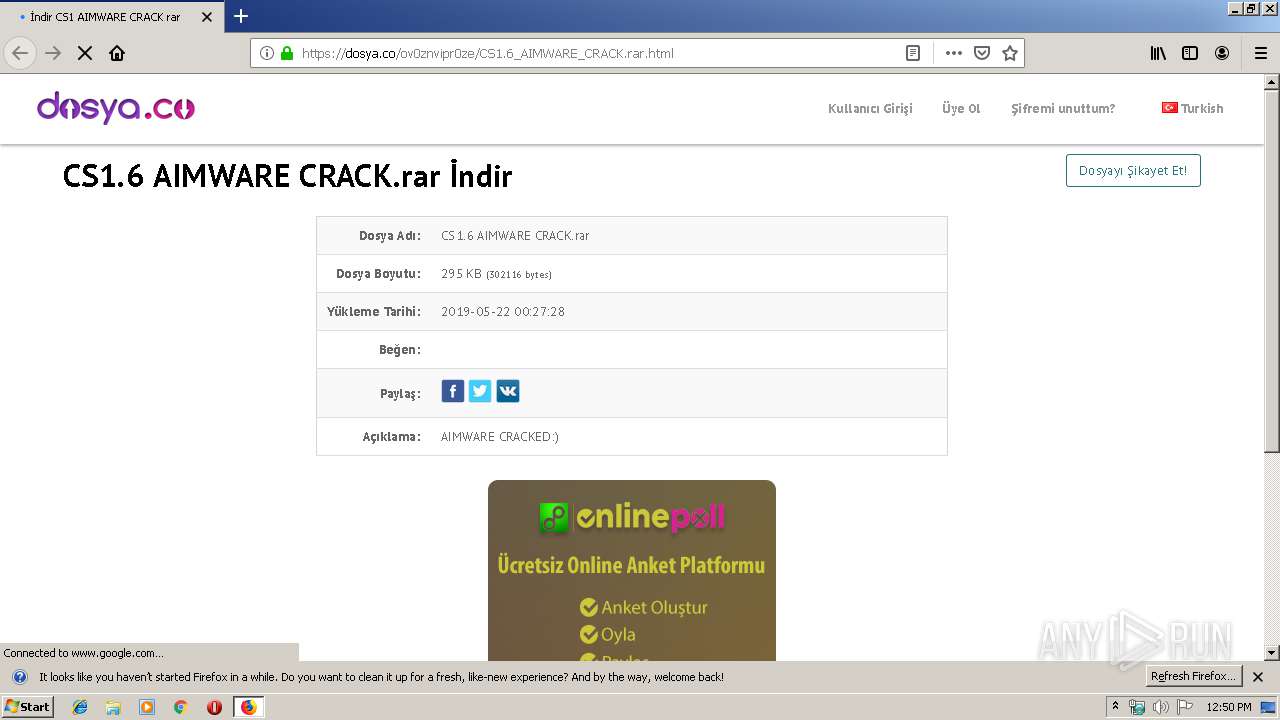
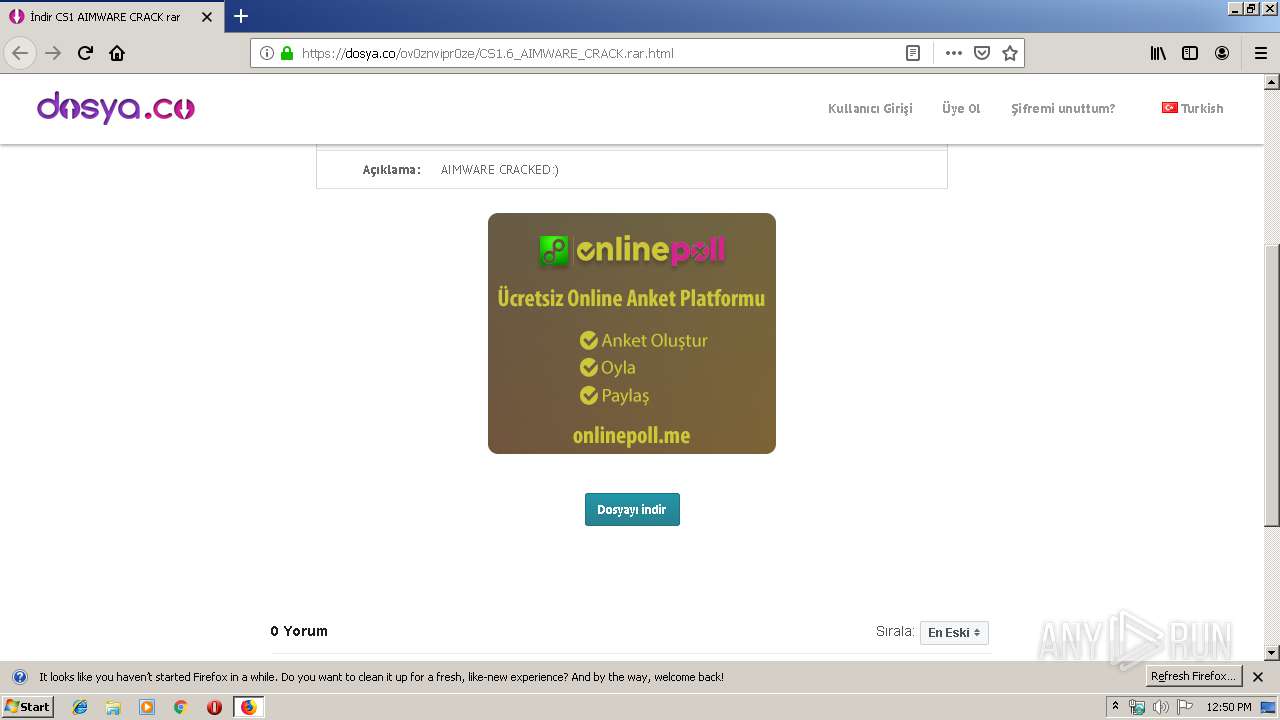
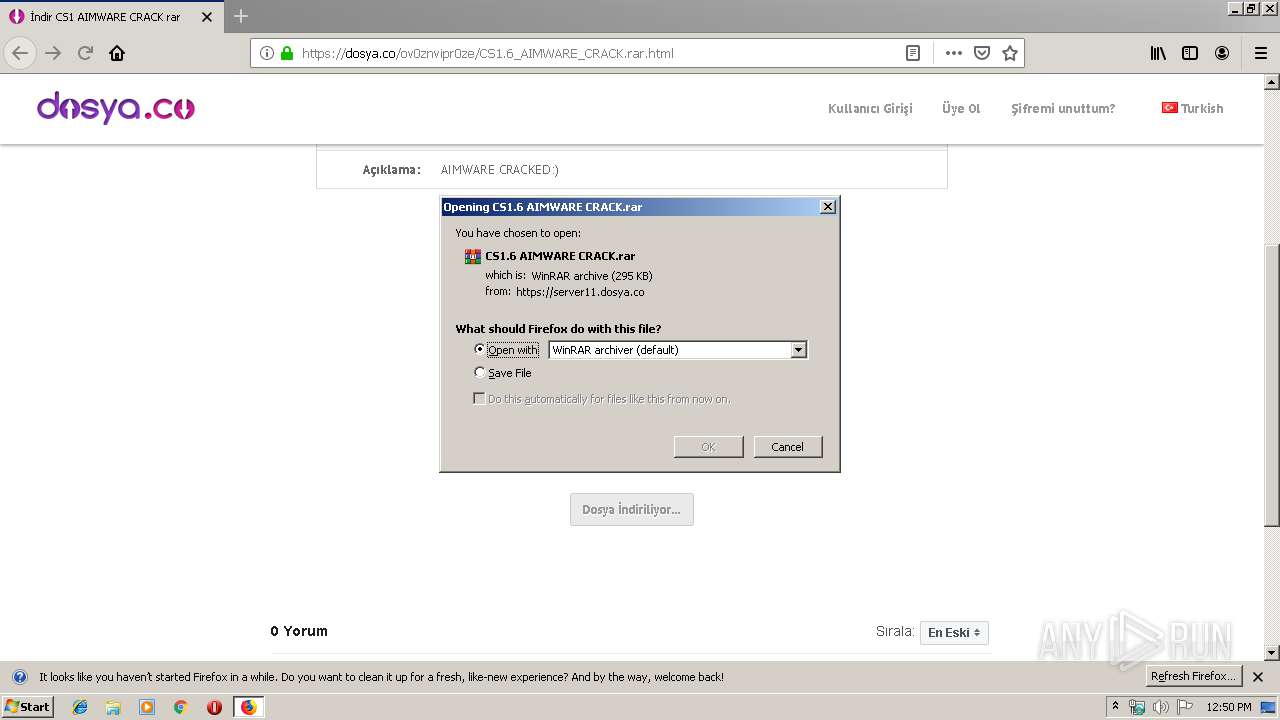
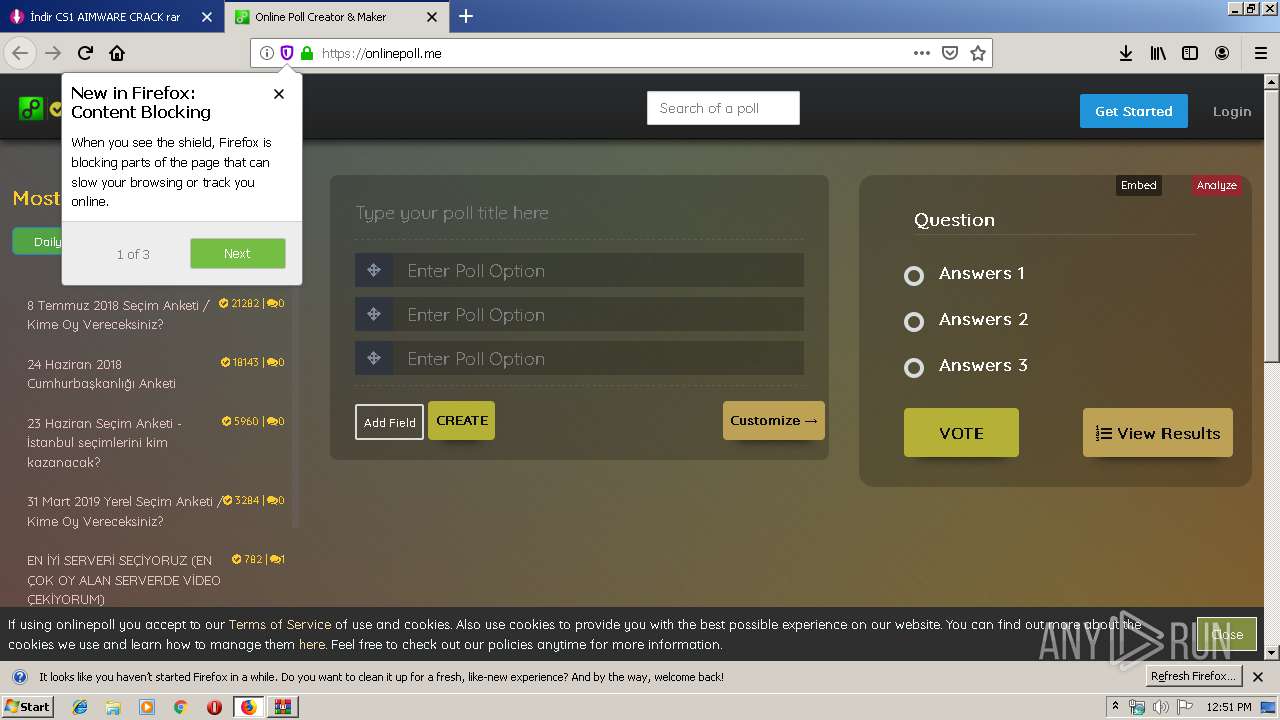
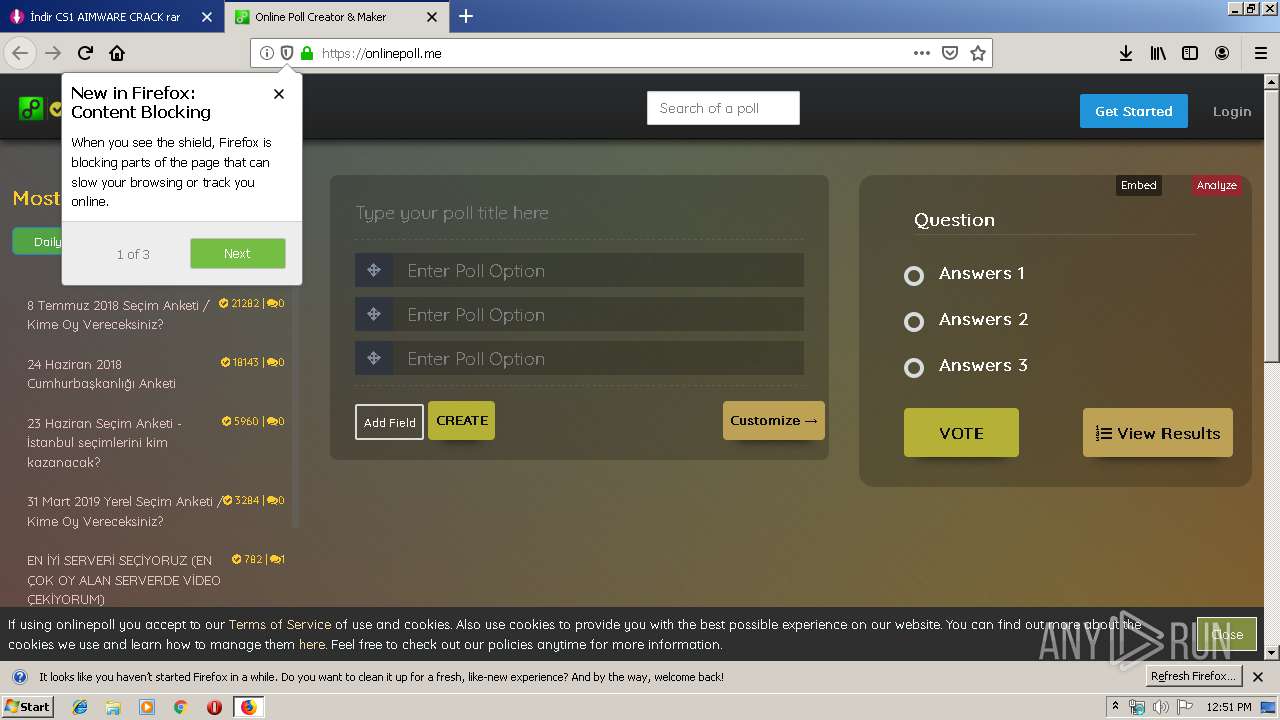
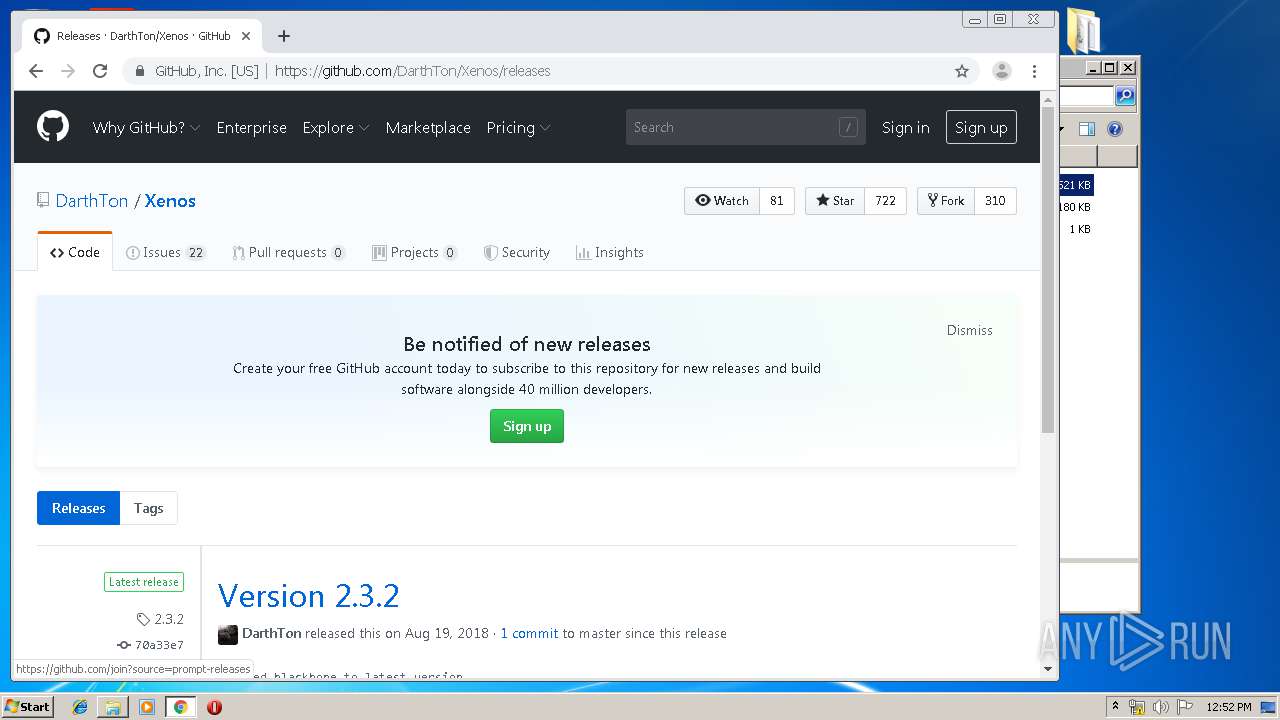
| URL: | https://dosya.co/ov0znvipr0ze/CS1.6_AIMWARE_CRACK.rar.html |
| Full analysis: | https://app.any.run/tasks/c3afa7f5-6321-48cd-b9fd-ea90ab045f00 |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | January 01, 2020, 12:50:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D50BF6040AB04E71794FE90D977D8C0B |
| SHA1: | 68ABE072FCD31877A3561B96E9AB4DE3BE097AF0 |
| SHA256: | 1006A50AAA07D9BE0F54D68EFBE7D2407702F9AF2D55CFF71513F697904F2EC3 |
| SSDEEP: | 3:N8SgLd1lOVoUs8kvQEUsn:2SK6Rs82Usn |
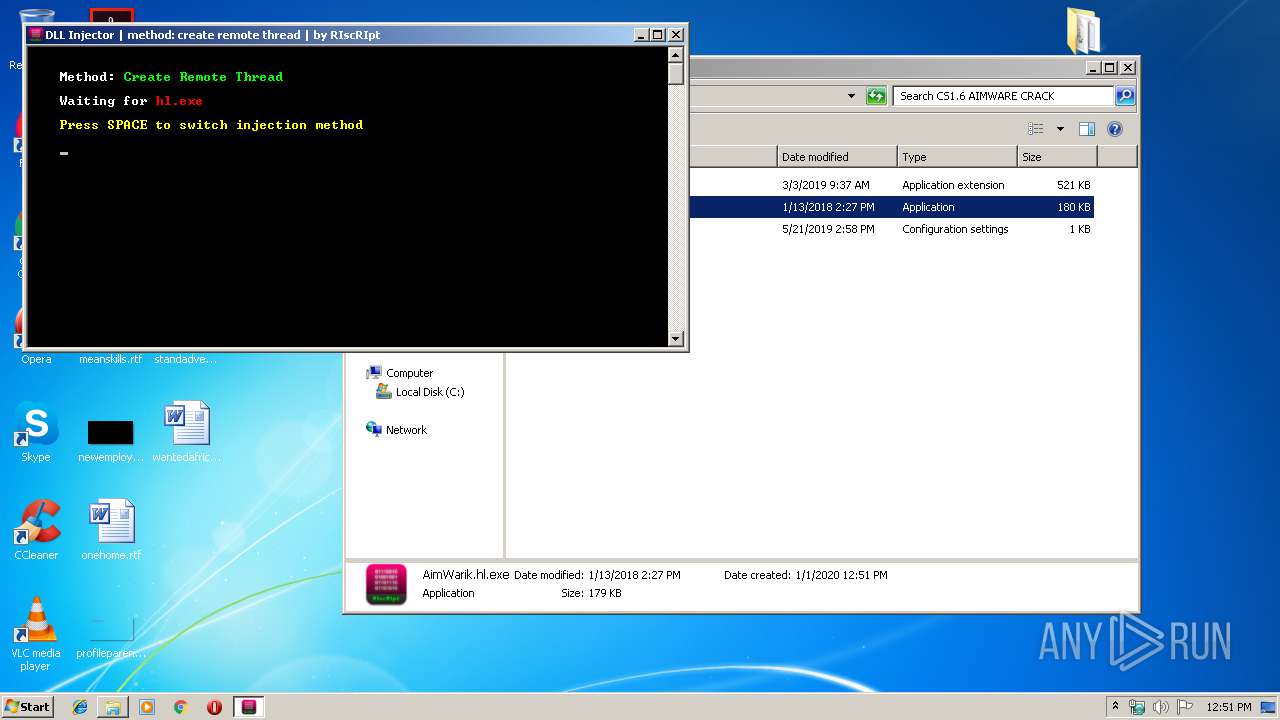
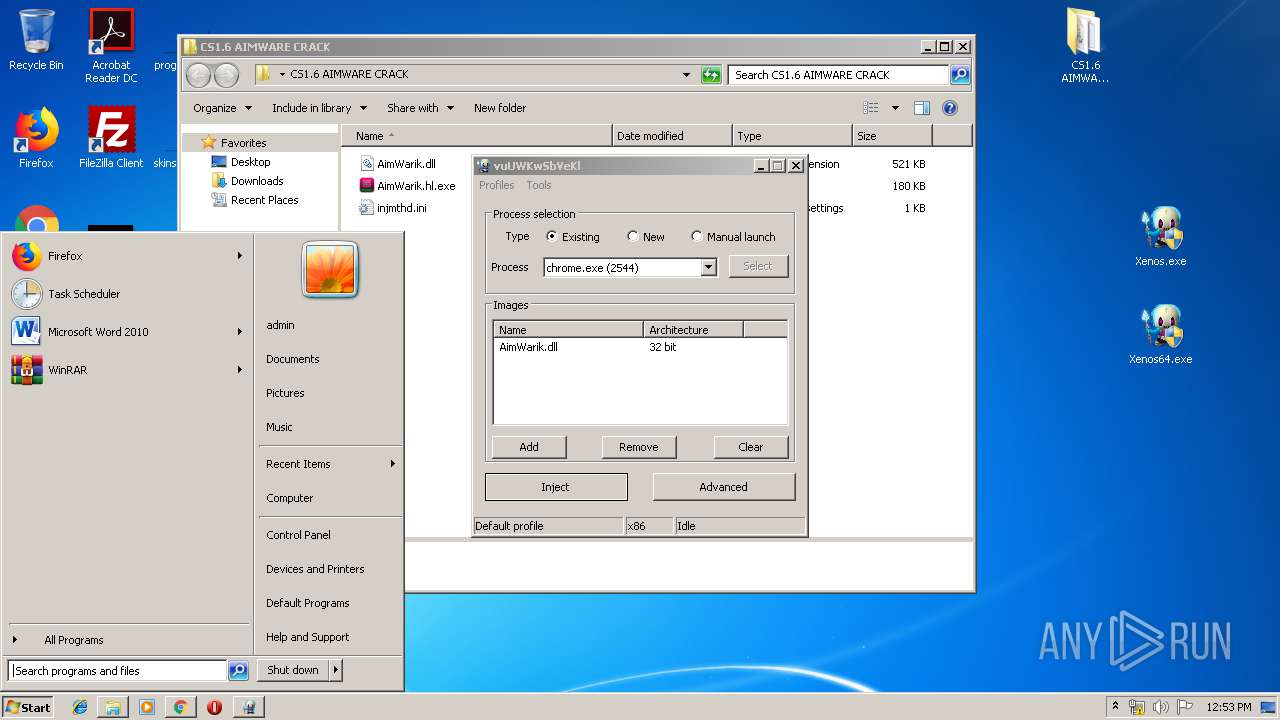
MALICIOUS
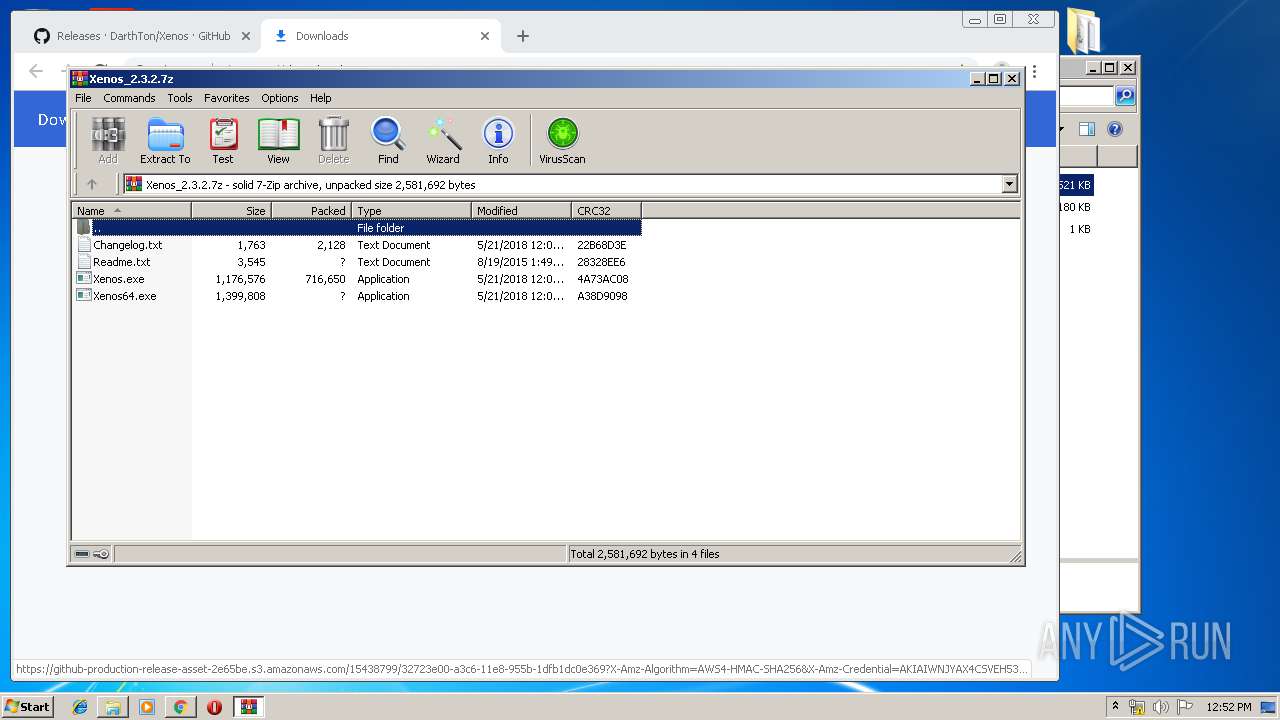
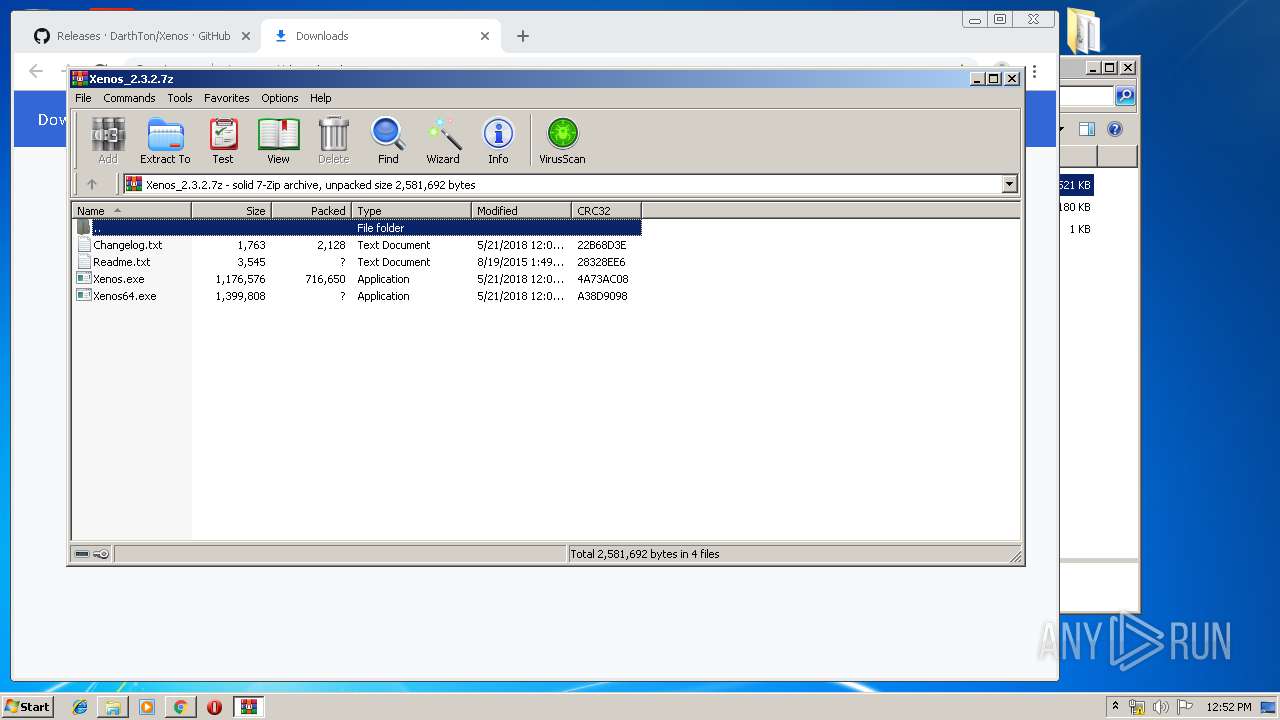
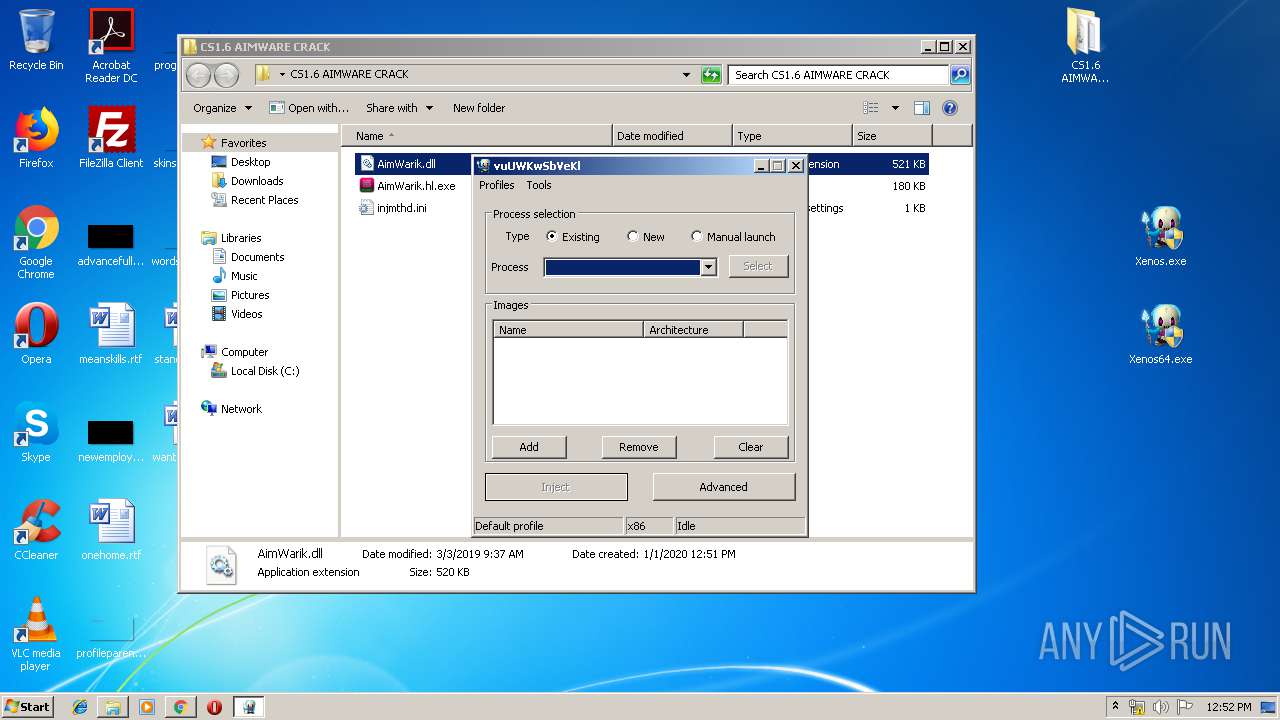
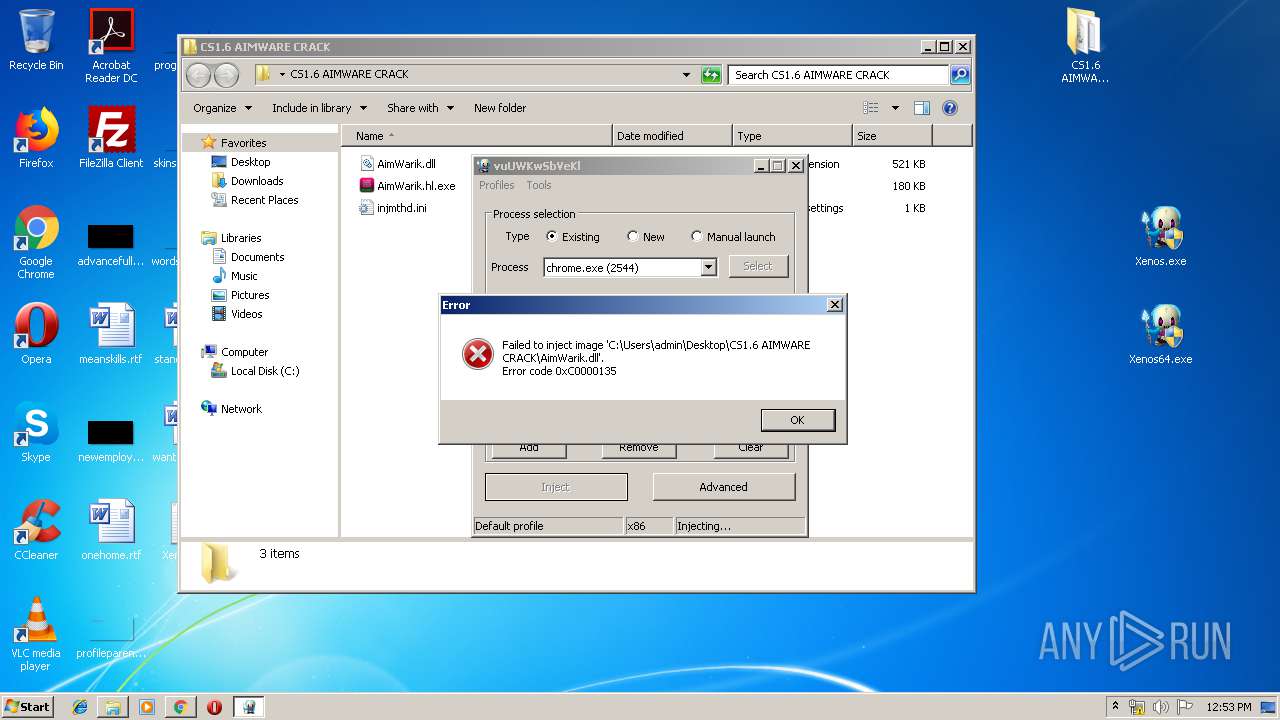
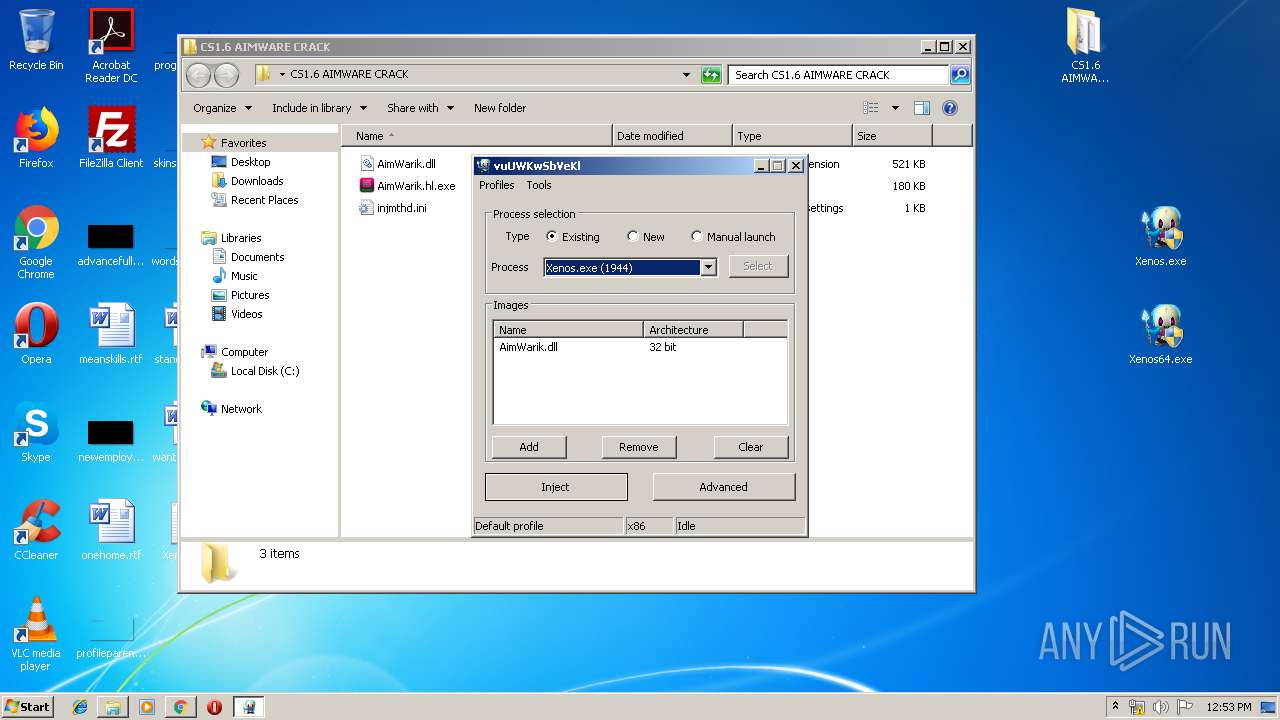
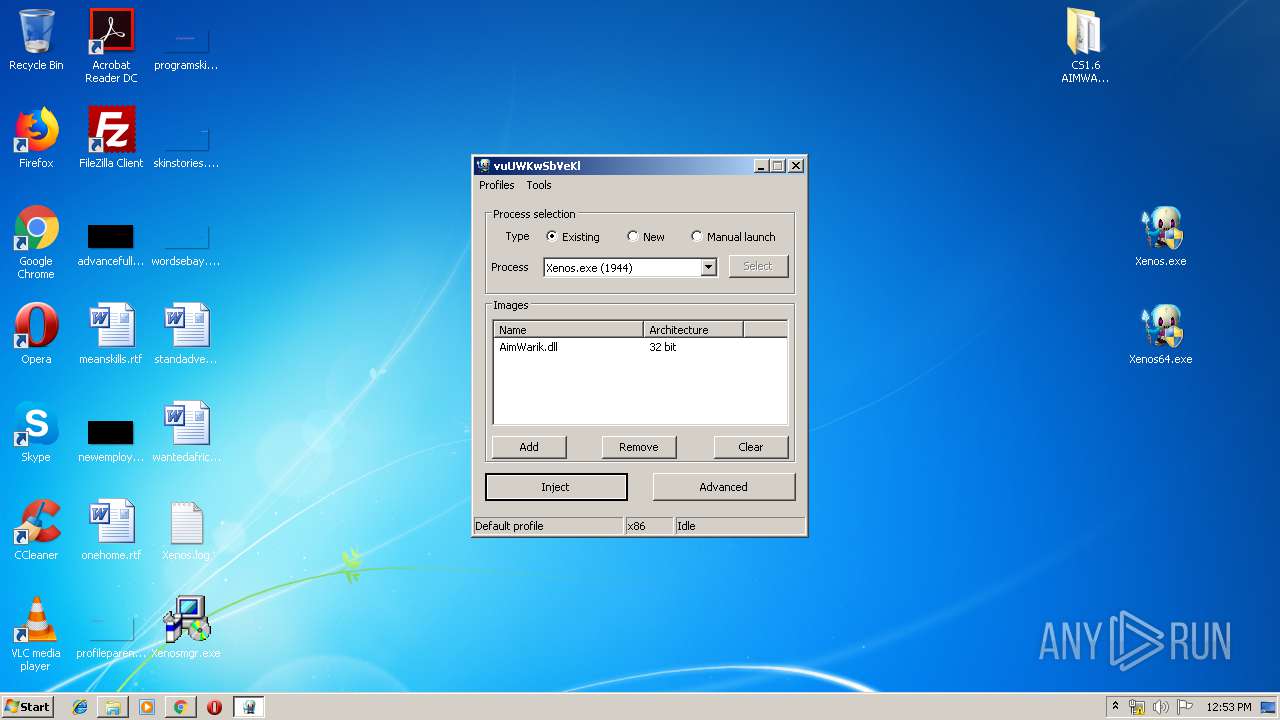
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3124)
- explorer.exe (PID: 352)
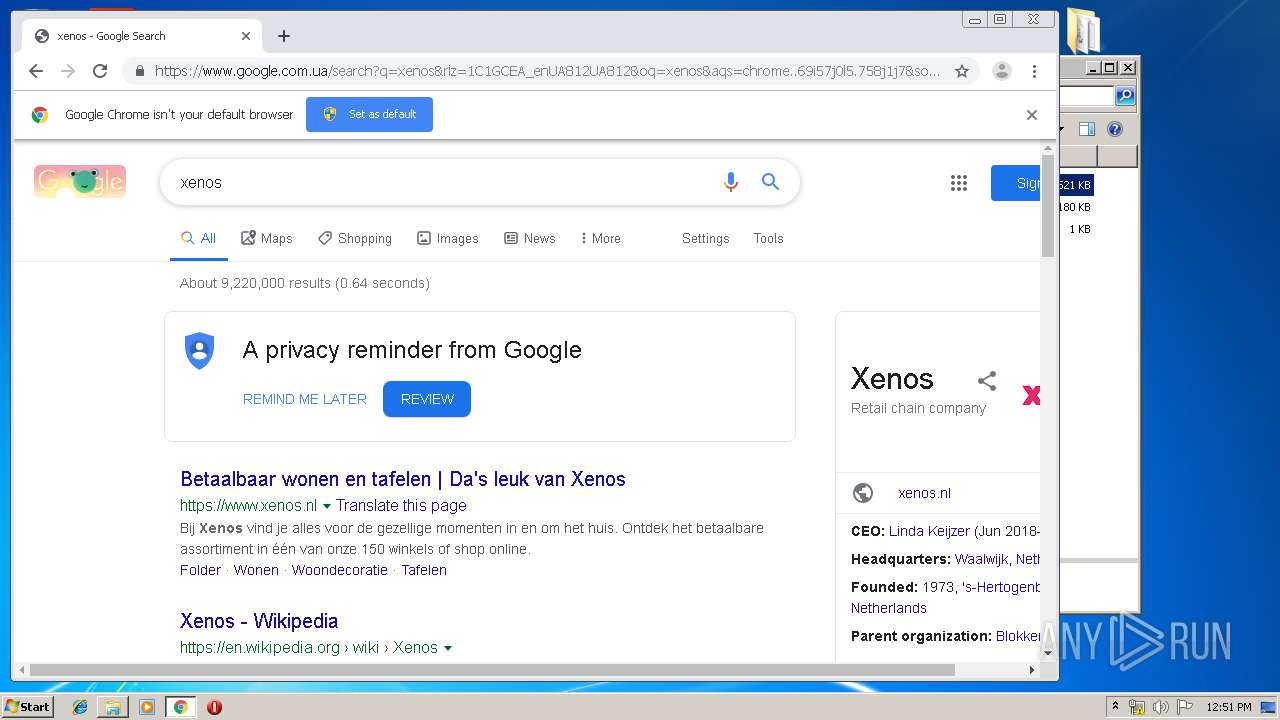
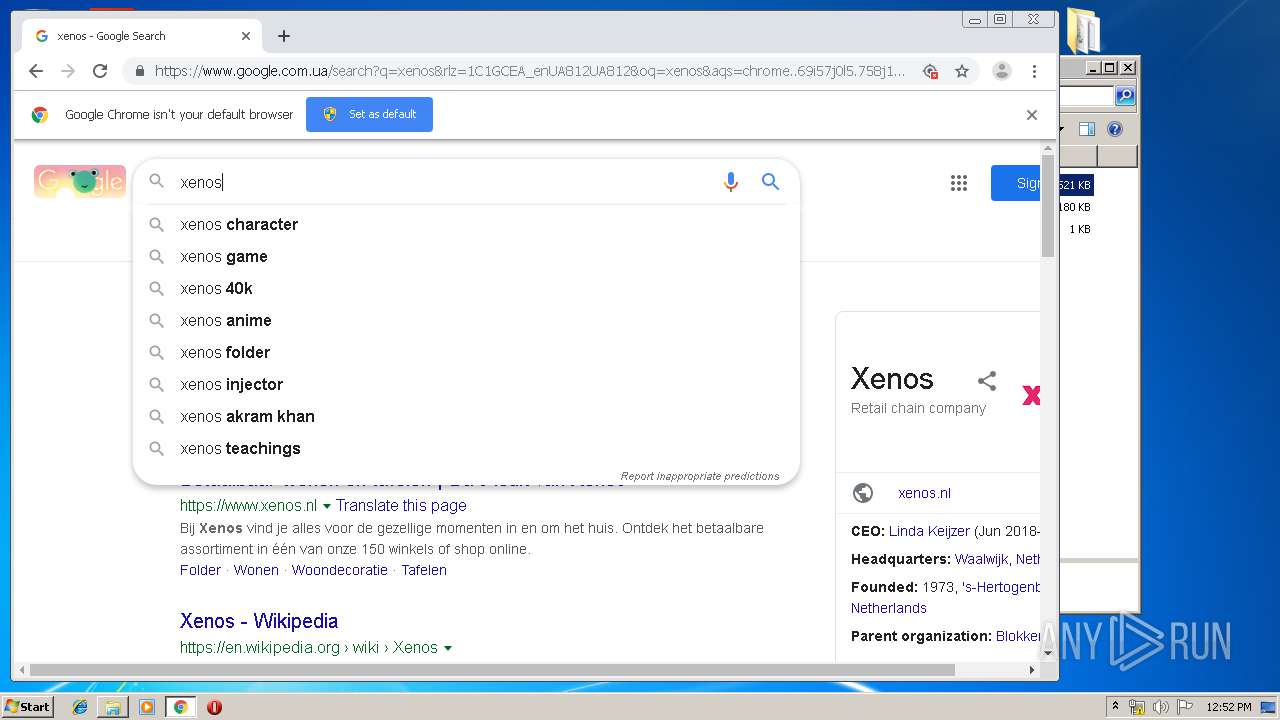
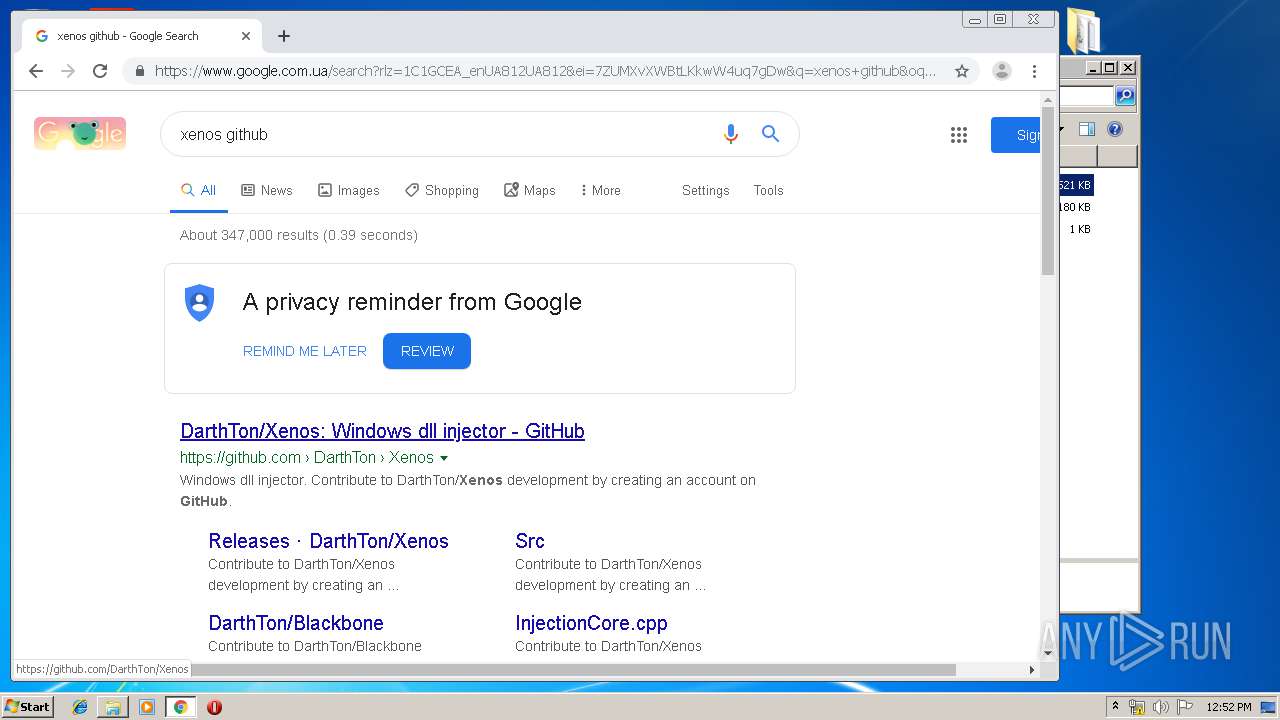
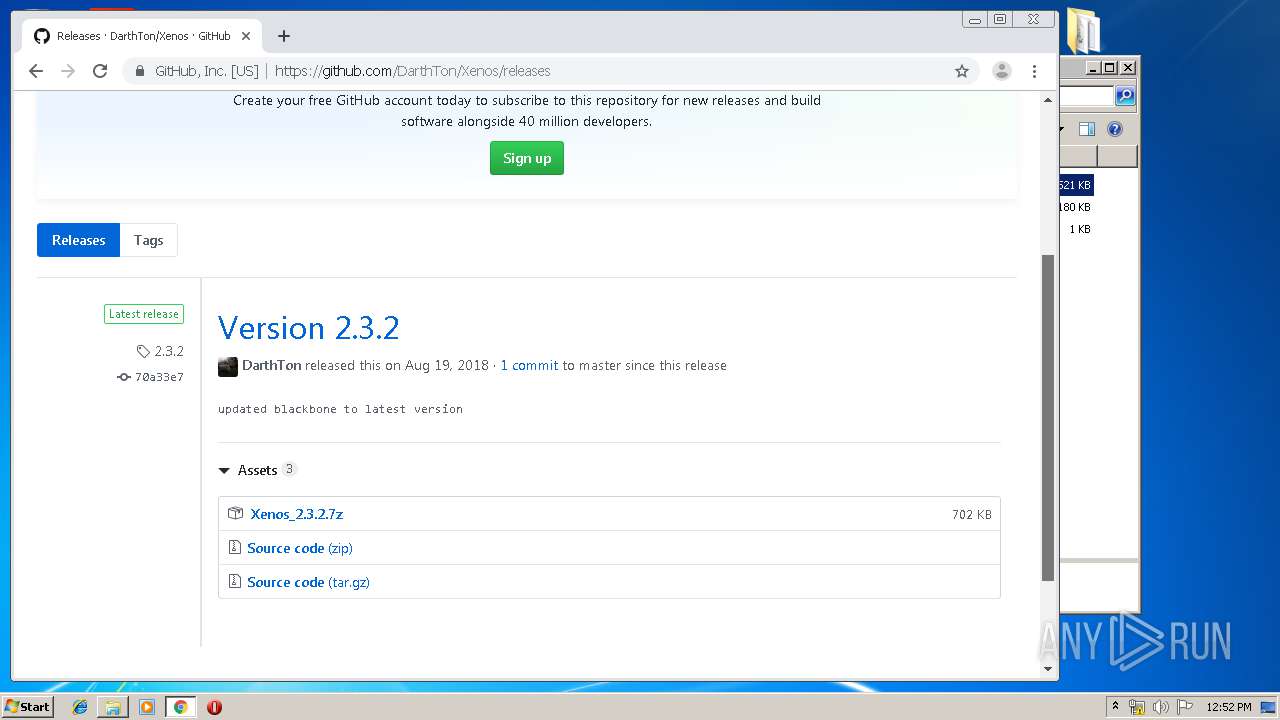
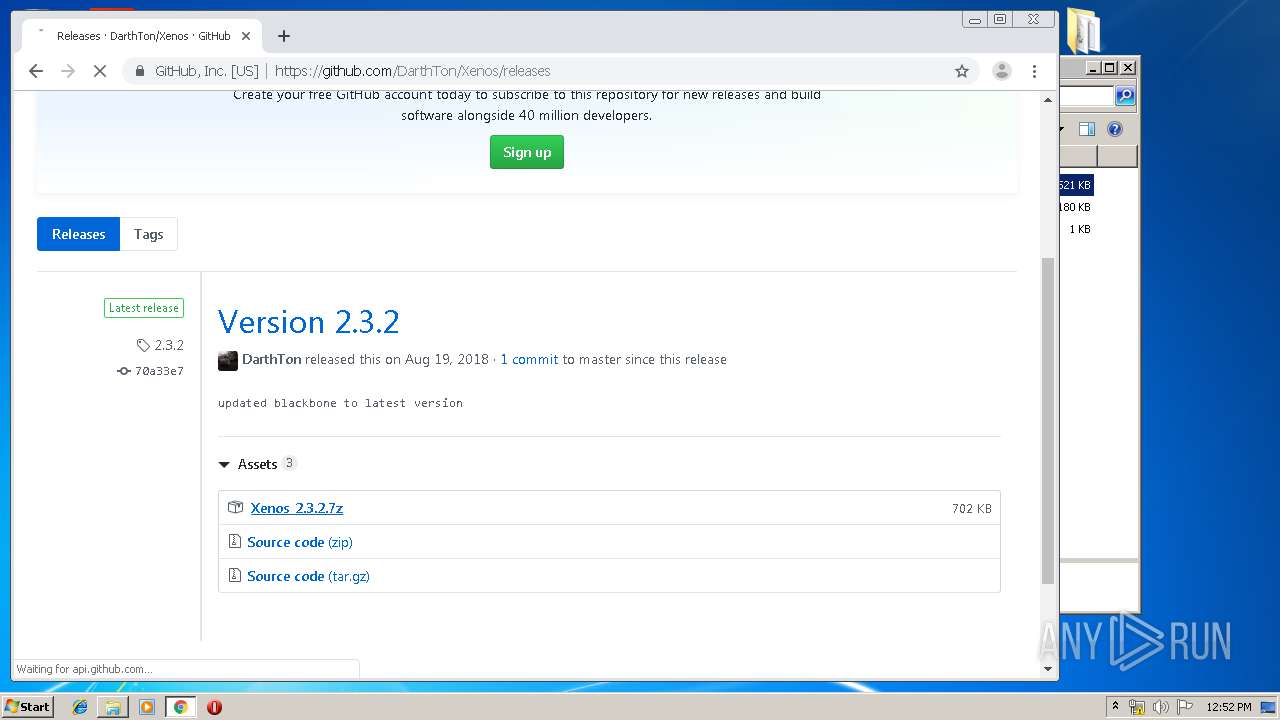
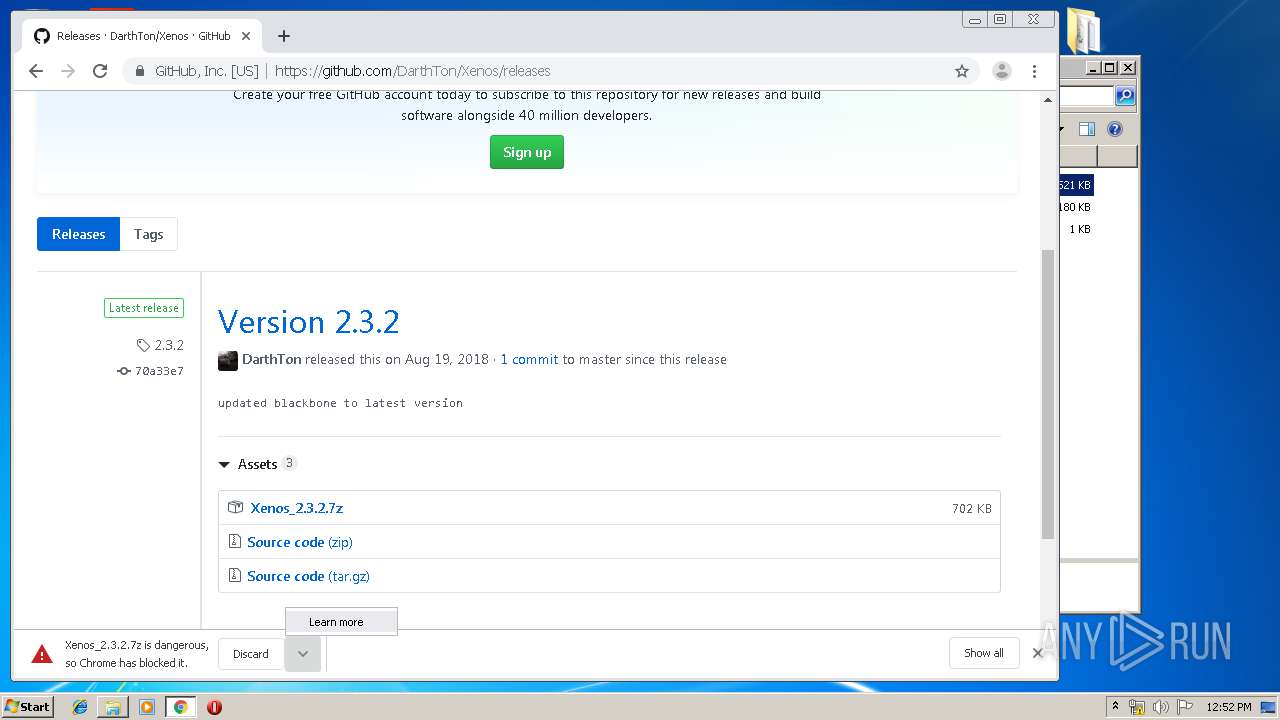
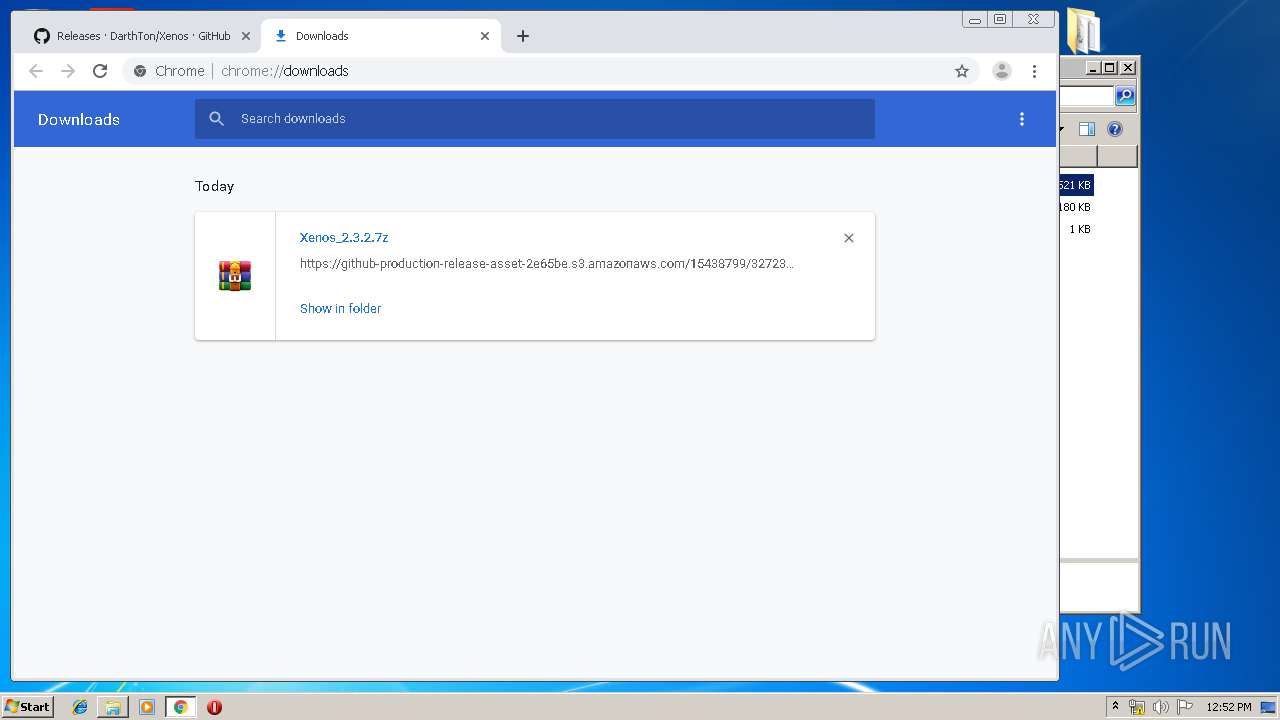
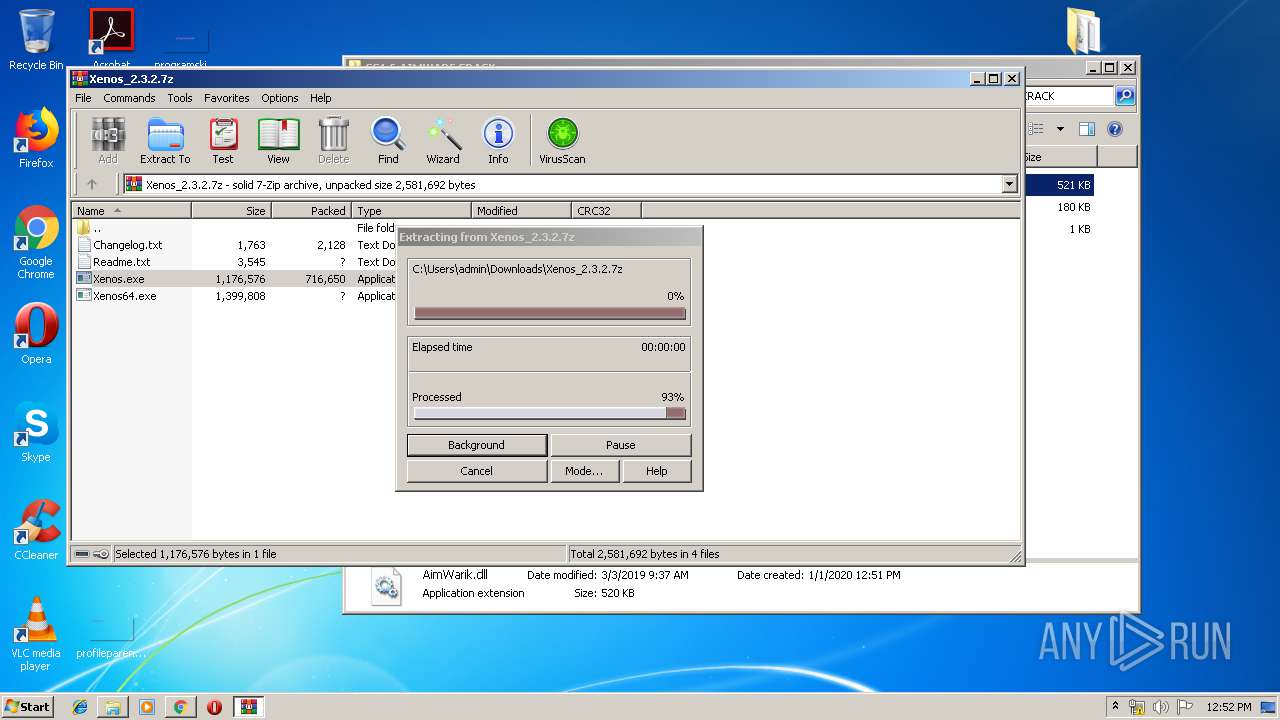
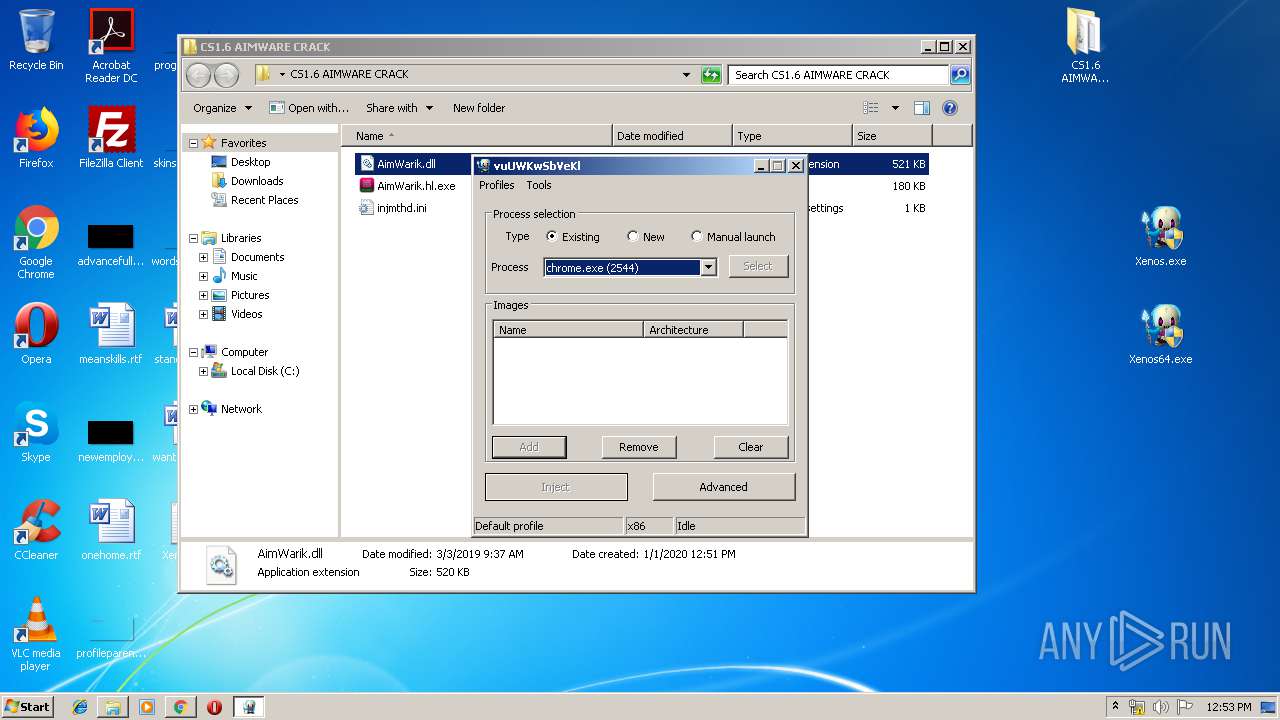
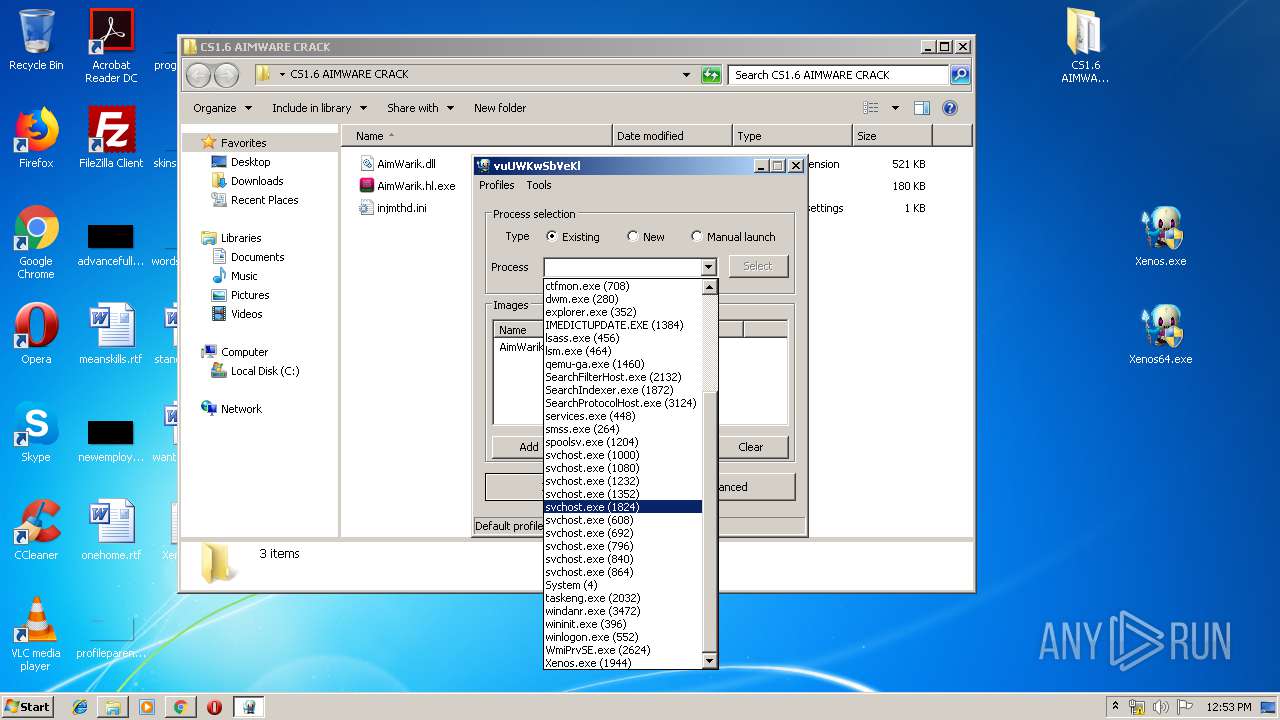
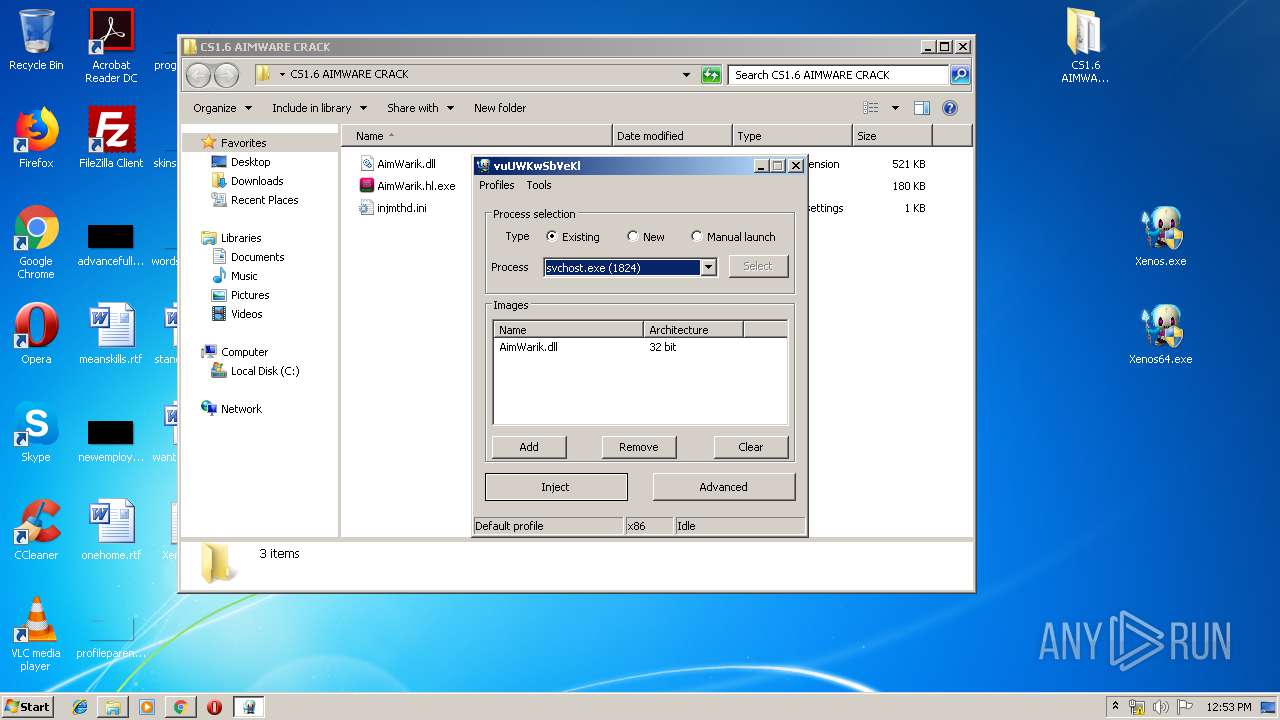
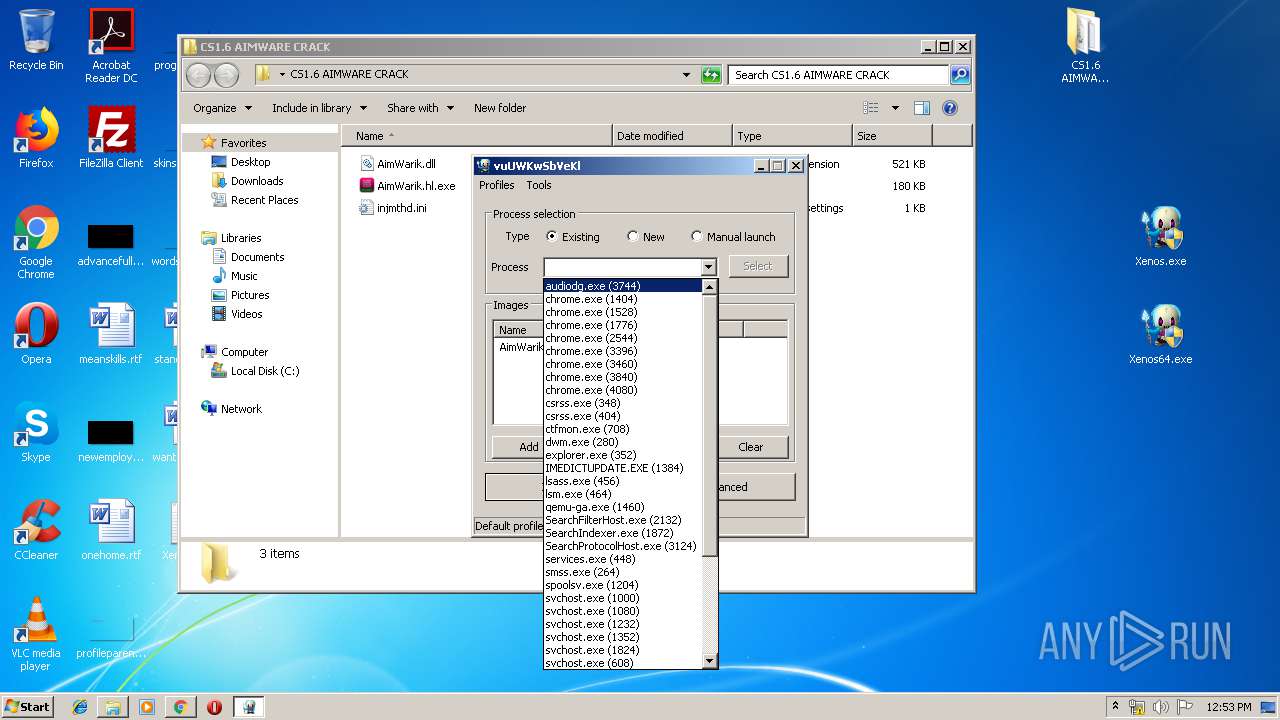
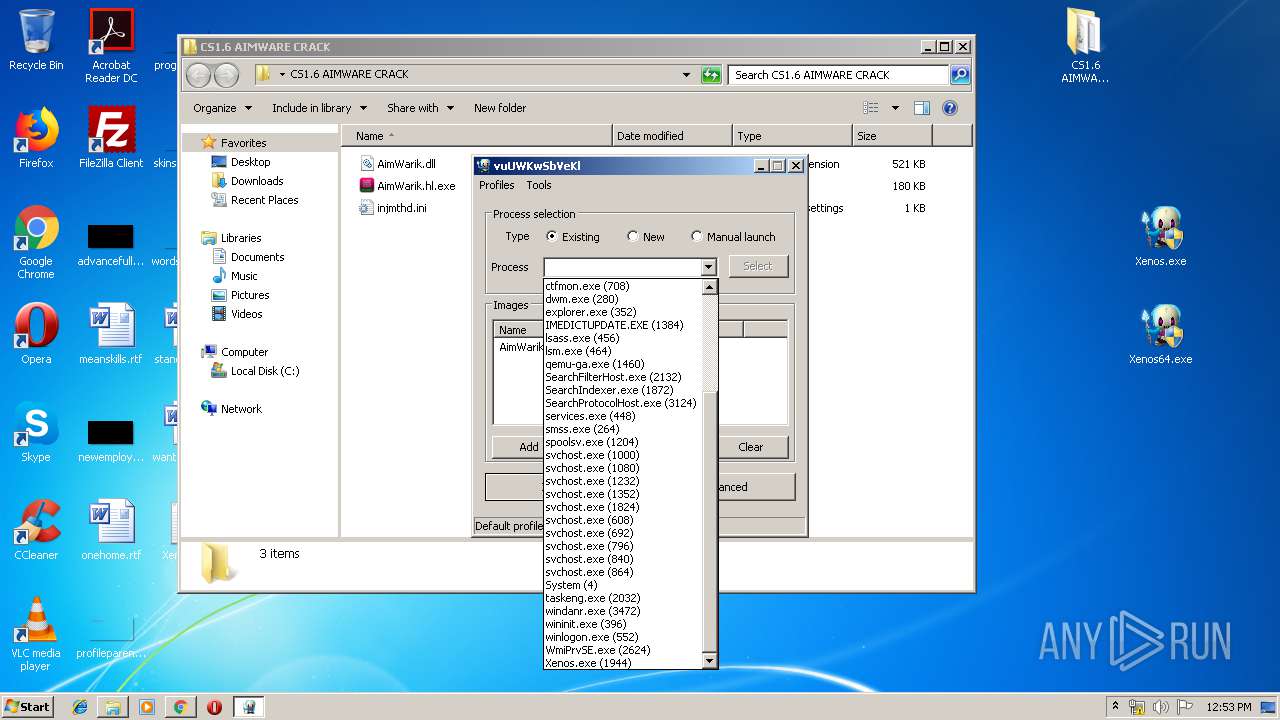
- Xenos.exe (PID: 1944)
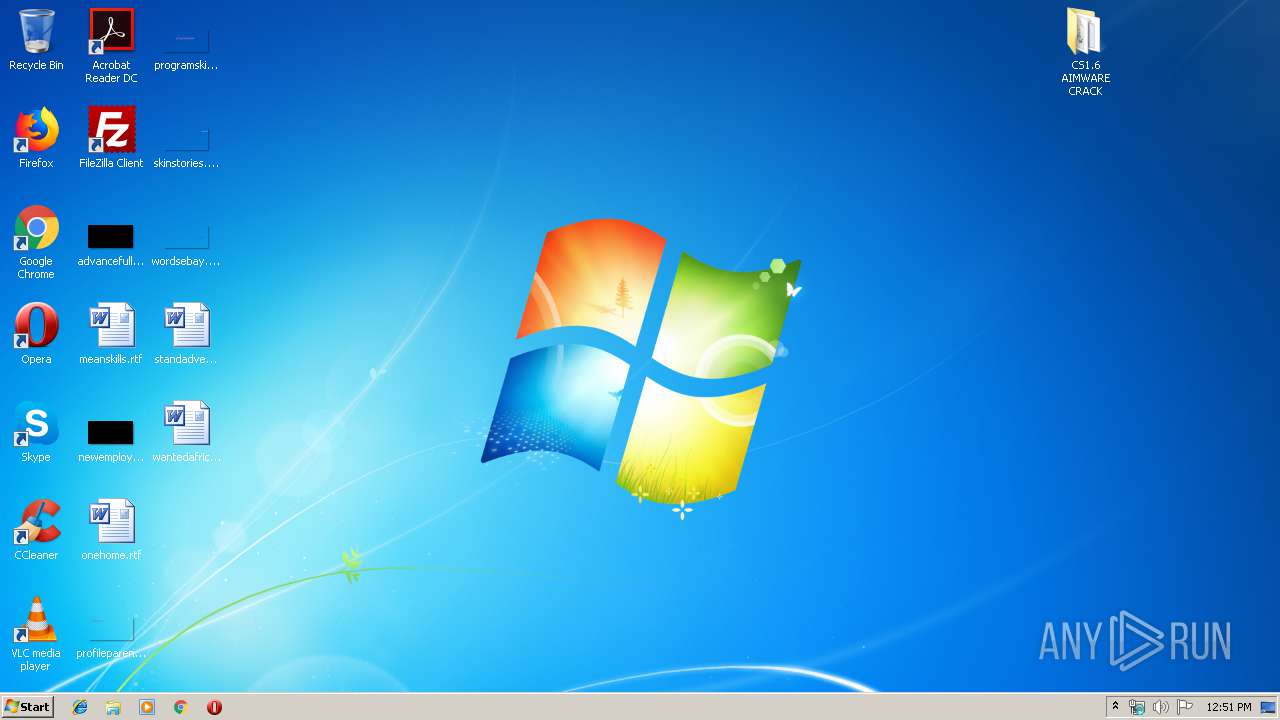
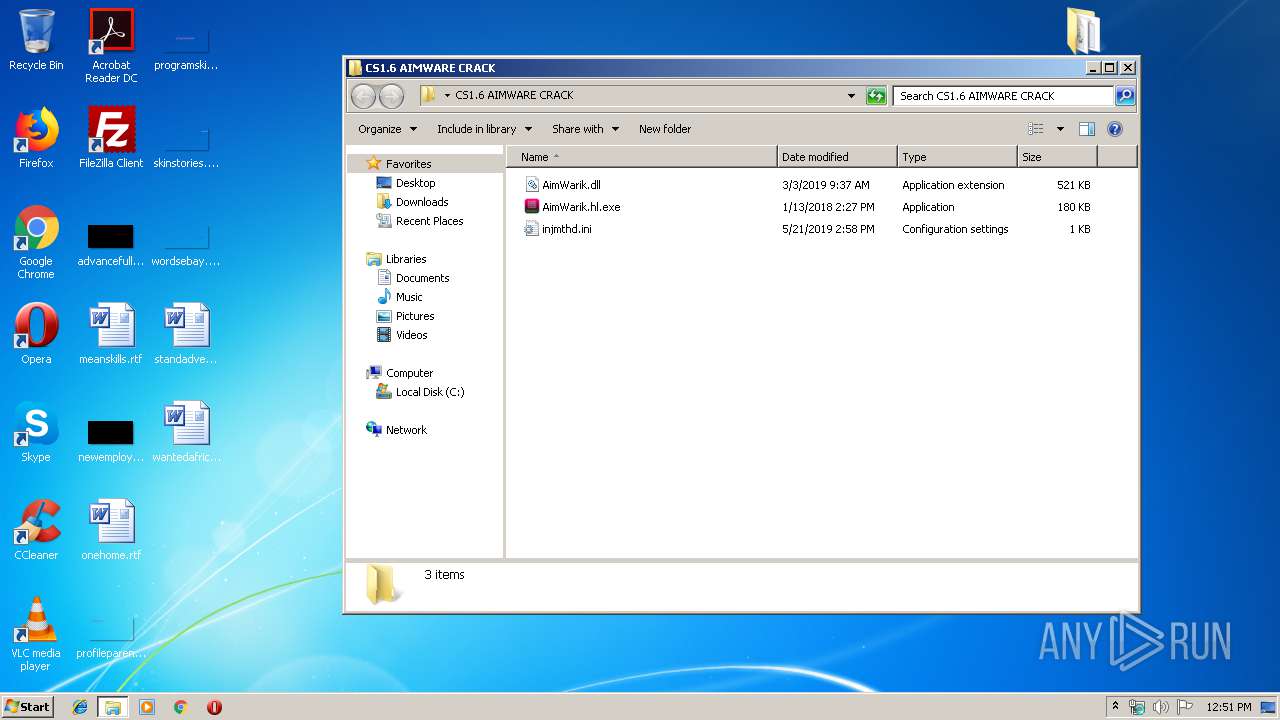
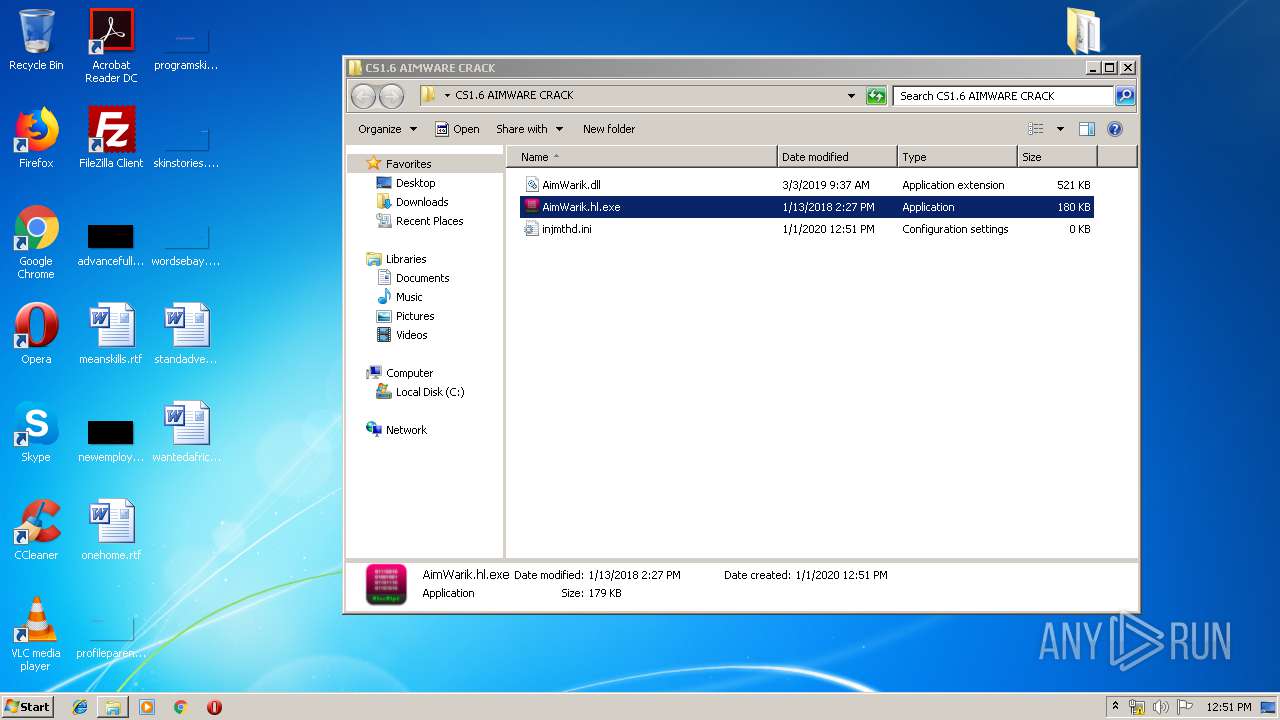
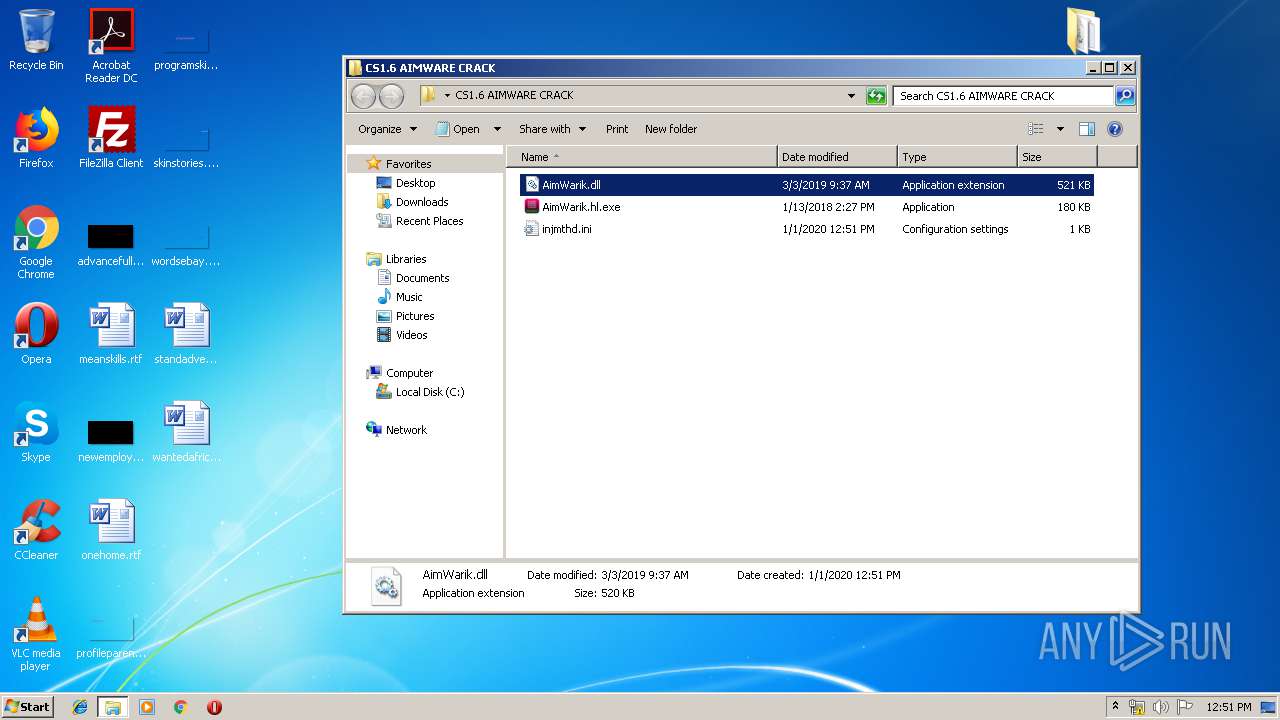
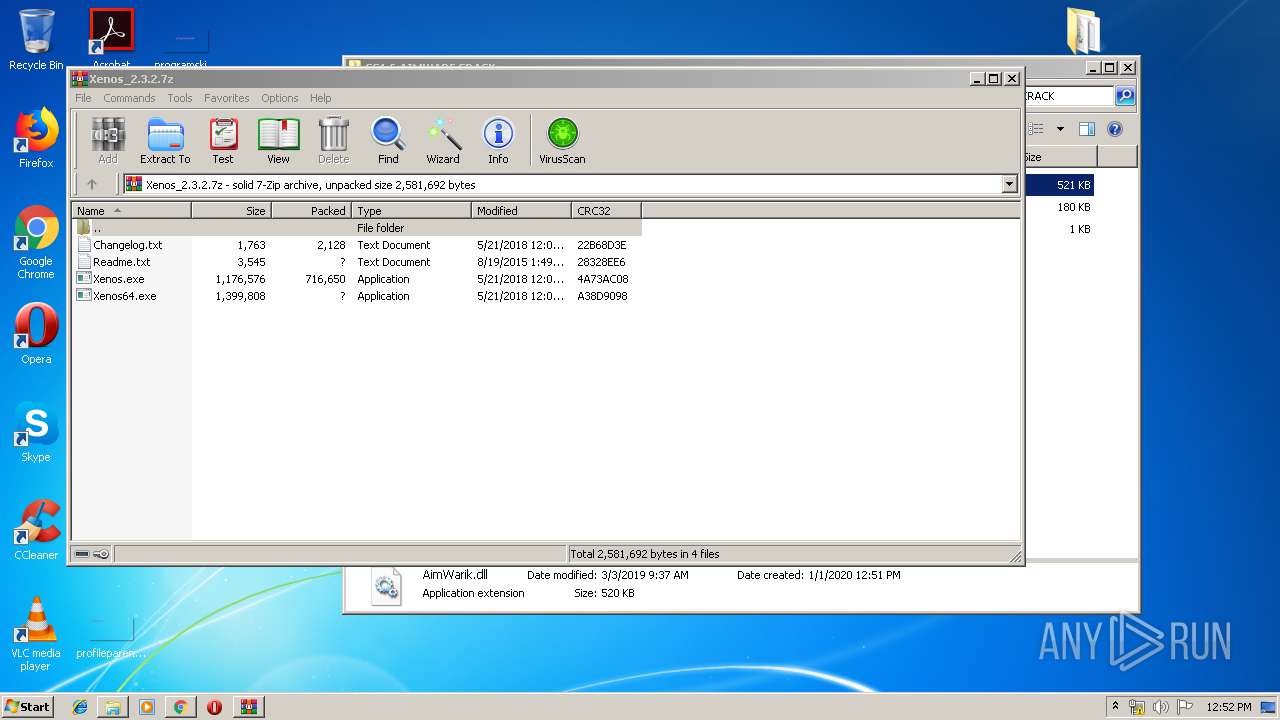
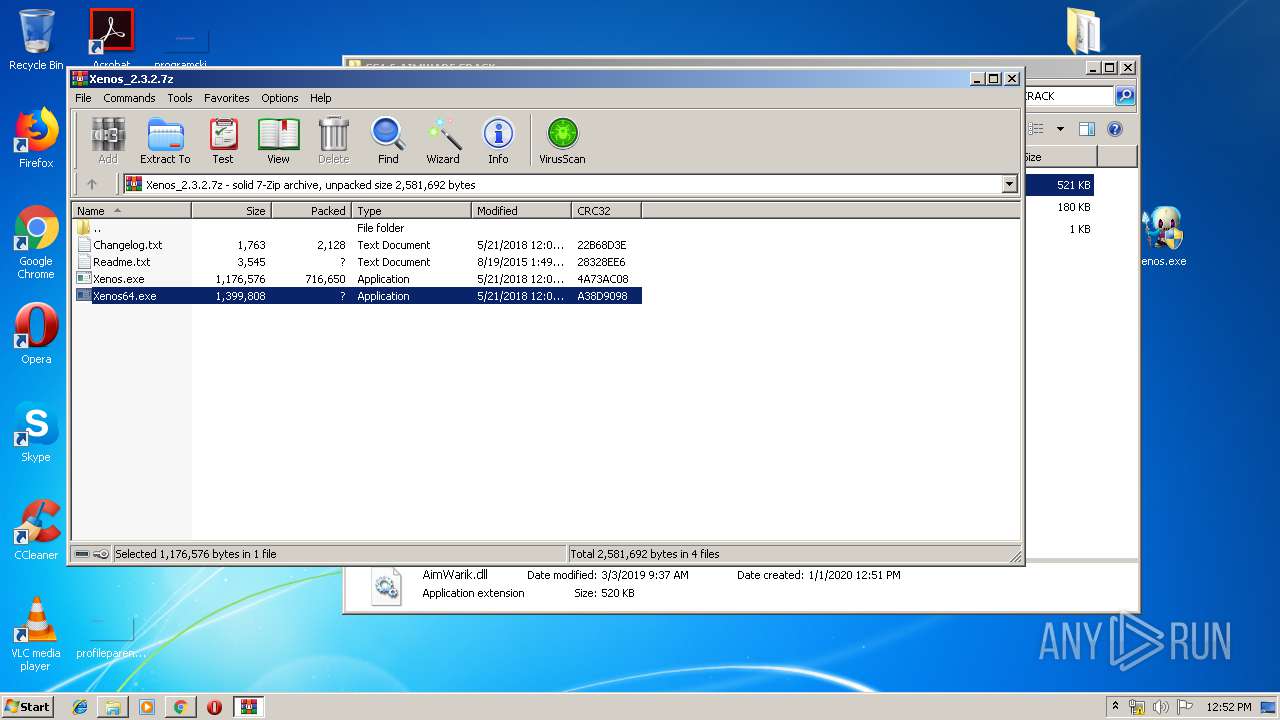
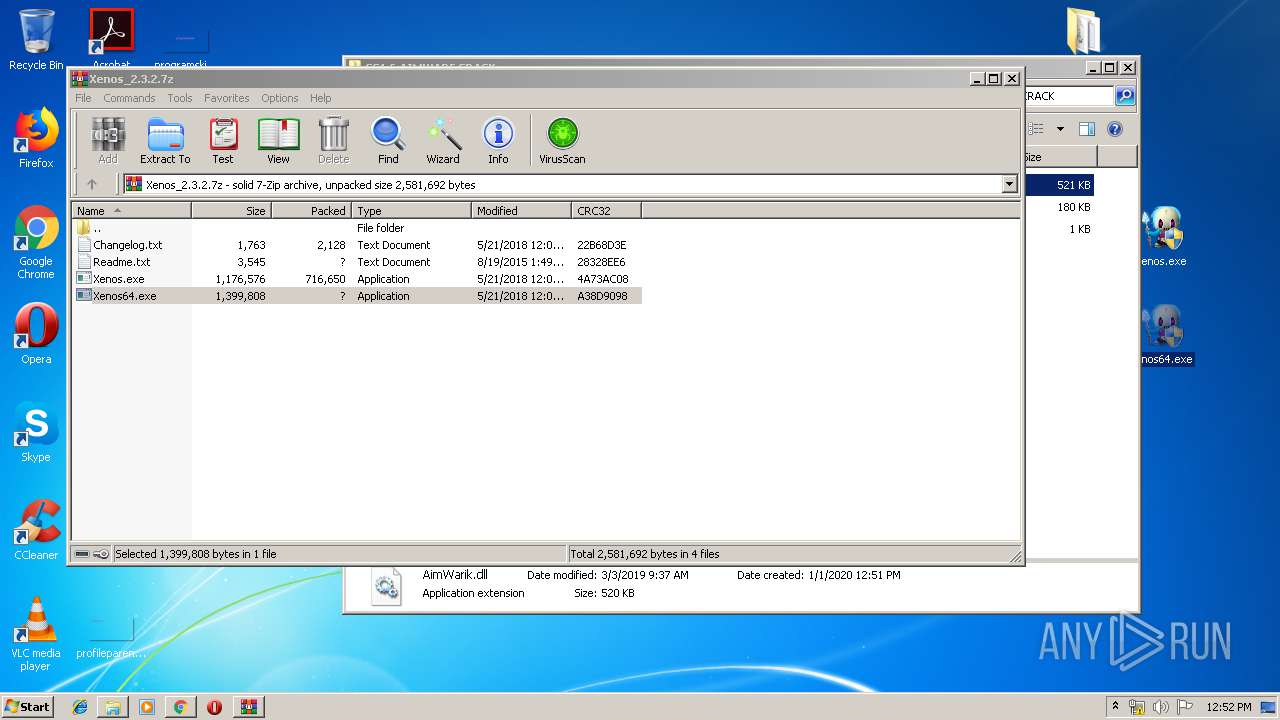
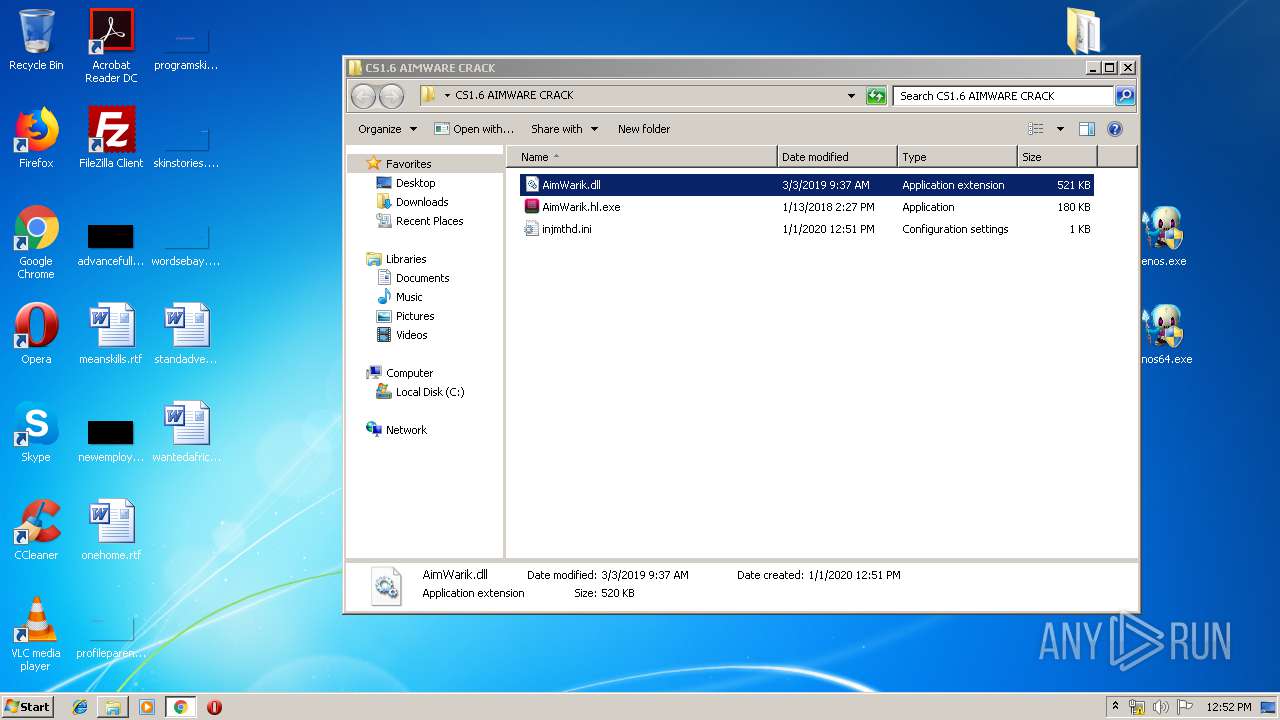
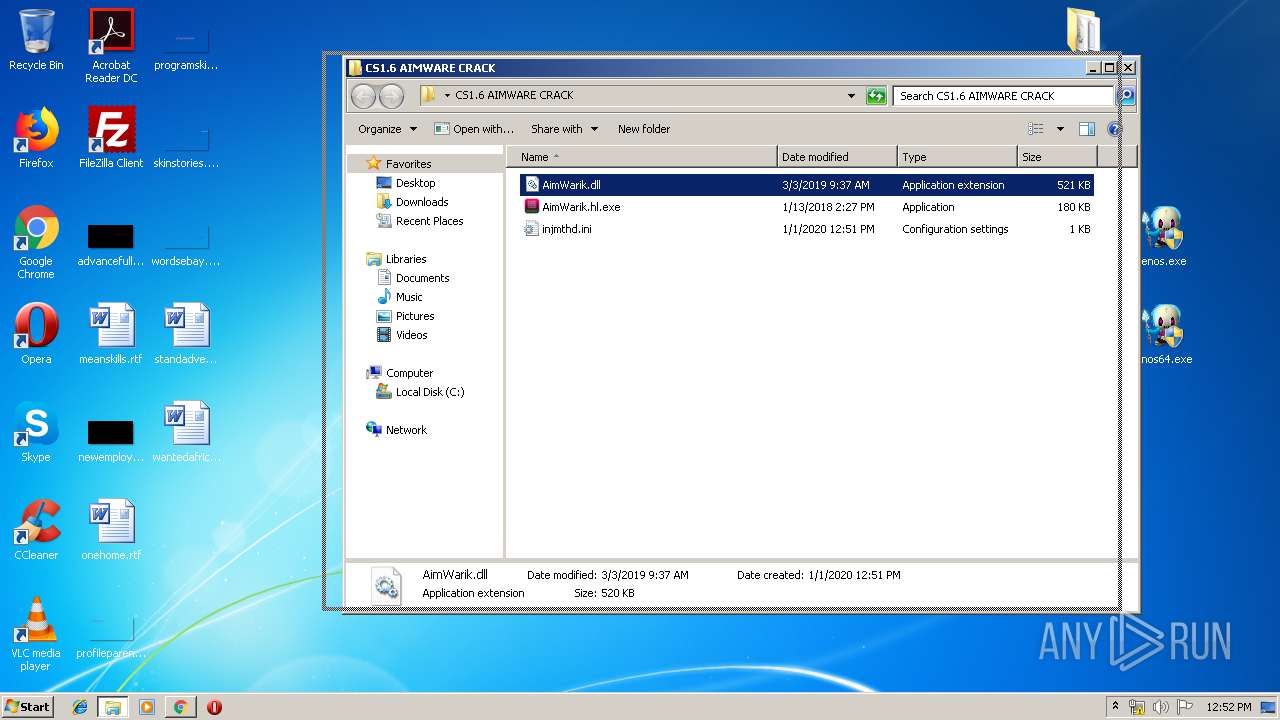
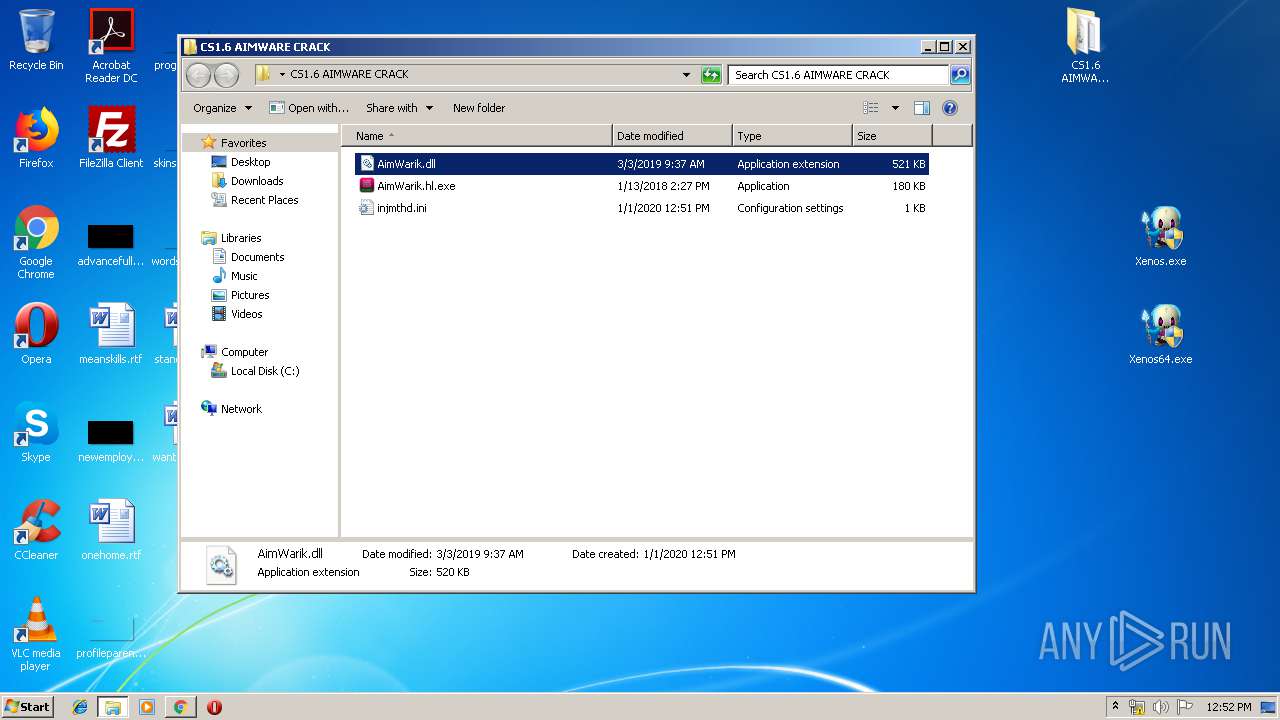
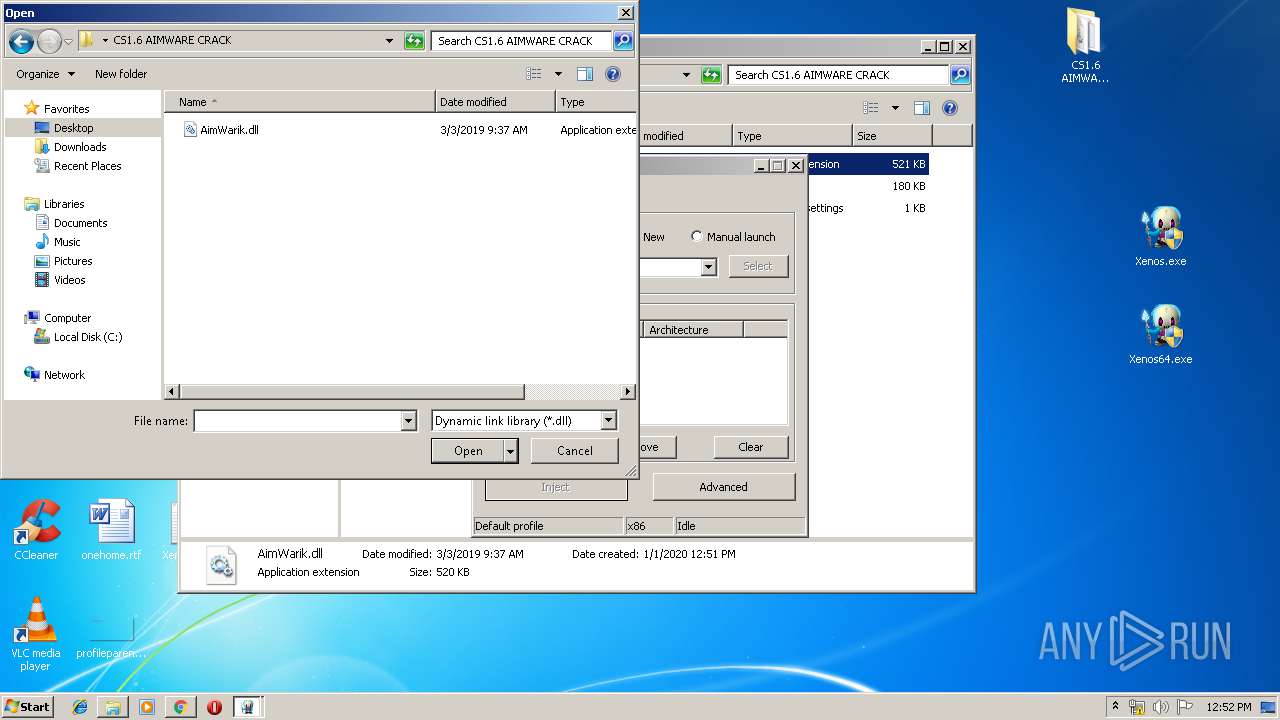
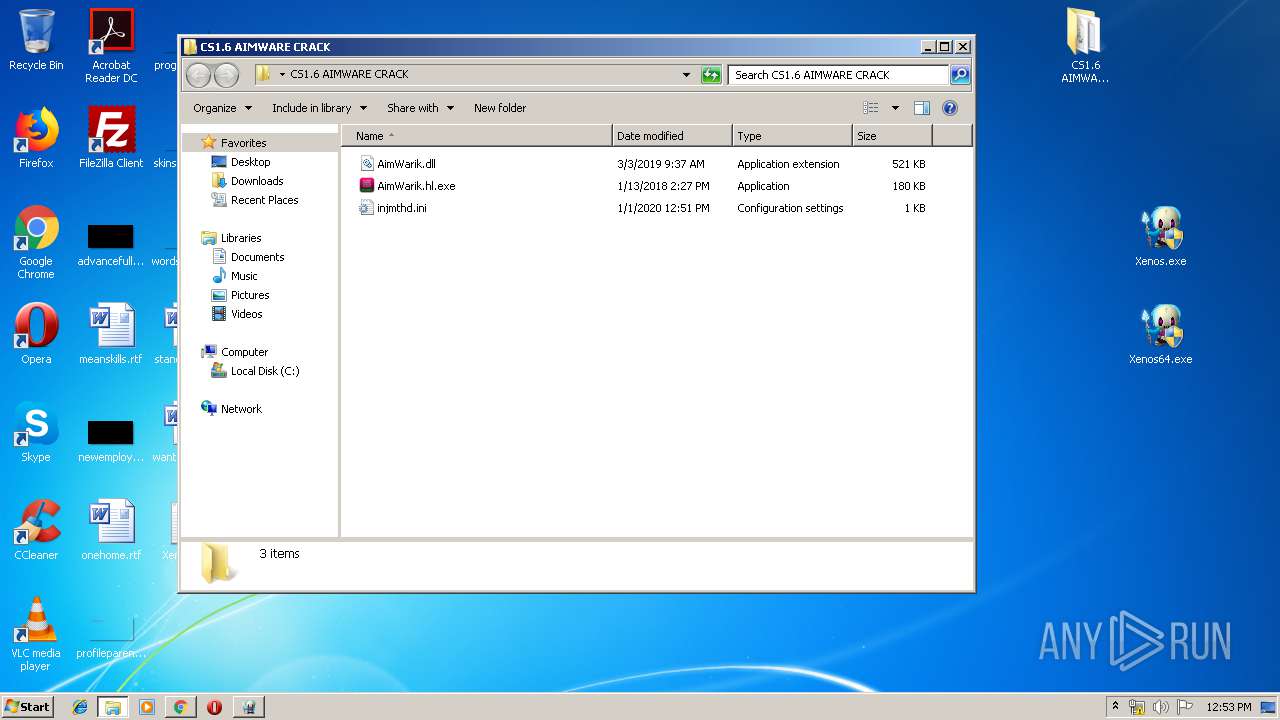
Application was dropped or rewritten from another process
- AimWarik.hl.exe (PID: 3484)
- Xenos.exe (PID: 2992)
- Xenos.exe (PID: 1944)
- Xenosmgr.exe (PID: 2752)
- Xenosmgr.exe (PID: 2540)
RAMNIT was detected
- iexplore.exe (PID: 2204)
Writes to a start menu file
- iexplore.exe (PID: 2204)
Connects to CnC server
- iexplore.exe (PID: 2204)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2160)
- iexplore.exe (PID: 2204)
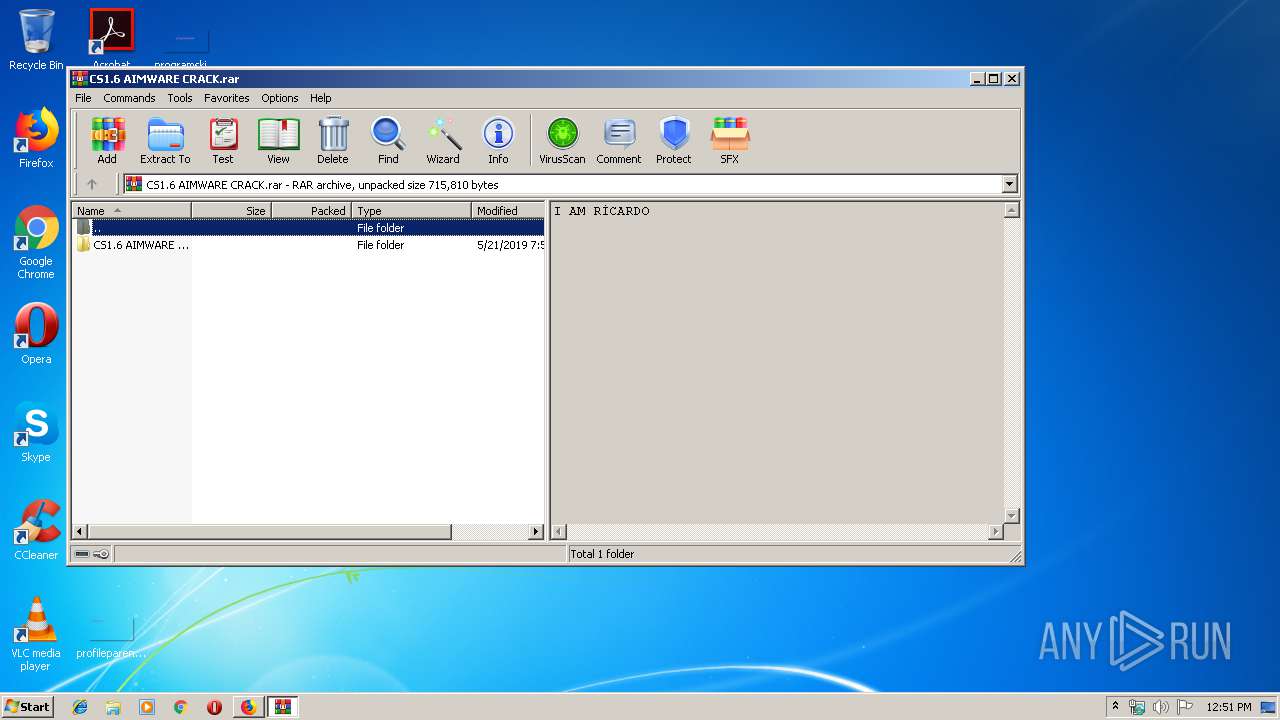
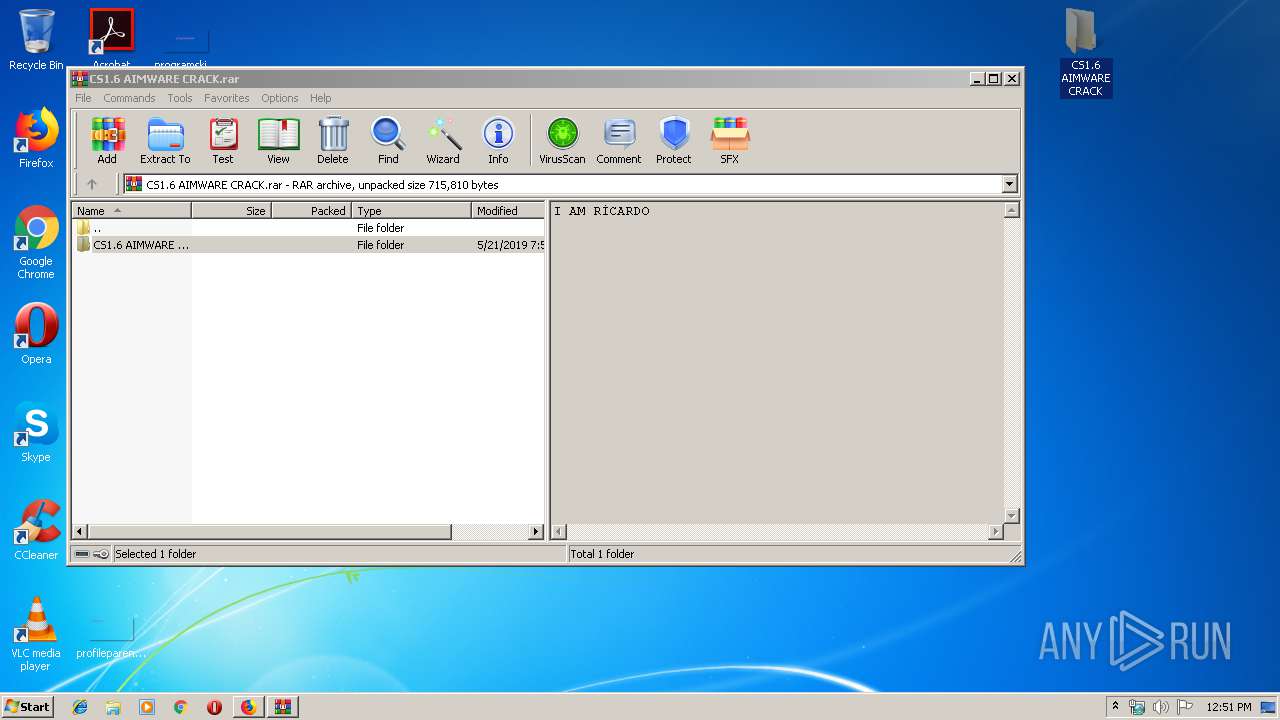
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3684)
- explorer.exe (PID: 352)
- Xenos.exe (PID: 1944)
- iexplore.exe (PID: 2204)
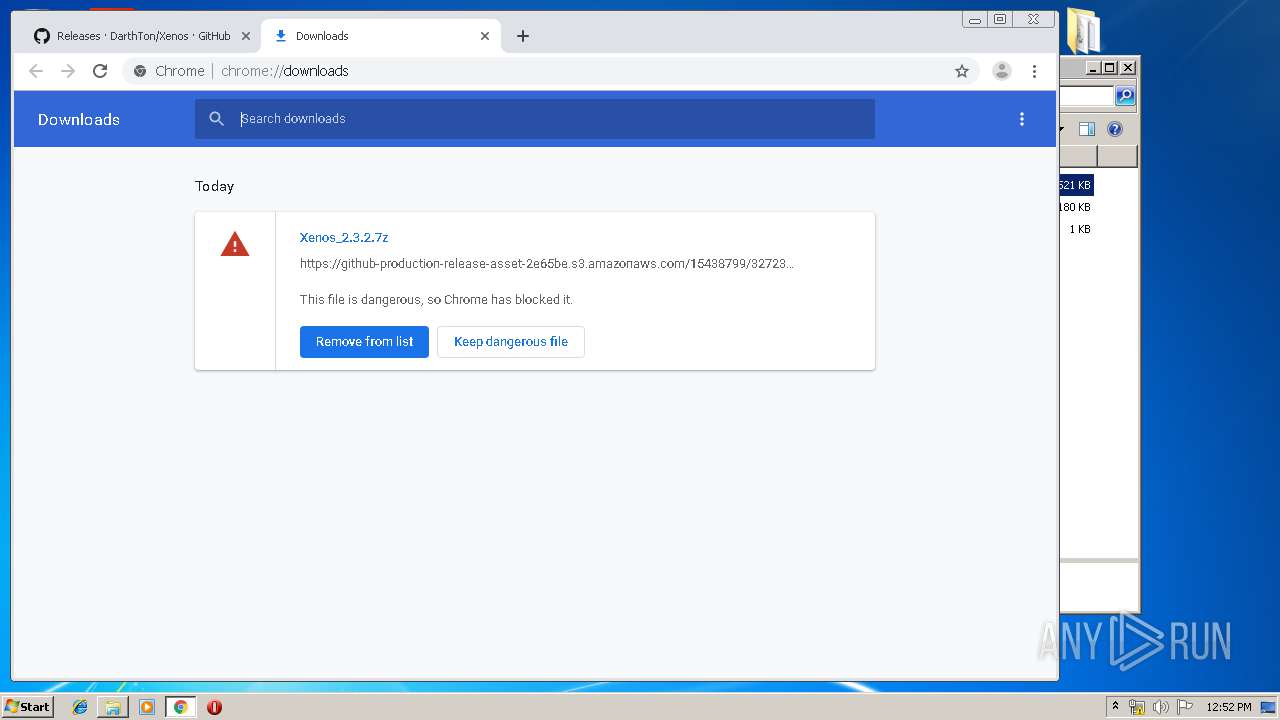
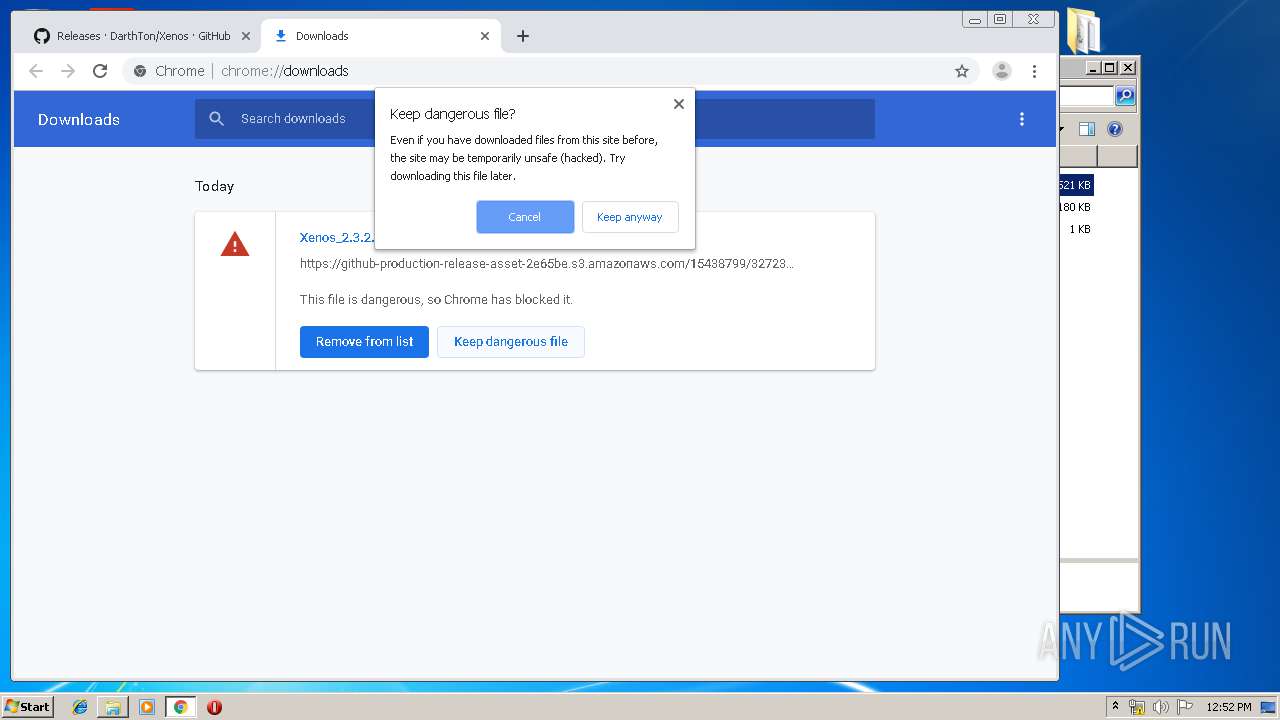
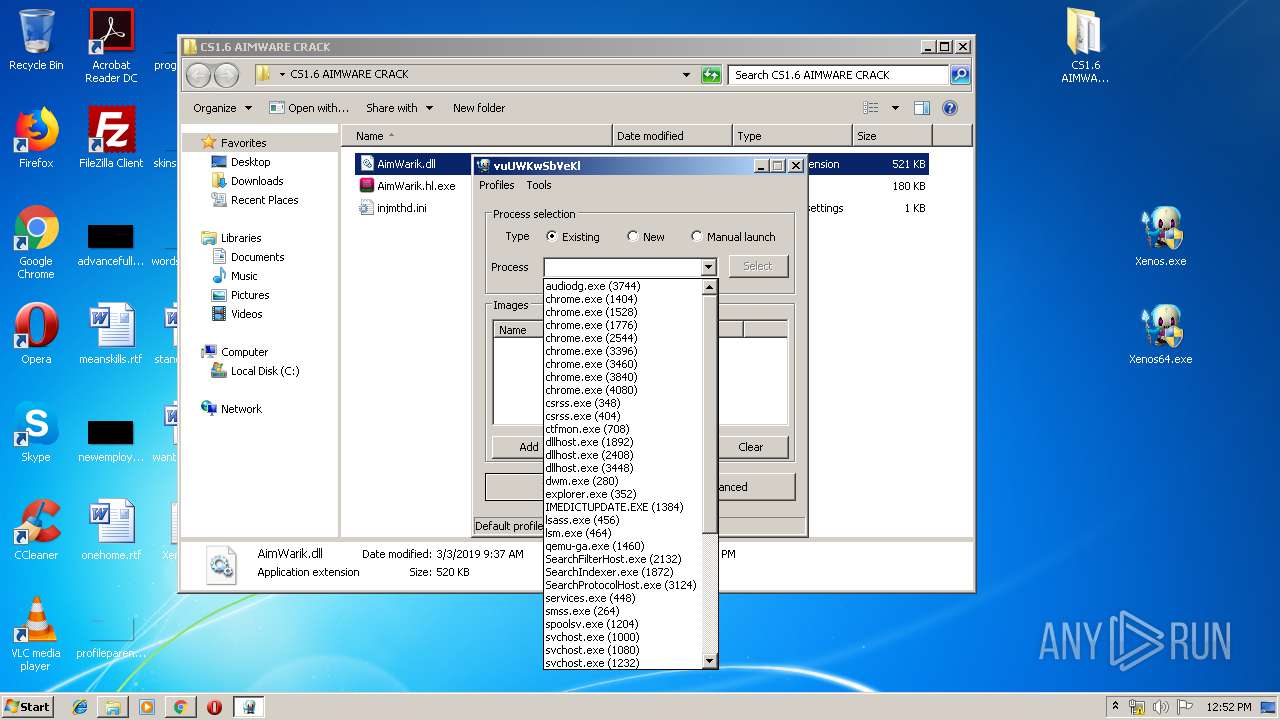
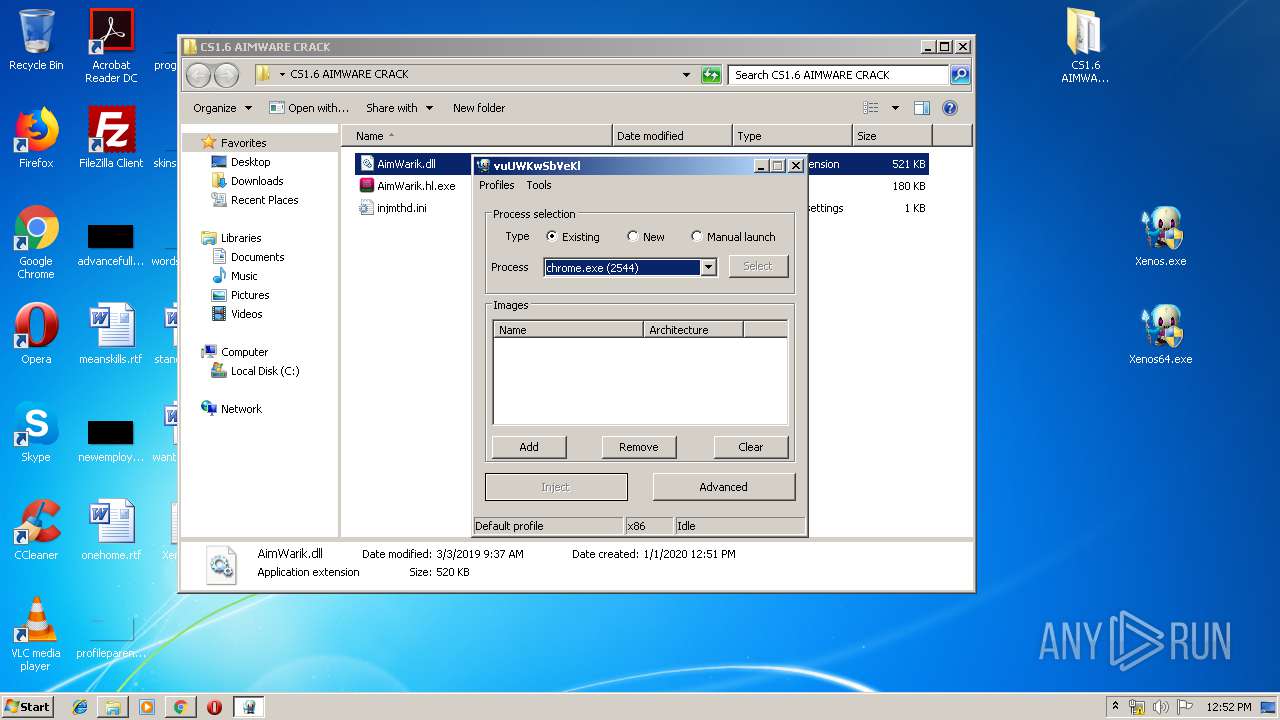
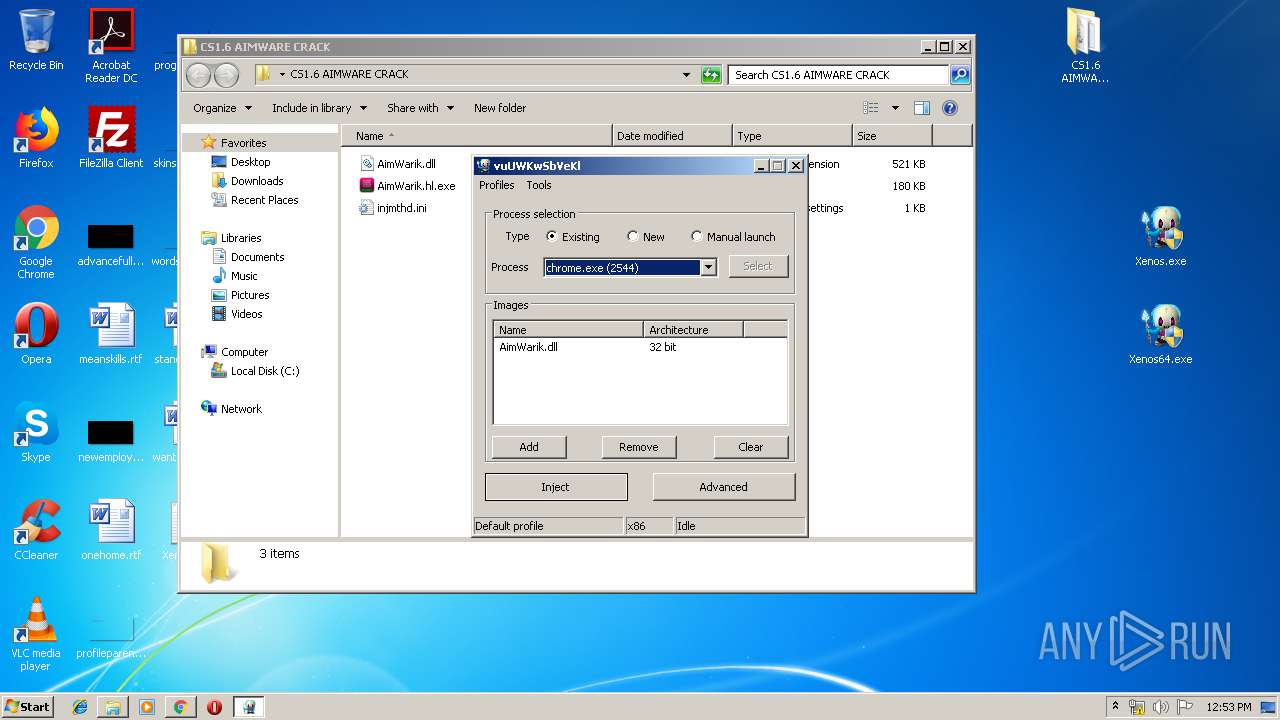
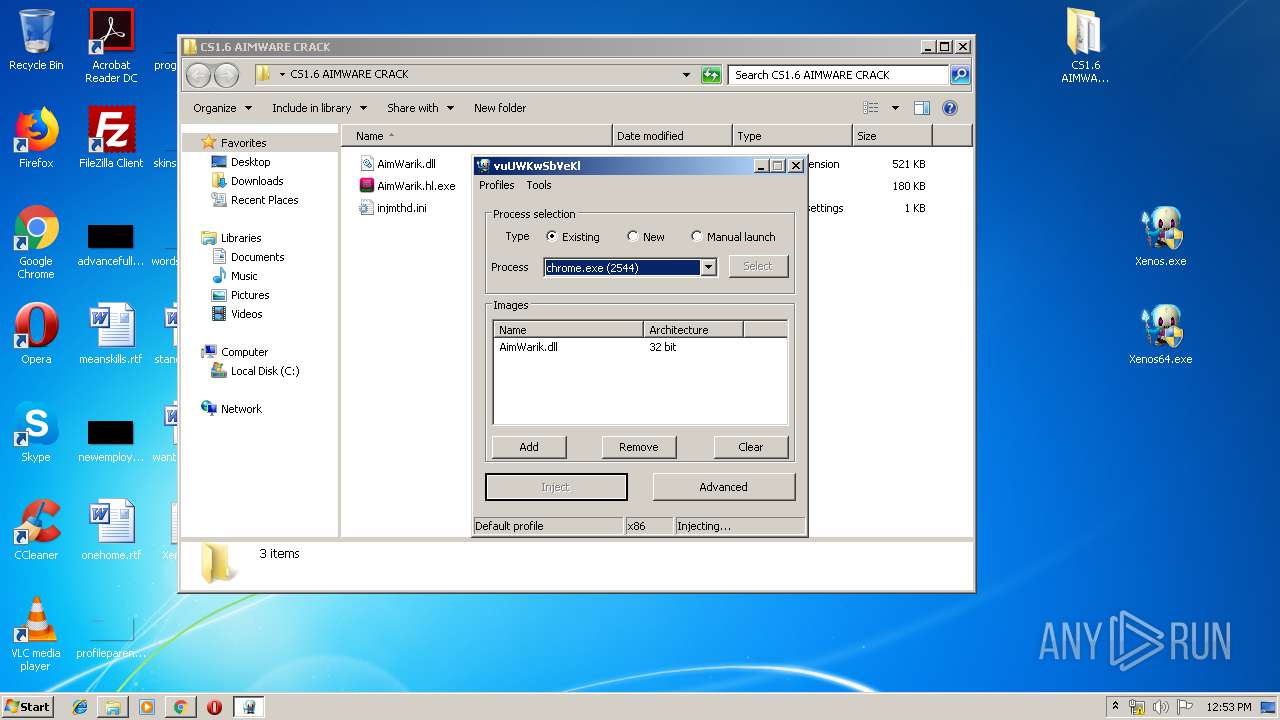
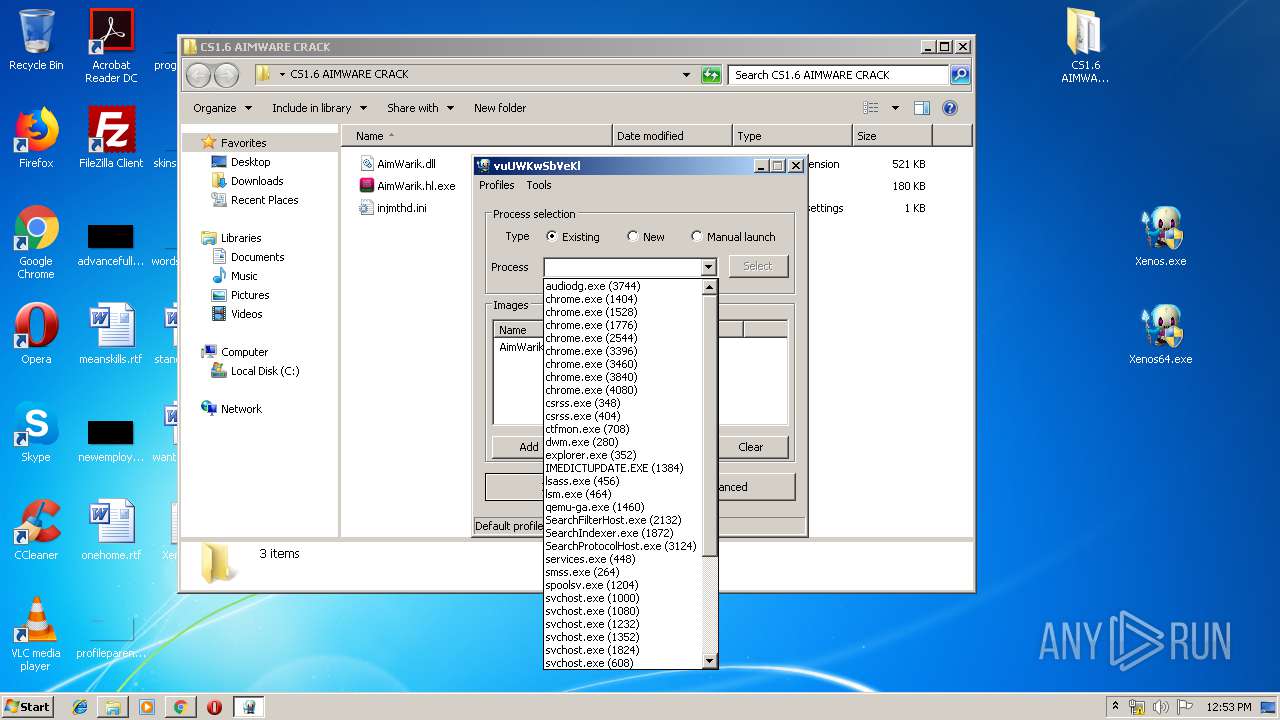
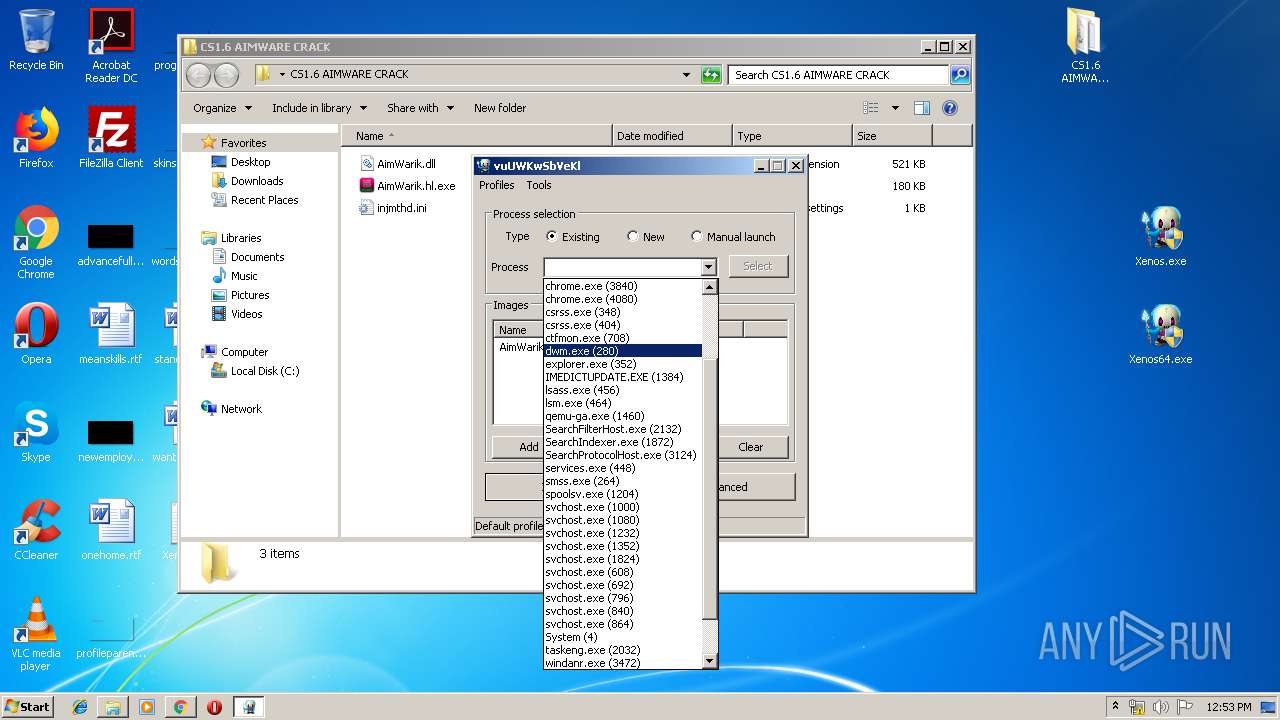
Modifies files in Chrome extension folder
- chrome.exe (PID: 1404)
Creates files in the user directory
- explorer.exe (PID: 352)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
Starts Internet Explorer
- Xenosmgr.exe (PID: 2752)
- Xenosmgr.exe (PID: 2540)
INFO
Application launched itself
- firefox.exe (PID: 2236)
- firefox.exe (PID: 2160)
- chrome.exe (PID: 1404)
Reads CPU info
- firefox.exe (PID: 2160)
Creates files in the user directory
- firefox.exe (PID: 2160)
- iexplore.exe (PID: 2204)
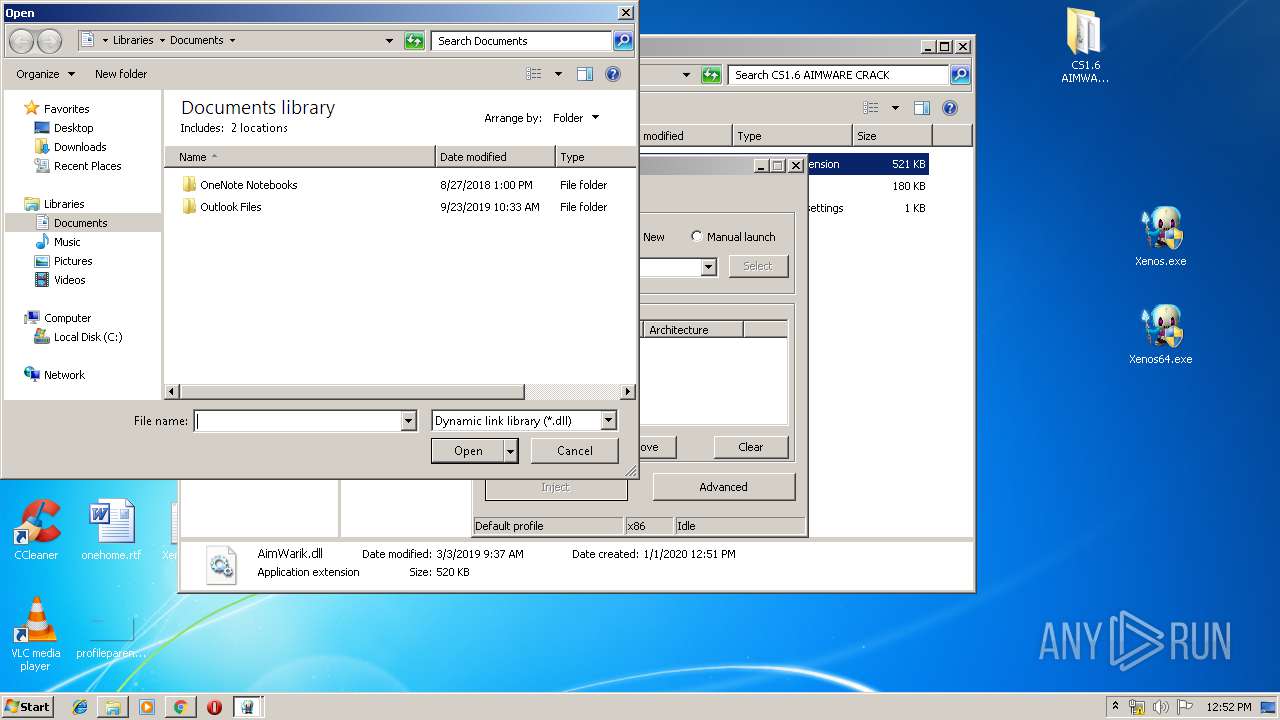
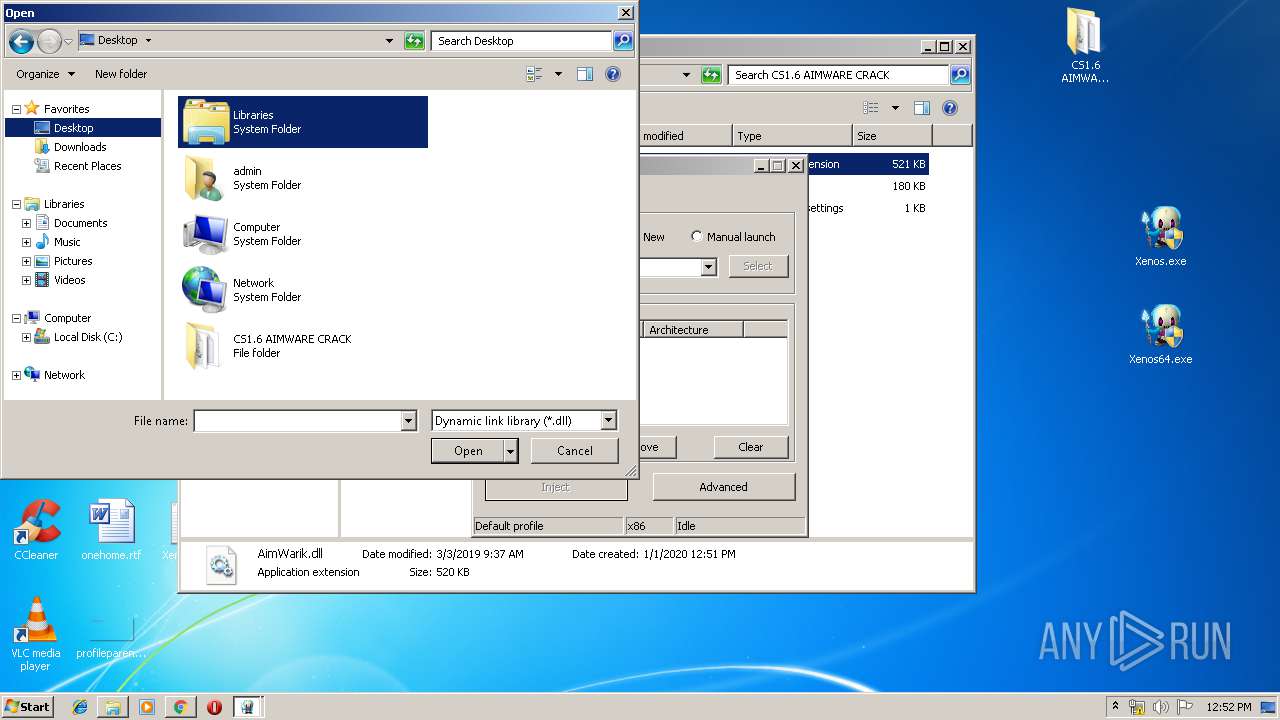
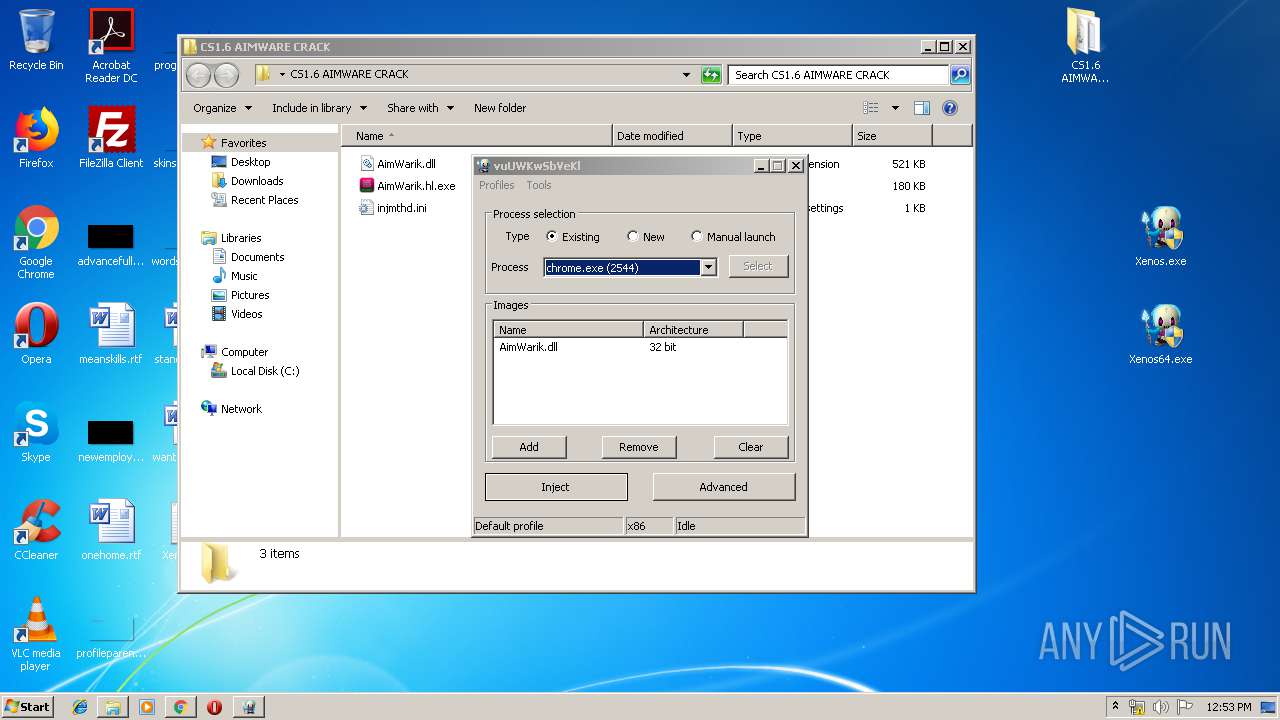
Manual execution by user
- AimWarik.hl.exe (PID: 3484)
Reads the hosts file
- chrome.exe (PID: 1404)
- chrome.exe (PID: 3840)
Reads settings of System Certificates
- chrome.exe (PID: 3840)
Reads Internet Cache Settings
- chrome.exe (PID: 1404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
98
Monitored processes
52
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 408 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2160.20.1121468363\1739466508" -childID 3 -isForBrowser -prefsHandle 3912 -prefMapHandle 3928 -prefsLen 7129 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2160 "\\.\pipe\gecko-crash-server-pipe.2160" 3936 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | Xenosmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1453166146419689479,11635882096823982310,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4244216430735957939 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1453166146419689479,11635882096823982310,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7443636802644147806 --mojo-platform-channel-handle=4276 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2108 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,1453166146419689479,11635882096823982310,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11546384266929969109 --mojo-platform-channel-handle=4048 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1453166146419689479,11635882096823982310,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13043321362106927834 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\Desktop\Xenos.exe" | C:\Users\admin\Desktop\Xenos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PE injector Exit code: 0 Version: 2.3.2.0 Modules
| |||||||||||||||
Total events
10 850
Read events
10 367
Write events
474
Delete events
9
Modification events
| (PID) Process: | (2160) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: FB32B60D03000000 | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 4FA2B20D03000000 | |||
| (PID) Process: | (2160) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 00000000090000000E000000CC190500000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605D425CD146D50100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000310000003800000037B91200090000000E000000CC19050033003000380030003400360042003000410046003400410033003900430042000000000060E4E700CDDE51742DAC977714E3E700F0DE5174D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000C065897506002A02F7000000000000000000D172ACE4E700EBE7E70050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000F10003003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172380A0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800B831120266D28875380A0000000000006A2C6877B8311202A8E5E700973C68779C3C6877FDAD9777B83112026A2C68770000000000000000FFFFFFFF0000000000000000A2100000E0E5E700E3610C763053280100000000EF610C761D91E1E300000000A210000000000000B8E5E70011000000B8452B00B0452B007CE6E70002000000A0F80A0420E707042066280058E600006A91E1E30CE6E70082916C7658E6E70010E6E70027956C76000000008C00FD0338E6E700CD946C768C00FD0300FCFC03DCE6E700E1946C760000000000FCFC03DCE6E70040E6E700090000000E000000CC19050033003000380030003400360042003000410046003400410033003900430042000000000060E4E700CDDE51742DAC977714E3E700F0DE5174D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000C065897506002A02F7000000000000000000D172ACE4E700EBE7E70050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000F10003003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172380A0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800B831120266D28875380A0000000000006A2C6877B8311202A8E5E700973C68779C3C6877FDAD9777B83112026A2C68770000000000000000FFFFFFFF0000000000000000A2100000E0E5E700E3610C763053280100000000EF610C761D91E1E300000000A210000000000000B8E5E70011000000B8452B00B0452B007CE6E70002000000A0F80A0420E707042066280058E600006A91E1E30CE6E70082916C7658E6E70010E6E70027956C76000000008C00FD0338E6E700CD946C768C00FD0300FCFC03DCE6E700E1946C760000000000FCFC03DCE6E70040E6E700090000000E000000CC19050033003000380030003400360042003000410046003400410033003900430042000000000060E4E700CDDE51742DAC977714E3E700F0DE5174D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000C065897506002A02F7000000000000000000D172ACE4E700EBE7E70050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000F10003003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172380A0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800B831120266D28875380A0000000000006A2C6877B8311202A8E5E700973C68779C3C6877FDAD9777B83112026A2C68770000000000000000FFFFFFFF0000000000000000A2100000E0E5E700E3610C763053280100000000EF610C761D91E1E300000000A210000000000000B8E5E70011000000B8452B00B0452B007CE6E70002000000A0F80A0420E707042066280058E600006A91E1E30CE6E70082916C7658E6E70010E6E70027956C76000000008C00FD0338E6E700CD946C768C00FD0300FCFC03DCE6E700E1946C760000000000FCFC03DCE6E70040E6E700 | |||
| (PID) Process: | (2160) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2160) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000310000003800000037B91200090000000E000000CC190500330030003800300034003600420030004100460034004100330039004300420000003900430042000000000060E4E700CDDE51742DAC977714E3E700F0DE5174D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000C065897506002A02F7000000000000000000D172ACE4E700EBE7E70050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000010102003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172380A0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800B83112020000000098ED130290EC130202000000A0F80A0420E70704206628000E0002007900000055000000050000000000FFFF7800000028E707044700000004000000307D280045000000000000000E000000E0160B0450E6E70047436977A0F80A0428020000C8030000E72F687711000000B8452B00B0452B00000028000D0047007900000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700090000000E000000CC190500330030003800300034003600420030004100460034004100330039004300420000003900430042000000000060E4E700CDDE51742DAC977714E3E700F0DE5174D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000C065897506002A02F7000000000000000000D172ACE4E700EBE7E70050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000010102003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172380A0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800B83112020000000098ED130290EC130202000000A0F80A0420E70704206628000E0002007900000055000000050000000000FFFF7800000028E707044700000004000000307D280045000000000000000E000000E0160B0450E6E70047436977A0F80A0428020000C8030000E72F687711000000B8452B00B0452B00000028000D0047007900000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700090000000E000000CC190500330030003800300034003600420030004100460034004100330039004300420000003900430042000000000060E4E700CDDE51742DAC977714E3E700F0DE5174D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000C065897506002A02F7000000000000000000D172ACE4E700EBE7E70050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000010102003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172380A0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800B83112020000000098ED130290EC130202000000A0F80A0420E70704206628000E0002007900000055000000050000000000FFFF7800000028E707044700000004000000307D280045000000000000000E000000E0160B0450E6E70047436977A0F80A0428020000C8030000E72F687711000000B8452B00B0452B00000028000D0047007900000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700 | |||
| (PID) Process: | (2160) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2160) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
11
Suspicious files
220
Text files
316
Unknown types
154
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\6EC291A57FECD9A53AED7BD92A7D616FF9D68C46 | der | |
MD5:— | SHA256:— | |||
| 2160 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
123
DNS requests
168
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2160 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2160 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2160 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2160 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2160 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2160 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2160 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3840 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 511 b | whitelisted |
2160 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2160 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | firefox.exe | 195.201.111.49:443 | dosya.co | Awanti Ltd. | RU | suspicious |
2160 | firefox.exe | 2.16.106.152:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2160 | firefox.exe | 52.35.182.58:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2160 | firefox.exe | 2.21.242.204:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | NL | whitelisted |
2160 | firefox.exe | 54.213.229.100:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
2160 | firefox.exe | 54.68.132.173:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2160 | firefox.exe | 13.35.253.53:443 | snippets.cdn.mozilla.net | — | US | malicious |
2160 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2160 | firefox.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2160 | firefox.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dosya.co |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
a771.dscq.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
2204 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
2204 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
2204 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
2204 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
2204 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Banker Ramnit CnC Connection |
2204 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
2204 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
2204 | iexplore.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |