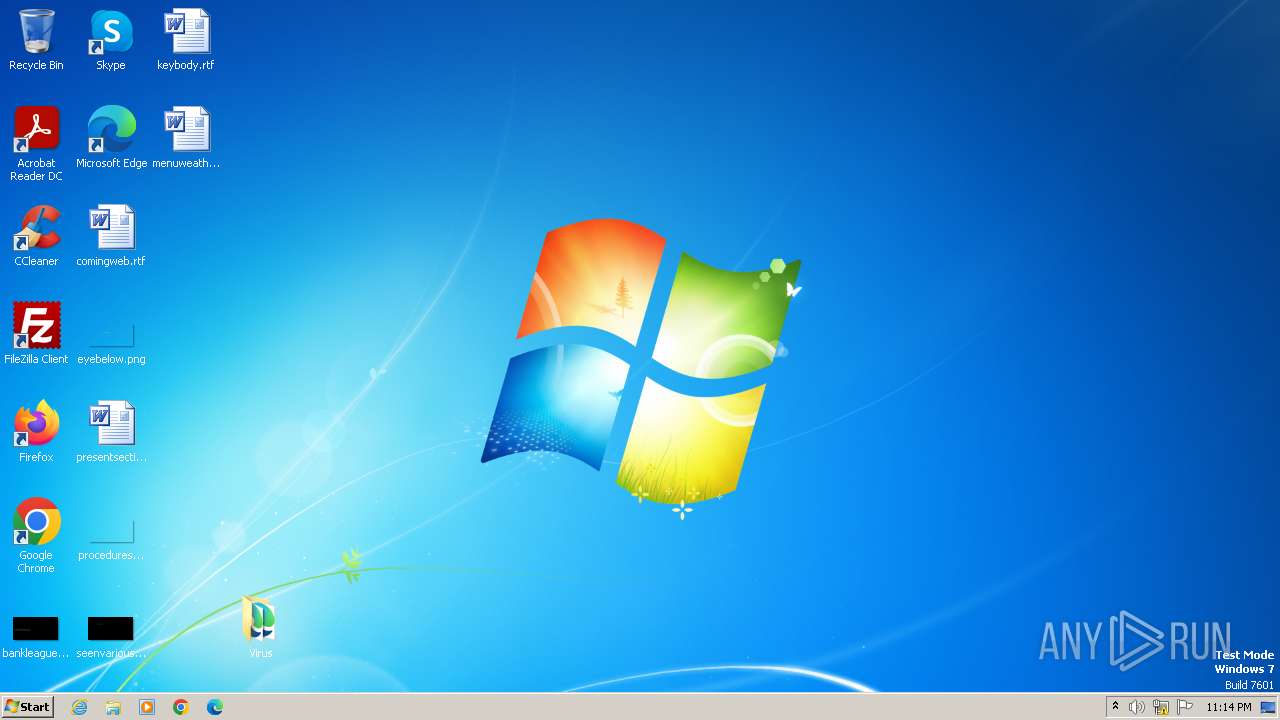
Manual execution by a user
- 6F638C122B17ABE917FE28AE7B07D287.exe (PID: 3632)
- wmpnscfg.exe (PID: 3828)
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- frchsysguard.exe (PID: 1356)
- sempalong.exe (PID: 3780)
- 02 el culpable(2)11.exe (PID: 2856)
- 3_AYTO_PTOING2010_TLALNEPANTLA(1).exe (PID: 2132)
- 6F63A59D00099D89004AE618E56C3425.exe (PID: 2940)
- 74BE16.EXE (PID: 2516)
- 1429952535.exe (PID: 3200)
- 1429952535.exe (PID: 2452)
- asr64_ldm.exe (PID: 3676)
- cmd.exe (PID: 1528)
- DisplaySwitch.exe (PID: 1856)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3828)
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- smss.exe (PID: 3616)
- winlogon.exe (PID: 3820)
- services.exe (PID: 1924)
- frchsysguard.exe (PID: 1356)
- lsass.exe (PID: 2260)
- inetinfo.exe (PID: 2428)
- sempalong.exe (PID: 3780)
- smss.exe (PID: 2120)
- 74BE16.EXE (PID: 2516)
- 1429952535.exe (PID: 3200)
- asr64_ldm.exe (PID: 3676)
Create files in a temporary directory
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- smss.exe (PID: 3616)
- winlogon.exe (PID: 3820)
- services.exe (PID: 1924)
- lsass.exe (PID: 2260)
