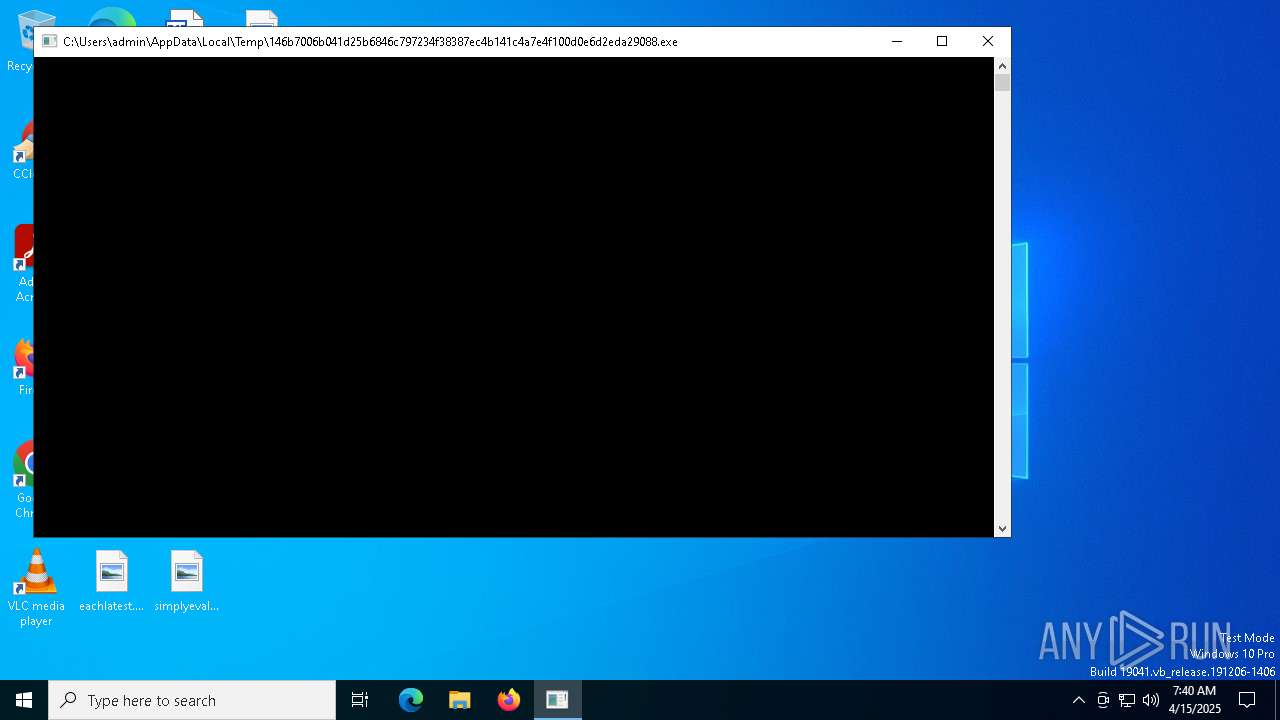
| File name: | 146b7006b041d25b6846c797234f38387ec4b141c4a7e4f100d0e6d2eda29088.exe |
| Full analysis: | https://app.any.run/tasks/63ee72ea-271c-44d5-9496-3bf05cb8e520 |
| Verdict: | Malicious activity |
| Threats: | Vidar is a dangerous malware that steals information and cryptocurrency from infected users. It derives its name from the ancient Scandinavian god of Vengeance. This stealer has been terrorizing the internet since 2018. |
| Analysis date: | April 15, 2025, 07:39:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 4A8A0CCFECC930091116324C79C1006E |
| SHA1: | D790BEFCBC31A4BEFAFEAF08879E15F99633B2A1 |
| SHA256: | 146B7006B041D25B6846C797234F38387EC4B141C4A7E4F100D0E6D2EDA29088 |
| SSDEEP: | 12288:XOVvSrqVURZPISoCnJ9CQcDnTWgTXvf0MWlk:XUvSrqVcZPISoCnJ9CfDnTWgTXvfNB |
MALICIOUS
Executing a file with an untrusted certificate
- 146b7006b041d25b6846c797234f38387ec4b141c4a7e4f100d0e6d2eda29088.exe (PID: 7336)
VIDAR has been detected (YARA)
- RegAsm.exe (PID: 7468)
VIDAR mutex has been found
- RegAsm.exe (PID: 7468)
SUSPICIOUS
Reads security settings of Internet Explorer
- RegAsm.exe (PID: 7468)
INFO
Checks supported languages
- 146b7006b041d25b6846c797234f38387ec4b141c4a7e4f100d0e6d2eda29088.exe (PID: 7336)
- RegAsm.exe (PID: 7468)
Reads the computer name
- RegAsm.exe (PID: 7468)
- 146b7006b041d25b6846c797234f38387ec4b141c4a7e4f100d0e6d2eda29088.exe (PID: 7336)
Create files in a temporary directory
- RegAsm.exe (PID: 7468)
Creates files in the program directory
- RegAsm.exe (PID: 7468)
Checks proxy server information
- RegAsm.exe (PID: 7468)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 7468)
Reads the software policy settings
- RegAsm.exe (PID: 7468)
Creates files or folders in the user directory
- RegAsm.exe (PID: 7468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Vidar
(PID) Process(7468) RegAsm.exe
C2https://t.me/edm0d
URLhttps://steamcommunity.com/profiles/76561199768374681
RC40123456789ABCDEF
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:19 23:23:51+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 276992 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4597e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | winterer dowered empressement |
| CompanyName: | listening triskelion |
| FileDescription: | outfawned |
| FileVersion: | 1.0.0.0 |
| InternalName: | VQP.exe |
| LegalCopyright: | Copyright 2024 |
| OriginalFileName: | VQP.exe |
| ProductName: | Shopman Stairs |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
133
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7336 | "C:\Users\admin\AppData\Local\Temp\146b7006b041d25b6846c797234f38387ec4b141c4a7e4f100d0e6d2eda29088.exe" | C:\Users\admin\AppData\Local\Temp\146b7006b041d25b6846c797234f38387ec4b141c4a7e4f100d0e6d2eda29088.exe | — | explorer.exe | |||||||||||
User: admin Company: listening triskelion Integrity Level: MEDIUM Description: outfawned Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 146b7006b041d25b6846c797234f38387ec4b141c4a7e4f100d0e6d2eda29088.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7468 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | 146b7006b041d25b6846c797234f38387ec4b141c4a7e4f100d0e6d2eda29088.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
Vidar(PID) Process(7468) RegAsm.exe C2https://t.me/edm0d URLhttps://steamcommunity.com/profiles/76561199768374681 RC40123456789ABCDEF | |||||||||||||||
| 7568 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7600 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
812
Read events
809
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7468) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7468) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7468) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
6
Text files
258
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7468 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\delays.tmp | text | |
MD5:B42966AAB5BA1ABC8837DEC7D4D7F572 | SHA256:A67B5E346C412D416C8DCAC42E61DD2FAE6401EF7E87C8C92ED6E3DE1B9FD6BC | |||
| 7468 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:DE2261AAB89E934330802FBD699213A7 | SHA256:376A91F97218DA8ACF0BE10BB223AAAFA2CBDAD89DF4C13E5F89E3A797C8074E | |||
| 7468 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:FA8325D4B614FB8DDB186ABCF1E3023F | SHA256:8EBF4F1898CC8771C38C09214C80F57B090B16766E4F067CDE764350869A2F1B | |||
| 7468 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:AFFBA4C75E931865FD073A4643A2C169 | SHA256:E70D50E3846B645E0260633FCC0930906E0839A112D21513D01F7F70D1443247 | |||
| 7468 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4E3D1101CFA1A79AF305FD7C55E37649_A8EAC700FEE71EDD327E06BEAA0C7F96 | binary | |
MD5:1A5C606AABDEED22163EA922DAFC1921 | SHA256:BD20BD94694916AF382F6762F0CE27D7A0C780D9D9C020584EA669B64C1BB97D | |||
| 7468 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:8CCB19649B6645F7E0333FFAE3957EFC | SHA256:0AAD7C8347CF03756BD297ADA14A543F01A77FDBA5DC2EEAAA8C270BDDCE6FD9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7468 | RegAsm.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |