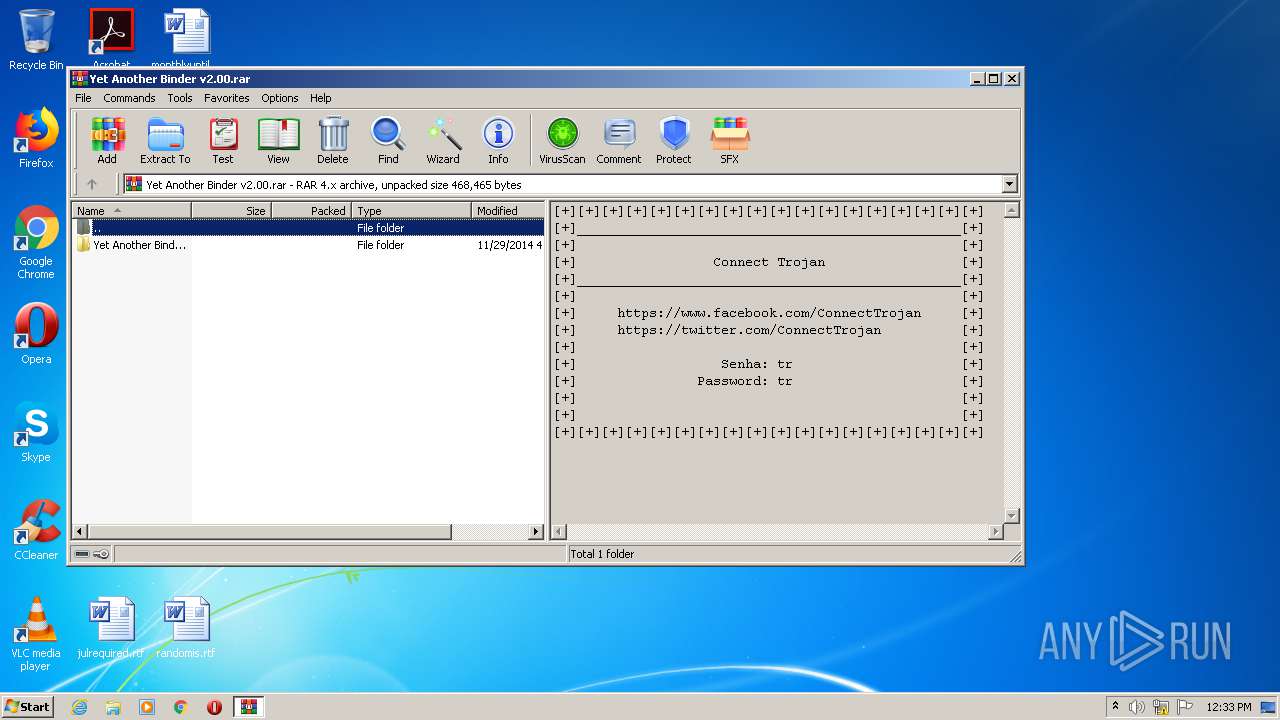
| File name: | Yet Another Binder v2.00.rar |
| Full analysis: | https://app.any.run/tasks/36b19d2a-85dd-4d73-87ab-c0cf757febec |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | July 23, 2020, 11:32:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 30DC183581F7878E93F5D263BB3151F3 |
| SHA1: | 43C280D31A3CF1D7E65125BA1FF7CEE66DDC464D |
| SHA256: | 12D1EBEAC1C2BBD130A80C0E1696E3C5494DAA40702C75A15A26539F76208B25 |
| SSDEEP: | 12288:rNoZXgyHzUuotrT/gMe+jlQ+SsbSVtq0ERzDg:mikzF+T/guLSsbJ93g |
MALICIOUS
Application was dropped or rewritten from another process
- Yab.exe (PID: 3012)
- YabSrv.exe (PID: 3640)
- DesktopLayer.exe (PID: 2260)
Changes the login/logoff helper path in the registry
- iexplore.exe (PID: 2904)
Connects to CnC server
- iexplore.exe (PID: 2904)
RAMNIT was detected
- iexplore.exe (PID: 2904)
SUSPICIOUS
Executable content was dropped or overwritten
- Yab.exe (PID: 3012)
- WinRAR.exe (PID: 2892)
Starts Internet Explorer
- DesktopLayer.exe (PID: 2260)
Creates files in the program directory
- iexplore.exe (PID: 2904)
INFO
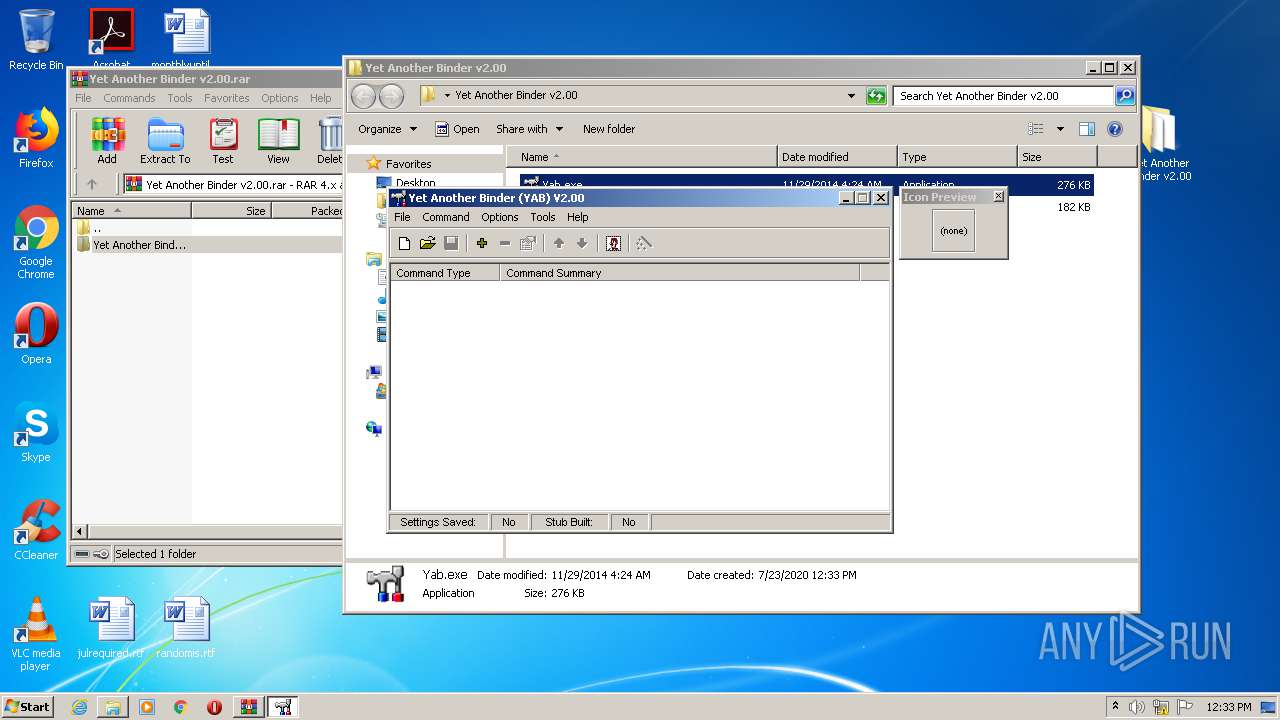
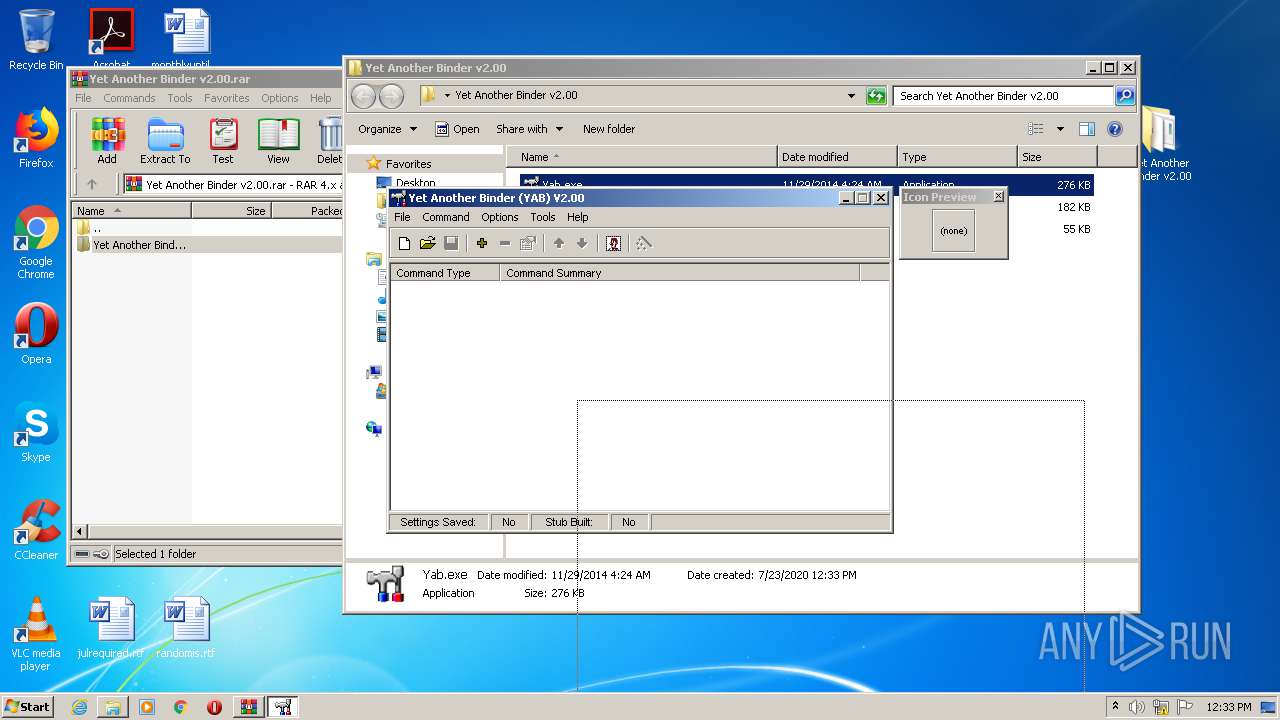
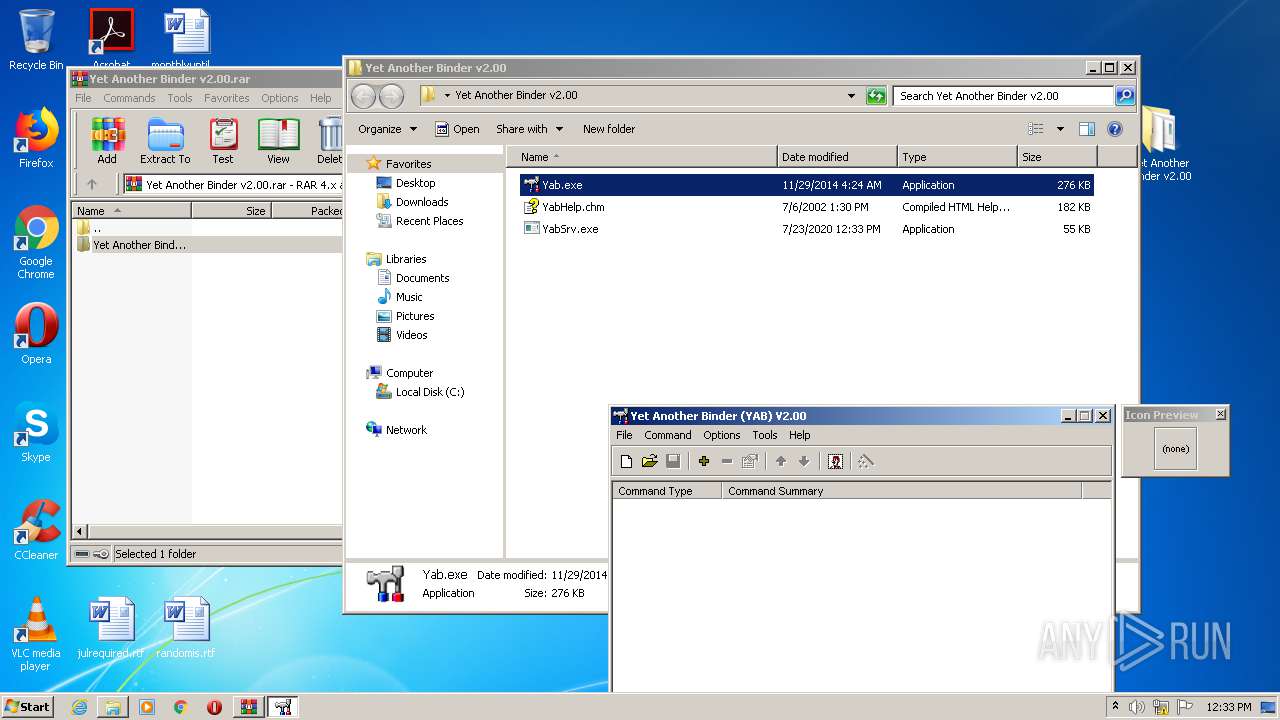
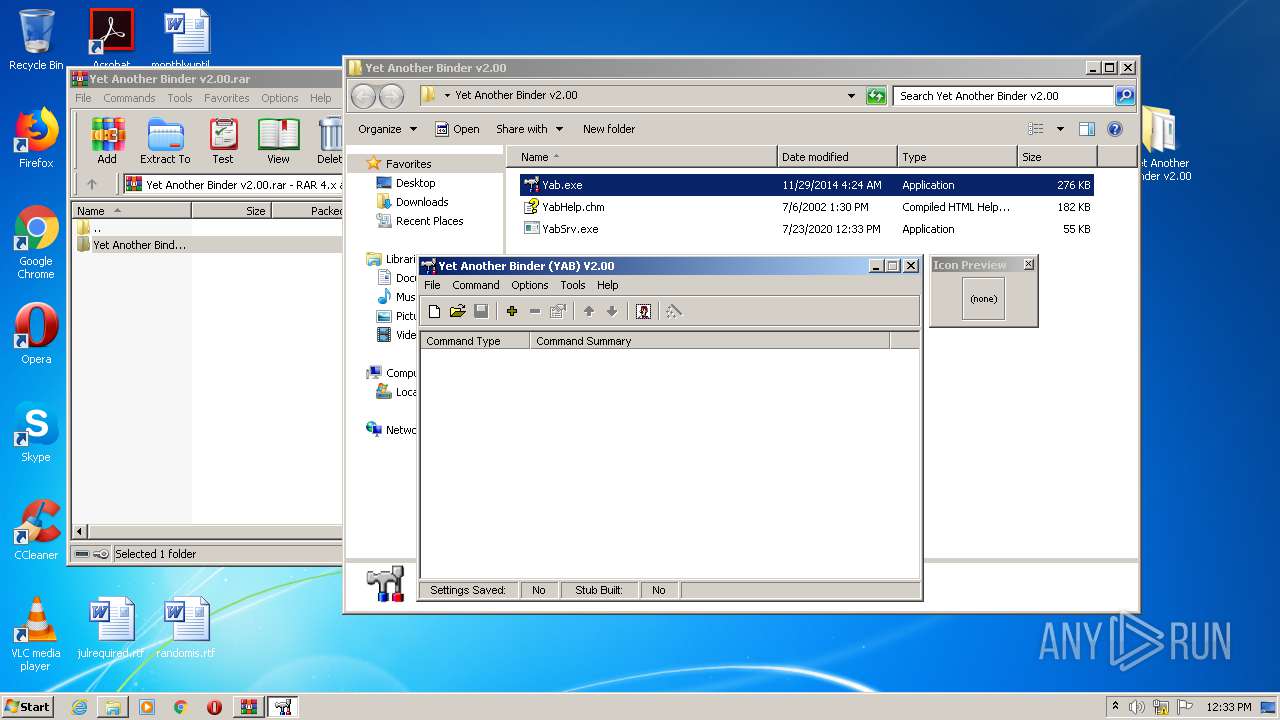
Manual execution by user
- Yab.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 271746 |
|---|---|
| UncompressedSize: | 282624 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2014:11:29 04:24:28 |
| PackingMethod: | Normal |
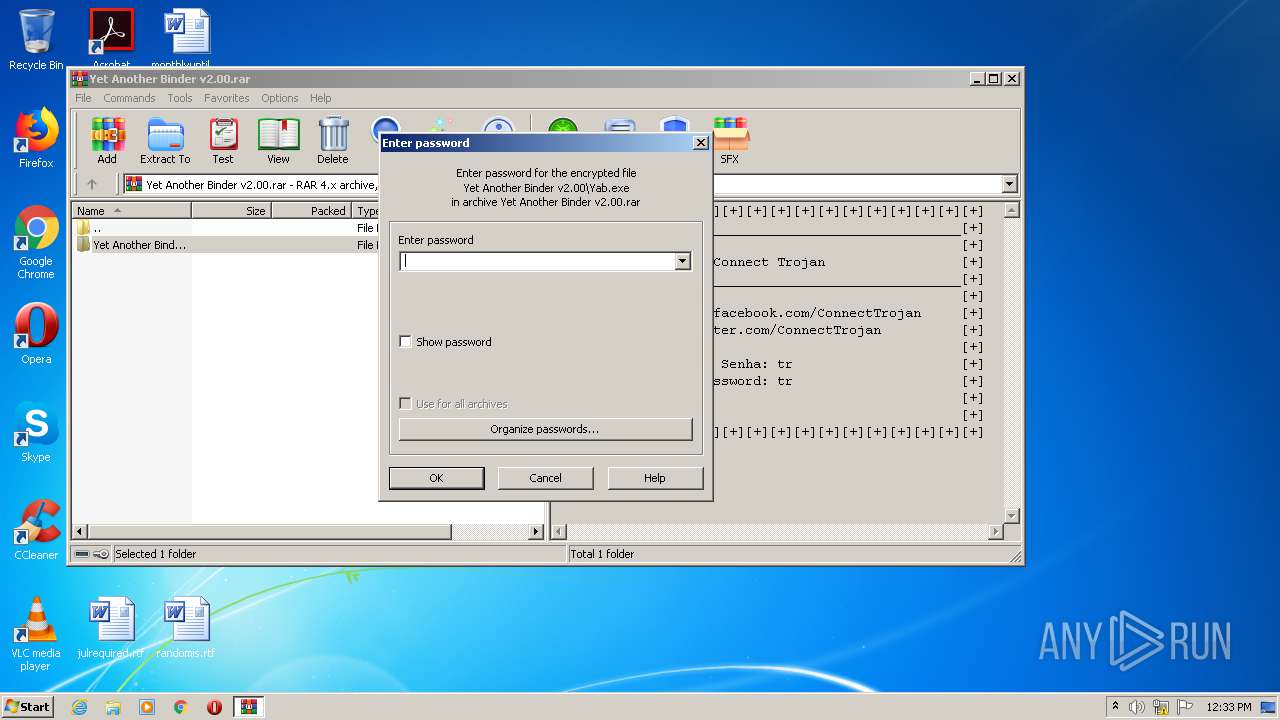
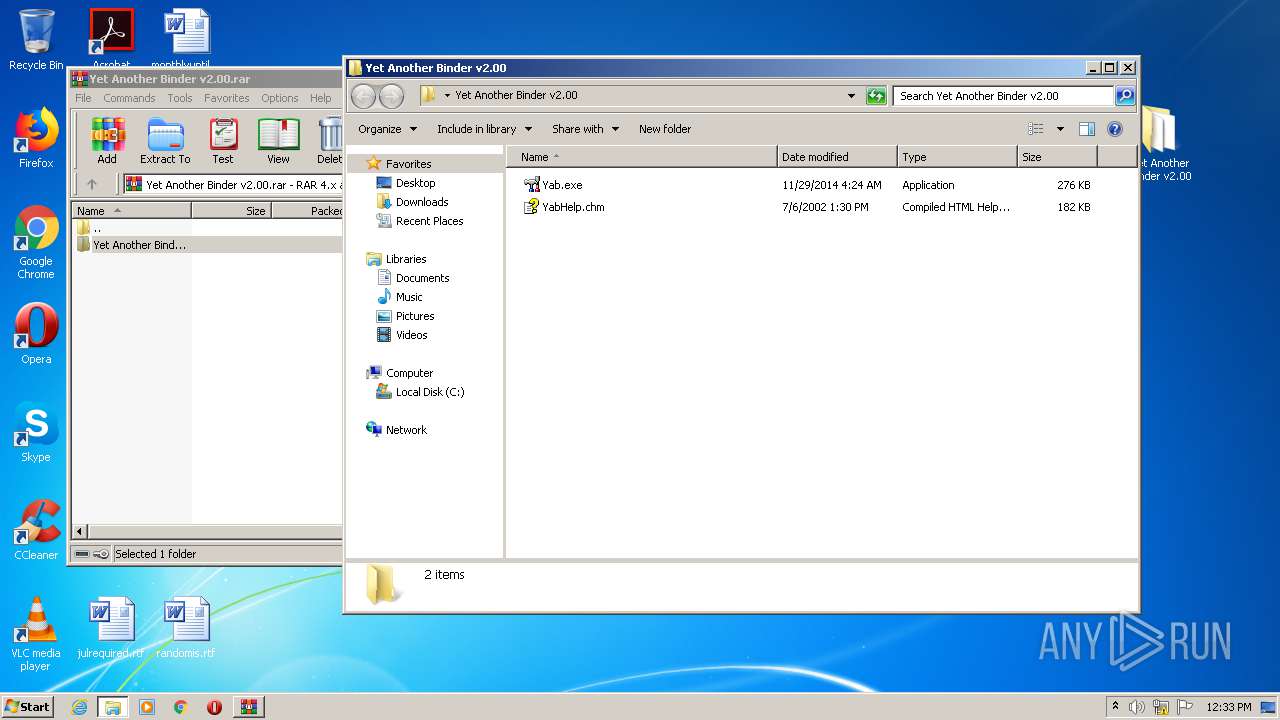
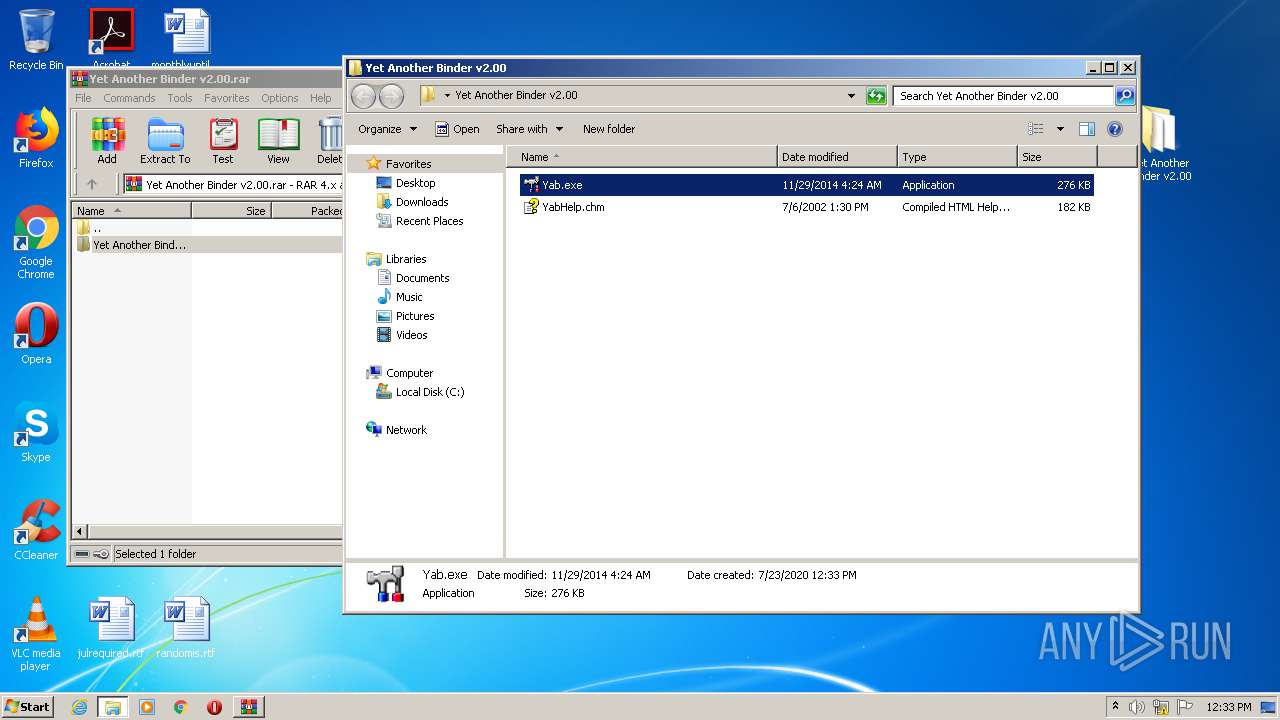
| ArchivedFileName: | Yet Another Binder v2.00\Yab.exe |
Total processes
38
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2260 | C:\Users\admin\Microsoft\DesktopLayer.exe | C:\Users\admin\Microsoft\DesktopLayer.exe | — | YabSrv.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Yet Another Binder v2.00.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2904 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | DesktopLayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3012 | "C:\Users\admin\Desktop\Yet Another Binder v2.00\Yab.exe" | C:\Users\admin\Desktop\Yet Another Binder v2.00\Yab.exe | explorer.exe | ||||||||||||
User: admin Company: Faceless Wonder Integrity Level: MEDIUM Description: Yet Another Binder (YAB) Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\Desktop\Yet Another Binder v2.00\YabSrv.exe" | C:\Users\admin\Desktop\Yet Another Binder v2.00\YabSrv.exe | — | Yab.exe | |||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
Total events
457
Read events
422
Write events
35
Delete events
0
Modification events
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Yet Another Binder v2.00.rar | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: c:\windows\system32\userinit.exe,,c:\users\admin\microsoft\desktoplayer.exe | |||
Executable files
2
Suspicious files
0
Text files
76
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | YabSrv.exe | C:\Users\admin\Microsoft\DesktopLayer.exe | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2892.32810\Yet Another Binder v2.00\Yab.exe | executable | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leame.htm | html | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm | html | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm | html | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | html | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeesMij.htm | html | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leggimi.htm | html | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Liesmich.htm | html | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeiaMe.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.23.110:80 | google.com | Google Inc. | US | whitelisted |
— | — | 72.26.218.70:443 | fget-career.com | Voxel Dot Net, Inc. | NL | malicious |
2904 | iexplore.exe | 72.26.218.70:443 | fget-career.com | Voxel Dot Net, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
fget-career.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2904 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
2904 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
2904 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
2904 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
1 ETPRO signatures available at the full report