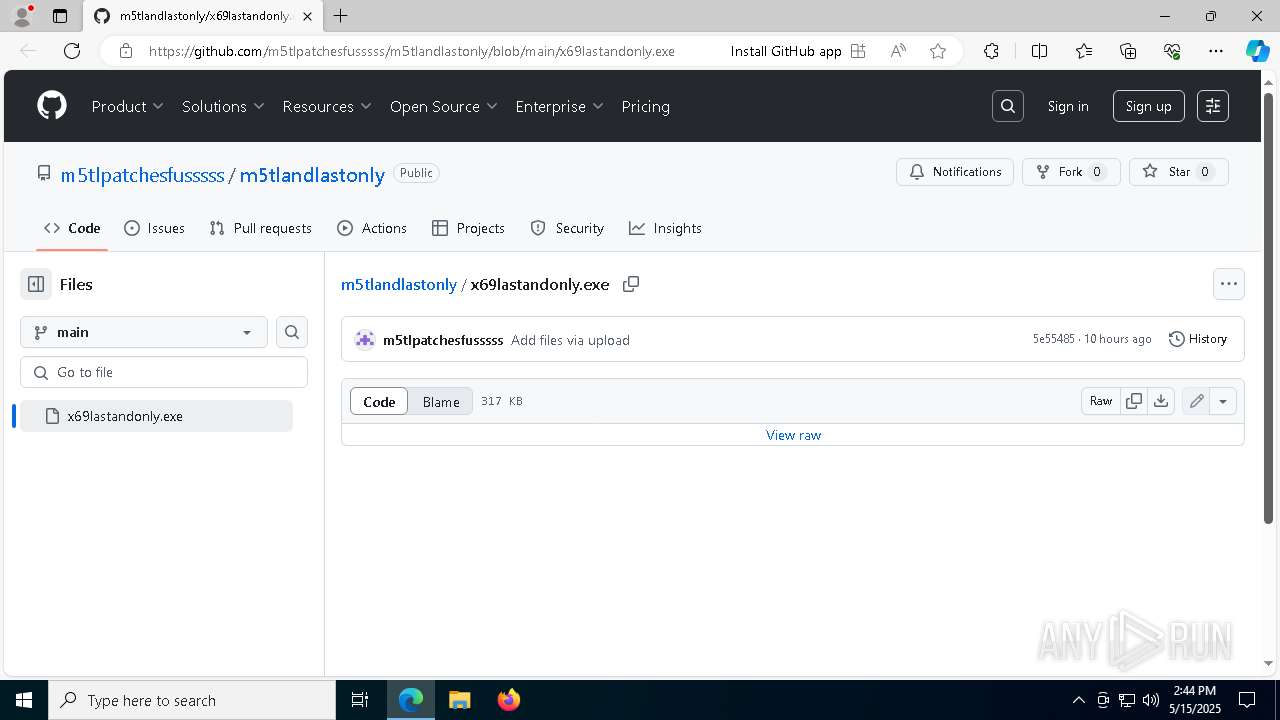
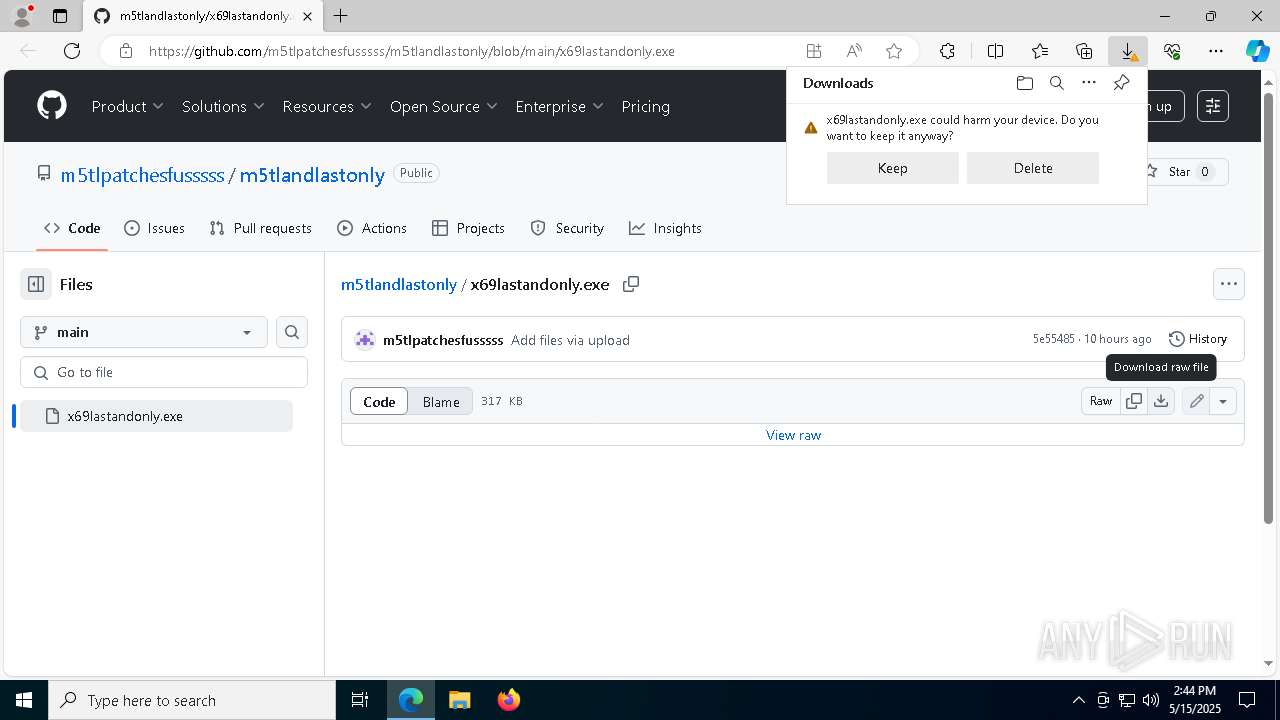
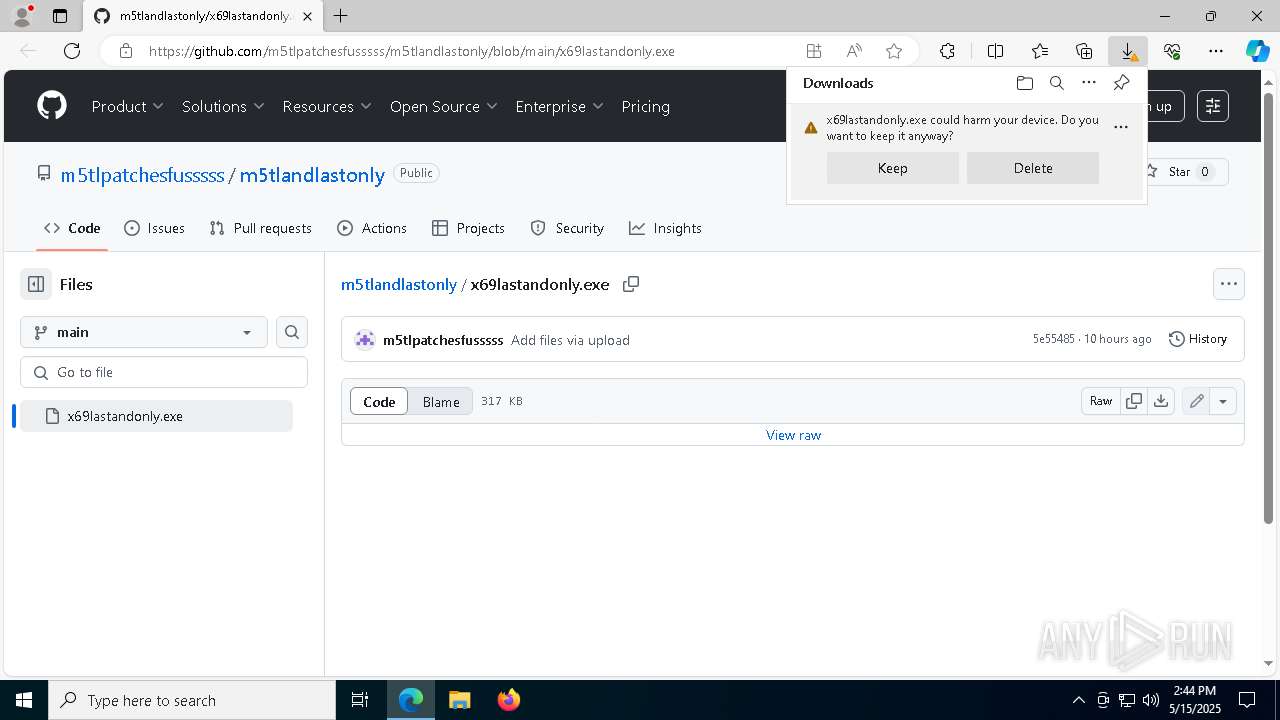
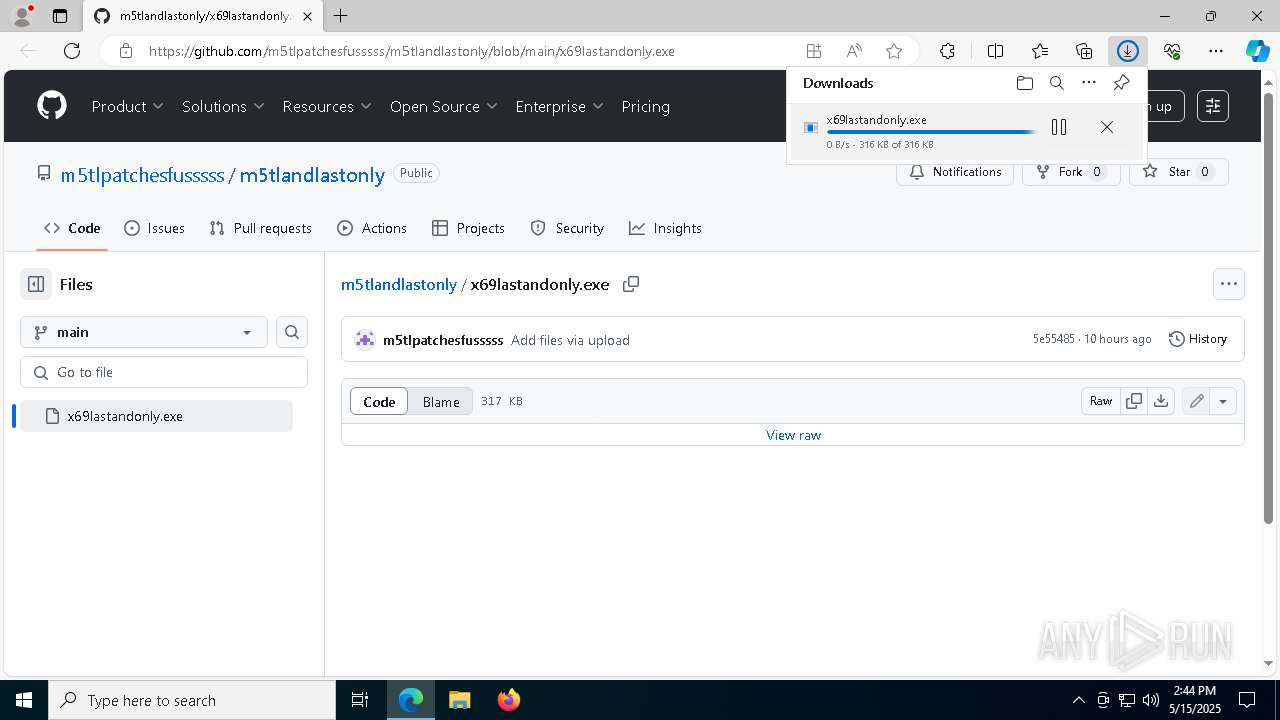
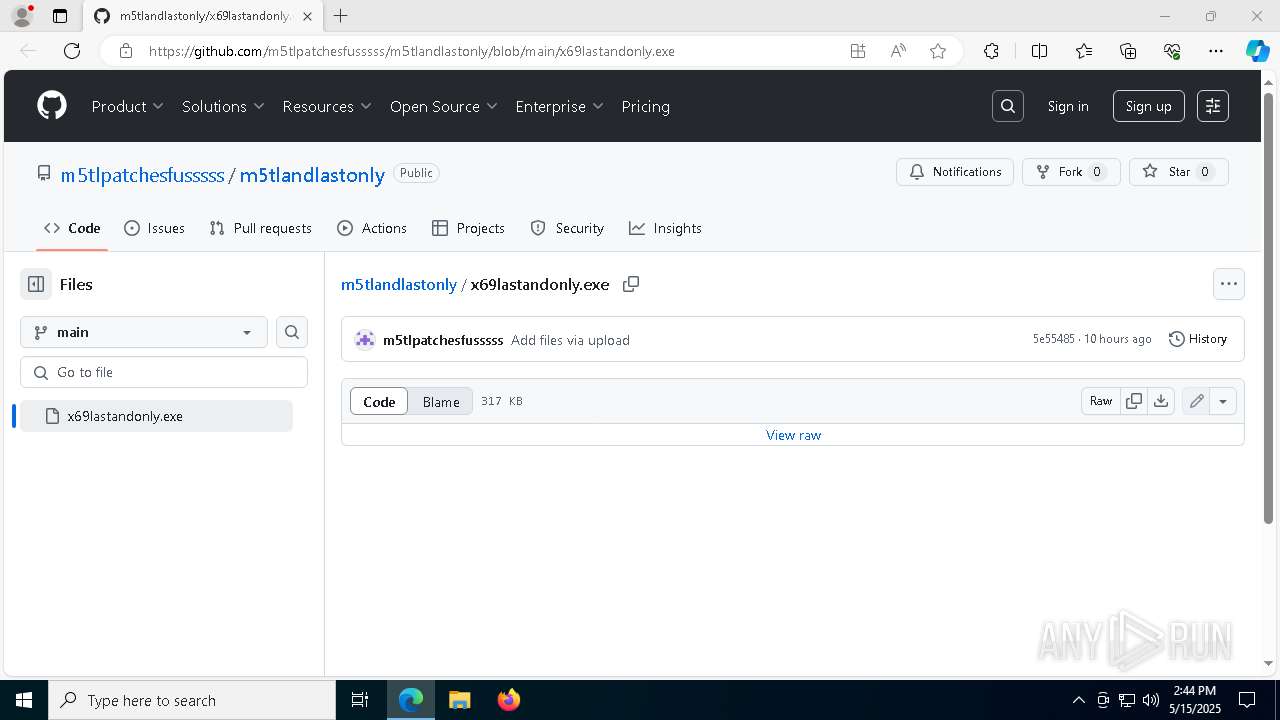
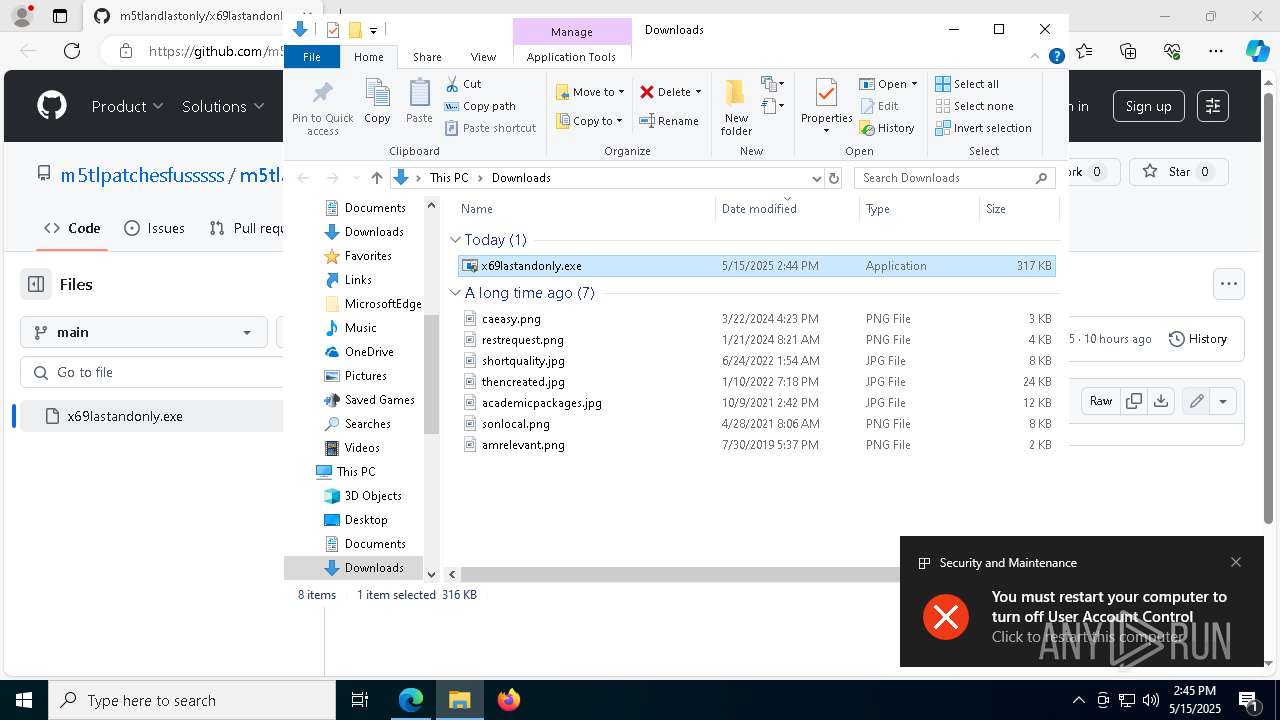
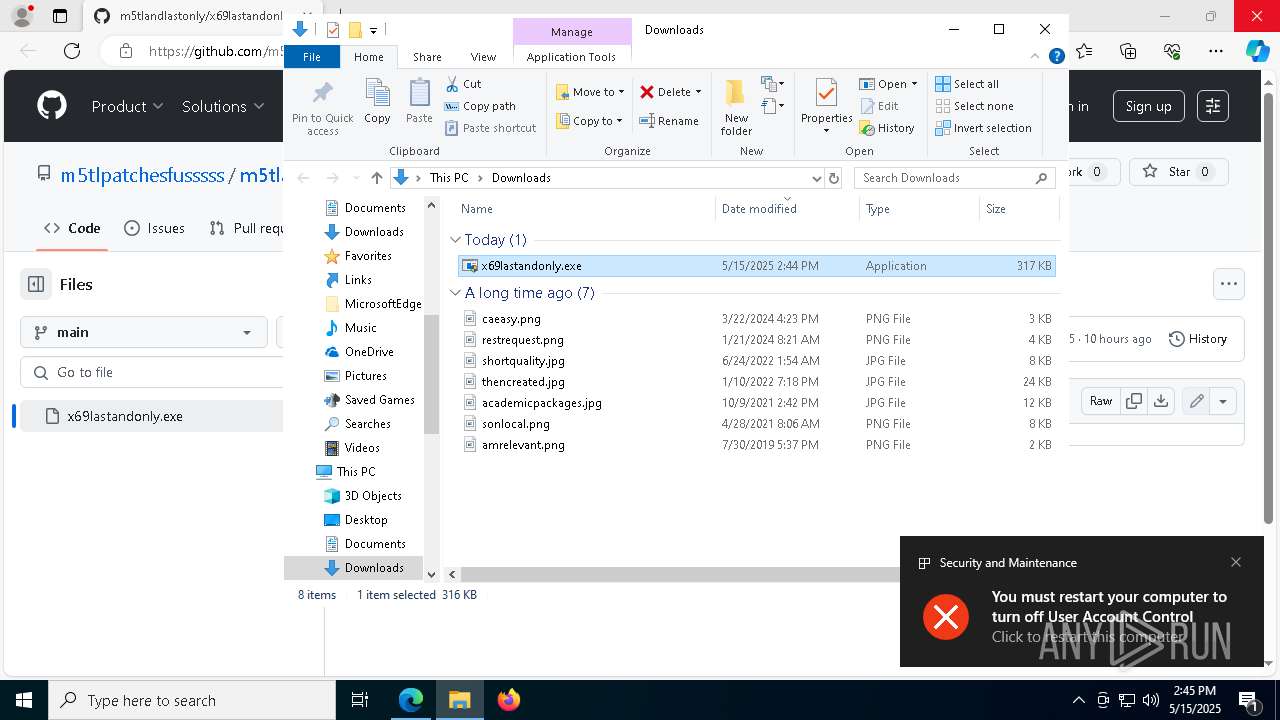
| URL: | https://github.com/m5tlpatchesfusssss/m5tlandlastonly/blob/main/x69lastandonly.exe |
| Full analysis: | https://app.any.run/tasks/caeb5f16-61a7-4d2d-91dc-cd9201f3f996 |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | May 15, 2025, 14:44:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 89E56AE37084B236F003D692D34FA30C |
| SHA1: | 8CFC2CD7049CF750D67E7CD73763C46AA405A619 |
| SHA256: | 125EC9303D8DA809F4A776DF1B2FA32EA5E86D3FD1426D1A72260FCBB7E93674 |
| SSDEEP: | 3:N8tEd4gV4azMWWsBJENLSKpKHKIERnWi1K5C:2uulWWgJEs4MsWi1Kc |
MALICIOUS
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 5756)
Changes Windows Defender settings
- cmd.exe (PID: 1328)
- cmd.exe (PID: 8168)
Changes settings for real-time protection
- powershell.exe (PID: 6576)
- powershell.exe (PID: 736)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 1764)
NJRAT has been detected (SURICATA)
- x69dllhost.exe (PID: 8184)
Connects to the CnC server
- x69dllhost.exe (PID: 8184)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 1096)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6668)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 9084)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7384)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- x69lastandonly.exe (PID: 8008)
Starts POWERSHELL.EXE for commands execution
- x69lastandonly.exe (PID: 8008)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 1328)
Base64-obfuscated command line is found
- x69lastandonly.exe (PID: 8008)
Executable content was dropped or overwritten
- x69lastandonly.exe (PID: 8008)
- x69lastm5tl.exe (PID: 6148)
- x69dllhost.exe (PID: 8184)
Reads security settings of Internet Explorer
- x69lastandonly.exe (PID: 8008)
- x69Disable-winDefender.exe (PID: 7992)
- x69lastm5tl.exe (PID: 6148)
The process executes via Task Scheduler
- powershell.exe (PID: 7908)
Invokes assembly entry point (POWERSHELL)
- powershell.exe (PID: 7908)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 1328)
- cmd.exe (PID: 8168)
Found strings related to reading or modifying Windows Defender settings
- x69Disable-winDefender.exe (PID: 7992)
Executing commands from a ".bat" file
- x69Disable-winDefender.exe (PID: 7992)
Starts CMD.EXE for commands execution
- x69Disable-winDefender.exe (PID: 7992)
- x69dllhost.exe (PID: 8184)
Script disables Windows Defender's behavior monitoring
- cmd.exe (PID: 1328)
Starts itself from another location
- x69lastm5tl.exe (PID: 6148)
Uses ATTRIB.EXE to modify file attributes
- x69dllhost.exe (PID: 8184)
Stops a currently running service
- sc.exe (PID: 8448)
Windows service management via SC.EXE
- sc.exe (PID: 8648)
- sc.exe (PID: 8376)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8680)
- powershell.exe (PID: 4108)
- powershell.exe (PID: 976)
- cmd.exe (PID: 1328)
Connects to unusual port
- x69dllhost.exe (PID: 8184)
Contacting a server suspected of hosting an CnC
- x69dllhost.exe (PID: 8184)
Script disables Windows Defender's IPS
- cmd.exe (PID: 1328)
Uses NETSH.EXE to change the status of the firewall
- powershell.exe (PID: 4452)
Modifies existing scheduled task
- schtasks.exe (PID: 8520)
- schtasks.exe (PID: 6384)
- schtasks.exe (PID: 9096)
- schtasks.exe (PID: 668)
- schtasks.exe (PID: 5324)
INFO
Checks supported languages
- identity_helper.exe (PID: 8060)
- x69lastandonly.exe (PID: 8008)
- x69lastm5tl.exe (PID: 6148)
- Install.exe (PID: 6436)
