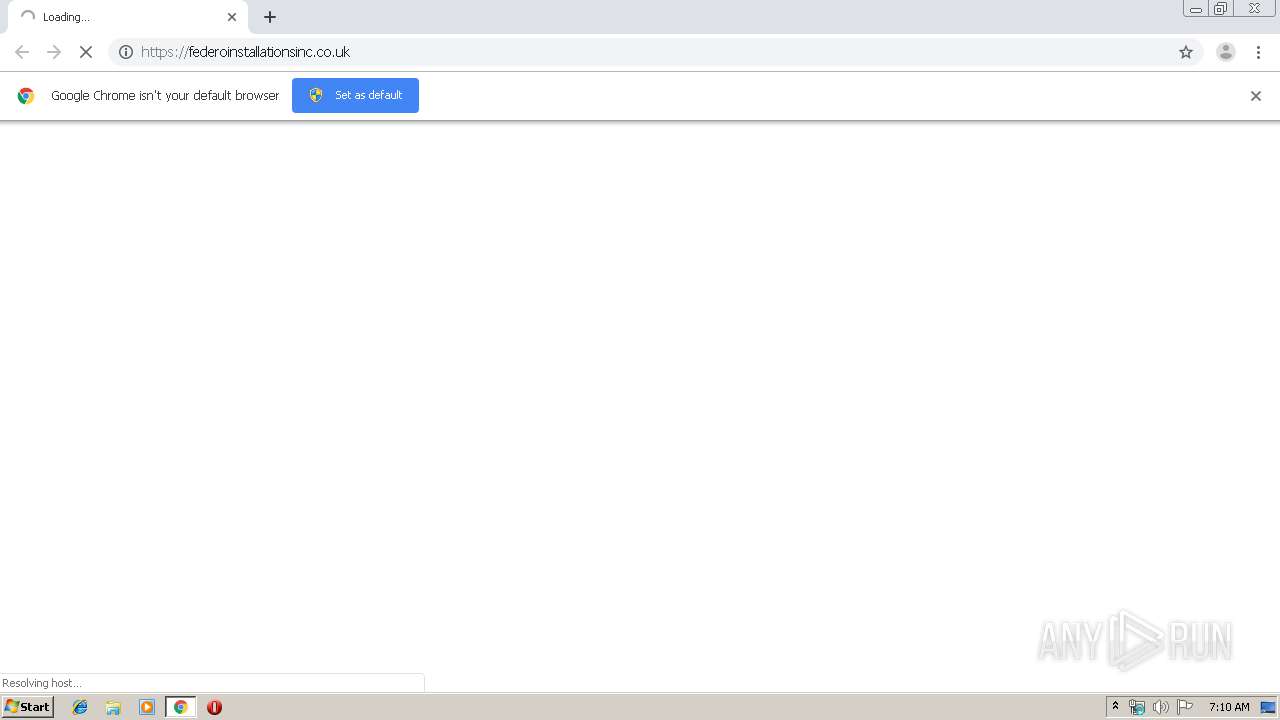
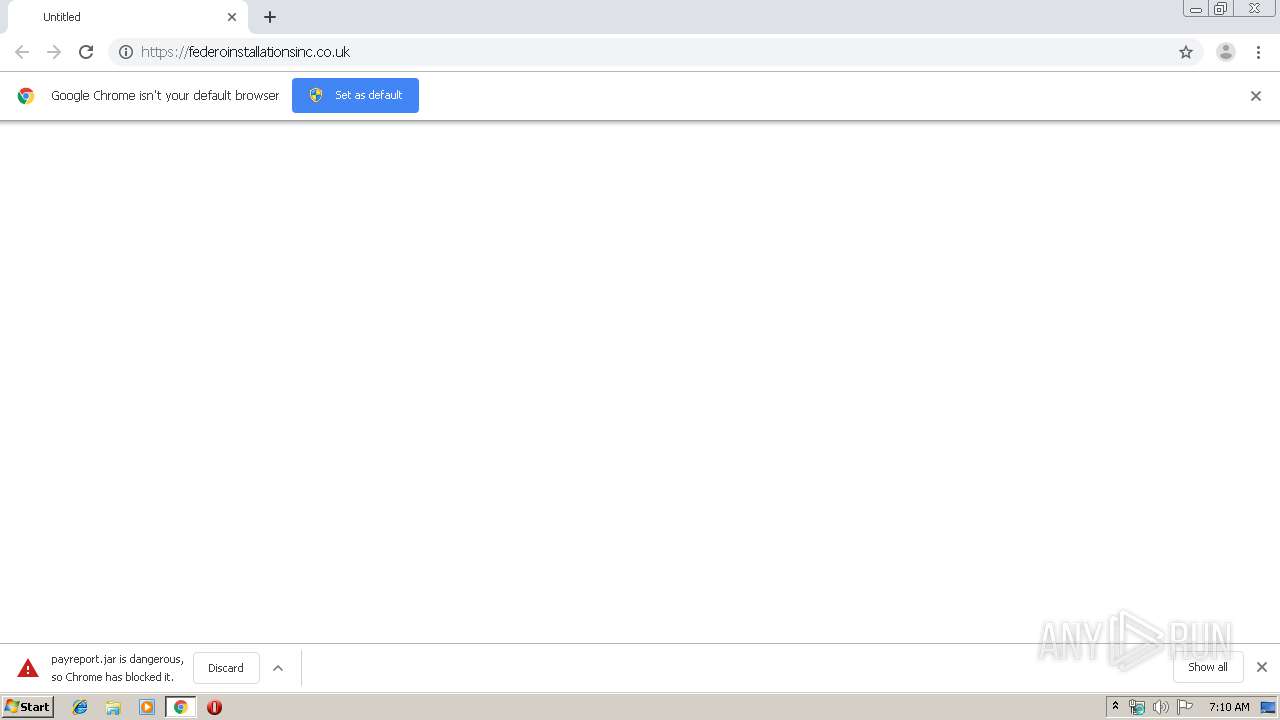
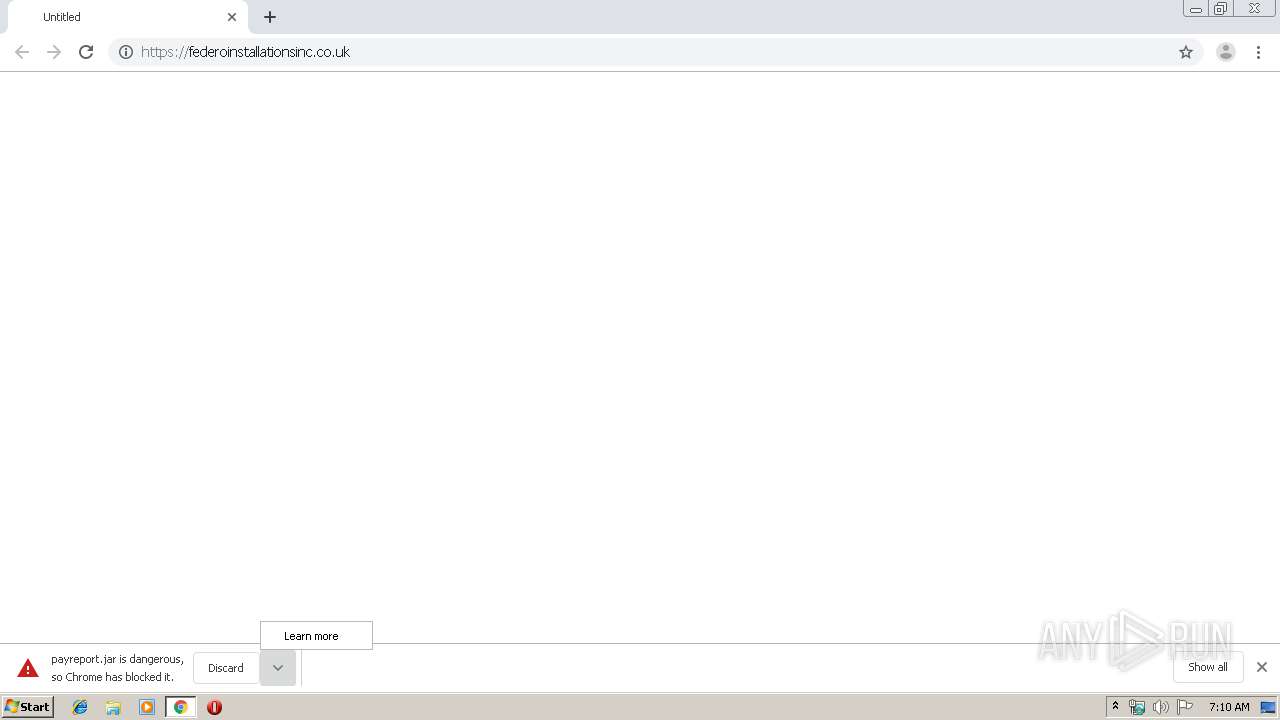
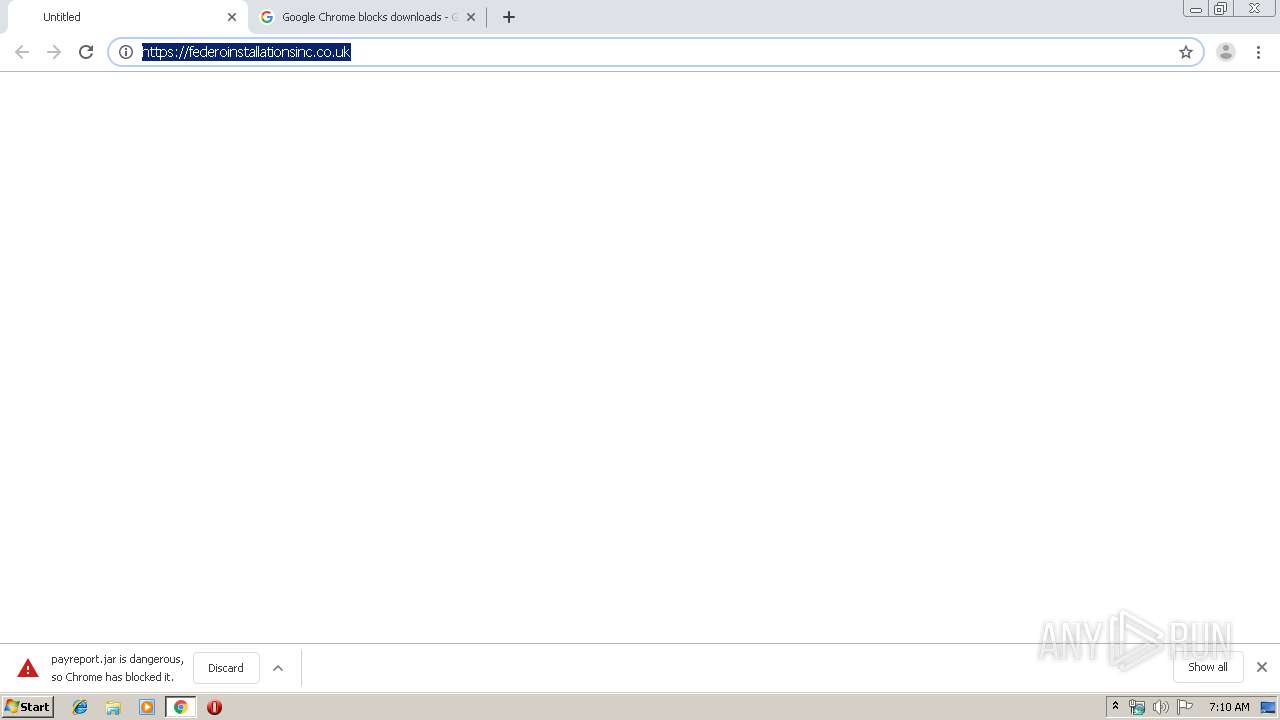
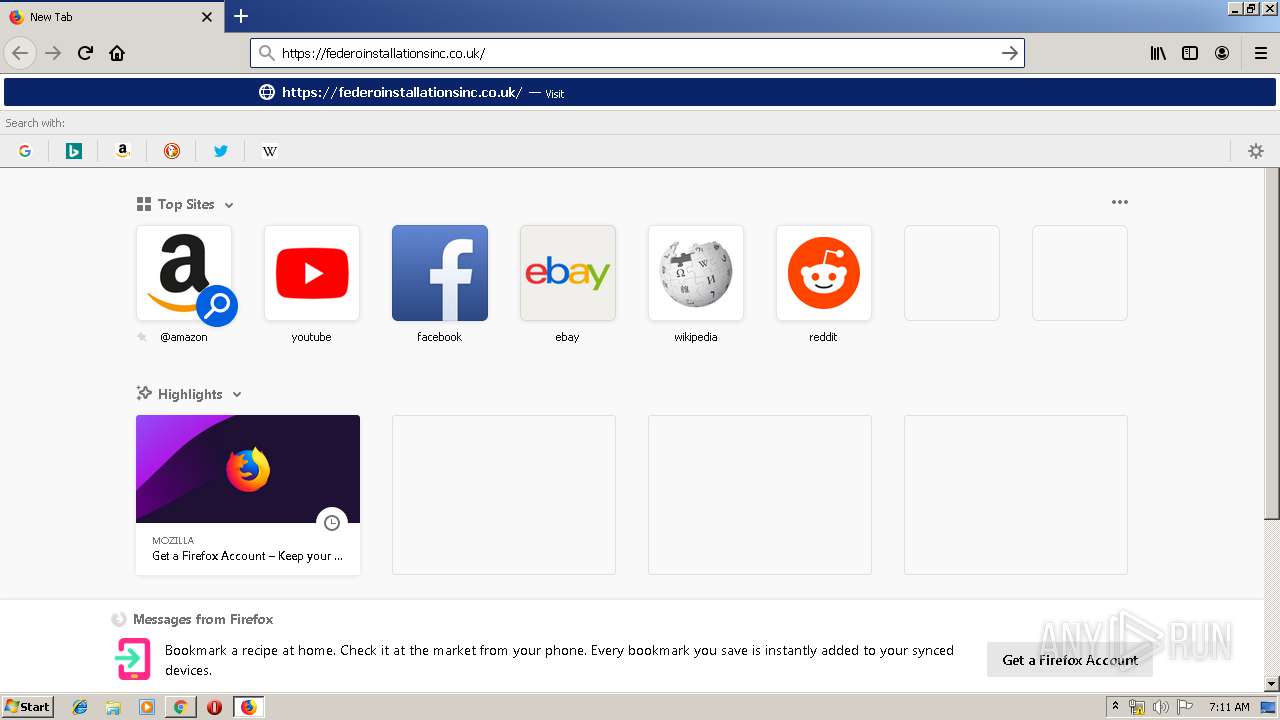
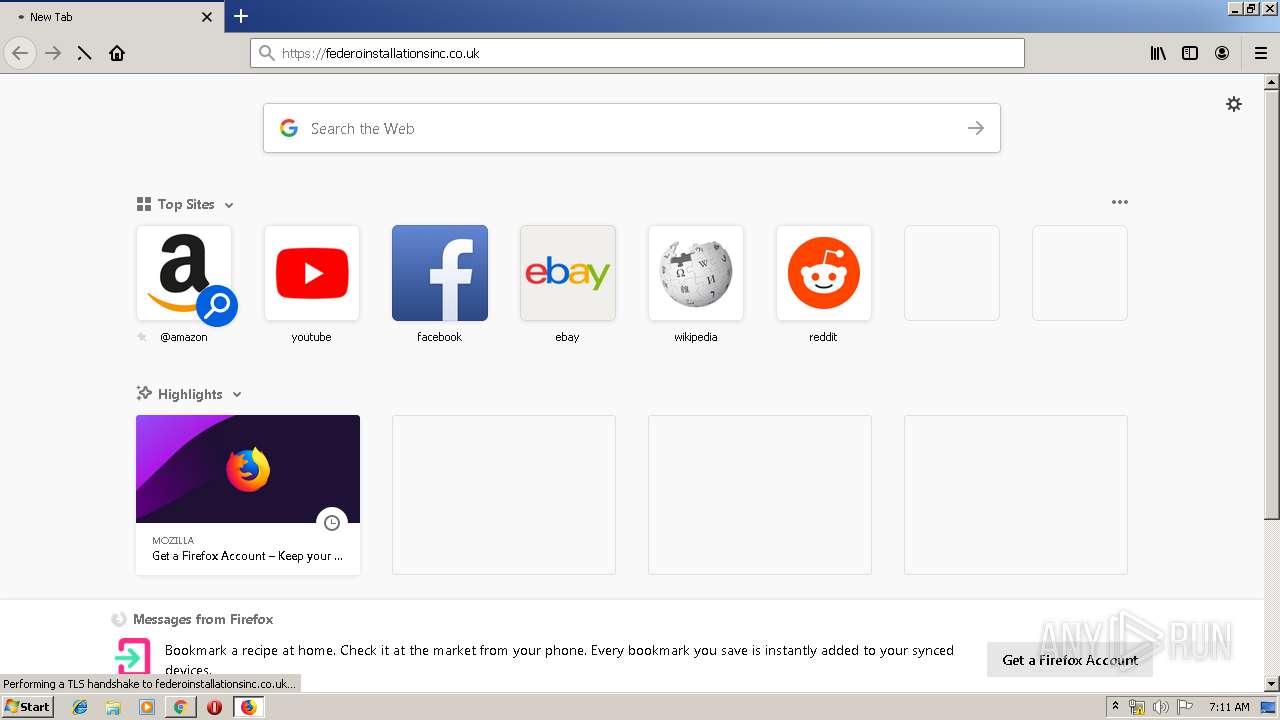
| URL: | https://federoinstallationsinc.co.uk/ |
| Full analysis: | https://app.any.run/tasks/d4090a4c-21bf-4cb1-8188-fbc6d98ab200 |
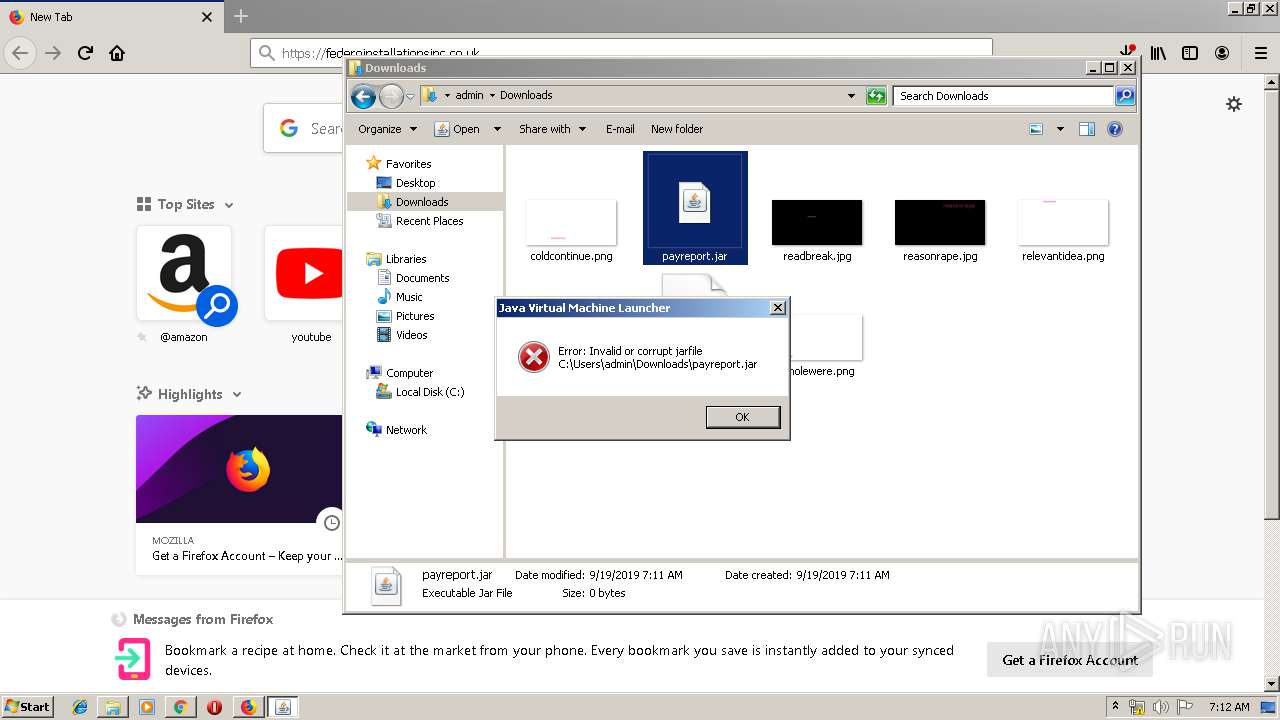
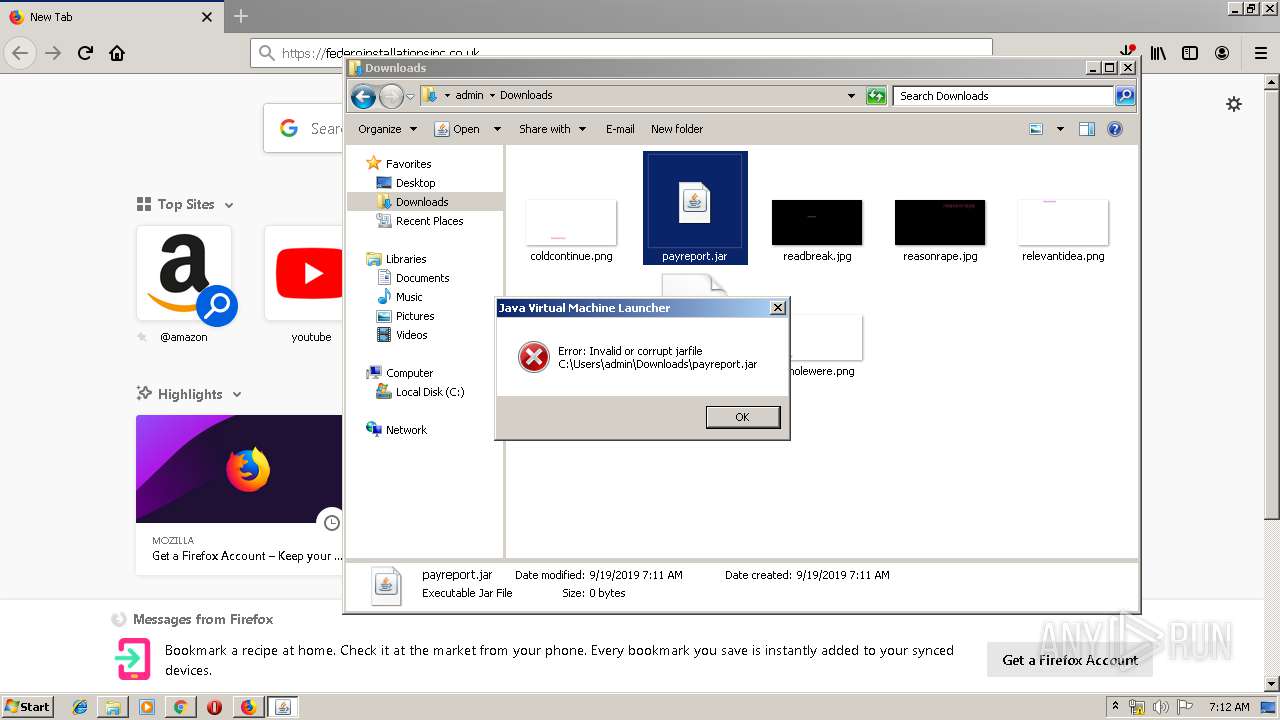
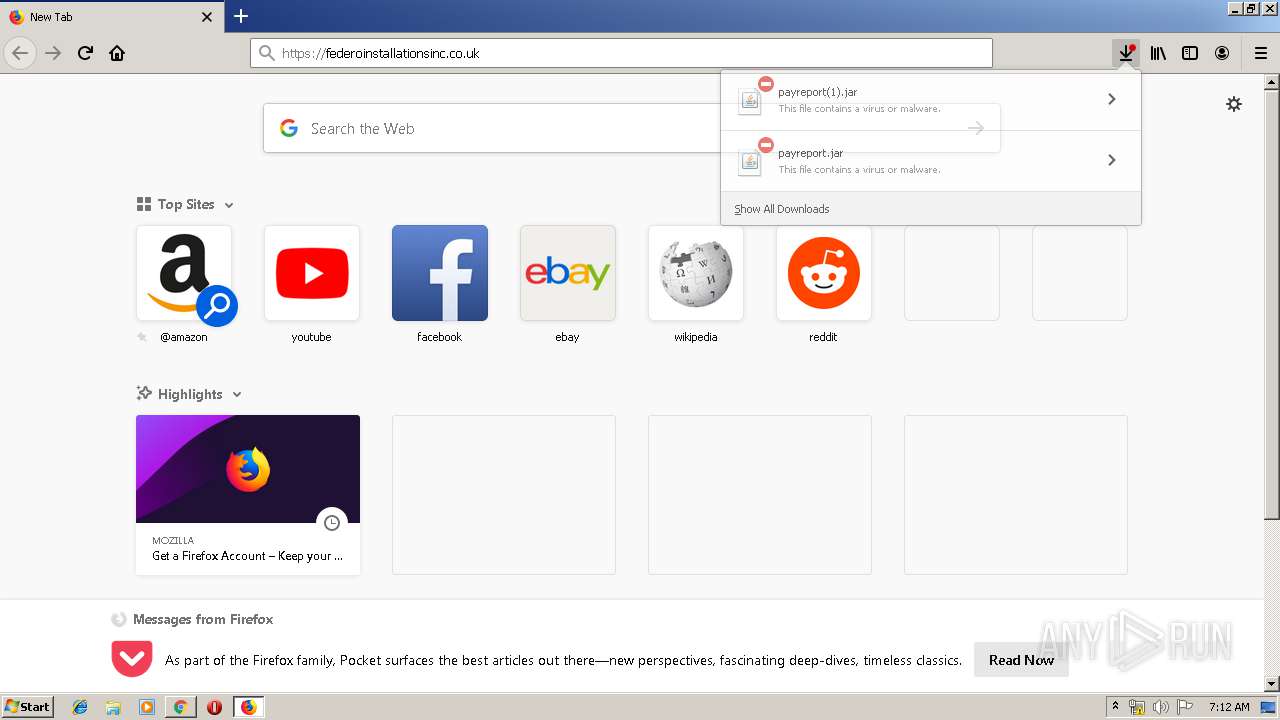
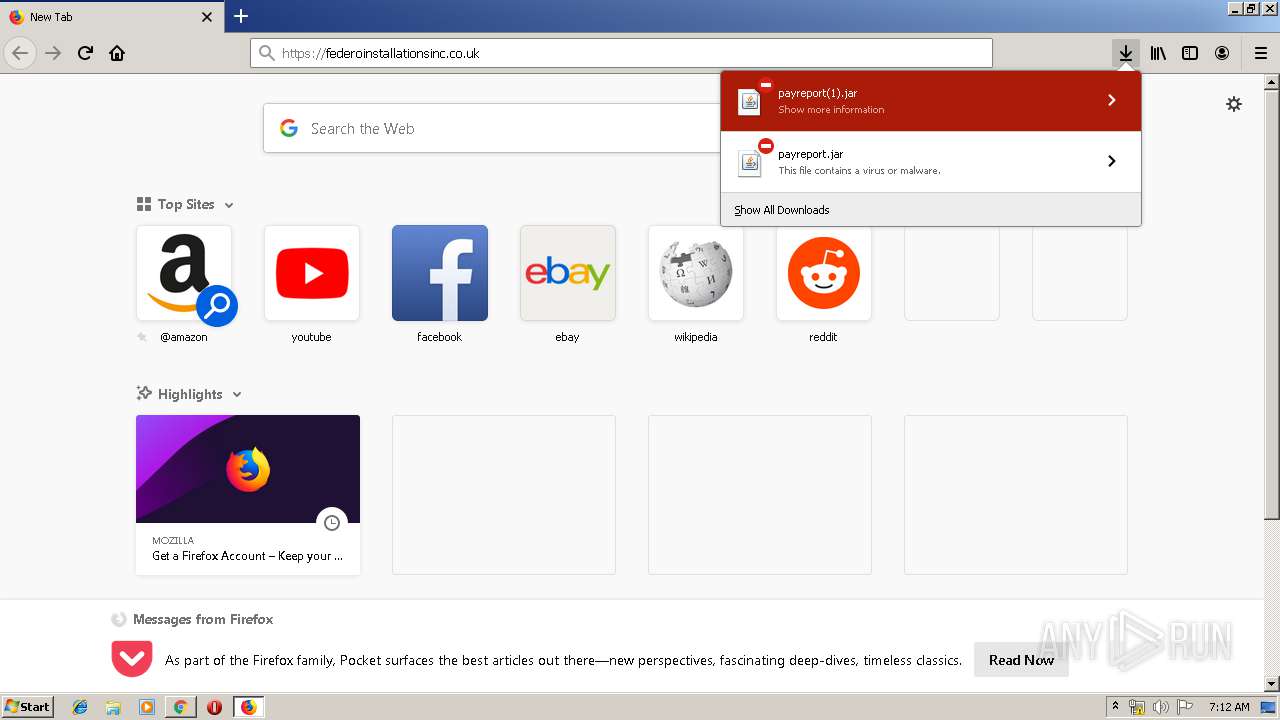
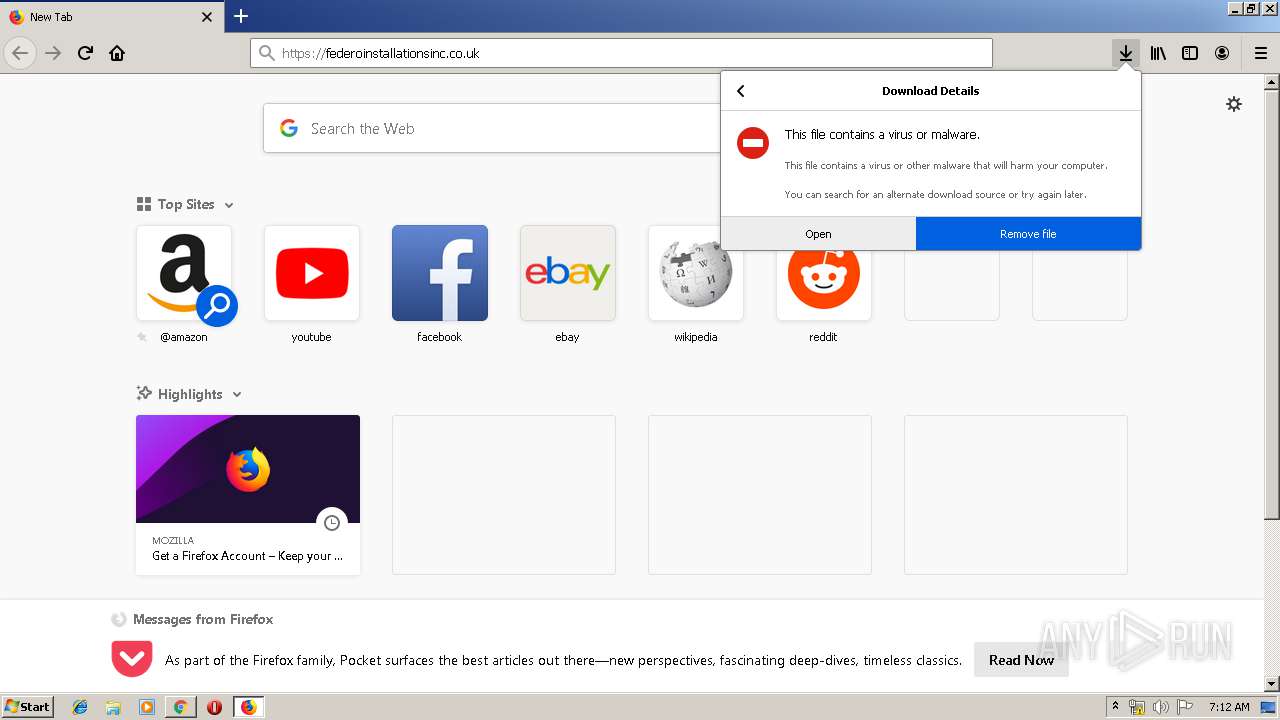
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | September 19, 2019, 06:10:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 98CE108B8612BC3A7B97862CEBB94A58 |
| SHA1: | BA138C2E40B09251020CB6121E9BEC2430B5A649 |
| SHA256: | 13203939C59C15AC3B3D60E1AD261F28EEFC7288CF742CF8642A45AA16240795 |
