| File name: | i.exe |
| Full analysis: | https://app.any.run/tasks/f5961a82-f60d-43de-bf0c-77be088cc438 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
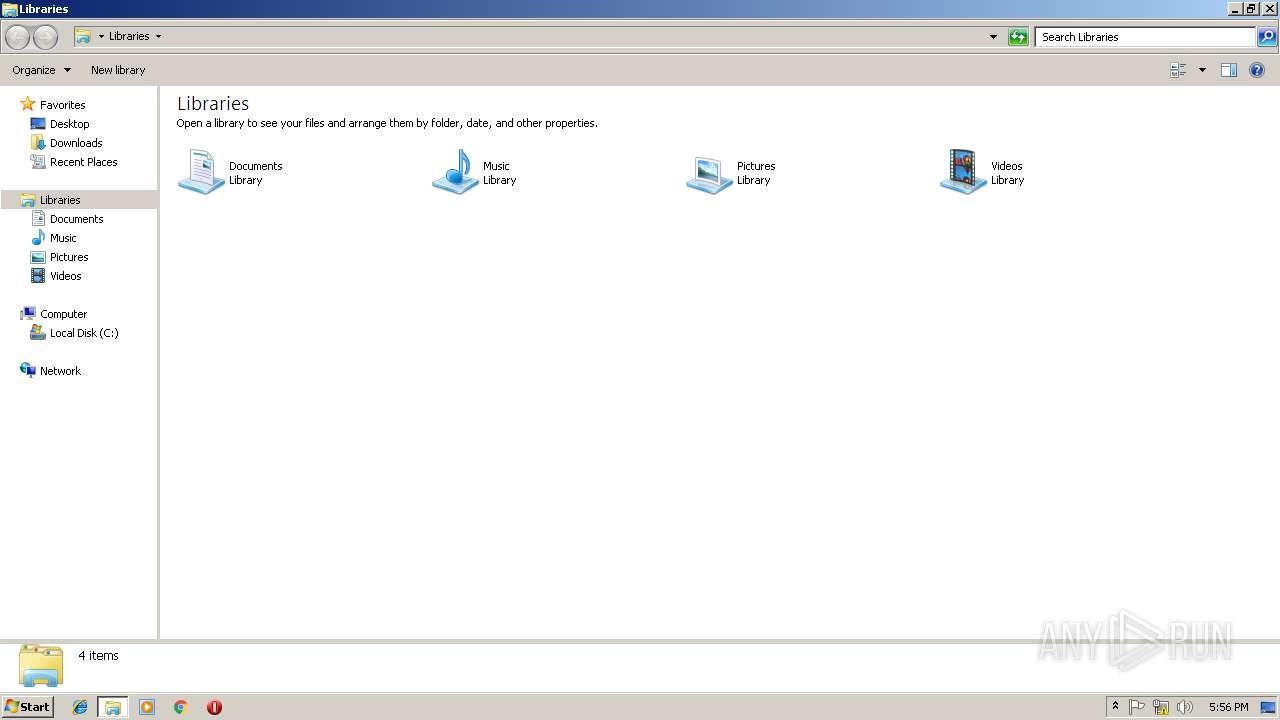
| Analysis date: | January 22, 2019, 17:53:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EC848B2A4F6AB3D723A8A898CC8F832B |
| SHA1: | ADA1DF40BA4BF8BFD31889690BC7EF0061F70680 |
| SHA256: | 114271B808957DE8AA6F486DF33584A171CD7615FB73CF6E14097D0D71E8DDCE |
| SSDEEP: | 12288:0zjUmrwfjFvDu6mVF/I1e1VYDMCKfaOn0L/RK0IvNliEZB:0/ZrEj1u65GYIBE/Q0GV |
MALICIOUS
Detected artifacts of LokiBot
- i.exe (PID: 3512)
LOKIBOT was detected
- i.exe (PID: 3512)
Connects to CnC server
- i.exe (PID: 3512)
Actions looks like stealing of personal data
- i.exe (PID: 3512)
SUSPICIOUS
Loads DLL from Mozilla Firefox
- i.exe (PID: 3512)
Application launched itself
- i.exe (PID: 3092)
Creates files in the user directory
- i.exe (PID: 3512)
Executable content was dropped or overwritten
- i.exe (PID: 3512)
INFO
Changes internet zones settings
- iexplore.exe (PID: 800)
Reads Internet Cache Settings
- iexplore.exe (PID: 1816)
Application launched itself
- iexplore.exe (PID: 800)
Reads internet explorer settings
- iexplore.exe (PID: 1816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:12 21:58:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 439808 |
| InitializedDataSize: | 237568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6c3f4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Jun-1992 19:58:55 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 12-Jun-1992 19:58:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0006B43C | 0x0006B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54774 |
DATA | 0x0006D000 | 0x000095D4 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.07025 |
BSS | 0x00077000 | 0x00000CA1 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00078000 | 0x0000248A | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93516 |
.tls | 0x0007B000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0007C000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x0007D000 | 0x00007D94 | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.67269 |
.rsrc | 0x00085000 | 0x00026234 | 0x00026400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.07365 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.76954 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 2.80231 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
769 | 5.63817 | 1329 | Latin 1 / Western European | English - United States | RT_BITMAP |
770 | 7.08537 | 1329 | Latin 1 / Western European | English - United States | RT_BITMAP |
771 | 7.14757 | 1329 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
34
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 800 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:800 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
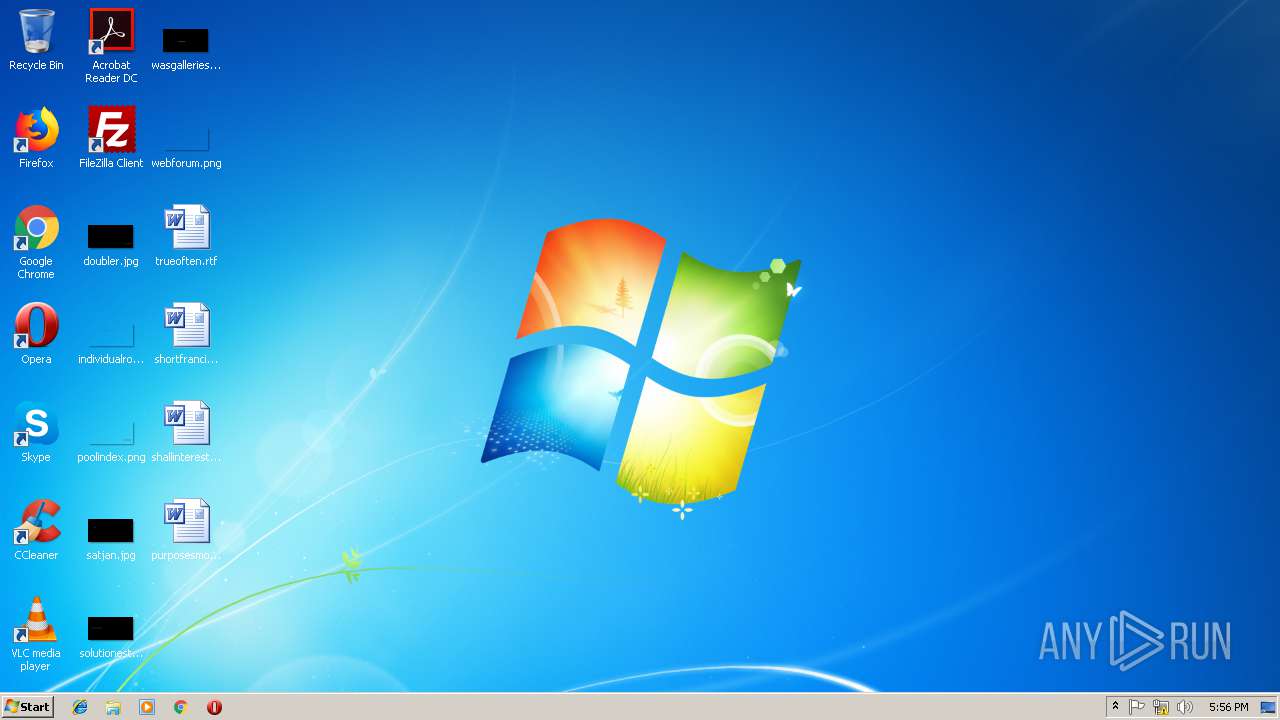
| 3092 | "C:\Users\admin\AppData\Local\Temp\i.exe" | C:\Users\admin\AppData\Local\Temp\i.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3512 | "C:\Users\admin\AppData\Local\Temp\i.exe" | C:\Users\admin\AppData\Local\Temp\i.exe | i.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4072 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
395
Read events
349
Write events
45
Delete events
1
Modification events
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {10ECBB09-1E6F-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100020016001100380028001300 | |||
Executable files
1
Suspicious files
0
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 800 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3512 | i.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 800 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF635764F40248E8EB.TMP | — | |
MD5:— | SHA256:— | |||
| 800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{4BBB6F4B-AC5C-11E8-969E-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 800 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA8E005C071E7480B.TMP | — | |
MD5:— | SHA256:— | |||
| 800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{10ECBB0A-1E6F-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 800 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFE92A01E1C386A1D6.TMP | — | |
MD5:— | SHA256:— | |||
| 800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{10ECBB09-1E6F-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3512 | i.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.hdb | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
2
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3512 | i.exe | POST | 404 | 31.31.196.194:80 | http://dnisve.com/zz/vi/m.php | RU | text | 15 b | malicious |
3512 | i.exe | POST | 200 | 31.31.196.194:80 | http://dnisve.com/zz/vi/m.php | RU | binary | 23 b | malicious |
3512 | i.exe | POST | 200 | 31.31.196.194:80 | http://dnisve.com/zz/vi/m.php | RU | binary | 23 b | malicious |
800 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3512 | i.exe | POST | 404 | 31.31.196.194:80 | http://dnisve.com/zz/vi/m.php | RU | text | 15 b | malicious |
3512 | i.exe | POST | 200 | 31.31.196.194:80 | http://dnisve.com/zz/vi/m.php | RU | binary | 23 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
800 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3512 | i.exe | 31.31.196.194:80 | dnisve.com | Domain names registrar REG.RU, Ltd | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
dnisve.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3512 | i.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3512 | i.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3512 | i.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3512 | i.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3512 | i.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3512 | i.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3512 | i.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3512 | i.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3512 | i.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3512 | i.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |