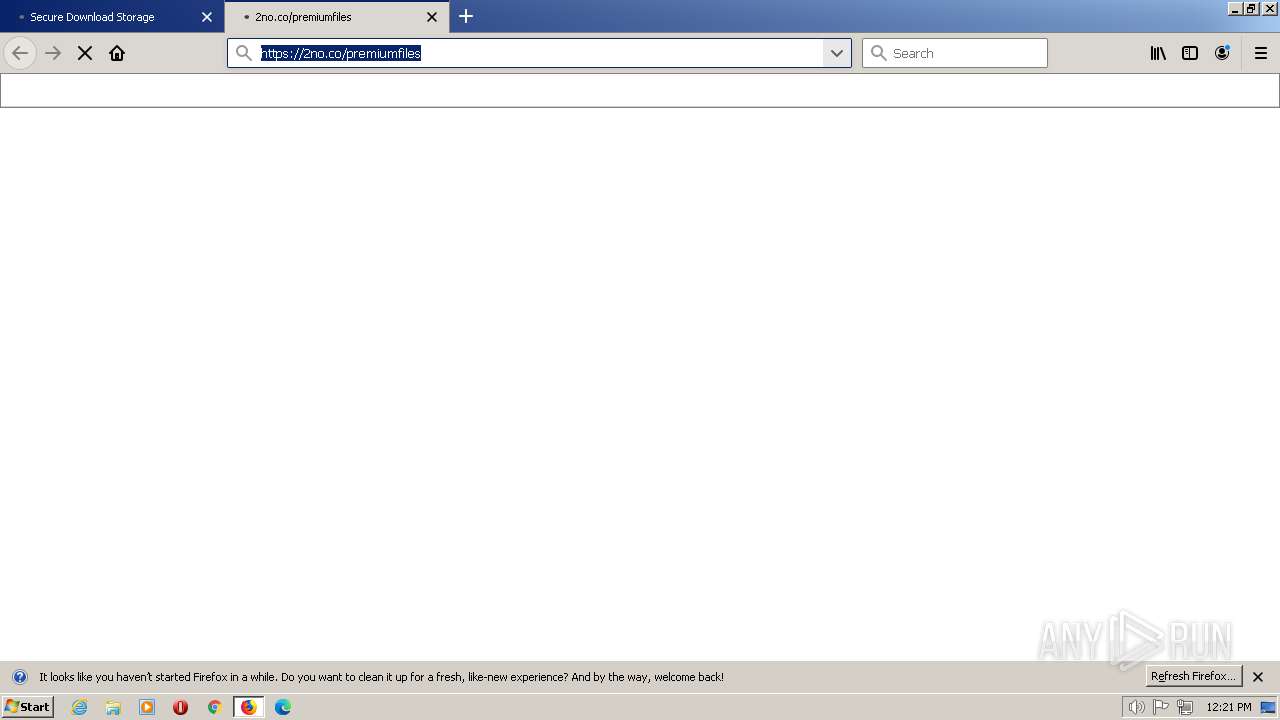
| URL: | https://boraflow.click |
| Full analysis: | https://app.any.run/tasks/710f9d6a-6a3d-4a7f-9194-190035fbe60d |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | July 14, 2023, 12:19:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2F17E2573EAAAC5AD05DD98AA1DDC688 |
| SHA1: | E6522EDB1834C345E33105994EEC2537C83E1068 |
| SHA256: | 104B3CD96A1A45EC98B1A9BC98E2A39E8B4EB9F60FE9535A89F4A1D91C66103C |
| SSDEEP: | 3:N87au:29 |
MALICIOUS
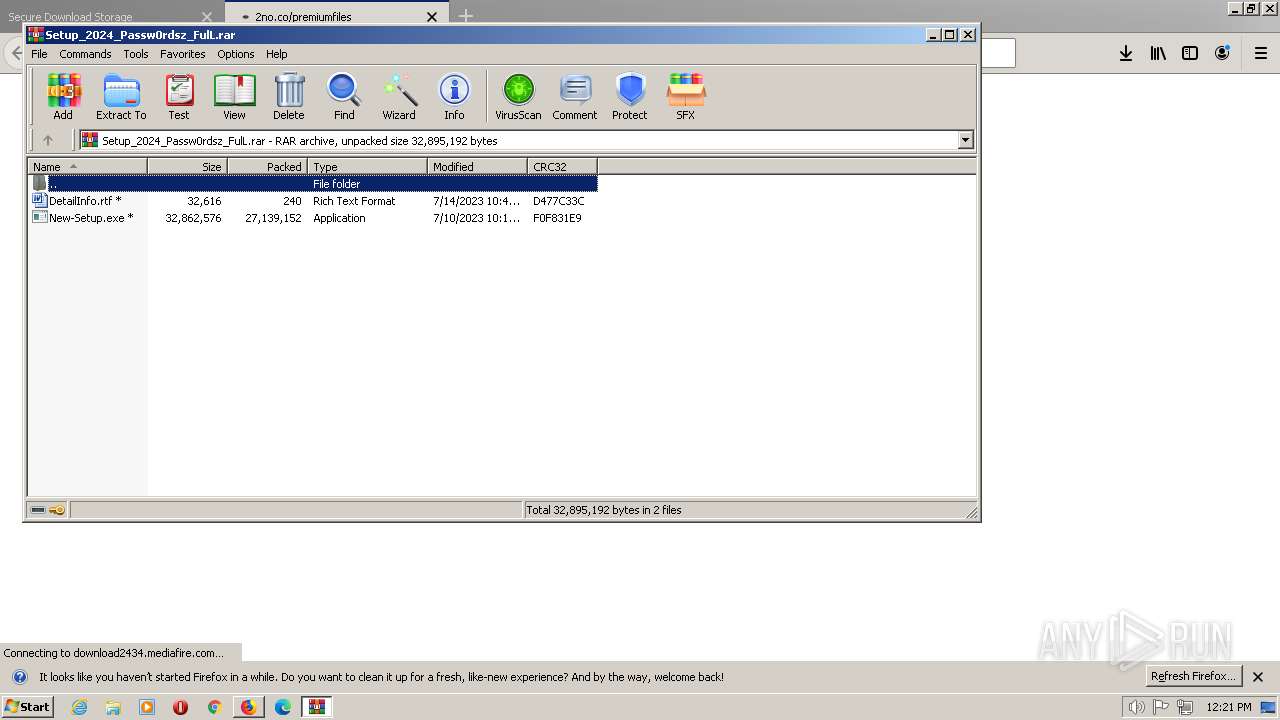
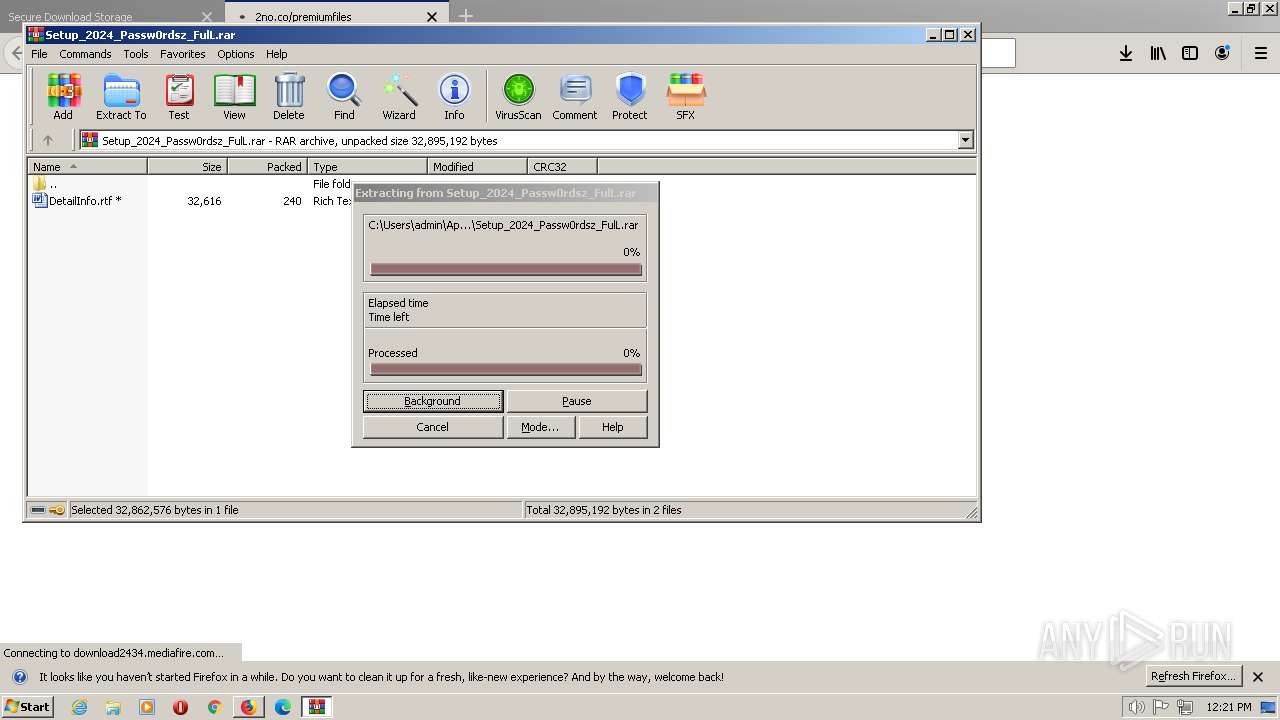
Application was dropped or rewritten from another process
- New-Setup.exe (PID: 2856)
- 91711067540821990379.exe (PID: 3216)
- jbruyer.exe (PID: 1260)
- jbruyer.exe (PID: 3572)
ARKEI detected by memory dumps
- AddInProcess32.exe (PID: 1400)
Steals credentials from Web Browsers
- AddInProcess32.exe (PID: 1400)
Connects to the CnC server
- AddInProcess32.exe (PID: 1400)
- jbruyer.exe (PID: 1260)
VIDAR was detected
- AddInProcess32.exe (PID: 1400)
Steals credentials
- AddInProcess32.exe (PID: 1400)
Loads dropped or rewritten executable
- AddInProcess32.exe (PID: 1400)
- rundll32.exe (PID: 1592)
- rundll32.exe (PID: 3464)
- WerFault.exe (PID: 2168)
- rundll32.exe (PID: 1960)
Changes the autorun value in the registry
- jbruyer.exe (PID: 1260)
Uses Task Scheduler to run other applications
- jbruyer.exe (PID: 1260)
AMADEY was detected
- jbruyer.exe (PID: 1260)
Actions looks like stealing of personal data
- rundll32.exe (PID: 1592)
- AddInProcess32.exe (PID: 1400)
SUSPICIOUS
Reads the Internet Settings
- New-Setup.exe (PID: 2856)
- AddInProcess32.exe (PID: 1400)
- jbruyer.exe (PID: 1260)
- 91711067540821990379.exe (PID: 3216)
Starts POWERSHELL.EXE for commands execution
- New-Setup.exe (PID: 2856)
Reads settings of System Certificates
- New-Setup.exe (PID: 2856)
- AddInProcess32.exe (PID: 1400)
The process bypasses the loading of PowerShell profile settings
- New-Setup.exe (PID: 2856)
BASE64 encoded PowerShell command has been detected
- New-Setup.exe (PID: 2856)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- AddInProcess32.exe (PID: 1400)
Checks Windows Trust Settings
- AddInProcess32.exe (PID: 1400)
Reads security settings of Internet Explorer
- AddInProcess32.exe (PID: 1400)
Executable content was dropped or overwritten
- AddInProcess32.exe (PID: 1400)
- 91711067540821990379.exe (PID: 3216)
- jbruyer.exe (PID: 1260)
Loads DLL from Mozilla Firefox
- AddInProcess32.exe (PID: 1400)
- rundll32.exe (PID: 1592)
Reads browser cookies
- AddInProcess32.exe (PID: 1400)
Searches for installed software
- AddInProcess32.exe (PID: 1400)
Starts itself from another location
- 91711067540821990379.exe (PID: 3216)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2628)
- jbruyer.exe (PID: 1260)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2628)
Application launched itself
- cmd.exe (PID: 2628)
Connects to the server without a host name
- jbruyer.exe (PID: 1260)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 3464)
Process requests binary or script from the Internet
- jbruyer.exe (PID: 1260)
The process executes via Task Scheduler
- jbruyer.exe (PID: 3572)
INFO
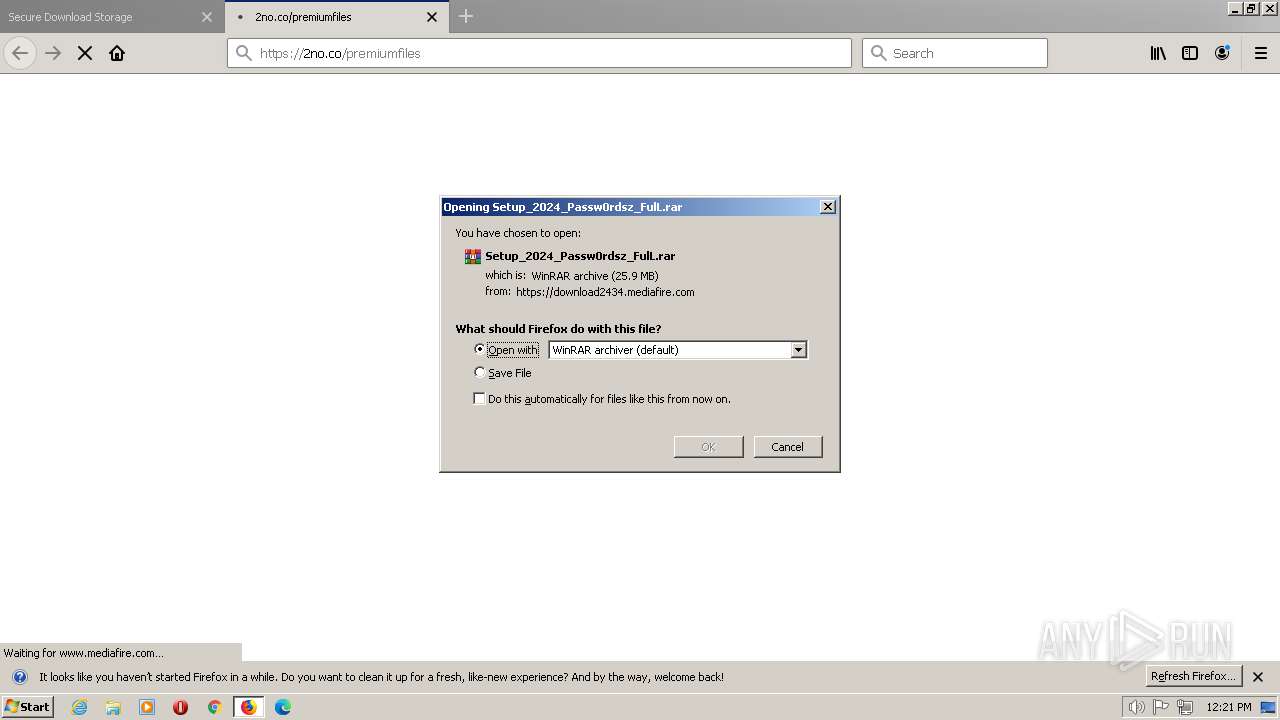
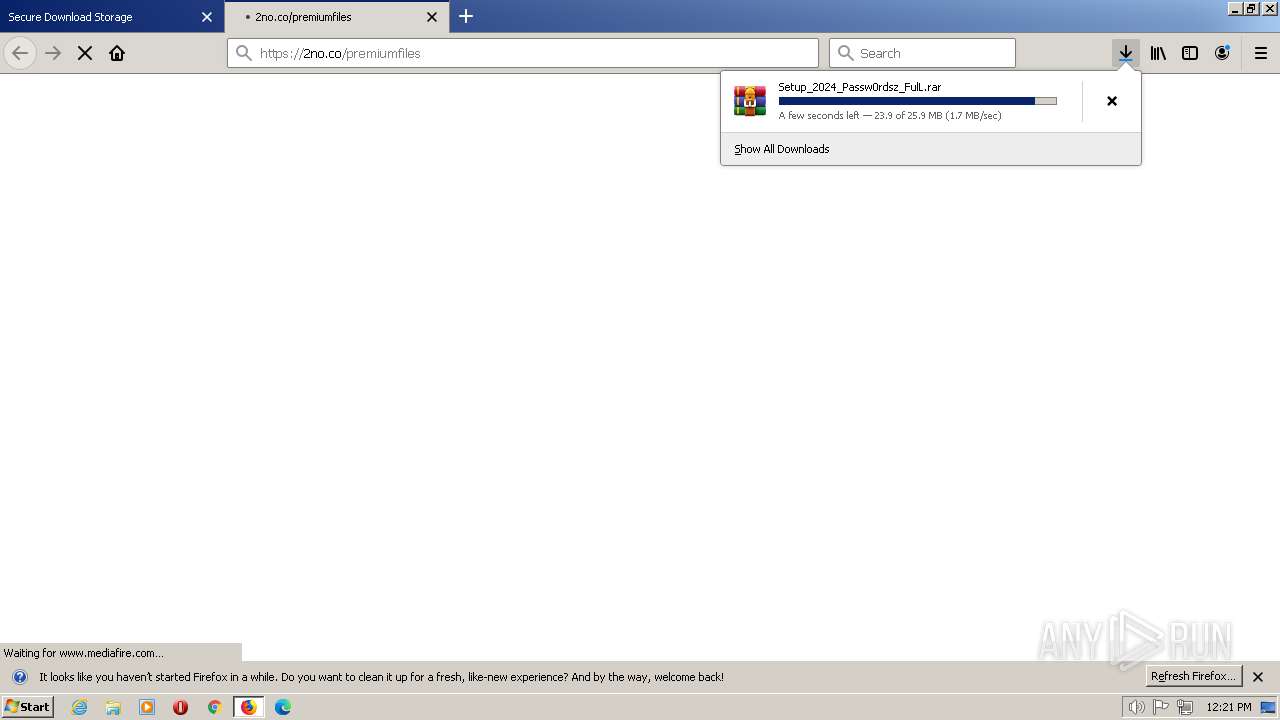
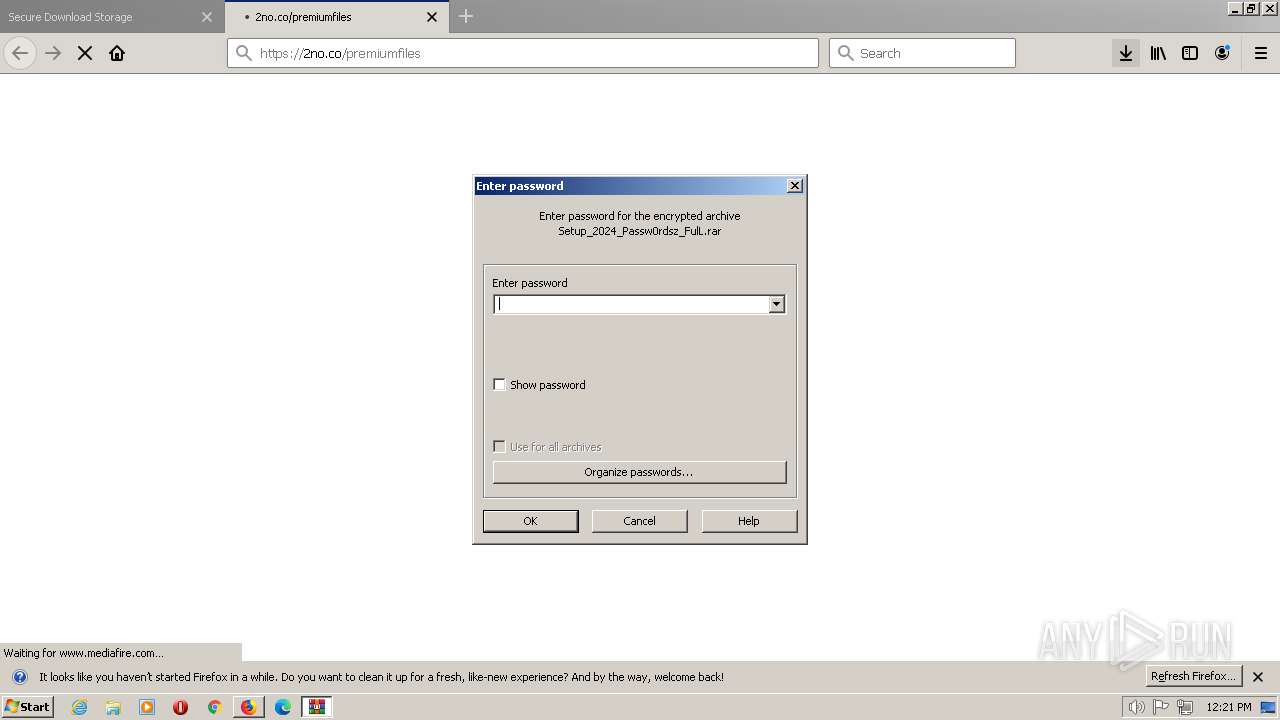
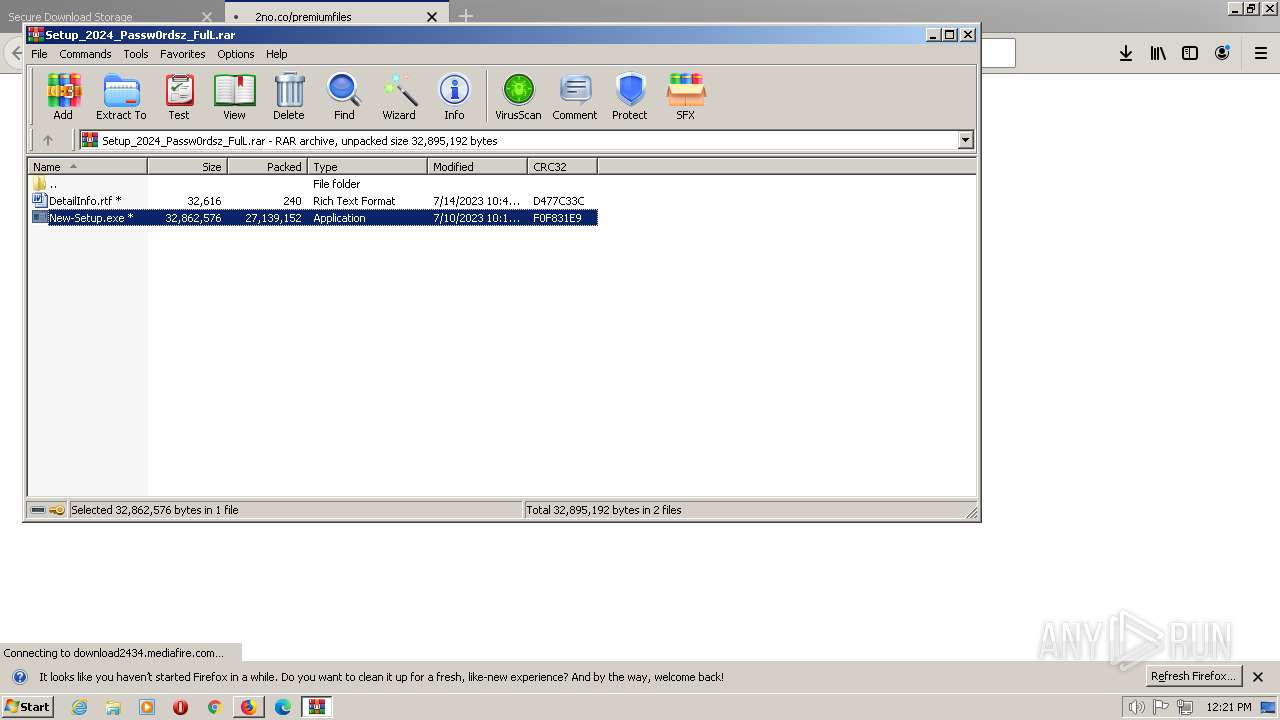
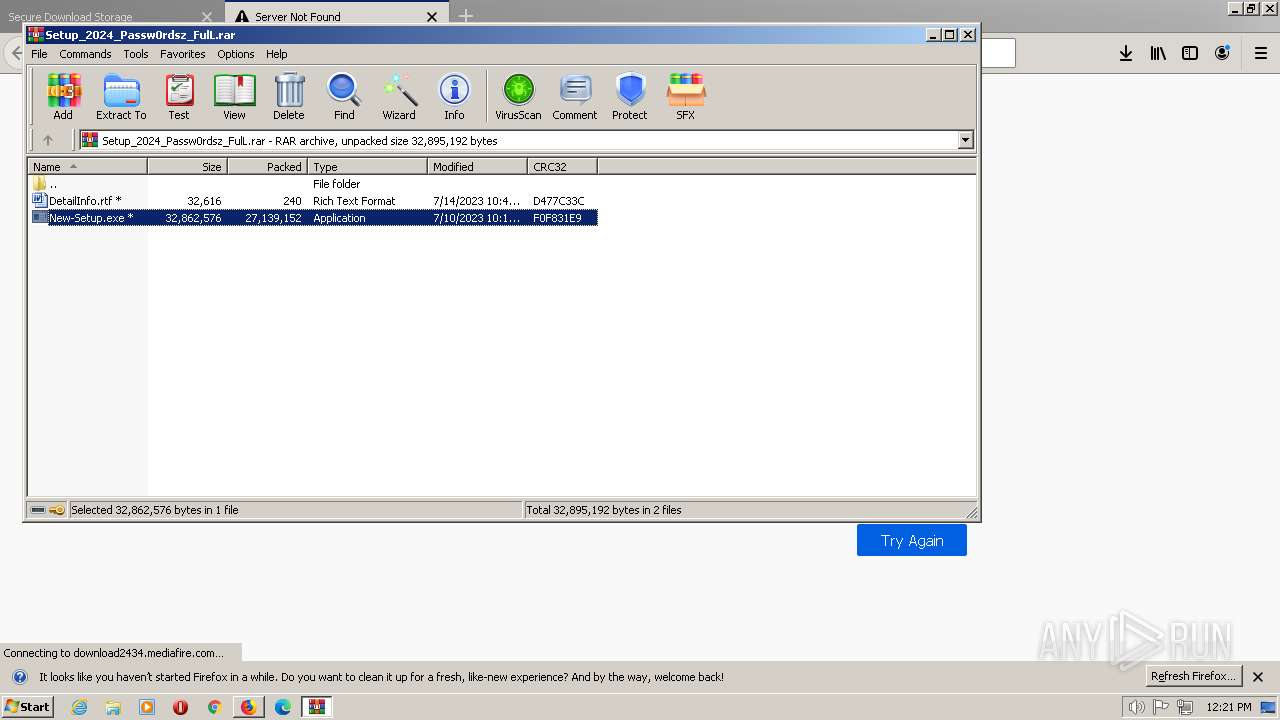
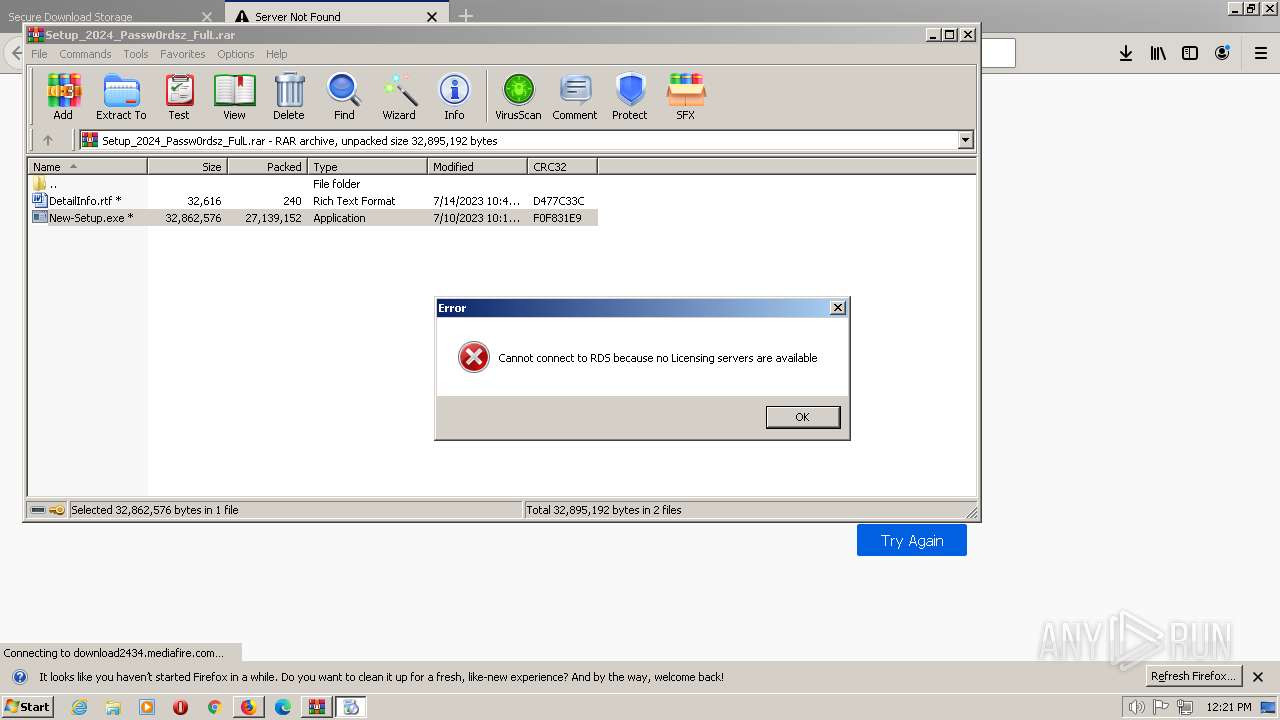
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2360)
- firefox.exe (PID: 1948)
Application launched itself
- firefox.exe (PID: 1948)
The process uses the downloaded file
- firefox.exe (PID: 1948)
- WinRAR.exe (PID: 2360)
Checks supported languages
- New-Setup.exe (PID: 2856)
- AddInProcess32.exe (PID: 1400)
- 91711067540821990379.exe (PID: 3216)
- jbruyer.exe (PID: 1260)
- jbruyer.exe (PID: 3572)
Reads the computer name
- New-Setup.exe (PID: 2856)
- AddInProcess32.exe (PID: 1400)
- 91711067540821990379.exe (PID: 3216)
- jbruyer.exe (PID: 1260)
Reads the machine GUID from the registry
- New-Setup.exe (PID: 2856)
- AddInProcess32.exe (PID: 1400)
- 91711067540821990379.exe (PID: 3216)
- jbruyer.exe (PID: 1260)
The process checks LSA protection
- New-Setup.exe (PID: 2856)
- AddInProcess32.exe (PID: 1400)
- 91711067540821990379.exe (PID: 3216)
- jbruyer.exe (PID: 1260)
Create files in a temporary directory
- New-Setup.exe (PID: 2856)
- 91711067540821990379.exe (PID: 3216)
- jbruyer.exe (PID: 1260)
Checks proxy server information
- New-Setup.exe (PID: 2856)
- AddInProcess32.exe (PID: 1400)
- jbruyer.exe (PID: 1260)
Creates files or folders in the user directory
- AddInProcess32.exe (PID: 1400)
- jbruyer.exe (PID: 1260)
Creates files in the program directory
- AddInProcess32.exe (PID: 1400)
Reads Environment values
- AddInProcess32.exe (PID: 1400)
Reads product name
- AddInProcess32.exe (PID: 1400)
Reads CPU info
- AddInProcess32.exe (PID: 1400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
26
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1948.27.1632153104\2133814738" -childID 4 -isForBrowser -prefsHandle 2916 -prefMapHandle 2016 -prefsLen 6726 -prefMapSize 189239 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1948 "\\.\pipe\gecko-crash-server-pipe.1948" 3644 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 1260 | "C:\Users\admin\AppData\Local\Temp\c2868ed41c\jbruyer.exe" | C:\Users\admin\AppData\Local\Temp\c2868ed41c\jbruyer.exe | 91711067540821990379.exe | ||||||||||||