- inetinfo.exe (PID: 2428)
- sempalong.exe (PID: 3780)
- smss.exe (PID: 2120)
- 74BE16.EXE (PID: 2516)
- WMIC.exe (PID: 3240)
- WMIC.exe (PID: 2824)
- WMIC.exe (PID: 3124)
- WMIC.exe (PID: 3584)
- WMIC.exe (PID: 3840)
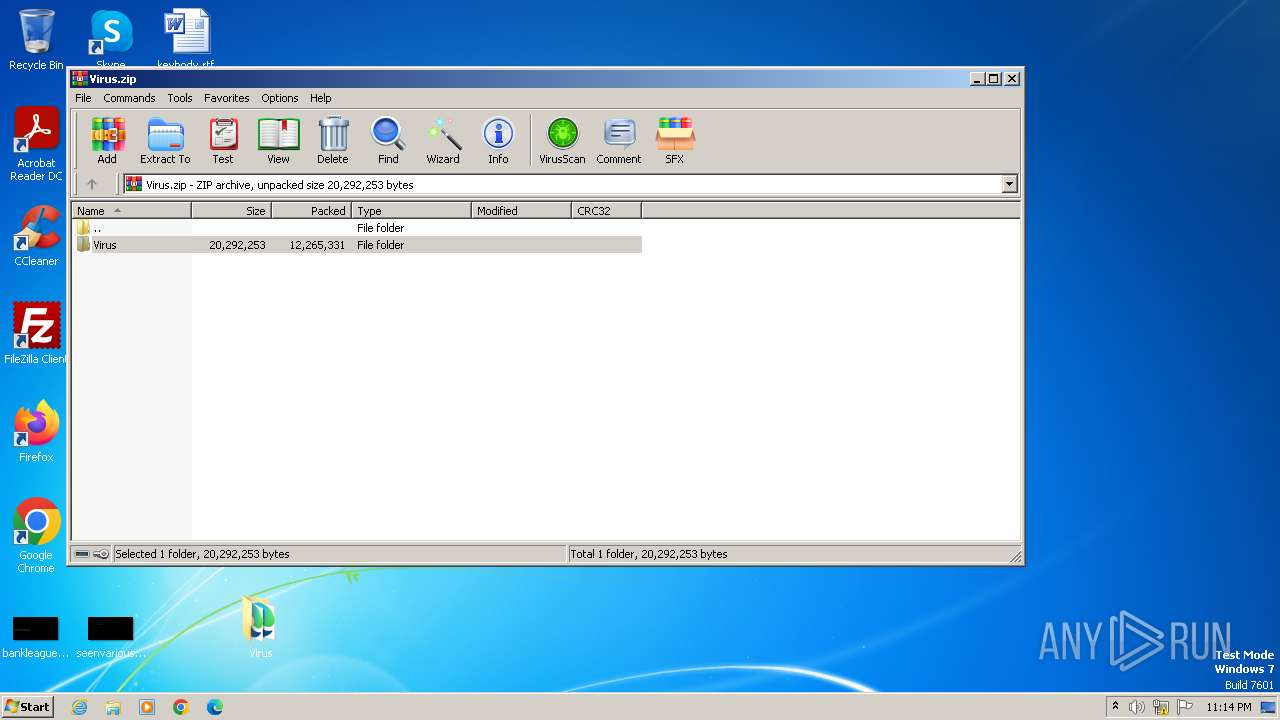
Creates files or folders in the user directory
- FeeLCoMz CoMMuNiTy.exe (PID: 4052)
- smss.exe (PID: 3616)
- asr64_ldm.exe (PID: 3676)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3440)
Reads Environment values
- frchsysguard.exe (PID: 1356)
Checks proxy server information
- 74BE16.EXE (PID: 2516)
- inetinfo.exe (PID: 2428)
- asr64_ldm.exe (PID: 3676)
Reads the Internet Settings
- explorer.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2008:04:14 05:00:00 |
| ZipCRC: | 0x0d7438c2 |
| ZipCompressedSize: | 196 |
| ZipUncompressedSize: | 707 |
| ZipFileName: | Virus/_default.pif |
Total processes
91
Monitored processes
36
Malicious processes
17
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | at /delete /y | C:\Windows\System32\at.exe | — | smss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Schedule service command line interface Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 988 | explorer.exe | C:\Windows\explorer.exe | — | sempalong.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | at 17:08 /every:M,T,W,Th,F,S,Su "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Brengkolang.com" | C:\Windows\System32\at.exe | — | smss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Schedule service command line interface Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | "C:\Users\admin\Desktop\Virus\hanvhm\frchsysguard.exe" | C:\Users\admin\Desktop\Virus\hanvhm\frchsysguard.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
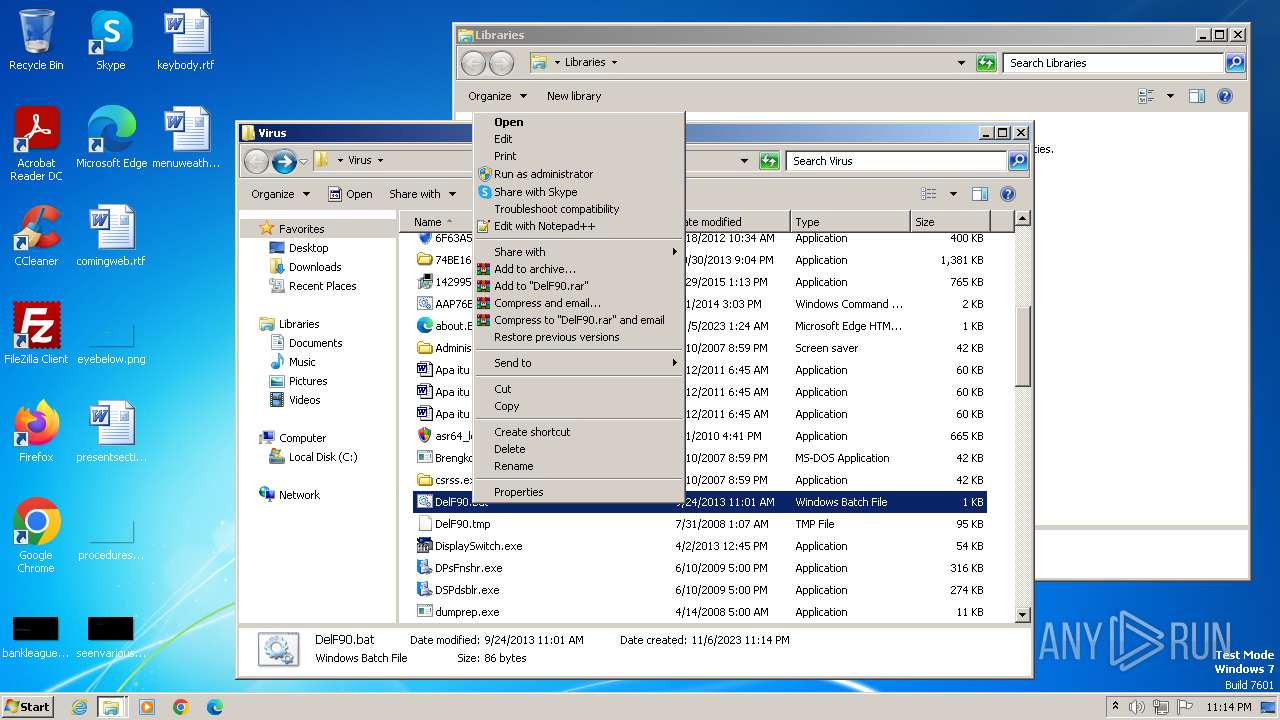
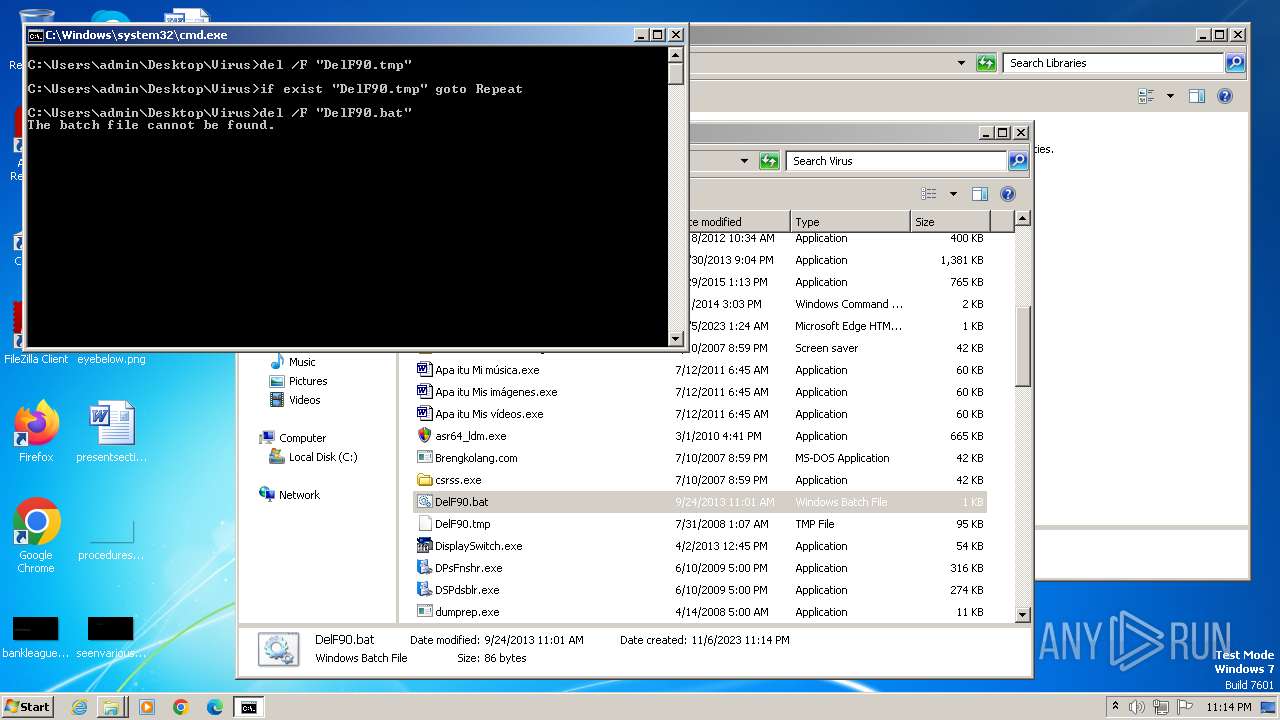
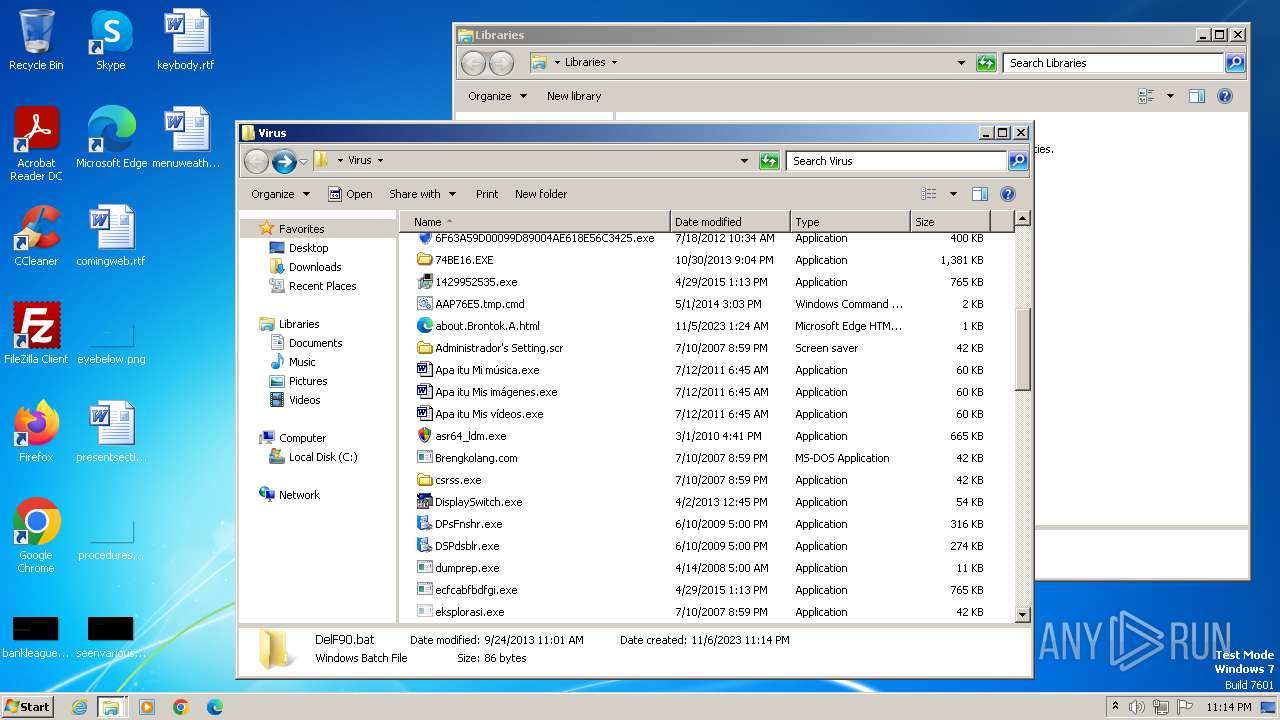
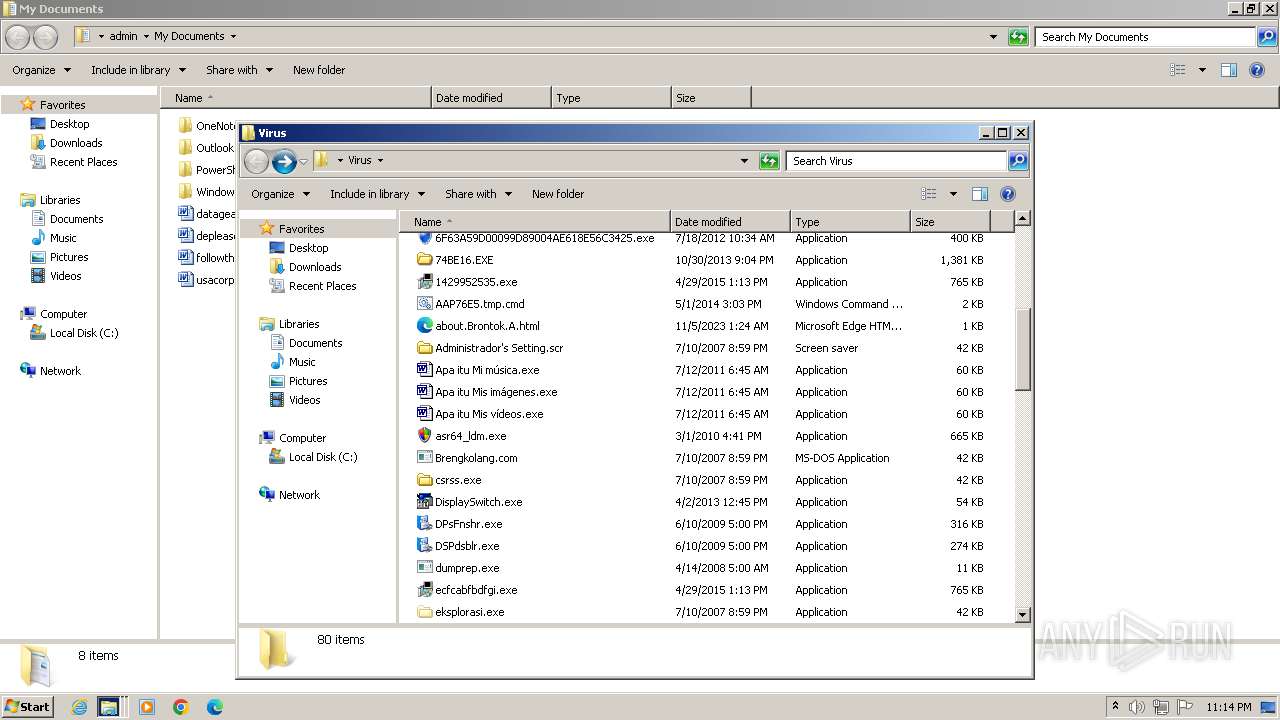
| 1528 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Virus\DelF90.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1840 | svchost.exe | C:\Users\admin\Desktop\Virus\svchost.exe | — | DisplaySwitch.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Microsoft Word Document Exit code: 0 Version: 1.01.0001 Modules
| |||||||||||||||
| 1856 | "C:\Users\admin\Desktop\Virus\DisplaySwitch.exe" | C:\Users\admin\Desktop\Virus\DisplaySwitch.exe | — | explorer.exe | |||||||||||
User: admin Company: Корпорация Майкрософт Integrity Level: MEDIUM Description: Конвертор групп диспетчера программ Windows Exit code: 0 Version: 5.1.2600.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
| 1924 | C:\Users\admin\AppData\Local\services.exe | C:\Users\admin\AppData\Local\services.exe | smss.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2120 | C:\Users\admin\AppData\Local\smss.exe | C:\Users\admin\AppData\Local\smss.exe | sempalong.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\Desktop\Virus\3_AYTO_PTOING2010_TLALNEPANTLA(1).exe" | C:\Users\admin\Desktop\Virus\3_AYTO_PTOING2010_TLALNEPANTLA(1).exe | explorer.exe | ||||||||||||
User: admin Company: Thamyras everybody Integrity Level: MEDIUM Description: Thamyras everybody Exit code: 0 Version: 2.48 Modules
| |||||||||||||||
Total events
13 981
Read events
13 752
Write events
226
Delete events
3
Modification events
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3440) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
110
Suspicious files
14
Text files
57
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\02 el culpable(2)11.exe | executable | |
MD5:AB2C5D3C4BD6615301A767B9FE9046DF | SHA256:0FD6A7B40D3D324BF84827EE1BE8F336D339A9778AAE4A900B565B34AD31719C | |||
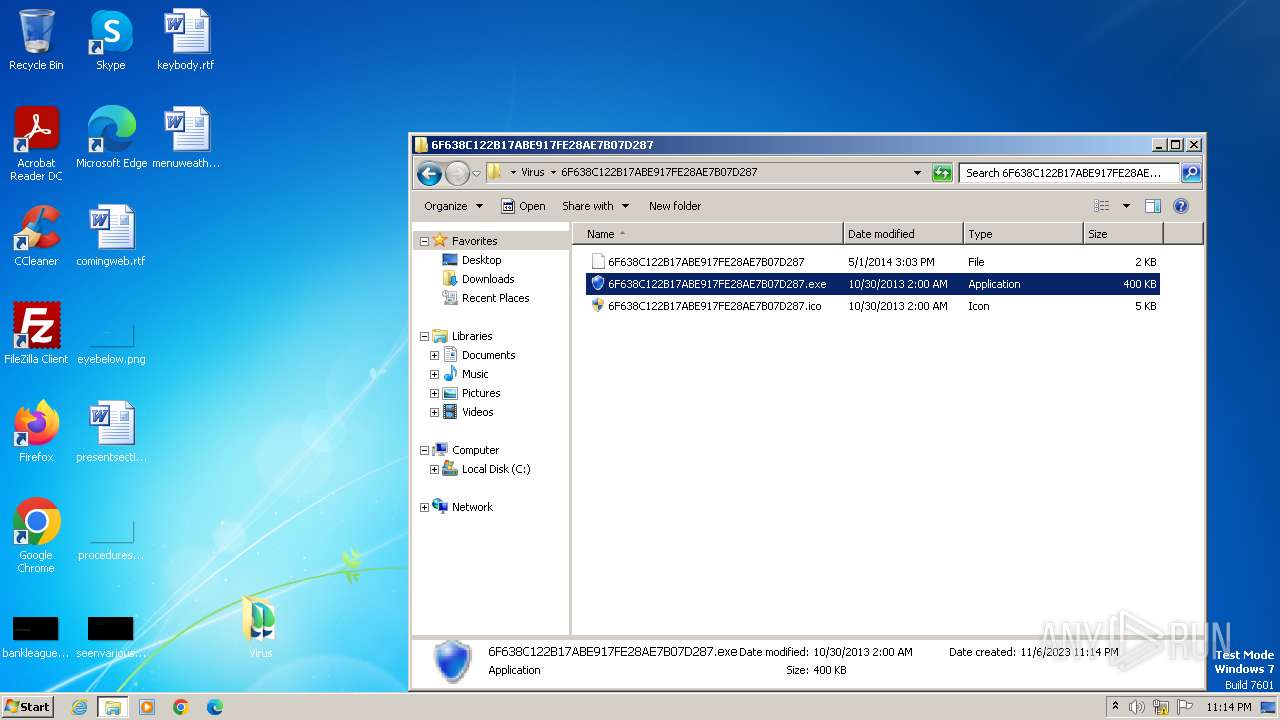
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\6F638C122B17ABE917FE28AE7B07D287\6F638C122B17ABE917FE28AE7B07D287 | binary | |
MD5:8819E6E359C933C6D2C9BD2A5ECFCEE9 | SHA256:B5032B298FE9052B9738F06757729EE17D9DE3F9C7CDBD431C2BB1D6D96F56DB | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\1429952535.exe | executable | |
MD5:17D34AB78A0C4146046C72FA59F9245F | SHA256:AEA5837BFFCB59FD382D14F4C4A6E96CF8099A2650FDCF709E7CB9735A0275DC | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\6F638C122B17ABE917FE28AE7B07D287\6F638C122B17ABE917FE28AE7B07D287.exe | executable | |
MD5:D8103D27E795B9753DF3239AB804B03E | SHA256:4315838DBAD913ADD8E05A1044CFB85D72E472FD65664F198EB841B0F831AC25 | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\6F63A59D00099D89004AE618E56C3425.exe | executable | |
MD5:D8103D27E795B9753DF3239AB804B03E | SHA256:4315838DBAD913ADD8E05A1044CFB85D72E472FD65664F198EB841B0F831AC25 | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\_default.pif | binary | |
MD5:B317B33694BAC49D492DD3F23E374899 | SHA256:75CAF5ACA5B155AFBD4CE7EFFE825FE1BF4767A0AFEE64A8D726C5E9694FA33A | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\Cookies\administrador@abmr[2].txt | text | |
MD5:9C439932726F35A12E164847763F5E7E | SHA256:97F914E6B8D0EAA1FF6F4A0536F5F1AB5C8544BD3485B3C05C83F569CC9C26D4 | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\buv2ewwhkqkt1skgh6.{2227A280-3AEA-1069-A2DE-08002B30309D}\bbnlmyqqs.exe | executable | |
MD5:F752133B5028B28DA8725A7E684EB7D1 | SHA256:1FDFA134673813CFA0EB87F8442322D9391D7C28BA7F162124A74AD7BC5537F8 | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\6F638C122B17ABE917FE28AE7B07D287\6F638C122B17ABE917FE28AE7B07D287.ico | image | |
MD5:EF6B46F858745A383AEAD66FBC674763 | SHA256:DE6E0C84C97C14E51667447AB59B9A83DC7517DF0D48D8F72D58729107BF8BC7 | |||
| 3440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3440.43087\Virus\Apa itu Mis vídeos.exe | executable | |
MD5:6C08BD41F70D51662DF04EB4ECD2F9EE | SHA256:D24596A87B810ED934078EB7F474973FDE52DD4866C9114BE2E53E720C118750 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
13
DNS requests
7
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3676 | asr64_ldm.exe | GET | 302 | 52.86.6.113:80 | http://Beinahe.com/readdatagateway.php?type=stats&affid=139&subid=1&version=3.0&adwareok | unknown | — | — | unknown |
2428 | inetinfo.exe | GET | — | 34.225.127.72:80 | http://www.geocities.com/sbllro2/IN12VLMLSDSDW.txt | unknown | — | — | unknown |
3632 | 6F638C122B17ABE917FE28AE7B07D287.exe | GET | 404 | 112.121.178.189:80 | http://112.121.178.189/api/urls/?ts=e711e20e&affid=46200 | unknown | html | 146 b | unknown |
3676 | asr64_ldm.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4768b7558eb38fcd | unknown | compressed | 4.66 Kb | unknown |
3676 | asr64_ldm.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3632 | 6F638C122B17ABE917FE28AE7B07D287.exe | 112.121.178.189:80 | — | Netsec Limited | HK | unknown |
2516 | 74BE16.EXE | 193.104.27.98:80 | — | MTS PJSC | RU | unknown |
2856 | 02 el culpable(2)11.exe | 77.247.179.86:8003 | ns1.timecheckings.com | NForce Entertainment B.V. | NL | unknown |
2132 | 3_AYTO_PTOING2010_TLALNEPANTLA(1).exe | 77.247.179.86:8003 | ns1.timecheckings.com | NForce Entertainment B.V. | NL | unknown |
2428 | inetinfo.exe | 34.225.127.72:80 | www.geocities.com | AMAZON-AES | US | unknown |
3676 | asr64_ldm.exe | 52.86.6.113:80 | beinahe.com | AMAZON-AES | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
newsoftspot.com |
| unknown |
ns1.timecheckings.com |
| malicious |
www.geocities.com |
| malicious |
beinahe.com |
| unknown |
www.hugedomains.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3632 | 6F638C122B17ABE917FE28AE7B07D287.exe | Unknown Traffic | ET HUNTING Suspicious Empty User-Agent |
3676 | asr64_ldm.exe | A Network Trojan was detected | ET MALWARE Fake AV GET |
3676 | asr64_ldm.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP RogueAntiSpyware.AntiVirusPro Checkin |
3676 | asr64_ldm.exe | A Network Trojan was detected | ET USER_AGENTS Long Fake wget 3.0 User-Agent Detected |
3676 | asr64_ldm.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Fake Wget User-Agent (wget 3.0) - Likely Hostile |
2428 | inetinfo.exe | A Network Trojan was detected | ET MALWARE Brontok User-Agent Detected (Brontok.A3 Browser) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
asr64_ldm.exe | C:\Users\admin\AppData\Roaming\Dr. Guard\drguard.exe |
asr64_ldm.exe | C:\Program Files\Dr. Guard\drguard.exe |