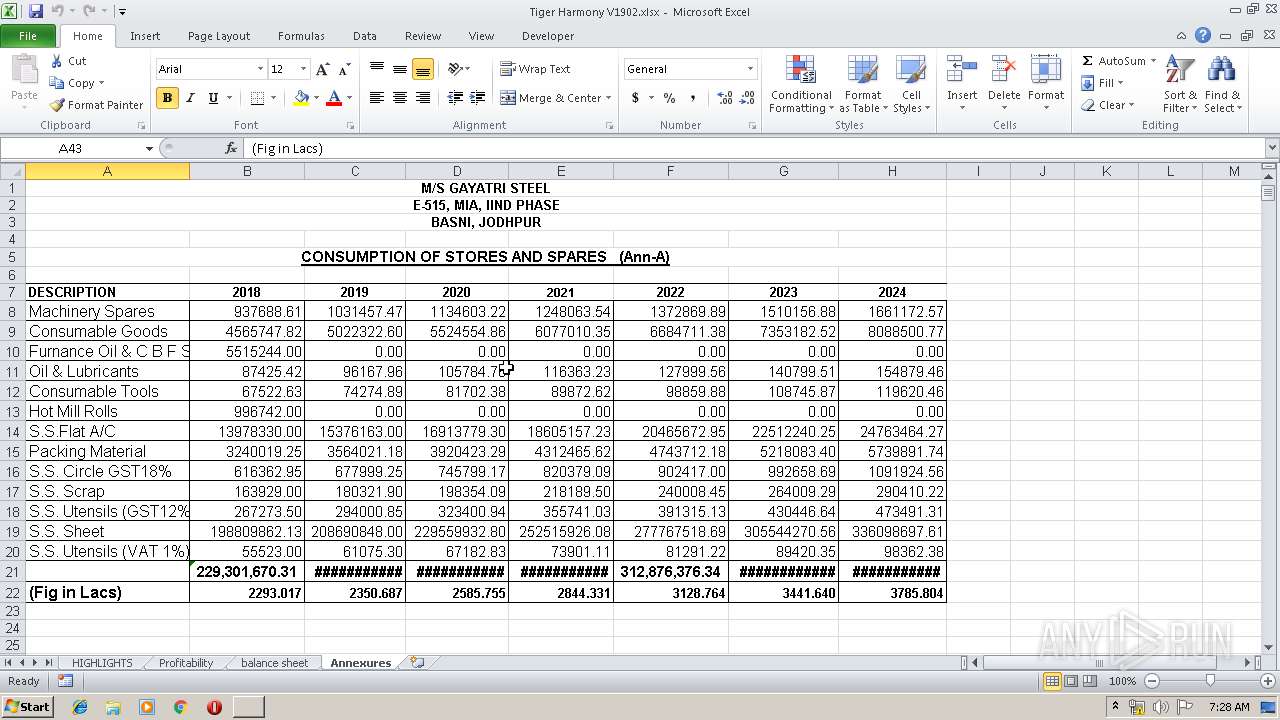
| File name: | Tiger Harmony V1902.xlsx |
| Full analysis: | https://app.any.run/tasks/92111725-856f-437f-838f-245a26b41a5b |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | May 20, 2019, 06:28:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 624F49AC48E8E12B5220D0977C43FE16 |
| SHA1: | 72D3C2E32422DFB2BB882753E257B056918D9304 |
| SHA256: | 1120309F76503EF8B16B3DDBCAF30E937F820D54463760A847B5092E4F9C56CA |
| SSDEEP: | 768:N+rwx4kSzgyYBvycVmb+H+/9pZK/cFNOuvScvMg4JxqmcPnYUBTVNlQ5HOt0rYQs:Irv4tVDHIFn91YG1Us |
MALICIOUS
Detected Hawkeye Keylogger
- RegAsm.exe (PID: 2768)
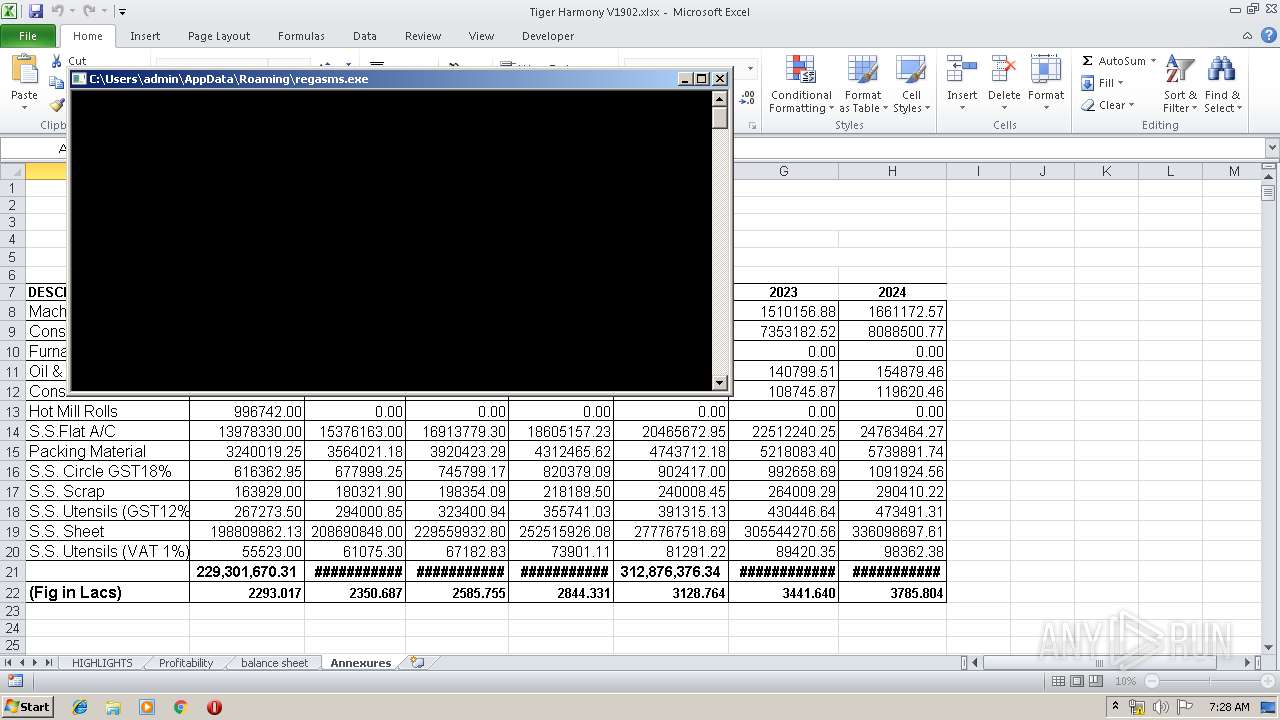
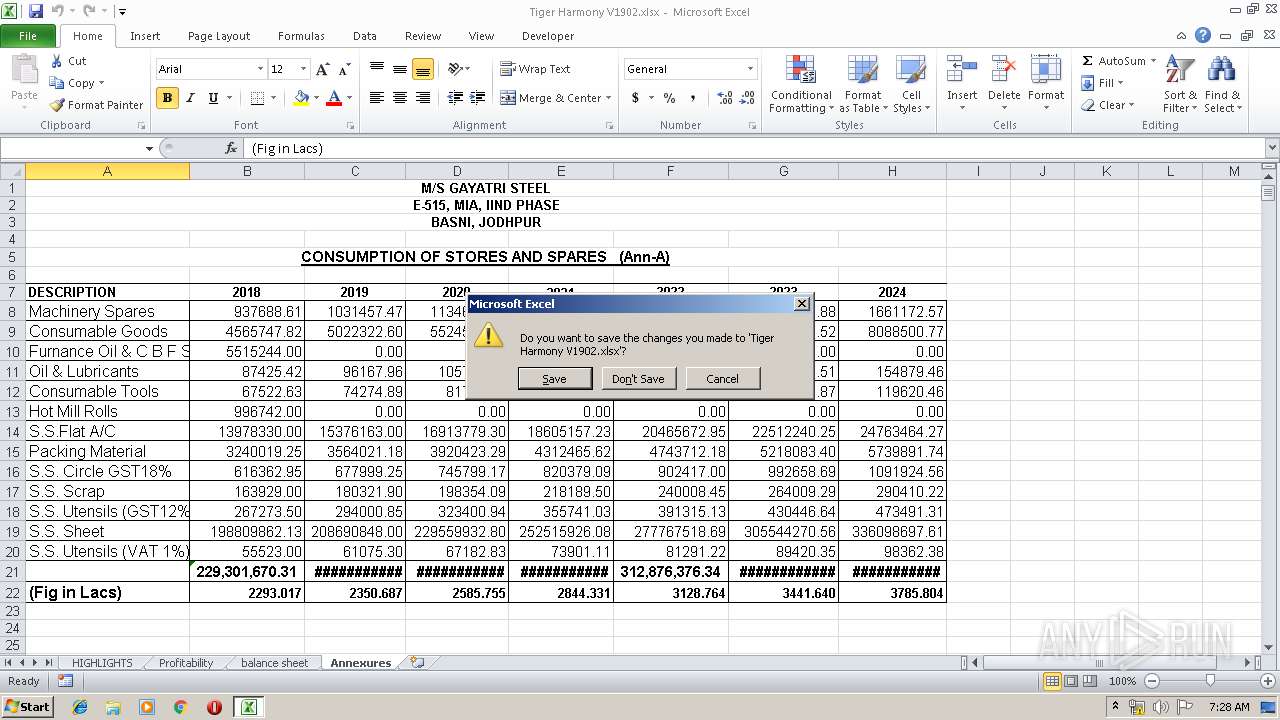
Application was dropped or rewritten from another process
- regasms.exe (PID: 3688)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3668)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 3668)
Writes to a start menu file
- regasms.exe (PID: 3688)
Actions looks like stealing of personal data
- vbc.exe (PID: 3536)
- vbc.exe (PID: 1896)
Stealing of credential data
- vbc.exe (PID: 1896)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 3668)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3668)
- regasms.exe (PID: 3688)
Creates files in the user directory
- EQNEDT32.EXE (PID: 3668)
- regasms.exe (PID: 3688)
Executes scripts
- RegAsm.exe (PID: 2768)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3536)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 3984)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:19 10:26:10 |
| ZipCRC: | 0x7782a3b5 |
| ZipCompressedSize: | 425 |
| ZipUncompressedSize: | 2041 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | COMPAQ |
|---|
XML
| LastModifiedBy: | COMPAQ |
|---|---|
| LastPrinted: | 2017:04:29 14:02:28Z |
| CreateDate: | 2010:02:14 08:32:05Z |
| ModifyDate: | 2018:09:22 03:48:48Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1896 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp6B94.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2768 | C:\Users\admin\AppData\Roaming\regasms.exe | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | regasms.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3536 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp53F4.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3668 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3688 | C:\Users\admin\AppData\Roaming\regasms.exe | C:\Users\admin\AppData\Roaming\regasms.exe | EQNEDT32.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3984 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
666
Read events
588
Write events
66
Delete events
12
Modification events
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 86? |
Value: 38363F00900F0000010000000000000000000000 | |||
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 900F0000C8A2993BD50ED50100000000 | |||
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 86? |
Value: 38363F00900F0000010000000000000000000000 | |||
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3984) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3668) EQNEDT32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109E60090400000000000F01FEC\Usage |
| Operation: | write | Name: | EquationEditorFilesIntl_1033 |
Value: 1320419331 | |||
Executable files
3
Suspicious files
0
Text files
5
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRFAA9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3984 | EXCEL.EXE | C:\Users\admin\Desktop\~$Tiger Harmony V1902.xlsx | — | |
MD5:— | SHA256:— | |||
| 3536 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp53F4.tmp | — | |
MD5:— | SHA256:— | |||
| 3984 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Tiger Harmony V1902.xlsx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3984 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3668 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\regasms.exe | executable | |
MD5:— | SHA256:— | |||
| 3688 | regasms.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\jhnysglllmplcxv.eu.url | ini | |
MD5:— | SHA256:— | |||
| 3668 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\ttkoooo[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3688 | regasms.exe | C:\Users\admin\AppData\Roaming\ifulvbcrzo\jhnysglllmplcxv.exe | executable | |
MD5:— | SHA256:— | |||
| 1896 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp6B94.tmp | text | |
MD5:7FB9A9AD0FD9B1E0108ED71FBB276048 | SHA256:7D63C301317E144B0133A72250AE2D8E09AF65A92E6A807EC58A71939FE530A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3668 | EQNEDT32.EXE | GET | 200 | 54.36.212.206:80 | http://www.terryhill.top/proforma/ttkoooo.exe | FR | executable | 823 Kb | malicious |
2768 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 11 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3668 | EQNEDT32.EXE | 54.36.212.206:80 | www.terryhill.top | OVH SAS | FR | malicious |
2768 | RegAsm.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
2768 | RegAsm.exe | 162.221.190.147:587 | mail.almeenamarine.com | HostDime.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.terryhill.top |
| malicious |
bot.whatismyipaddress.com |
| shared |
mail.almeenamarine.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3668 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016 |
3668 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3668 | EQNEDT32.EXE | Misc activity | ET INFO Packed Executable Download |
3668 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3668 | EQNEDT32.EXE | Misc activity | ET INFO Possible EXE Download From Suspicious TLD |
3668 | EQNEDT32.EXE | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2768 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spy.HawkEye IP Check |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
regasms.exe | User32.dll |
regasms.exe | User32.dll |
regasms.exe | User32.dll |
regasms.exe | User32.dll |
regasms.exe | User32.dll |
regasms.exe | User32.dll |
regasms.exe | User32.dll |
regasms.exe | User32.dll |
regasms.exe | User32.dll |
regasms.exe | User32.dll |