| File name: | sunilmilkcentre.exe |
| Full analysis: | https://app.any.run/tasks/9179606b-7de7-4bce-9f66-90fffd4bb488 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | April 10, 2026, 16:17:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | F572EDE80A77DEA54EE24935C54602DB |
| SHA1: | 05C4C806500D11865AF62D295221AB5C9BDF928C |
| SHA256: | 129DC1113EC0E22BB9C2FF5A3E71527DBBE2B2E06AB9EF6F02958360FEF04C97 |
| SSDEEP: | 49152:xZZ8pHUw2HoV6nUr9a7Ke7CDElgFtnivEHt/3DgGPwpMDM3knTWzzqJLoGd4uIH8:82HosnUr07Ke7CDElgFtnictDg4WCY |
MALICIOUS
QUASAR has been detected (YARA)
- sunilmilkcentre.exe (PID: 1456)
SUSPICIOUS
No suspicious indicators.INFO
Reads Environment values
- sunilmilkcentre.exe (PID: 1456)
Checks supported languages
- sunilmilkcentre.exe (PID: 1456)
Reads the computer name
- sunilmilkcentre.exe (PID: 1456)
Reads the machine GUID from the registry
- sunilmilkcentre.exe (PID: 1456)
There is functionality for taking screenshot (YARA)
- sunilmilkcentre.exe (PID: 1456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(1456) sunilmilkcentre.exe
C2 (2)sunilmilkcentre.in.net:4782
qh88vh.jp.net:4782
Version1.4.1
Sub_Dirsunilmilkcentre.in.net
Install_Namesunilmilkcentre.in.net.exe
Mutexsunilmilkcentre.in.net
Startupsunilmilkcentre.in.net
Tagsunilmilkcentre.in.net
LogDirLogs
SignaturedNZpoLLUVhIUfmcJK6lRbtHWhMG7UA3NW8QEXqO9217ycZ87EAjwcgOobztpYTP/3AKM9VPila3a+ZsXk4GhkQ9sEJVaRYWWZ1ZDuMwvi0OLHBgKX3x2cdfcGMVq3wQ17cM20l2OuhimGcV5PDUhwgZOoNfrfSNH3FFBxq8V1MH4NgjOzE/KENPD1X49h8jmzbUmGEbu7Y36rZGlLYRDHDnFOC/b4r4lLRYfx4jdQkzUBAvryPUvzMGyWlK1FhYzPSQVGnyFpNk5qkZawCUvU7gvY275i8UYwB5X9NhqisAN...
CertificateMIIE9DCCAtygAwIBAgIQAMyLxOGLdEdAA8ENgAq9QzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI2MDIxODA4MDUyOVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAgg/7VZFyN7dtlKk2iMKEFOIeUL/5GWZjvfRksIadzM8hqPhf42HDk6jOat07AqfE4+5fKi4c...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 16:16:39+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261952 |
| InitializedDataSize: | 373760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e46e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | sunilmilkcentre.in.net |
| FileDescription: | - |
| FileVersion: | 0.0.0.0 |
| InternalName: | sunilmilkcentre.in.net |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | sunilmilkcentre.in.net |
| ProductName: | sunilmilkcentre.in.net |
| ProductVersion: | 0.0.0.1 |
| AssemblyVersion: | 0.0.0.1 |
Total processes
133
Monitored processes
2
Malicious processes
1
Suspicious processes
0
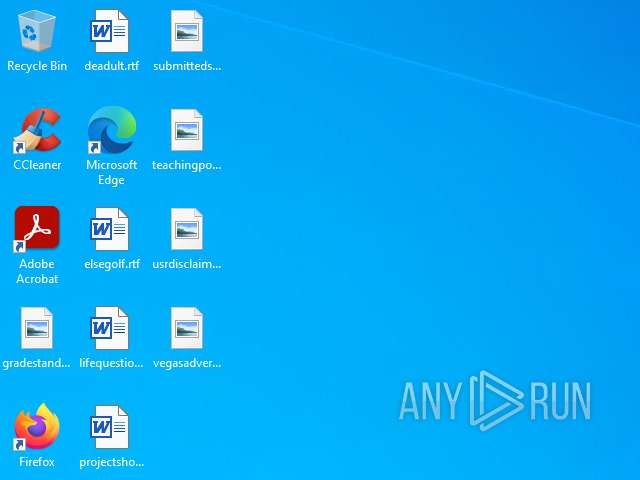
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1456 | "C:\Users\admin\Desktop\sunilmilkcentre.exe" | C:\Users\admin\Desktop\sunilmilkcentre.exe | explorer.exe | ||||||||||||
User: admin Company: sunilmilkcentre.in.net Integrity Level: MEDIUM Version: 0.0.0.0 Modules
Quasar(PID) Process(1456) sunilmilkcentre.exe C2 (2)sunilmilkcentre.in.net:4782 qh88vh.jp.net:4782 Version1.4.1 Sub_Dirsunilmilkcentre.in.net Install_Namesunilmilkcentre.in.net.exe Mutexsunilmilkcentre.in.net Startupsunilmilkcentre.in.net Tagsunilmilkcentre.in.net LogDirLogs SignaturedNZpoLLUVhIUfmcJK6lRbtHWhMG7UA3NW8QEXqO9217ycZ87EAjwcgOobztpYTP/3AKM9VPila3a+ZsXk4GhkQ9sEJVaRYWWZ1ZDuMwvi0OLHBgKX3x2cdfcGMVq3wQ17cM20l2OuhimGcV5PDUhwgZOoNfrfSNH3FFBxq8V1MH4NgjOzE/KENPD1X49h8jmzbUmGEbu7Y36rZGlLYRDHDnFOC/b4r4lLRYfx4jdQkzUBAvryPUvzMGyWlK1FhYzPSQVGnyFpNk5qkZawCUvU7gvY275i8UYwB5X9NhqisAN... CertificateMIIE9DCCAtygAwIBAgIQAMyLxOGLdEdAA8ENgAq9QzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI2MDIxODA4MDUyOVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAgg/7VZFyN7dtlKk2iMKEFOIeUL/5GWZjvfRksIadzM8hqPhf42HDk6jOat07AqfE4+5fKi4c... | |||||||||||||||
| 6884 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 580
Read events
3 579
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6884) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
22
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3044 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3044 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6884 | slui.exe | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | text | 512 b | whitelisted |
6884 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | text | 512 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 400 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 400 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | US | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3044 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7352 | slui.exe | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.241.201:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3044 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
3044 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |