| URL: | https://mail.notifyvisitors.com/tracker/email_tracker/handler/click/59153/14566?cd=aktPMUFtRXRLeXhOT3pUYzZJeEw1Y2ptMzBDSDJkYm1IWEdmNk5GVEFvVlRyN1FMVjdQUFEyWmpkUURtQndBMnJ2Nk1iOWtYSEJQY0UzY1NodklLd05WQ2RtaG9SSHJrL0FGZk40Y0FNdlFTeThVR2ZGRlJjOEt2QW54WS8wTFVnSmdRNC9BNHVDUDJvMFcwYjZLOHNjWXlaUmRnaTdYa2ZJRXl1c1loUnlTd25WWWJuazhwQVFtYnFKQ3podmRrTUZYNVJ6L0pBd0JYdTk3bWRmNUR2N1Nyc1MyT21tQTh1TklvMGVPU0s1YjY2akZ3VmRsaHVYSEF4Q0dWemFOV0lVR3FFWmNuZnF0MnpsTW9lZStjR0RwZm5YTlFwQjd3cVk5TTFRejdGRlR2ZkNKRmJiV2pqWXJCOWR4c1czanhZd0F3RmlIMWMwRnlqZ3VmTHFLT1loU0pQc2ZEM2lWZFk2eGhDVytJUkVlbC81MExGMHZhM200aWk4NzdJRFk4N3FlcHozemRxUmRKQVFwMkR0TDQ3UVlxVGI1UE9teFI3TUxEMk1jVk5zTXNPYlFmYllPL0I1dVkwZEdMUU5kVVpUV01PTzV1cnRTUExFdTNtSkpzMnlaWjVmRUpHRWh4b1RjYWlZQmw0RDQwQ1BSVFZmaEtOZ3VXU0lxL2c0REpMTlYwcjIvNFJLcVh3ZG9BbWNlaG82UXN6SmNZajRMV0pJVGI5eWF0bXRiQXJoWUtlRzdpRTNZMW5kbHlLdmkrR1ZuQndlaEY2K1B3NXZHMlJiYXRIRkpmcVRqRkMybnFOc3hXTWFWVzlUWVJ3M1VncjJOcnZteHJwWUNxK0VoRXdzb24rMkZITzRUL3R1bGVGVnFHMS9pYm93SUxpUkxqVGt4UER2eUZSYUk9 |
| Full analysis: | https://app.any.run/tasks/cbefebff-48dc-4432-b609-b47473a081a6 |
| Verdict: | Malicious activity |
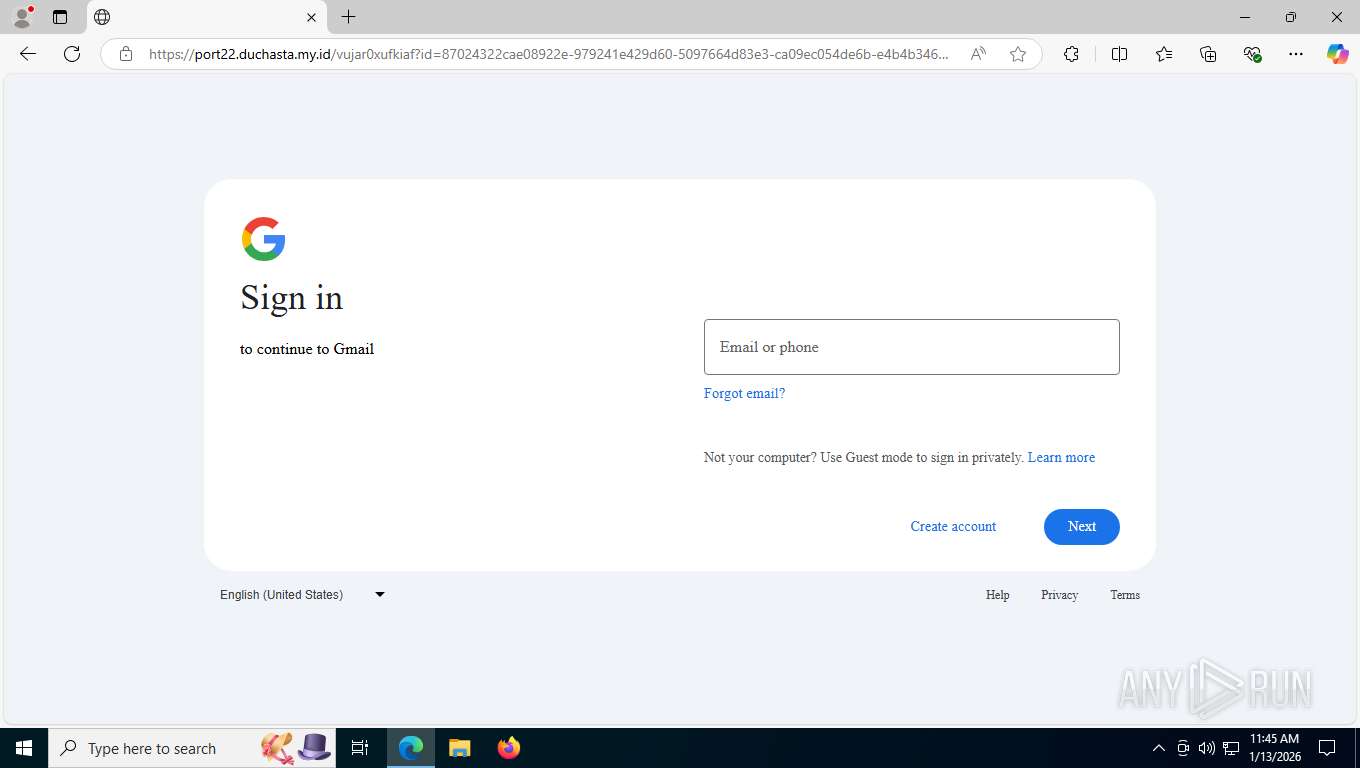
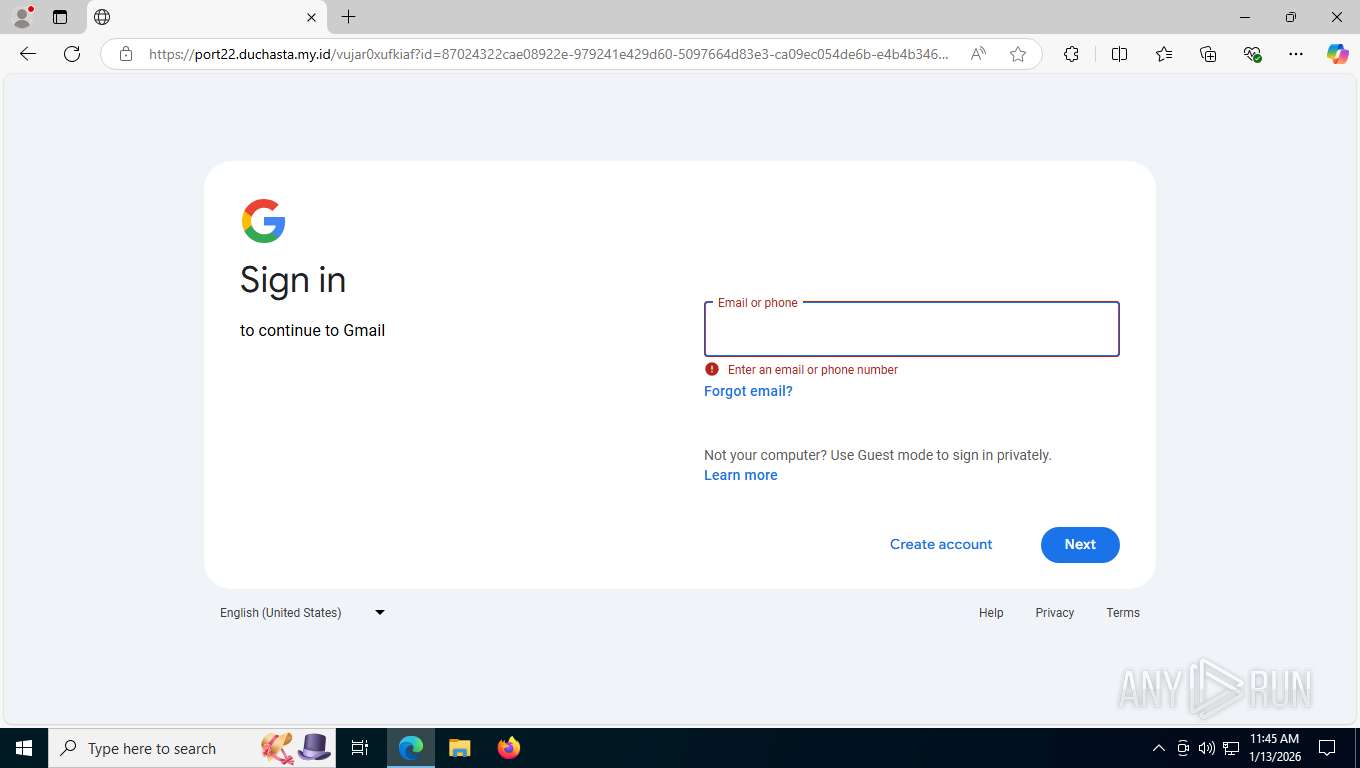
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | January 13, 2026, 16:44:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 09E1BC92AECE9B7B815E8F1A6CD30300 |
| SHA1: | 82F0454E481C27D033B86F5D85784210A6DABA83 |
| SHA256: | 1497E5D06D91748BE1EC6D1E03663411C0DFDD2AD8BD2FEEBBD56E9C00866AA5 |
| SSDEEP: | 24:2wCHaPDD1lZaTQgkffruWre83enT4BaA7vDFDuliaF:zPDJlZ20aWrju4BaKbFyPF |
MALICIOUS
PHISHING has been detected (ML)
- msedge.exe (PID: 7520)
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7852)
SUSPICIOUS
No suspicious indicators.INFO
Reads the computer name
- identity_helper.exe (PID: 7024)
Checks supported languages
- identity_helper.exe (PID: 7024)
Application launched itself
- msedge.exe (PID: 7520)
Reads Environment values
- identity_helper.exe (PID: 7024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
167
Monitored processes
22
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1976 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4004,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=6008 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5784,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=5736 