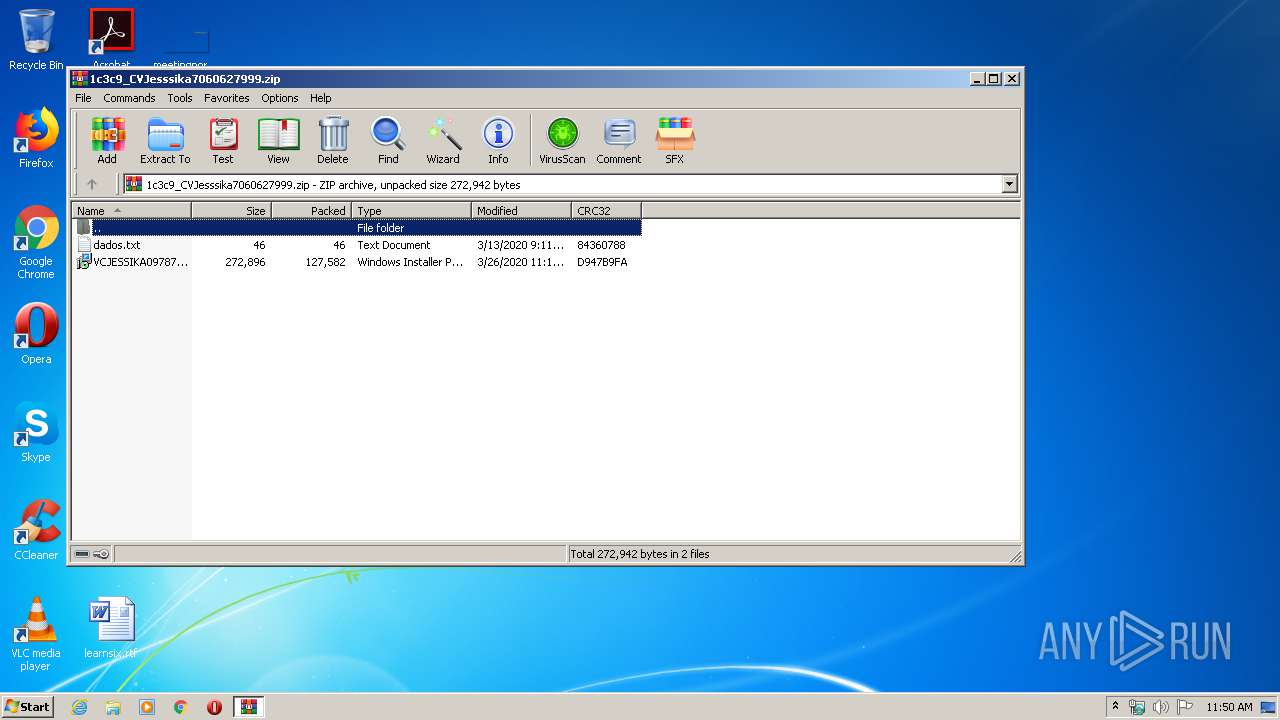
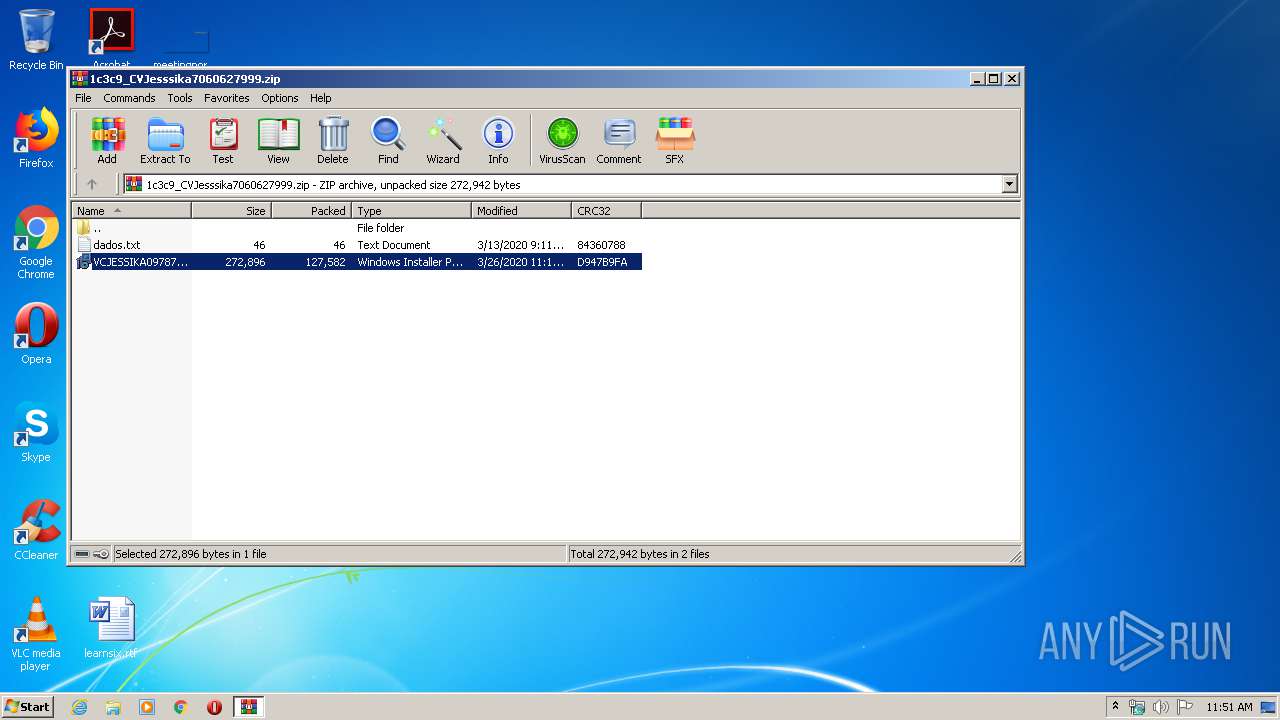
| File name: | 1c3c9_CVJesssika7060627999.zip |
| Full analysis: | https://app.any.run/tasks/38da815d-0840-4039-8ebb-7984747bbec7 |
| Verdict: | Malicious activity |
| Threats: | Metamorfo is a trojan malware family that has been active since 2018. It remains a top threat, focusing on stealing victims’ financial information, including banking credentials and other data. The malware is known for targeting users in Brazil. |
| Analysis date: | March 31, 2020, 10:50:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1C3C904EF8CE6021F1F2E06D5AD3A00B |
| SHA1: | 4D00E5463AEE0B1D972108B5C3FEEE783D8F9BC0 |
| SHA256: | 136D99EA17307B10C34997D605F7EB746A6FD50C2DDDB4576337B8DAAE3A83C6 |
| SSDEEP: | 3072:bSB+EiHORS29FAUUx5ziaN1T98ehPPO6zYrnmejVMp+:+B+JHORT0H98eh1zCnmeBMI |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 2860)
- NPIE.EXE (PID: 3456)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3548)
- NPIE.EXE (PID: 3456)
Application was dropped or rewritten from another process
- NPIE.EXE (PID: 3456)
METAMORFO was detected
- NPIE.EXE (PID: 3456)
Connects to CnC server
- NPIE.EXE (PID: 3456)
SUSPICIOUS
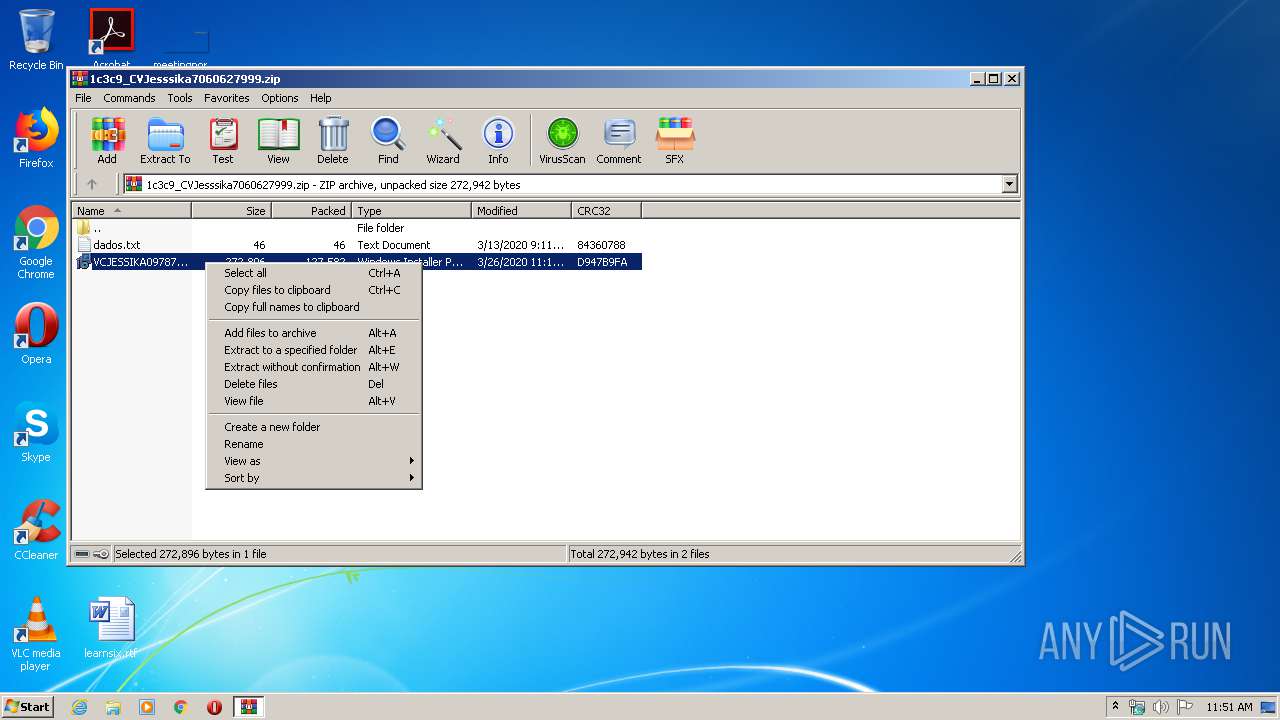
Executable content was dropped or overwritten
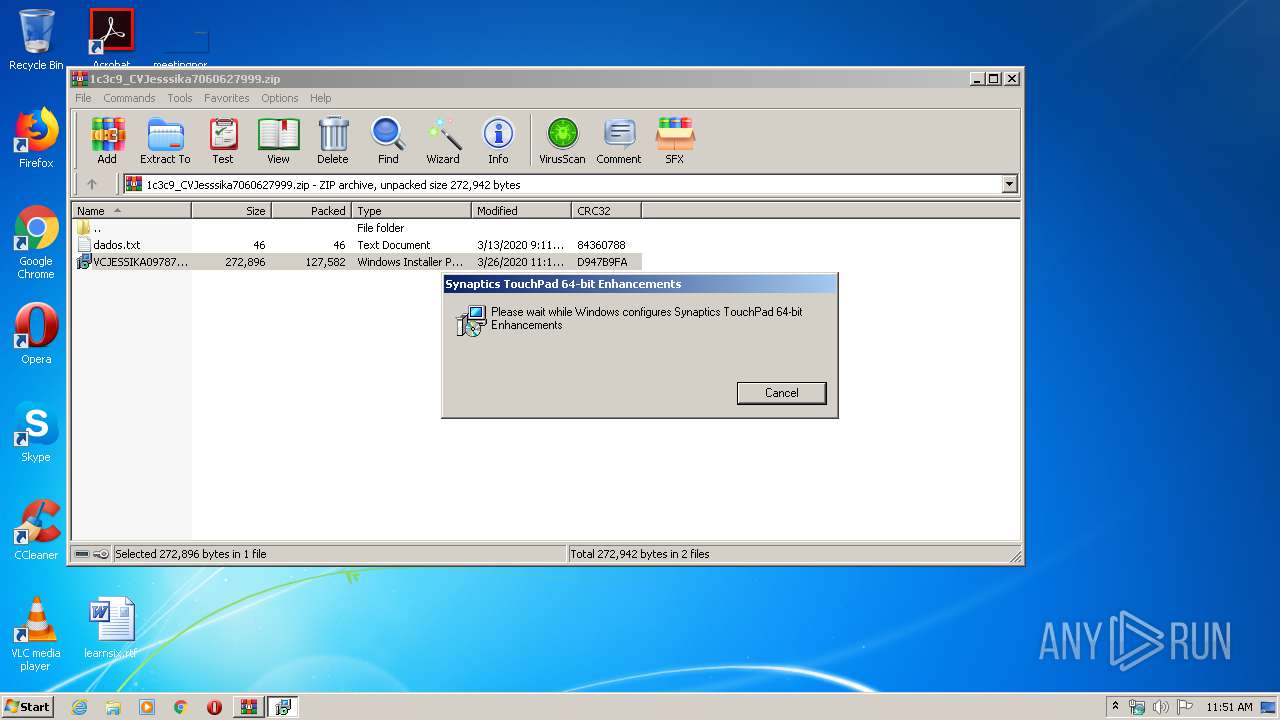
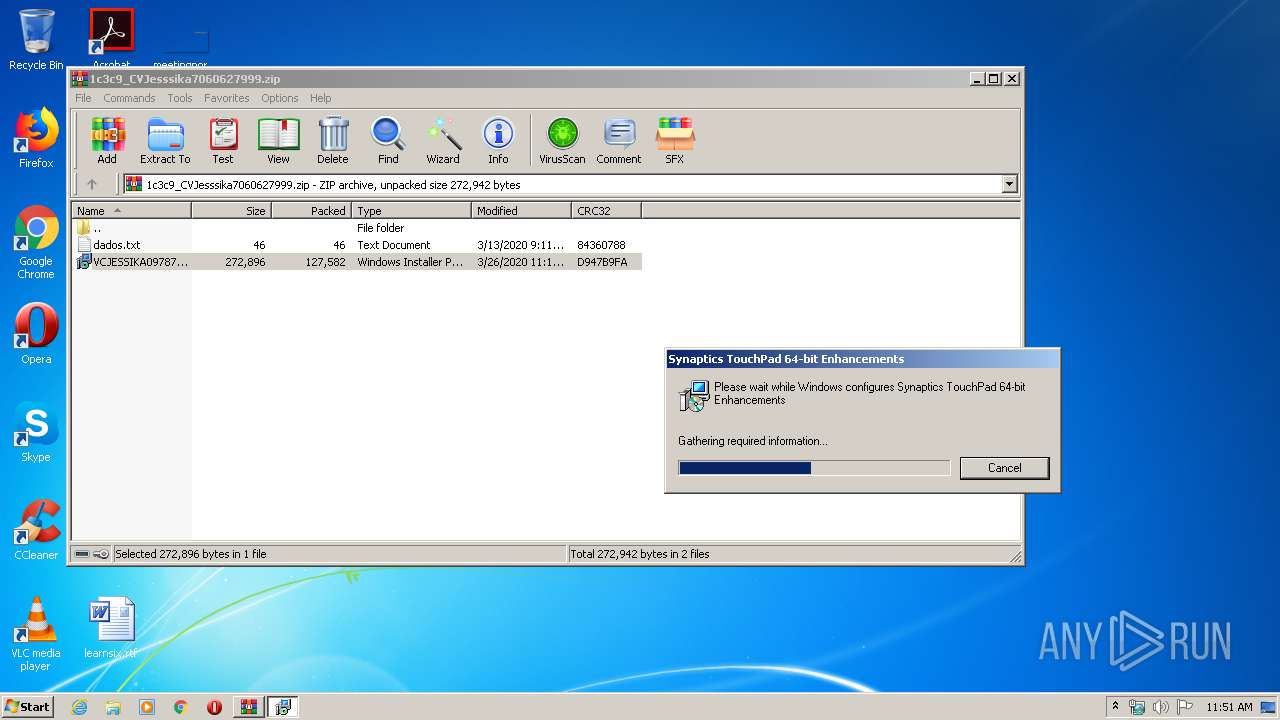
- WinRAR.exe (PID: 2864)
- MsiExec.exe (PID: 2704)
- msiexec.exe (PID: 2936)
Reads Internet Cache Settings
- MsiExec.exe (PID: 2704)
Starts Microsoft Installer
- WinRAR.exe (PID: 2864)
Reads Environment values
- NPIE.EXE (PID: 3456)
Uses REG.EXE to modify Windows registry
- MsiExec.exe (PID: 2704)
INFO
Application launched itself
- msiexec.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:03:26 23:16:02 |
| ZipCRC: | 0xd947b9fa |
| ZipCompressedSize: | 127582 |
| ZipUncompressedSize: | 272896 |
| ZipFileName: | VCJESSIKA097878.msi |
Total processes
40
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2492 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rar$EXa2864.18880\VCJESSIKA097878.msi" | C:\Windows\System32\msiexec.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2704 | C:\Windows\system32\MsiExec.exe -Embedding 0527538C5457464D9DBB5FD922AEE1A4 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | "C:\Windows\System32\reg.exe" add "HKCU\software\Microsoft\Windows\CurrentVersion\RunOnce" /v NPIE /t reg_sz /d C:\Users\admin\Documents\NPIE\NPIE.EXE | C:\Windows\System32\reg.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\1c3c9_CVJesssika7060627999.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2936 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3456 | "C:\Users\admin\Documents\NPIE\NPIE.EXE" | C:\Users\admin\Documents\NPIE\NPIE.EXE | MsiExec.exe | ||||||||||||
User: admin Company: Avira Operations GmbH & Co. KG Integrity Level: MEDIUM Description: Avira Exit code: 0 Version: 1.2.144.30330 Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 628
Read events
1 576
Write events
40
Delete events
12
Modification events
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\1c3c9_CVJesssika7060627999.zip | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msimsg.dll,-34 |
Value: Windows Installer Package | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
5
Text files
19
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | msiexec.exe | C:\Windows\Installer\MSI8CC7.tmp | — | |
MD5:— | SHA256:— | |||
| 2936 | msiexec.exe | C:\Windows\Installer\MSI8D36.tmp | — | |
MD5:— | SHA256:— | |||
| 2936 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF46BF722D02CC1BD6.TMP | — | |
MD5:— | SHA256:— | |||
| 2704 | MsiExec.exe | C:\Users\admin\Documents\NPIE\Avira.OE.NativeCore.dll | — | |
MD5:— | SHA256:— | |||
| 2936 | msiexec.exe | C:\Windows\Installer\a68c2d.ipi | binary | |
MD5:— | SHA256:— | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2864.18880\dados.txt | text | |
MD5:— | SHA256:— | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2864.18880\VCJESSIKA097878.msi | executable | |
MD5:— | SHA256:— | |||
| 2704 | MsiExec.exe | C:\Users\admin\Documents\NPIE_NPIE_NPIE.zip | compressed | |
MD5:— | SHA256:— | |||
| 2936 | msiexec.exe | C:\Windows\Installer\a68c2b.msi | executable | |
MD5:— | SHA256:— | |||
| 2704 | MsiExec.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\video2[1].tar | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3456 | NPIE.EXE | POST | — | 5.57.226.202:80 | http://novamultimidea.webcindario.com/covid19/ | ES | — | — | malicious |
2704 | MsiExec.exe | GET | 200 | 187.17.111.35:80 | http://moggiempilhadeiras.com.br/js/video2.Tar | BR | compressed | 13.0 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3456 | NPIE.EXE | 5.57.226.202:80 | novamultimidea.webcindario.com | ServiHosting Networks S.L. | ES | malicious |
2704 | MsiExec.exe | 187.17.111.35:80 | moggiempilhadeiras.com.br | Universo Online S.A. | BR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
moggiempilhadeiras.com.br |
| malicious |
novamultimidea.webcindario.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3456 | NPIE.EXE | Potentially Bad Traffic | ET INFO Suspicious POST Request with Possible COVID-19 URI M1 |
1 ETPRO signatures available at the full report