| File name: | docropool.exe |
| Full analysis: | https://app.any.run/tasks/87e34c3c-3948-4950-ab5a-c35f965f6f01 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | February 27, 2019, 15:10:10 |
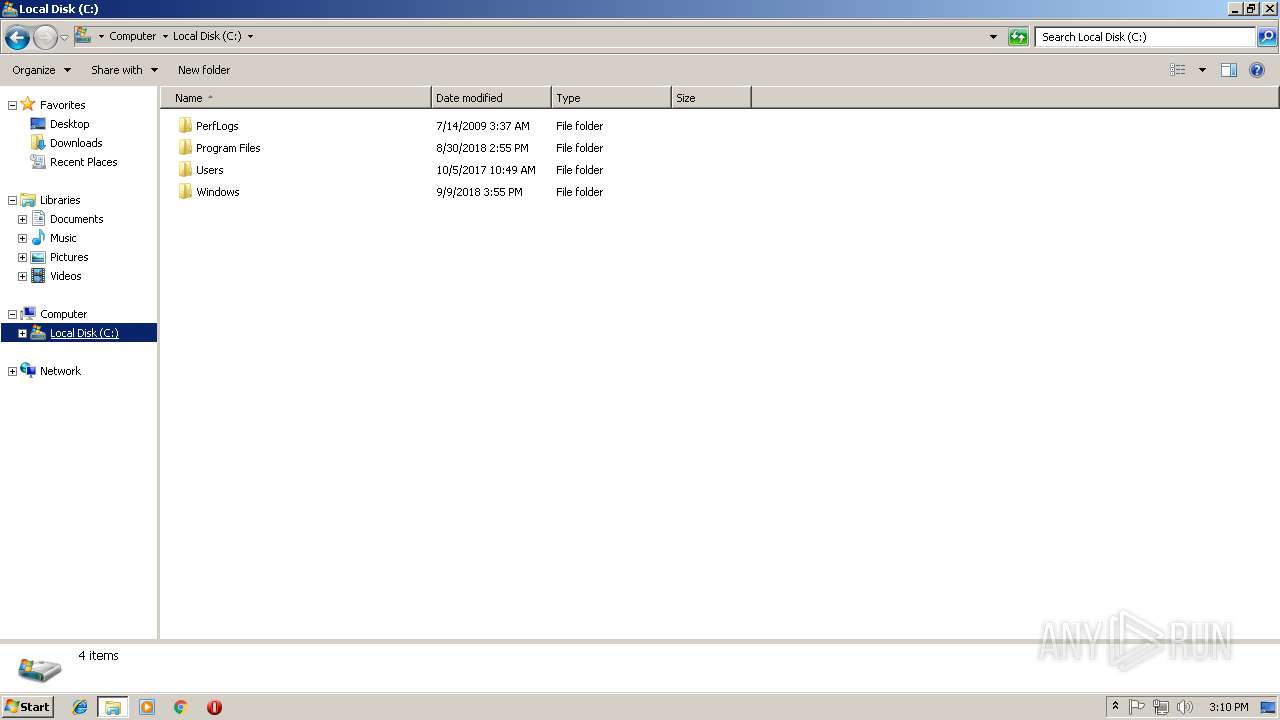
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 36968503F54DAD1165A47EE5DEC357FF |
| SHA1: | 0F007A09C859CF1C0EEF85B55068B9770E0ADB2A |
| SHA256: | 100B49C780AC60366FF07517B96D4B090F3A420D24D5200B9252C5E0EAB38380 |
| SSDEEP: | 98304:hNguFpgSHhKafJo569O80DSRQK7Mxr4uYeV+R/bGlicUw3YIkaDR3AuVgc3Uv1:hNc06U7RQ9xaeVITP43Xkw3Pe |
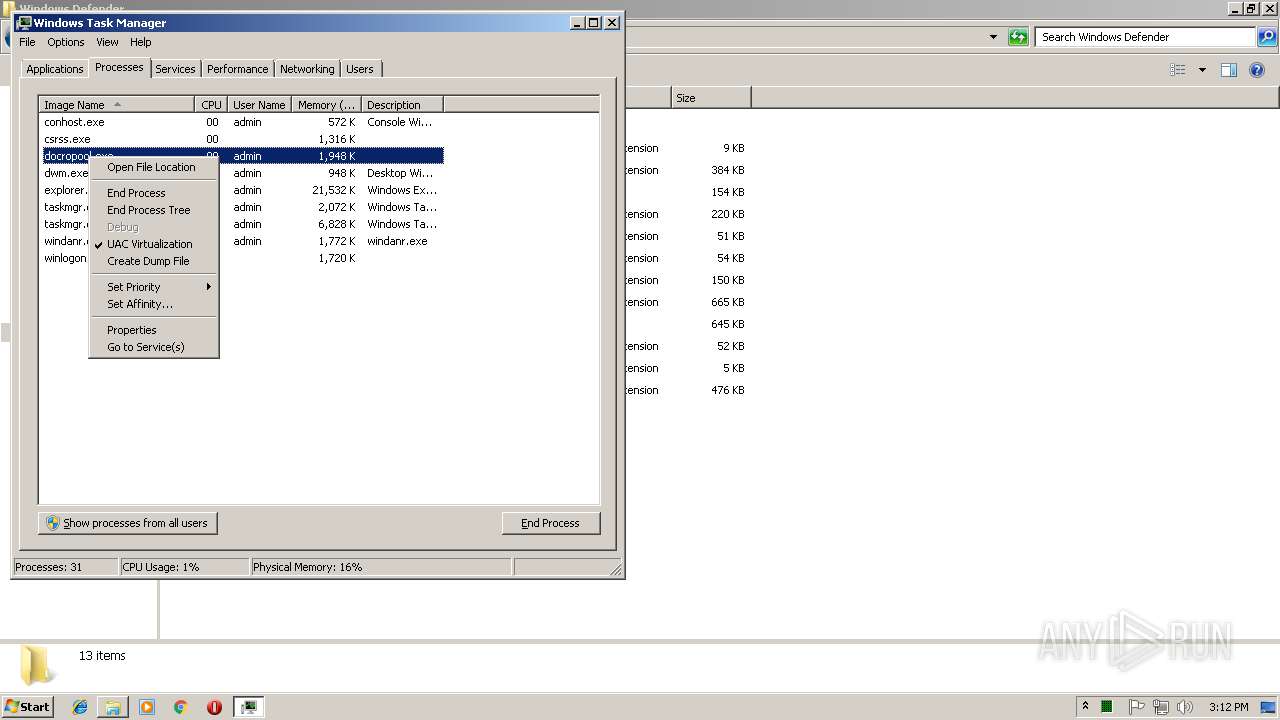
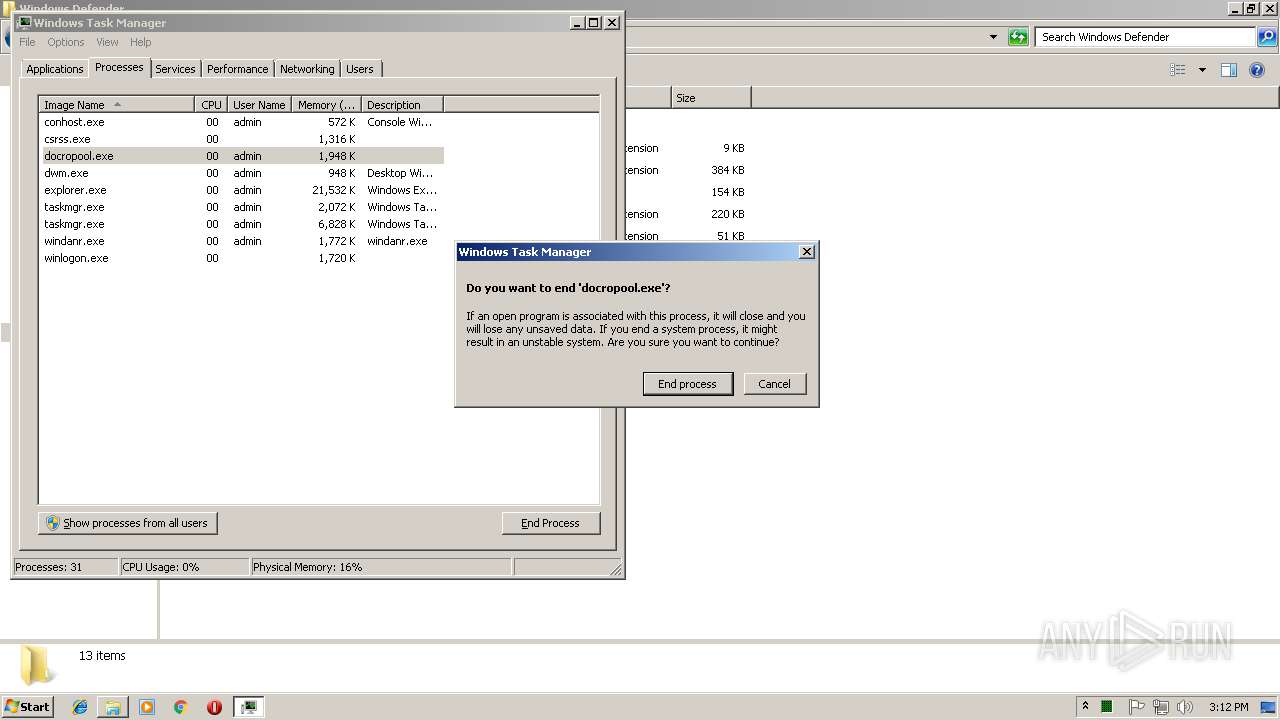
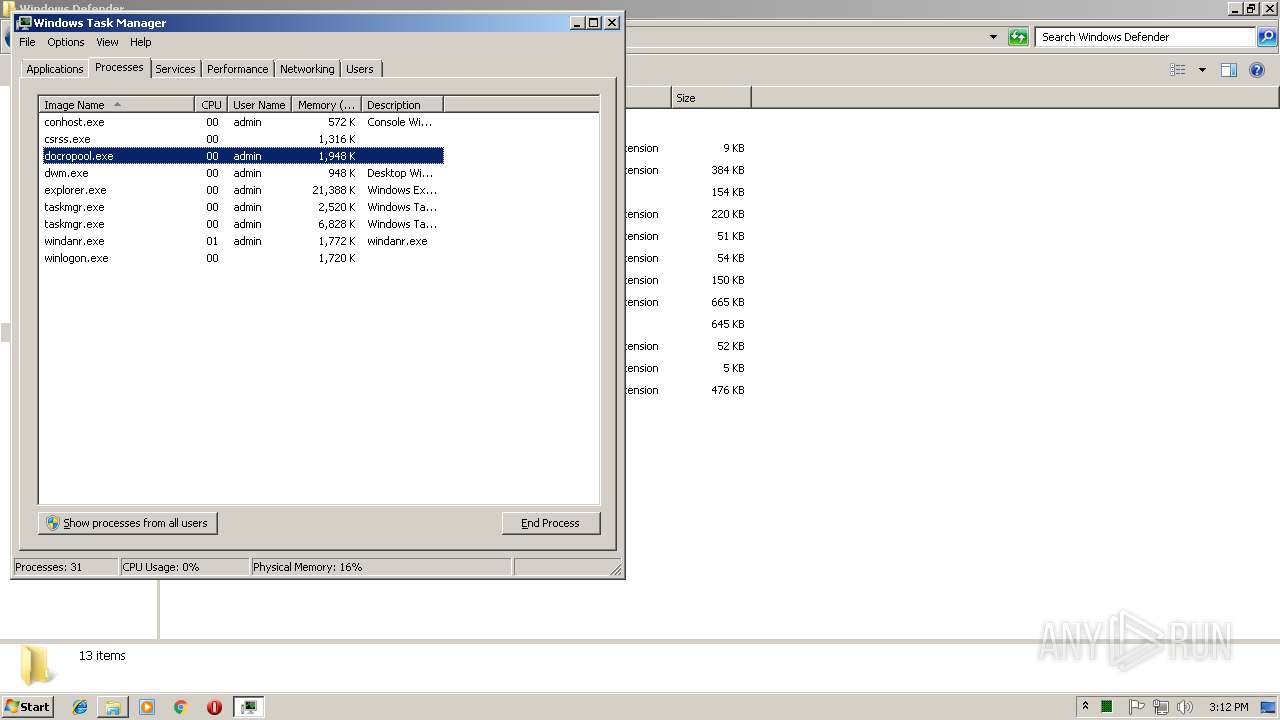
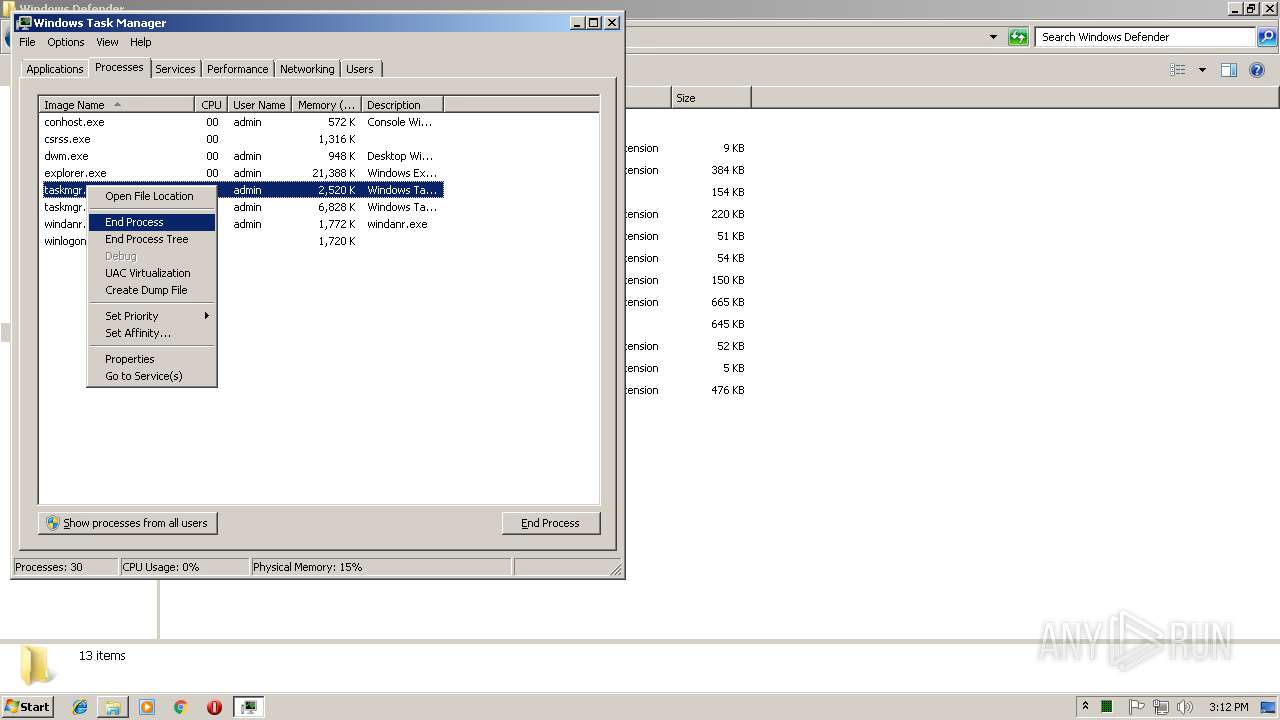
MALICIOUS
Changes the autorun value in the registry
- docropool.exe (PID: 3192)
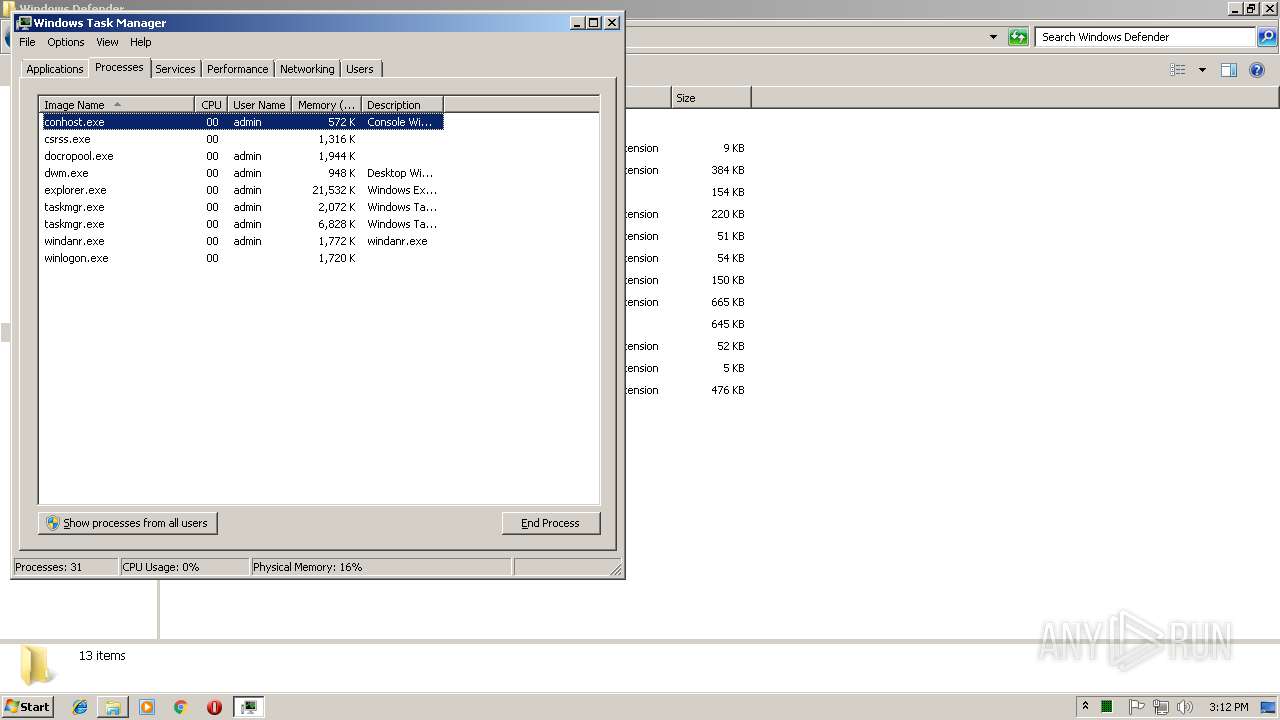
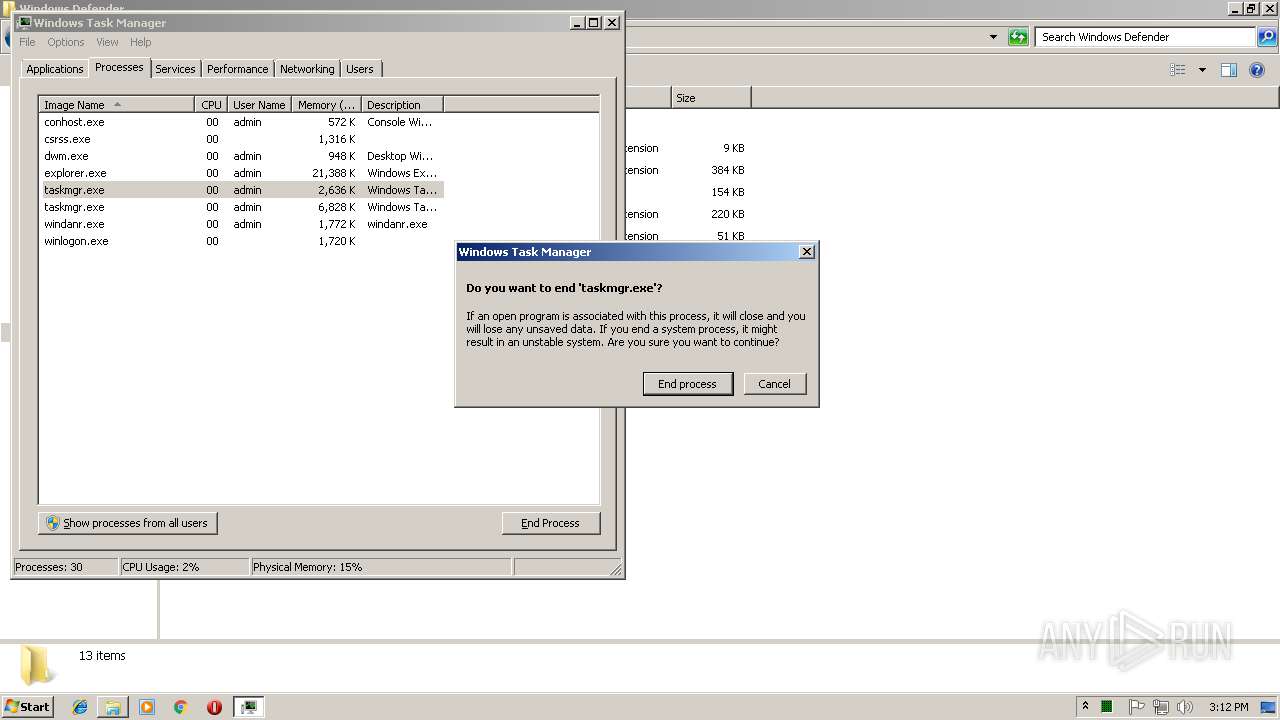
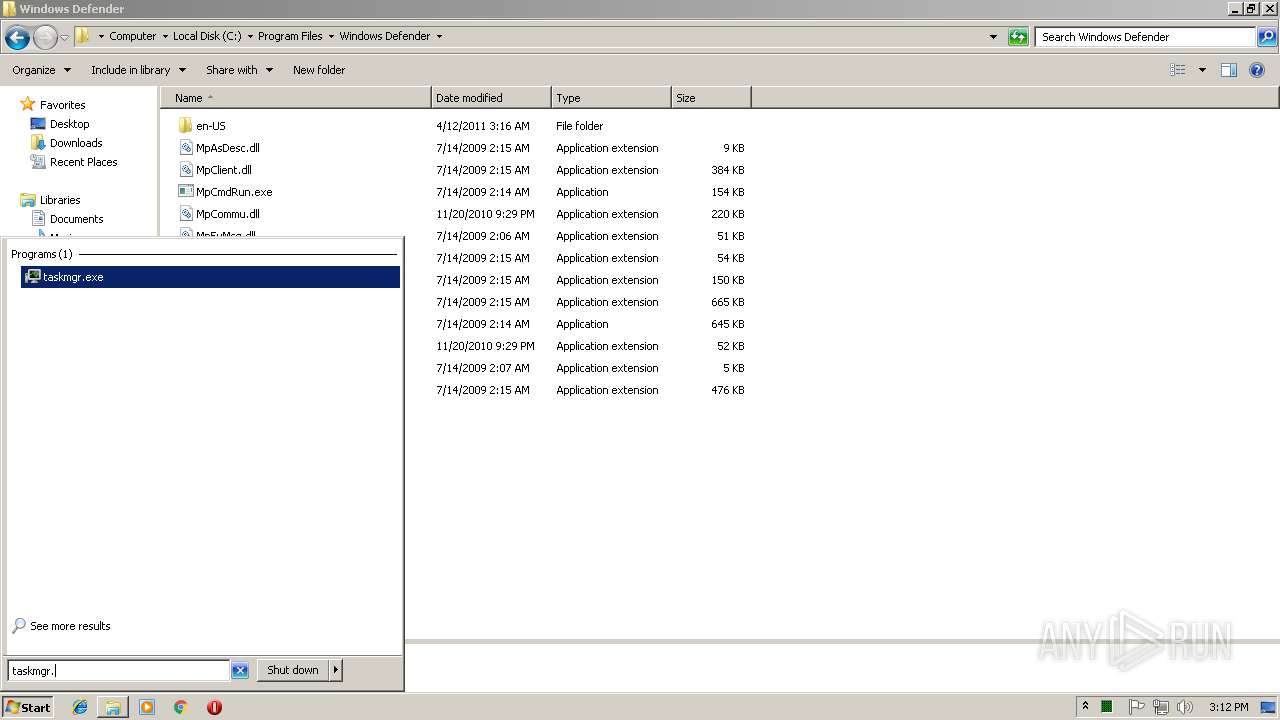
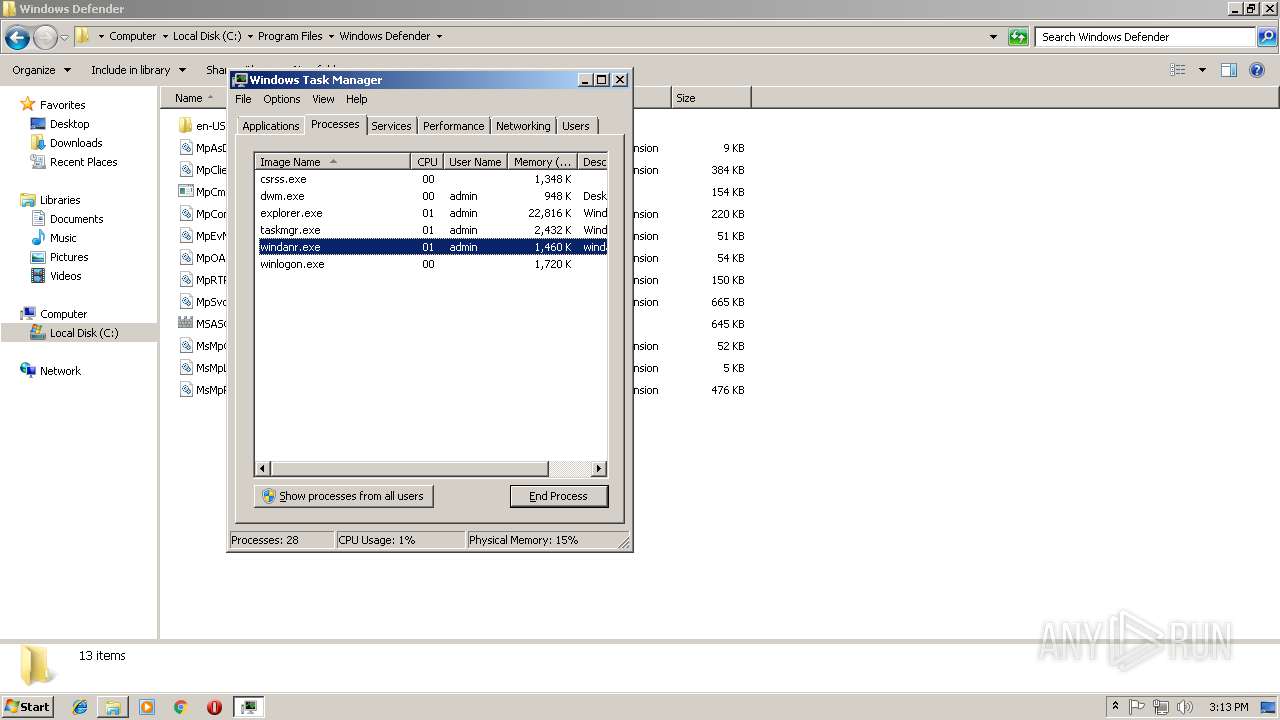
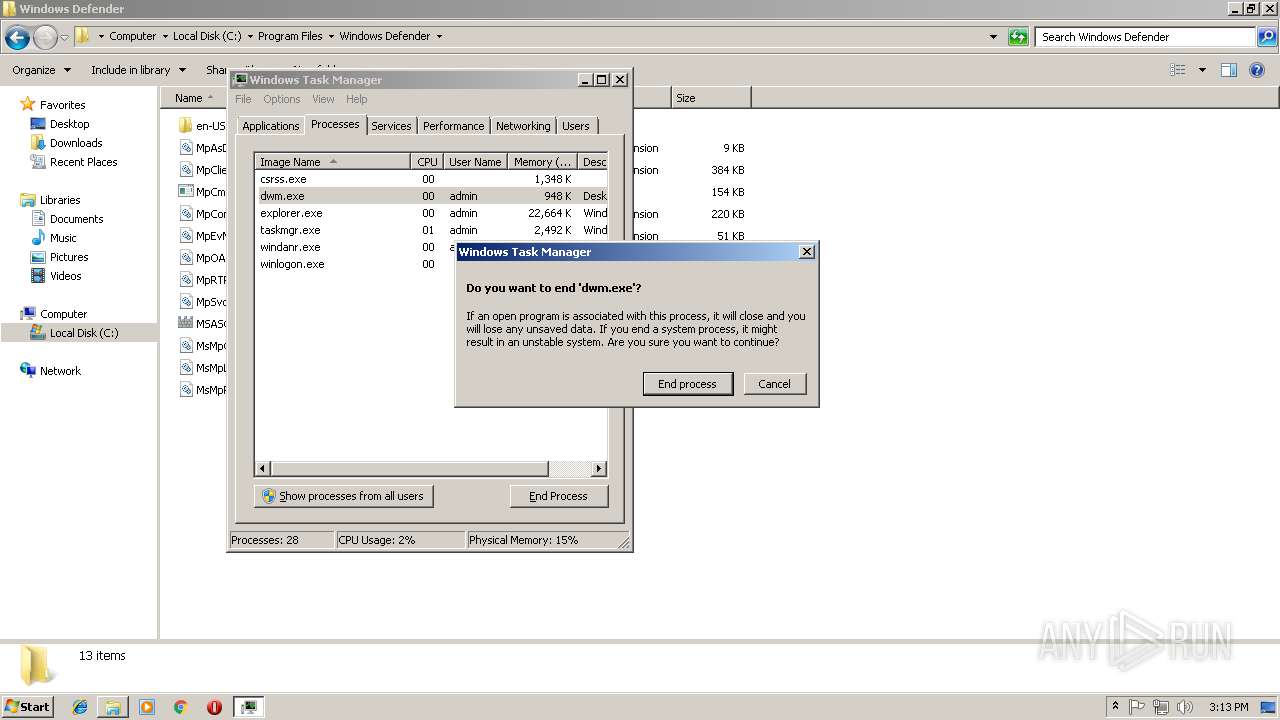
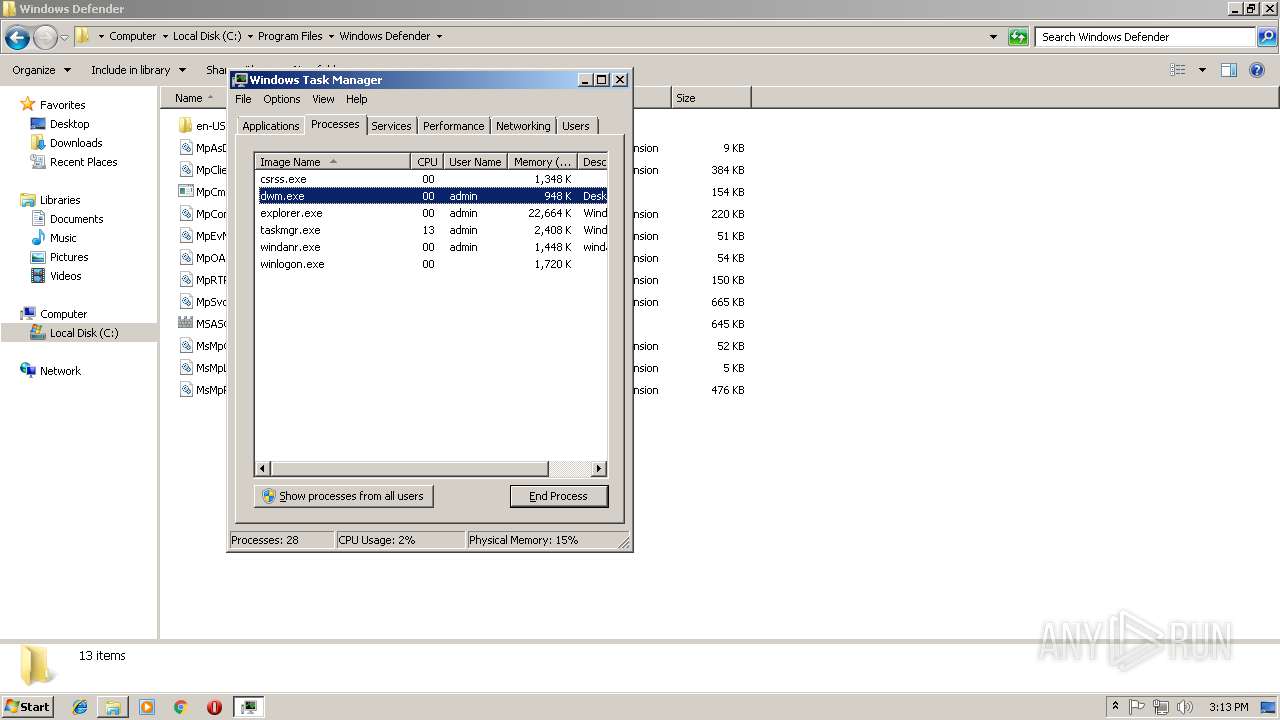
Application was dropped or rewritten from another process
- taskmgr.exe (PID: 3652)
- wimnat.exe (PID: 3072)
MINER was detected
- docropool.exe (PID: 3192)
- taskmgr.exe (PID: 3652)
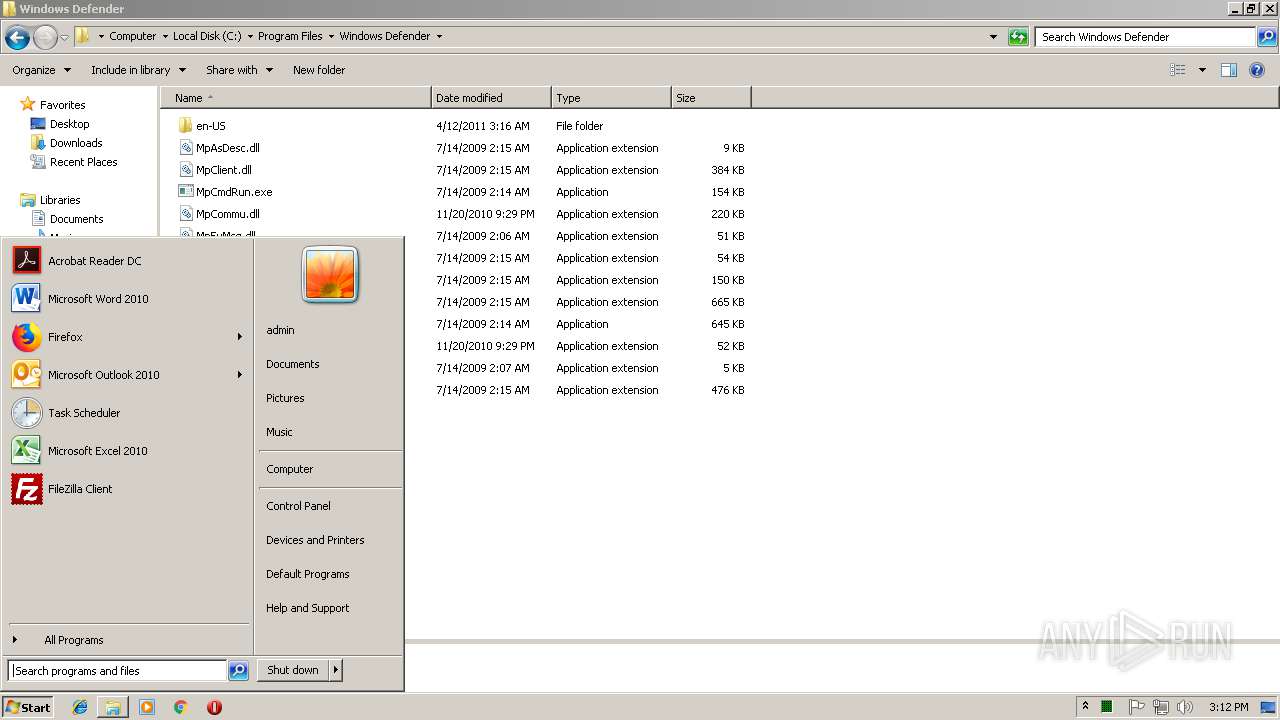
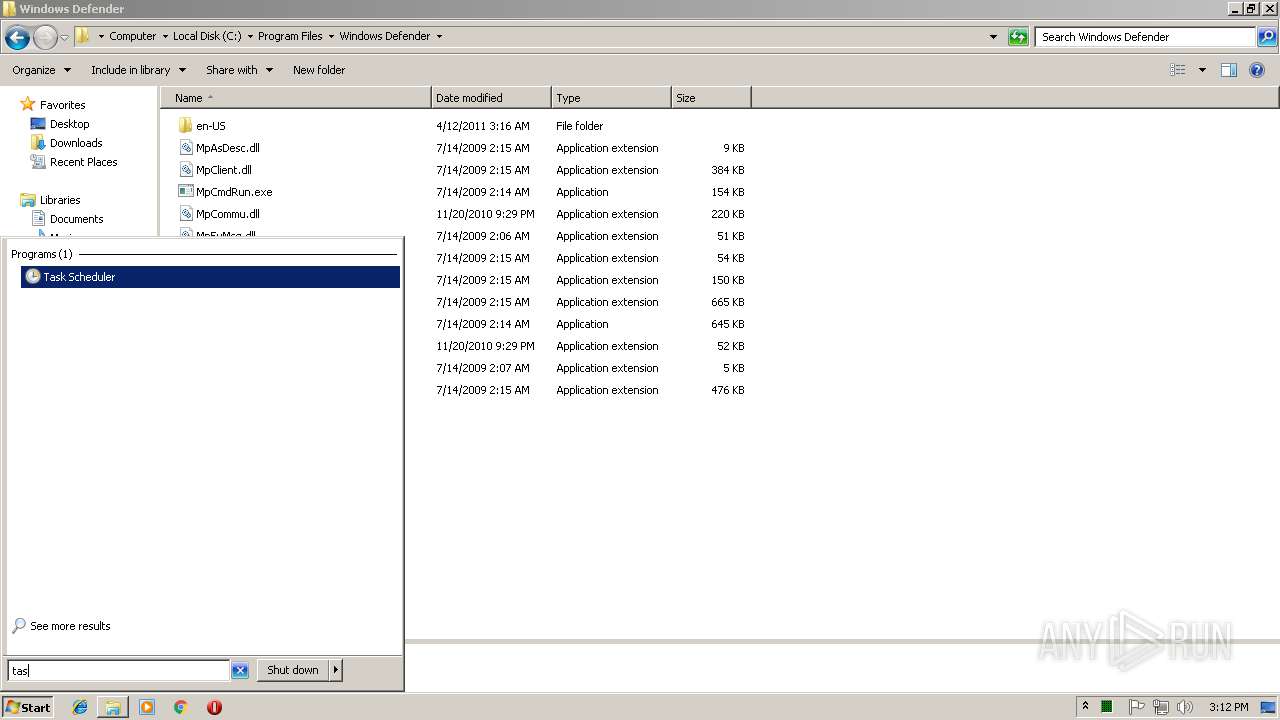
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 3628)
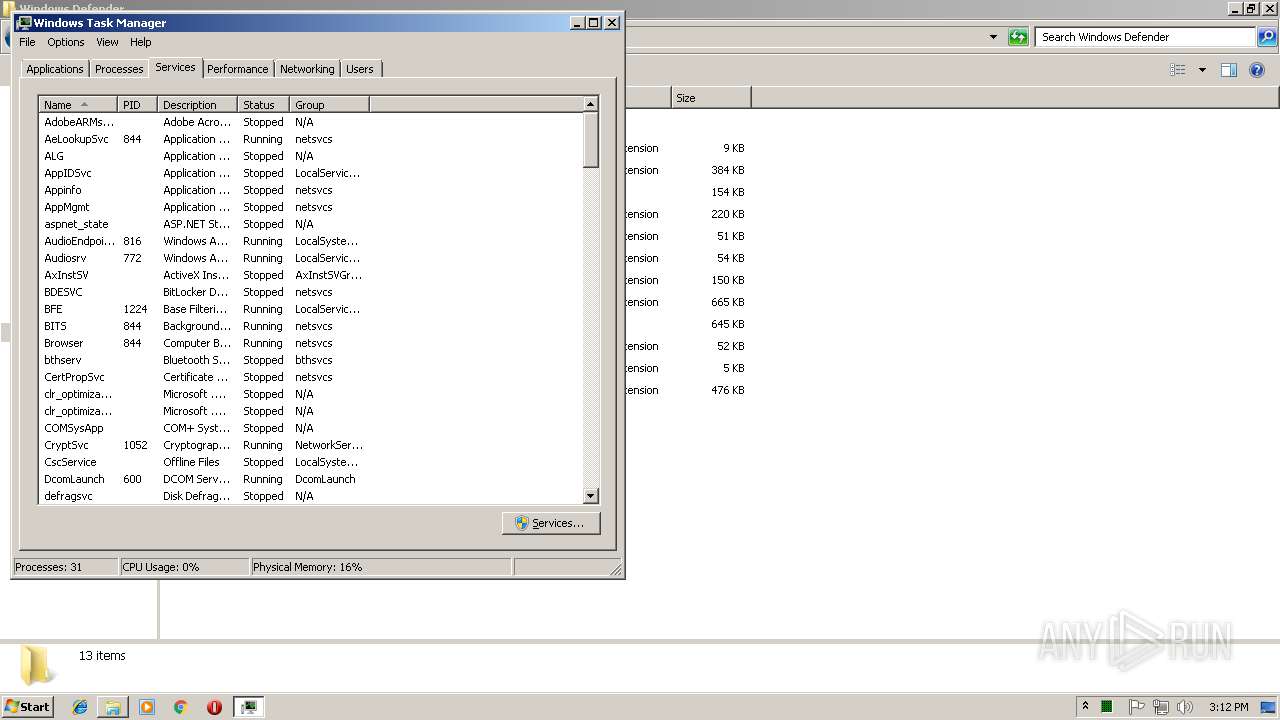
Starts NET.EXE for service management
- cmd.exe (PID: 3768)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 4032)
- cmd.exe (PID: 952)
- cmd.exe (PID: 2728)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 952)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 4084)
- schtasks.exe (PID: 3908)
- schtasks.exe (PID: 2864)
Connects to CnC server
- taskmgr.exe (PID: 3652)
Changes settings of System certificates
- docropool.exe (PID: 3192)
SUSPICIOUS
Connects to unusual port
- docropool.exe (PID: 3192)
- taskmgr.exe (PID: 3652)
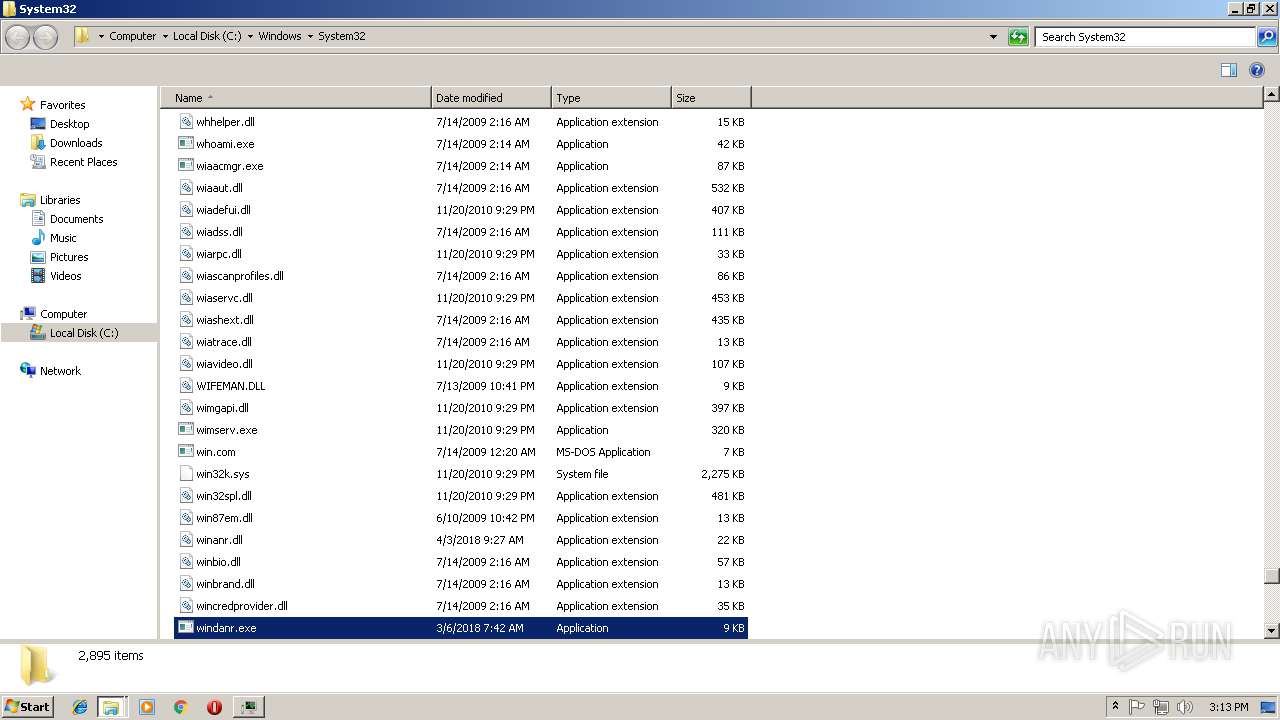
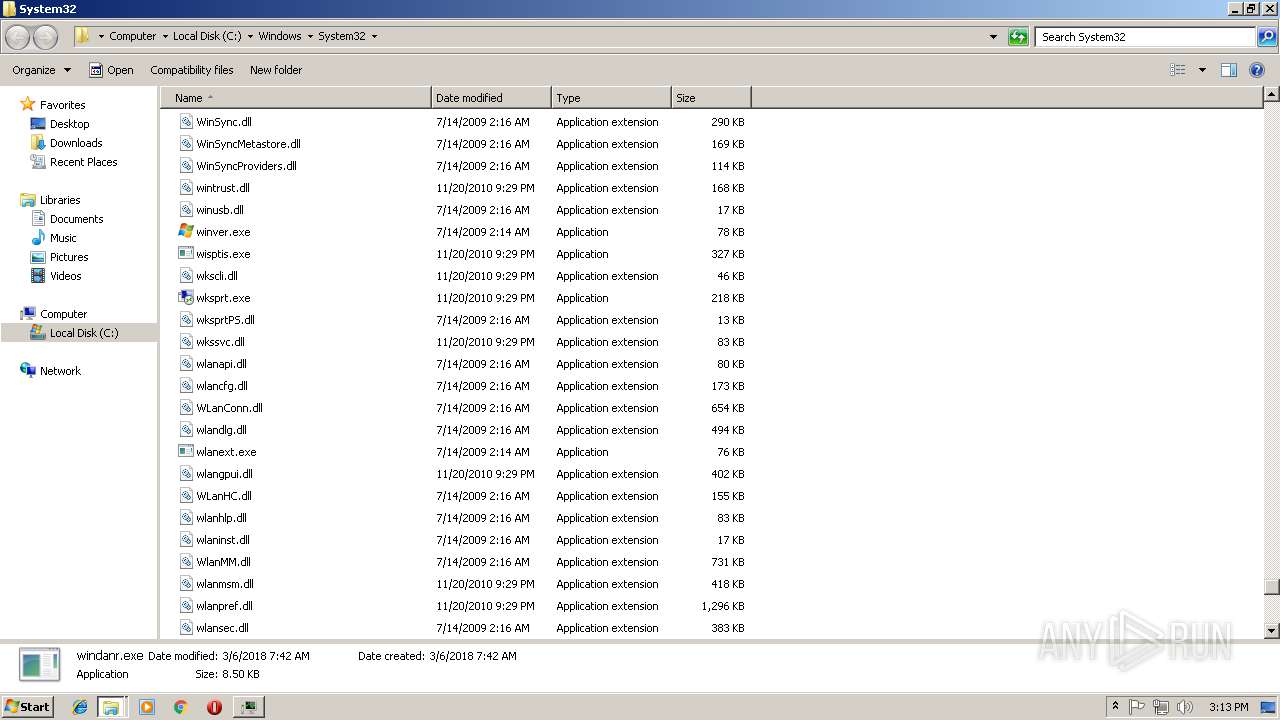
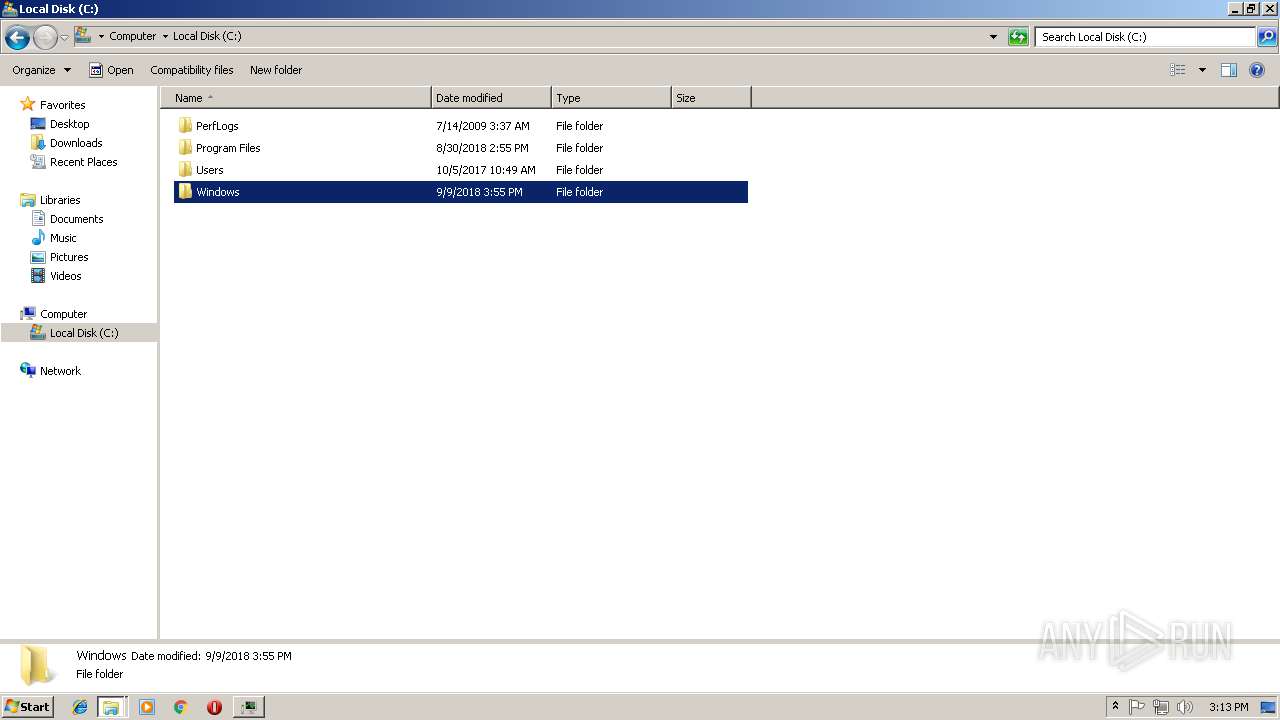
Executable content was dropped or overwritten
- docropool.exe (PID: 3192)
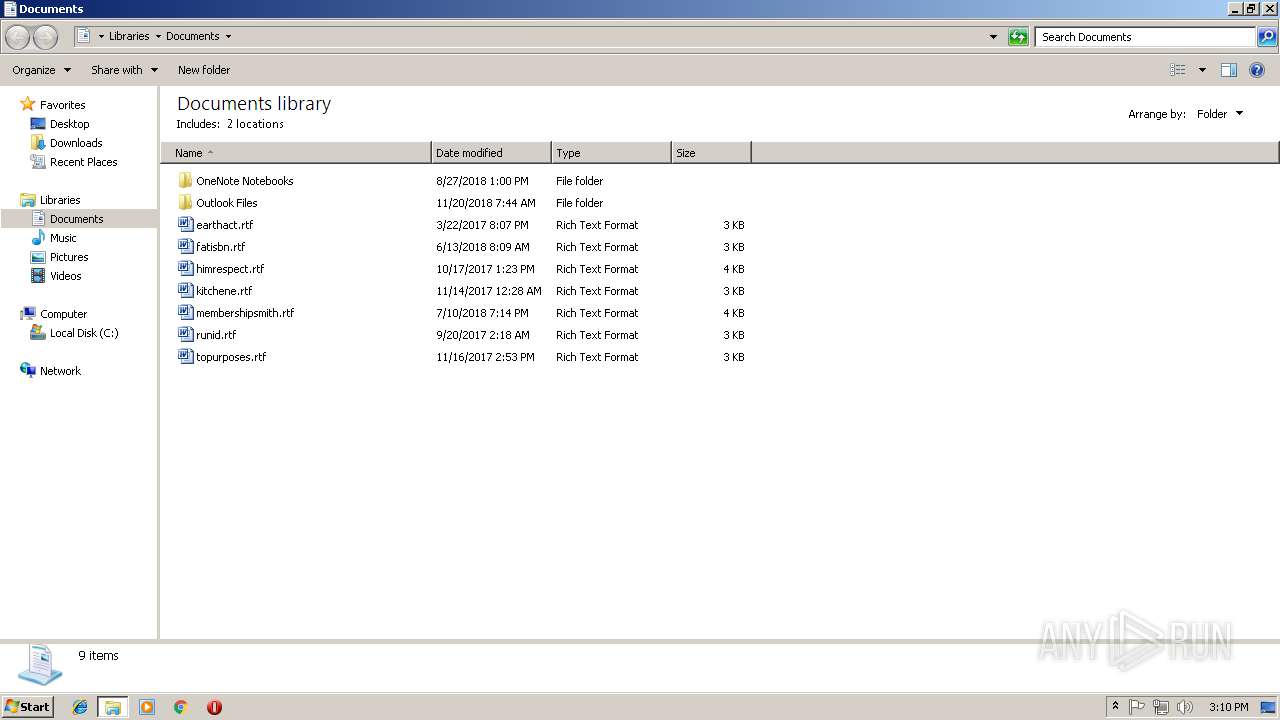
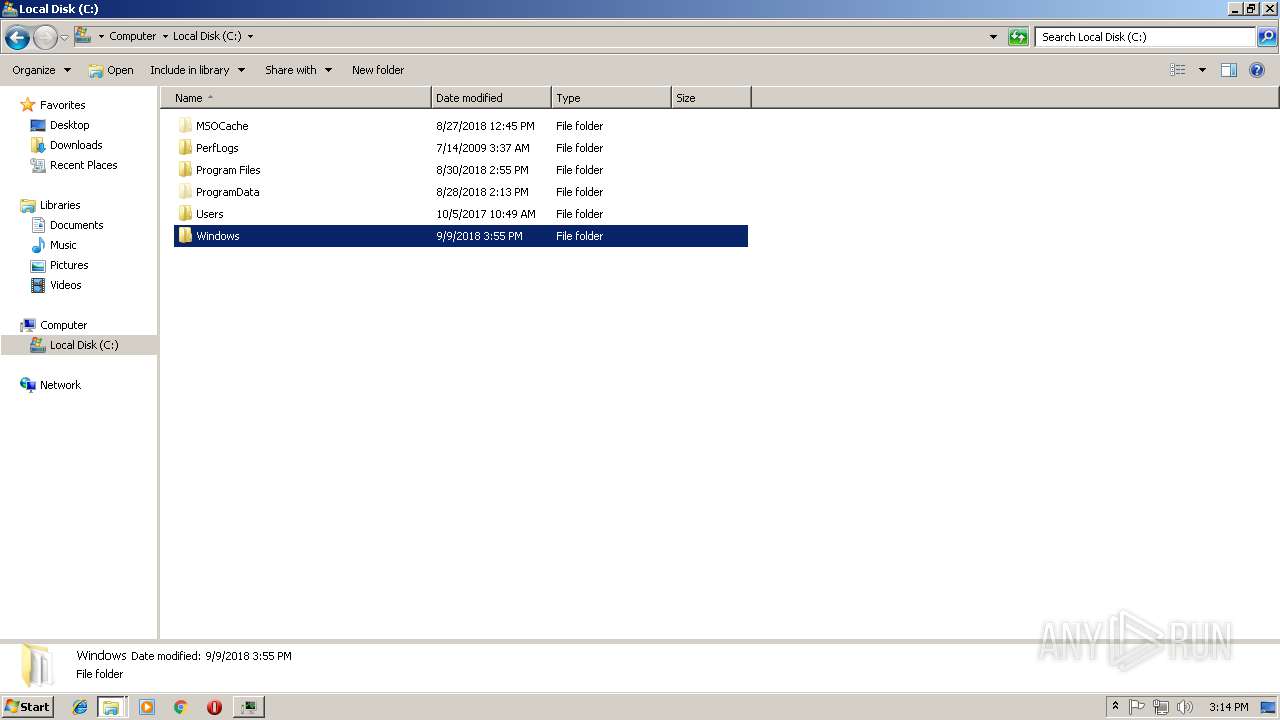
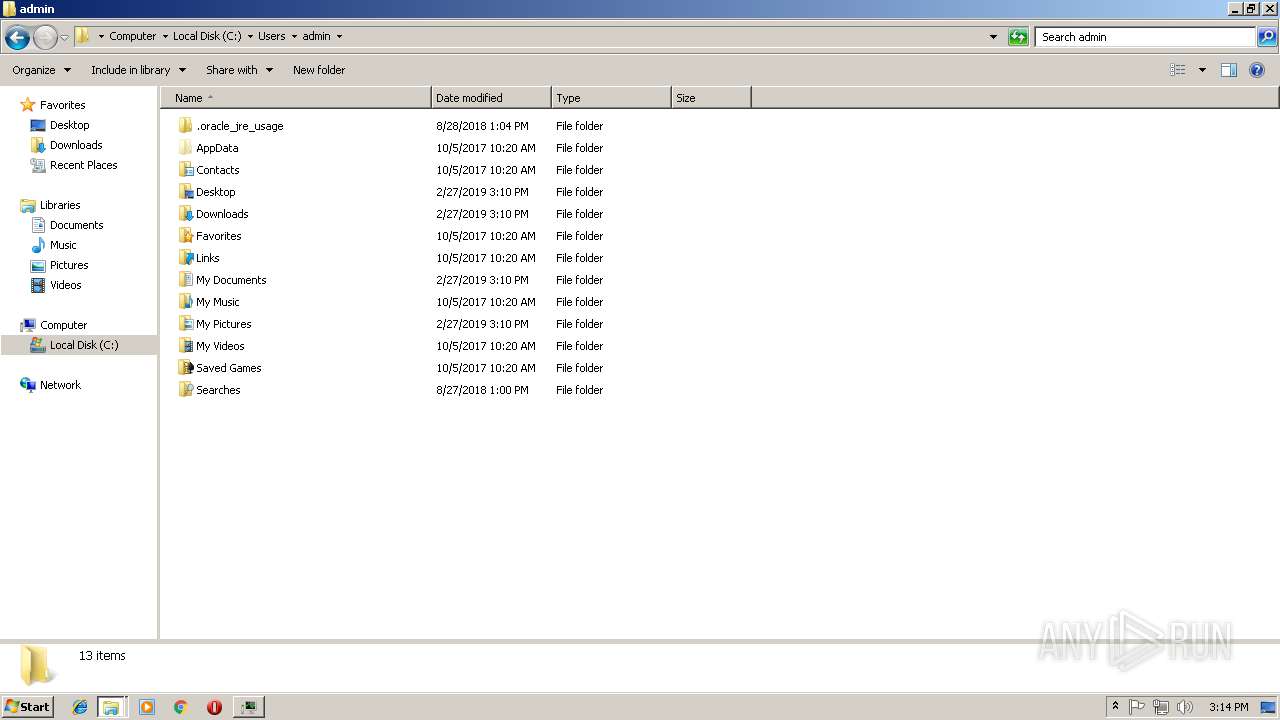
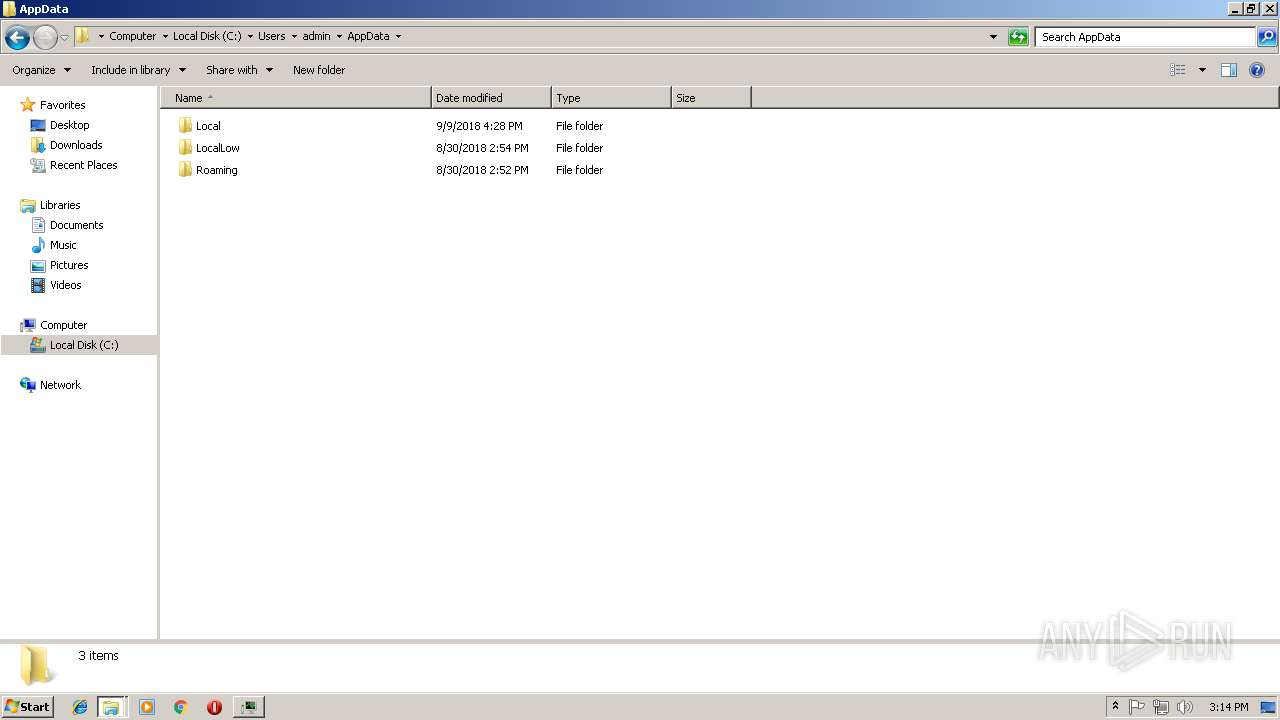
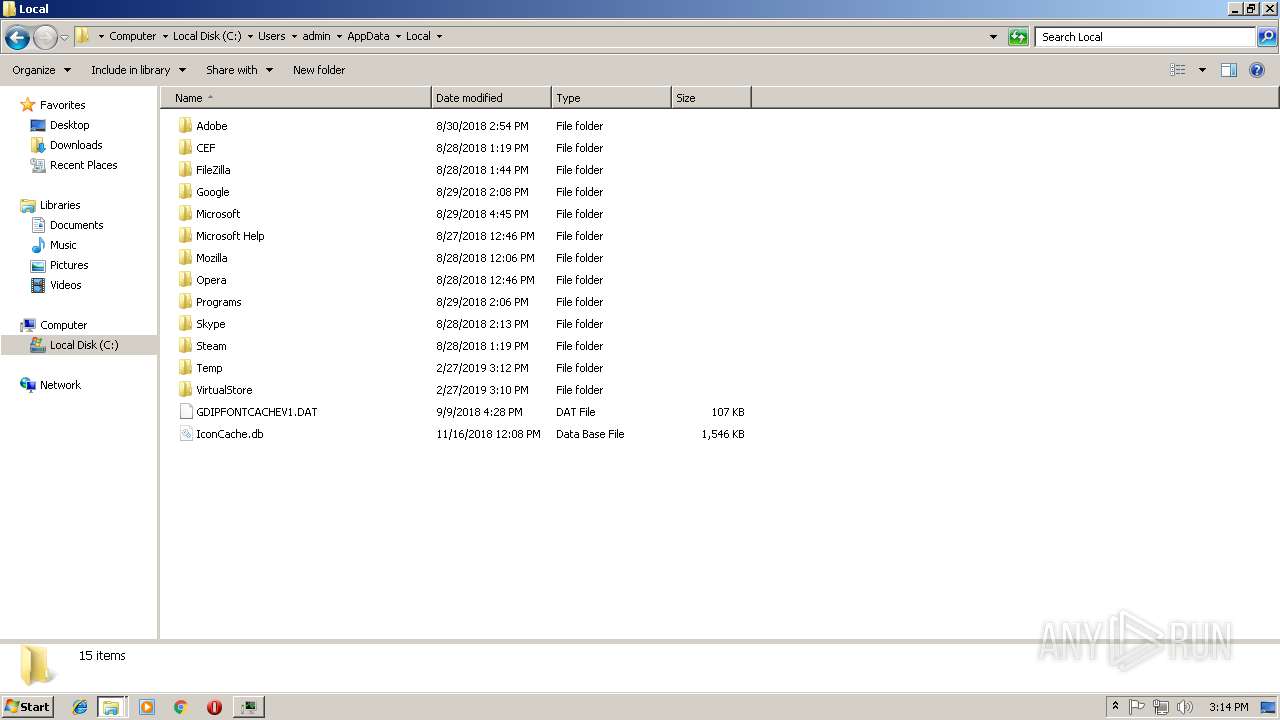
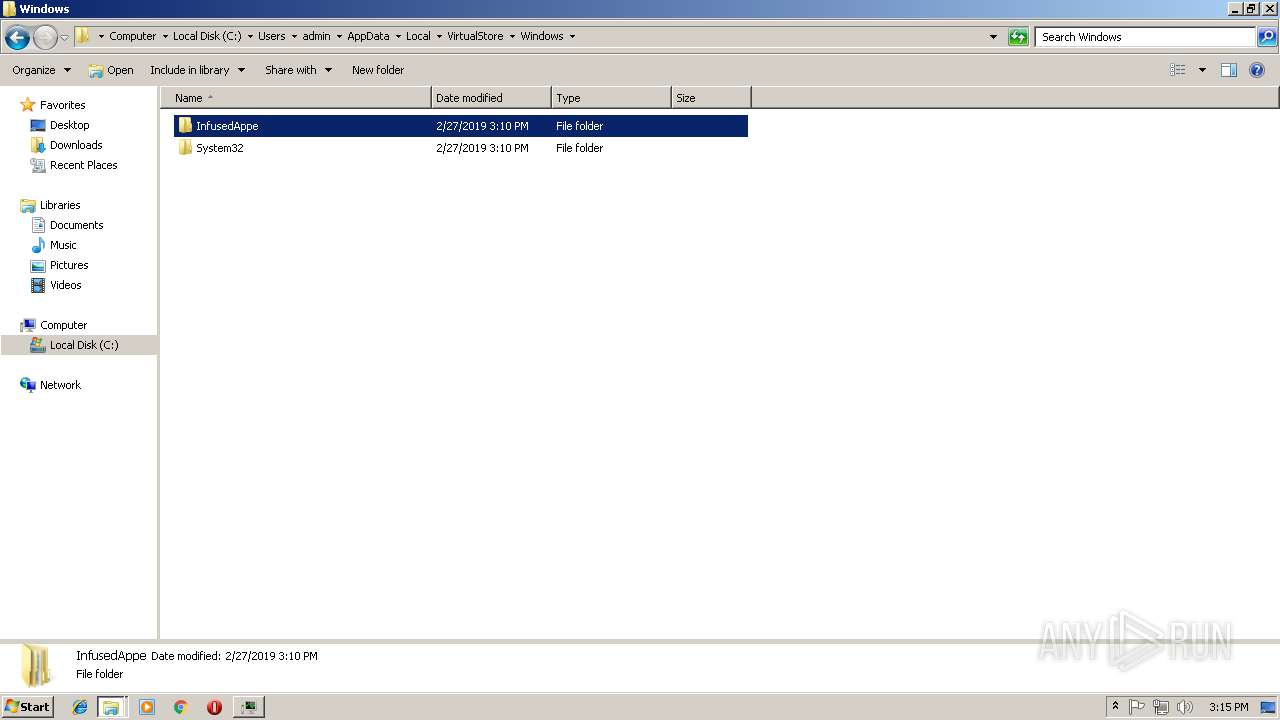
Creates files in the user directory
- docropool.exe (PID: 3192)
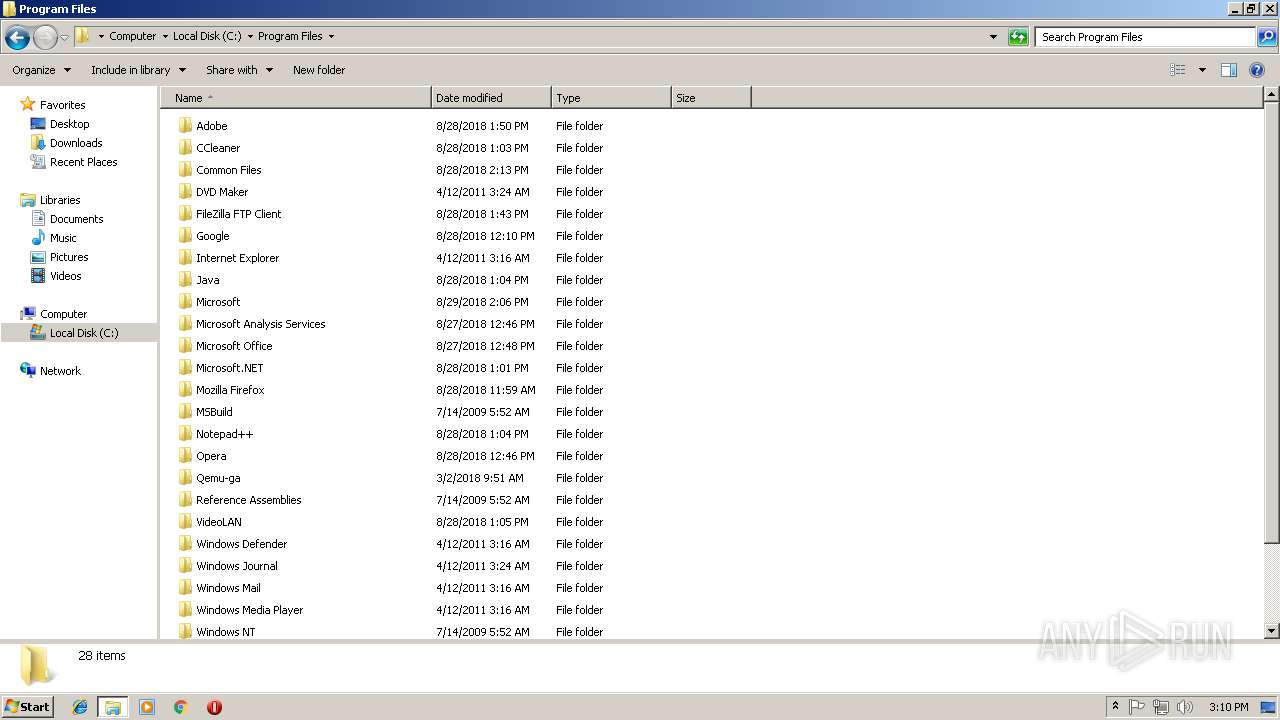
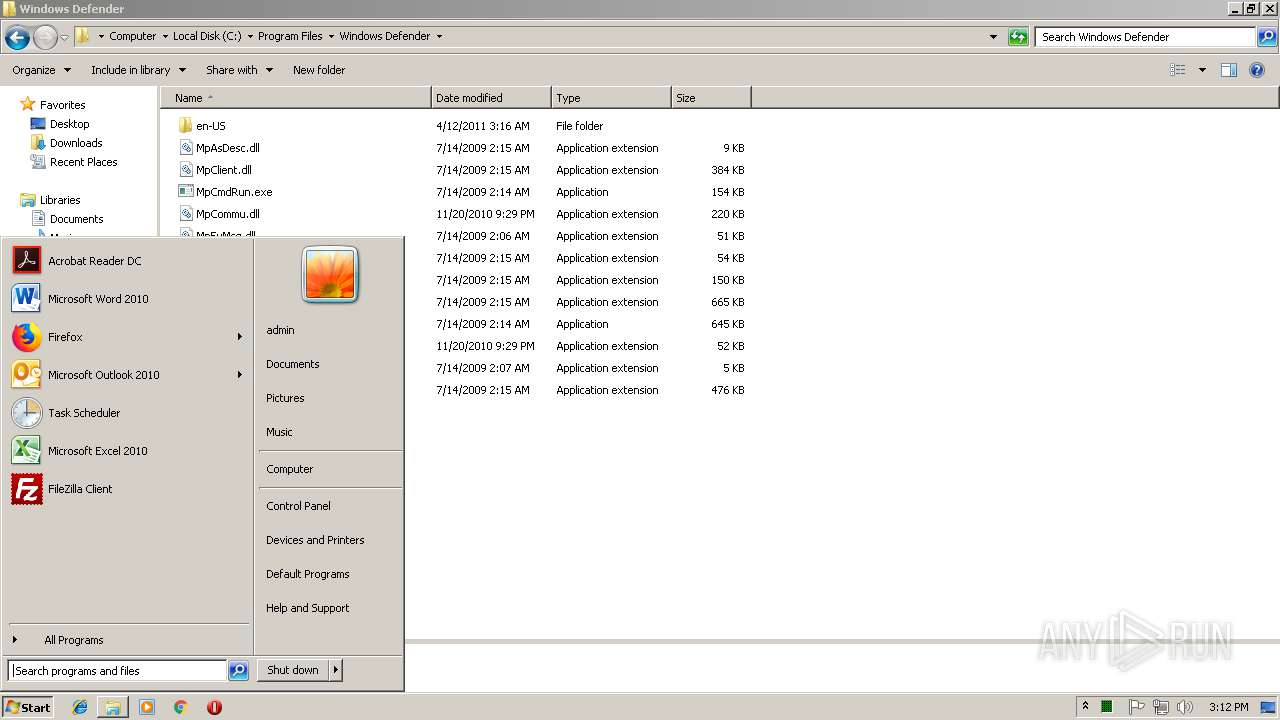
- notepad++.exe (PID: 576)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3544)
- docropool.exe (PID: 3192)
- cmd.exe (PID: 3628)
Application launched itself
- cmd.exe (PID: 3544)
- cmd.exe (PID: 3628)
Starts SC.EXE for service management
- cmd.exe (PID: 2392)
- cmd.exe (PID: 2484)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 2824)
- cmd.exe (PID: 2588)
Adds / modifies Windows certificates
- docropool.exe (PID: 3192)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:13 17:56:07+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 3768320 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 1163264 |
| EntryPoint: | 0x4b4380 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | OLED DocFile Propertray Page |
| FileVersion: | 6.1.7600.16385 |
| InternalName: | docropool.exe |
| LegalCopyright: | Microsoft Corporation. All rights reserved. |
| OriginalFileName: | docropool.exe |
| ProductName: | Microsoft Windows Operating System |
| ProductVersion: | 6.1.7600.16385 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jan-2019 16:56:07 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | OLED DocFile Propertray Page |
| FileVersion: | 6.1.7600.16385 |
| InternalName: | docropool.exe |
| LegalCopyright: | Microsoft Corporation. All rights reserved. |
| OriginalFilename: | docropool.exe |
| ProductName: | Microsoft Windows Operating System |
| ProductVersion: | 6.1.7600.16385 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Jan-2019 16:56:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0011C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0011D000 | 0x00398000 | 0x00397600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.8137 |
.rsrc | 0x004B5000 | 0x00001000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11366 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
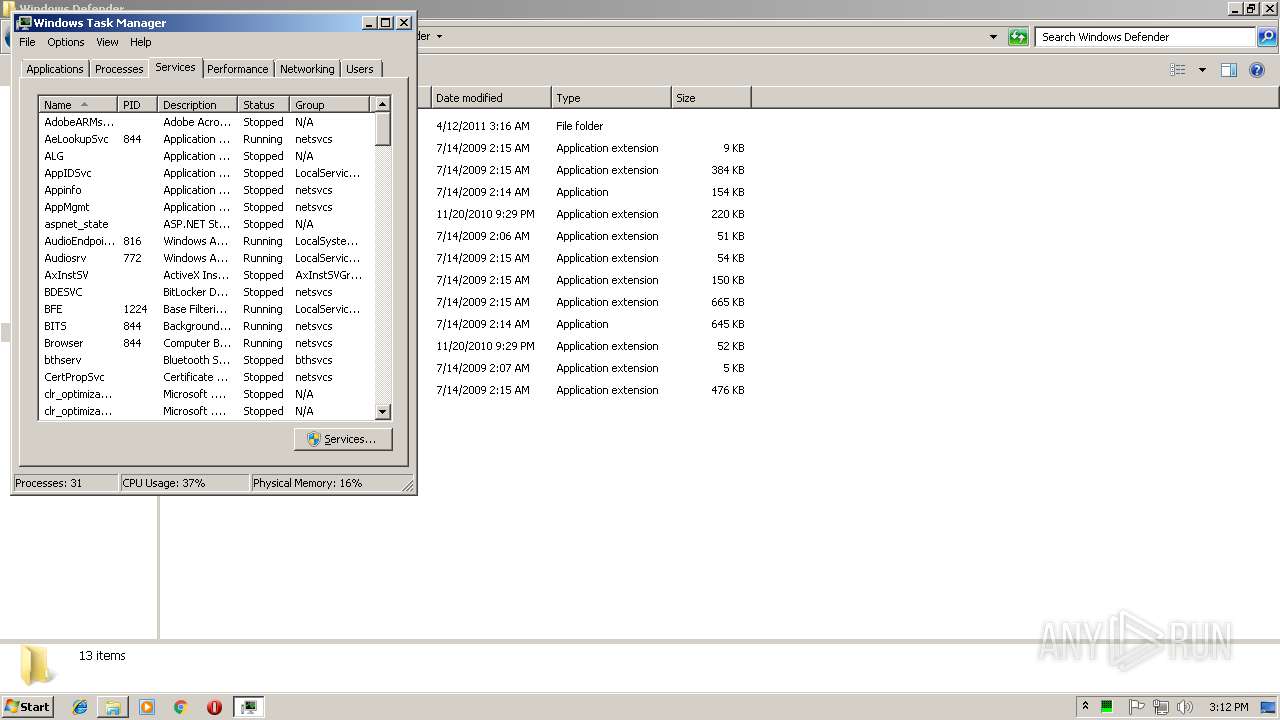
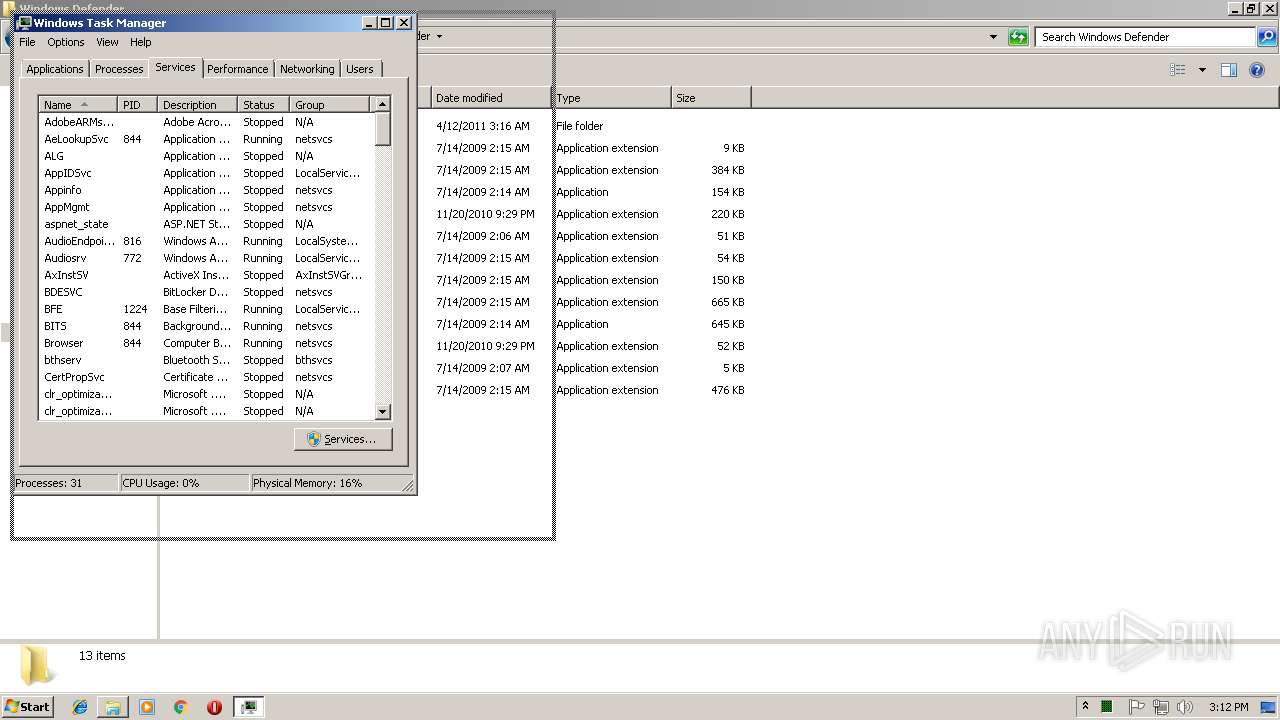
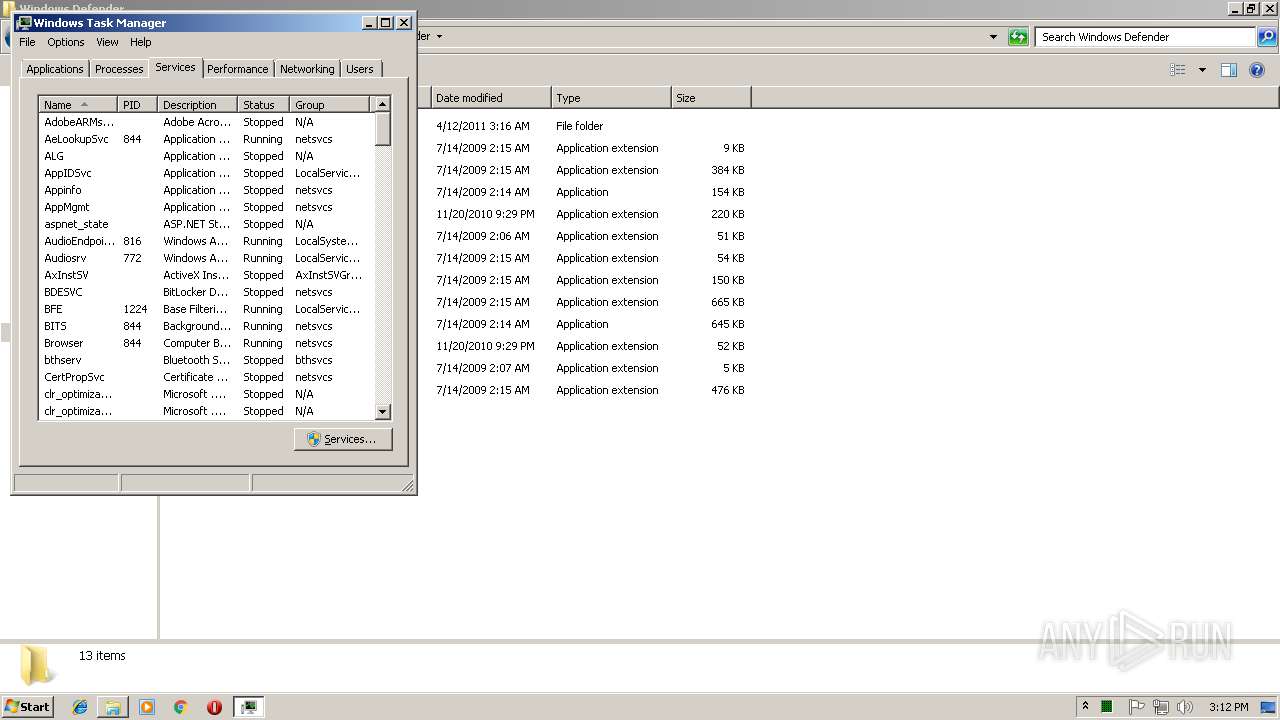
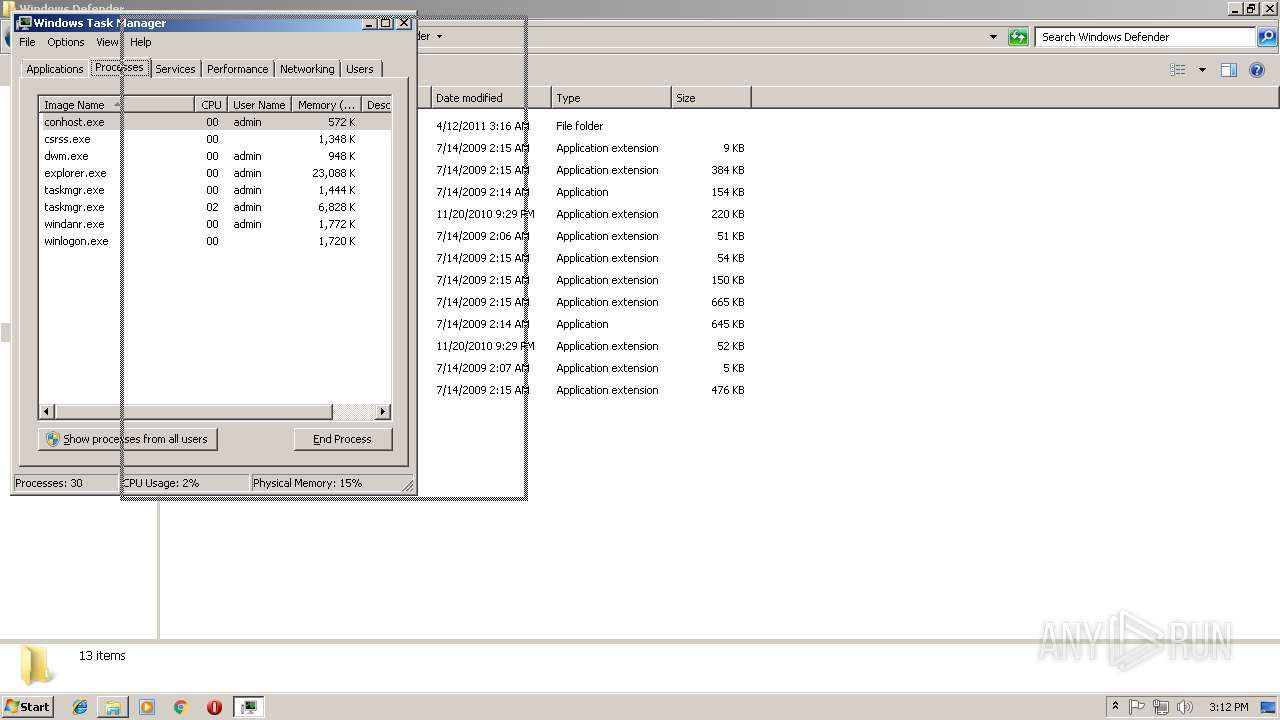
Total processes
100
Monitored processes
44
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
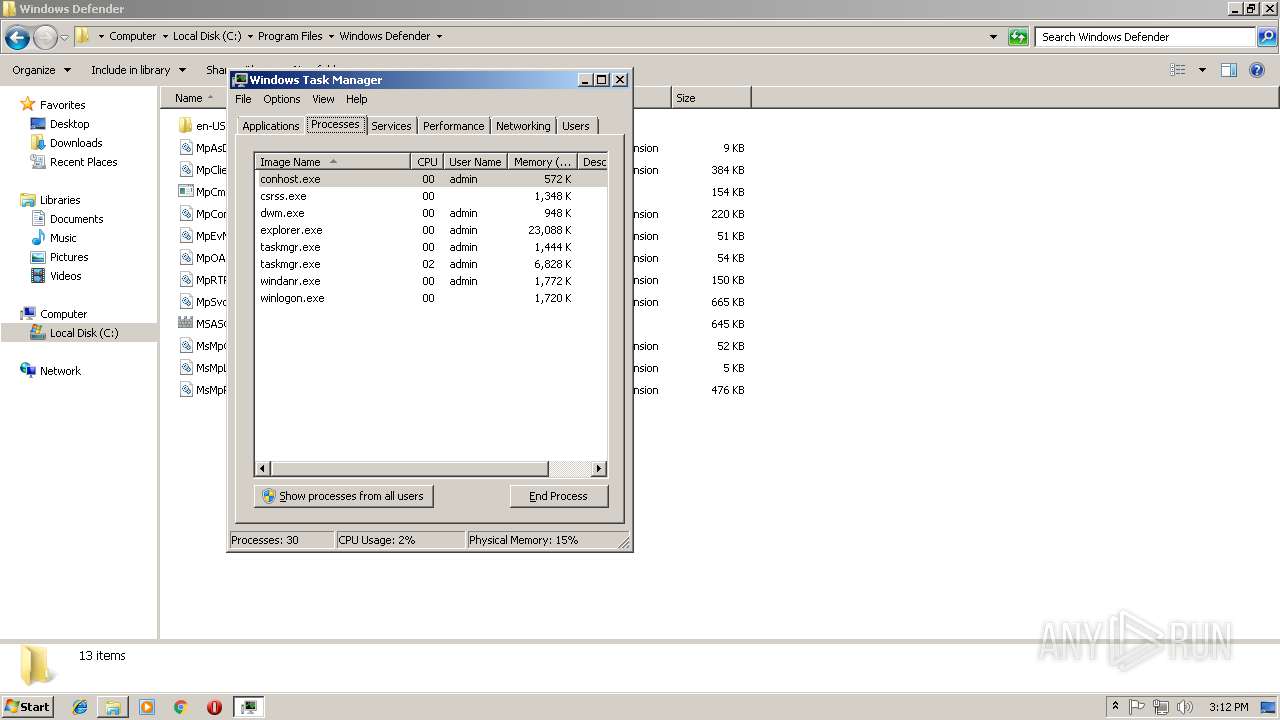
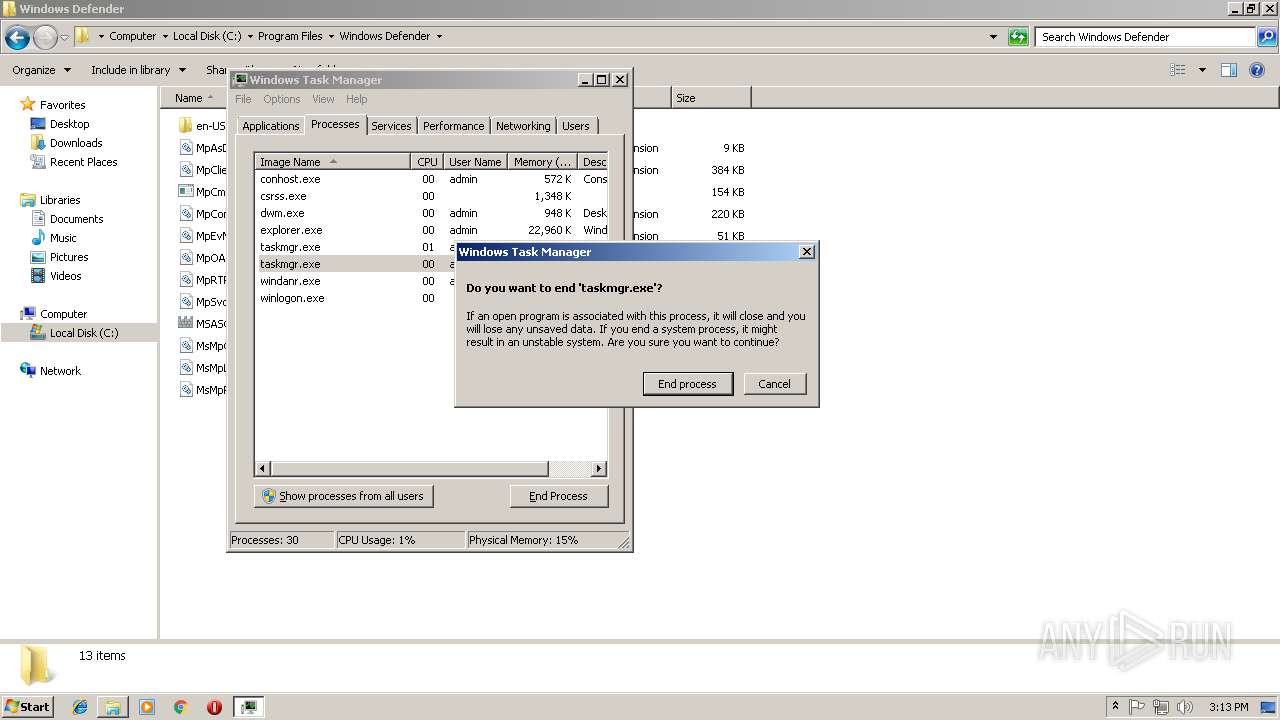
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
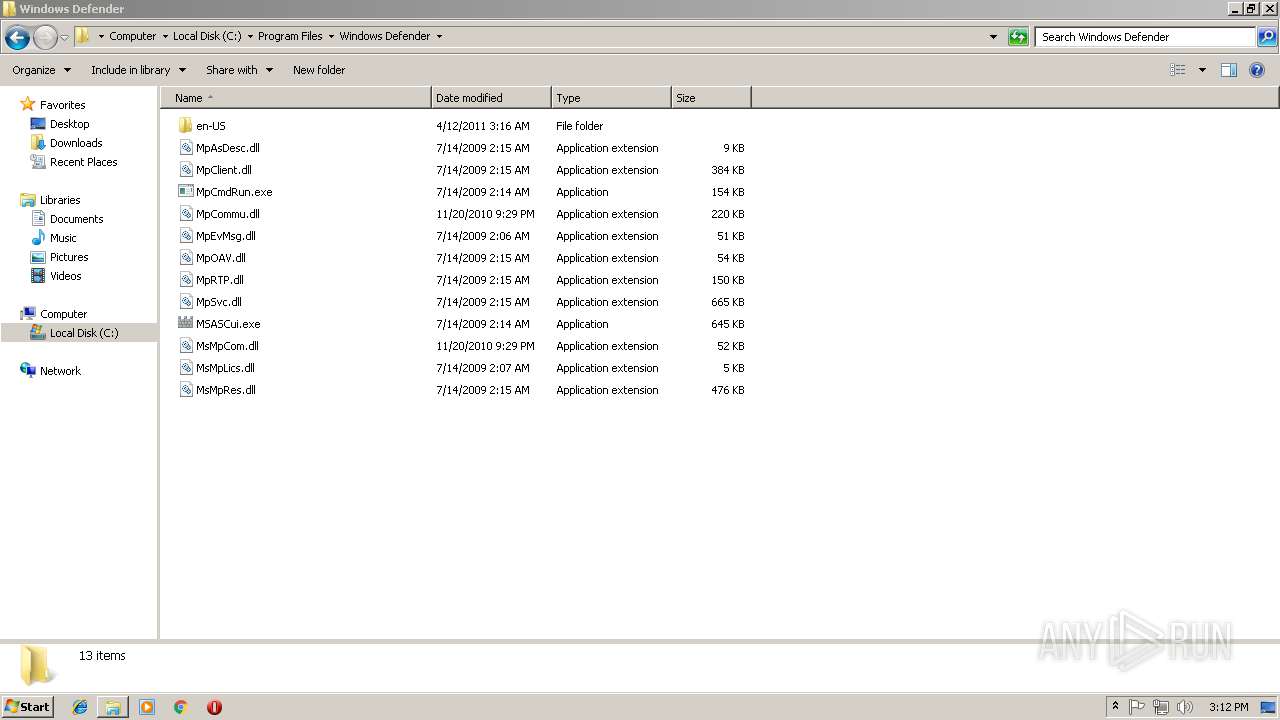
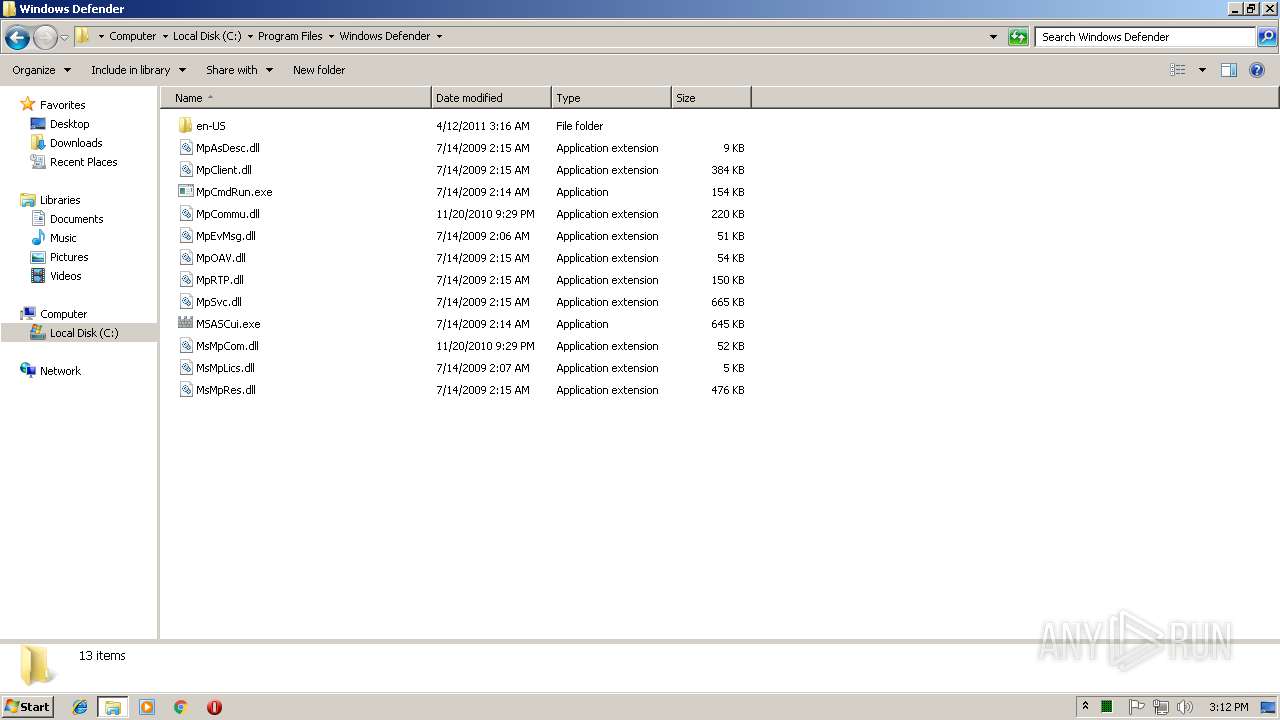
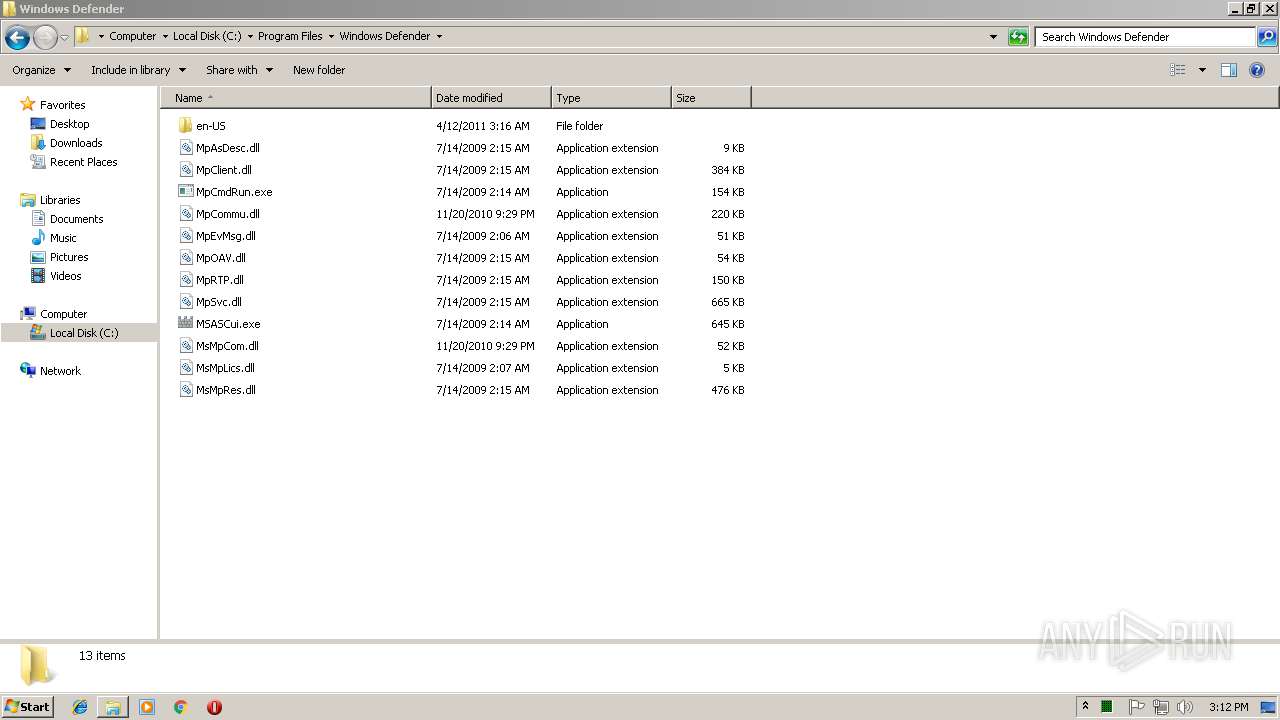
| 252 | sc config WinDefend start= disabled | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
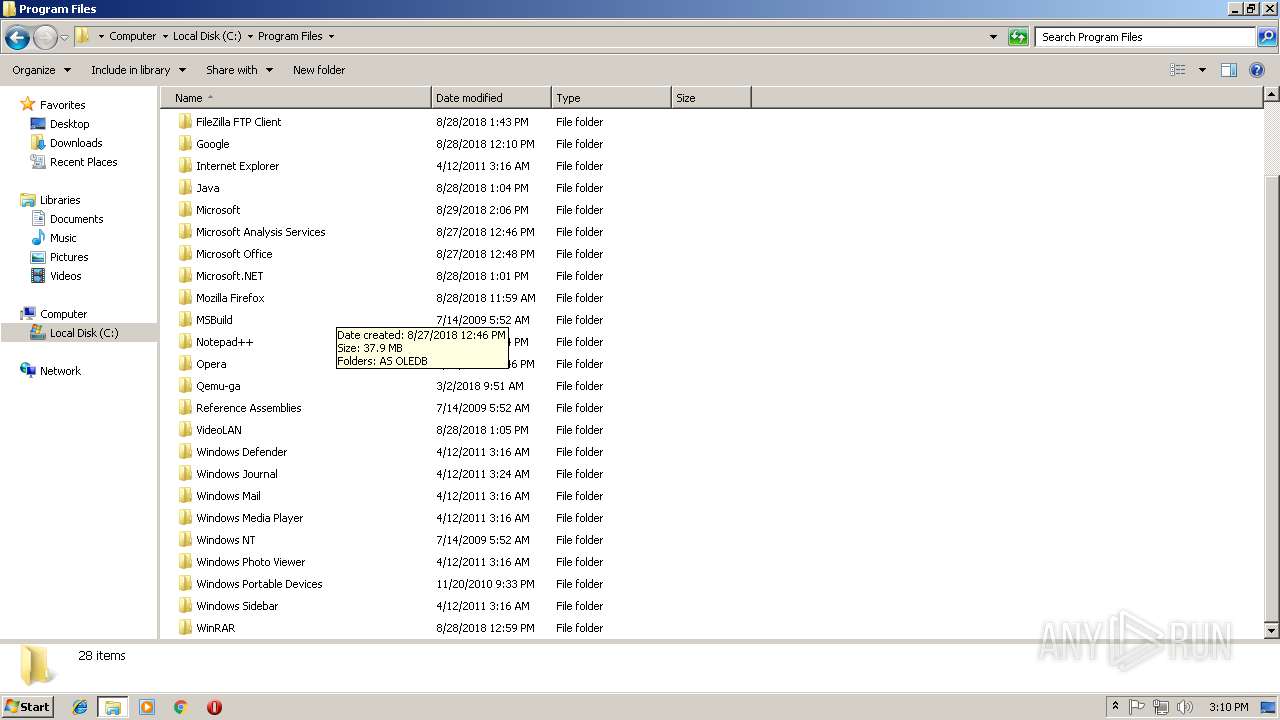
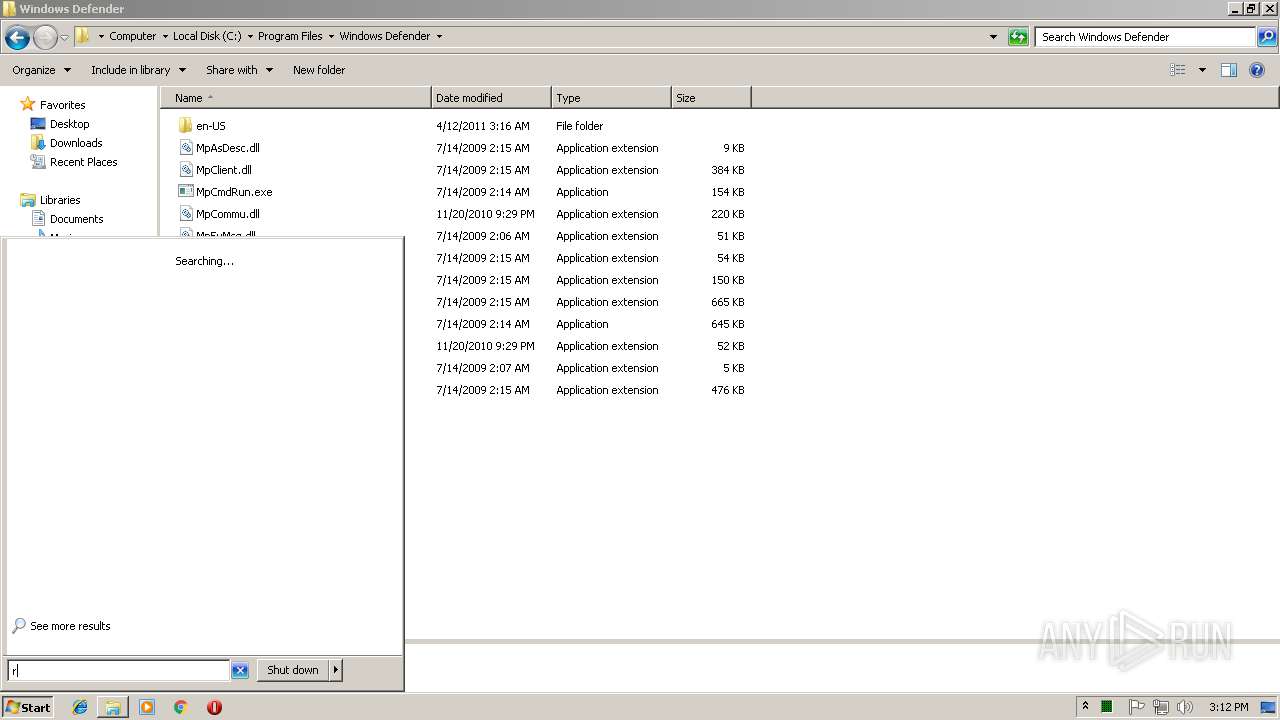
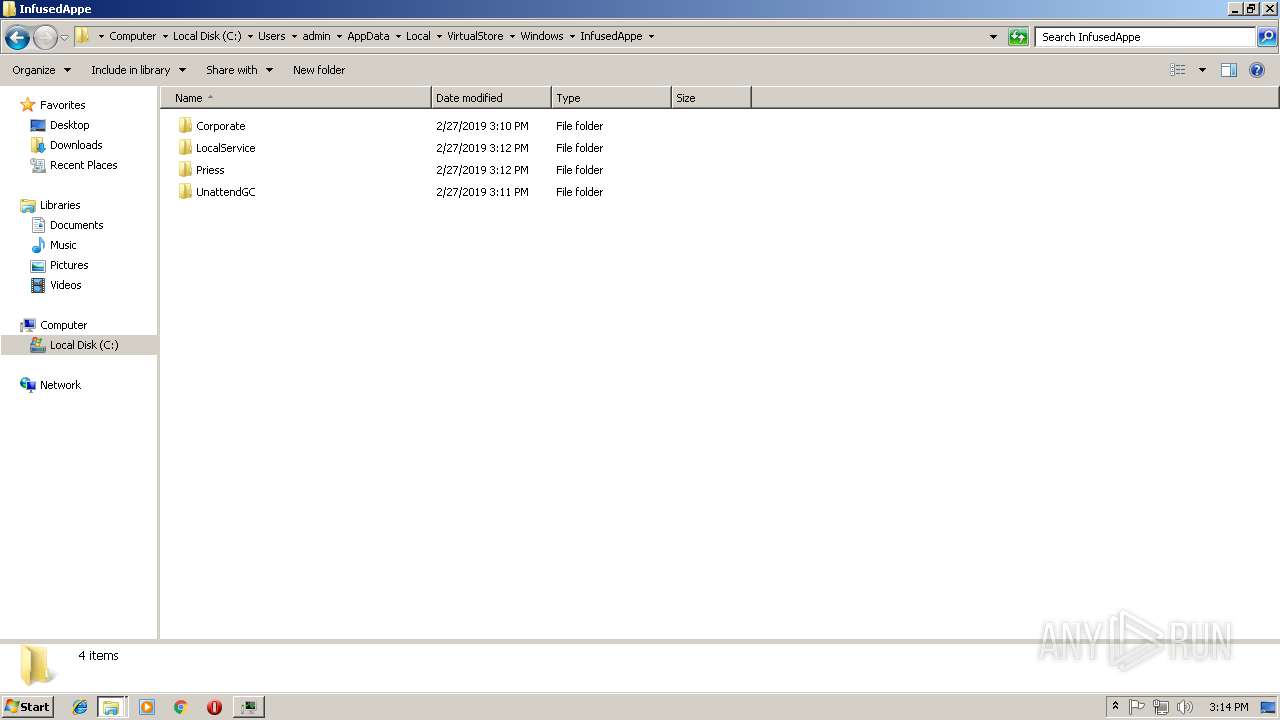
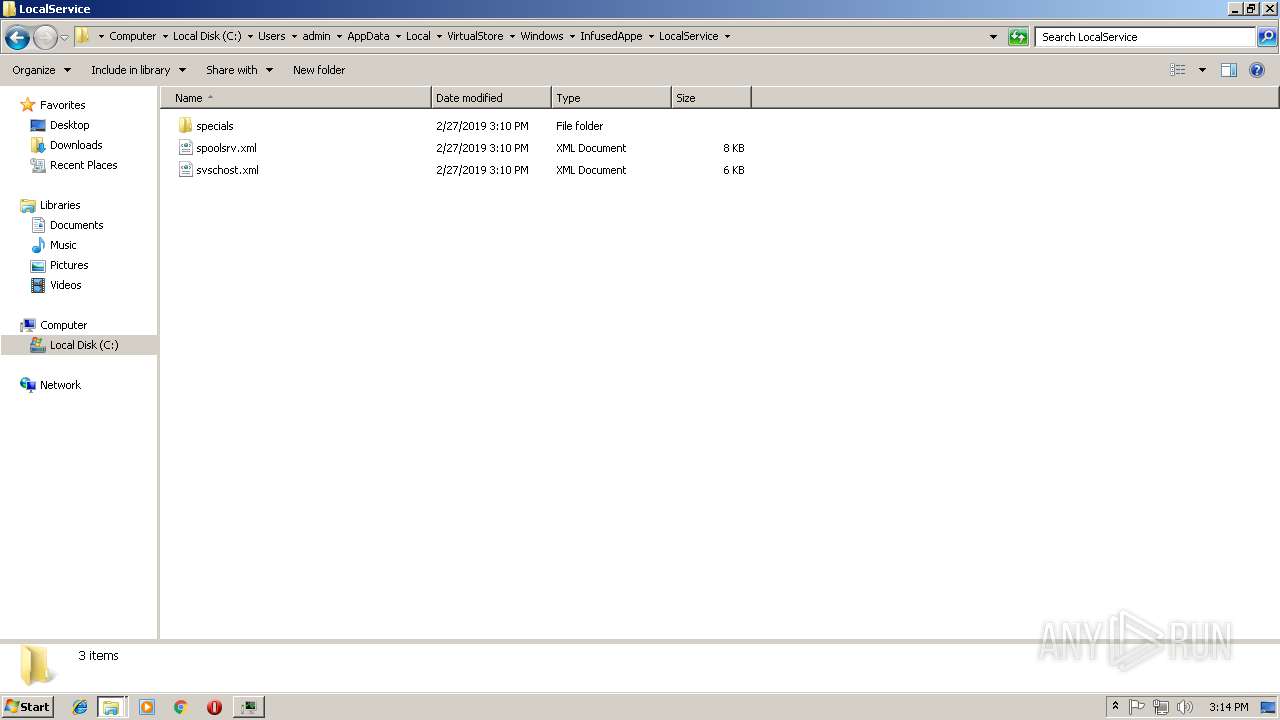
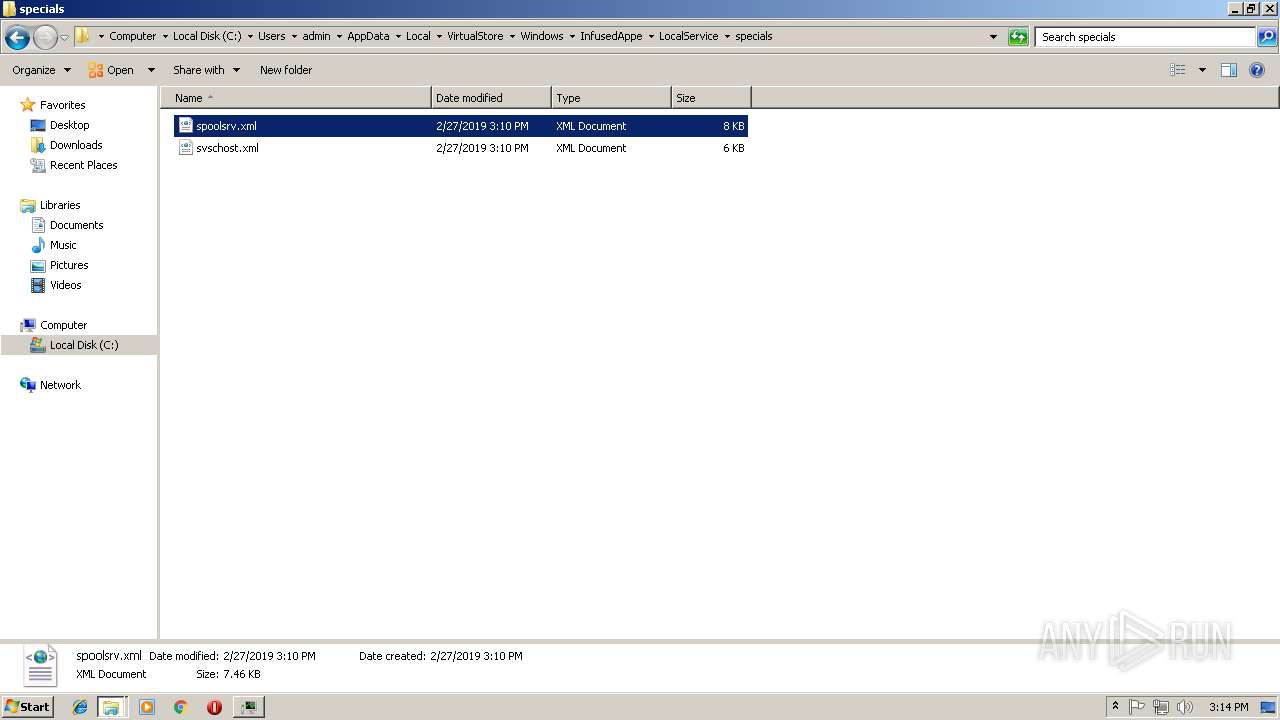
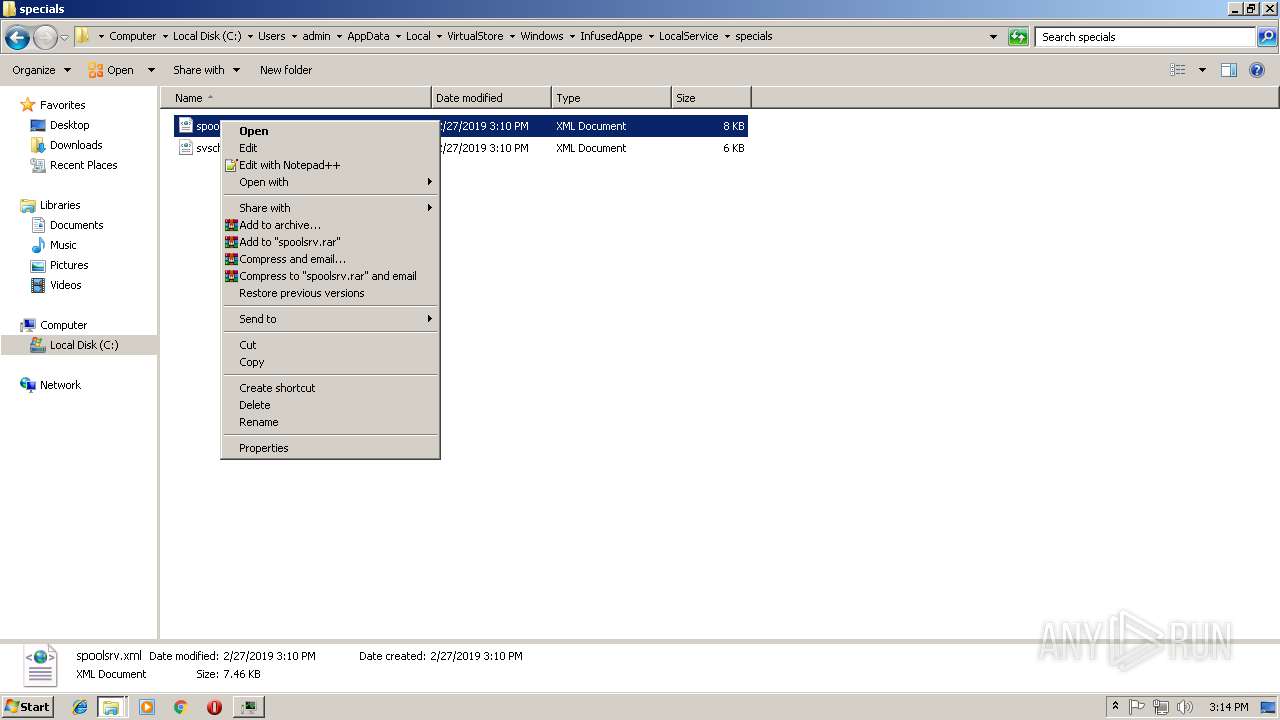
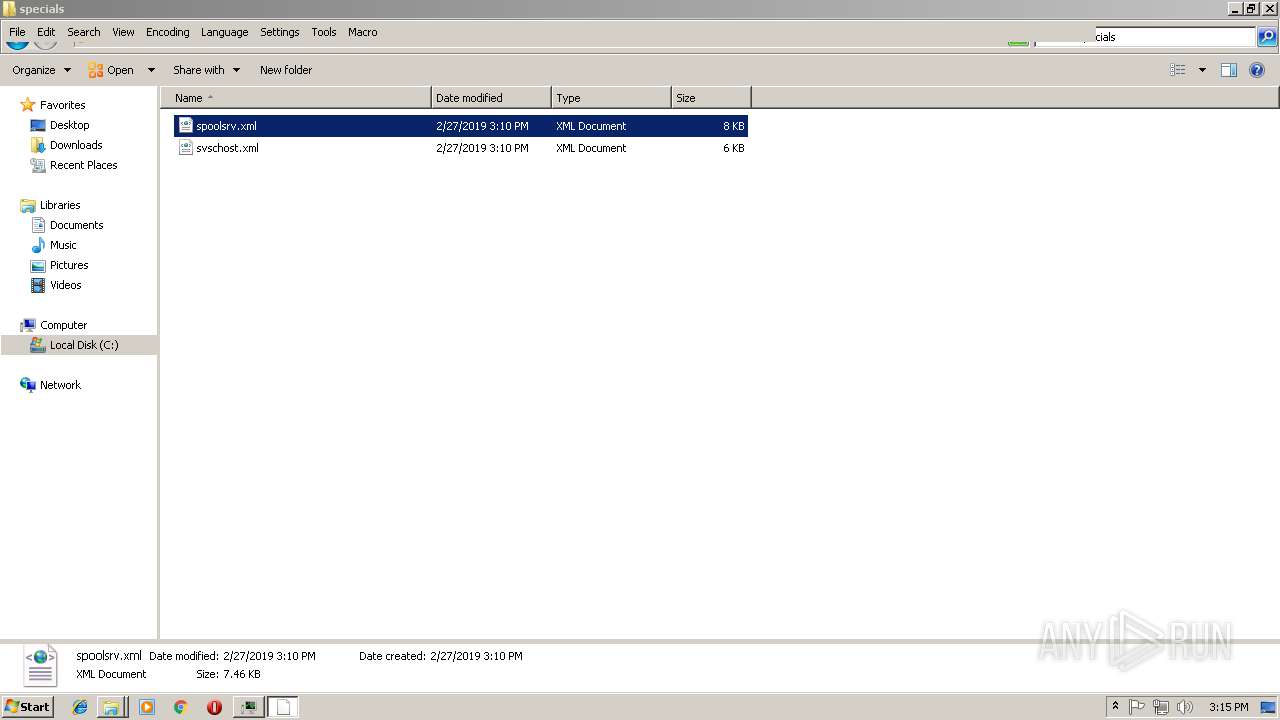
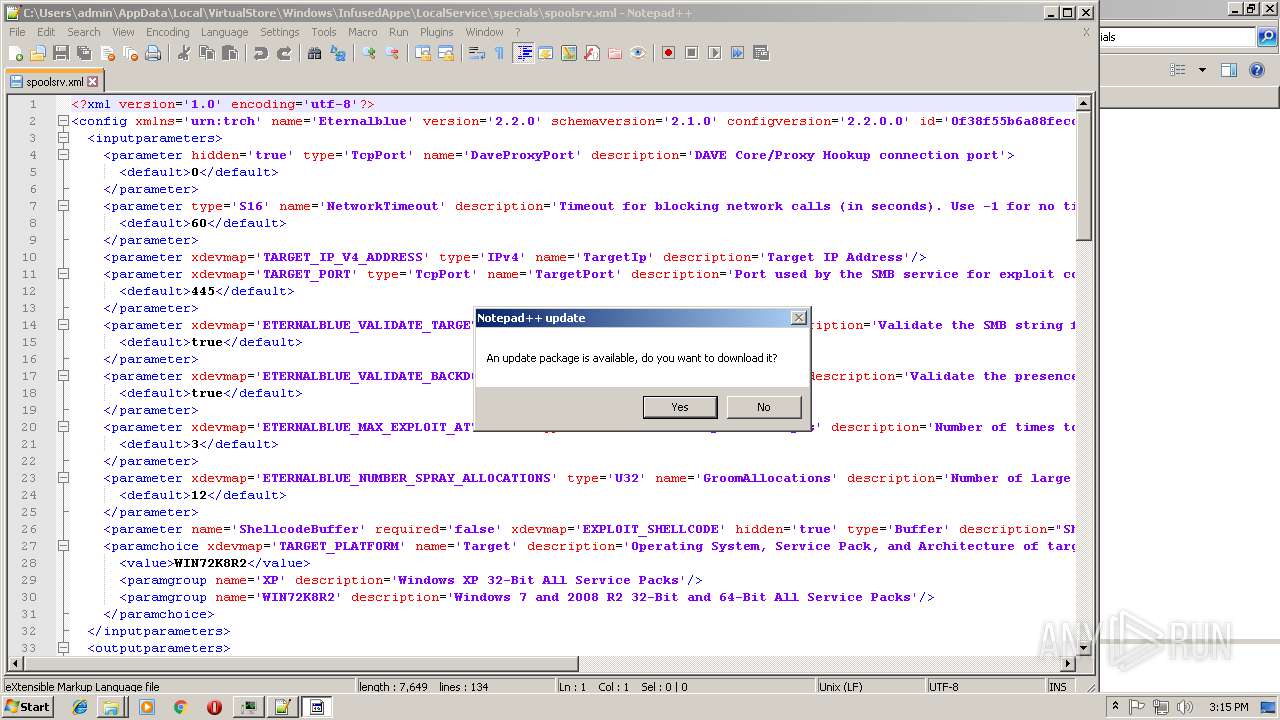
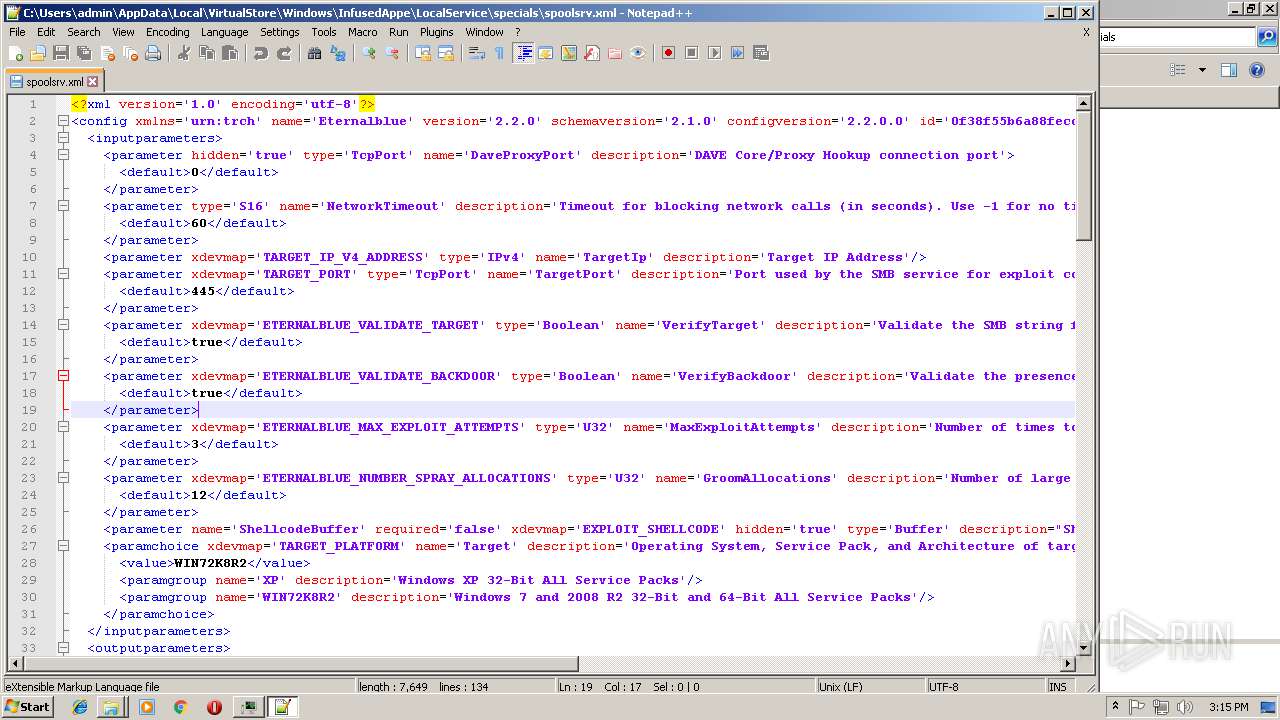
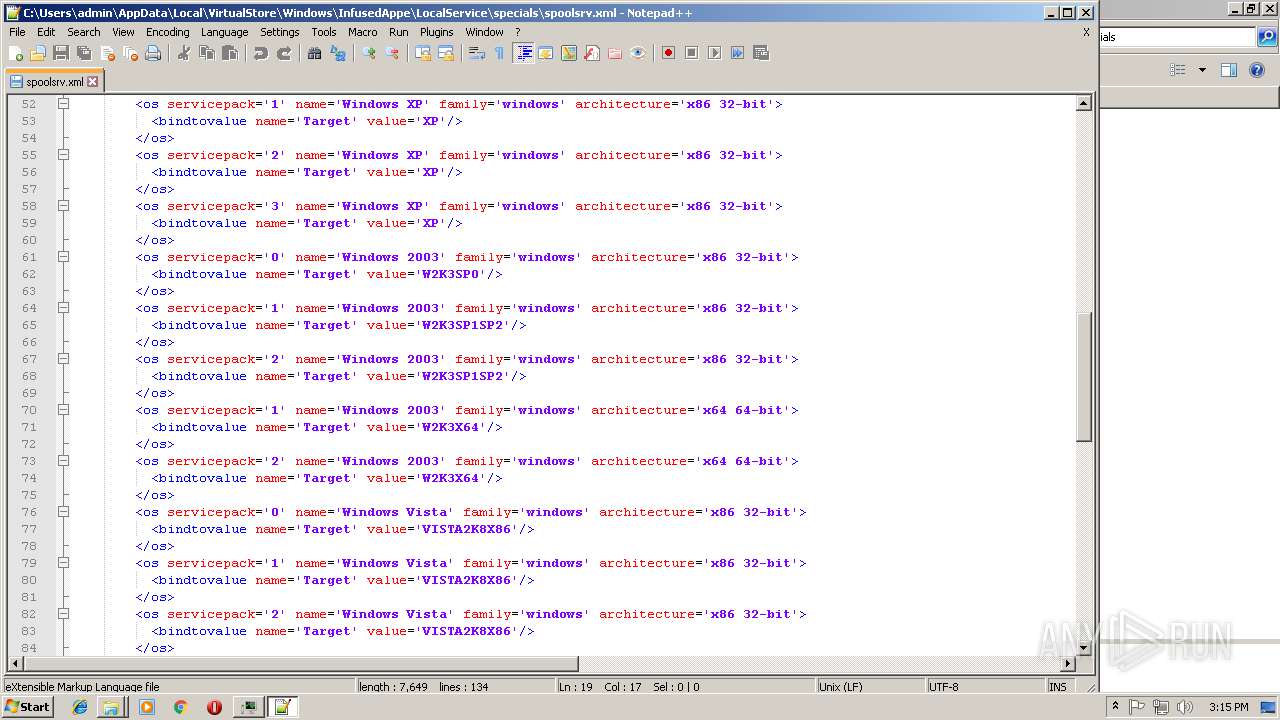
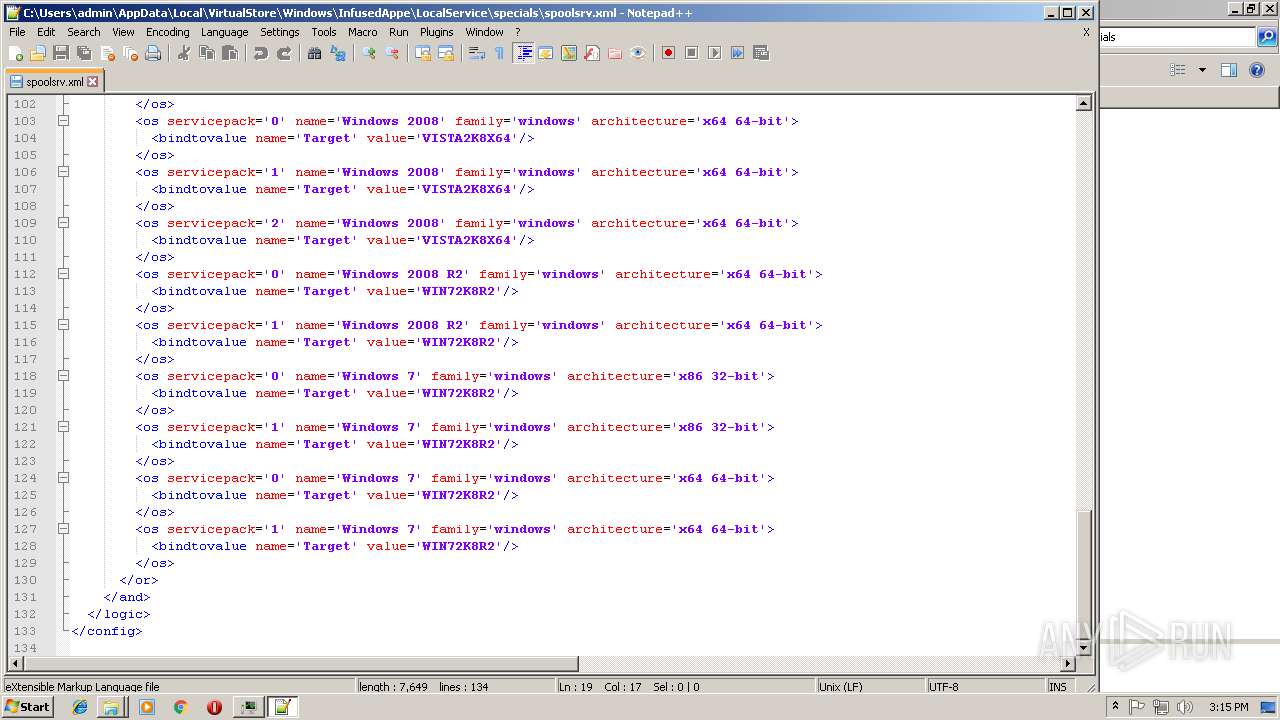
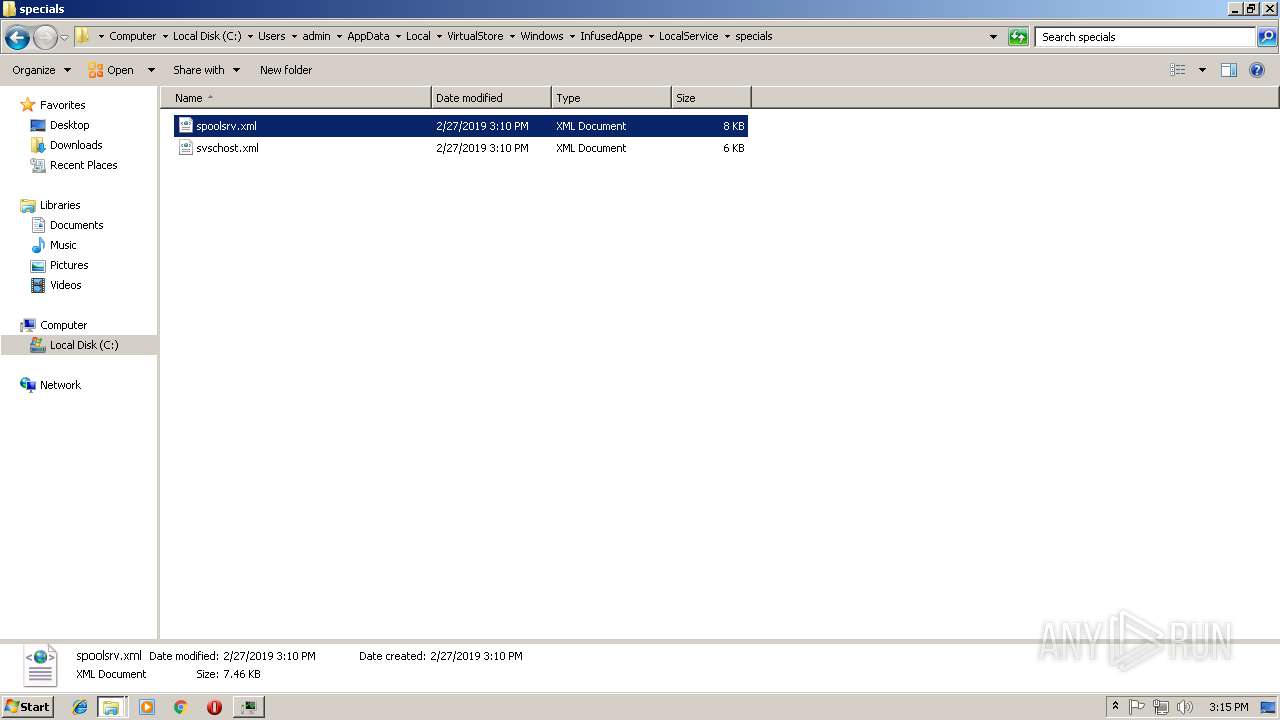
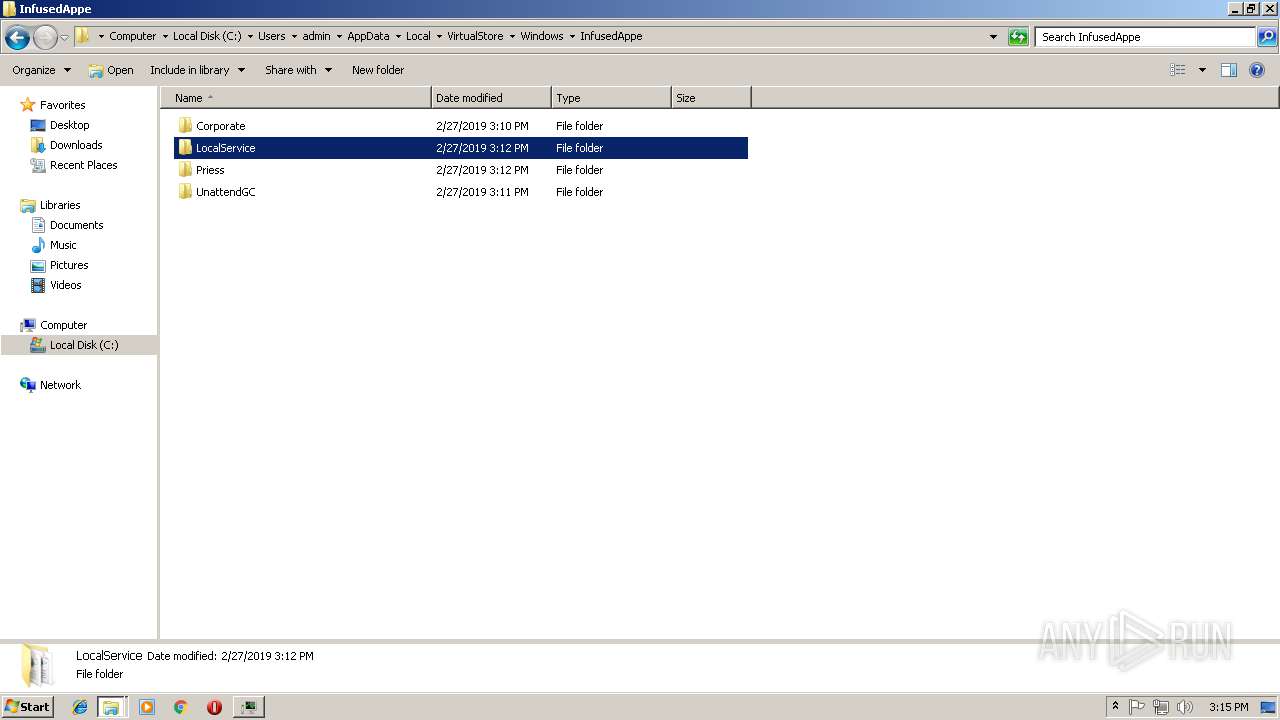
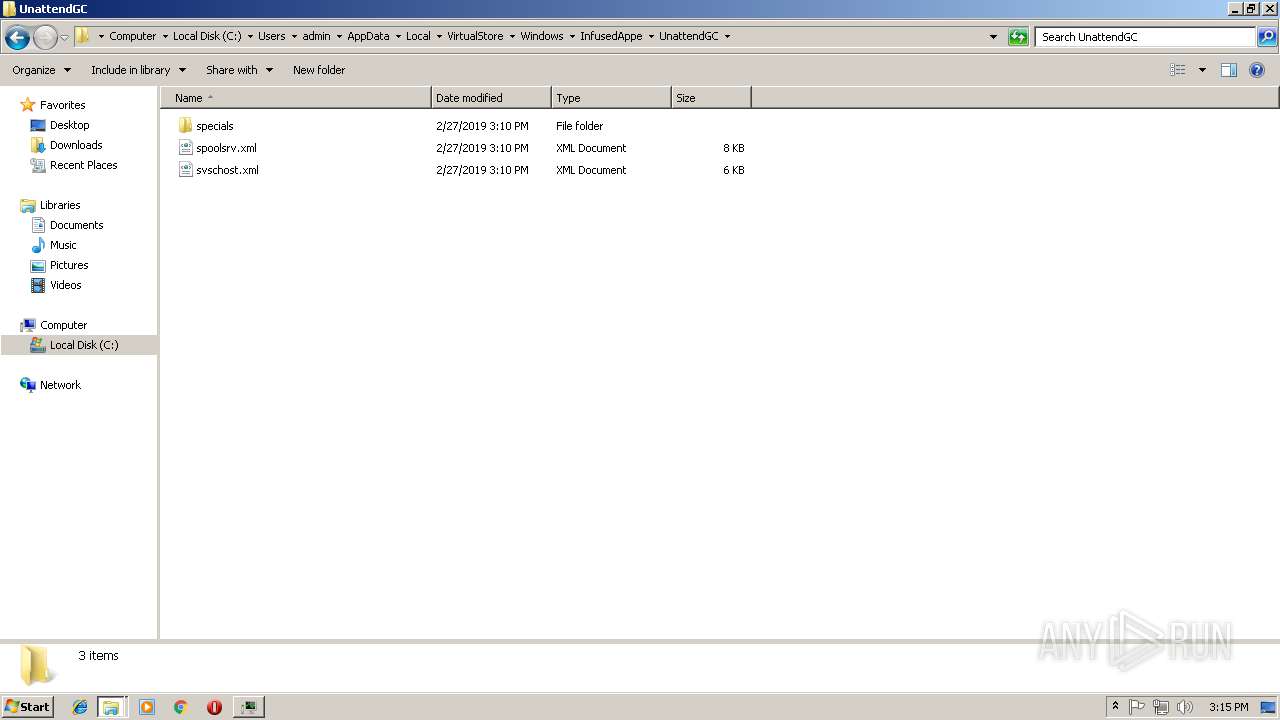
| 576 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\VirtualStore\Windows\InfusedAppe\LocalService\specials\spoolsrv.xml" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 952 | cmd /c net stop wuauserv | C:\Windows\system32\cmd.exe | — | docropool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
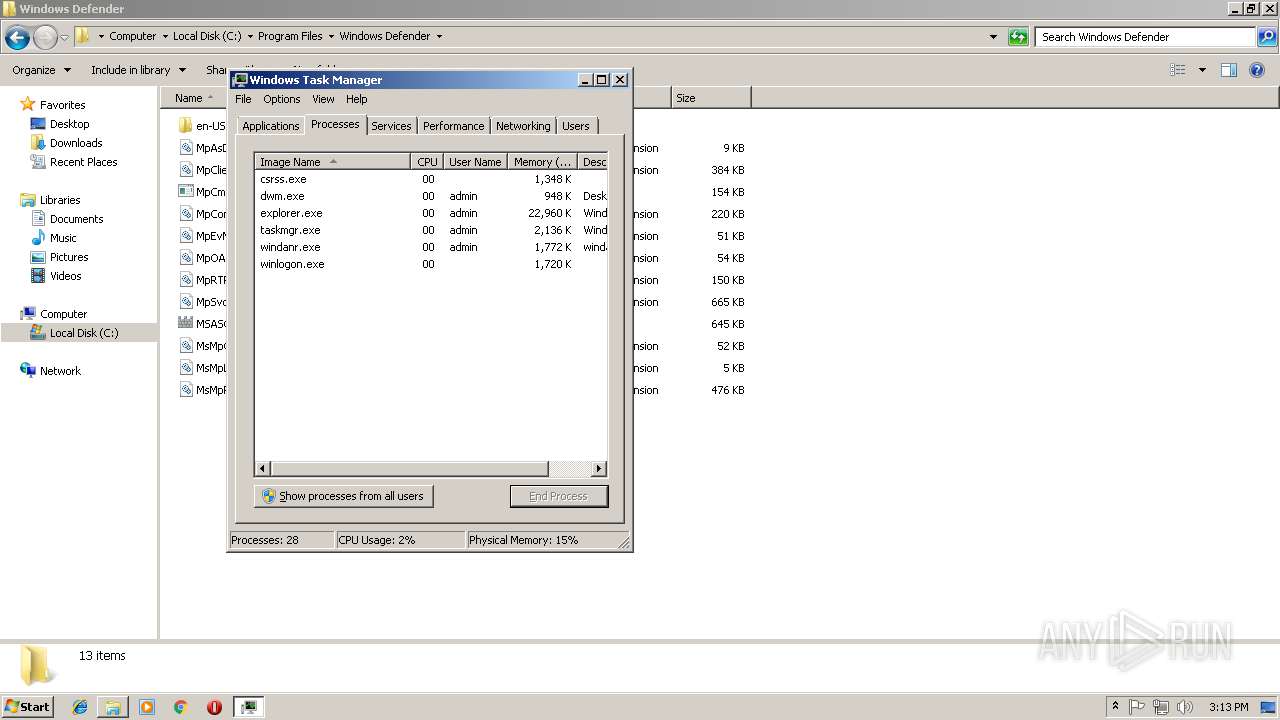
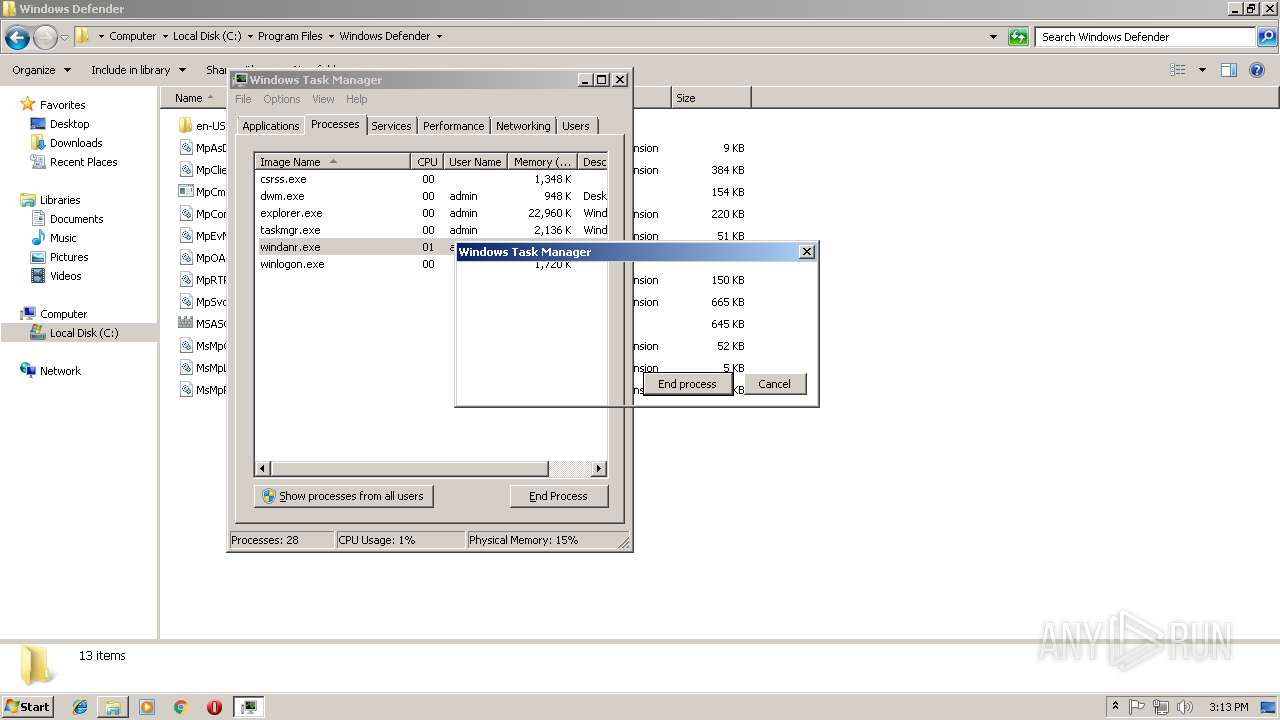
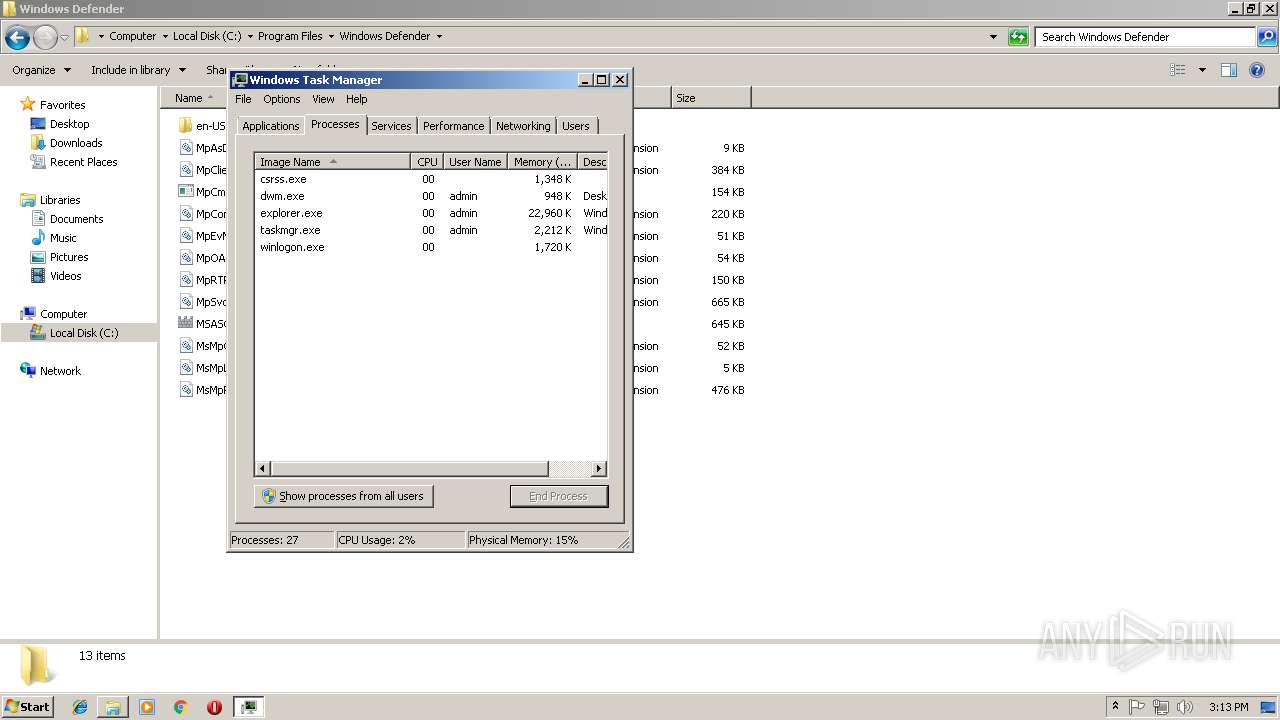
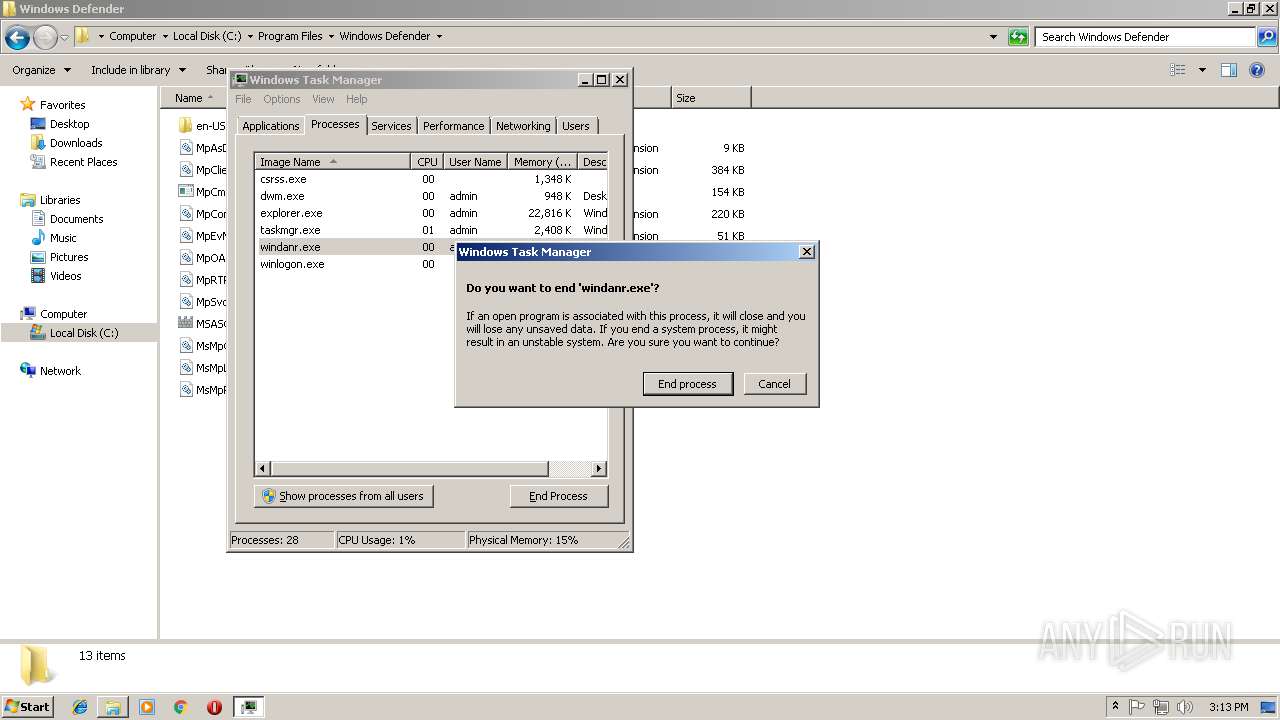
| 1852 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\net1 stop LanmanServer | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2168 | sc config LanmanServer start= disabled | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2252 | cmd /c sc config SharedAccess start= disabled | C:\Windows\system32\cmd.exe | — | docropool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2388 | net stop MpsSvc | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | cmd /c sc config MpsSvc start= disabled | C:\Windows\system32\cmd.exe | — | docropool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2440 | net stop LanmanServer | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
319
Read events
266
Write events
52
Delete events
1
Modification events
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | DocFilePropertray |
Value: C:\Users\admin\AppData\Local\Temp\docropool.exe | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3192) docropool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\docropool_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
0
Text files
19
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\Temp\2158609\....\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\Temp\2158609\TemporaryFile | — | |
MD5:— | SHA256:— | |||
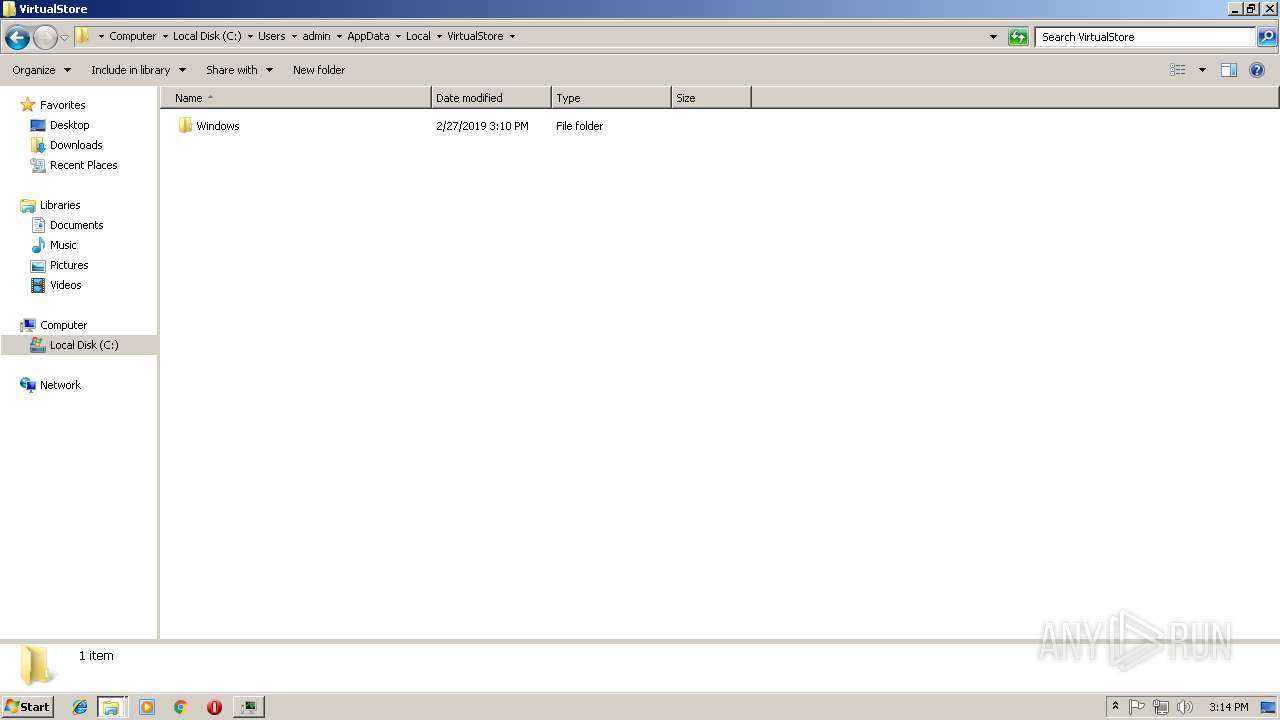
| 3072 | wimnat.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Windows\System32\2161296.bak | — | |
MD5:— | SHA256:— | |||
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\Temp\2161546\....\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\Temp\2161546\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\Temp\2199218\....\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\Temp\2199218\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\Temp\2251843\....\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\Temp\2251843\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3192 | docropool.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\InfusedAppe\Priess\ip.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
10
DNS requests
8
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3192 | docropool.exe | GET | — | 117.25.157.119:80 | http://2019.ip138.com/ic.asp | CN | — | — | suspicious |
3192 | docropool.exe | GET | — | 117.25.157.119:80 | http://2019.ip138.com/ic.asp | CN | — | — | suspicious |
3192 | docropool.exe | GET | — | 117.25.157.119:80 | http://2019.ip138.com/ic.asp | CN | — | — | suspicious |
3192 | docropool.exe | GET | 200 | 172.105.201.31:57890 | http://a88.bulehero.in:57890/Cfg.ini | US | text | 410 b | suspicious |
3192 | docropool.exe | GET | 200 | 172.105.201.31:57890 | http://a88.bulehero.in:57890/Cfg.ini | US | text | 410 b | suspicious |
— | — | GET | 200 | 2.16.106.50:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | unknown | der | 727 b | whitelisted |
— | — | GET | 200 | 2.16.106.50:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | unknown | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.106.50:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
3192 | docropool.exe | 172.105.201.31:57890 | a88.bulehero.in | — | US | suspicious |
3192 | docropool.exe | 45.32.254.54:80 | a47.bulehero.in | Choopa, LLC | JP | suspicious |
3652 | taskmgr.exe | 139.99.120.75:7777 | pool.bulehero.in | OVH SAS | SG | suspicious |
3780 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
3192 | docropool.exe | 117.25.157.119:80 | 2019.ip138.com | Xiamen | CN | suspicious |
3192 | docropool.exe | 216.239.32.21:443 | ifconfig.me | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
a88.bulehero.in |
| malicious |
a47.bulehero.in |
| malicious |
a48.bulehero.in |
| malicious |
pool.bulehero.in |
| malicious |
2019.ip138.com |
| unknown |
ifconfig.me |
| shared |
notepad-plus-plus.org |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3192 | docropool.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3192 | docropool.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32/64.XMR-Miner |
3192 | docropool.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3652 | taskmgr.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
3652 | taskmgr.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
3652 | taskmgr.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3652 | taskmgr.exe | Misc activity | MINER [PTsecurity] Risktool.W32.coinminer!c |
3192 | docropool.exe | Misc activity | SUSPICIOUS [PTsecurity] IP lookup service ip138.com |
3192 | docropool.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32/64.XMR-Miner |
3192 | docropool.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|