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2364 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5500,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=3992 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4296,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=4312 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2460 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5576,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=5632 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4288,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=4380 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6592,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=6180 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4828 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6636 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=136,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=6140 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 7024 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4004,i,10924449397798032301,12293265525510103469,262144 --variations-seed-version --mojo-platform-channel-handle=6008 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
592
Read events
592
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
46
Text files
95
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfdcda.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfdcda.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfdce9.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfdce9.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfdcda.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfdce9.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
92
TCP/UDP connections
65
DNS requests
65
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7852 | msedge.exe | GET | 302 | 13.226.244.14:443 | https://mail.notifyvisitors.com/tracker/email_tracker/handler/click/59153/14566?cd=aktPMUFtRXRLeXhOT3pUYzZJeEw1Y2ptMzBDSDJkYm1IWEdmNk5GVEFvVlRyN1FMVjdQUFEyWmpkUURtQndBMnJ2Nk1iOWtYSEJQY0UzY1NodklLd05WQ2RtaG9SSHJrL0FGZk40Y0FNdlFTeThVR2ZGRlJjOEt2QW54WS8wTFVnSmdRNC9BNHVDUDJvMFcwYjZLOHNjWXlaUmRnaTdYa2ZJRXl1c1loUnlTd25WWWJuazhwQVFtYnFKQ3podmRrTUZYNVJ6L0pBd0JYdTk3bWRmNUR2N1Nyc1MyT21tQTh1TklvMGVPU0s1YjY2akZ3VmRsaHVYSEF4Q0dWemFOV0lVR3FFWmNuZnF0MnpsTW9lZStjR0RwZm5YTlFwQjd3cVk5TTFRejdGRlR2ZkNKRmJiV2pqWXJCOWR4c1czanhZd0F3RmlIMWMwRnlqZ3VmTHFLT1loU0pQc2ZEM2lWZFk2eGhDVytJUkVlbC81MExGMHZhM200aWk4NzdJRFk4N3FlcHozemRxUmRKQVFwMkR0TDQ3UVlxVGI1UE9teFI3TUxEMk1jVk5zTXNPYlFmYllPL0I1dVkwZEdMUU5kVVpUV01PTzV1cnRTUExFdTNtSkpzMnlaWjVmRUpHRWh4b1RjYWlZQmw0RDQwQ1BSVFZmaEtOZ3VXU0lxL2c0REpMTlYwcjIvNFJLcVh3ZG9BbWNlaG82UXN6SmNZajRMV0pJVGI5eWF0bXRiQXJoWUtlRzdpRTNZMW5kbHlLdmkrR1ZuQndlaEY2K1B3NXZHMlJiYXRIRkpmcVRqRkMybnFOc3hXTWFWVzlUWVJ3M1VncjJOcnZteHJwWUNxK0VoRXdzb24rMkZITzRUL3R1bGVGVnFHMS9pYm93SUxpUkxqVGt4UER2eUZSYUk9 | US | — | — | unknown |
7852 | msedge.exe | GET | 302 | 104.18.34.45:443 | https://click.kit-mail6.com/d0umw02mzeh0horgx8ntmhzl7d544ilhg9/dpheh0hzhm/aHR0cHM6Ly9hbGxvbnppaWkudmVyY2VsLmFwcC9tYXJzLmh0bWw=?utm_source=NotifyVisitors&utm_medium=NV_EMAIL&utm_campaign=NV_X%3CWX%3C&_nv_em_clid=59153_0_0&nv_channel=email&nv_uid=50f92061-c526-48f7-83a8-5aac2f71b55c | US | — | — | unknown |
7852 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
7852 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7852 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
7852 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
7852 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1768322693&lafgdate=0 | US | text | 4.71 Kb | whitelisted |
7852 | msedge.exe | GET | 200 | 216.198.79.3:443 | https://allonziii.vercel.app/mars.html | US | html | 939 b | unknown |
7852 | msedge.exe | GET | 200 | 2.16.204.136:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 128 Kb | whitelisted |
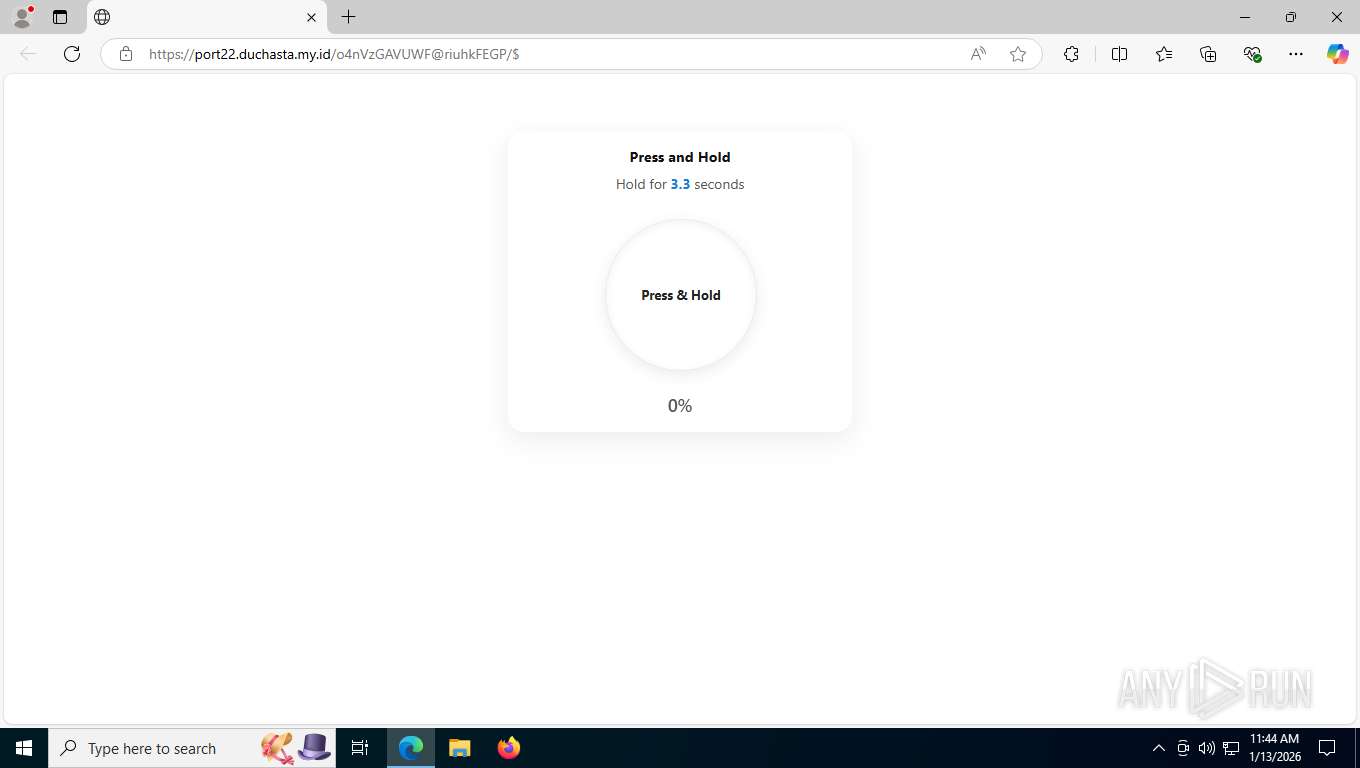
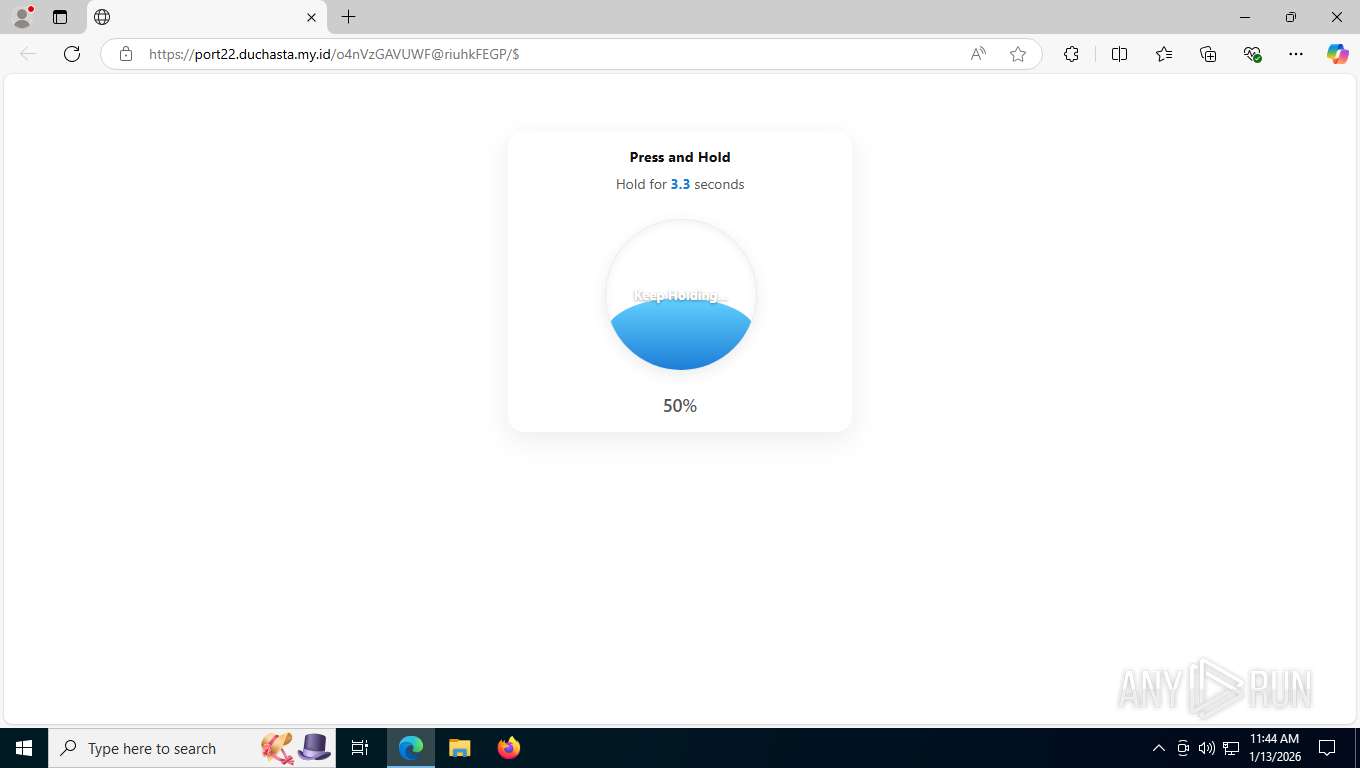
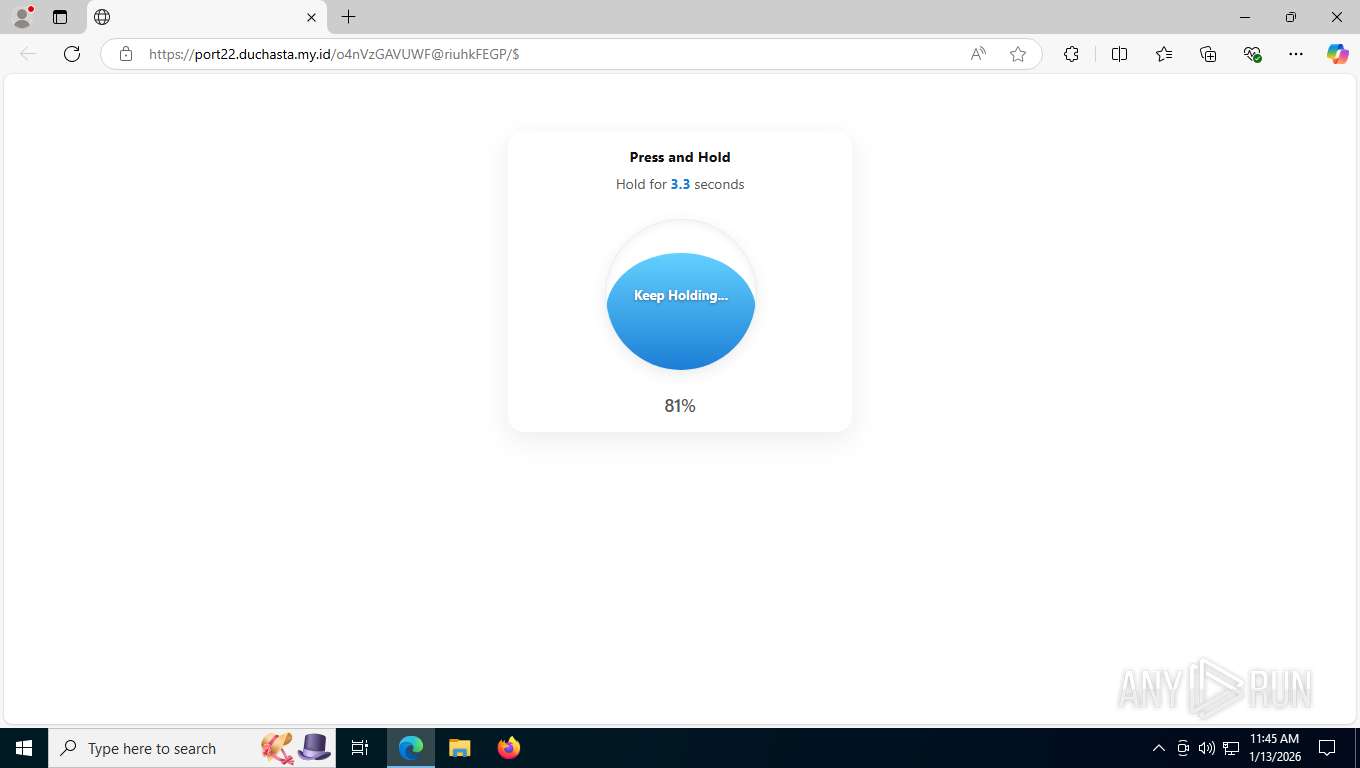
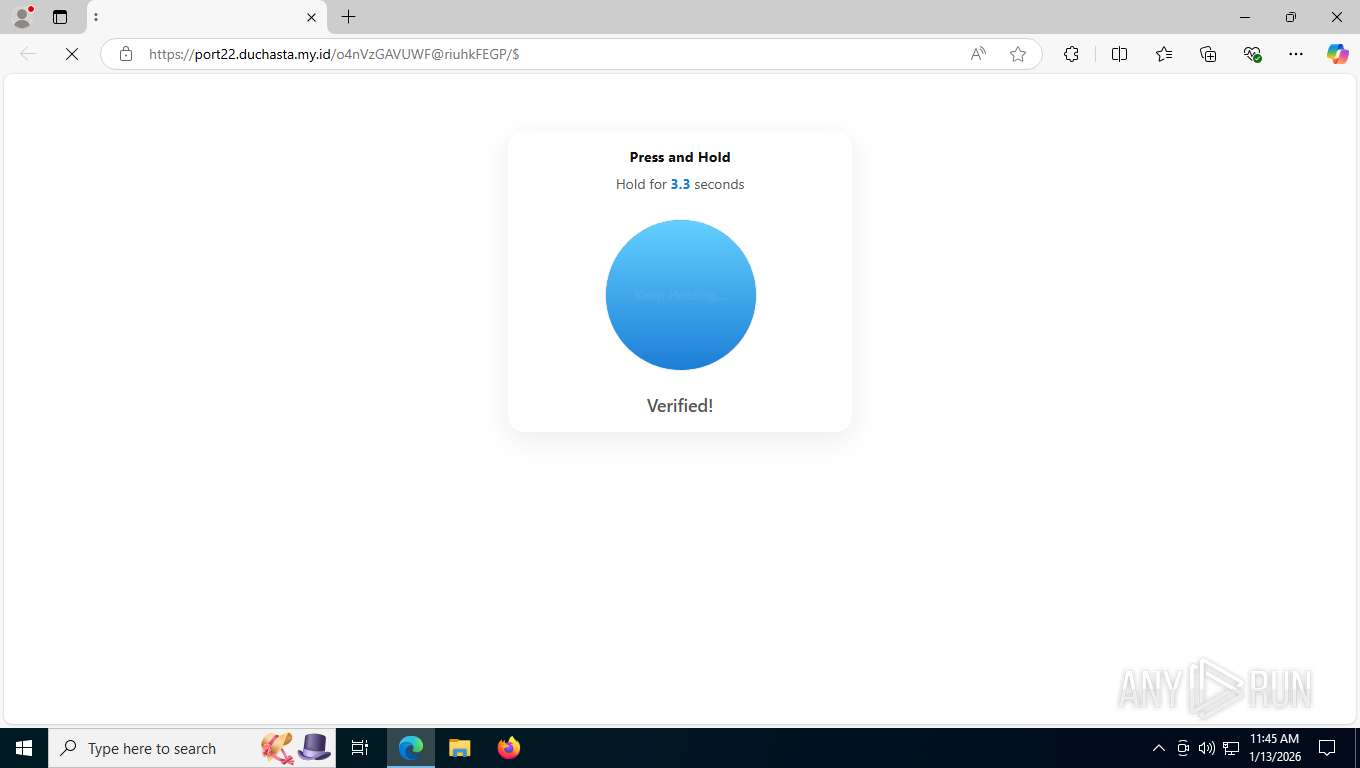
7852 | msedge.exe | GET | 200 | 104.21.70.60:443 | https://port22.duchasta.my.id/o4nVzGAVUWF@riuhkFEGP/$ | US | html | 4.78 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6244 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2680 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7852 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7852 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7852 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7852 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
7852 | msedge.exe | 13.226.244.14:443 | mail.notifyvisitors.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mail.notifyvisitors.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
click.kit-mail6.com |
| whitelisted |
allonziii.vercel.app |
| unknown |
www.bing.com |
| whitelisted |
port22.duchasta.my.id |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7852 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed DNS Query to Actor Abused Cloud Hosting Service Domain (vercel .app) |
7852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud infrastructure to build app (vercel .app) |
7852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Web apps custom Builder (.my .id) |
7852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Web apps custom Builder (.my .id) |
7852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud infrastructure to build app (vercel .app) |
7852 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Cloud Hosting Service Domain (vercel .app in TLS SNI) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7852 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as Tycoon (thewichaiyioce .qpon) |
7852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |