| download: | /Myshas/Data-Encoder-Crypter-Encoded-Aes-Hidden-Startup/raw/main/Data%20Encoder%20Src/DataEncoder%20Crypte%E2%80%AEnls..scr |
| Full analysis: | https://app.any.run/tasks/c506335a-5b49-4e68-9423-2cf8a5d95790 |
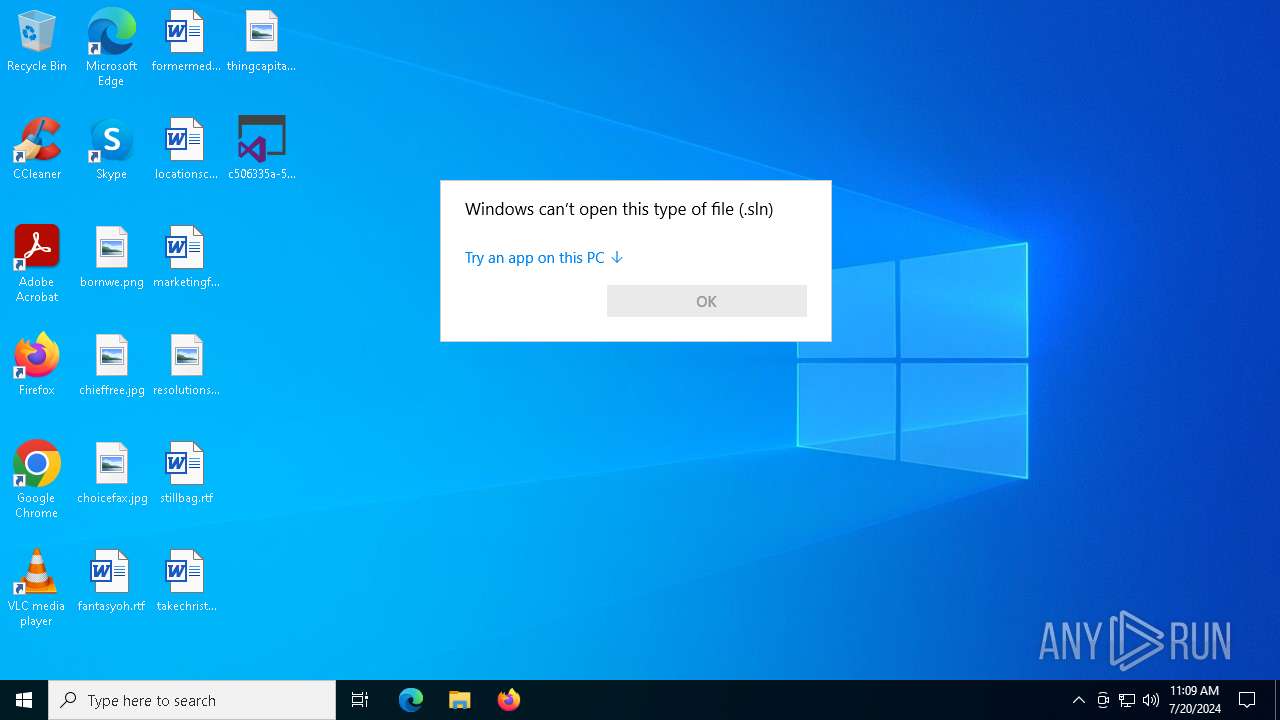
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | July 20, 2024, 11:09:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 7C031479DEDAB585B453098453A09F35 |
| SHA1: | 401EC0BF7CE170A67C0317150C2B83885E8ABC54 |
| SHA256: | 138BE3A5769AF371A332CF9404CCA591CD78D594D6A072FA8047E222AC92770E |
| SSDEEP: | 12288:6B3nNy7YxUxwiHiNa16z+VKJD0fSKz/dWDHKcD2k:enNyMxHiHcKVKJD0fSKz1WzKcD2k |
MALICIOUS
Drops the executable file immediately after the start
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- 7z.exe (PID: 7144)
- MicrosoftCorporation.exe (PID: 3020)
- 7z.exe (PID: 5948)
- WinSAT.exe (PID: 5168)
- Runtime Broker.exe (PID: 7012)
- 7z.exe (PID: 7076)
- Microsoft.exe (PID: 5108)
- 7z.exe (PID: 8160)
Changes the autorun value in the registry
- Service.exe (PID: 5772)
- Service.exe (PID: 2060)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 5720)
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 5720)
Bypass execution policy to execute commands
- powershell.exe (PID: 7700)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5720)
UAC/LUA settings modification
- reg.exe (PID: 3944)
ASYNCRAT has been detected (SURICATA)
- RegAsm.exe (PID: 6384)
- RegAsm.exe (PID: 7840)
Uses Task Scheduler to run other applications
- MicrosoftCorporation.exe (PID: 3020)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 6492)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 7548)
The DLL Hijacking
- Microsoft.exe (PID: 3108)
Attempting to use instant messaging service
- MicrosoftCorporation.exe (PID: 3020)
Stealers network behavior
- MicrosoftCorporation.exe (PID: 3020)
SUSPICIOUS
Executable content was dropped or overwritten
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- 7z.exe (PID: 7144)
- MicrosoftCorporation.exe (PID: 3020)
- 7z.exe (PID: 5948)
- WinSAT.exe (PID: 5168)
- Runtime Broker.exe (PID: 7012)
- 7z.exe (PID: 7076)
- Microsoft.exe (PID: 5108)
- 7z.exe (PID: 8160)
Drops 7-zip archiver for unpacking
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- WinSAT.exe (PID: 5168)
Reads security settings of Internet Explorer
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
- WinSAT.exe (PID: 5168)
Application launched itself
- MicrosoftCorporation.exe (PID: 8084)
- cmd.exe (PID: 1964)
- Runtime Broker.exe (PID: 7012)
- Microsoft.exe (PID: 5108)
- cmd.exe (PID: 7044)
Process drops legitimate windows executable
- MicrosoftCorporation.exe (PID: 3020)
- WinSAT.exe (PID: 5168)
- 7z.exe (PID: 7076)
- Microsoft.exe (PID: 5108)
The process executes VB scripts
- MicrosoftCorporation.exe (PID: 3020)
- cmd.exe (PID: 5408)
Likely accesses (executes) a file from the Public directory
- cscript.exe (PID: 7300)
- cmd.exe (PID: 1964)
- powershell.exe (PID: 6500)
- Service.exe (PID: 5772)
- cmd.exe (PID: 7508)
- attrib.exe (PID: 5464)
- cmd.exe (PID: 6880)
- cmd.exe (PID: 7540)
- attrib.exe (PID: 5716)
- attrib.exe (PID: 5252)
- cmd.exe (PID: 5408)
- wscript.exe (PID: 8108)
- cmd.exe (PID: 7044)
- powershell.exe (PID: 8116)
- Service.exe (PID: 2060)
Runs shell command (SCRIPT)
- cscript.exe (PID: 7300)
- wscript.exe (PID: 8108)
Executing commands from a ".bat" file
- cscript.exe (PID: 7300)
- Service.exe (PID: 5772)
- Microsoft.exe (PID: 5108)
- wscript.exe (PID: 8108)
- Service.exe (PID: 2060)
Starts CMD.EXE for commands execution
- cscript.exe (PID: 7300)
- cmd.exe (PID: 1964)
- Service.exe (PID: 5772)
- Runtime Broker.exe (PID: 7012)
- Microsoft.exe (PID: 5108)
- wscript.exe (PID: 8108)
- cmd.exe (PID: 7044)
- Service.exe (PID: 2060)
Identifying current user with WHOAMI command
- cmd.exe (PID: 1964)
- cmd.exe (PID: 7044)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1964)
- cmd.exe (PID: 7044)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1964)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 116)
- cmd.exe (PID: 7044)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7912)
Starts a Microsoft application from unusual location
- Service.exe (PID: 5772)
- Service.exe (PID: 2060)
Powershell scripting: start process
- cmd.exe (PID: 1964)
- cmd.exe (PID: 116)
- cmd.exe (PID: 7044)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7912)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5720)
Query Microsoft Defender preferences
- cmd.exe (PID: 5720)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5720)
The process creates files with name similar to system file names
- 7z.exe (PID: 5948)
- MicrosoftCorporation.exe (PID: 3020)
- WinSAT.exe (PID: 5168)
- 7z.exe (PID: 8160)
Reads the date of Windows installation
- MicrosoftCorporation.exe (PID: 3020)
Connects to unusual port
- RegAsm.exe (PID: 6384)
- RegAsm.exe (PID: 7840)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 6384)
- RegAsm.exe (PID: 7840)
Malware-specific behavior (creating "System.dll" in Temp)
- WinSAT.exe (PID: 5168)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5720)
Starts application with an unusual extension
- cmd.exe (PID: 3836)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 7768)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6872)
- cmd.exe (PID: 6972)
Uses WMIC.EXE to obtain memory chip information
- cmd.exe (PID: 8116)
Checks for external IP
- curl.exe (PID: 6104)
- MicrosoftCorporation.exe (PID: 3020)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7508)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 6880)
- cmd.exe (PID: 7540)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MicrosoftCorporation.exe (PID: 3020)
The process connected to a server suspected of theft
- MicrosoftCorporation.exe (PID: 3020)
INFO
Reads the computer name
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- 7z.exe (PID: 7144)
- MicrosoftCorporation.exe (PID: 8084)
- MicrosoftCorporation.exe (PID: 3020)
- Service.exe (PID: 5772)
- 7z.exe (PID: 5948)
- aitstatic.exe (PID: 7212)
- RegAsm.exe (PID: 6384)
- ComSvcConfig.exe (PID: 8044)
- RegAsm.exe (PID: 7840)
- WinSAT.exe (PID: 5168)
- MicrosoftCertificateServices.exe (PID: 6944)
- RegAsm.exe (PID: 8124)
- Runtime Broker.exe (PID: 7012)
- Runtime Broker.exe (PID: 2828)
- Runtime Broker.exe (PID: 6068)
- curl.exe (PID: 6104)
- 7z.exe (PID: 7076)
- Microsoft.exe (PID: 5108)
- Microsoft.exe (PID: 6852)
- 7z.exe (PID: 8160)
- aitstatic.exe (PID: 5180)
- RegAsm.exe (PID: 544)
- Service.exe (PID: 2060)
- ComSvcConfig.exe (PID: 6140)
- MicrosoftCertificateServices.exe (PID: 5660)
- RegAsm.exe (PID: 6916)
- Microsoft.exe (PID: 3108)
- RegAsm.exe (PID: 3500)
Reads the machine GUID from the registry
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 8084)
- MicrosoftCorporation.exe (PID: 3020)
- RegAsm.exe (PID: 6384)
- aitstatic.exe (PID: 7212)
- ComSvcConfig.exe (PID: 8044)
- RegAsm.exe (PID: 7840)
- MicrosoftCertificateServices.exe (PID: 6944)
- Runtime Broker.exe (PID: 7012)
- RegAsm.exe (PID: 8124)
- aitstatic.exe (PID: 5180)
- RegAsm.exe (PID: 544)
- ComSvcConfig.exe (PID: 6140)
- RegAsm.exe (PID: 3500)
- MicrosoftCertificateServices.exe (PID: 5660)
- RegAsm.exe (PID: 6916)
Disables trace logs
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
Checks proxy server information
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
- Runtime Broker.exe (PID: 7012)
- Microsoft.exe (PID: 5108)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 8180)
Creates files or folders in the user directory
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
- Microsoft.exe (PID: 5108)
Checks supported languages
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
- MicrosoftCorporation.exe (PID: 8084)
- Service.exe (PID: 5772)
- 7z.exe (PID: 7144)
- 7z.exe (PID: 5948)
- aitstatic.exe (PID: 7212)
- RegAsm.exe (PID: 6384)
- ComSvcConfig.exe (PID: 8044)
- RegAsm.exe (PID: 7840)
- WinSAT.exe (PID: 5168)
- MicrosoftCertificateServices.exe (PID: 6944)
- RegAsm.exe (PID: 8124)
- Runtime Broker.exe (PID: 7012)
- chcp.com (PID: 6088)
- curl.exe (PID: 6104)
- Runtime Broker.exe (PID: 2828)
- Runtime Broker.exe (PID: 6068)
- 7z.exe (PID: 7076)
- Microsoft.exe (PID: 5108)
- Microsoft.exe (PID: 6852)
- Microsoft.exe (PID: 3108)
- 7z.exe (PID: 8160)
- aitstatic.exe (PID: 5180)
- RegAsm.exe (PID: 544)
- Service.exe (PID: 2060)
- ComSvcConfig.exe (PID: 6140)
- RegAsm.exe (PID: 3500)
- MicrosoftCertificateServices.exe (PID: 5660)
- RegAsm.exe (PID: 6916)
Reads Environment values
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
- RegAsm.exe (PID: 6384)
- RegAsm.exe (PID: 7840)
- Runtime Broker.exe (PID: 7012)
- Microsoft.exe (PID: 5108)
Reads the software policy settings
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
- RegAsm.exe (PID: 6384)
- RegAsm.exe (PID: 7840)
Create files in a temporary directory
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
- Service.exe (PID: 5772)
- 7z.exe (PID: 7144)
- 7z.exe (PID: 5948)
- WinSAT.exe (PID: 5168)
- Runtime Broker.exe (PID: 7012)
- Microsoft.exe (PID: 5108)
- Service.exe (PID: 2060)
- 7z.exe (PID: 8160)
Reads security settings of Internet Explorer
- cscript.exe (PID: 7300)
- WMIC.exe (PID: 6524)
- WMIC.exe (PID: 7376)
Creates files in the program directory
- c506335a-5b49-4e68-9423-2cf8a5d95790.exe (PID: 6800)
- MicrosoftCorporation.exe (PID: 3020)
- 7z.exe (PID: 7076)
- Microsoft.exe (PID: 5108)
Checks operating system version
- cmd.exe (PID: 1964)
- cmd.exe (PID: 7044)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7700)
Potential library load (Base64 Encoded 'LoadLibrary')
- MicrosoftCorporation.exe (PID: 3020)
- Microsoft.exe (PID: 5108)
Potential dynamic function import (Base64 Encoded 'GetProcAddress')
- MicrosoftCorporation.exe (PID: 3020)
- Microsoft.exe (PID: 5108)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- MicrosoftCorporation.exe (PID: 3020)
- Microsoft.exe (PID: 5108)
Process checks computer location settings
- MicrosoftCorporation.exe (PID: 3020)
Reads product name
- Microsoft.exe (PID: 5108)
Reads CPU info
- MicrosoftCorporation.exe (PID: 3020)
The executable file from the user directory is run by the Powershell process
- aitstatic.exe (PID: 5180)
- ComSvcConfig.exe (PID: 6140)
- MicrosoftCertificateServices.exe (PID: 5660)
Attempting to use instant messaging service
- MicrosoftCorporation.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2064:05:07 09:41:15+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 319488 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4fefe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | YnkgdW5rbm93bg== |
| FileDescription: | Microsoft Visual Studio Solution (.sln) |
| FileVersion: | 1.0.0.0 |
| InternalName: | VisualStudio.exe |
| LegalCopyright: | Microsoft Visual Studio Solution (.sln) |
| LegalTrademarks: | - |
| OriginalFileName: | VisualStudio.exe |
| ProductName: | Microsoft Visual Studio Solution (.sln) |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
276
Monitored processes
130
Malicious processes
20
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell -Command "Start-Process -FilePath 'C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\CRLs\aitstatic.exe'"" | C:\Windows\System32\cmd.exe | — | Microsoft.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | #system32 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | aitstatic.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 636 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 912 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1032 | powershell -Command "Start-Process -FilePath 'C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\CRLs\aitstatic.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1340 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | schtasks /create /tn "DobeDiscovery" /tr "C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\CRLs\ComSvcConfig.exe" /st 00:00 /du 9999:59 /sc once /ri 10 /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1956 | attrib +h +s "C:\ProgramData\lock.ddmb" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\Videos\b.bat" " | C:\Windows\SysWOW64\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
115 793
Read events
115 667
Write events
124
Delete events
2
Modification events
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6800) c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\c506335a-5b49-4e68-9423-2cf8a5d95790_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
40
Suspicious files
134
Text files
26
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | MicrosoftCorporation.exe | C:\Users\admin\AppData\Local\Temp\0501748c-d414-4609-b8d2-ce6062af69bc.7z | — | |
MD5:— | SHA256:— | |||
| 5948 | 7z.exe | C:\Users\admin\AppData\Local\Temp\V0501748c-d414-4609-b8d2-ce6062af69bc\WinSAT.exe | — | |
MD5:— | SHA256:— | |||
| 6800 | c506335a-5b49-4e68-9423-2cf8a5d95790.exe | C:\ProgramData\sevenZip\7z.exe | executable | |
MD5:C31C4B04558396C6FABAB64DCF366534 | SHA256:9D182F421381429FD77598FEB609FEFB54DCAEF722DDBF5AA611B68A706C10D3 | |||
| 7144 | 7z.exe | C:\Users\admin\AppData\Local\Temp\c411d7f6-eb9c-4e67-8fe4-a16268e8ebc3FO\MicrosoftCorporation.exe | executable | |
MD5:F24C087BFD6A5A11079A0FF8EE778593 | SHA256:C9F5CFBA7202DB9FDE50C885C96B787258358398B8738E4B3954845EF0936866 | |||
| 3020 | MicrosoftCorporation.exe | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\CTLs\WinSAT.exe | — | |
MD5:— | SHA256:— | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sgafrqig.hvf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5168 | WinSAT.exe | C:\Users\admin\AppData\Local\Temp\nse88B3.tmp\app-32.7z | — | |
MD5:— | SHA256:— | |||
| 7700 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kmo43nku.ksl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6800 | c506335a-5b49-4e68-9423-2cf8a5d95790.exe | C:\Users\admin\AppData\Local\Temp\uwzg5z004r.7z | compressed | |
MD5:E59BEC64102B5FC4EC846B1C742EAFD4 | SHA256:9F8B0A94DF65ADF17F63F57F61C7D34C925536548C7076F6A13BC53429D54858 | |||
| 3020 | MicrosoftCorporation.exe | C:\Users\Public\Videos\b.bat | text | |
MD5:874525C405F65DAA259081784A3458F1 | SHA256:98679E199F231AA012B301BC3B2A678B1FF52A87BC1C59C546183B9F53BC65ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
55
DNS requests
22
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6104 | curl.exe | GET | 200 | 172.67.74.152:80 | http://api.ipify.org/ | unknown | — | — | whitelisted |
3020 | MicrosoftCorporation.exe | GET | 200 | 172.67.74.152:80 | http://api.ipify.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5620 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4716 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
7856 | svchost.exe | 4.208.221.206:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2760 | svchost.exe | 40.113.110.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6800 | c506335a-5b49-4e68-9423-2cf8a5d95790.exe | 49.12.202.237:443 | www.7-zip.org | Hetzner Online GmbH | DE | unknown |
6800 | c506335a-5b49-4e68-9423-2cf8a5d95790.exe | 172.67.75.40:443 | rentry.co | CLOUDFLARENET | US | unknown |
6800 | c506335a-5b49-4e68-9423-2cf8a5d95790.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
www.7-zip.org |
| whitelisted |
rentry.co |
| unknown |
raw.githubusercontent.com |
| shared |
text.is |
| unknown |
paste.fo |
| malicious |
cdn.gilcdn.com |
| unknown |
muckcompany.store |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6800 | c506335a-5b49-4e68-9423-2cf8a5d95790.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
2168 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6384 | RegAsm.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
6384 | RegAsm.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
6384 | RegAsm.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
7840 | RegAsm.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
7840 | RegAsm.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
7840 | RegAsm.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
6384 | RegAsm.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2 ETPRO signatures available at the full report