User: admin Company: NortonLifeLock Inc. Integrity Level: MEDIUM Description: Norton Remove and Reinstall Exit code: 0 Version: 4.5.0.157 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1948.20.1404393709\803560882" -childID 3 -isForBrowser -prefsHandle 3324 -prefMapHandle 3336 -prefsLen 6545 -prefMapSize 189239 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1948 "\\.\pipe\gecko-crash-server-pipe.1948" 3348 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 1400 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | New-Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.7.2558.0 built by: NET471REL1 Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\cmd.exe /S /D /c" echo Y" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1592 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\cred64.dll, Main | C:\Windows\System32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | CACLS "jbruyer.exe" /P "admin:N" | C:\Windows\SysWOW64\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://boraflow.click" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 1960 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\clip64.dll, Main | C:\Windows\SysWOW64\rundll32.exe | — | jbruyer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | C:\Windows\system32\WerFault.exe -u -p 1592 -s 324 | C:\Windows\System32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 655
Read events
10 568
Write events
87
Delete events
0
Modification events
| (PID) Process: | (1948) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (1948) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1948) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000008E000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1948) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1948) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1948) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1948) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\155\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7AndW2K8R2-KB3191566-x64.zip | |||
Executable files
19
Suspicious files
245
Text files
50
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1948 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\urlCache-current.bin | binary | |
MD5:6BED2A248268034CA1F73B2925365DE2 | SHA256:A45996AA907815E86366A17ED448F75A584D7B600AA9398E14DE21DFAD3D613A | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:2B6B5ABCA010270C502C5DD277CD9E7A | SHA256:99DF8717921F70577FCE3386BB7962A804E490C7157F764458001843A1EC606C | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\prefs-1.js | text | |
MD5:1759FBCEFAC92AE1A7B8E457ACF71748 | SHA256:5DA473B0E0C84BE5B289DC97C259B98F674E17AF49F4723B4A90F73AA972B739 | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1948 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\NLTXVM~1.DEF\cert9.db-journal | binary | |
MD5:792D2ECB457ED874B257F847CB42A25D | SHA256:7BD5F09CDC8D4707248C78A58AD4760F94C52046FE11E09FC1F31410522C635D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
114
DNS requests
156
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1400 | AddInProcess32.exe | GET | — | 128.140.92.122:8081 | http://128.140.92.122:8081/files.zip | IR | — | — | malicious |
1948 | firefox.exe | GET | — | 2.22.61.56:80 | http://ciscobinary.openh264.org/openh264-win64-2e1774ab6dc6c43debb0b5b628bdf122a391d521.zip | unknown | — | — | whitelisted |
1948 | firefox.exe | POST | 200 | 184.24.77.82:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
1948 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
1948 | firefox.exe | POST | 200 | 184.24.77.82:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
1948 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | whitelisted |
1948 | firefox.exe | POST | 200 | 184.24.77.82:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
1948 | firefox.exe | POST | 200 | 184.24.77.82:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
1948 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
1948 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1948 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
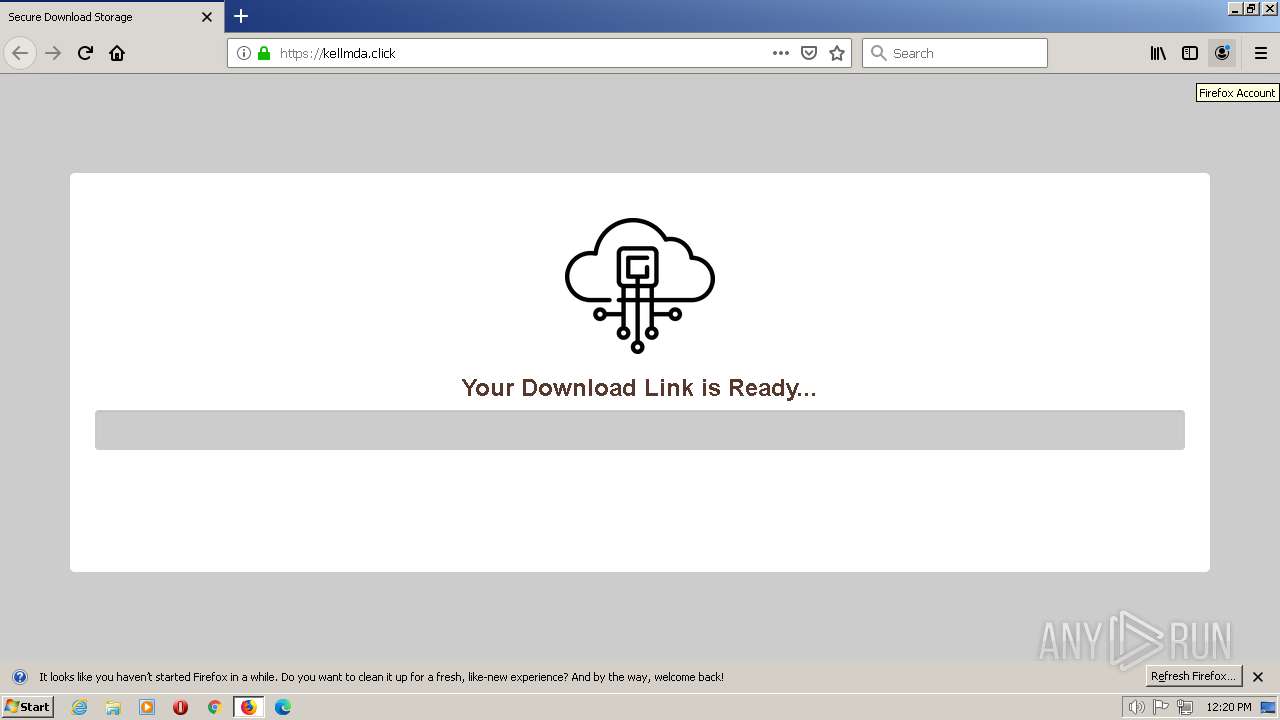
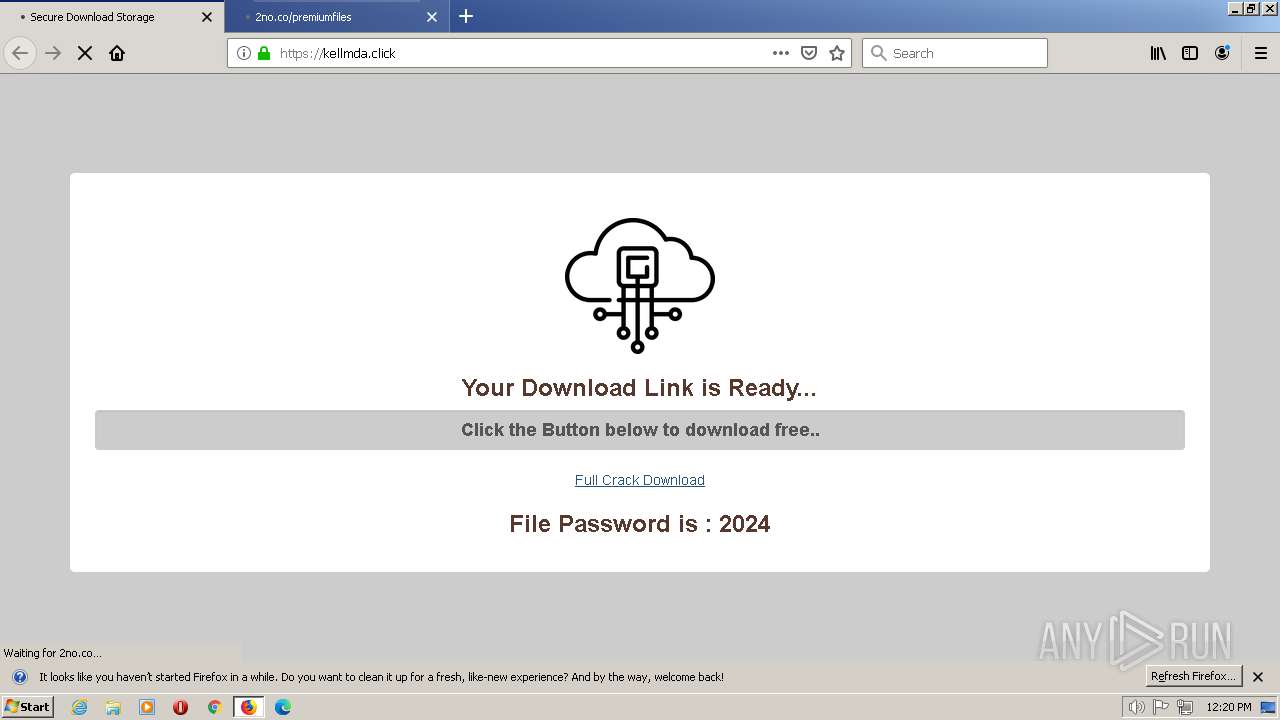
1948 | firefox.exe | 172.67.162.209:443 | boraflow.click | CLOUDFLARENET | US | unknown |
1948 | firefox.exe | 34.160.46.54:443 | search.services.mozilla.com | GOOGLE | US | suspicious |
1948 | firefox.exe | 34.117.65.55:443 | push.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | suspicious |
1948 | firefox.exe | 13.32.121.49:443 | snippets.cdn.mozilla.net | AMAZON-02 | US | suspicious |
1948 | firefox.exe | 188.114.96.3:443 | kellmda.click | CLOUDFLARENET | NL | malicious |
1948 | firefox.exe | 184.24.77.82:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
1948 | firefox.exe | 13.32.121.85:443 | snippets.cdn.mozilla.net | AMAZON-02 | US | suspicious |
1948 | firefox.exe | 52.11.233.163:443 | shavar.services.mozilla.com | AMAZON-02 | US | unknown |
1948 | firefox.exe | 188.114.97.3:443 | kellmda.click | CLOUDFLARENET | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
boraflow.click |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
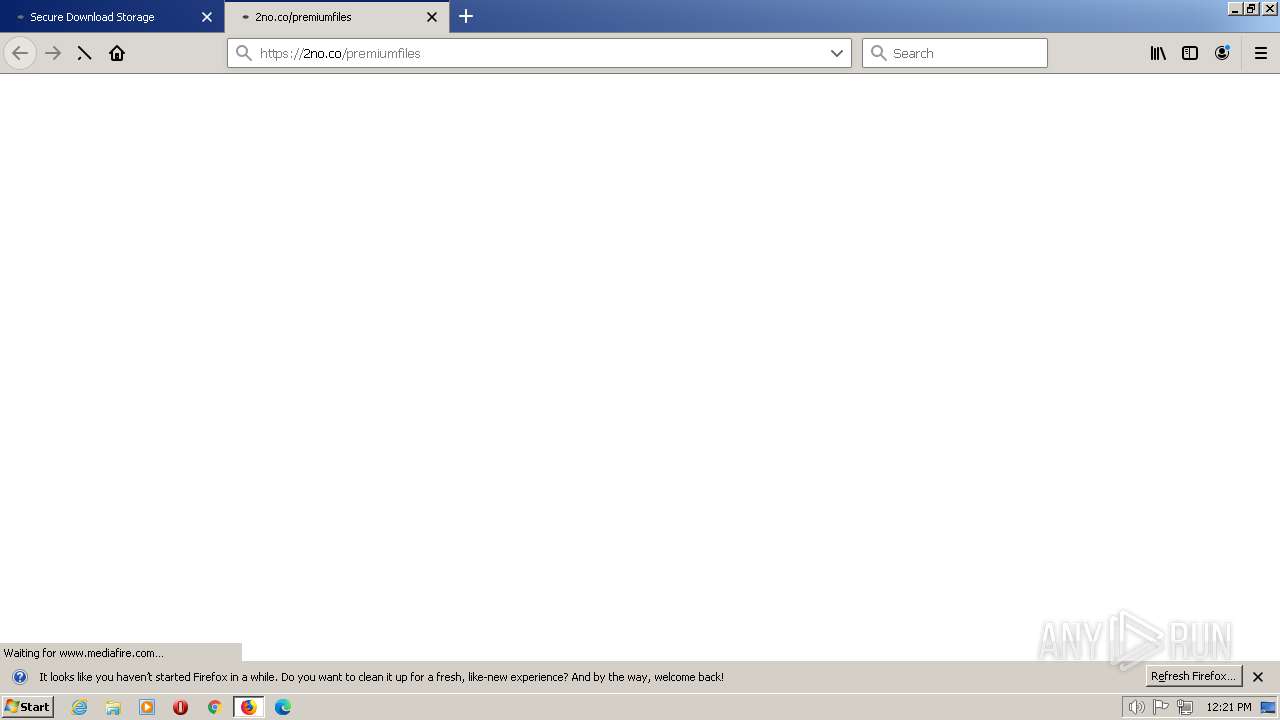
324 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
324 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
324 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
324 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
324 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
324 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
324 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
324 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1400 | AddInProcess32.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
1400 | AddInProcess32.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
2 ETPRO signatures available at the full report