| File name: | payment confirmation.exe |
| Full analysis: | https://app.any.run/tasks/f1de81b8-8d0f-4c17-b3ef-f770b0412b86 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | December 18, 2023, 08:53:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 099521FA325BBE1280463E5B38464301 |
| SHA1: | F09356846B6AA5F0F9E648051765398E17E77107 |
| SHA256: | 10D4F54E3353007E0238CDFE1F380F8130B36A9D53915B78CA759561AEF90ECE |
| SSDEEP: | 24576:7CPmmmmmmmm8KYdlVt7AwKwk2QNLameuwshdmW4gzIlquwXb1p4Ce0b:7CPmmmmmmmm8KYdlVt7AwLk2QNLameu5 |
MALICIOUS
Drops the executable file immediately after the start
- payment confirmation.exe (PID: 1744)
Actions looks like stealing of personal data
- payment confirmation.exe (PID: 2156)
Steals credentials from Web Browsers
- payment confirmation.exe (PID: 2156)
Connects to the CnC server
- payment confirmation.exe (PID: 2156)
AGENTTESLA has been detected (YARA)
- payment confirmation.exe (PID: 2156)
SUSPICIOUS
Reads the Internet Settings
- payment confirmation.exe (PID: 1744)
- powershell.exe (PID: 2856)
- payment confirmation.exe (PID: 2156)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 3028)
Base64-obfuscated command line is found
- payment confirmation.exe (PID: 1744)
Starts POWERSHELL.EXE for commands execution
- payment confirmation.exe (PID: 1744)
Process drops legitimate windows executable
- payment confirmation.exe (PID: 1744)
BASE64 encoded PowerShell command has been detected
- payment confirmation.exe (PID: 1744)
Process uses IPCONFIG to renew DHCP configuration
- cmd.exe (PID: 1036)
Application launched itself
- payment confirmation.exe (PID: 1744)
Starts CMD.EXE for commands execution
- payment confirmation.exe (PID: 1744)
Checks for external IP
- payment confirmation.exe (PID: 2156)
Accesses Microsoft Outlook profiles
- payment confirmation.exe (PID: 2156)
Connects to SMTP port
- payment confirmation.exe (PID: 2156)
INFO
Checks supported languages
- payment confirmation.exe (PID: 1744)
- payment confirmation.exe (PID: 2156)
Reads the computer name
- payment confirmation.exe (PID: 1744)
- payment confirmation.exe (PID: 2156)
Reads the machine GUID from the registry
- payment confirmation.exe (PID: 1744)
- payment confirmation.exe (PID: 2156)
Creates files or folders in the user directory
- payment confirmation.exe (PID: 1744)
Reads Environment values
- payment confirmation.exe (PID: 2156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(2156) payment confirmation.exe
Protocolsmtp
Hostmail.bezzleauto.com
Port25
Usernamepayables@bezzleauto.com
PasswordKene123456789
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:11 17:10:57+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 855552 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd2d2e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.8.4115.0 |
| ProductVersionNumber: | 4.8.4115.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Microsoft .NET Framework 4.8 Setup |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft .NET Framework 4.8 Setup |
| FileVersion: | 4.8.4115.0 |
| InternalName: | Grzjdxvnv.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | Grzjdxvnv.exe |
| ProductName: | Microsoft .NET Framework 4.8 |
| ProductVersion: | 4.8.4115.0 |
| AssemblyVersion: | 4.8.4115.0 |
Total processes
279
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 976 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2452 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1036 | "C:\Windows\System32\cmd.exe" /c ipconfig /renew | C:\Windows\SysWOW64\cmd.exe | — | payment confirmation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1744 | "C:\Users\admin\AppData\Local\Temp\payment confirmation.exe" | C:\Users\admin\AppData\Local\Temp\payment confirmation.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.8 Setup Exit code: 0 Version: 4.8.4115.0 Modules
| |||||||||||||||
| 1764 | ipconfig /renew | C:\Windows\SysWOW64\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\AppData\Local\Temp\payment confirmation.exe" | C:\Users\admin\AppData\Local\Temp\payment confirmation.exe | payment confirmation.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.8 Setup Exit code: 0 Version: 4.8.4115.0 Modules
AgentTesla(PID) Process(2156) payment confirmation.exe Protocolsmtp Hostmail.bezzleauto.com Port25 Usernamepayables@bezzleauto.com PasswordKene123456789 | |||||||||||||||
| 2260 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2452 CREDAT:726278 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
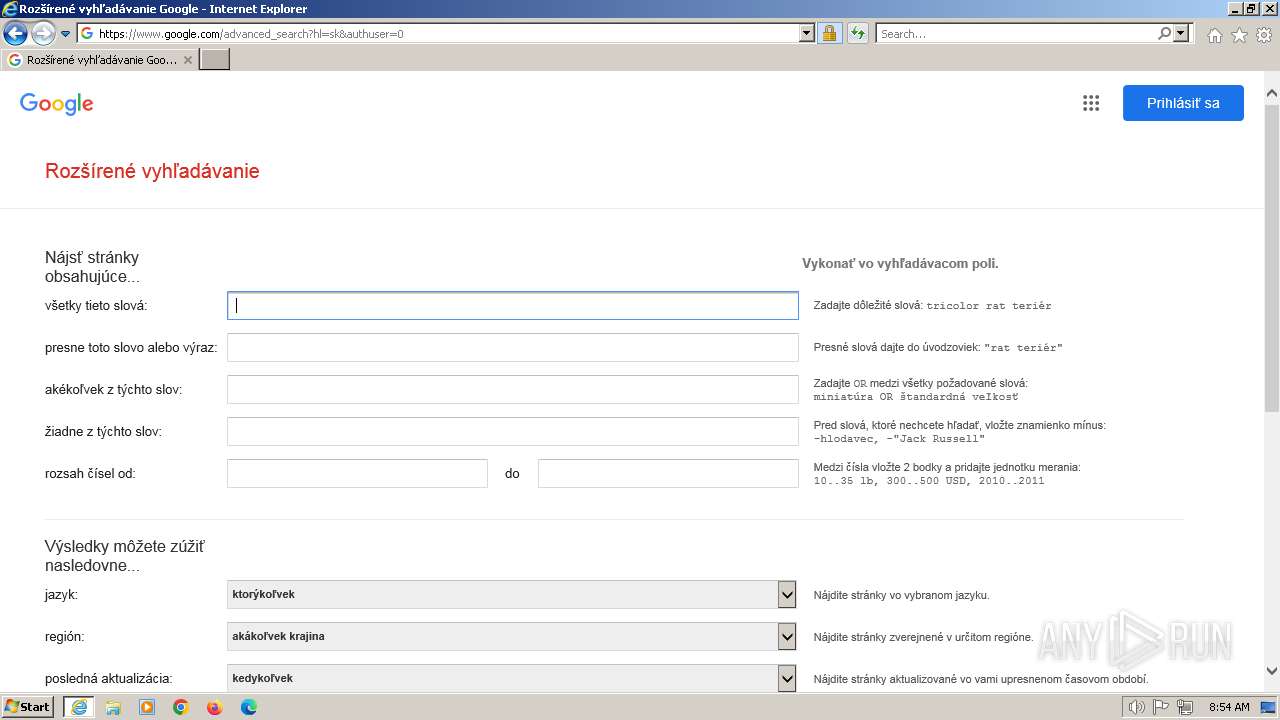
| 2452 | "C:\Program Files\Internet Explorer\iexplore.exe" https://google.com/ | C:\Program Files\Internet Explorer\iexplore.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2620 | ipconfig /release | C:\Windows\SysWOW64\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2856 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc UwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgACcAaAB0AHQAcABzADoALwAvAGcAbwBvAGcAbABlAC4AYwBvAG0AJwA= | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | payment confirmation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3028 | "C:\Windows\System32\cmd.exe" /c ipconfig /release | C:\Windows\SysWOW64\cmd.exe | — | payment confirmation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
7 675
Read events
7 596
Write events
78
Delete events
1
Modification events
| (PID) Process: | (1744) payment confirmation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1744) payment confirmation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1744) payment confirmation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1744) payment confirmation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 5 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 91676960 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31049115 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31049165 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
17
Text files
80
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vb3pf3h5.leq.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1744 | payment confirmation.exe | C:\Users\admin\AppData\Roaming\pdf.exe | executable | |
MD5:099521FA325BBE1280463E5B38464301 | SHA256:10D4F54E3353007E0238CDFE1F380F8130B36A9D53915B78CA759561AEF90ECE | |||
| 2856 | powershell.exe | C:\Users\admin\AppData\Local\Temp\knco0qal.5nr.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UJFUX3OG\LNM8POAU.htm | html | |
MD5:276BBB20C29087E88DB63899FD8F9129 | SHA256:5B61B0C2032B4AA9519D65CC98C6416C12415E02C7FBBAA1BE5121DC75162EDB | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ZOYIQ18X\nav_logo229[1].png | image | |
MD5:1B12CAB0347F8728AF450FE2457E79C3 | SHA256:CA858453CE21CABDF9911C6FA3291AA630DF344244BC183A4D5AE9972E59F675 | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SRO10HZK.txt | text | |
MD5:3DB7BD3D133D5FF9AA77C0DE91913DE4 | SHA256:8ABBA9352965531A3A947CAEB82CEE8416A6965F6971CA95539CA7899137EF98 | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XLWA6BPE\JXN77DF5.htm | html | |
MD5:68CB2BB648EFB05AF19CCA36F2603338 | SHA256:CDDBD5D80A552E8DF1044A28B57C38069CD9D416F510729FE5E22C83EBBAC448 | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YQPEPCE1\tia[1].png | image | |
MD5:201E50D8DD7A30C0A918213686CA43B7 | SHA256:C532312EEA8020A0370685B222A02B11BECD58CD394B509029DFF5956127DD81 | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\FC0ZPZ4C.txt | text | |
MD5:A407C7C33CCD40BA99BE095E623DE9A4 | SHA256:E267A117144CCD091D61623A8EA4E9B68E4C7D9E57E4CEBA03ECEA5156D59098 | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TYNEX6ZJ.txt | text | |
MD5:5389803BD9F36317802D621F2EDFB52C | SHA256:FA0C6C6A178EB3D405DF9ECFFF82350F55B43571EFDC75588E65D3D0CD13FC66 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
69
DNS requests
28
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2156 | payment confirmation.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | text | 6 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
352 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1220 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
976 | iexplore.exe | 172.217.18.110:443 | google.com | GOOGLE | US | whitelisted |
976 | iexplore.exe | 172.217.16.196:443 | www.google.com | GOOGLE | US | whitelisted |
976 | iexplore.exe | 172.217.18.3:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
976 | iexplore.exe | 142.250.185.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
976 | iexplore.exe | 172.217.16.206:443 | clients1.google.com | GOOGLE | US | whitelisted |
2452 | iexplore.exe | 172.217.16.196:443 | www.google.com | GOOGLE | US | whitelisted |
976 | iexplore.exe | 142.250.186.174:443 | apis.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
ip-api.com |
| shared |
mail.bezzleauto.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2156 | payment confirmation.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2156 | payment confirmation.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2156 | payment confirmation.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1 ETPRO signatures available at the full report