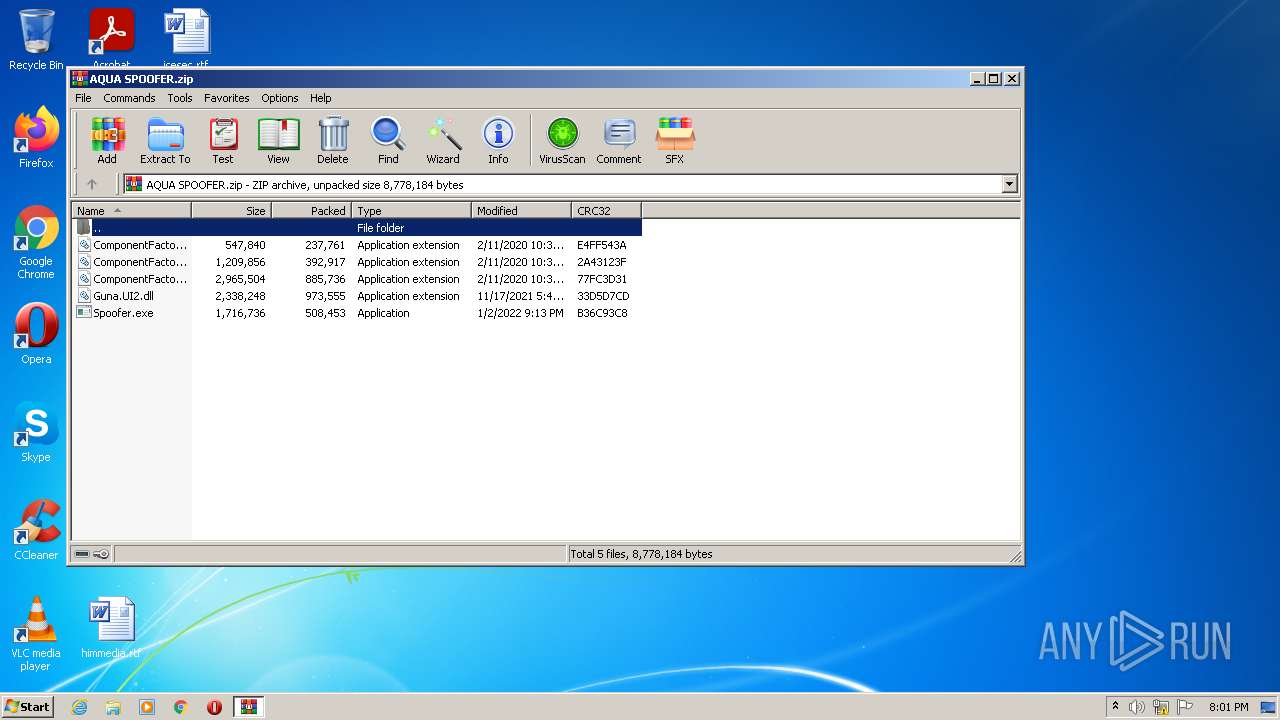
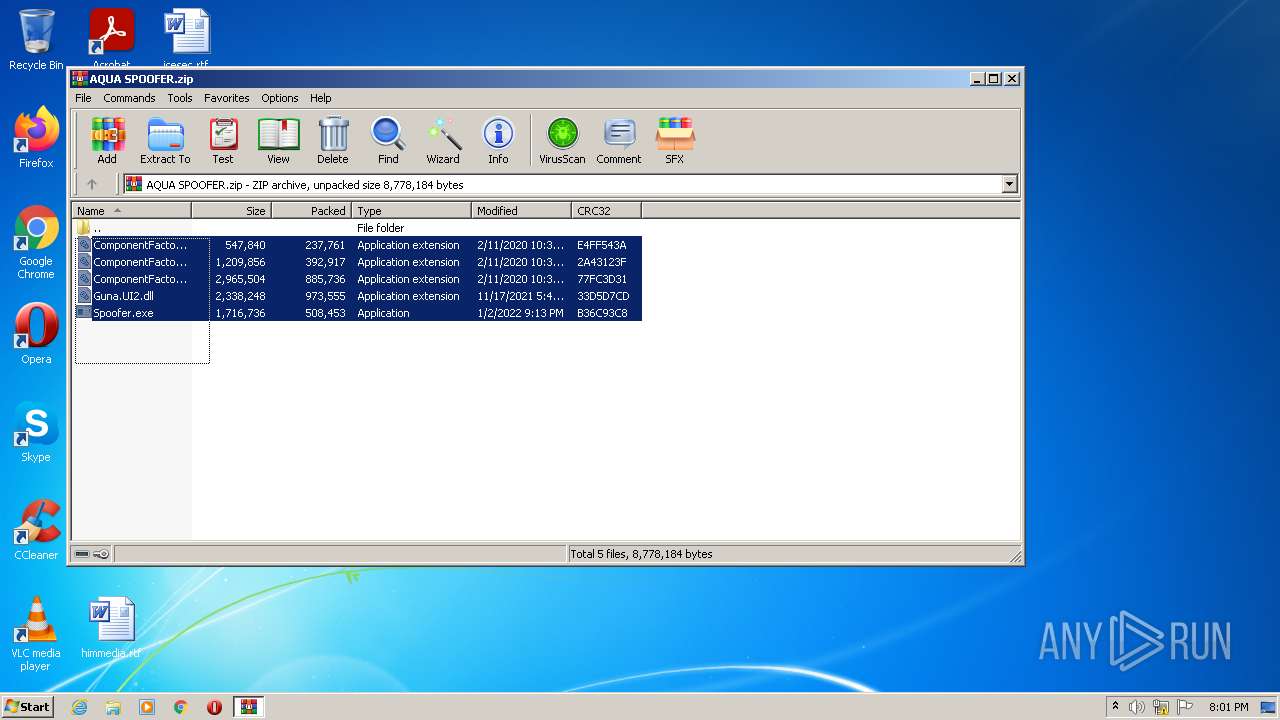
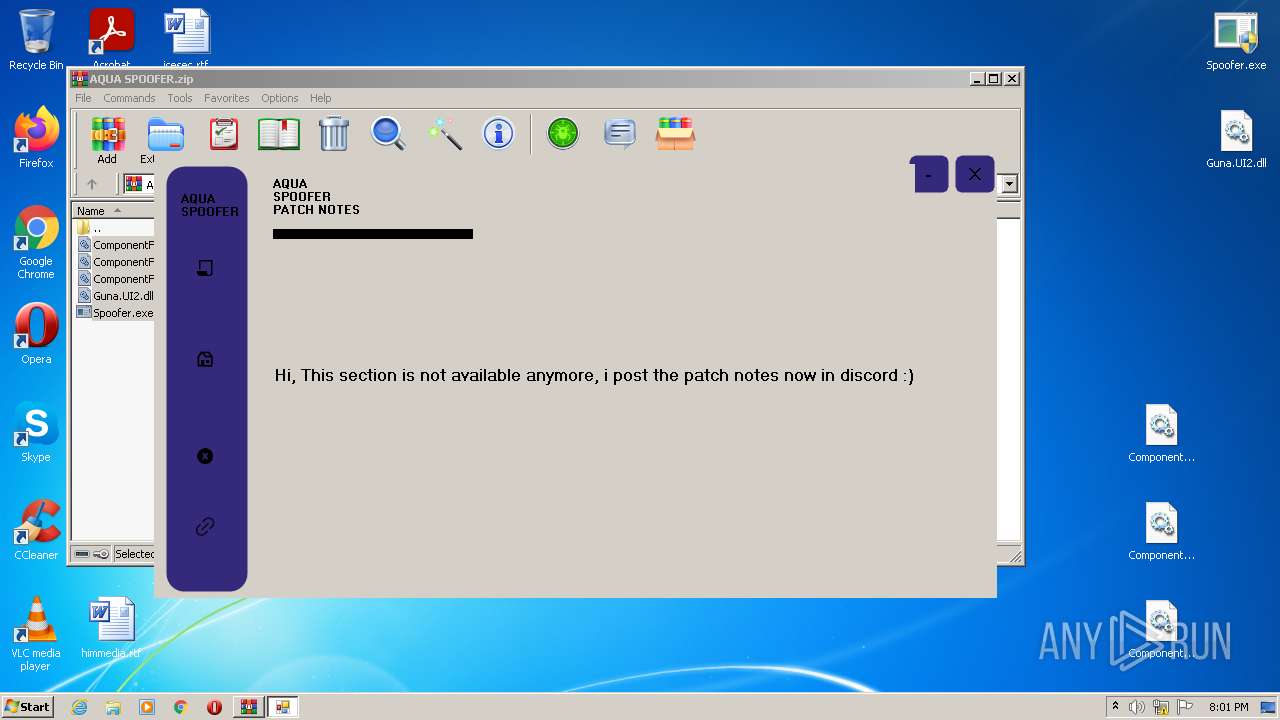
| File name: | AQUA SPOOFER.zip |
| Full analysis: | https://app.any.run/tasks/d6ae304a-bc8c-4865-9628-43f7cb0a1521 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 02, 2022, 20:01:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 021E091A6EAF841754C44856110D8394 |
| SHA1: | C2F7A338A8EFA88882306DC7A3D134CCD616374B |
| SHA256: | 116FC1A07F5E2D3CD3ED67CFAA529A2E7BE04B649FB3E37129C76F8A623E86BC |
| SSDEEP: | 49152:T6j4UlD6qsW67AVt2XnyY4hQctNbnWhNJqgWTf5usM7TZrx7M4CwoS9iGc+Xia+P:TrpBTXyJiwbnWvUZf53M71raXN8c+Xit |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3456)
- Spoofer.exe (PID: 3220)
Application was dropped or rewritten from another process
- Spoofer.exe (PID: 3220)
- Spoofer.exe (PID: 2340)
- DiskManager.exe (PID: 3308)
- Disable-Windows-Defender.exe (PID: 2152)
- WindowsFormsApp19.exe (PID: 2548)
Drops executable file immediately after starts
- Spoofer.exe (PID: 3220)
Changes the autorun value in the registry
- Spoofer.exe (PID: 3220)
ASYNCRAT was detected
- DiskManager.exe (PID: 3308)
Actions looks like stealing of personal data
- WindowsFormsApp19.exe (PID: 2548)
Writes to a start menu file
- Spoofer.exe (PID: 3220)
Disables Windows Defender
- Disable-Windows-Defender.exe (PID: 2152)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2200)
- Spoofer.exe (PID: 3220)
- DiskManager.exe (PID: 3308)
- WindowsFormsApp19.exe (PID: 2548)
- Disable-Windows-Defender.exe (PID: 2152)
- powershell.exe (PID: 3532)
Checks supported languages
- WinRAR.exe (PID: 2200)
- Spoofer.exe (PID: 3220)
- WindowsFormsApp19.exe (PID: 2548)
- DiskManager.exe (PID: 3308)
- Disable-Windows-Defender.exe (PID: 2152)
- powershell.exe (PID: 3532)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2200)
- Spoofer.exe (PID: 3220)
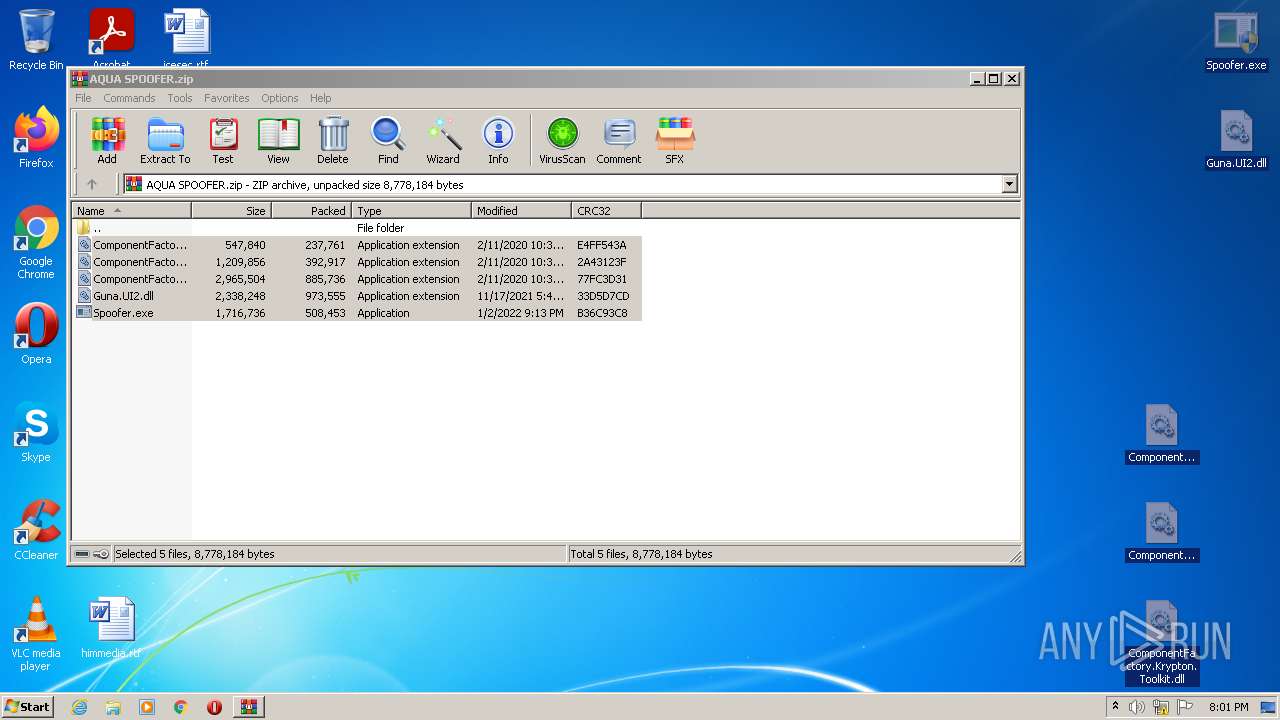
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2200)
- Spoofer.exe (PID: 3220)
Creates files in the user directory
- Spoofer.exe (PID: 3220)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2200)
- Spoofer.exe (PID: 3220)
Reads Environment values
- Spoofer.exe (PID: 3220)
- WindowsFormsApp19.exe (PID: 2548)
- DiskManager.exe (PID: 3308)
Creates files in the Windows directory
- Spoofer.exe (PID: 3220)
Executes PowerShell scripts
- Disable-Windows-Defender.exe (PID: 2152)
INFO
Manual execution by user
- Spoofer.exe (PID: 2340)
- Spoofer.exe (PID: 3220)
Reads settings of System Certificates
- Spoofer.exe (PID: 3220)
- DiskManager.exe (PID: 3308)
- powershell.exe (PID: 3532)
- WindowsFormsApp19.exe (PID: 2548)
Checks Windows Trust Settings
- powershell.exe (PID: 3532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | ComponentFactory.Krypton.Toolkit.dll |
|---|---|
| ZipUncompressedSize: | 2965504 |
| ZipCompressedSize: | 885736 |
| ZipCRC: | 0x77fc3d31 |
| ZipModifyDate: | 2020:02:11 10:39:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
46
Monitored processes
8
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2152 | "C:\Windows\IME\Disable-Windows-Defender.exe" | C:\Windows\IME\Disable-Windows-Defender.exe | — | Spoofer.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Disable-Windows-Defender Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\AQUA SPOOFER.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\Desktop\Spoofer.exe" | C:\Users\admin\Desktop\Spoofer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: 20188-2222 Integrity Level: MEDIUM Description: AQUA SPOOFER Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WindowsFormsApp19.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WindowsFormsApp19.exe | Spoofer.exe | ||||||||||||
User: admin Company: 20188-2222 Integrity Level: HIGH Description: WindowsFormsApp19 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3220 | "C:\Users\admin\Desktop\Spoofer.exe" | C:\Users\admin\Desktop\Spoofer.exe | Explorer.EXE | ||||||||||||
User: admin Company: 20188-2222 Integrity Level: HIGH Description: AQUA SPOOFER Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3308 | "C:\Windows\IME\DiskManager.exe" | C:\Windows\IME\DiskManager.exe | Spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3456 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3532 | "powershell" Get-MpPreference -verbose | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Disable-Windows-Defender.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
16 354
Read events
16 241
Write events
113
Delete events
0
Modification events
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AQUA SPOOFER.zip | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
10
Suspicious files
5
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2200.35631\Spoofer.exe | executable | |
MD5:— | SHA256:— | |||
| 3220 | Spoofer.exe | C:\Windows\IME\DiskManager.exe | executable | |
MD5:— | SHA256:— | |||
| 3308 | DiskManager.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3220 | Spoofer.exe | C:\Windows\IME\Disable-Windows-Defender.exe | executable | |
MD5:— | SHA256:— | |||
| 2200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2200.35631\ComponentFactory.Krypton.Toolkit.dll | executable | |
MD5:129884DE0E136521FD650C59B2633E82 | SHA256:8C69F5DF110BC1A61BDC3D8754EBFD3F49D9D995B9DD129ACCAF88371CE71E30 | |||
| 3220 | Spoofer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WindowsFormsApp19.exe | executable | |
MD5:— | SHA256:— | |||
| 3220 | Spoofer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DiskManager.exe | executable | |
MD5:— | SHA256:— | |||
| 2200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2200.35631\Guna.UI2.dll | executable | |
MD5:38AB8E6E56CEE9F49E2167FB43275F05 | SHA256:1CAA3FD09153C8EA3D623D5723133F98751F2AFC1C135992F19F1F1A7044490C | |||
| 2200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2200.35631\ComponentFactory.Krypton.Navigator.dll | executable | |
MD5:E9311C190494179547F9D804F39813EA | SHA256:FA49250585D7D1F44D1688571F9DF020E55B92663D9E94557EE1F228EBF280B7 | |||
| 3308 | DiskManager.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | DiskManager.exe | GET | 200 | 2.16.186.89:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f2781c65bcdf1a77 | unknown | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3220 | Spoofer.exe | 162.159.133.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
3308 | DiskManager.exe | 3.131.207.170:19665 | 2.tcp.ngrok.io | — | US | malicious |
3308 | DiskManager.exe | 2.16.186.89:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2548 | WindowsFormsApp19.exe | 162.159.135.232:443 | discord.com | Cloudflare Inc | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
2.tcp.ngrok.io |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
discord.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
1 ETPRO signatures available at the full report