- x69Disable-winDefender.exe (PID: 7992)
- MpCmdRun.exe (PID: 5756)
- x69dllhost.exe (PID: 8184)
Executable content was dropped or overwritten
- msedge.exe (PID: 616)
- msedge.exe (PID: 5772)
Application launched itself
- msedge.exe (PID: 616)
Reads the machine GUID from the registry
- Install.exe (PID: 6436)
Reads Environment values
- identity_helper.exe (PID: 8060)
Reads the computer name
- identity_helper.exe (PID: 8060)
- x69lastandonly.exe (PID: 8008)
- x69Disable-winDefender.exe (PID: 7992)
- MpCmdRun.exe (PID: 5756)
- x69lastm5tl.exe (PID: 6148)
- x69dllhost.exe (PID: 8184)
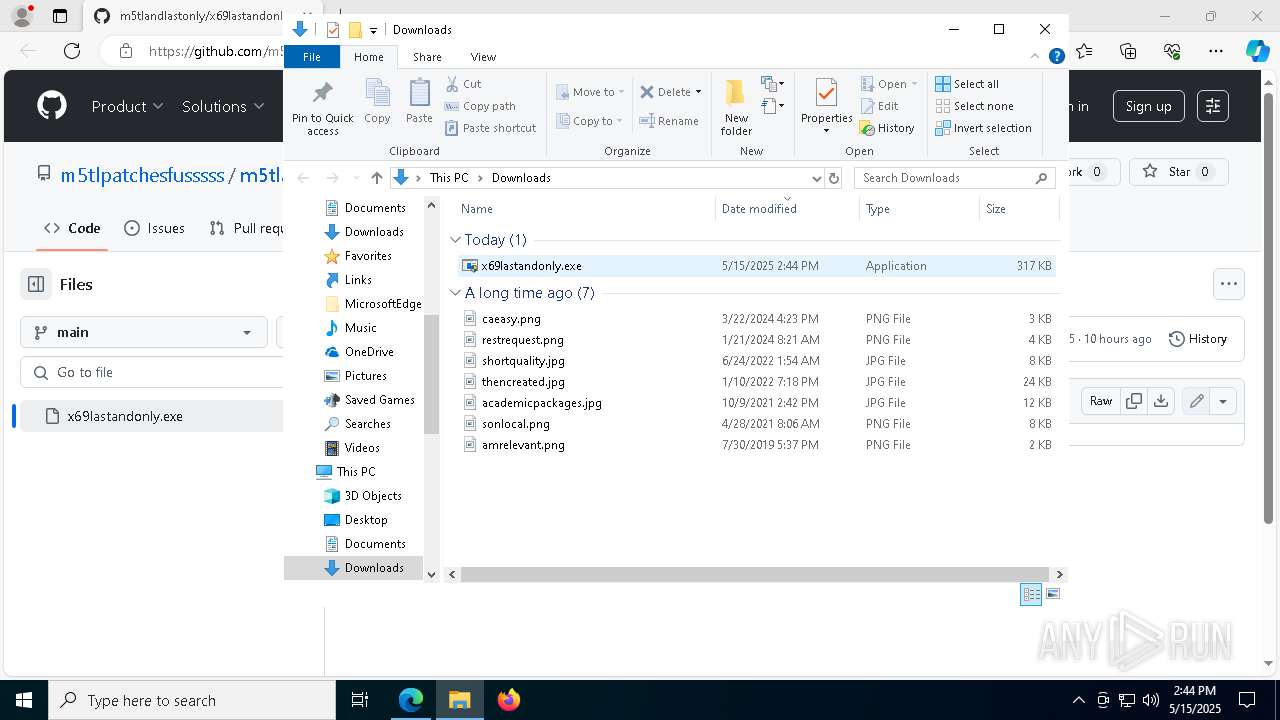
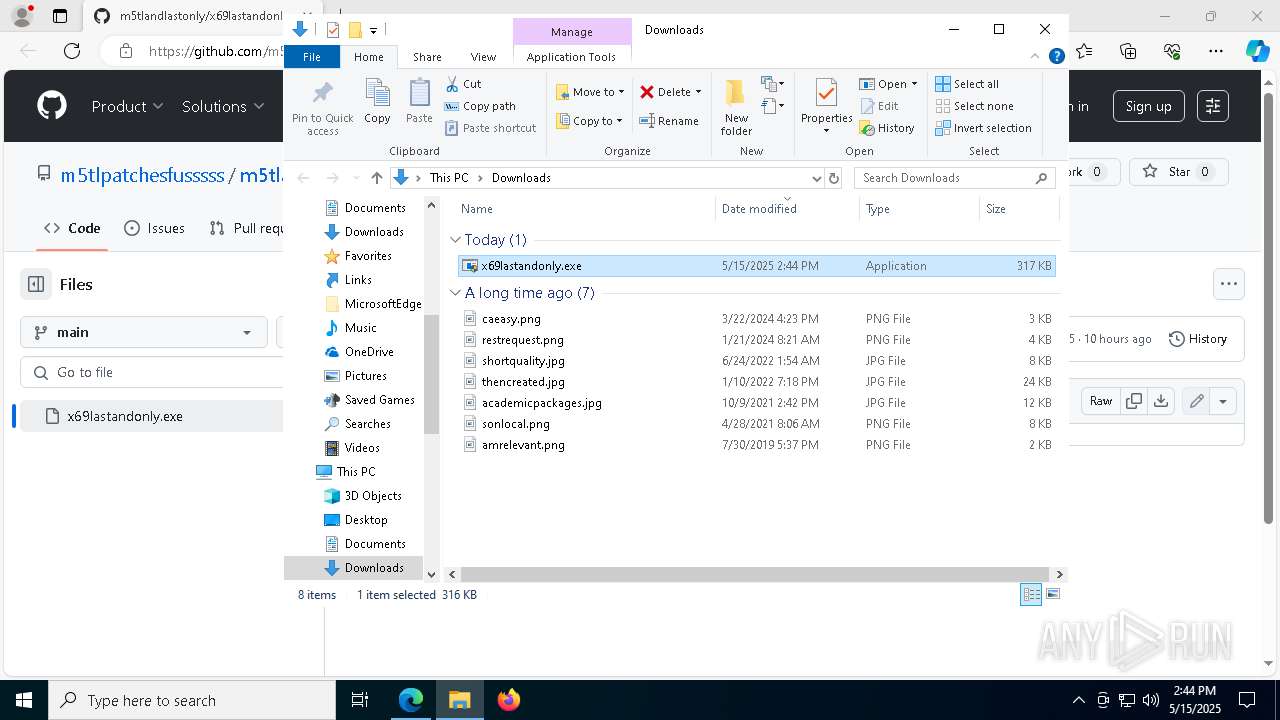
Manual execution by a user
- x69lastandonly.exe (PID: 7420)
- x69lastandonly.exe (PID: 8008)
Process checks computer location settings
- x69lastandonly.exe (PID: 8008)
- x69Disable-winDefender.exe (PID: 7992)
- x69lastm5tl.exe (PID: 6148)
Create files in a temporary directory
- x69lastandonly.exe (PID: 8008)
- x69Disable-winDefender.exe (PID: 7992)
- MpCmdRun.exe (PID: 5756)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 2096)
- powershell.exe (PID: 8168)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 8168)
- powershell.exe (PID: 2096)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
262
Monitored processes
128
Malicious processes
7
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/m5tlpatchesfusssss/m5tlandlastonly/blob/main/x69lastandonly.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | schtasks /Change /TN "Microsoft\Windows\Windows Defender\Windows Defender Scheduled Scan" /Disable | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | reg delete "HKCR\*\shellex\ContextMenuHandlers\EPP" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender" /v "DisableAntiSpyware" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | attrib.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | powershell.exe -command "REG ADD ΓÇ£hklm\software\policies\microsoft\windows defenderΓÇ¥ /v DisableAntiSpyware /t REG_DWORD /d 1 /f" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | powershell.exe -command "Set-MpPreference -DisableIntrusionPreventionSystem $true" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
117 420
Read events
117 232
Write events
180
Delete events
8
Modification events
| (PID) Process: | (616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AE7E8AFCC3932F00 | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EDD792FCC3932F00 | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328284 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9166CF8E-B0BC-4388-B1CB-78E4D9B30085} | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328284 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2A4469E0-8F36-40E5-823B-80FC30DEEA1E} | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328284 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7E4E5153-697C-4459-84F2-44DEB8411628} | |||
| (PID) Process: | (616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328284 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B3106502-7C0E-4853-BFE4-345059514437} | |||
Executable files
19
Suspicious files
384
Text files
87
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b807.TMP | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b807.TMP | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b807.TMP | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b807.TMP | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b826.TMP | — | |
MD5:— | SHA256:— | |||
| 616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
57
DNS requests
67
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2800 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4188 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747701639&P2=404&P3=2&P4=d1E%2fJ4a0Mute44QNUIPFlqB3pWPwJv67yevXVn3XKfz9seqBtLRS1dNGWParquKMVhudCugquBWBUaKzvKCCNw%3d%3d | unknown | — | — | whitelisted |
4188 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1747701640&P2=404&P3=2&P4=dwUaizJ0alLXKemqMmFsD9I77wRZrmEGxYNXAgwgERm0rg4%2bwf7pYzcuI2pP%2fjBy5qt%2b715w%2f3Okjo5udu7TWQ%3d%3d | unknown | — | — | whitelisted |
4188 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747701639&P2=404&P3=2&P4=d1E%2fJ4a0Mute44QNUIPFlqB3pWPwJv67yevXVn3XKfz9seqBtLRS1dNGWParquKMVhudCugquBWBUaKzvKCCNw%3d%3d | unknown | — | — | whitelisted |
2800 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4188 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747701639&P2=404&P3=2&P4=Ir0b6udsxKDkoEADKIWju56skA%2blsoE%2f7bp86ArRLmEM1Ww45JFMnPLNMQEioFRxWMnDEQZrpXp%2bBNOTGcqefQ%3d%3d | unknown | — | — | whitelisted |
4188 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747701639&P2=404&P3=2&P4=Ir0b6udsxKDkoEADKIWju56skA%2blsoE%2f7bp86ArRLmEM1Ww45JFMnPLNMQEioFRxWMnDEQZrpXp%2bBNOTGcqefQ%3d%3d | unknown | — | — | whitelisted |
4188 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747701639&P2=404&P3=2&P4=Ir0b6udsxKDkoEADKIWju56skA%2blsoE%2f7bp86ArRLmEM1Ww45JFMnPLNMQEioFRxWMnDEQZrpXp%2bBNOTGcqefQ%3d%3d | unknown | — | — | whitelisted |
4188 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747701639&P2=404&P3=2&P4=Ir0b6udsxKDkoEADKIWju56skA%2blsoE%2f7bp86ArRLmEM1Ww45JFMnPLNMQEioFRxWMnDEQZrpXp%2bBNOTGcqefQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
616 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5772 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5772 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
5772 | msedge.exe | 13.107.253.53:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5772 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5772 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5772 | msedge.exe | 185.199.111.133:443 | avatars.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5772 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
5772 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
8184 | x69dllhost.exe | Malware Command and Control Activity Detected | ET MALWARE Generic njRAT/Bladabindi CnC Activity (ll) |
8184 | x69dllhost.exe | Malware Command and Control Activity Detected | BACKDOOR [ANY.RUN] njRAT Bladabindi CnC Communication command ll |