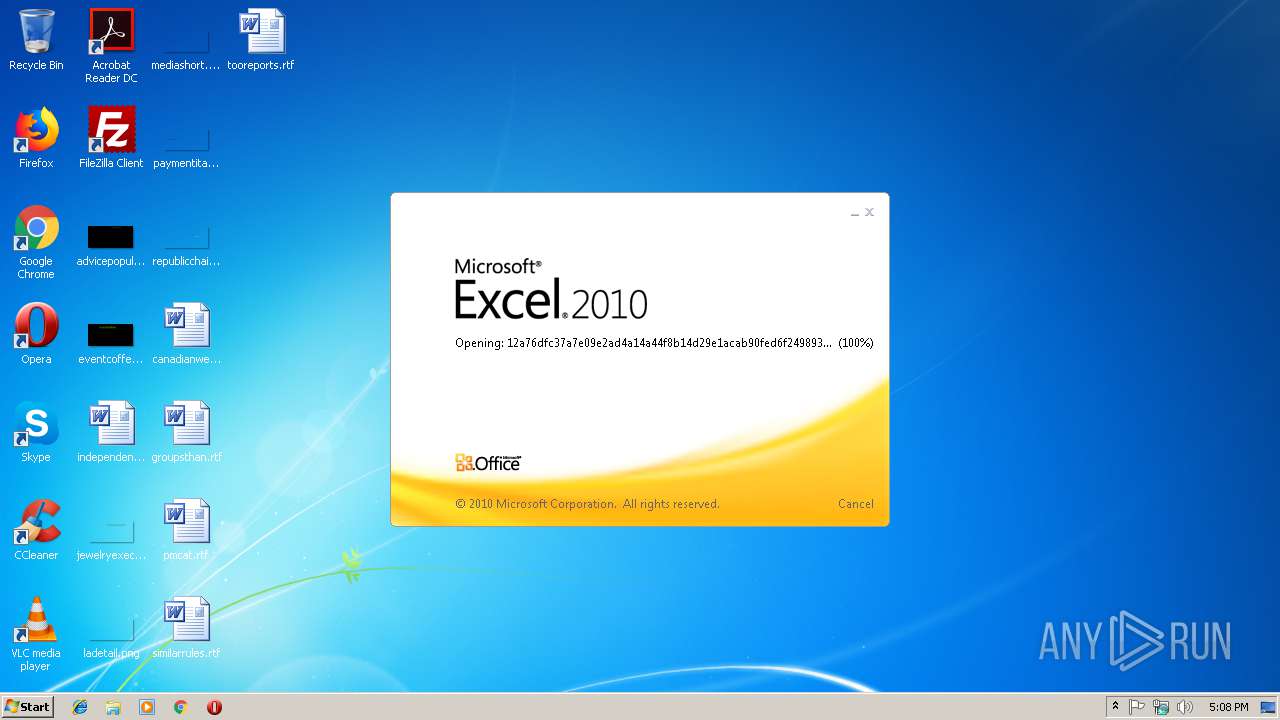
| File name: | 12a76dfc37a7e09e2ad4a14a44f8b14d29e1acab90fed6f249893671a7b90b4f |
| Full analysis: | https://app.any.run/tasks/e56d108e-956f-46ff-a354-bd4d0cc9ca4c |
| Verdict: | Malicious activity |
| Threats: | Hancitor was created in 2014 to drop other malware on infected machines. It is also known as Tordal and Chanitor. This malware is available as a service which makes it accessible tools to criminals and contributes to the popularity of this virus. |
| Analysis date: | January 17, 2019, 17:07:42 |
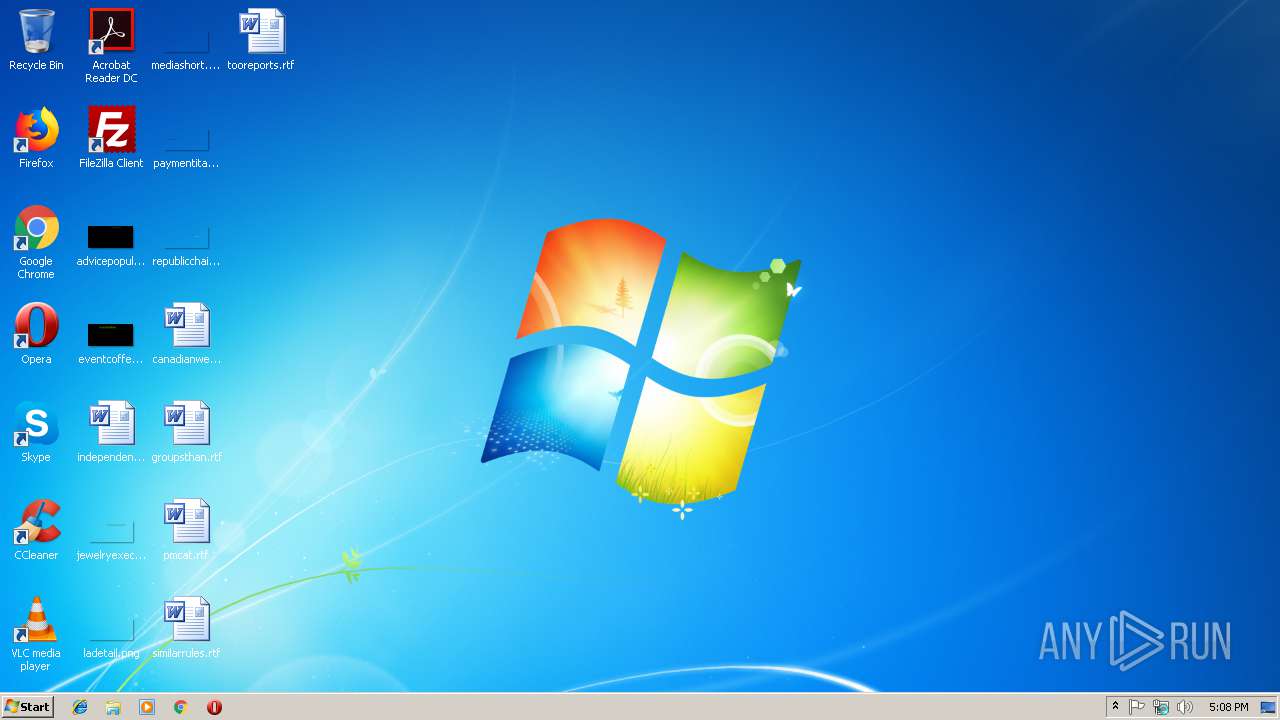
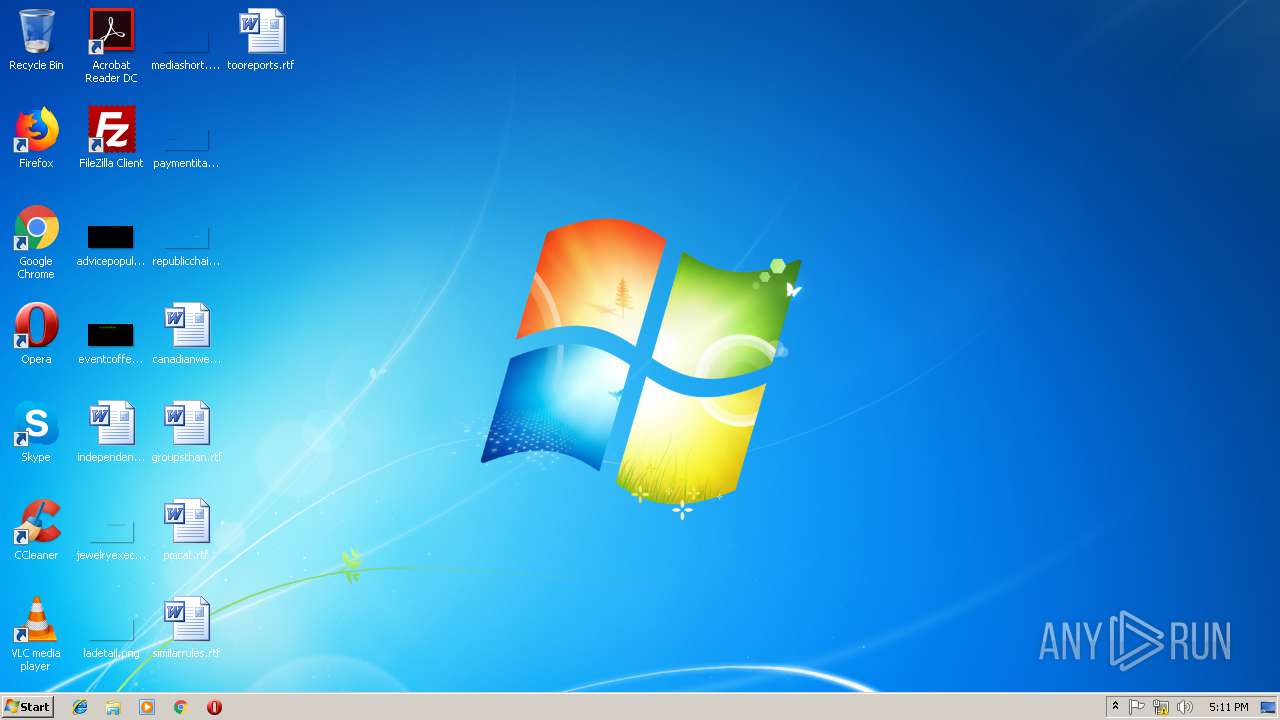
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Name of Creating Application: Microsoft Excel, Create Time/Date: Sat Sep 16 01:00:00 2006, Last Saved Time/Date: Thu Jan 17 09:21:43 2019, Security: 0 |
| MD5: | 8244344B9BDF42DEBD1ADA23E28C99B9 |
| SHA1: | 8D5ED91134AF0244CDEC219DEA02EB873065158E |
| SHA256: | 12A76DFC37A7E09E2AD4A14A44F8B14D29E1ACAB90FED6F249893671A7B90B4F |
| SSDEEP: | 6144:ITGrBZAPUGvtZkiWnkHLty/xcl8/dgCAyXbL5OphCIfwJKCJ5ODzTORGU6Q:LbZOphCIfw73YzyRGUR |
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2700)
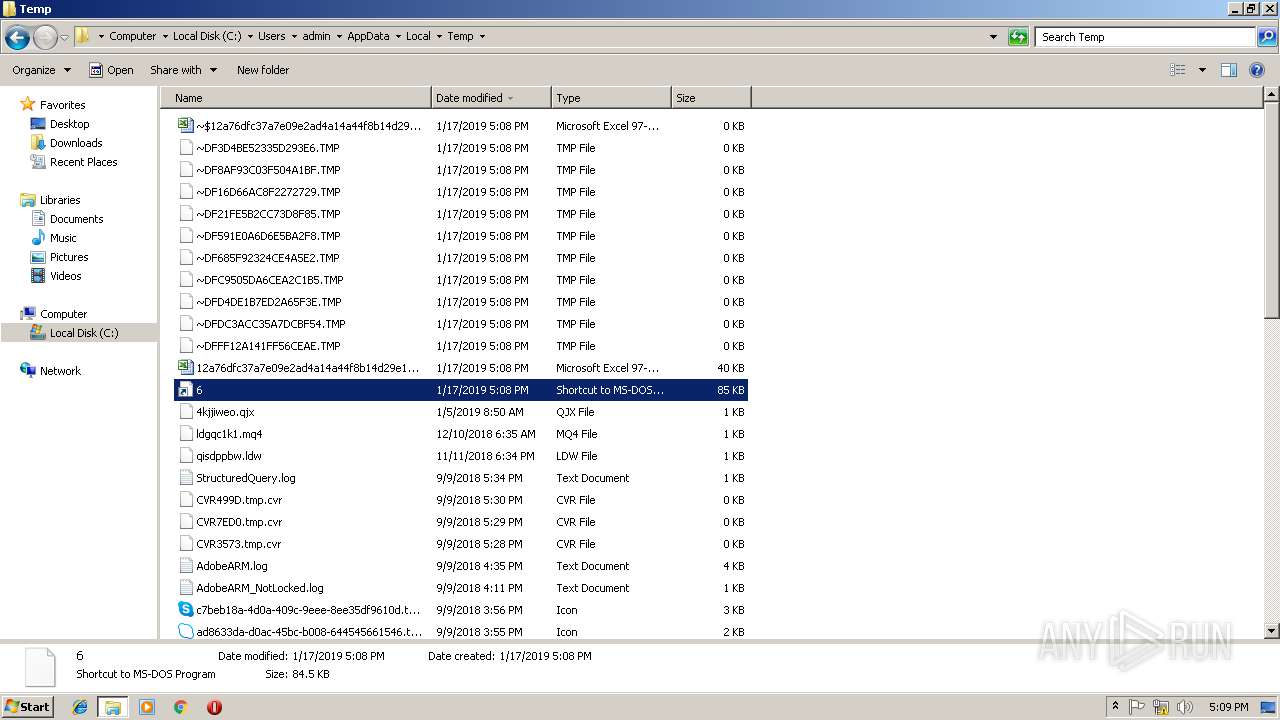
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2700)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2700)
Application was dropped or rewritten from another process
- 6.pif (PID: 2400)
- 6.pif (PID: 3156)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3152)
HANCITOR was detected
- 6.pif (PID: 2400)
- 6.pif (PID: 3156)
Connects to CnC server
- 6.pif (PID: 2400)
- 6.pif (PID: 3156)
SUSPICIOUS
Checks for external IP
- 6.pif (PID: 2400)
- 6.pif (PID: 3156)
Starts application with an unusual extension
- cmd.exe (PID: 3152)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2006:09:16 00:00:00 |
| ModifyDate: | 2019:01:17 09:21:43 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | - |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Лист2 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 26 |
| CompObjUserType: | ???? Microsoft Excel 2003 |
Total processes
41
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
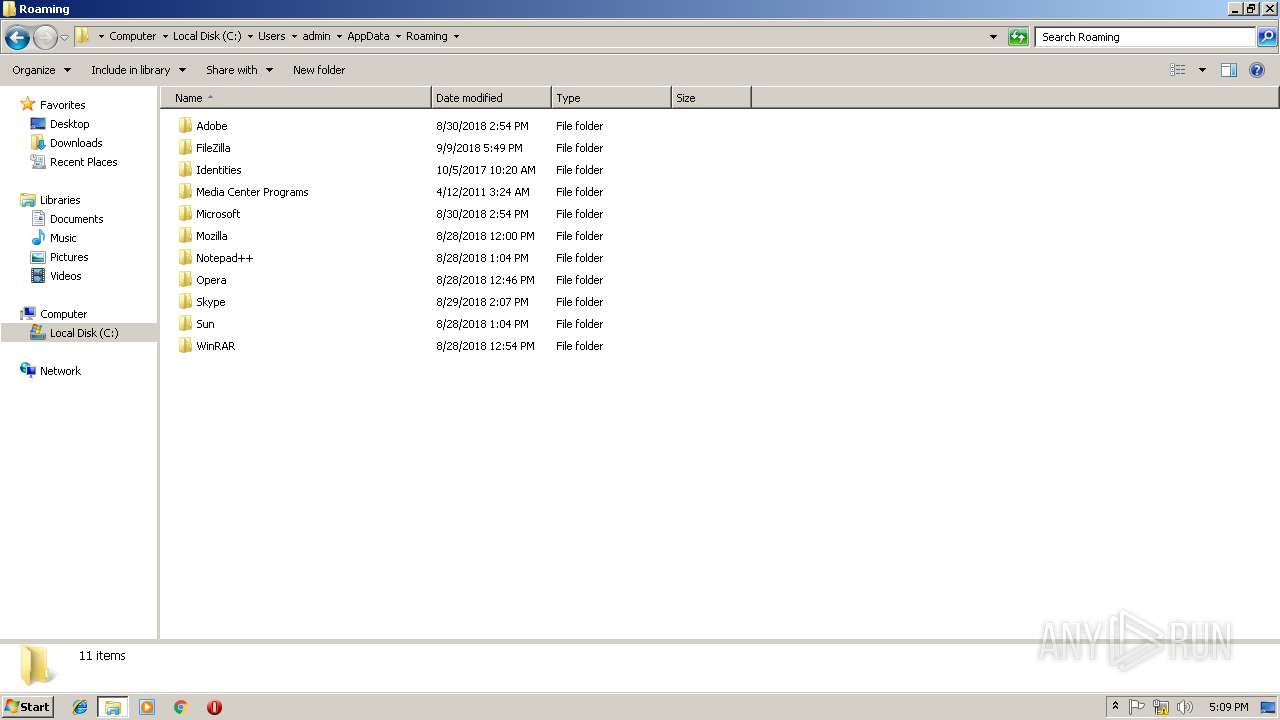
| 2400 | "C:\Users\admin\AppData\Local\Temp\6.pif" | C:\Users\admin\AppData\Local\Temp\6.pif | explorer.exe | ||||||||||||
User: admin Company: PostgreSQL Global Development Group Integrity Level: MEDIUM Description: initdb - initialize a new database cluster Exit code: 0 Version: 9.1.2 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3052 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3152 | cmd.exe /c ping localhost -n 100 && C:\Users\admin\AppData\Local\Temp\6.pif | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3156 | C:\Users\admin\AppData\Local\Temp\6.pif | C:\Users\admin\AppData\Local\Temp\6.pif | cmd.exe | ||||||||||||
User: admin Company: PostgreSQL Global Development Group Integrity Level: MEDIUM Description: initdb - initialize a new database cluster Exit code: 0 Version: 9.1.2 Modules
| |||||||||||||||
| 3652 | ping localhost -n 100 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
830
Read events
693
Write events
119
Delete events
18
Modification events
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | c7$ |
Value: 633724008C0A0000010000000000000000000000 | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 8C0A000010232C3587AED40100000000 | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | c7$ |
Value: 633724008C0A0000010000000000000000000000 | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2700) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\198EAA |
| Operation: | write | Name: | 198EAA |
Value: 040000008C0A00006600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0031003200610037003600640066006300330037006100370065003000390065003200610064003400610031003400610034003400660038006200310034006400320039006500310061006300610062003900300066006500640036006600320034003900380039003300360037003100610037006200390030006200340066002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000D0A7DB3687AED401AA8E1900AA8E190000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
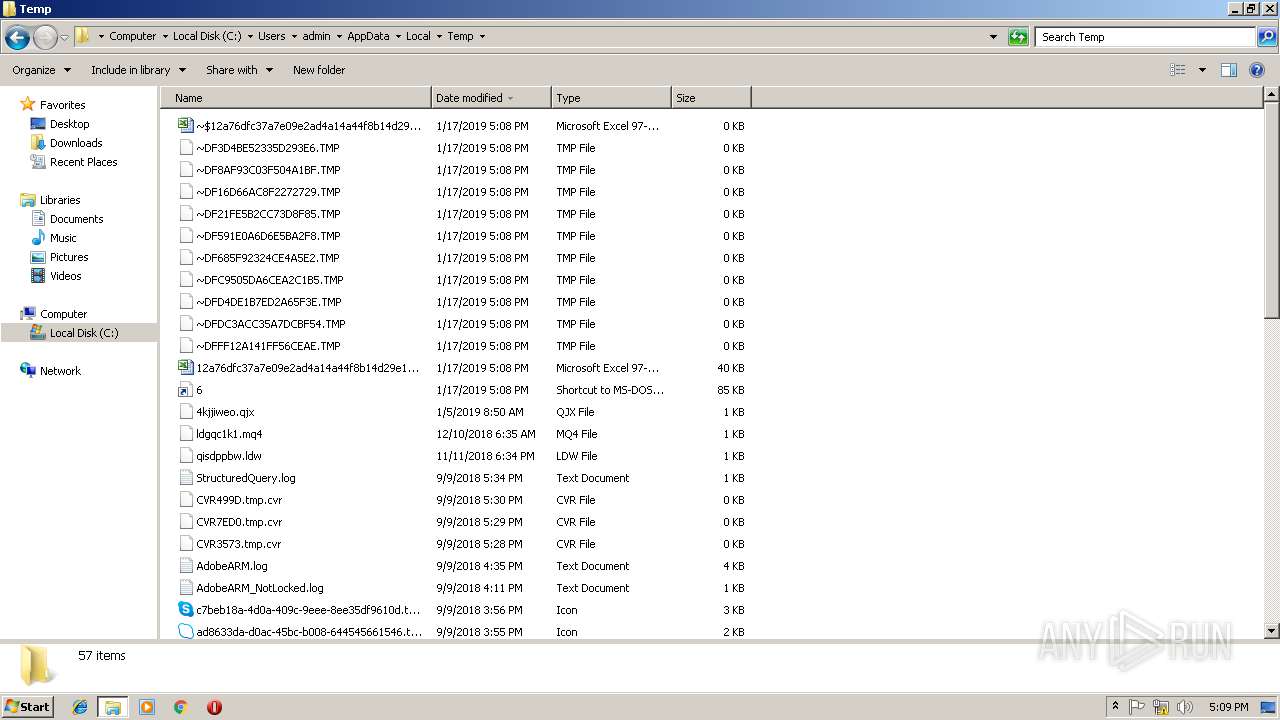
Executable files
2
Suspicious files
2
Text files
0
Unknown types
1
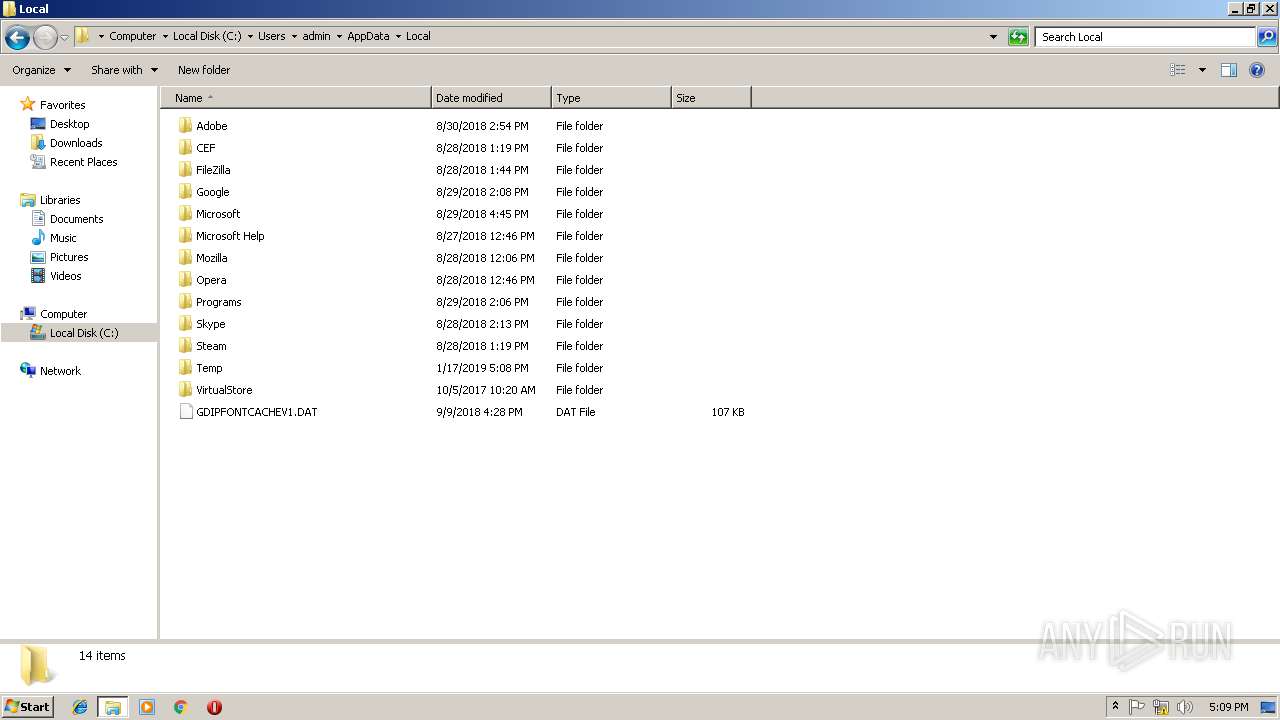
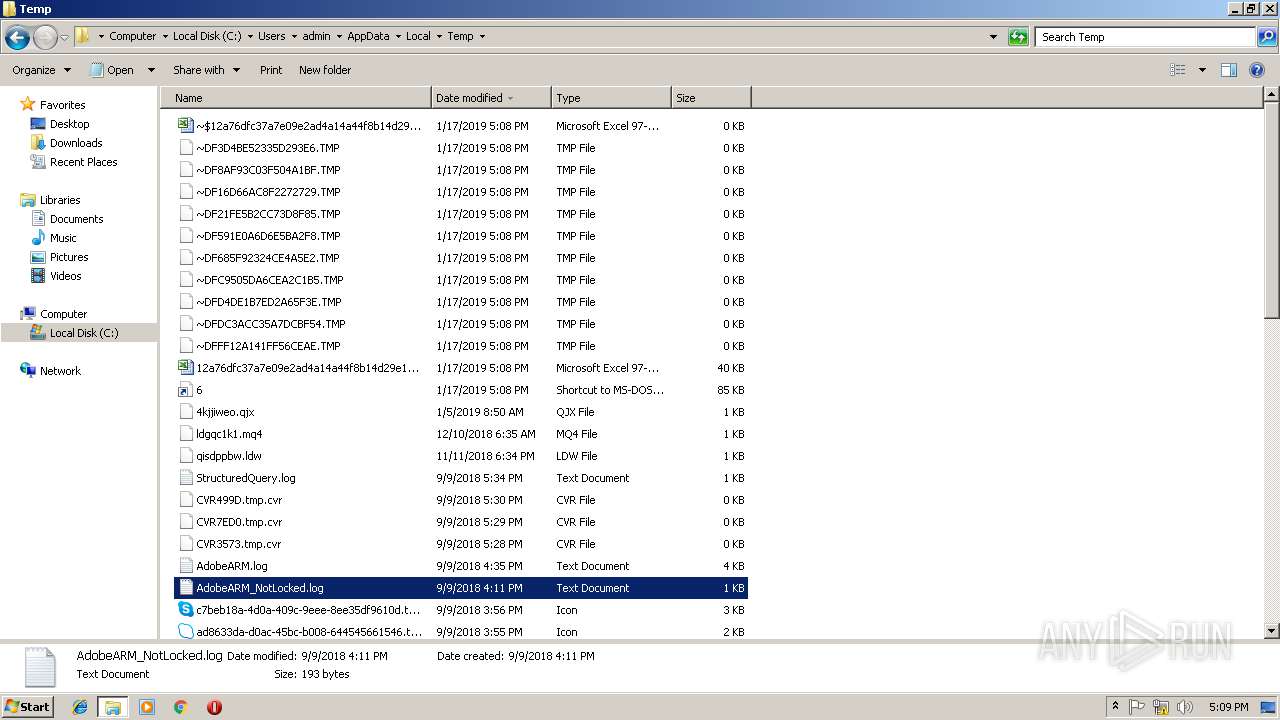
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR87D3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF21FE5B2CC73D8F85.TMP | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\C3A91000 | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF685F92324CE4A5E2.TMP | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF3D4BE52335D293E6.TMP | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFC9505DA6CEA2C1B5.TMP | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF16D66AC8F2272729.TMP | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFFF12A141FF56CEAE.TMP | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFDC3ACC35A7DCBF54.TMP | — | |
MD5:— | SHA256:— | |||
| 2700 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF591E0A6D6E5BA2F8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
3
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2400 | 6.pif | GET | 200 | 23.21.121.219:80 | http://api.ipify.org/ | US | text | 13 b | shared |
2400 | 6.pif | POST | 200 | 185.178.47.247:80 | http://toldlighnosup.com/4/forum.php | UA | text | 12 b | malicious |
3156 | 6.pif | GET | 200 | 54.243.123.39:80 | http://api.ipify.org/ | US | text | 13 b | shared |
3156 | 6.pif | POST | 200 | 185.178.47.247:80 | http://toldlighnosup.com/4/forum.php | UA | text | 12 b | malicious |
2400 | 6.pif | POST | 200 | 185.178.47.247:80 | http://toldlighnosup.com/4/forum.php | UA | text | 12 b | malicious |
3156 | 6.pif | POST | 200 | 185.178.47.247:80 | http://toldlighnosup.com/4/forum.php | UA | text | 12 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | 6.pif | 23.21.121.219:80 | api.ipify.org | Amazon.com, Inc. | US | whitelisted |
2400 | 6.pif | 185.178.47.247:80 | toldlighnosup.com | — | UA | malicious |
3156 | 6.pif | 54.243.123.39:80 | api.ipify.org | Amazon.com, Inc. | US | whitelisted |
3156 | 6.pif | 185.178.47.247:80 | toldlighnosup.com | — | UA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
toldlighnosup.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2400 | 6.pif | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
2400 | 6.pif | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
3156 | 6.pif | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
3156 | 6.pif | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2400 | 6.pif | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
3156 | 6.pif | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
6.pif | ux9L40o |
6.pif | ux9L40o |