| SSDEEP: | 3:N8IRLidFK:2IRLidFK |
MALICIOUS
Loads dropped or rewritten executable
- iexplore.exe (PID: 3760)
- javaw.exe (PID: 564)
- svchost.exe (PID: 824)
- explorer.exe (PID: 276)
- java.exe (PID: 2840)
- firefox.exe (PID: 2160)
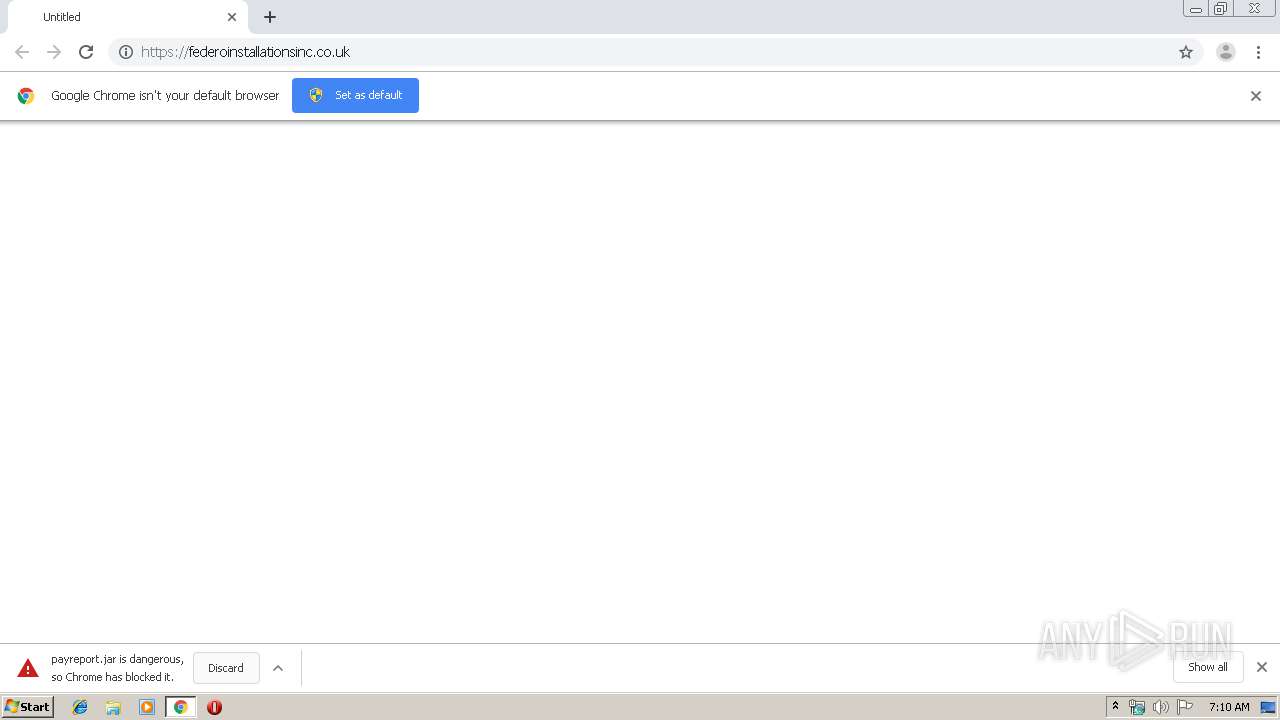
AdWind was detected
- java.exe (PID: 2840)
Application was dropped or rewritten from another process
- java.exe (PID: 2840)
- javaw.exe (PID: 2692)
- javaw.exe (PID: 3796)
- javaw.exe (PID: 564)
SUSPICIOUS
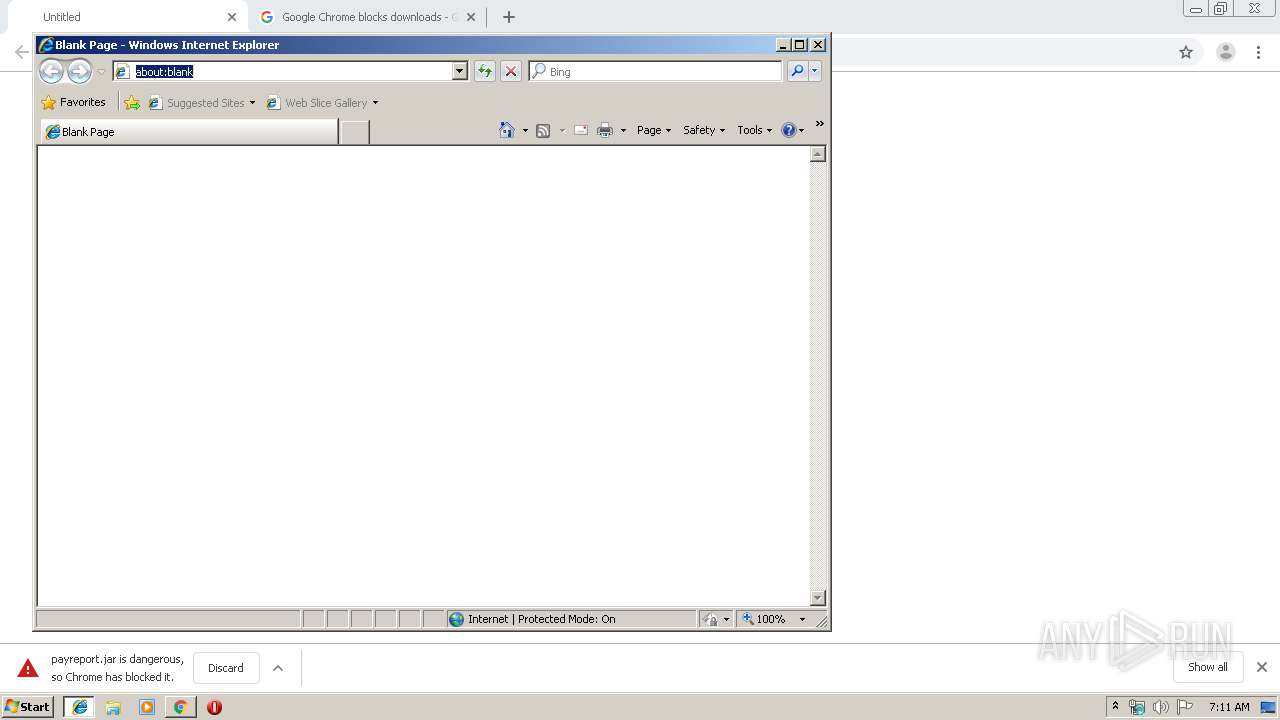
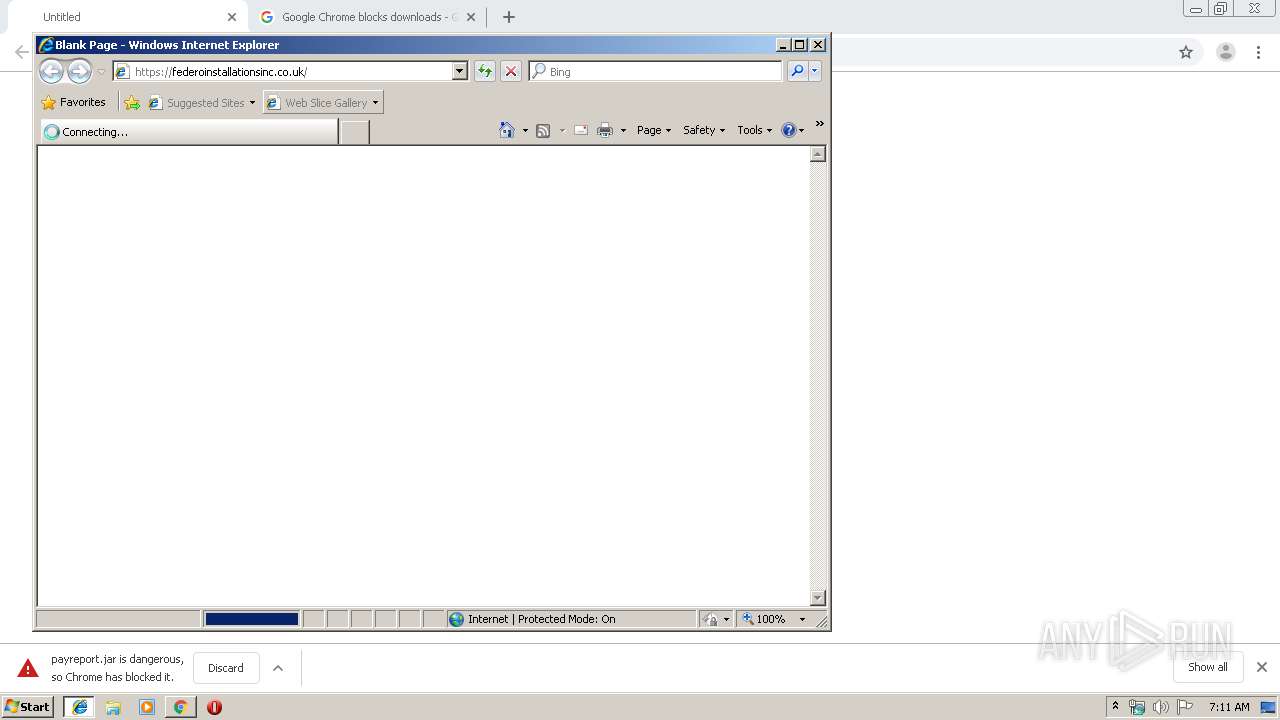
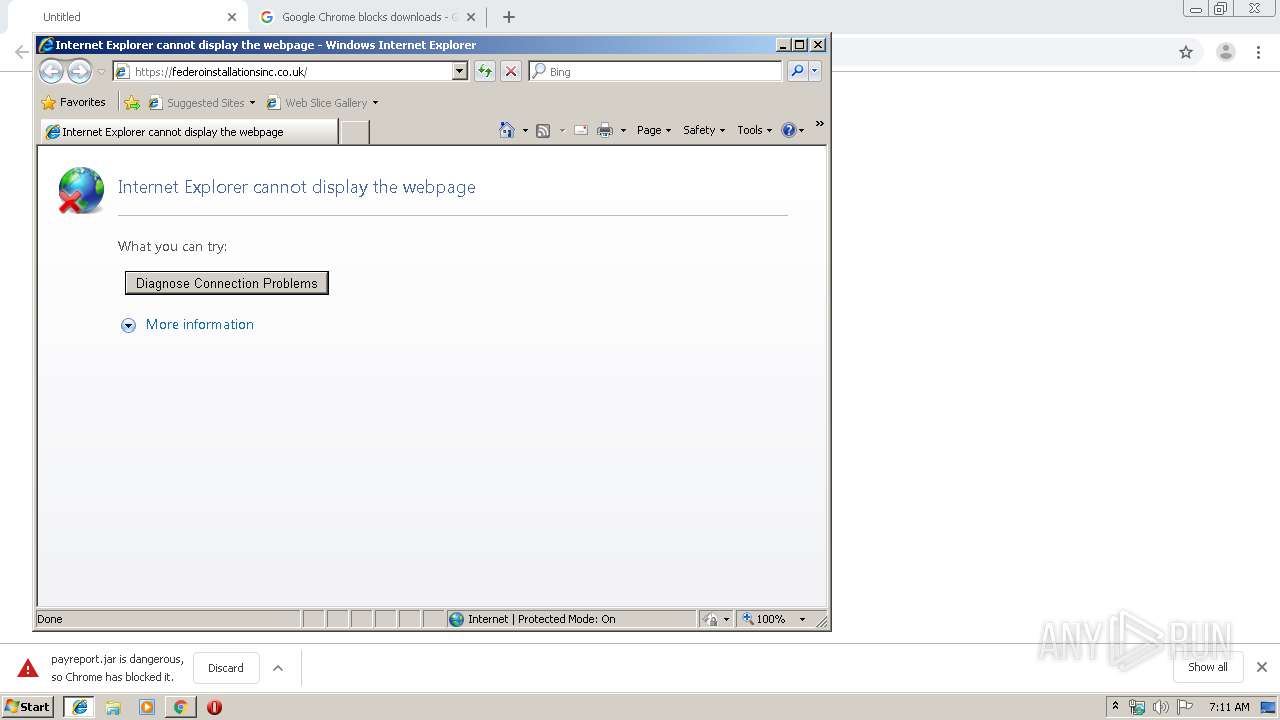
Starts Internet Explorer
- explorer.exe (PID: 276)
Executes JAVA applets
- explorer.exe (PID: 276)
- firefox.exe (PID: 2160)
- javaw.exe (PID: 564)
Creates files in the program directory
- firefox.exe (PID: 2160)
Creates files in the user directory
- explorer.exe (PID: 276)
- javaw.exe (PID: 564)
- xcopy.exe (PID: 1520)
Executes scripts
- cmd.exe (PID: 2284)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 2224)
- cmd.exe (PID: 2600)
Reads Internet Cache Settings
- explorer.exe (PID: 276)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 564)
- java.exe (PID: 2840)
Executable content was dropped or overwritten
- xcopy.exe (PID: 1520)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2892)
INFO
Application launched itself
- chrome.exe (PID: 2892)
- firefox.exe (PID: 2160)
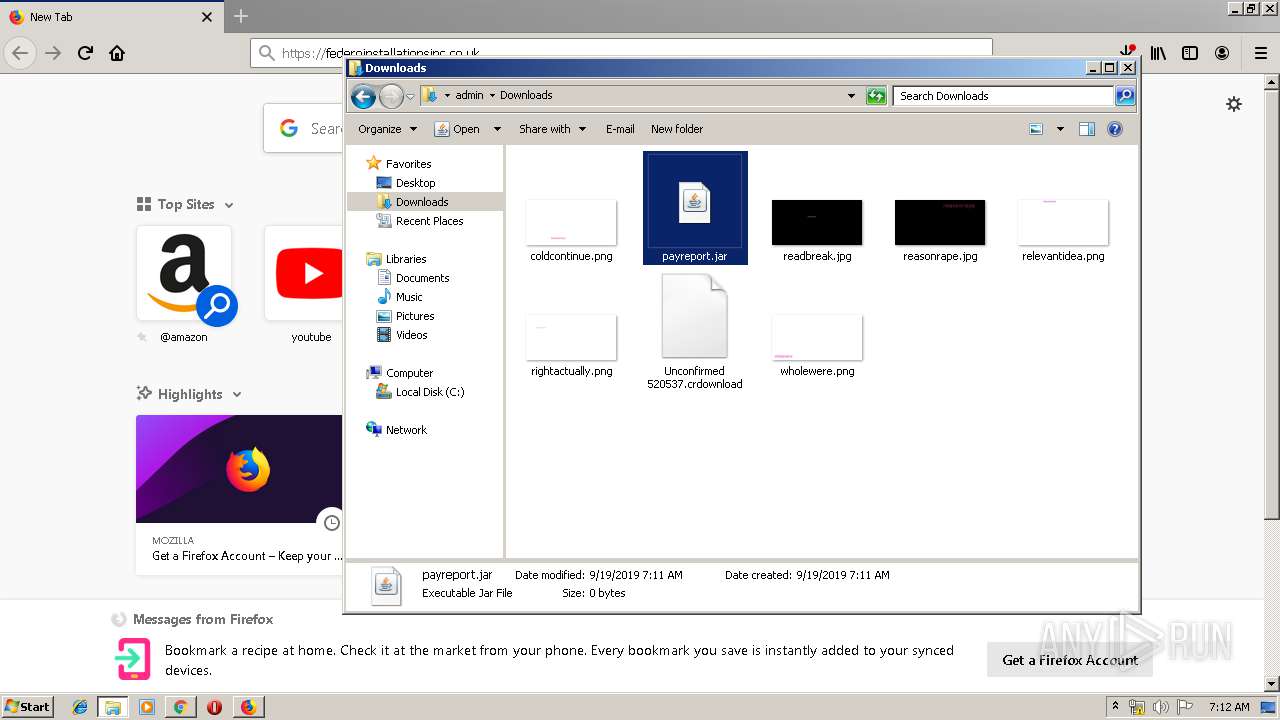
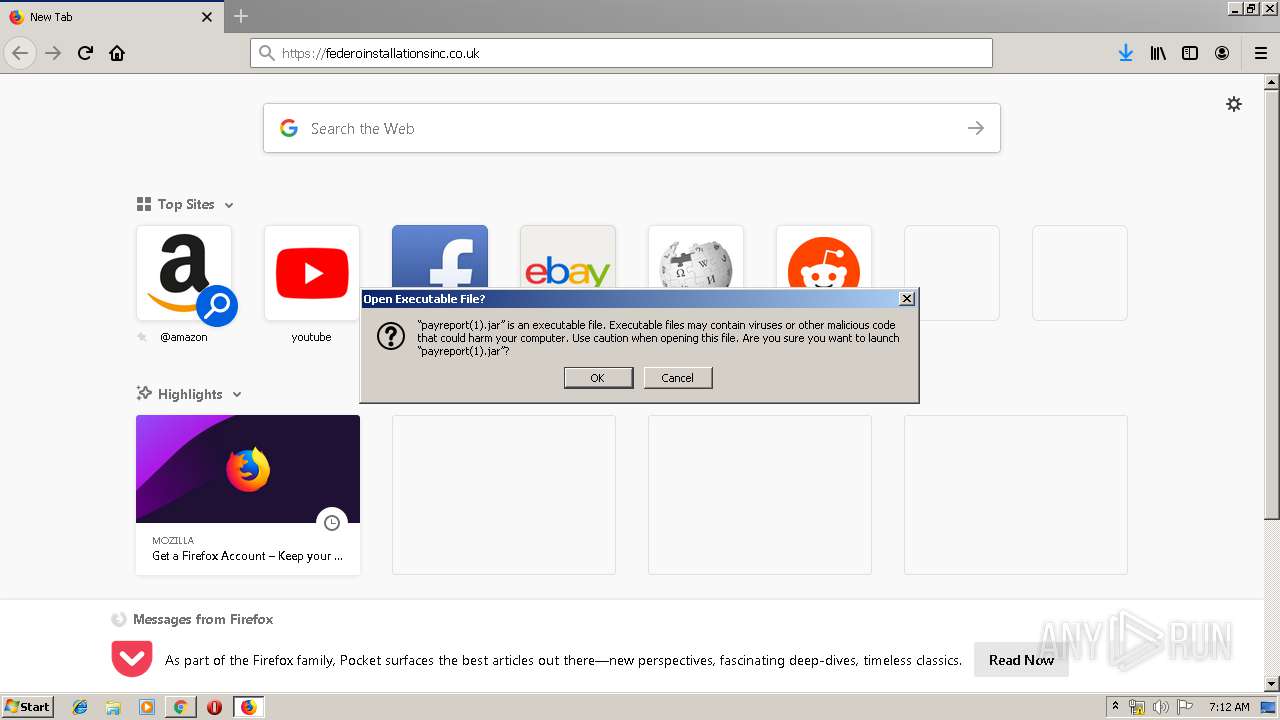
Manual execution by user
- iexplore.exe (PID: 3548)
- explorer.exe (PID: 2972)
- javaw.exe (PID: 3796)
- firefox.exe (PID: 2704)
- javaw.exe (PID: 2692)
Reads the hosts file
- chrome.exe (PID: 2200)
- chrome.exe (PID: 2892)
Reads Internet Cache Settings
- iexplore.exe (PID: 3760)
Changes internet zones settings
- iexplore.exe (PID: 3548)
Reads settings of System Certificates
- chrome.exe (PID: 2200)
Reads internet explorer settings
- iexplore.exe (PID: 3760)
Creates files in the user directory
- firefox.exe (PID: 2160)
- iexplore.exe (PID: 3760)
- iexplore.exe (PID: 3548)
Reads CPU info
- firefox.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
48
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive5022320596047777397.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17828327642524778717,1700573805475035910,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3725050850336115425 --mojo-platform-channel-handle=4028 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
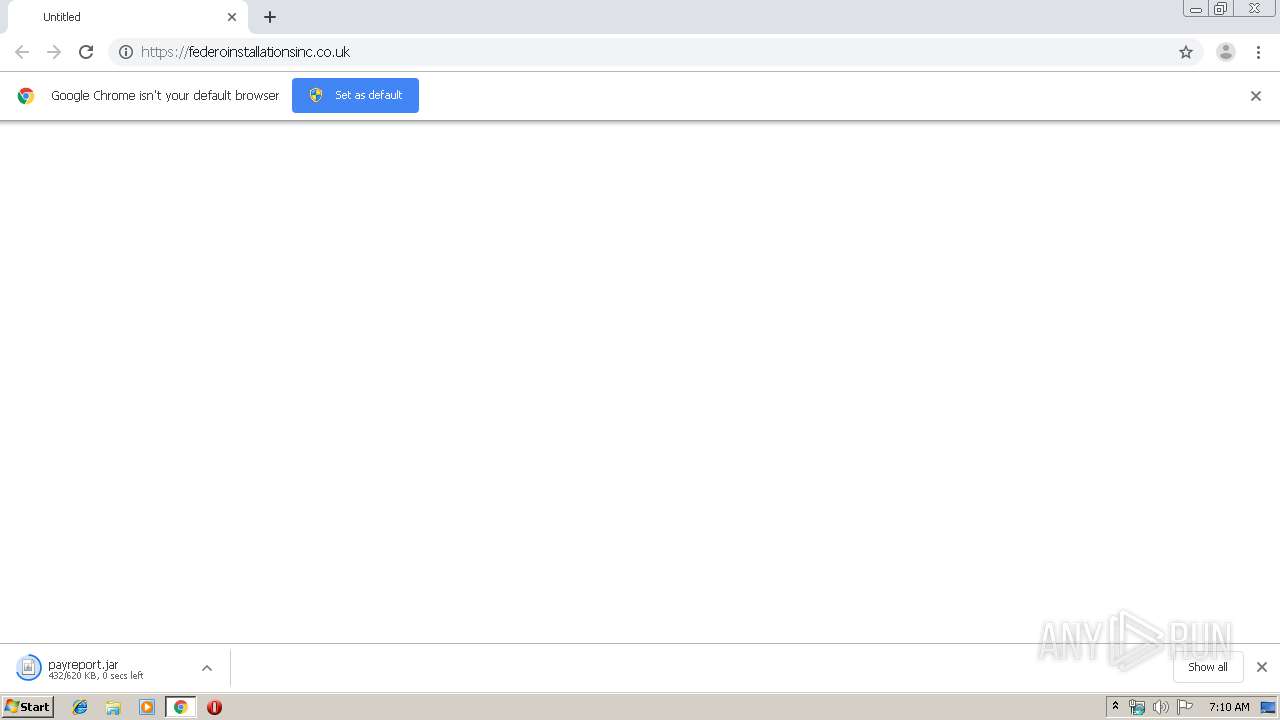
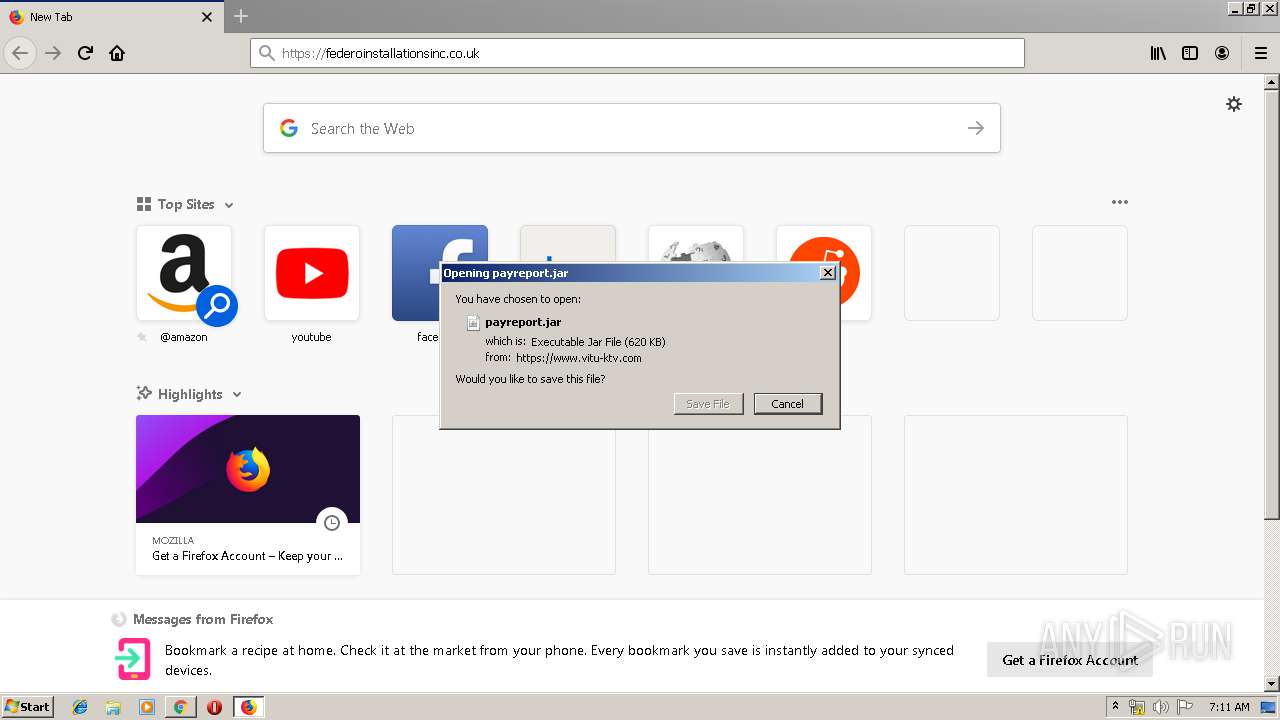
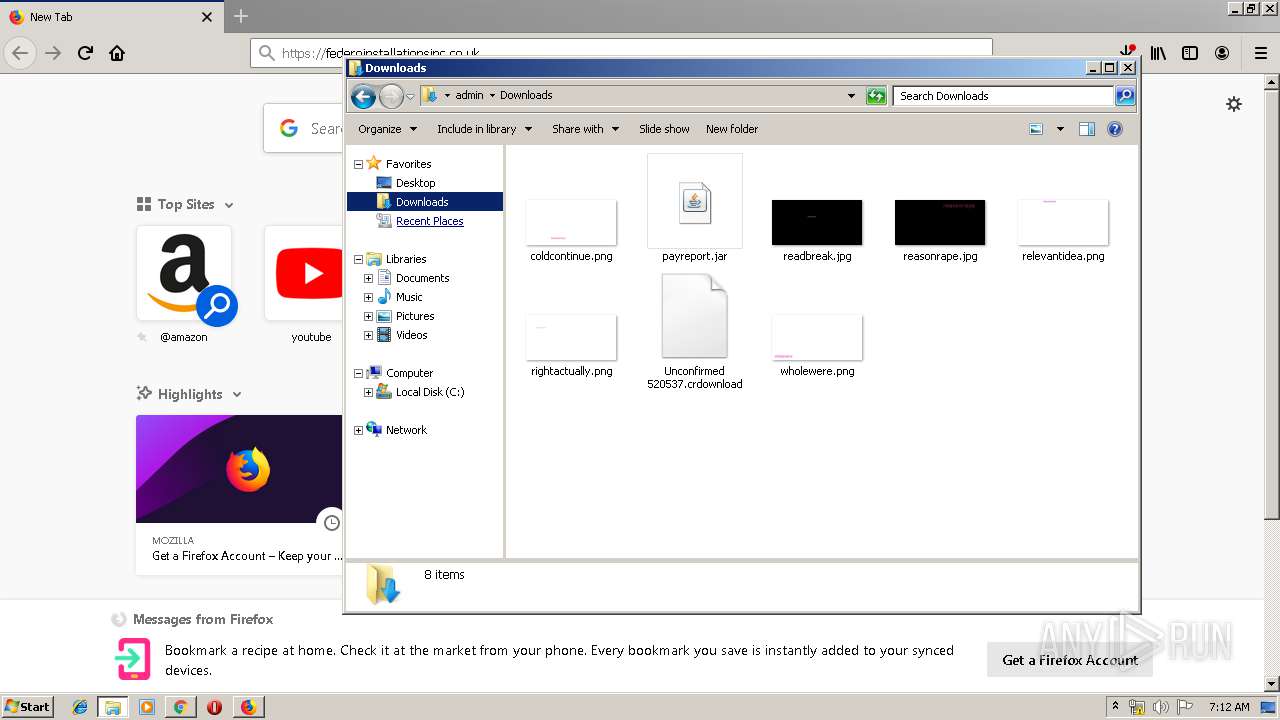
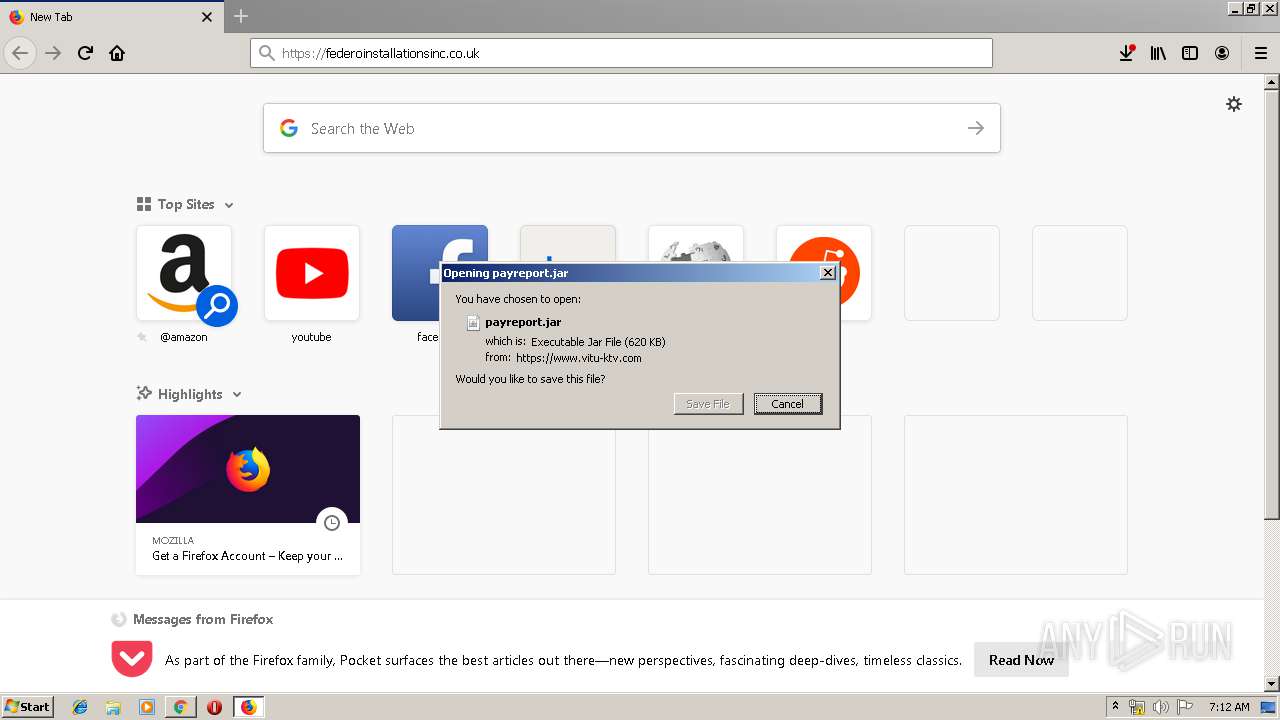
| 564 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\payreport(1).jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | firefox.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 824 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive6591653877261809564.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2160.0.274372410\2071777879" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2160 "\\.\pipe\gecko-crash-server-pipe.2160" 1180 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17828327642524778717,1700573805475035910,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5091700330456245311 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2160.3.1793964364\807910450" -childID 1 -isForBrowser -prefsHandle 1672 -prefMapHandle 1328 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2160 "\\.\pipe\gecko-crash-server-pipe.2160" 1752 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17828327642524778717,1700573805475035910,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14488948822226623577 --mojo-platform-channel-handle=2056 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 931
Read events
2 604
Write events
321
Delete events
6
Modification events
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2892-13213347021964500 |
Value: 259 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
115
Suspicious files
108
Text files
291
Unknown types
78
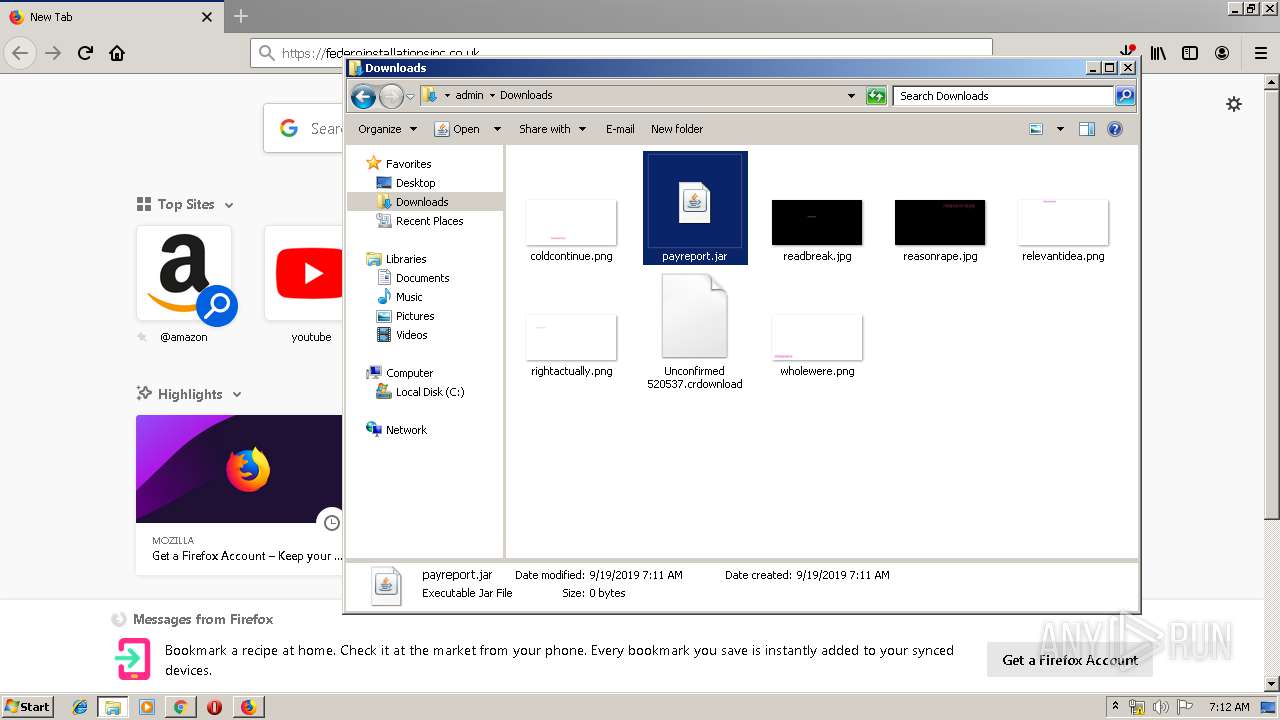
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dbddb775-3782-4914-8371-aeae1350e024.tmp | — | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF168dbe.TMP | text | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF168dcd.TMP | text | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF168dbe.TMP | text | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
61
DNS requests
109
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2160 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2160 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2160 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2160 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2200 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2160 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2160 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
3548 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2200 | chrome.exe | GET | 200 | 172.217.133.135:80 | http://r2---sn-hpa7znsd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.128.27.133&mm=28&mn=sn-hpa7znsd&ms=nvh&mt=1568873539&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2160 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2200 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2200 | chrome.exe | 146.66.104.246:443 | federoinstallationsinc.co.uk | — | US | unknown |
2200 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2200 | chrome.exe | 194.31.53.109:443 | www.vitu-ktv.com | — | — | unknown |
2200 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2200 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
2200 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
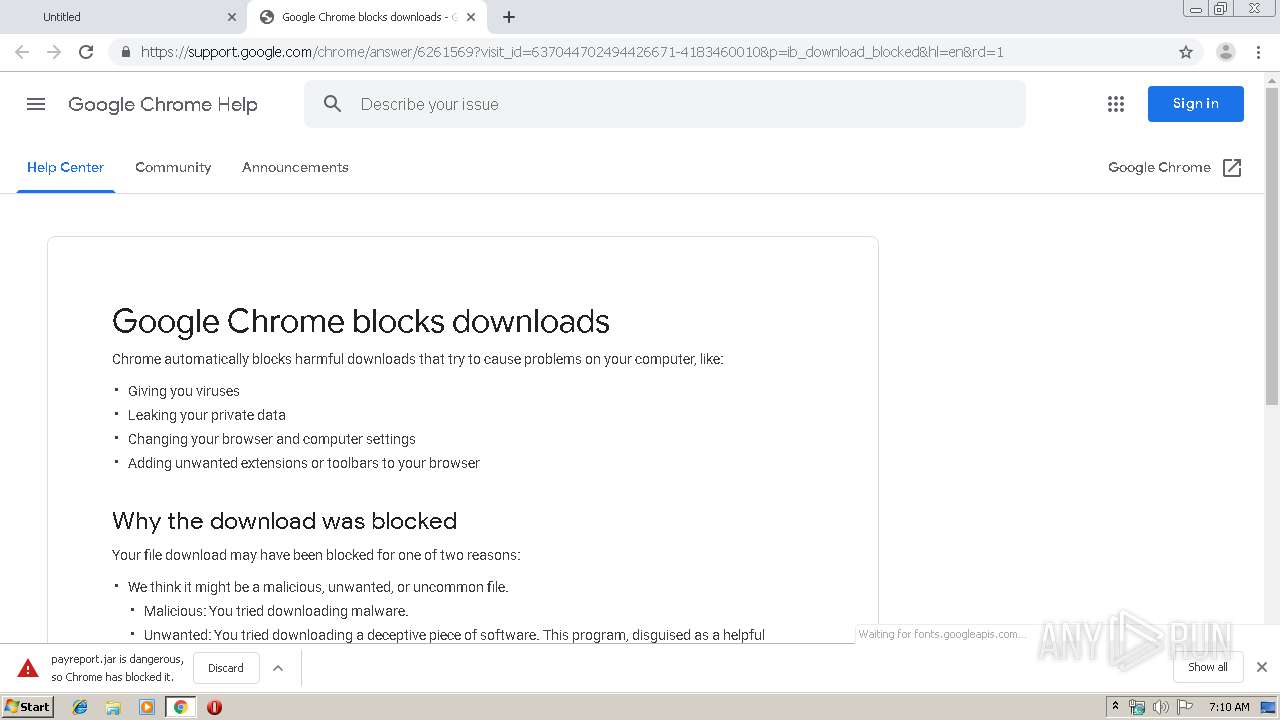
2200 | chrome.exe | 172.217.23.142:443 | support.google.com | Google Inc. | US | whitelisted |
2200 | chrome.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2200 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
federoinstallationsinc.co.uk |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.vitu-ktv.com |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
support.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |