| File name: | jjsploit.exe |
| Full analysis: | https://app.any.run/tasks/4bfb3bc5-b947-4ba0-9b41-72adacdc51ec |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | June 08, 2025, 23:47:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 8E1273328063201E1A3747D7B70B6573 |
| SHA1: | 69CBD5820BDF3298F4D0ABDE857BB9C4F887ED1F |
| SHA256: | 1309338682131C954F14699359424EC3CD3C4D1531ABE6E338DAE1B91B11D377 |
| SSDEEP: | 6144:KjBiMrq81F0+7JK0N7njjYyllLxBS6Pvhrd6vrJ4f94R2H7K7Gfm14hb+9s64DTz:S7jUyllLxAsvCvw4R2HVei64aG |
MALICIOUS
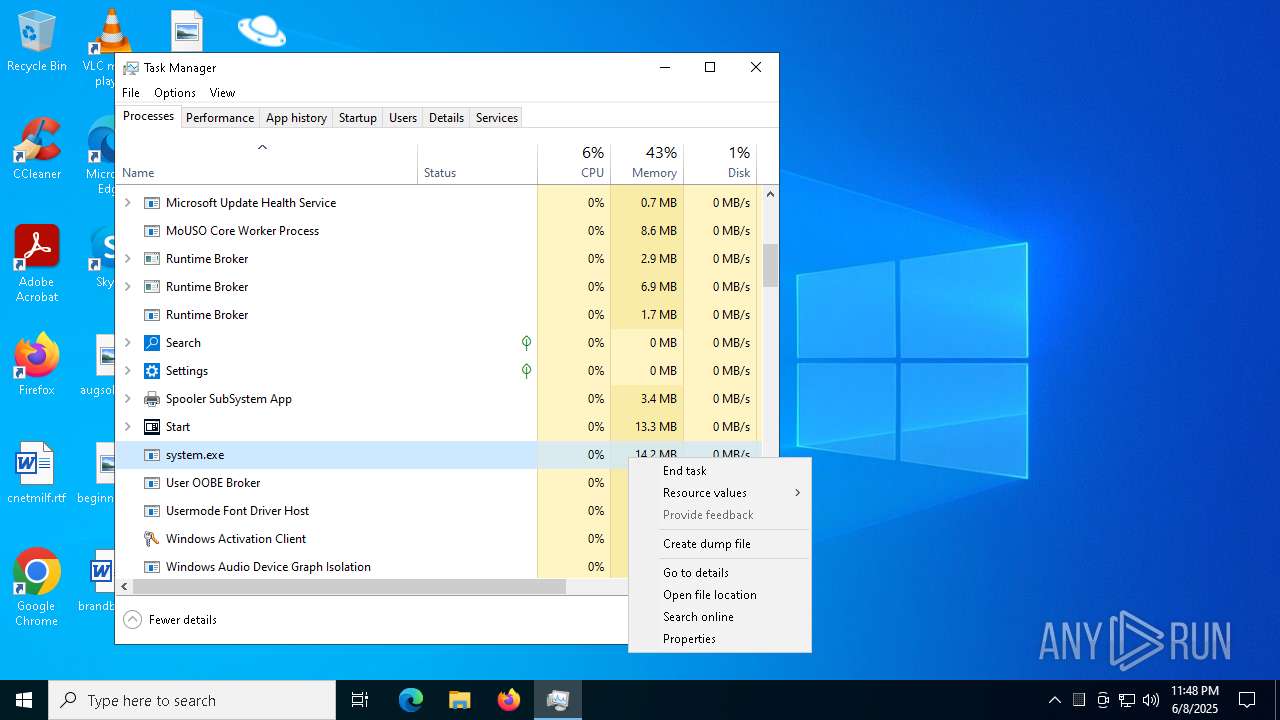
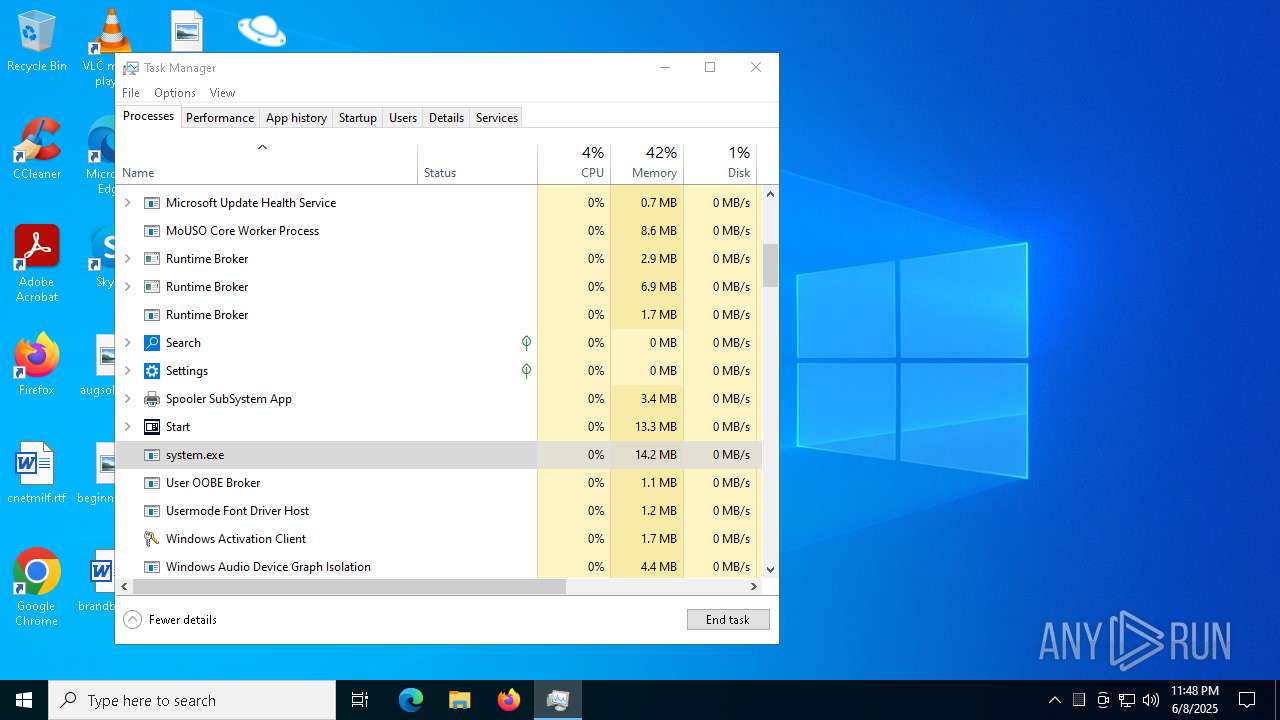
AGENTTESLA has been detected (SURICATA)
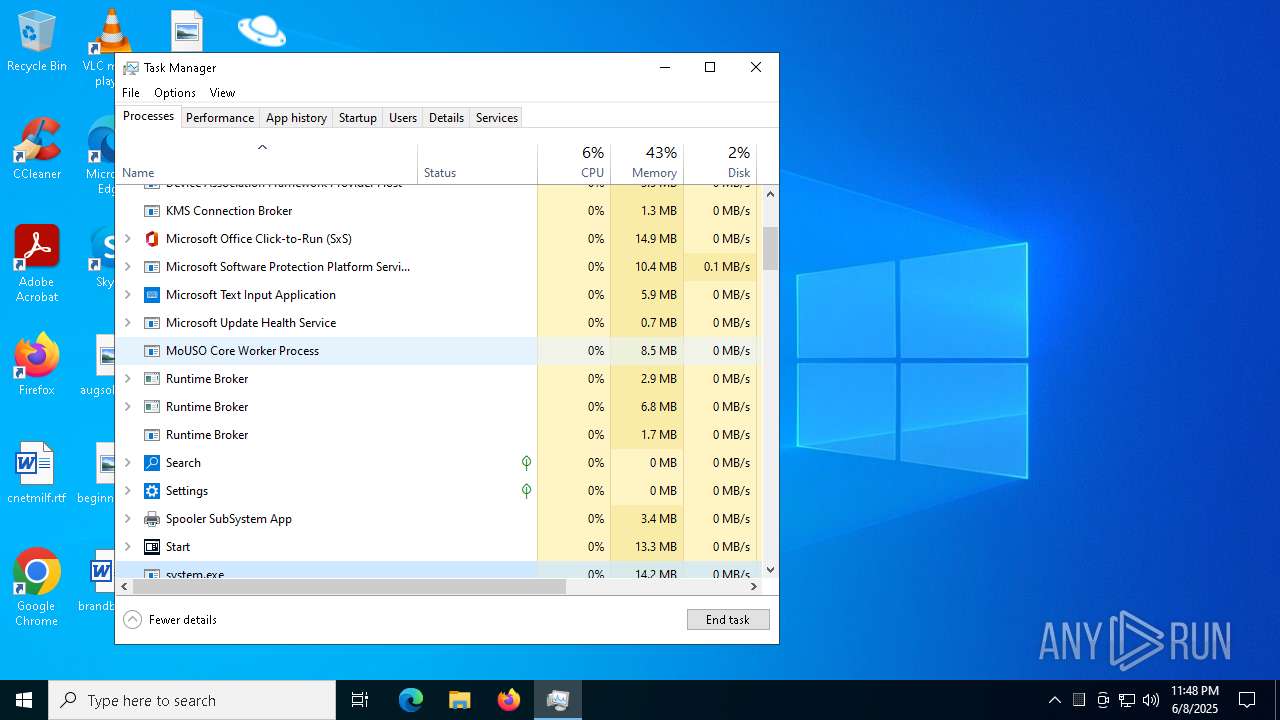
- system.exe (PID: 6368)
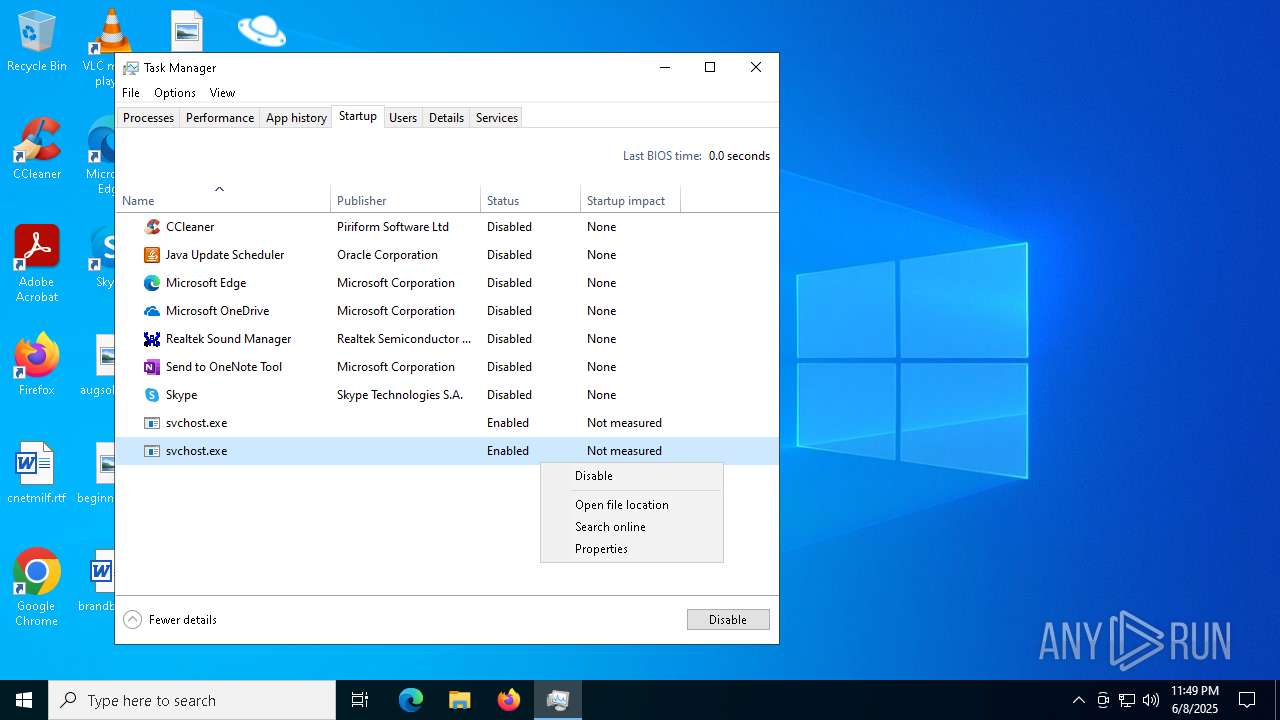
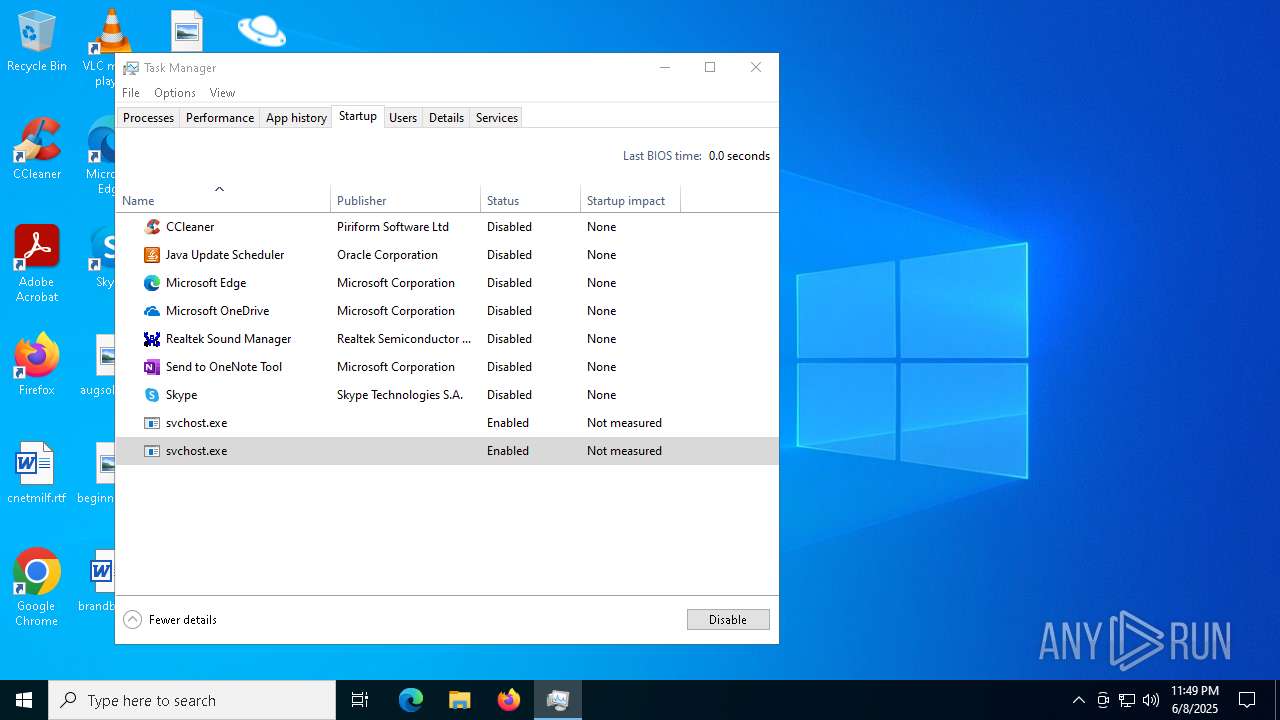
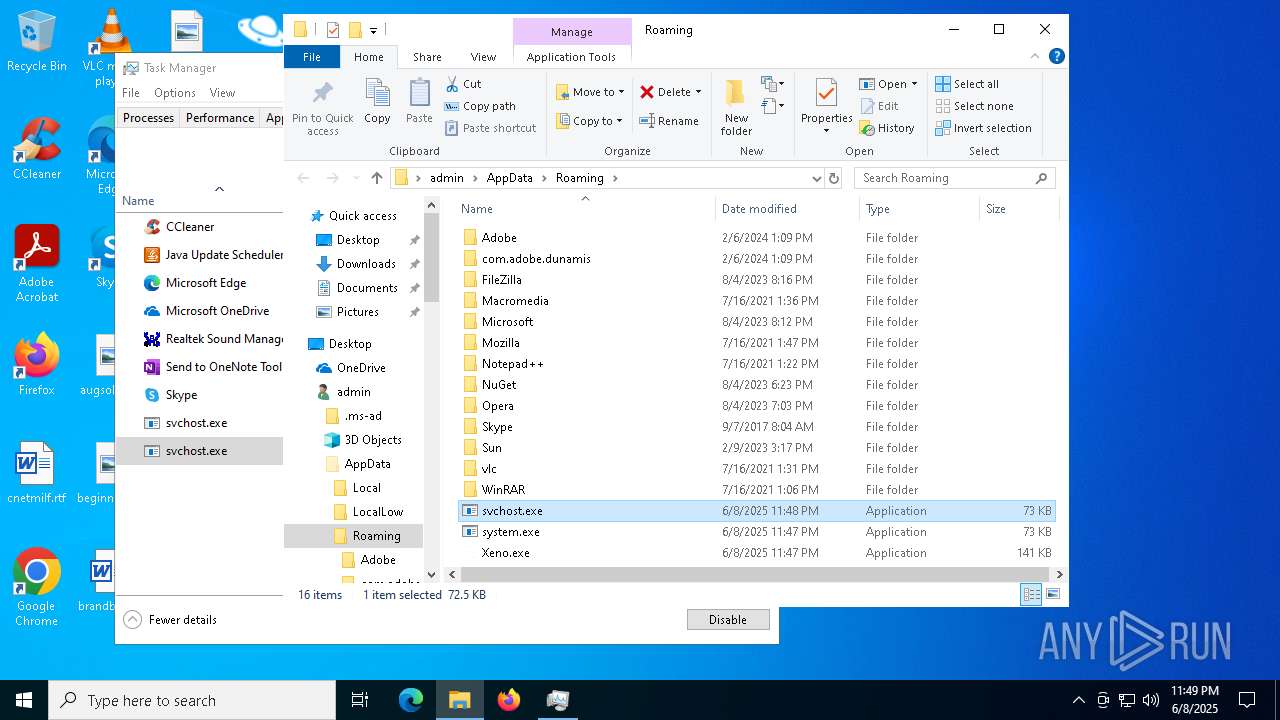
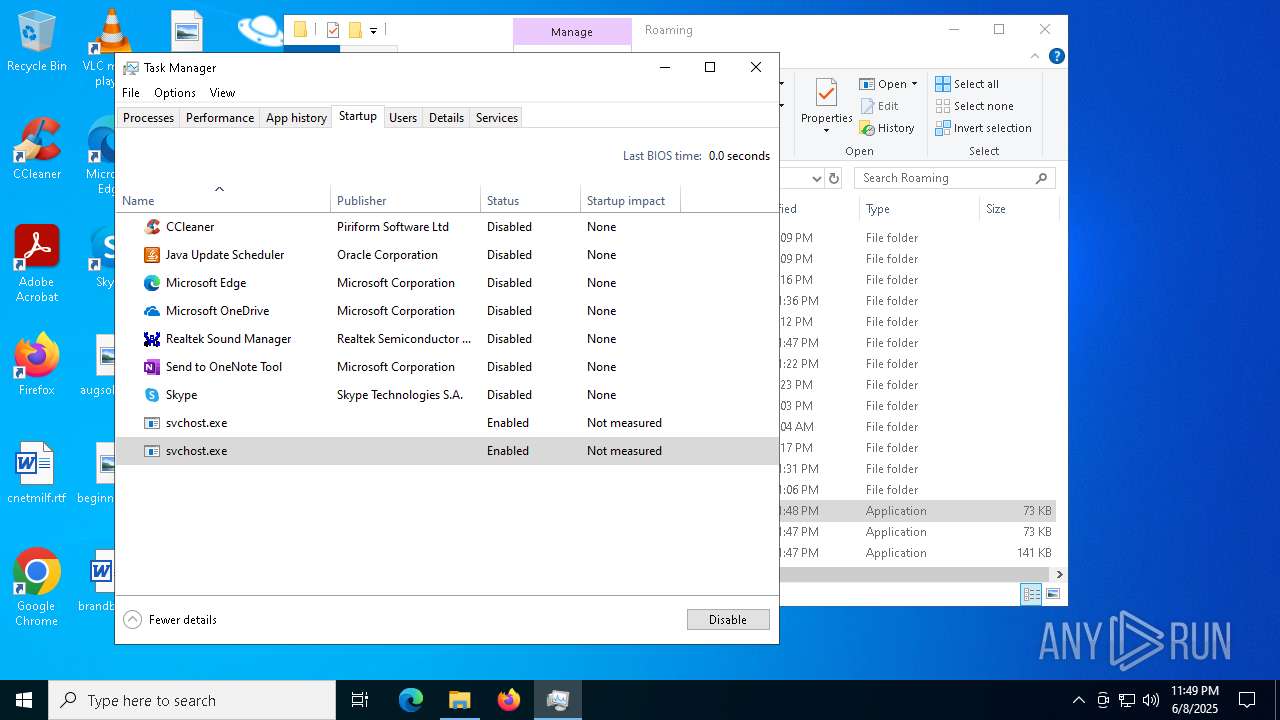
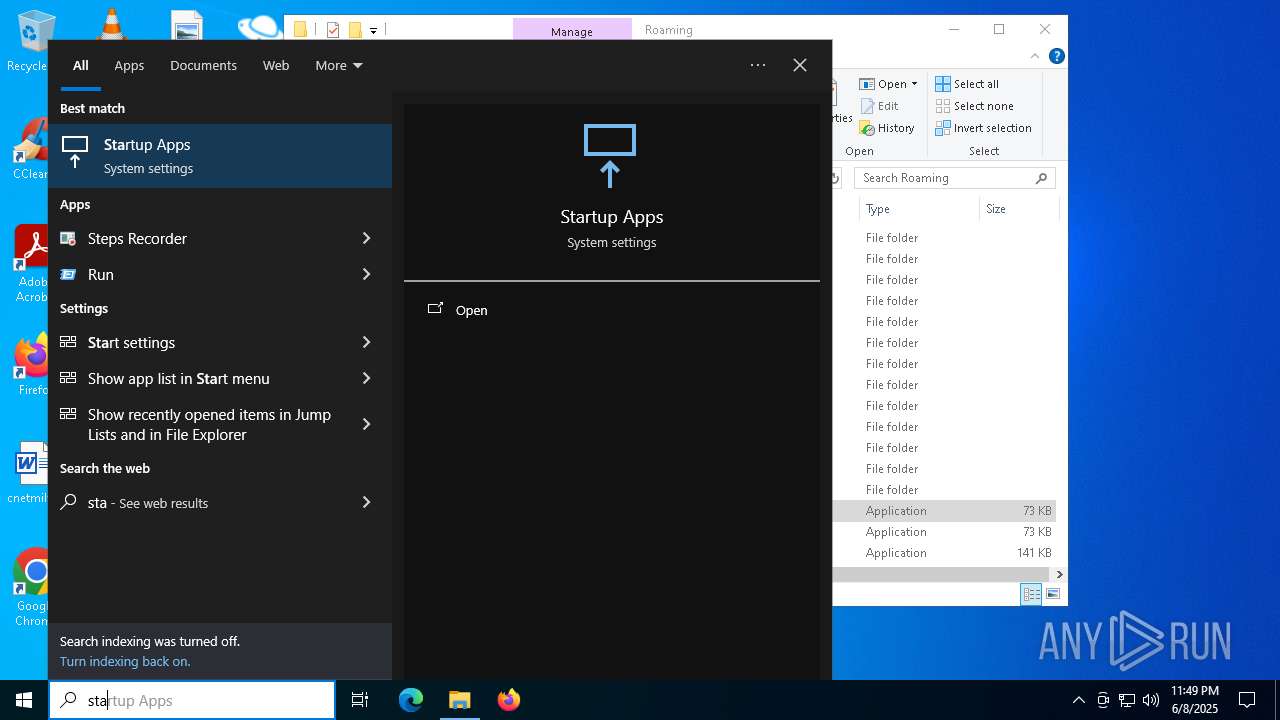
Create files in the Startup directory
- system.exe (PID: 6368)
Changes the autorun value in the registry
- system.exe (PID: 6368)
XWORM has been detected
- system.exe (PID: 6368)
- svchost.exe (PID: 5452)
XWORM has been detected (YARA)
- system.exe (PID: 6368)
SUSPICIOUS
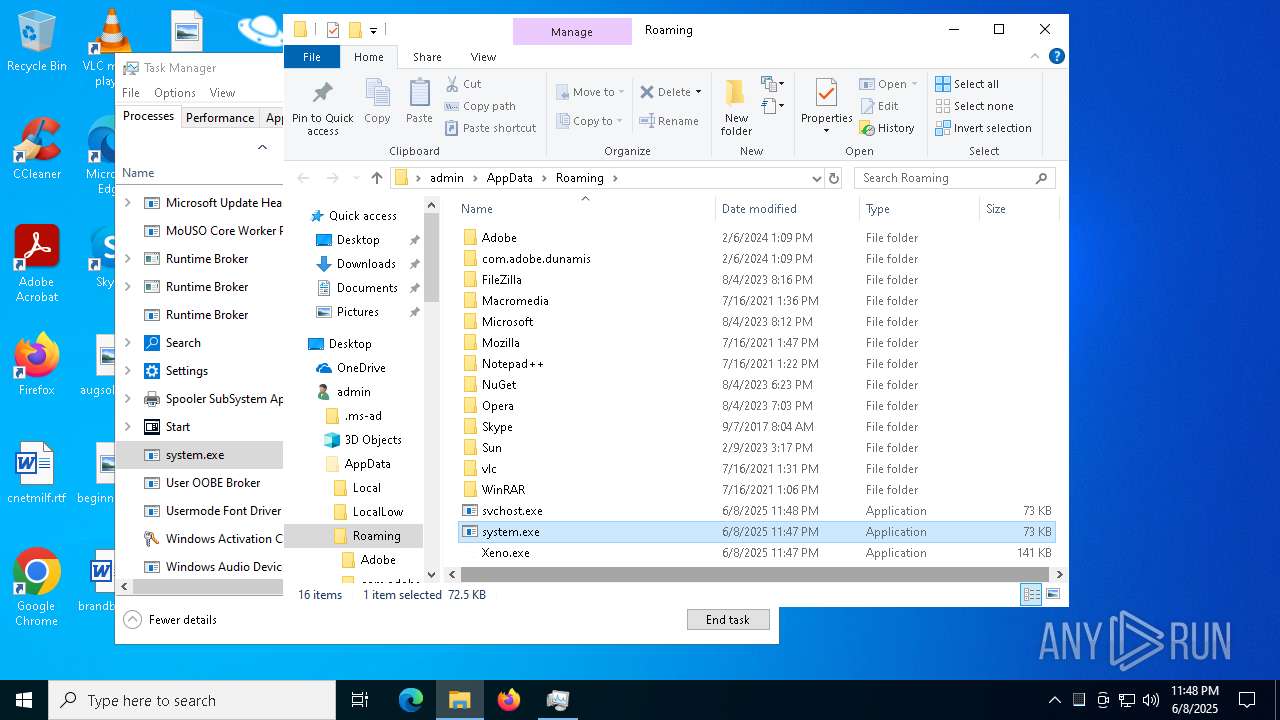
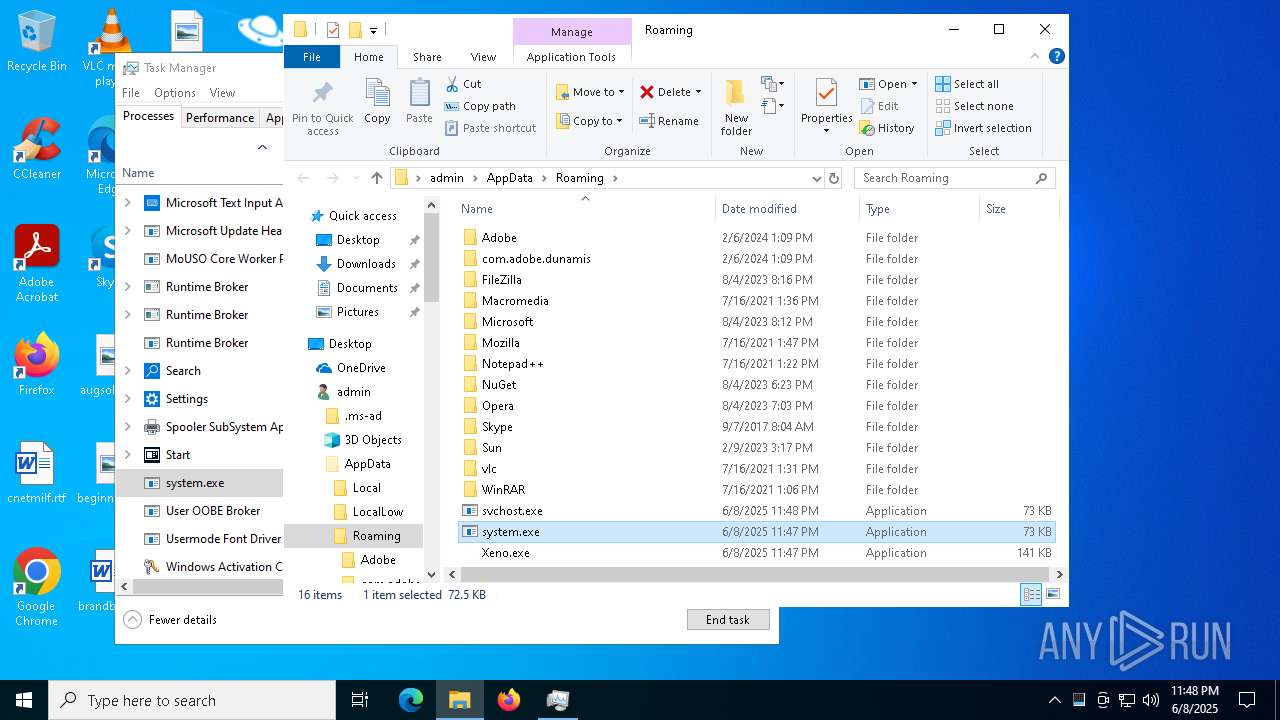
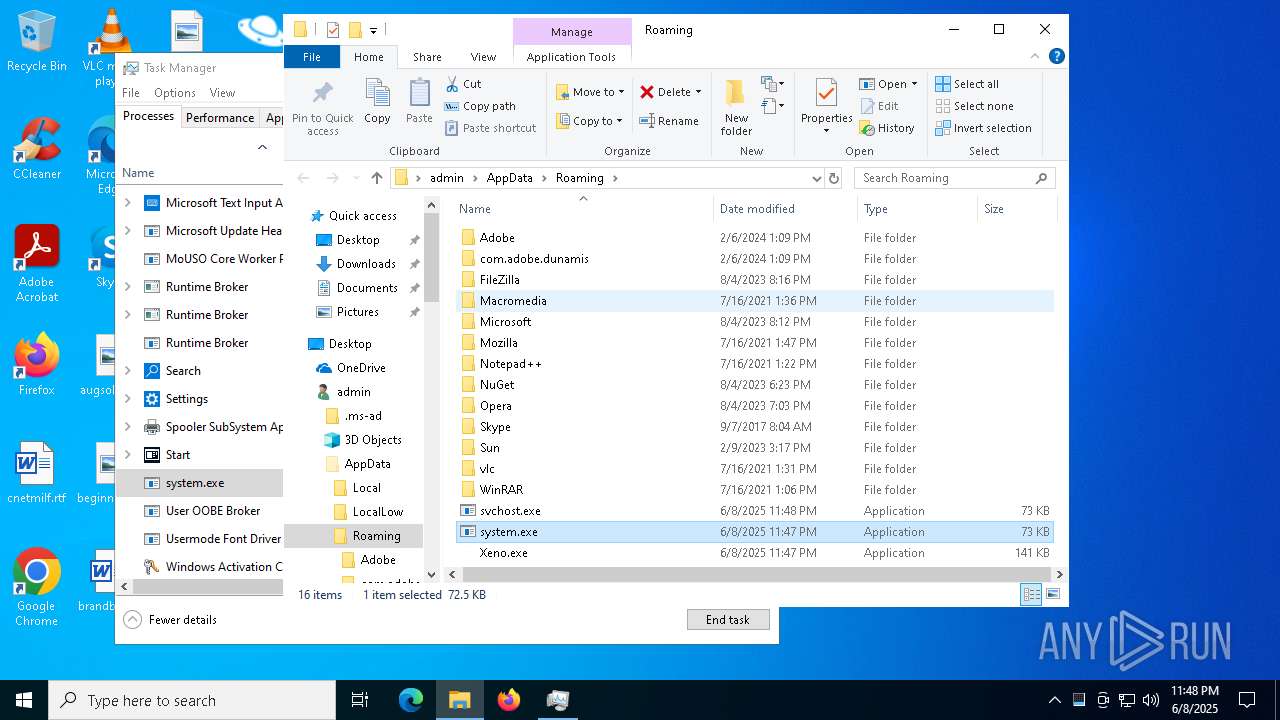
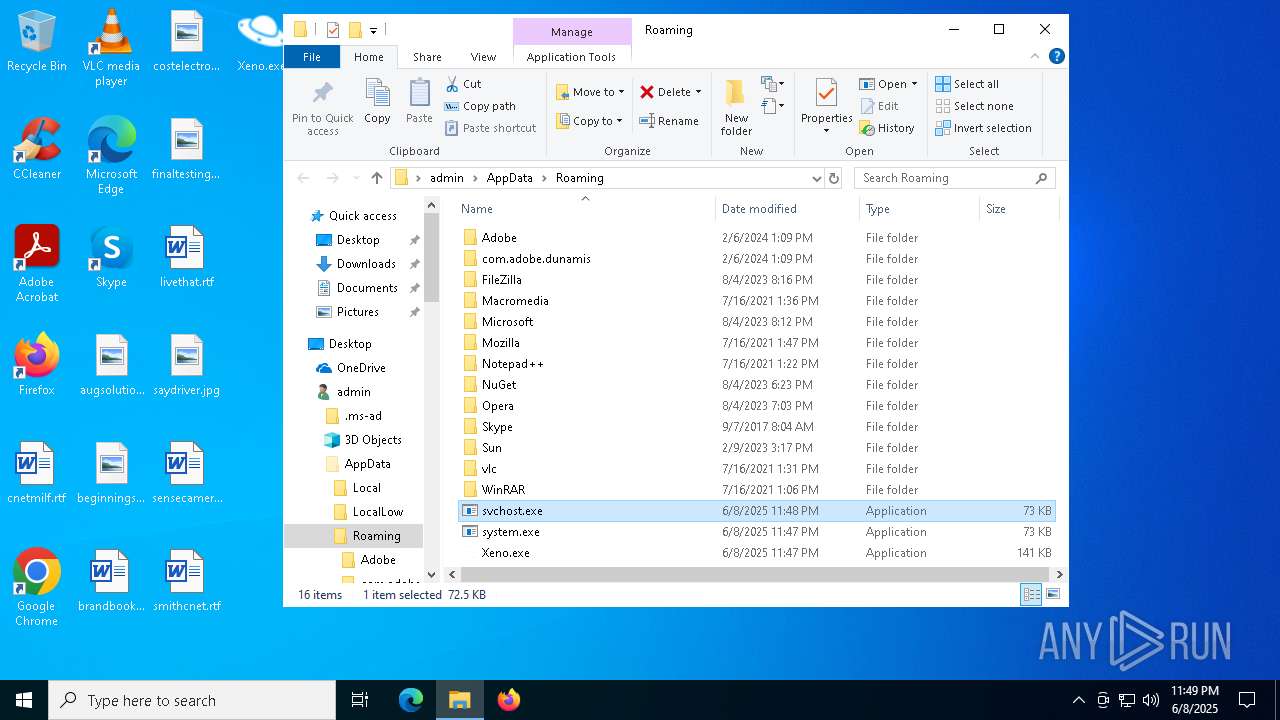
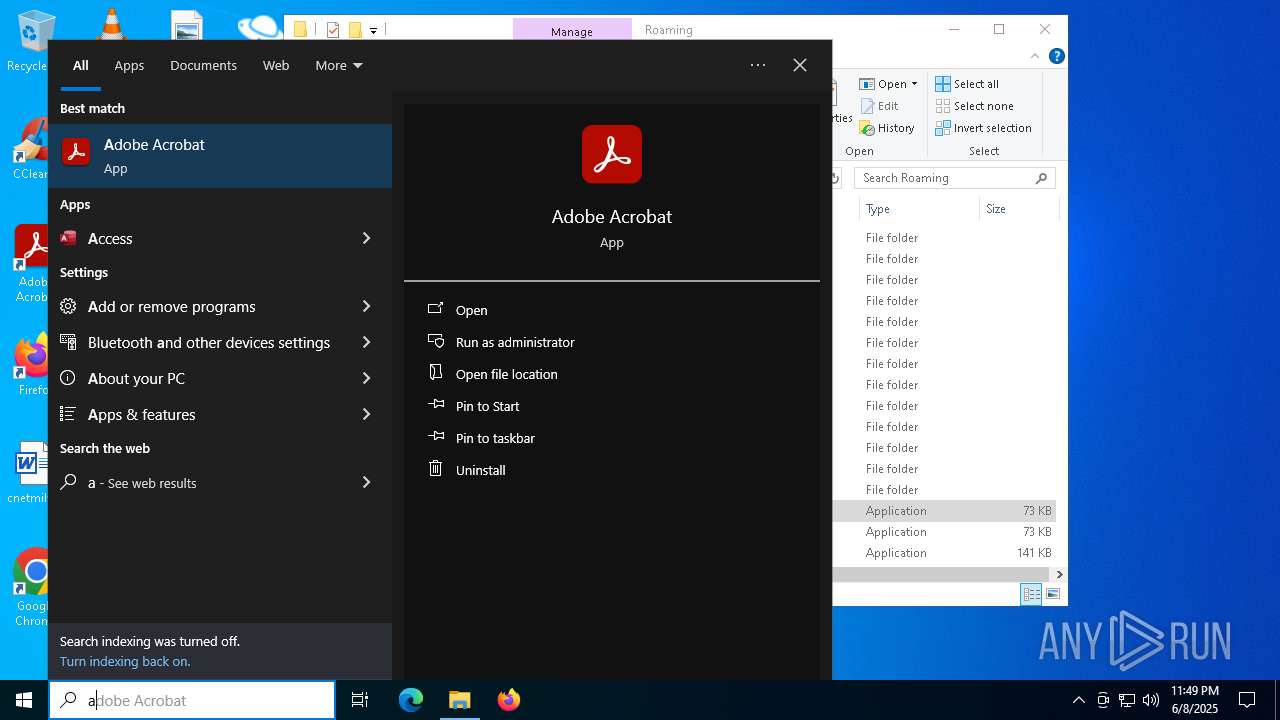
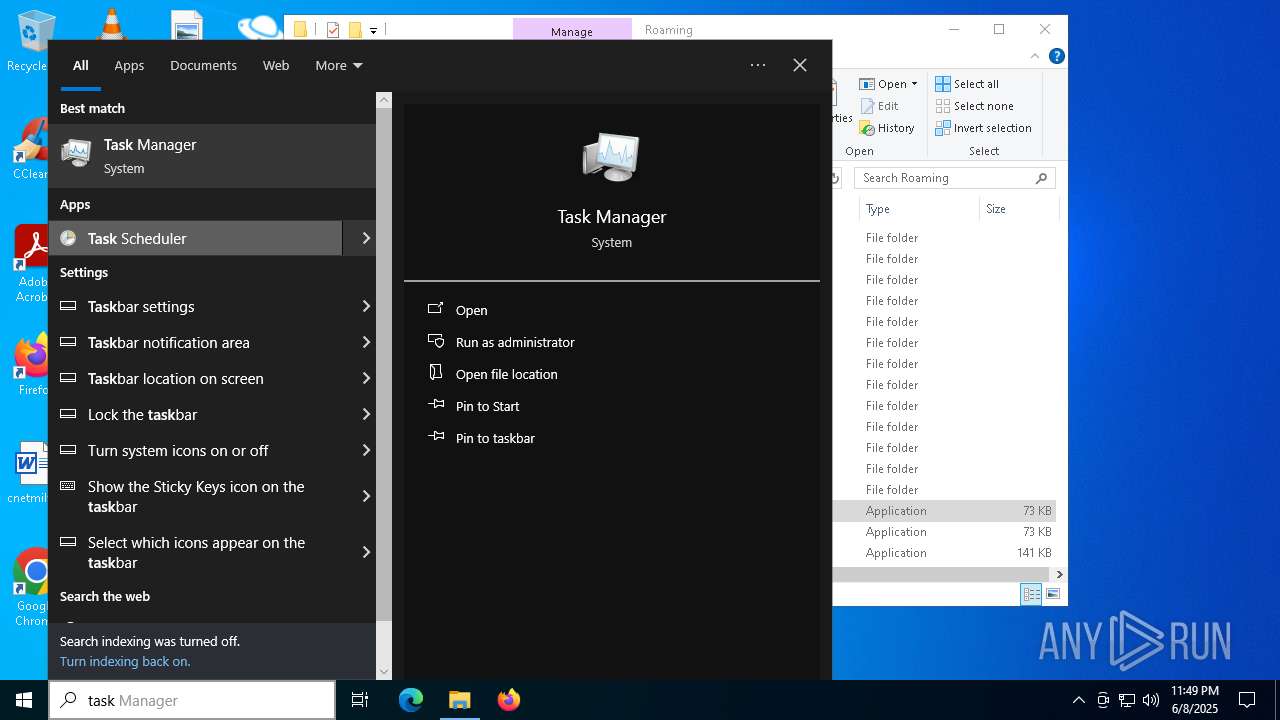
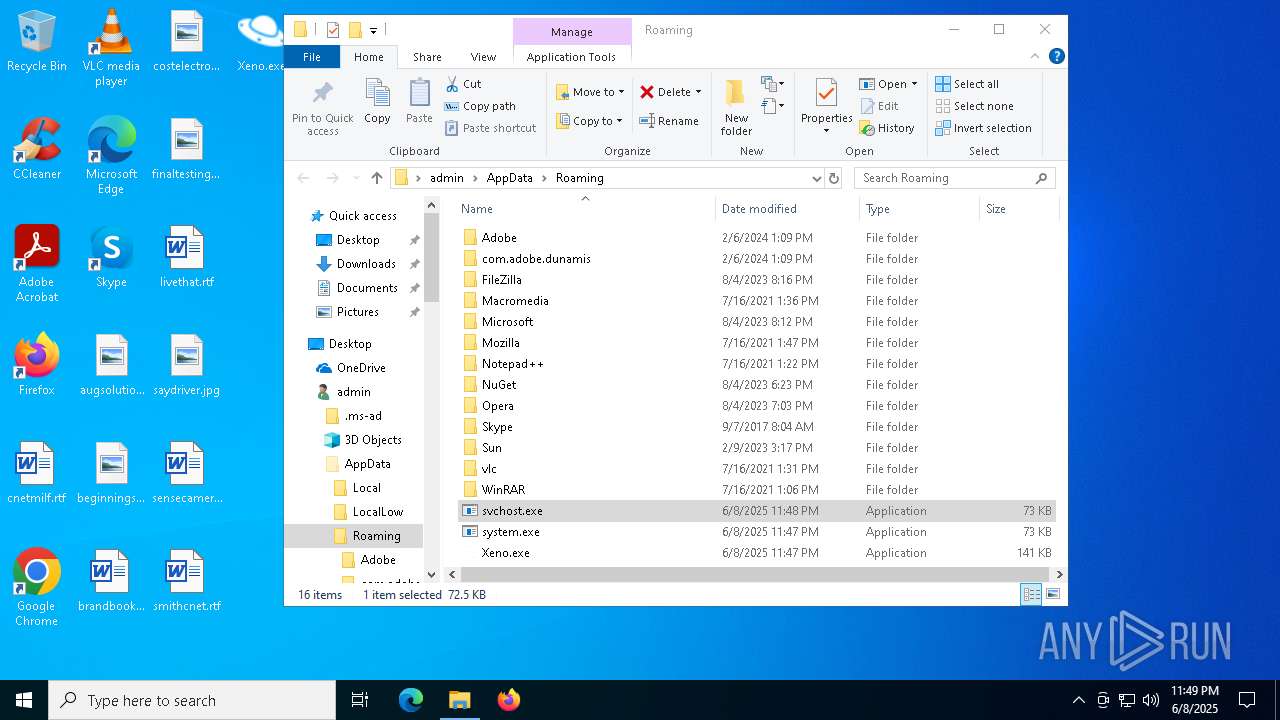
Process drops legitimate windows executable
- jjsploit.exe (PID: 3364)
Starts a Microsoft application from unusual location
- jjsploit.exe (PID: 3364)
The process creates files with name similar to system file names
- Xeno.exe (PID: 5400)
- system.exe (PID: 6368)
Executable content was dropped or overwritten
- Xeno.exe (PID: 5400)
- system.exe (PID: 6368)
Reads security settings of Internet Explorer
- Xeno.exe (PID: 5400)
Reads the date of Windows installation
- Xeno.exe (PID: 5400)
Checks for external IP
- system.exe (PID: 6368)
- svchost.exe (PID: 2196)
- svchost.exe (PID: 5452)
- svchost.exe (PID: 2168)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
- svchost.exe (PID: 2168)
Connects to unusual port
- system.exe (PID: 6368)
- svchost.exe (PID: 5452)
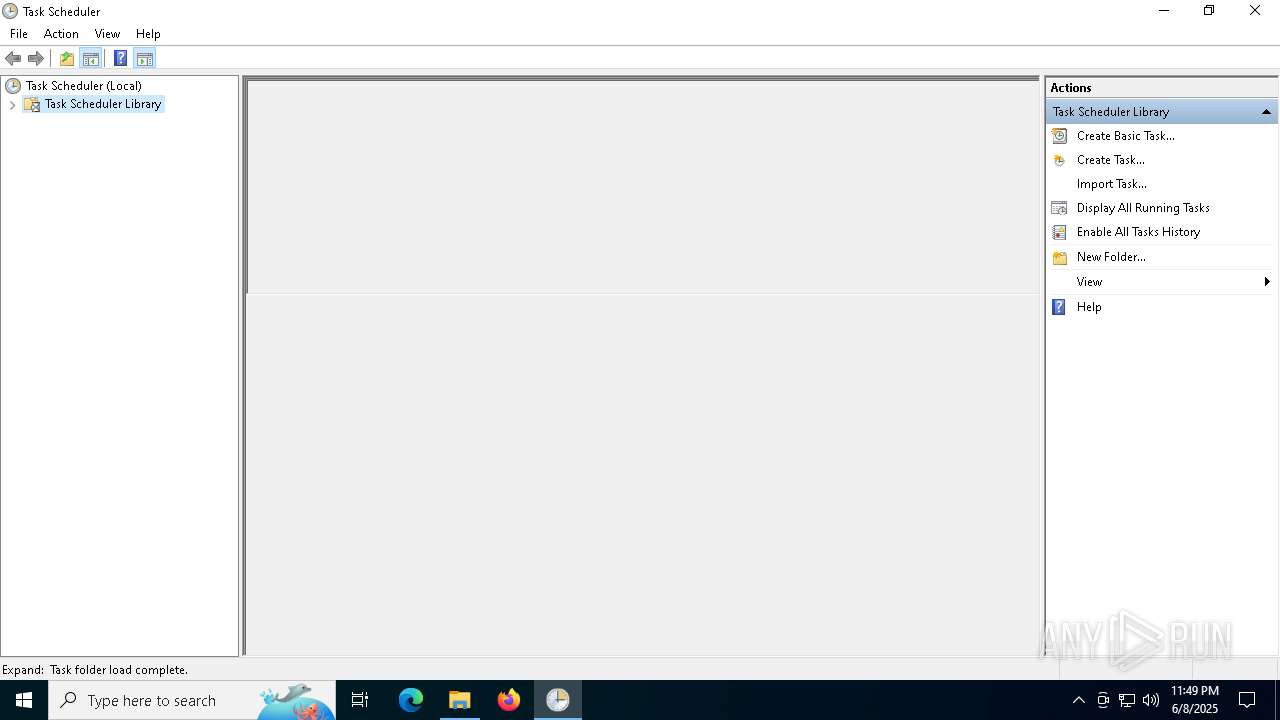
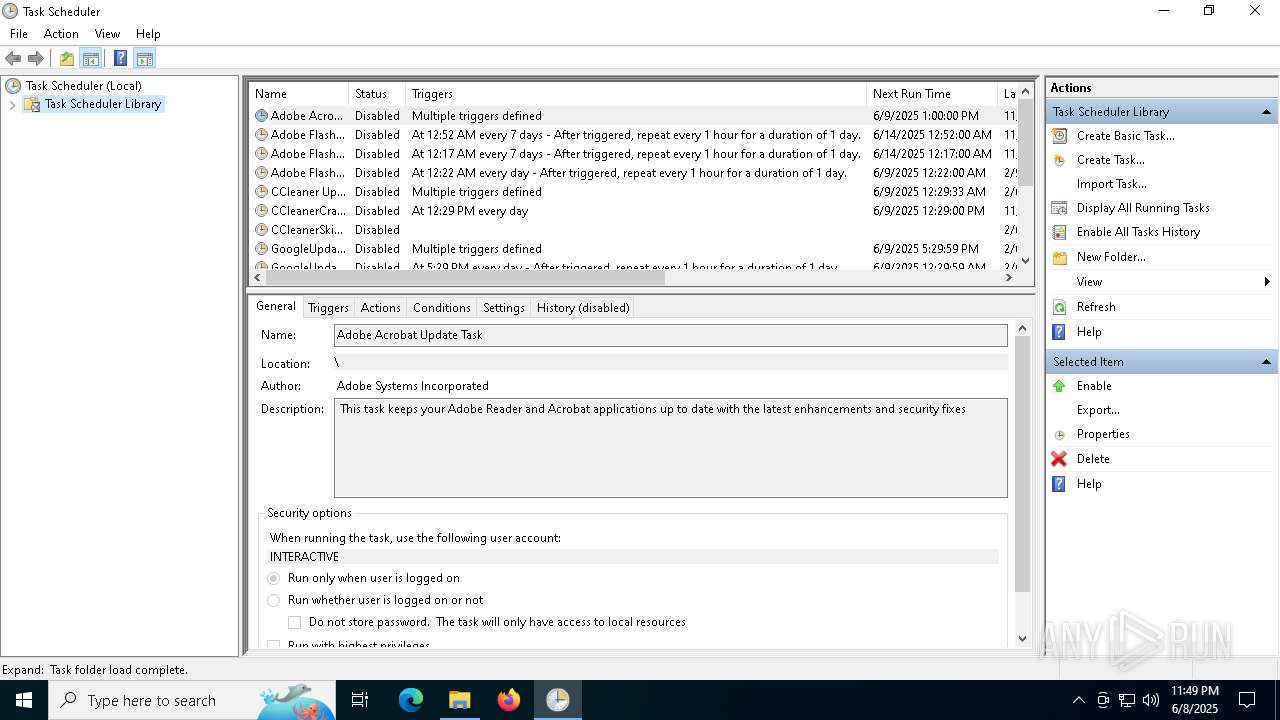
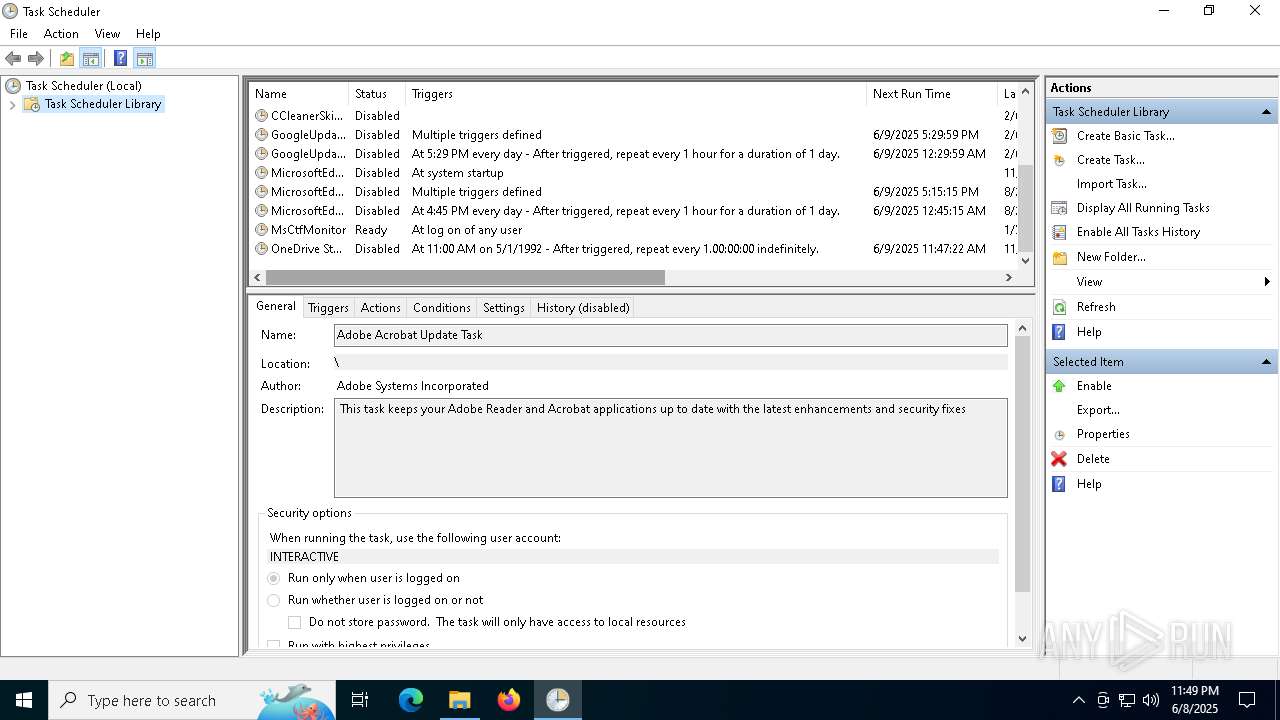
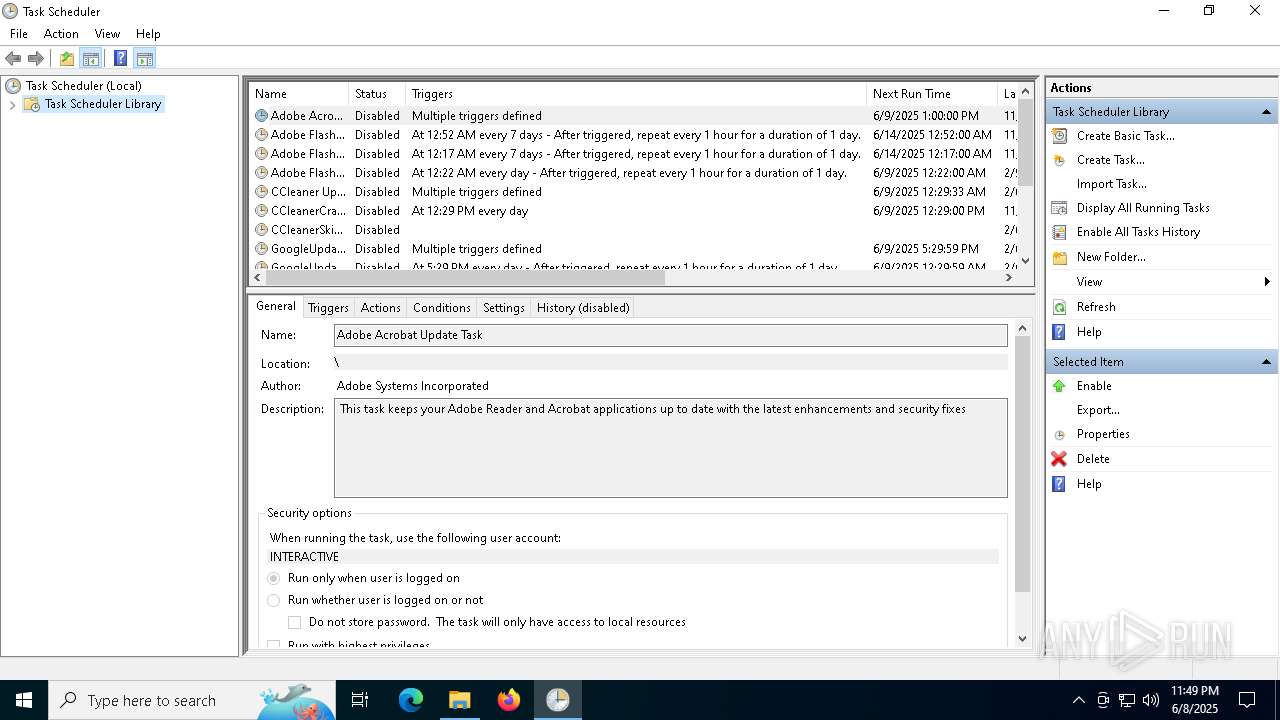
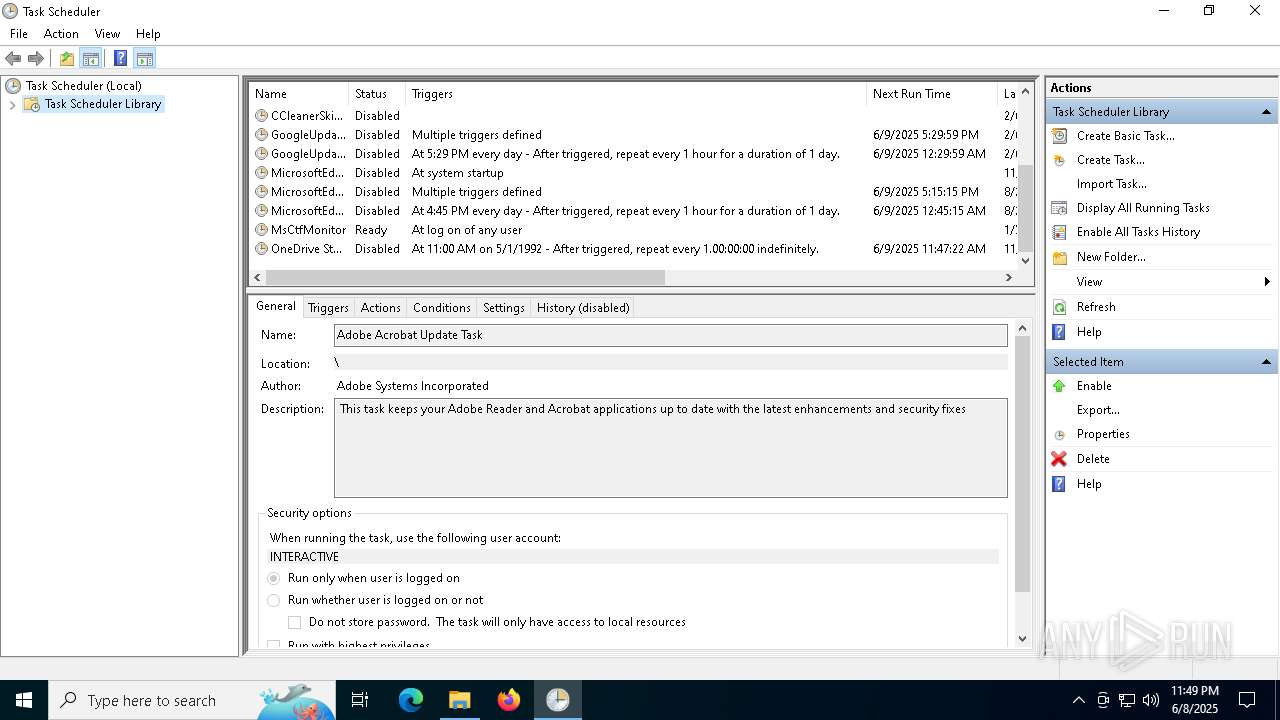
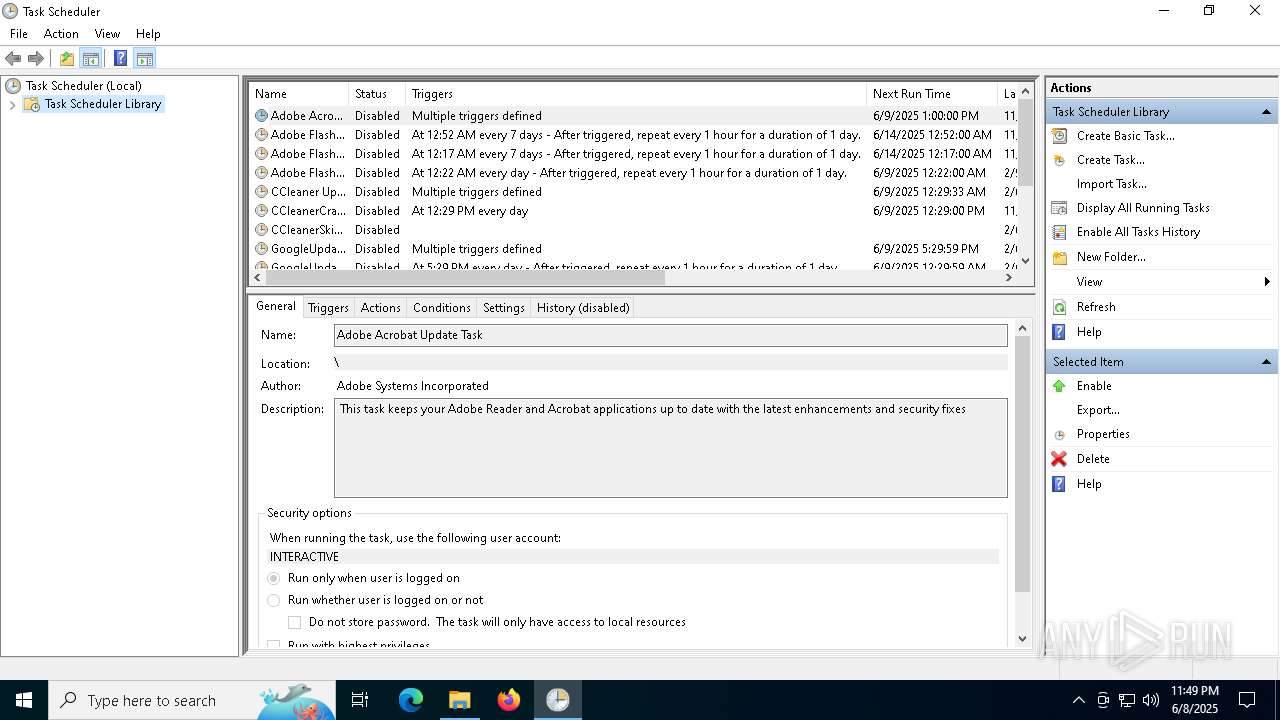
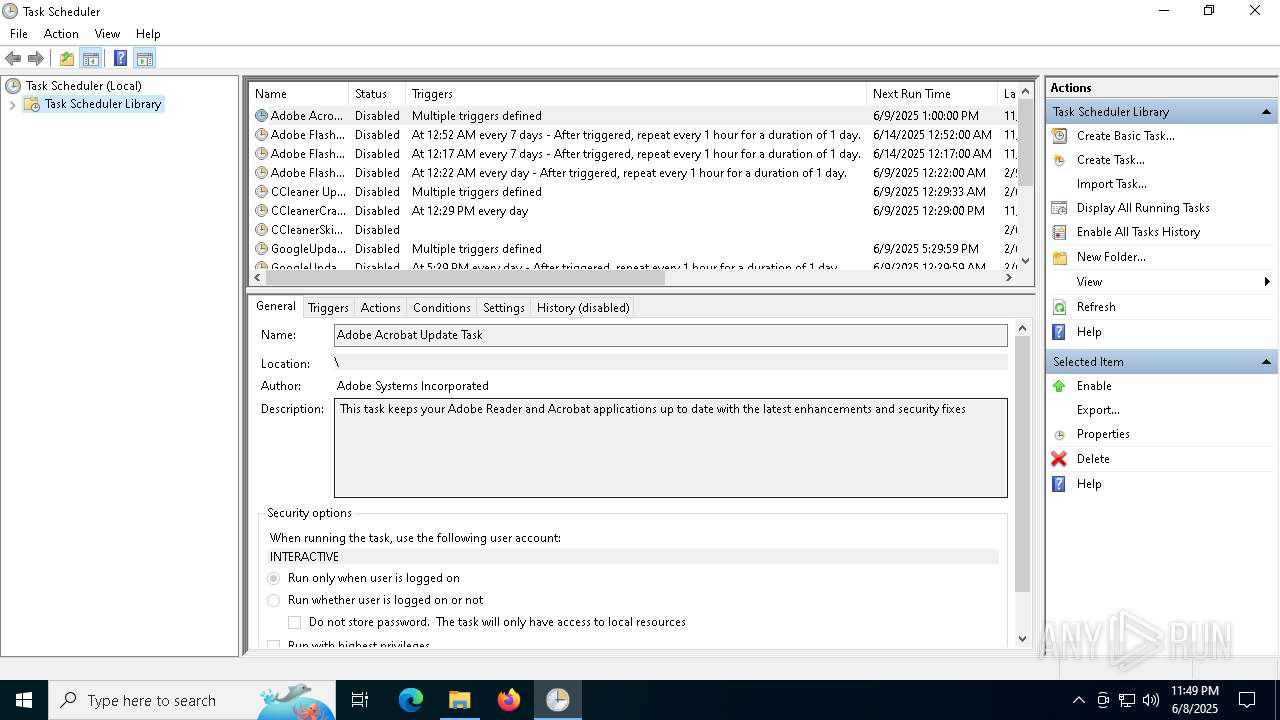
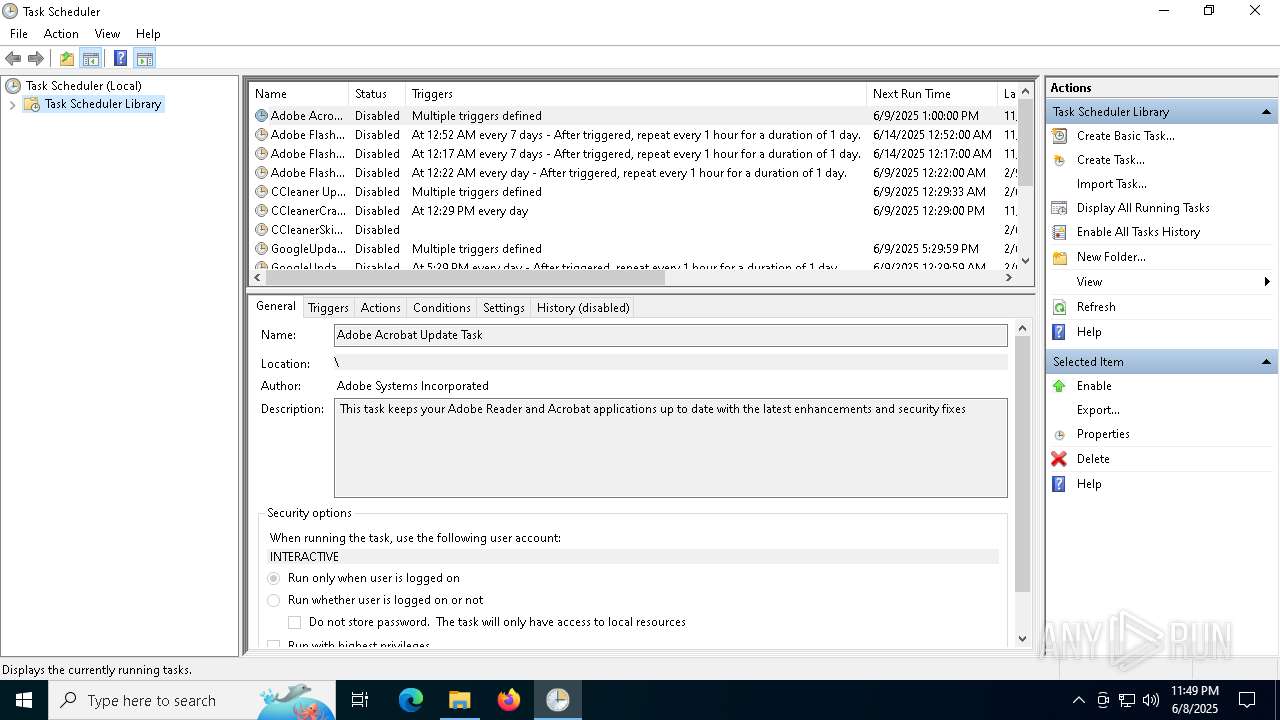
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 2580)
INFO
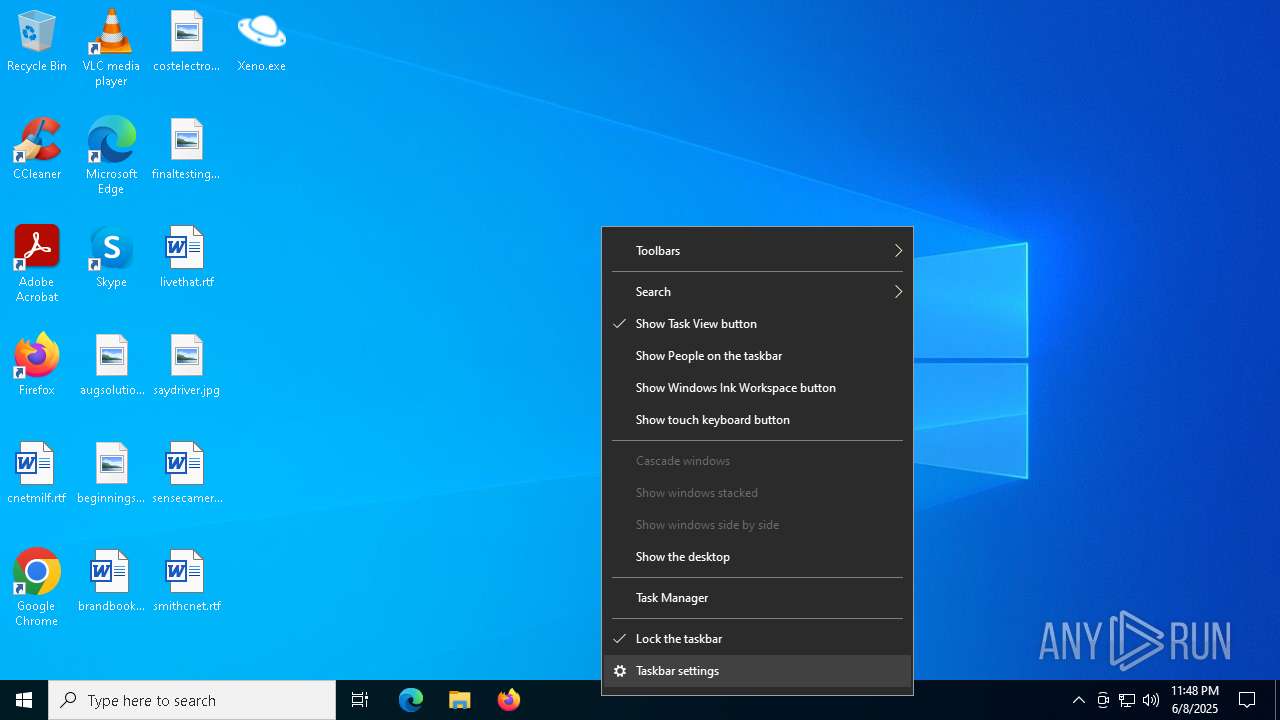
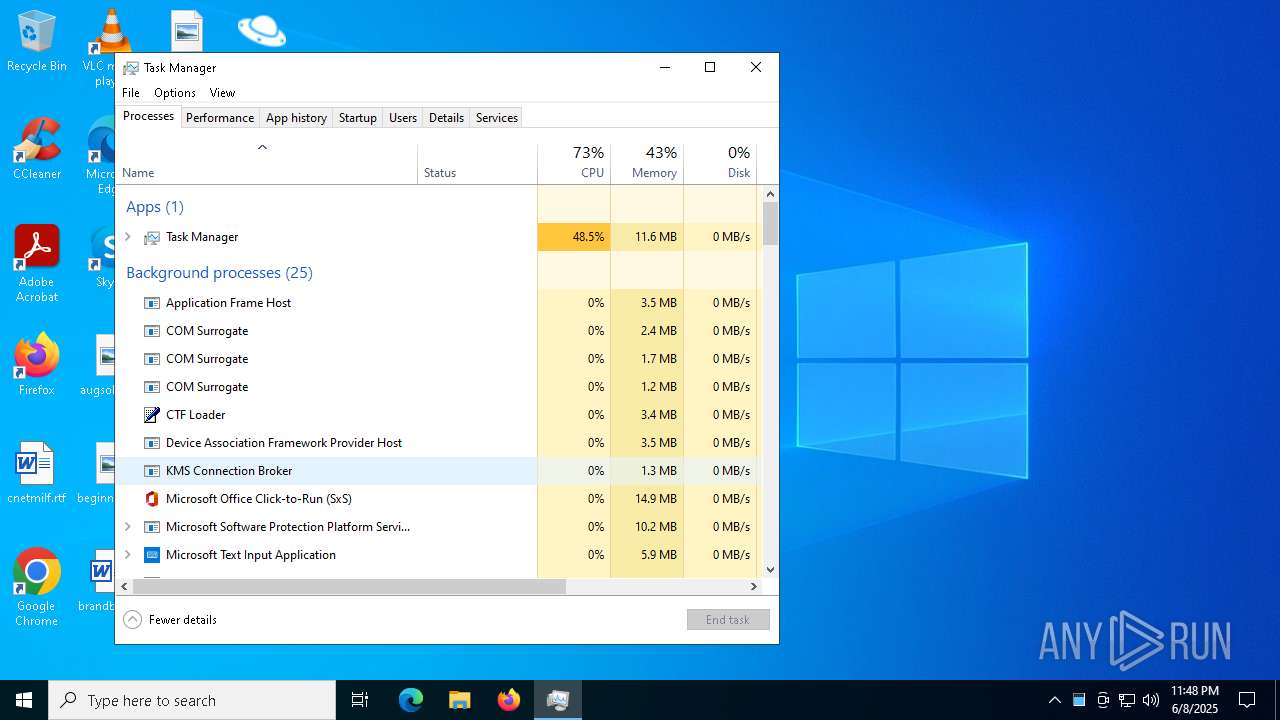
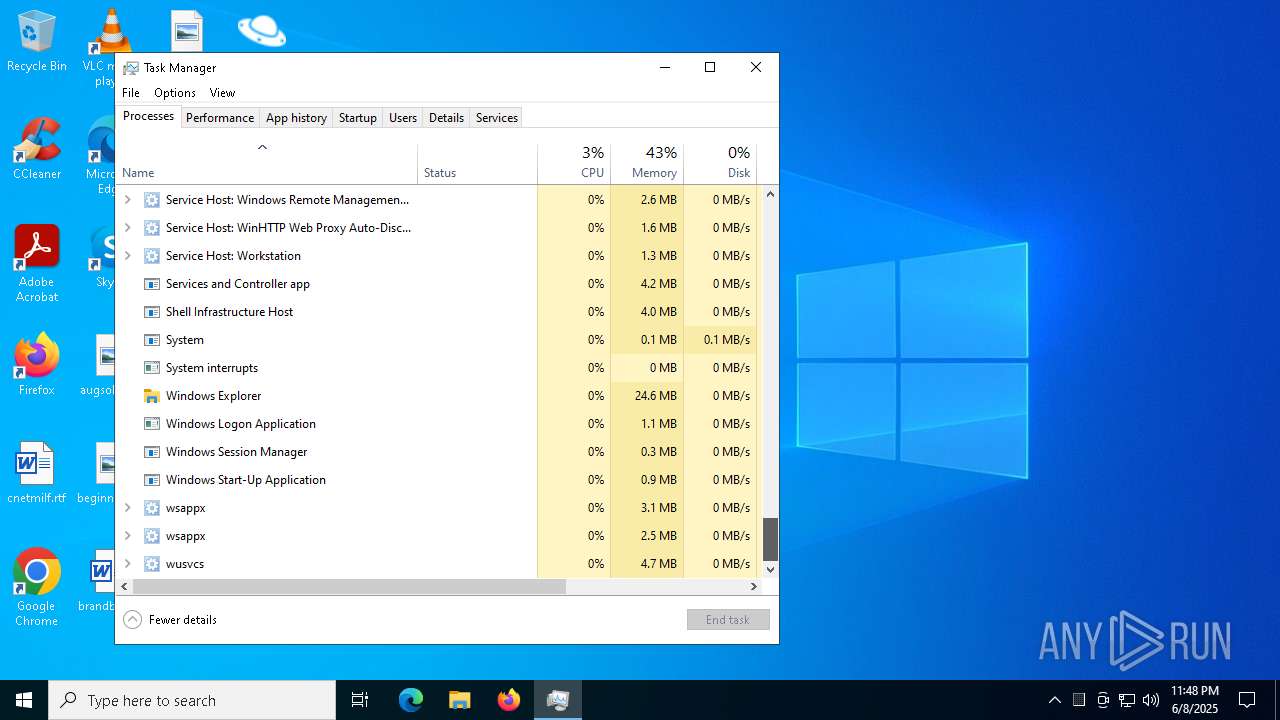
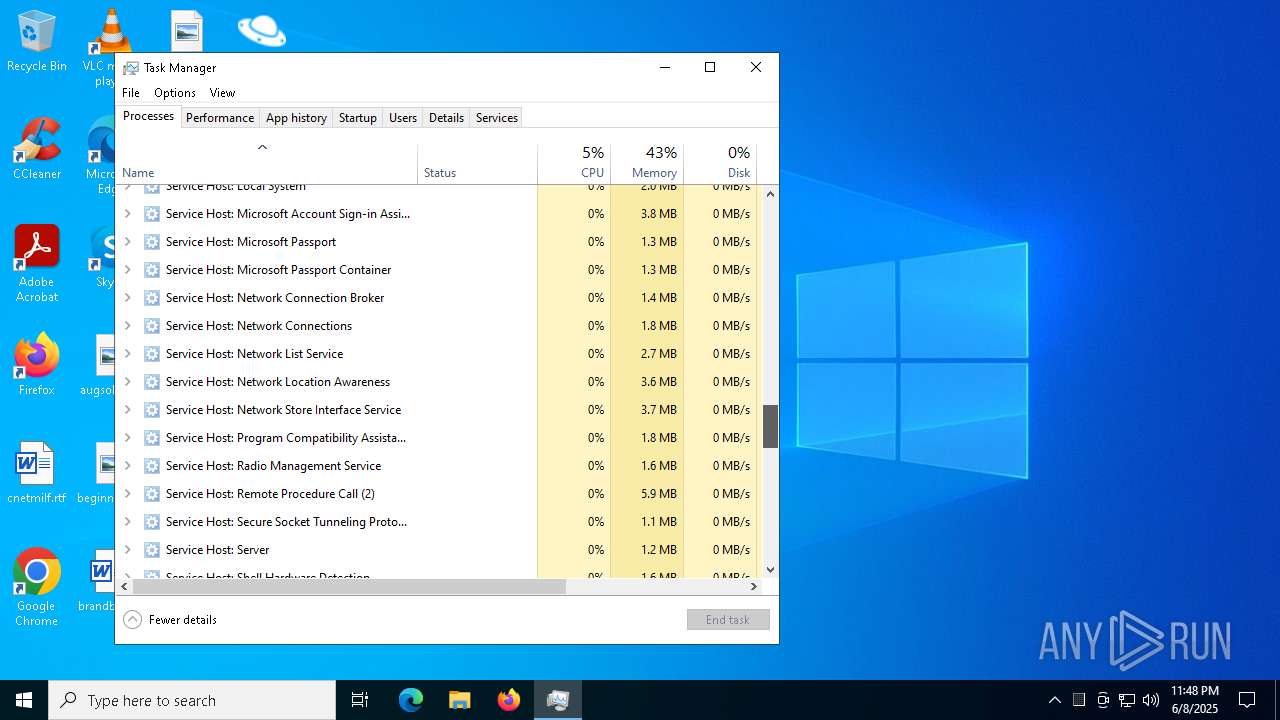
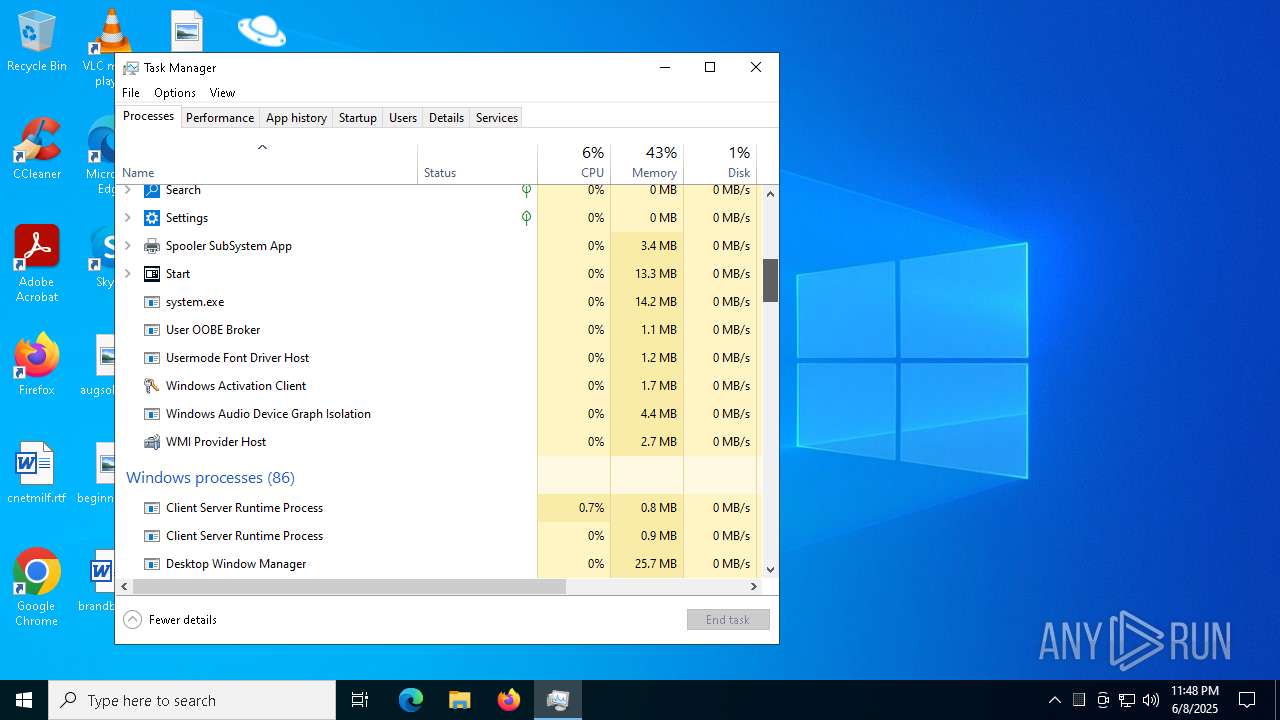
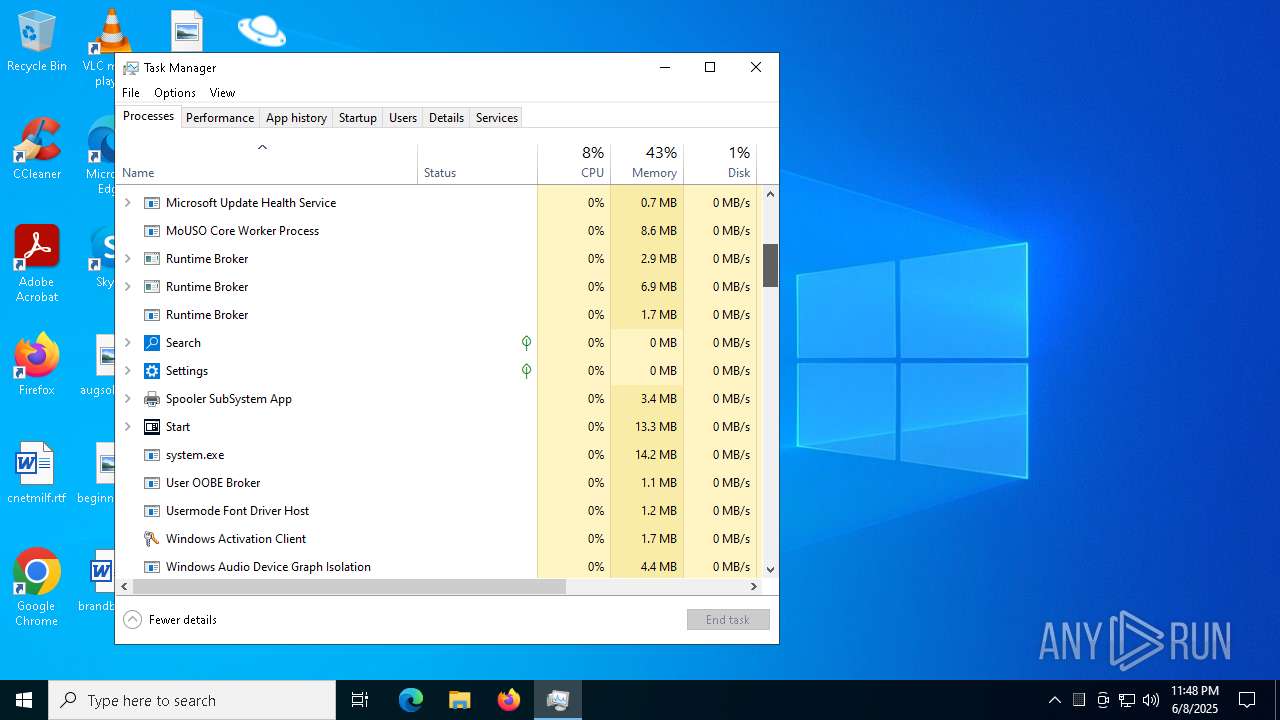
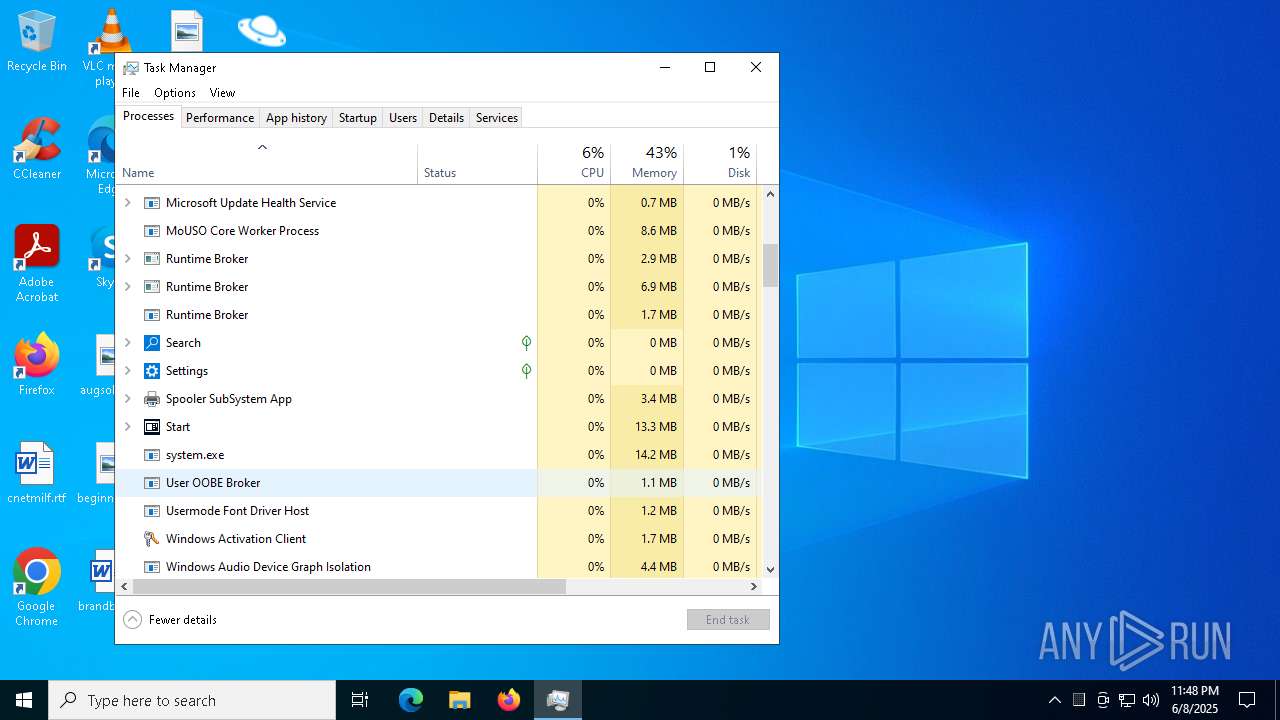
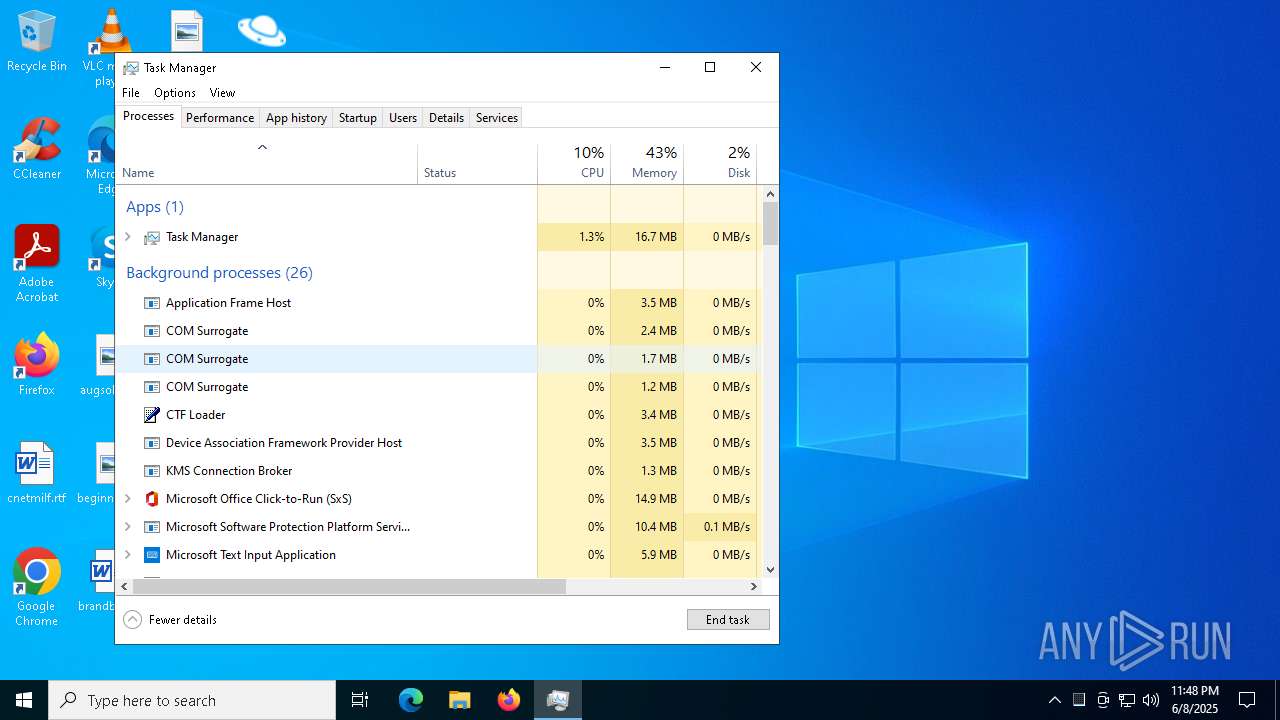
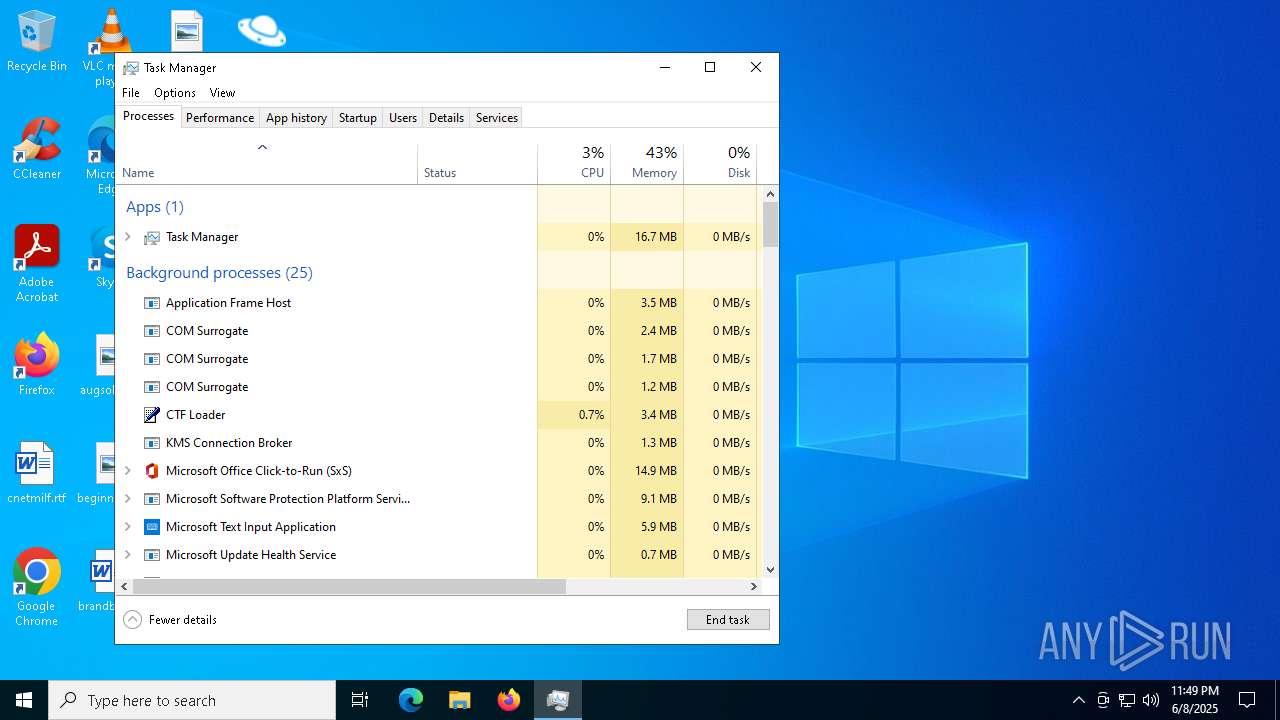
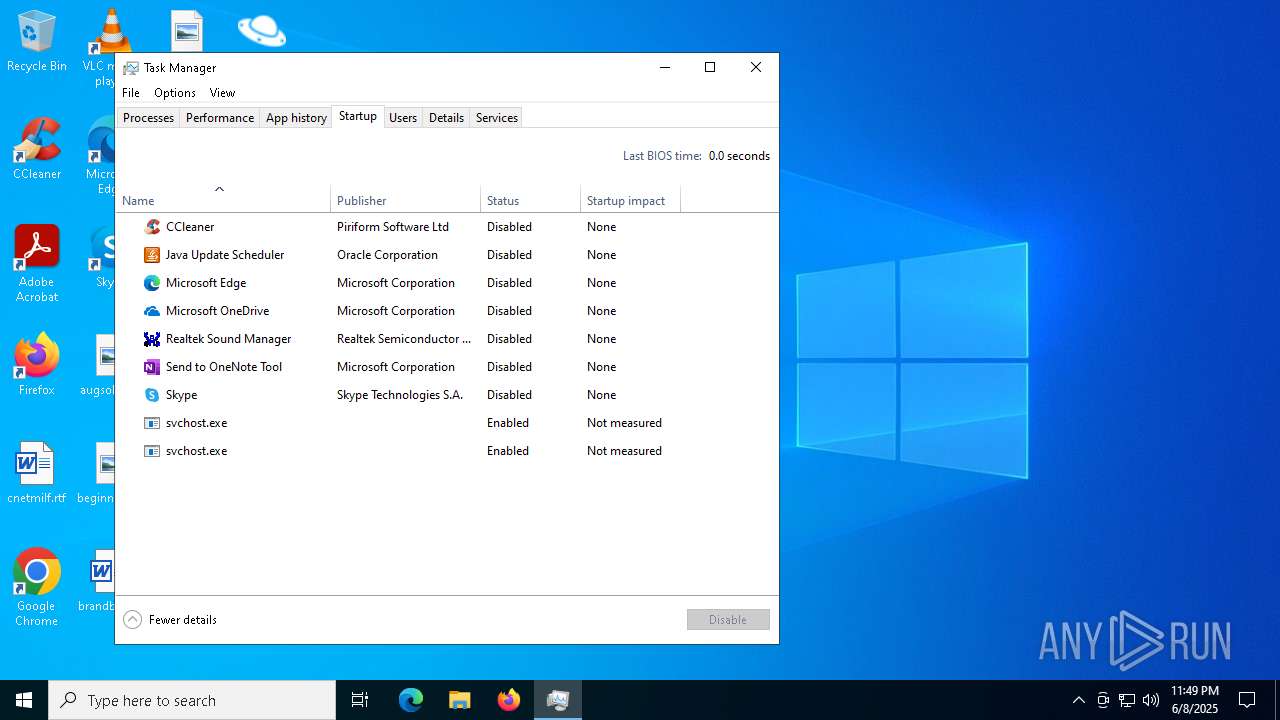
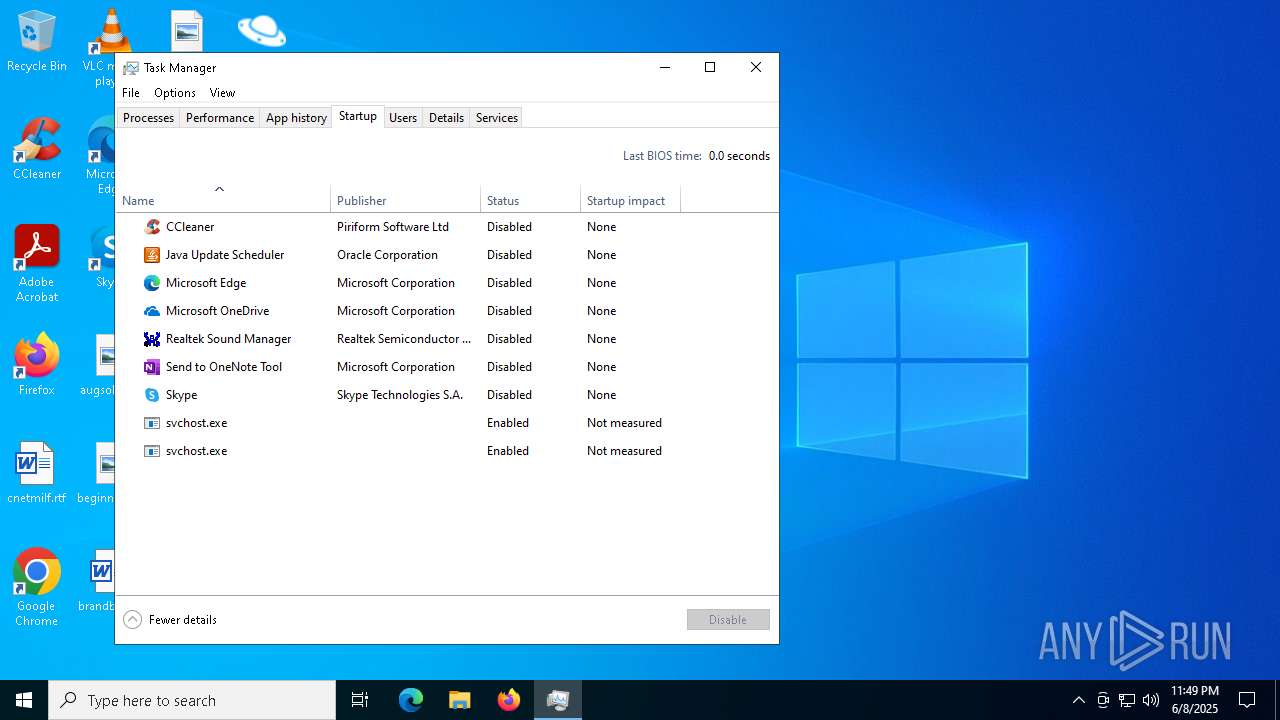
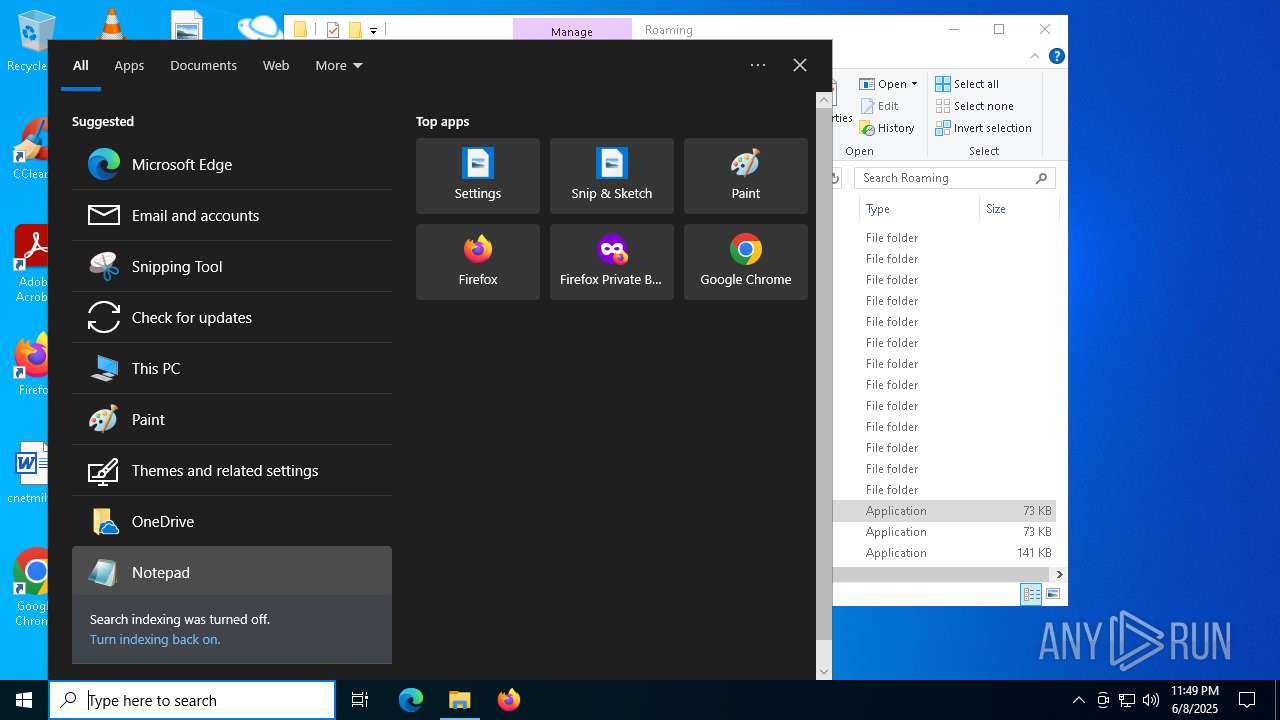
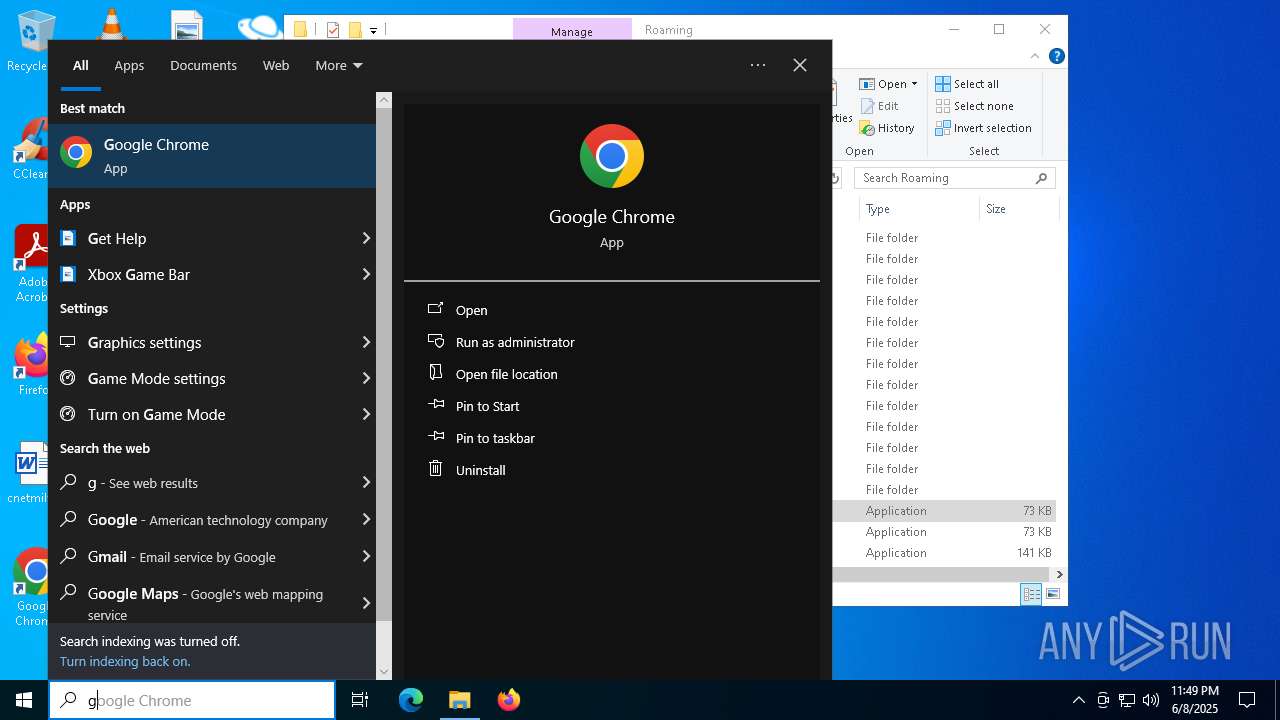
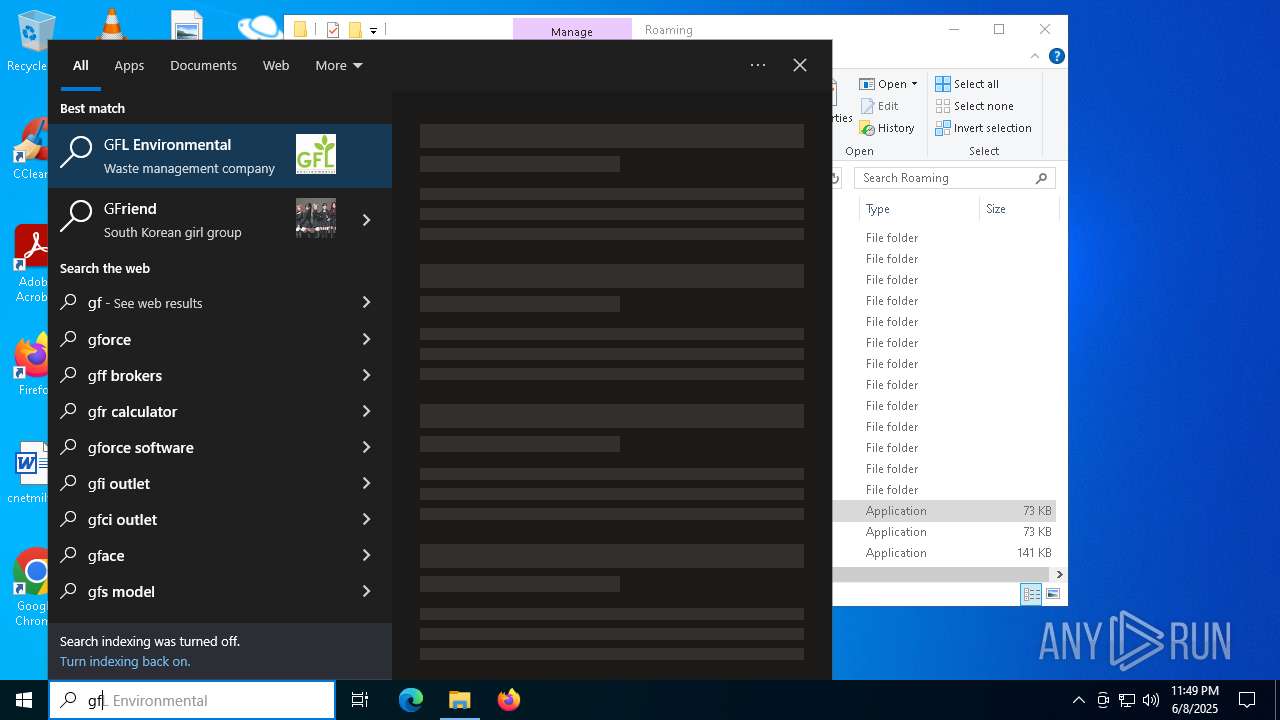
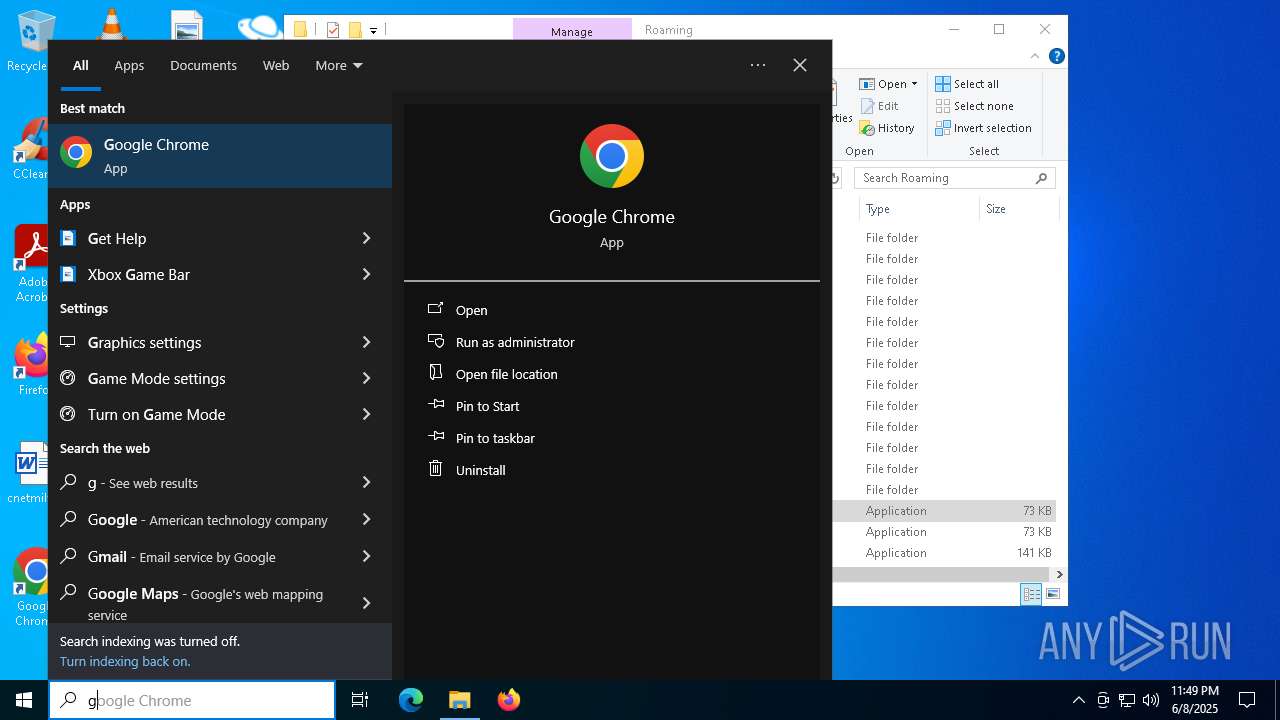
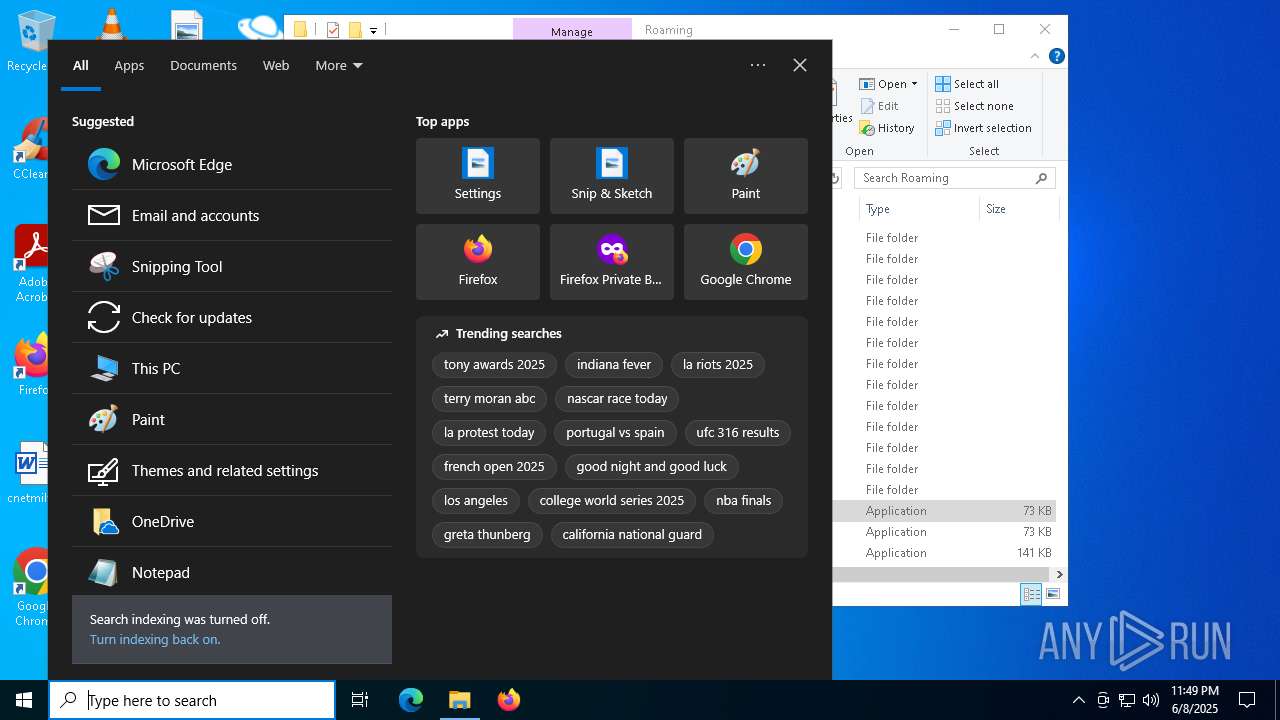
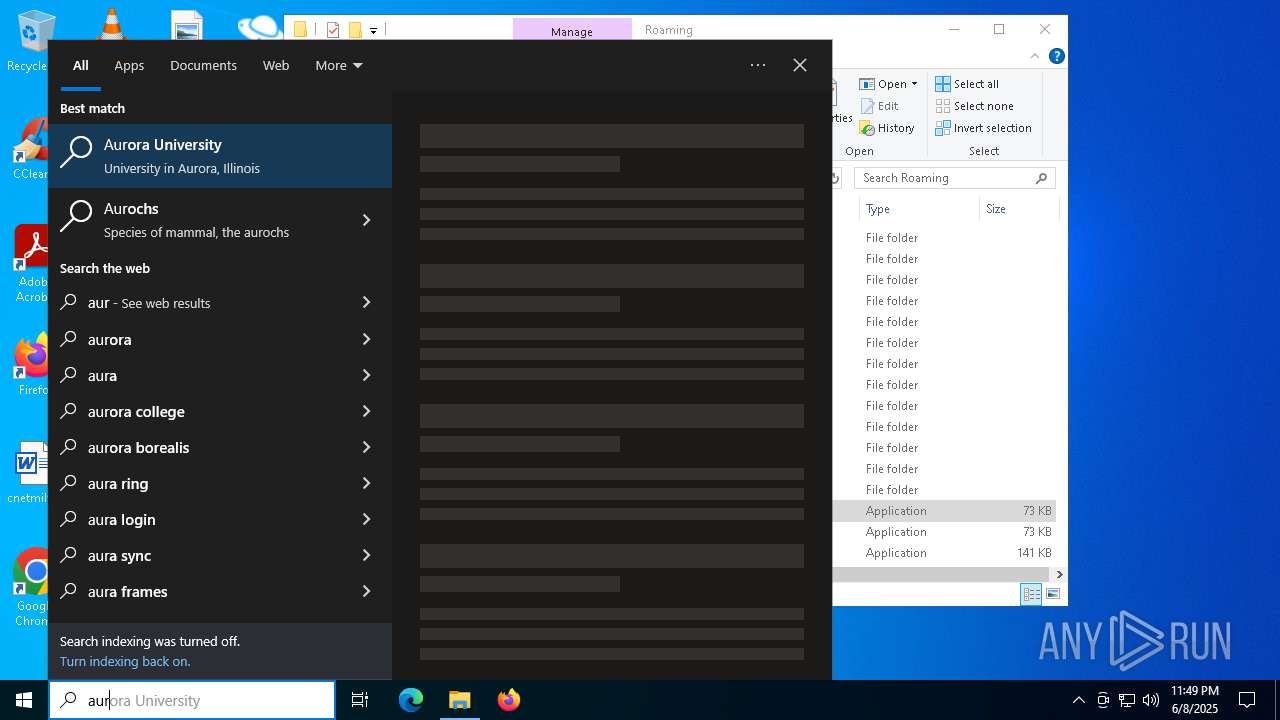
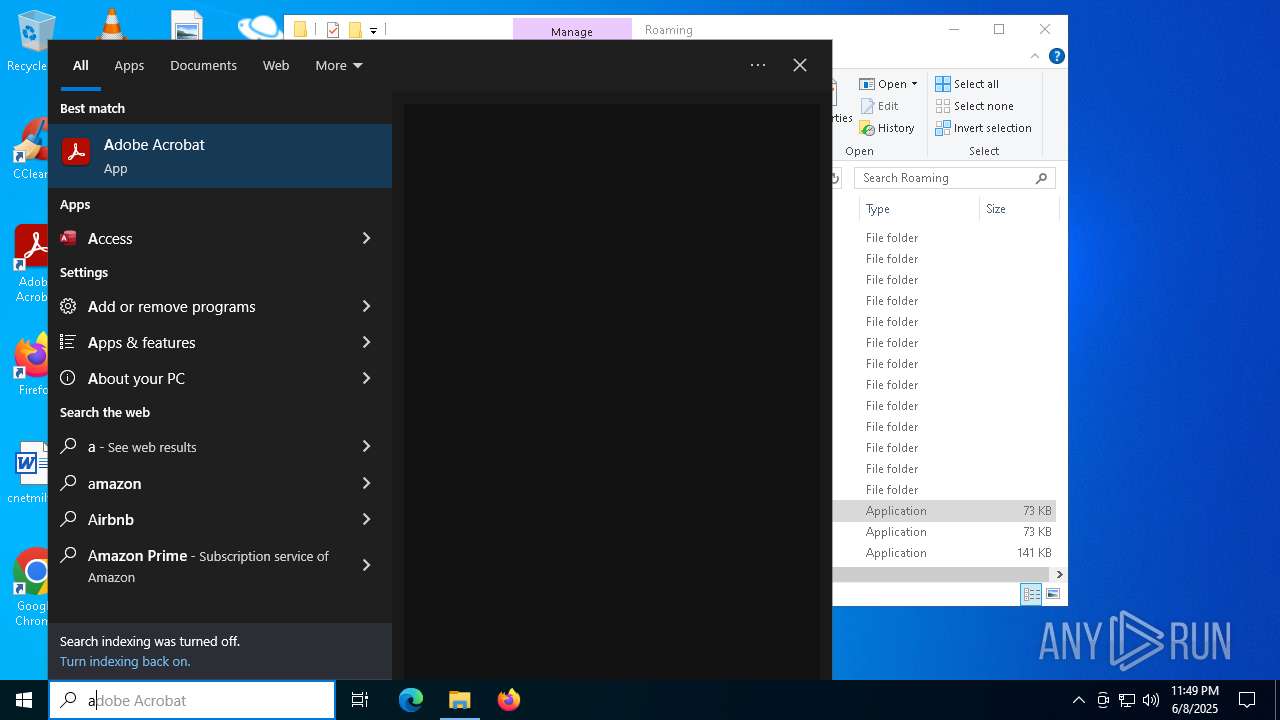
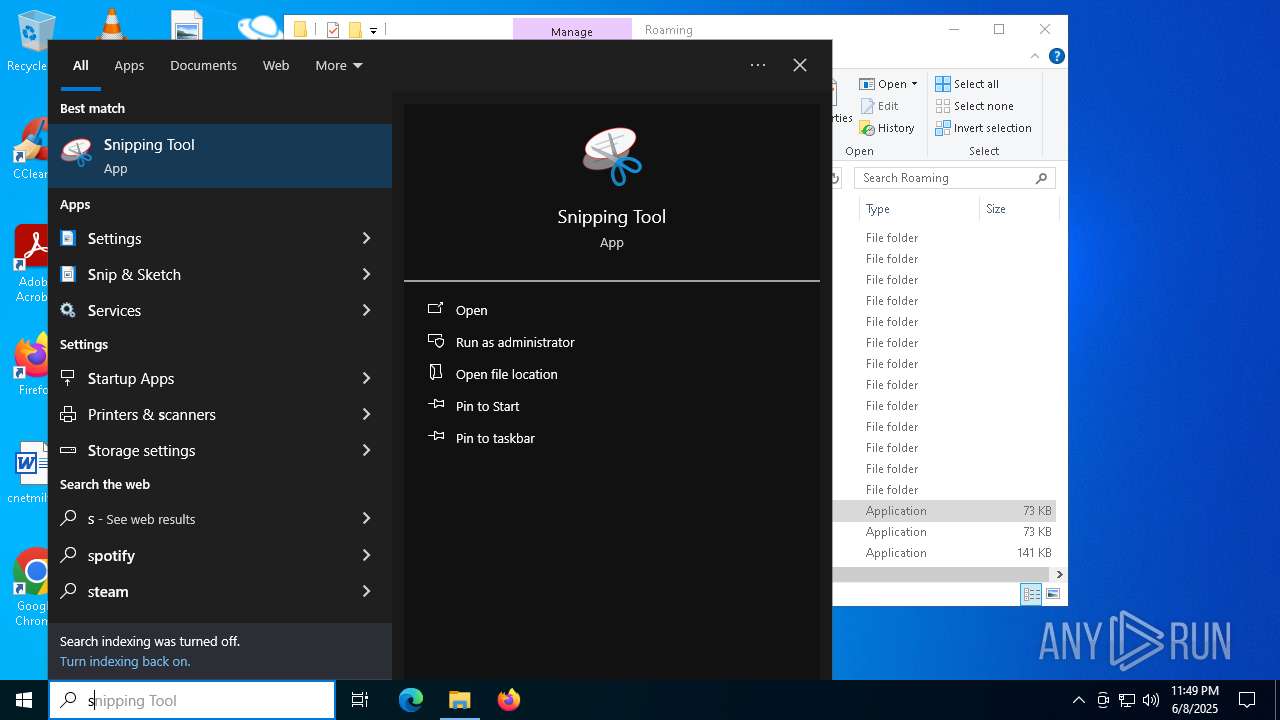
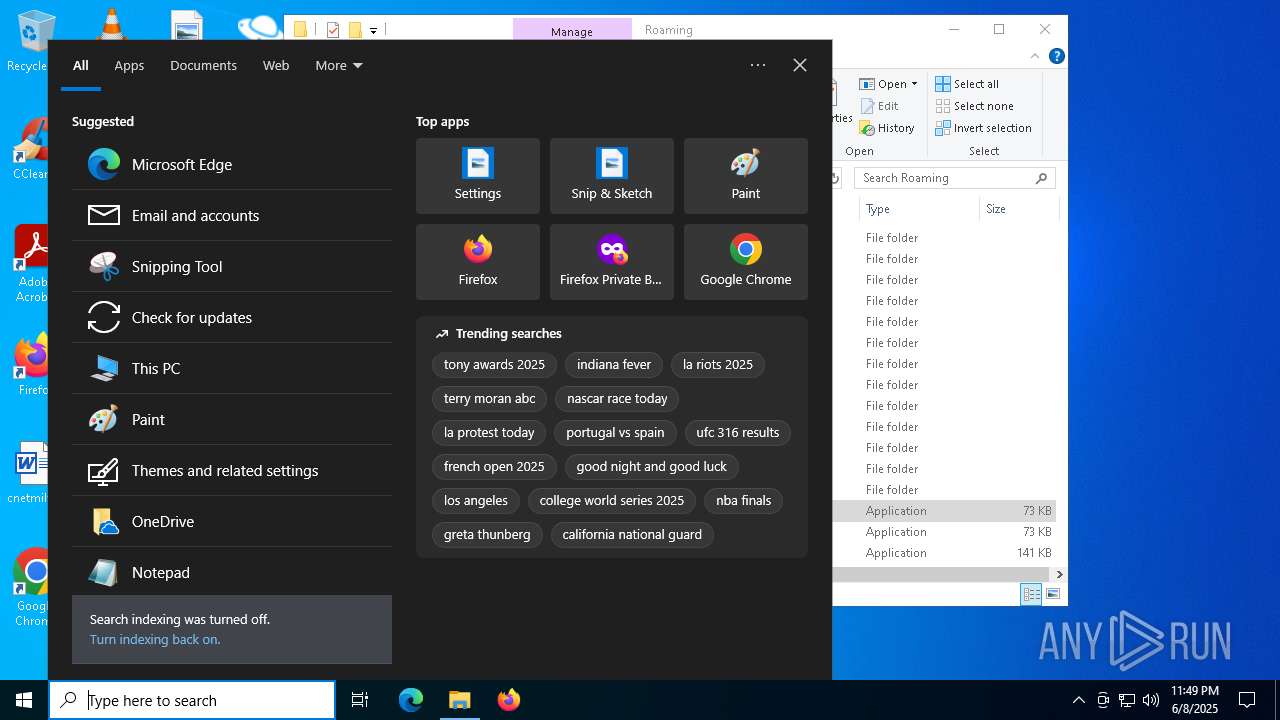
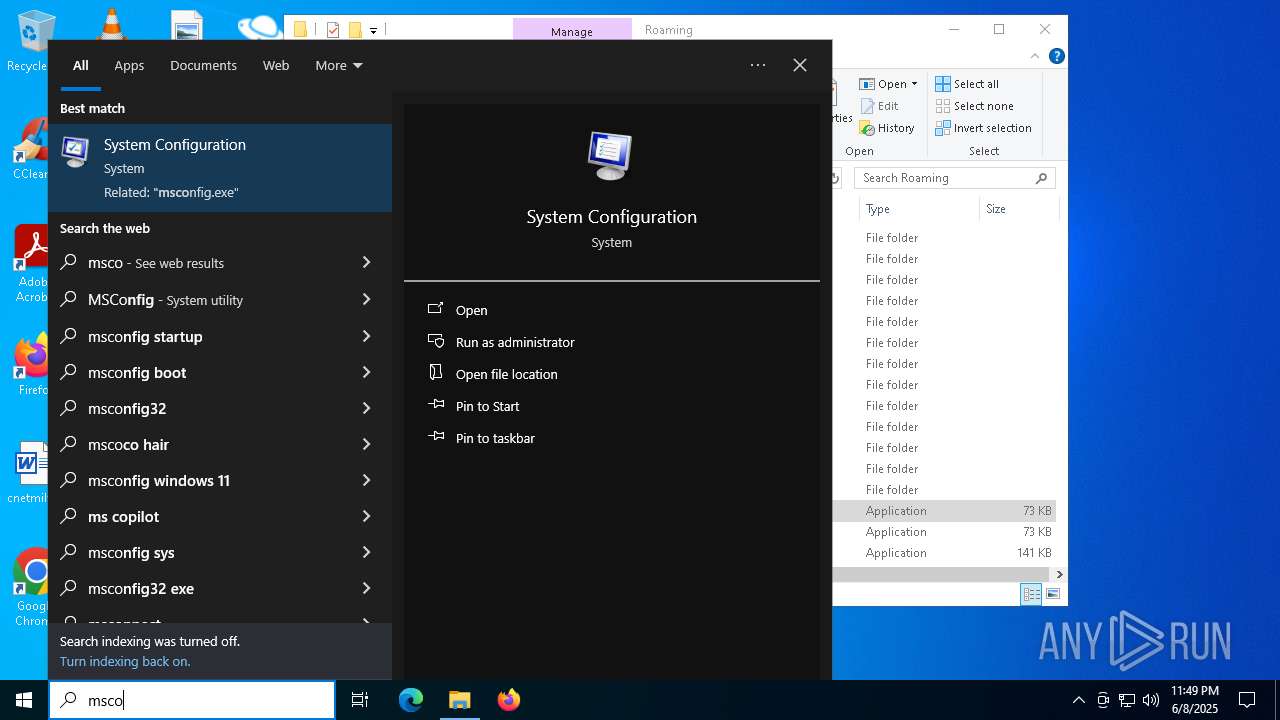
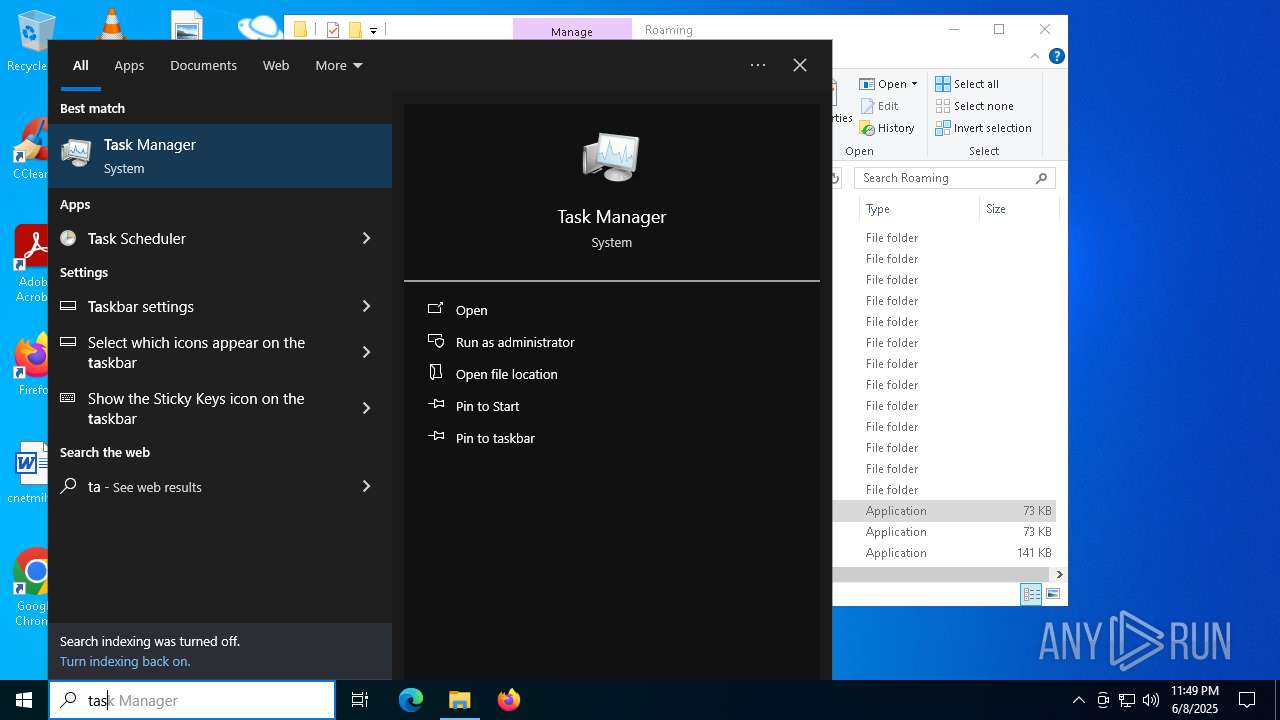
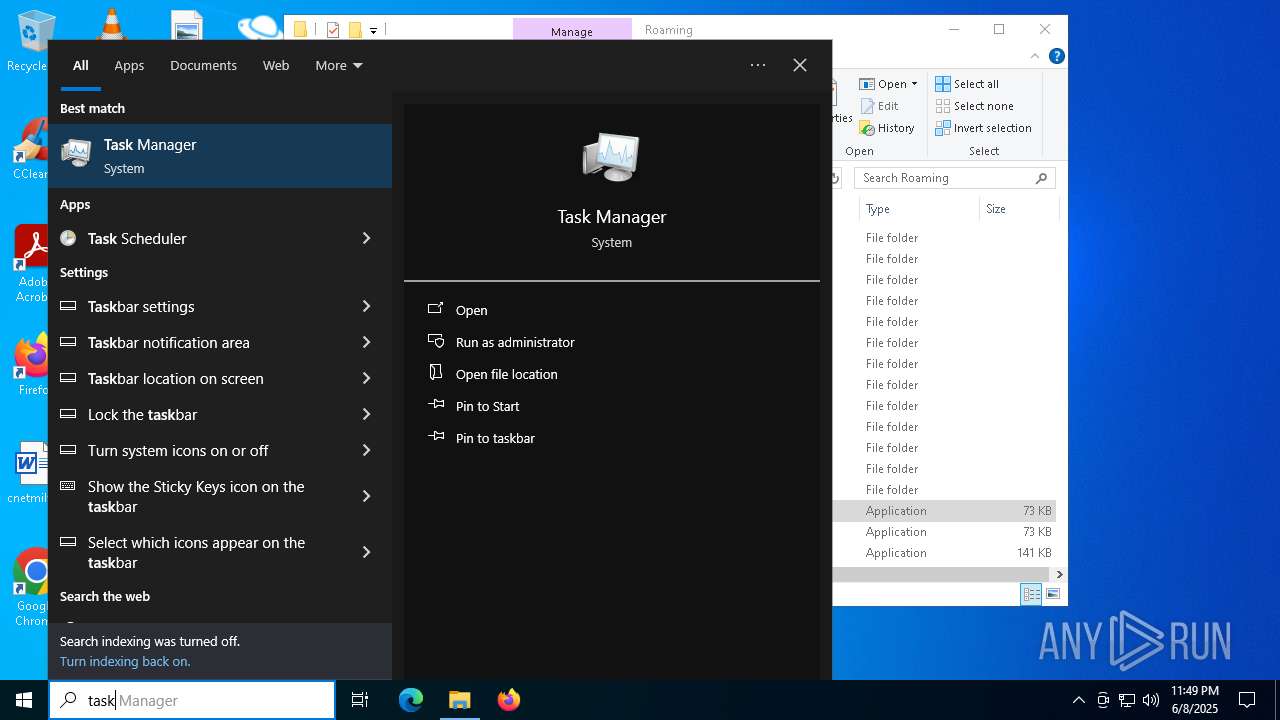
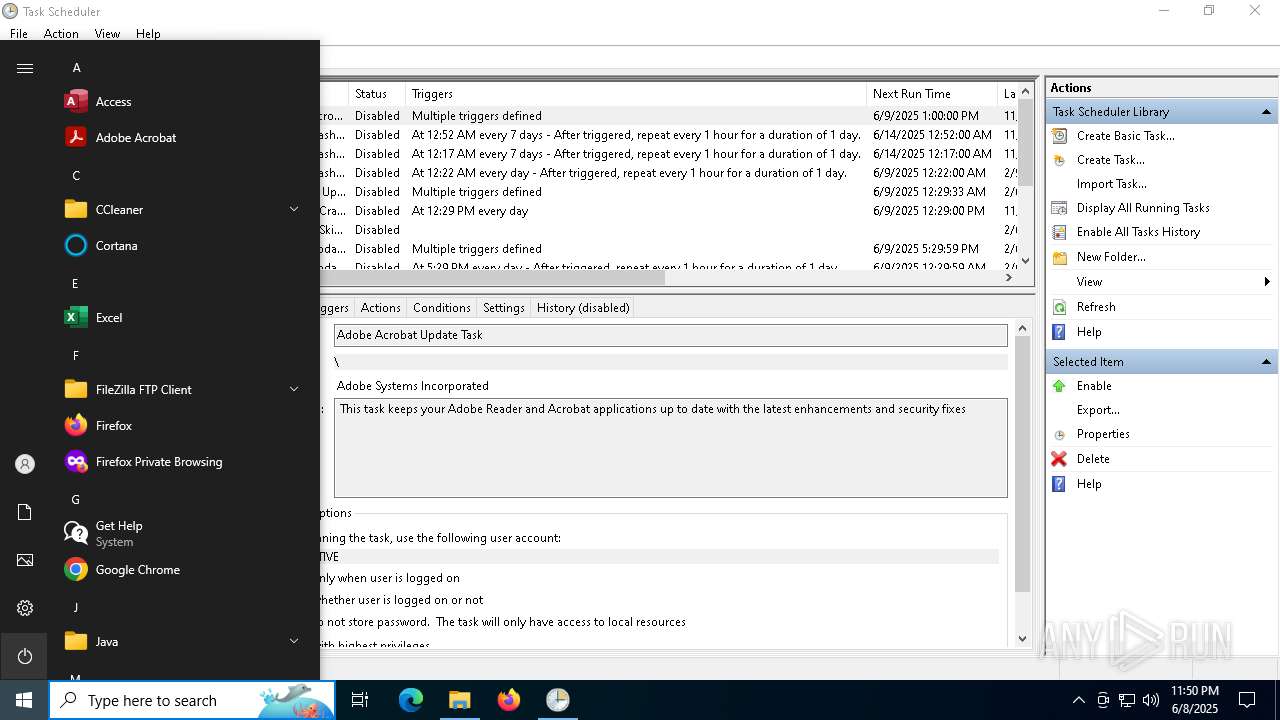
Manual execution by a user
- Xeno.exe (PID: 5400)
- Taskmgr.exe (PID: 7332)
- Taskmgr.exe (PID: 7252)
- Taskmgr.exe (PID: 2600)
- Taskmgr.exe (PID: 7596)
- svchost.exe (PID: 5416)
- mmc.exe (PID: 2432)
- mmc.exe (PID: 1132)
- svchost.exe (PID: 5452)
Reads the computer name
- jjsploit.exe (PID: 3364)
- Xeno.exe (PID: 5400)
- Xeno.exe (PID: 5984)
- system.exe (PID: 6368)
Checks supported languages
- jjsploit.exe (PID: 3364)
- Xeno.exe (PID: 5400)
- system.exe (PID: 6368)
- Xeno.exe (PID: 5984)
Creates files or folders in the user directory
- Xeno.exe (PID: 5400)
- system.exe (PID: 6368)
Reads the machine GUID from the registry
- Xeno.exe (PID: 5400)
- system.exe (PID: 6368)
Process checks computer location settings
- Xeno.exe (PID: 5400)
Reads Environment values
- system.exe (PID: 6368)
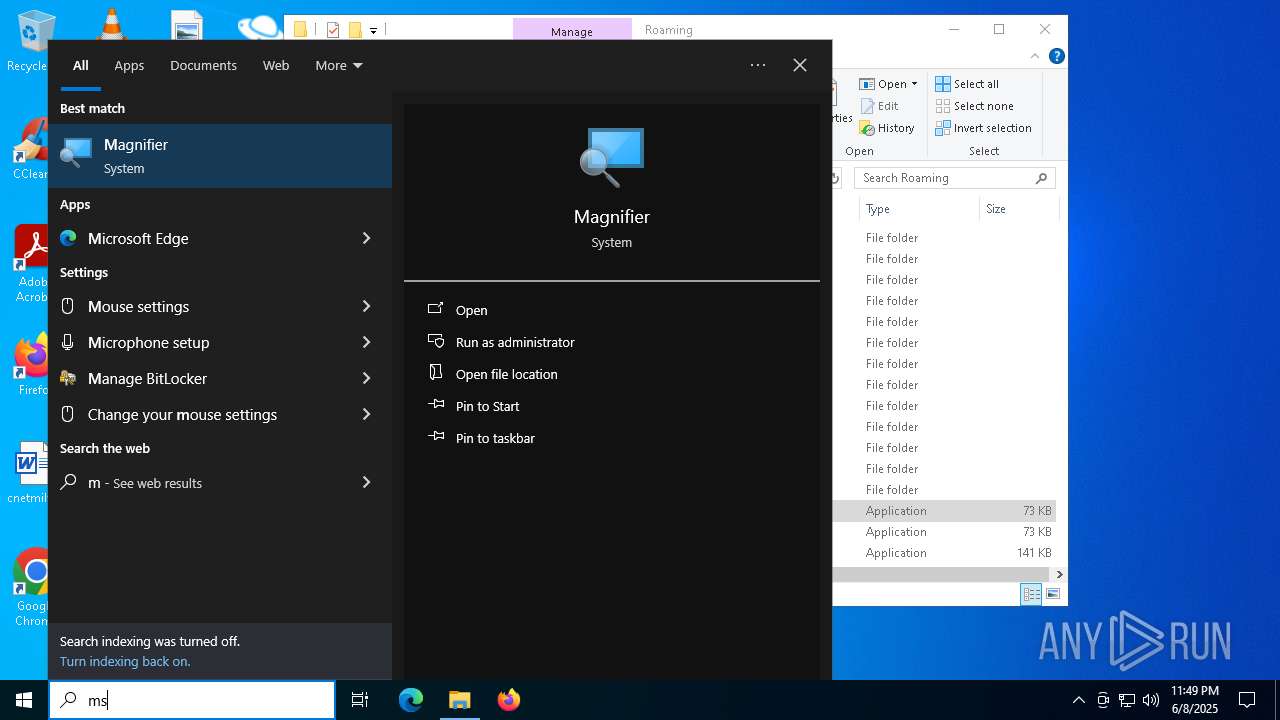
Disables trace logs
- system.exe (PID: 6368)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7252)
Launching a file from a Registry key
- system.exe (PID: 6368)
Launching a file from the Startup directory
- system.exe (PID: 6368)
Reads the software policy settings
- slui.exe (PID: 6040)
- slui.exe (PID: 7868)
Checks proxy server information
- system.exe (PID: 6368)
- slui.exe (PID: 7868)
Create files in a temporary directory
- system.exe (PID: 6368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(6368) system.exe
C2Dokuru-32085.portmap.io:32085
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.6
MutexRP8kurSOZfBAVtUO
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:08 16:58:08+00:00 |
| ImageFileCharacteristics: | Executable |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 332800 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5337e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.26100.2454 |
| ProductVersionNumber: | 6.2.26100.2454 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Обработчик команд Windows |
| FileVersion: | 6.2.26100.2454 |
| InternalName: | cmd |
| LegalCopyright: | © Корпорация Майкрософт. Все права защищены. |
| LegalTrademarks: | - |
| OriginalFileName: | cmd |
| ProductName: | Операционная система Microsoft® Windows® |
| ProductVersion: | 6.2.26100.2454 |
| AssemblyVersion: | 6.2.26100.2454 |
Total processes
293
Monitored processes
19
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2168 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2600 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\AppData\Local\Temp\jjsploit.exe" | C:\Users\admin\AppData\Local\Temp\jjsploit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Обработчик команд Windows Exit code: 0 Version: 6.2.26100.2454 Modules
| |||||||||||||||
| 5400 | "C:\Users\admin\Desktop\Xeno.exe" | C:\Users\admin\Desktop\Xeno.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5416 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5452 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
9 707
Read events
9 677
Write events
29
Delete events
1
Modification events
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6368) system.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\system_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
3
Suspicious files
45
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7252 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 6368 | system.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\svchost.lnk | binary | |
MD5:D60D3B1A88E626D1CF758C8011D13B89 | SHA256:4A27B3B242A415185985F6873A893745AF1A40E34FECD95E3A0C59CD82EF9DA8 | |||
| 2580 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.048.etl | binary | |
MD5:A23907B6FDD47DCABFDFD7CF2FCD7671 | SHA256:0C9C33FE9E984A2E5A70EBA51F36B9929A86199E424AF2F8080E1267B87DC970 | |||
| 6368 | system.exe | C:\Users\admin\AppData\Roaming\svchost.exe | executable | |
MD5:DCD2FB856701CB85E7C0913402FEEF7D | SHA256:00B419EF99233D634A6CB57940B5C6C61F35F151FD57BDA534DC5A33741D0716 | |||
| 6368 | system.exe | C:\Users\admin\AppData\Local\Temp\Log.tmp | text | |
MD5:48F952E36C0232D16AF67A8CA303EF40 | SHA256:62DF6237EEAFAFCE91E89980A6F855FAF097FB93C73333B8EBEA4A7F85937FC7 | |||
| 2580 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.046.etl | binary | |
MD5:A7A21FBC9D00F33F186B34A50E170C13 | SHA256:64CAC91E46D4FC832958232A658431CBF9D8D9F265653ACA2BEB32428D4688EC | |||
| 2580 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.049.etl | binary | |
MD5:5EA68411BF8E9EAF4621BAF73F61449E | SHA256:9D4CA5A1D871F819C139A498BB910A63576C2FE6367853544F8D172D8B6EBFF7 | |||
| 2580 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.042.etl | binary | |
MD5:C1F87CF12DD702D2185E703BA004D216 | SHA256:9D993487866C9538DC19F281A6346E1796E7478C7C164D61437AF6E698C66125 | |||
| 2580 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.043.etl | binary | |
MD5:8A2BDE0EAFA7E946196A1B114AB636E9 | SHA256:1C338CBDD9316D7FD8F208341466FEDC554A04D489B3A86C736EC3831A2F2BA2 | |||
| 2580 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.041.etl | binary | |
MD5:09359EE89B0634478ADFF73CDA7BFB12 | SHA256:4D800AC7C55960B107C9D3E40F63130407835E69DF4F5C558C500FC0BD20D8ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
188
DNS requests
45
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.100.248.115:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4284 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4284 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6368 | system.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5292 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4048 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7340 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
864 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.100.248.115:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
864 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
ip-api.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6368 | system.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6368 | system.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6368 | system.exe | A Network Trojan was detected | ET MALWARE Xworm/Agent Tesla Behavior – IP-API Source IP Associated with Hosting Provider Check |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .io) |
2168 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
5452 | svchost.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
5452 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |