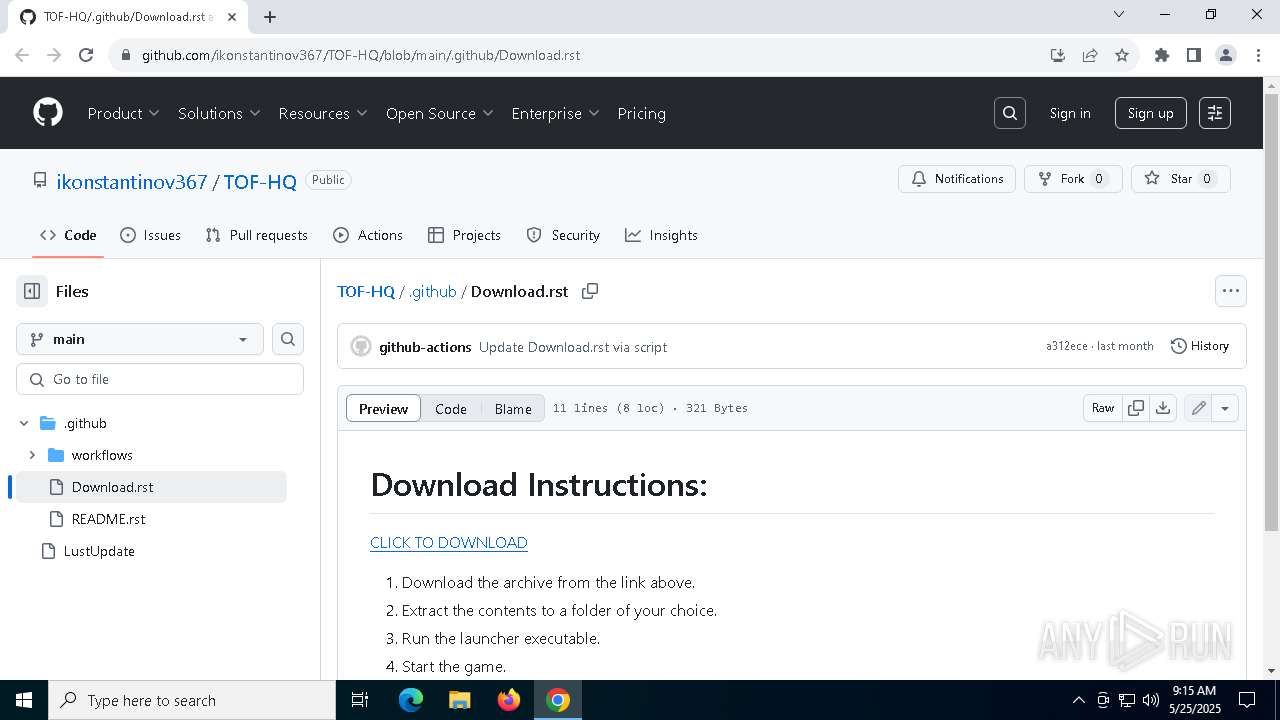
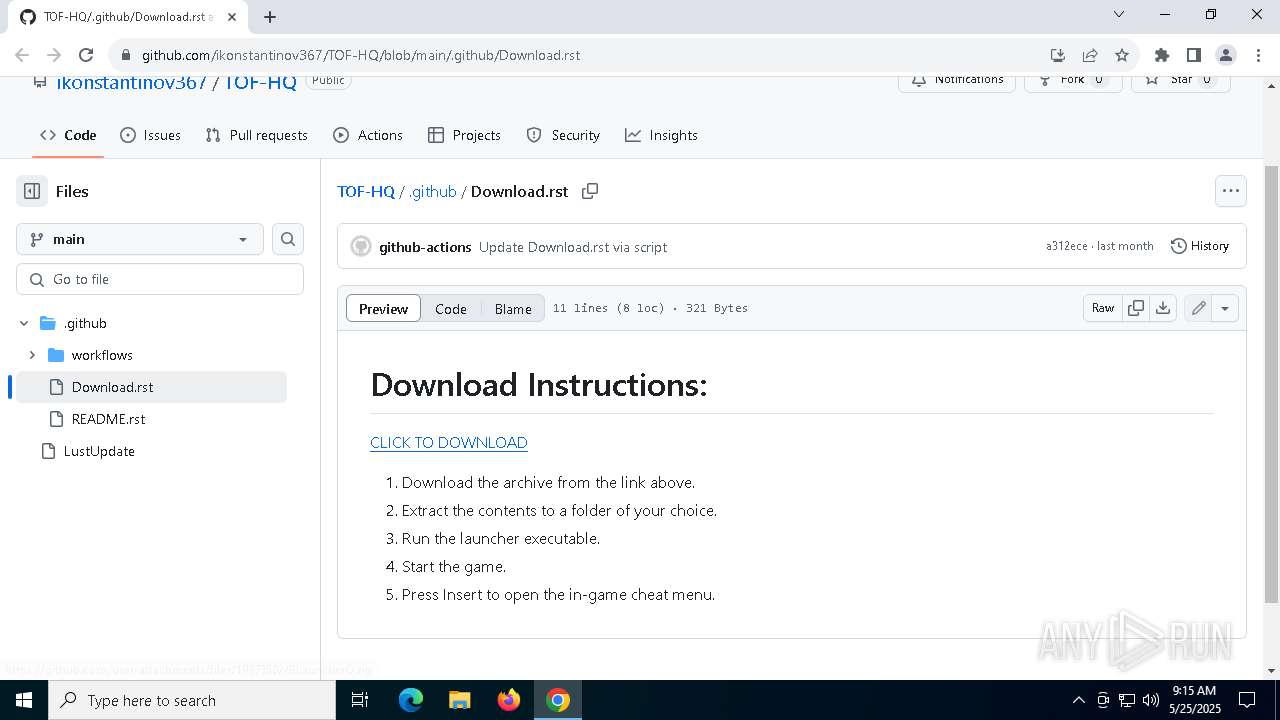
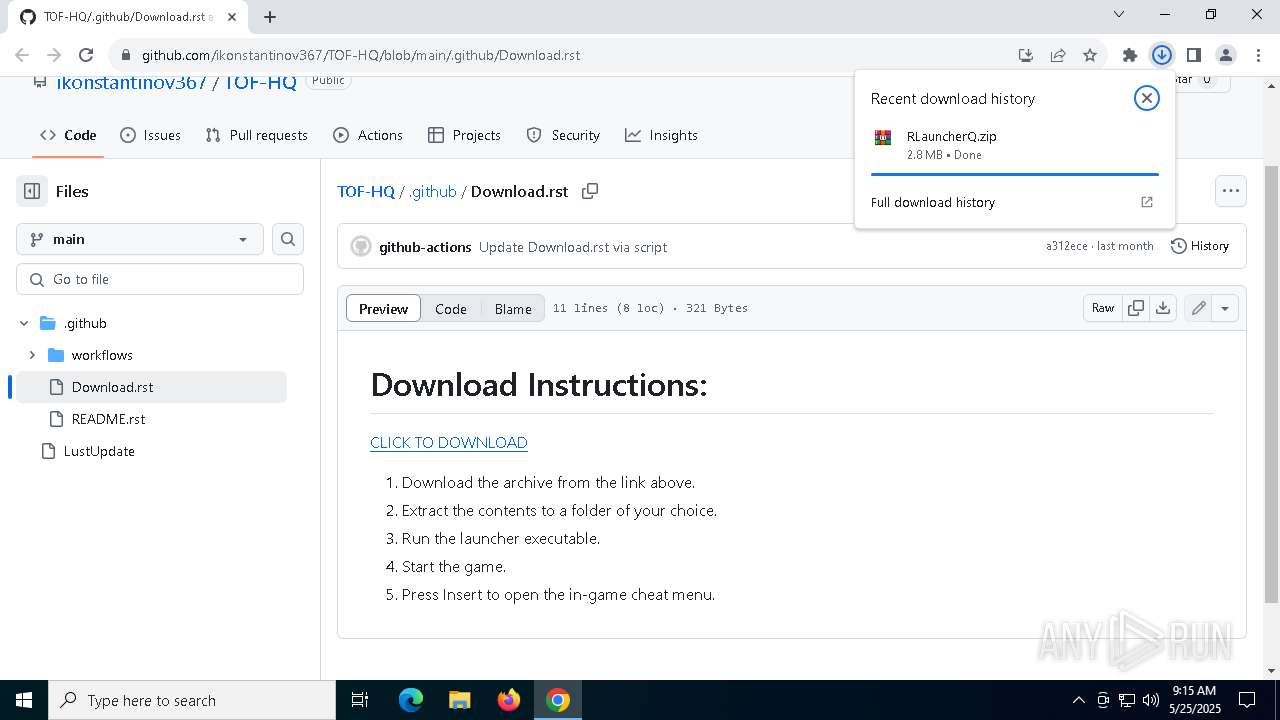
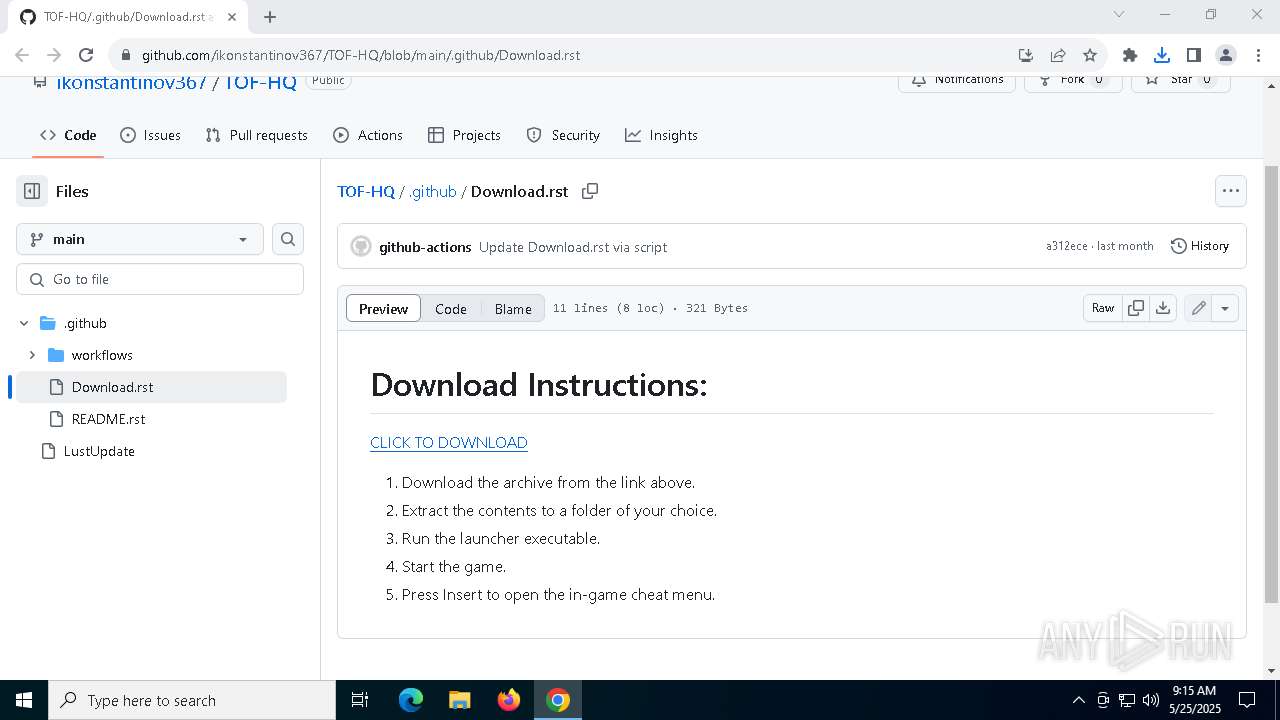
| URL: | https://github.com/ikonstantinov367/TOF-HQ/blob/main/.github/Download.rst |
| Full analysis: | https://app.any.run/tasks/9eca960e-8b1a-42fe-b2e4-cdaeb1e452a6 |
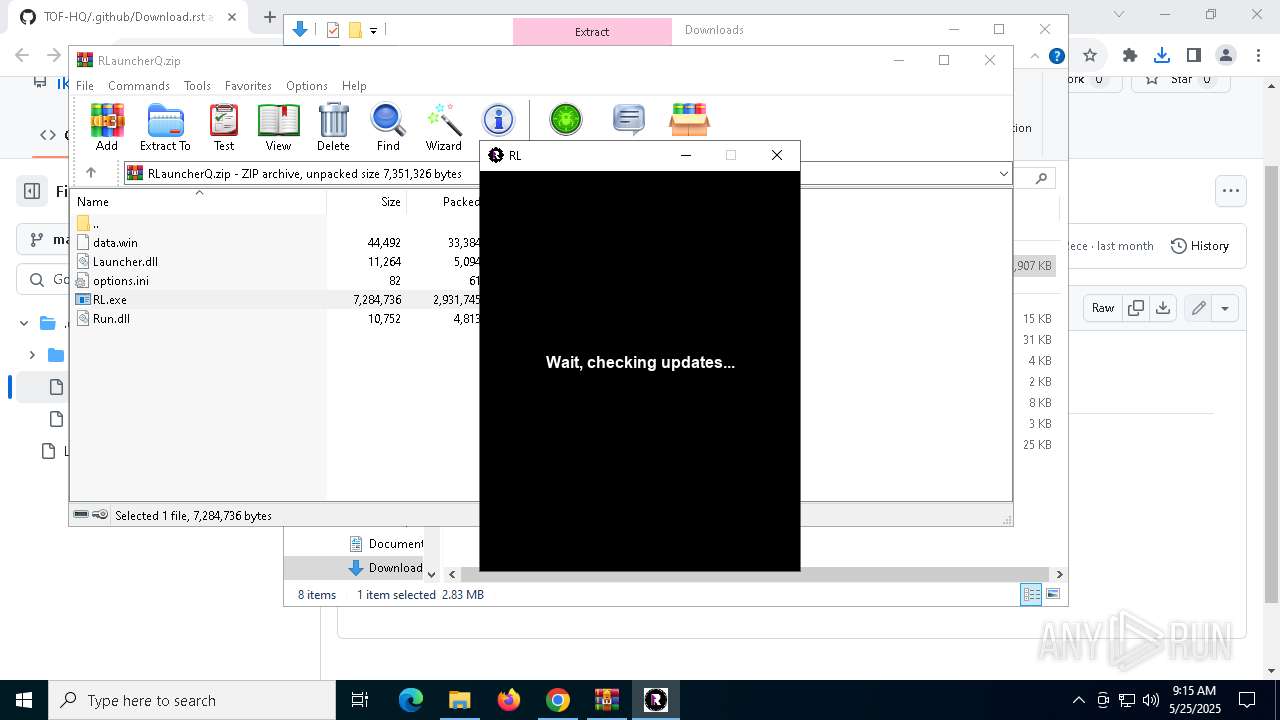
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 25, 2025, 09:15:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D4D0EAA16266E8EE48A87EC0C75B8D49 |
| SHA1: | 4E3CFE15AF9B7EB0C87B00E364279D4517DDED66 |
| SHA256: | 140031B66E5A71E56214DD41EB4855E71DAB9AEE4B6E6E2E52BC8964B9E92AC0 |
| SSDEEP: | 3:N8tEd8k9CQ0HzERLPEq3t9GR:2uqkL0TsLht9G |
MALICIOUS
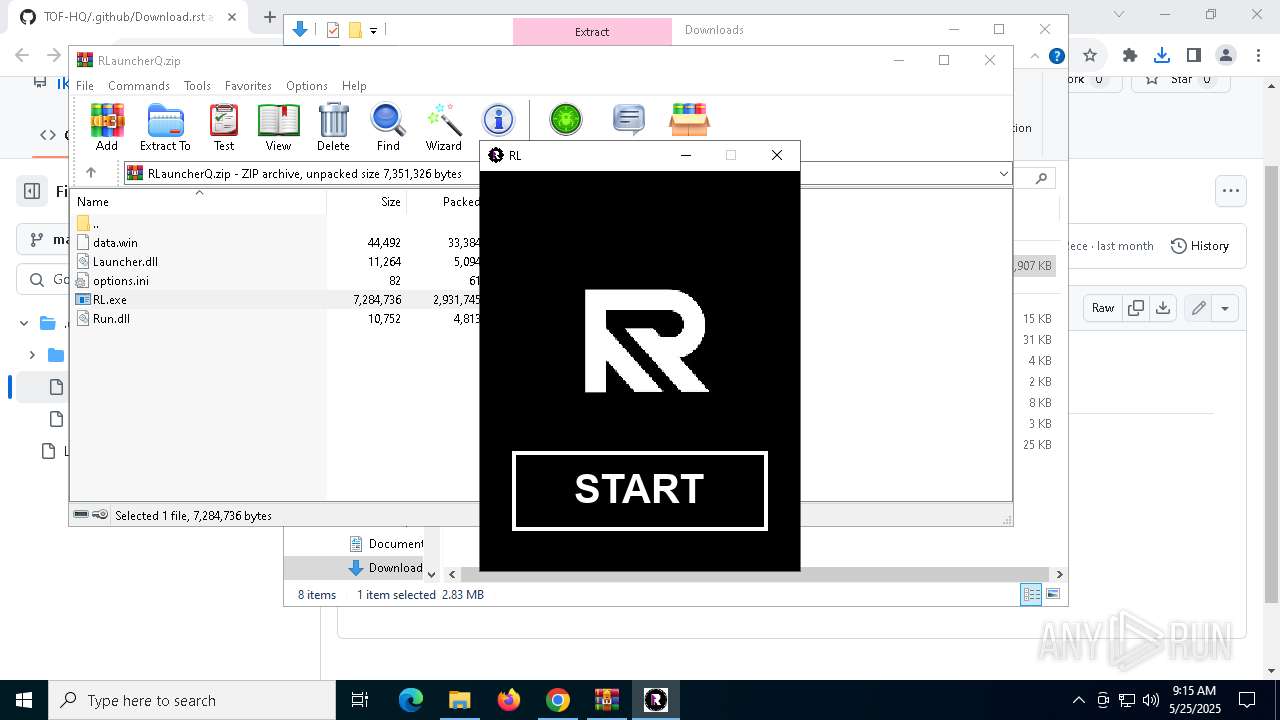
Adds path to the Windows Defender exclusion list
- RL.exe (PID: 7596)
- cmd.exe (PID: 7940)
Changes Windows Defender settings
- cmd.exe (PID: 7940)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 6988)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 6988)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- MSBuild.exe (PID: 6988)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 6988)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2600)
- RL.exe (PID: 7596)
Reads the date of Windows installation
- RL.exe (PID: 7596)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7940)
Executable content was dropped or overwritten
- RL.exe (PID: 7596)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 6988)
Searches for installed software
- MSBuild.exe (PID: 6988)
Starts CMD.EXE for commands execution
- RL.exe (PID: 7596)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7940)
INFO
Application launched itself
- chrome.exe (PID: 2320)
Reads the machine GUID from the registry
- RL.exe (PID: 7596)
Reads the computer name
- RL.exe (PID: 7596)
- MSBuild.exe (PID: 6988)
The sample compiled with english language support
- WinRAR.exe (PID: 2600)
- chrome.exe (PID: 2320)
Checks supported languages
- RL.exe (PID: 7596)
- MSBuild.exe (PID: 6988)
- kosdko0.exe (PID: 5408)
Executable content was dropped or overwritten
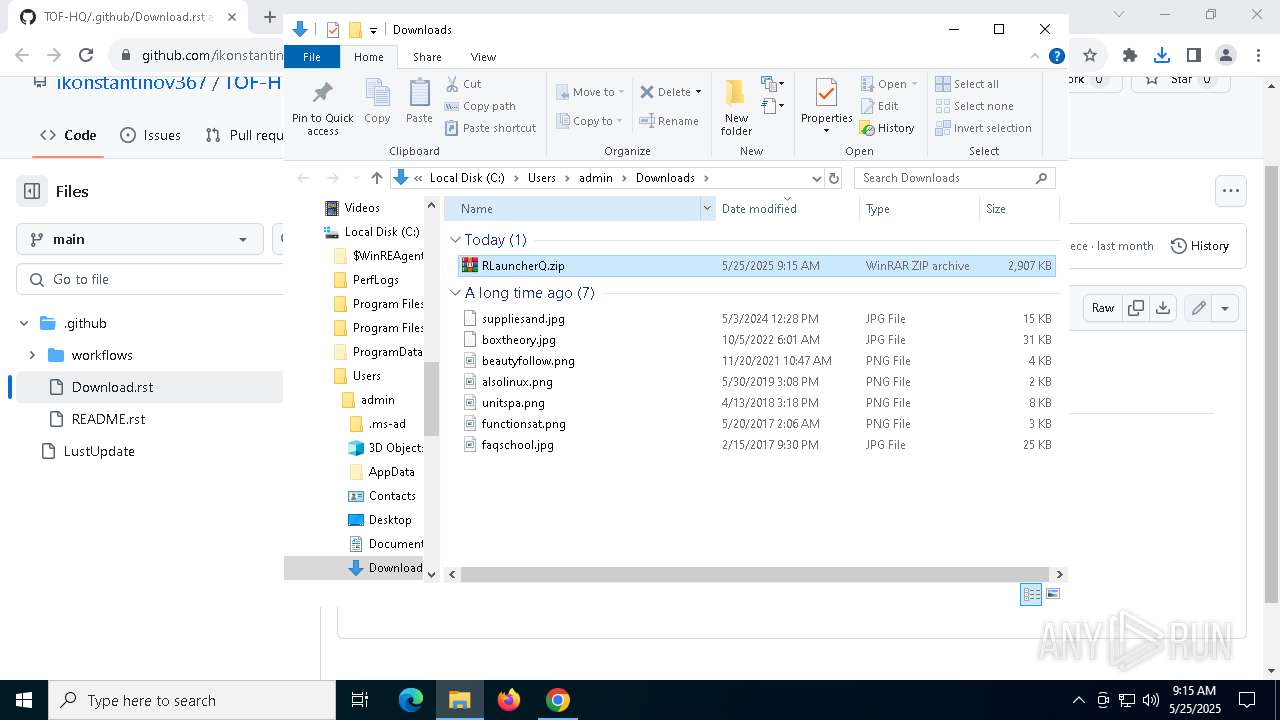
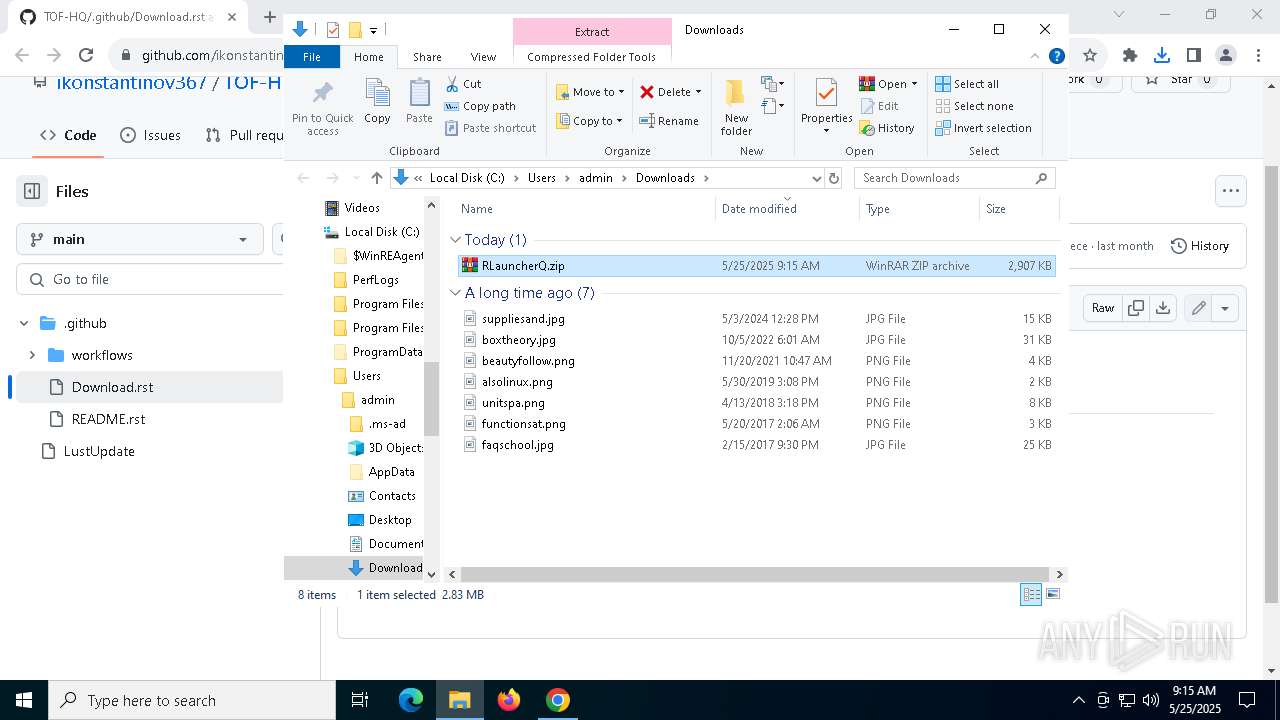
- WinRAR.exe (PID: 2600)
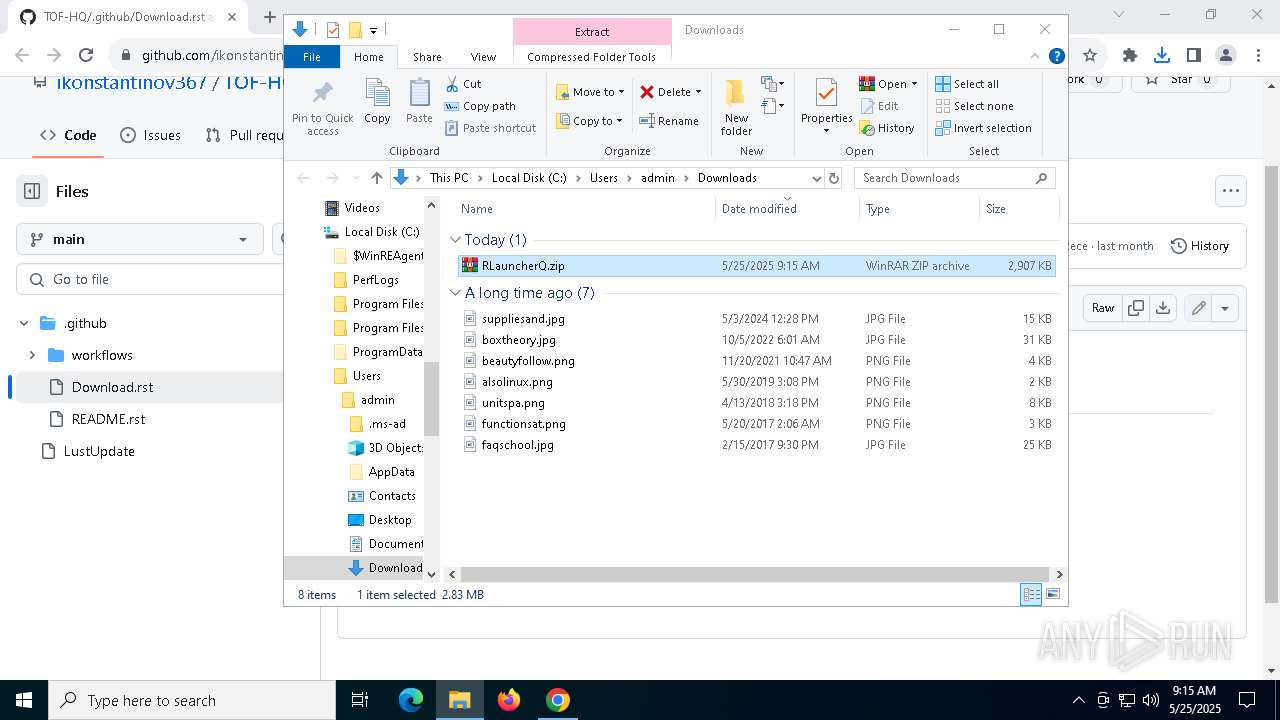
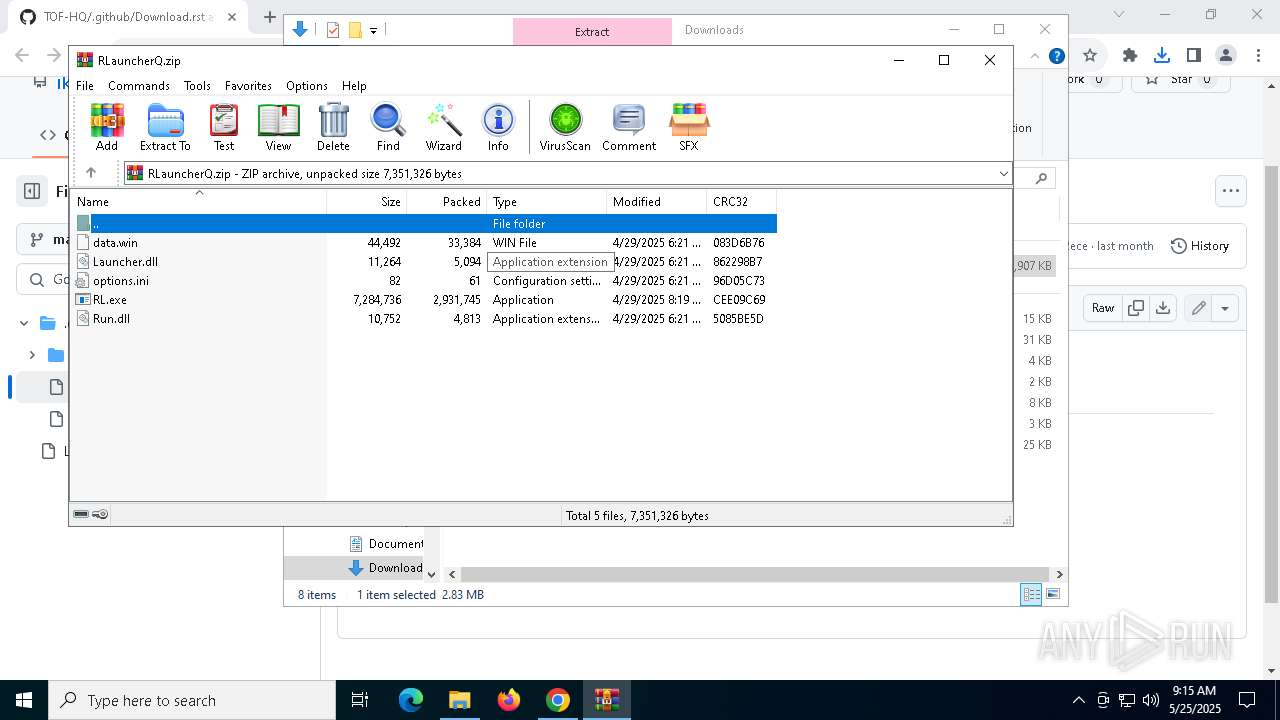
Manual execution by a user
- WinRAR.exe (PID: 2600)
Process checks computer location settings
- RL.exe (PID: 7596)
Creates files or folders in the user directory
- RL.exe (PID: 7596)
Checks proxy server information
- RL.exe (PID: 7596)
Reads the software policy settings
- RL.exe (PID: 7596)
- MSBuild.exe (PID: 6988)
- slui.exe (PID: 7660)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8036)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
159
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://github.com/ikonstantinov367/TOF-HQ/blob/main/.github/Download.rst" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\RLauncherQ.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
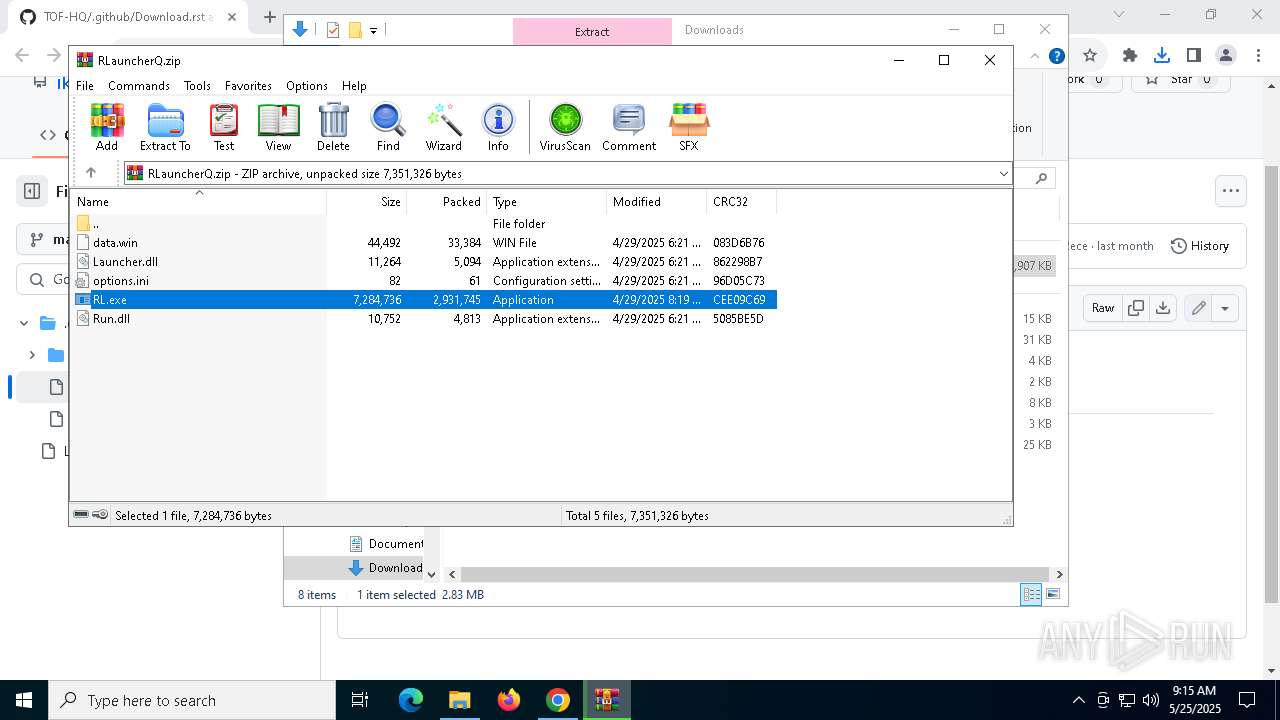
| 4920 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.35280\RL.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.35280\RL.exe | — | WinRAR.exe | |||||||||||
User: admin Company: YoYo Games Ltd Integrity Level: MEDIUM Description: A GameMaker Game Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1920 --field-trial-handle=1924,i,13388526827734541855,3932712370257610576,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5648 --field-trial-handle=1924,i,13388526827734541855,3932712370257610576,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5408 | "C:\Users\admin\Documents\update\kosdko0.exe" | C:\Users\admin\Documents\update\kosdko0.exe | — | RL.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3580 --field-trial-handle=1924,i,13388526827734541855,3932712370257610576,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6372 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x220,0x224,0x228,0x21c,0x22c,0x7ffc88ebdc40,0x7ffc88ebdc4c,0x7ffc88ebdc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
13 741
Read events
13 720
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2320) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000357D6B9355CDDB01 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\RLauncherQ.zip | |||
Executable files
7
Suspicious files
69
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
58
DNS requests
51
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6944 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
7596 | RL.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | binary | 1.42 Kb | whitelisted |
2560 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | US | — | — | whitelisted |
7596 | RL.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | whitelisted |
2560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | US | binary | 98 b | whitelisted |
6944 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
2560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | US | compressed | 4.69 Kb | whitelisted |
2560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | US | binary | 1.09 Kb | whitelisted |
2560 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | US | compressed | 4.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2320 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7172 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7172 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7172 | chrome.exe | 185.199.108.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (cornerdurv .top) |
6988 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (narrathfpt .top) |
6988 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
6988 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
6988 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
6988 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
6988 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |