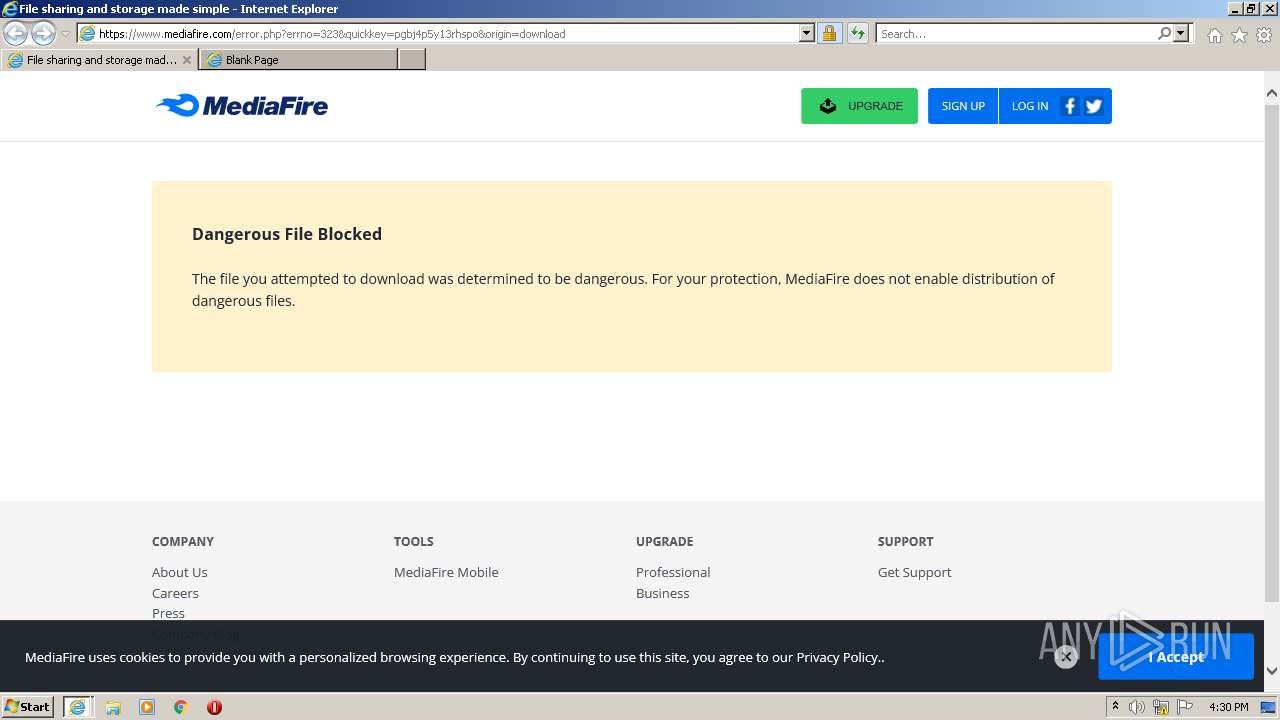
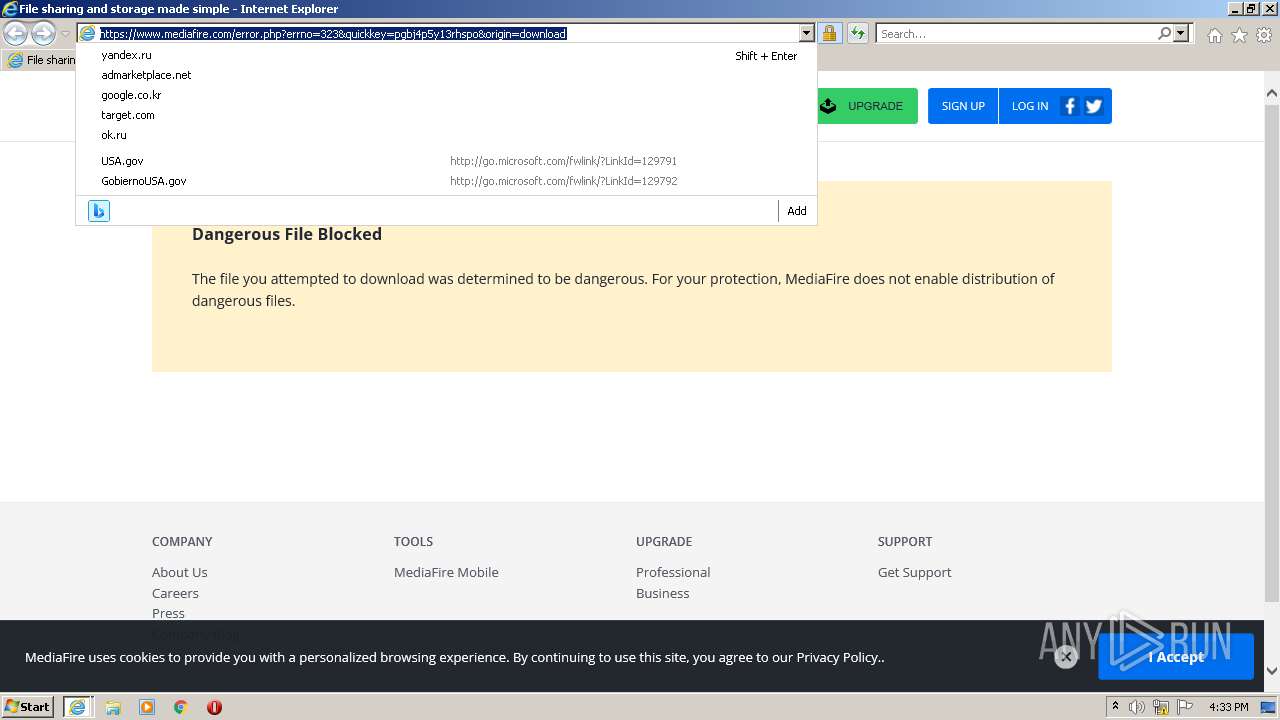
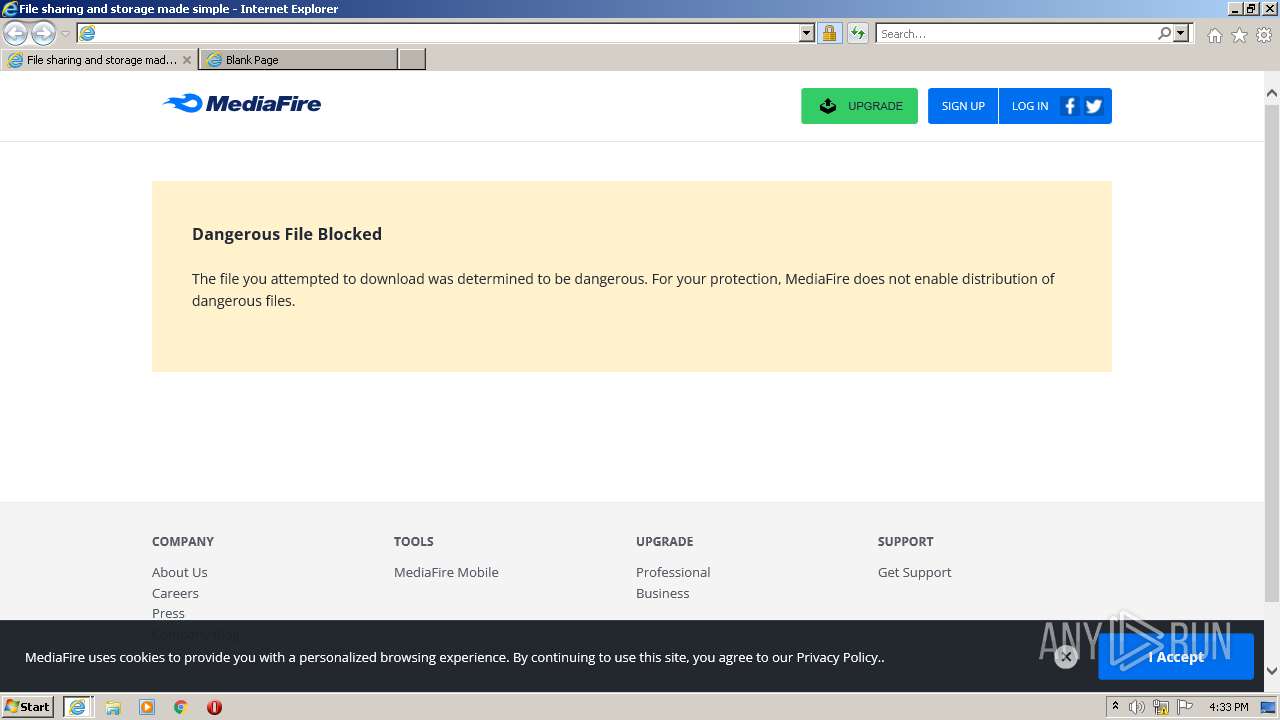
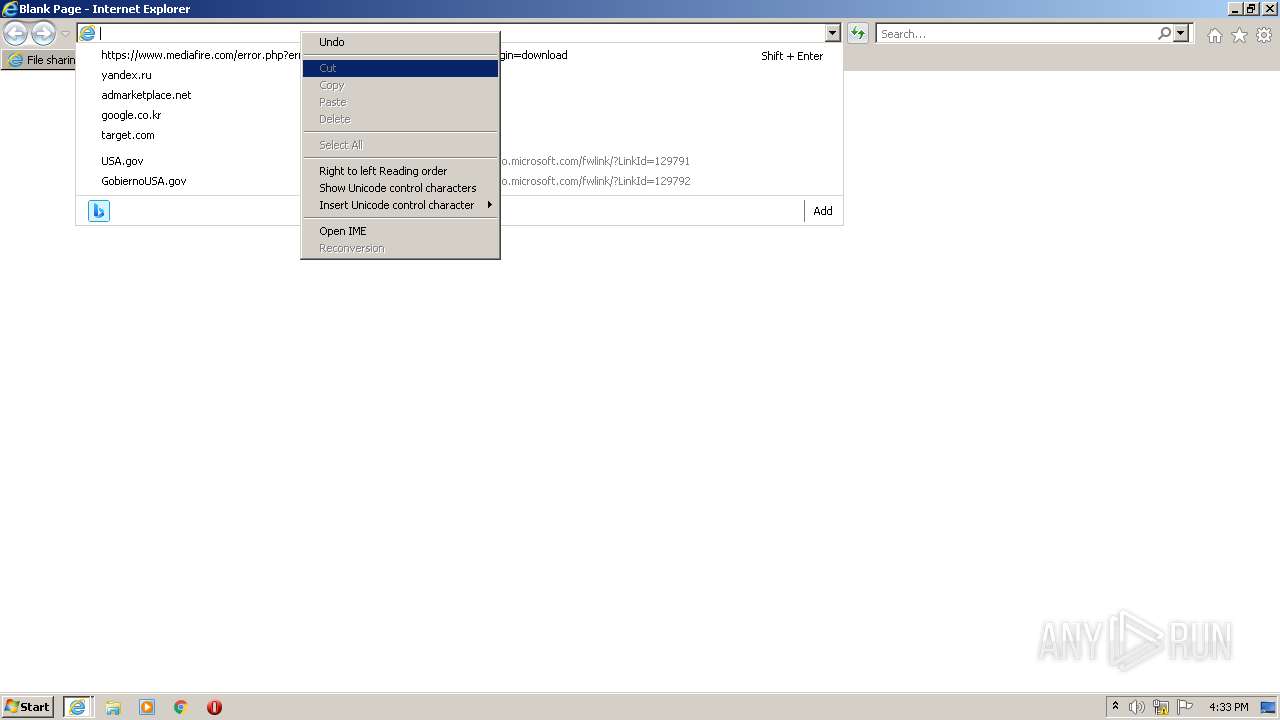
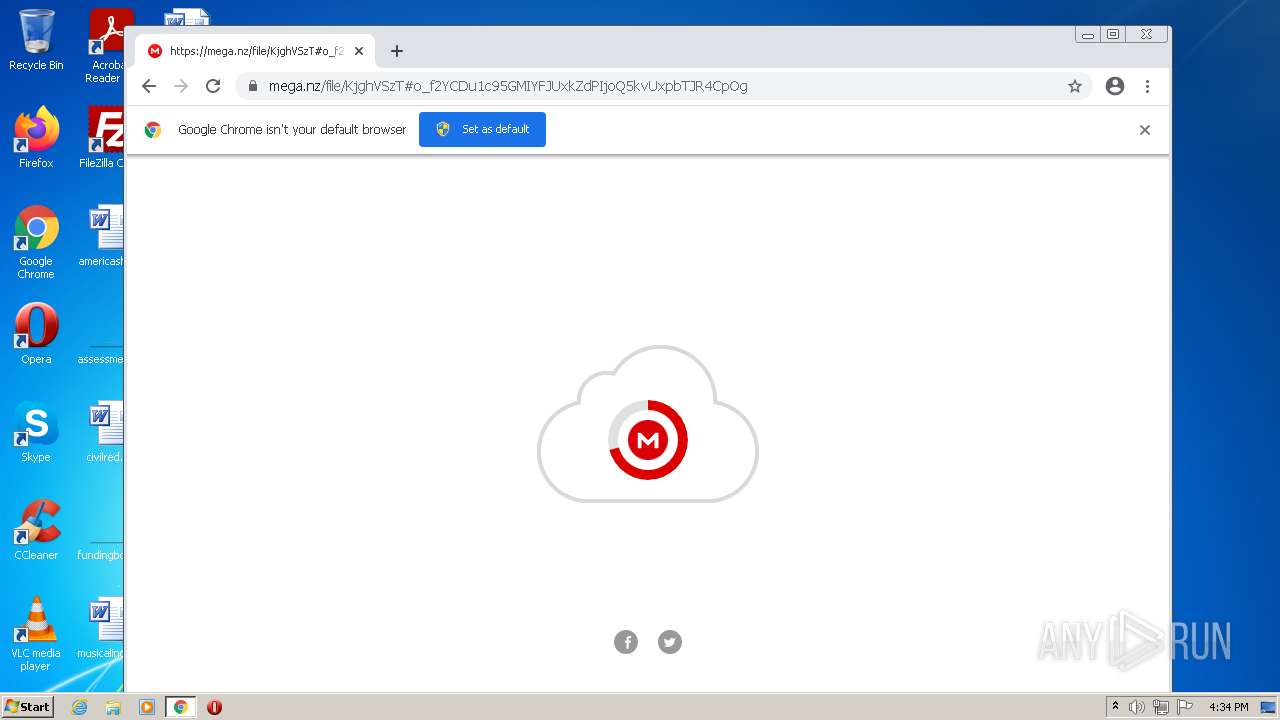
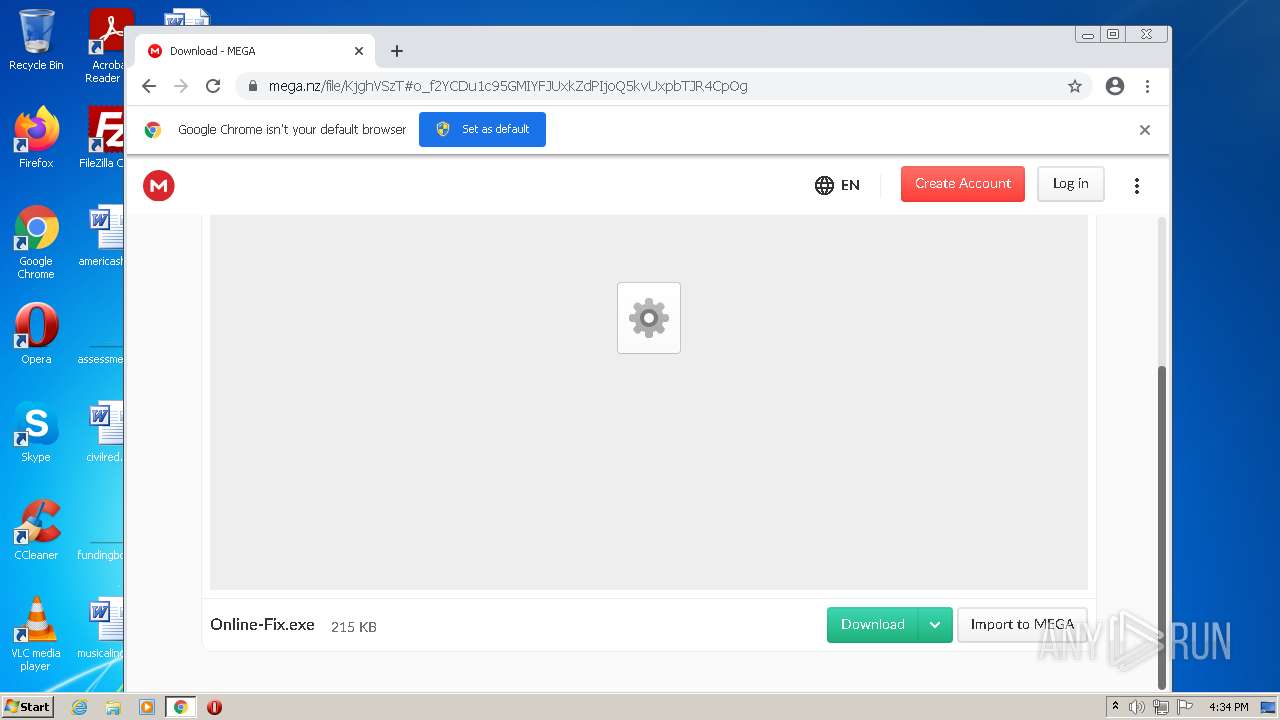
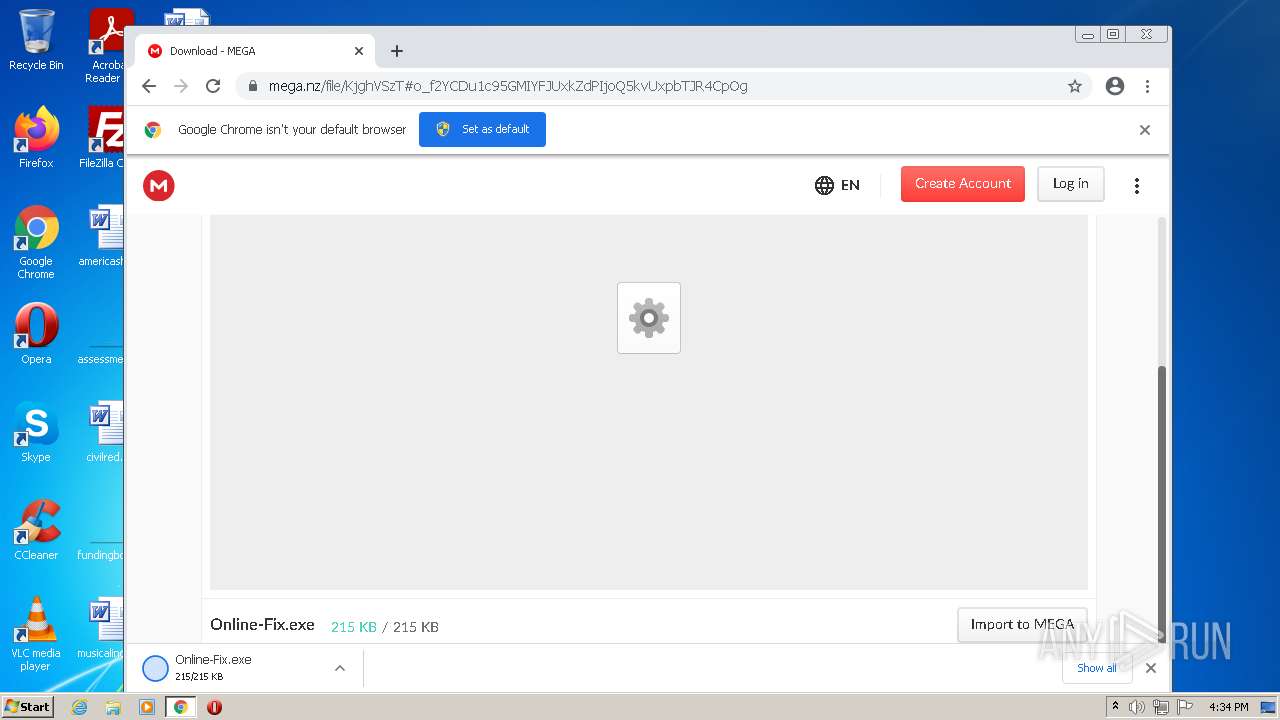
| URL: | https://www.mediafire.com/file/pgbj4p5y13rhspo/Online-Fix.exe/file |
| Full analysis: | https://app.any.run/tasks/11bad1d7-f497-4018-8dd8-243e9d8e01ba |
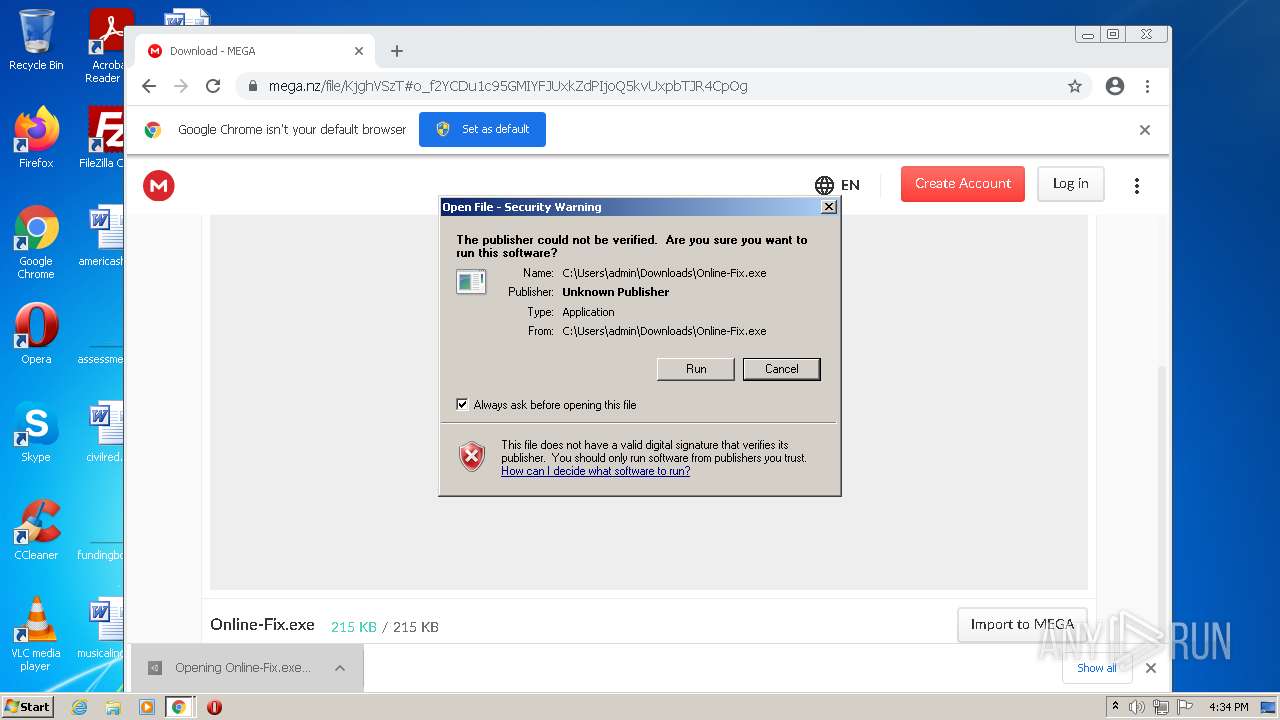
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | February 19, 2022, 16:30:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7D2333340019615DAA8759AA37DB3E95 |
| SHA1: | 738FE64FCE151F950D8CE8D505C2ED4C23979CDD |
| SHA256: | 10CFA7E69969E088444041350D6F6522BE0FAEEA6E5AEA7E4D27344FDDF0BD1E |
| SSDEEP: | 3:N8DSLw3eGUo4/8KLLuIA:2OLw3eGM/u9 |
MALICIOUS
Application was dropped or rewritten from another process
- Online-Fix.exe (PID: 2328)
- EpicWebHelper.exe (PID: 2740)
Changes the autorun value in the registry
- Online-Fix.exe (PID: 2328)
ASYNCRAT was detected
- EpicWebHelper.exe (PID: 2740)
Actions looks like stealing of personal data
- EpicWebHelper.exe (PID: 2740)
Steals credentials from Web Browsers
- EpicWebHelper.exe (PID: 2740)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 2284)
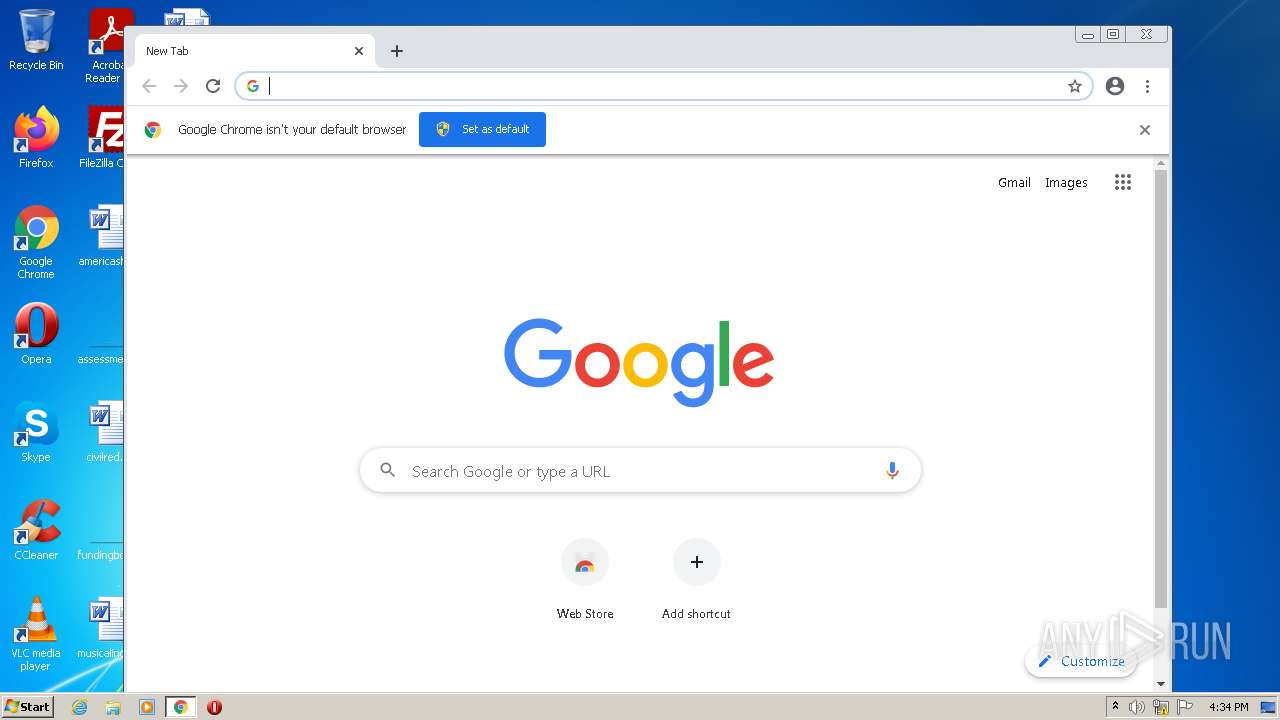
Executable content was dropped or overwritten
- chrome.exe (PID: 2812)
- Online-Fix.exe (PID: 2328)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2812)
Reads the computer name
- Online-Fix.exe (PID: 2328)
- EpicWebHelper.exe (PID: 2740)
Starts CMD.EXE for commands execution
- Online-Fix.exe (PID: 2328)
Checks supported languages
- Online-Fix.exe (PID: 2328)
- cmd.exe (PID: 3808)
- EpicWebHelper.exe (PID: 2740)
Creates files in the user directory
- Online-Fix.exe (PID: 2328)
Reads Environment values
- EpicWebHelper.exe (PID: 2740)
Reads the cookies of Mozilla Firefox
- EpicWebHelper.exe (PID: 2740)
Loads DLL from Mozilla Firefox
- EpicWebHelper.exe (PID: 2740)
INFO
Checks supported languages
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 3860)
- chrome.exe (PID: 2812)
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 968)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 776)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 1648)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 524)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 960)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3736)
- timeout.exe (PID: 1488)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 532)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 3672)
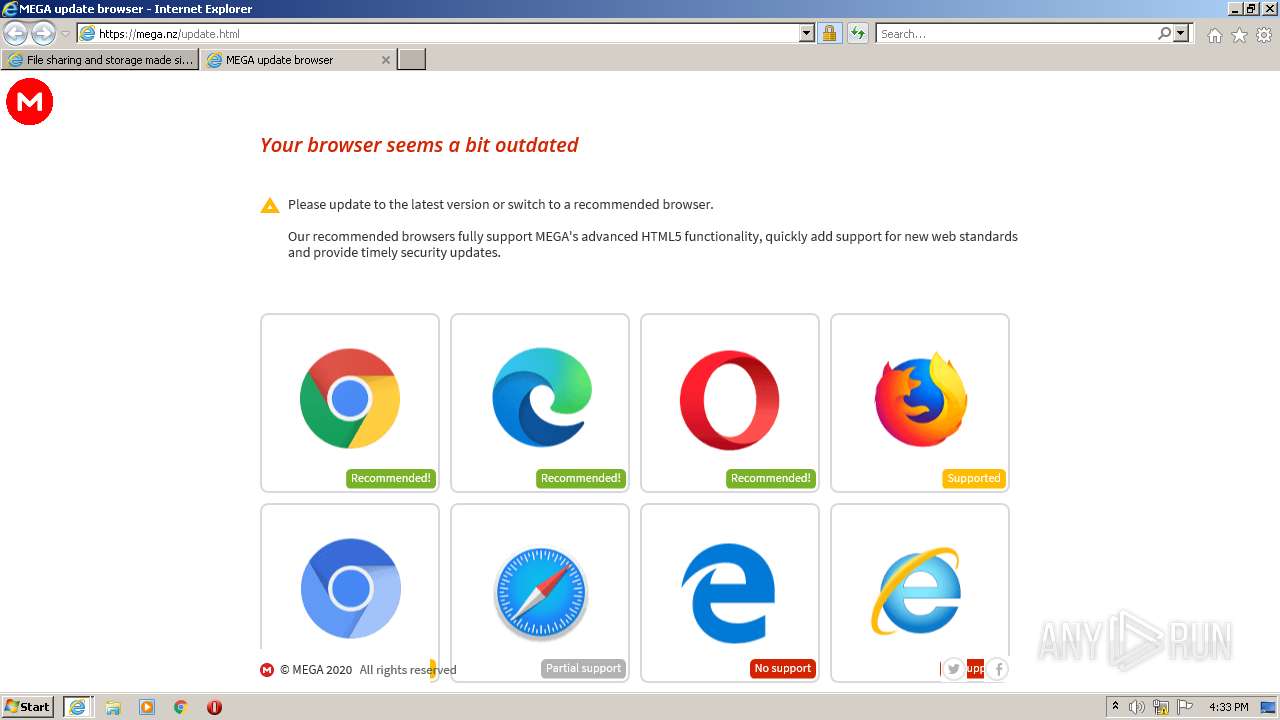
Changes internet zones settings
- iexplore.exe (PID: 1536)
Creates files in the user directory
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 2956)
Reads internet explorer settings
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 2956)
Application launched itself
- iexplore.exe (PID: 1536)
- chrome.exe (PID: 2812)
Reads the computer name
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 968)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 776)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 524)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 532)
- chrome.exe (PID: 3256)
Checks Windows Trust Settings
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 2812)
Reads settings of System Certificates
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 2068)
- EpicWebHelper.exe (PID: 2740)
Changes settings of System certificates
- iexplore.exe (PID: 1536)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1536)
Manual execution by user
- chrome.exe (PID: 2812)
Reads the hosts file
- chrome.exe (PID: 2812)
- chrome.exe (PID: 2068)
Reads the date of Windows installation
- iexplore.exe (PID: 1536)
- chrome.exe (PID: 532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
32
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,8571525639122445037,4263560193577117265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1944 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,8571525639122445037,4263560193577117265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1696 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,8571525639122445037,4263560193577117265,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1076 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,8571525639122445037,4263560193577117265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3880 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,8571525639122445037,4263560193577117265,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1488 | timeout 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
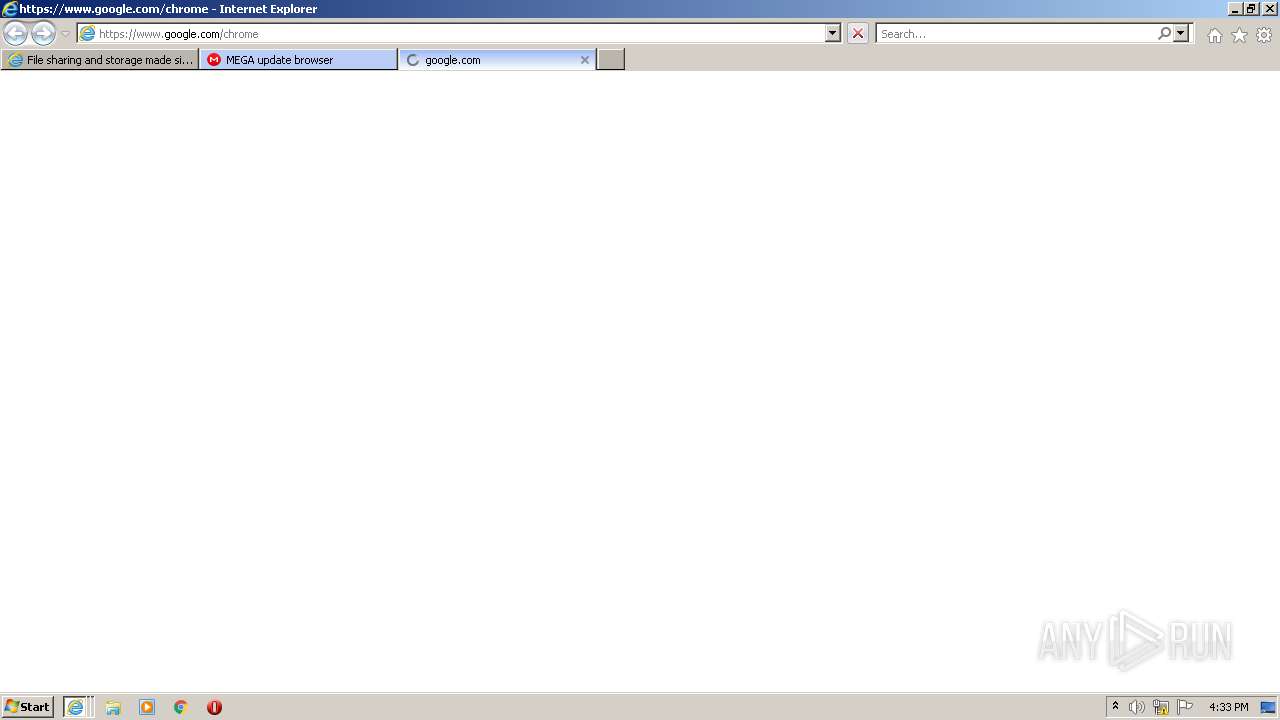
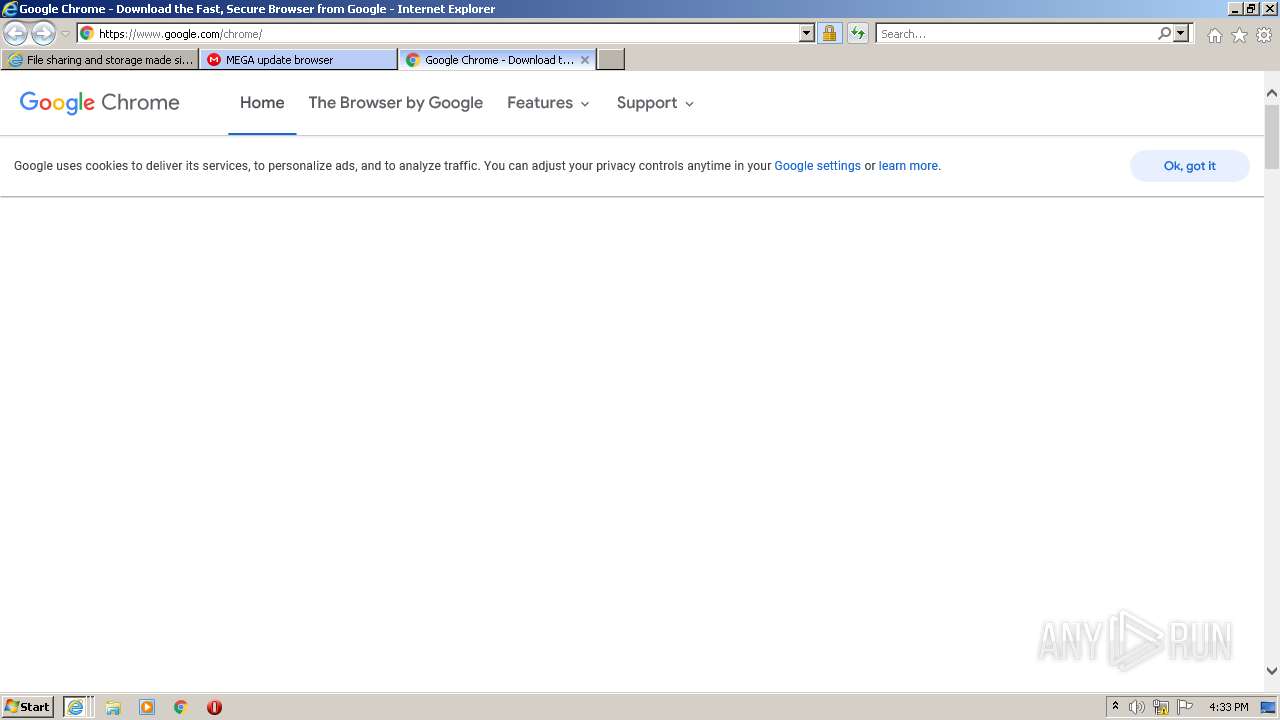
| 1536 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.mediafire.com/file/pgbj4p5y13rhspo/Online-Fix.exe/file" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1020,8571525639122445037,4263560193577117265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3756 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,8571525639122445037,4263560193577117265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1020,8571525639122445037,4263560193577117265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1340 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
46 764
Read events
46 284
Write events
471
Delete events
9
Modification events
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30942637 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 280833152 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30942638 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
232
Text files
298
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | der | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\92GUONXX.txt | text | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\mfv3_121864[1].css | text | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\default[1].png | image | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\H3IN9N0M.txt | text | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\mfv4_121864[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
221
DNS requests
83
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1536 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3860 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.61 Kb | whitelisted |
3860 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEC5GLYwFefbxEgAAAAAAYIc%3D | US | der | 471 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEC5GLYwFefbxEgAAAAAAYIc%3D | US | der | 471 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCYyccBU%2BO5JwoAAAABM%2FlK | US | der | 472 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
3860 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 142.250.185.238:80 | http://crls.pki.goog/gts1c3/moVDfISia2k.crl | US | der | 12.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3860 | iexplore.exe | 104.16.202.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
3860 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
3860 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
1536 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 142.250.181.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3860 | iexplore.exe | 142.250.181.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3860 | iexplore.exe | 104.16.95.65:443 | static.cloudflareinsights.com | Cloudflare Inc | US | shared |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3860 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
static.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
2740 | EpicWebHelper.exe | A Network Trojan was detected | ET TROJAN Observed Malicious SSL Cert (AsyncRAT Server) |
1 ETPRO signatures available at the full report