| File name: | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe |
| Full analysis: | https://app.any.run/tasks/699e4b81-1ab3-41b9-a5b3-7e63d48e97b2 |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | March 25, 2025, 00:01:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | D0074EDAB5CEE4B432BF2E9F075E6301 |
| SHA1: | 71A829B476596AD54566C823499B1BFDFA86AE3E |
| SHA256: | 0FF51F1BFCEF0CABF76AF8A2C9BB5C01AEF4940A97C9B5CEBE83CDDF62D5BE77 |
| SSDEEP: | 24576:9G3VZ4D6o/QBl6tmlUc/TqCWIgA1QLQjzt:E3VZ4D6o/QBl6tmlUc/TqCWIgA1QLQjx |
MALICIOUS
GULOADER has been found (auto)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
SNAKEKEYLOGGER has been detected (SURICATA)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
Steals credentials from Web Browsers
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
Actions looks like stealing of personal data
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- certutil.exe (PID: 8444)
- HTTPDebuggerSvc.exe (PID: 4880)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
SUSPICIOUS
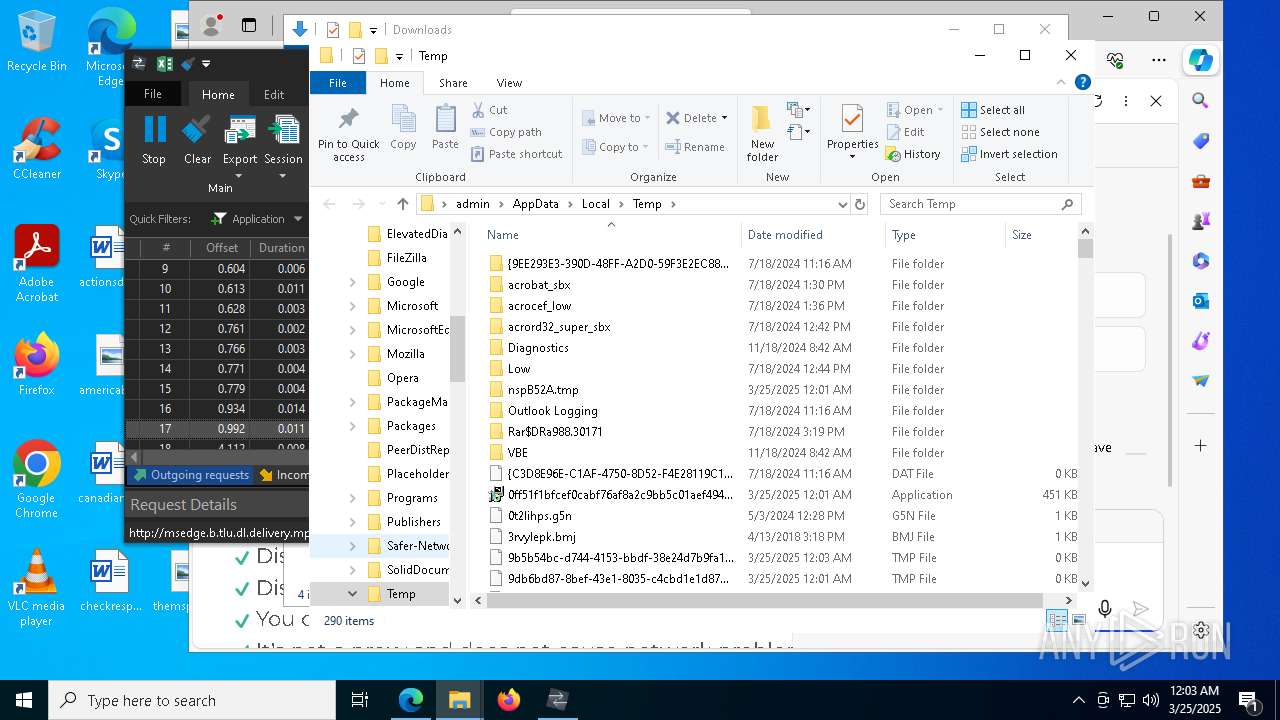
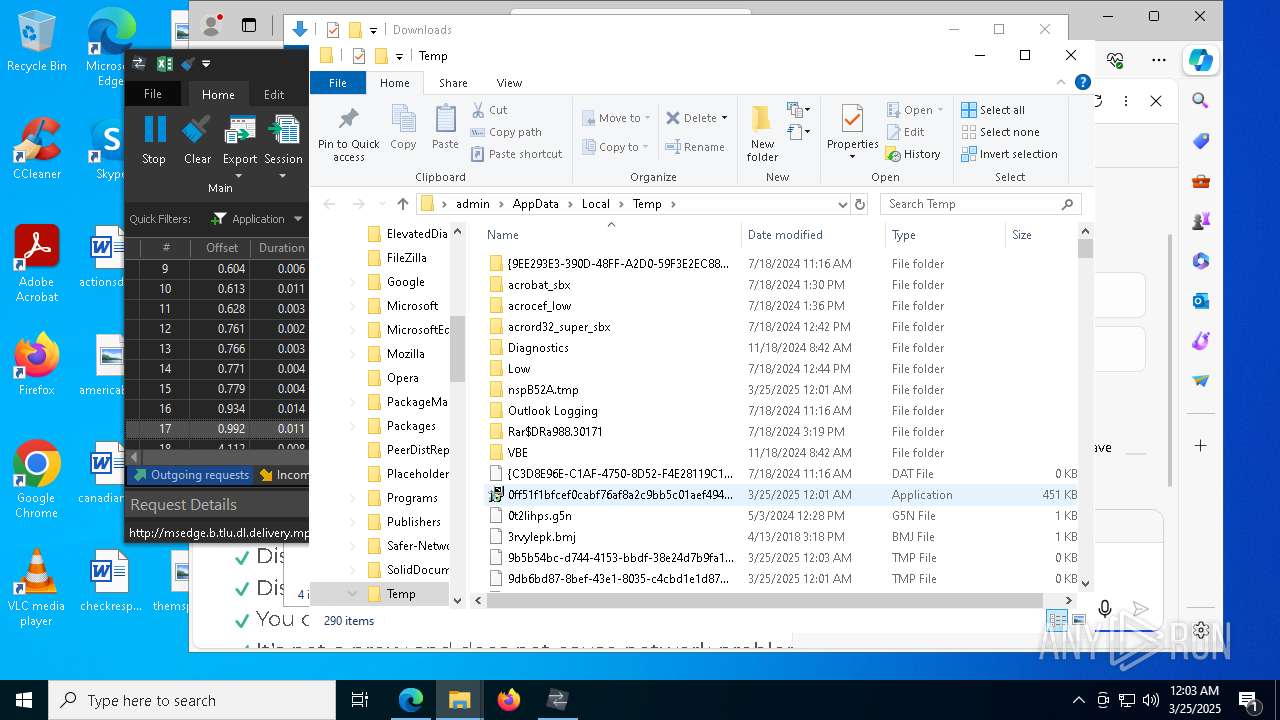
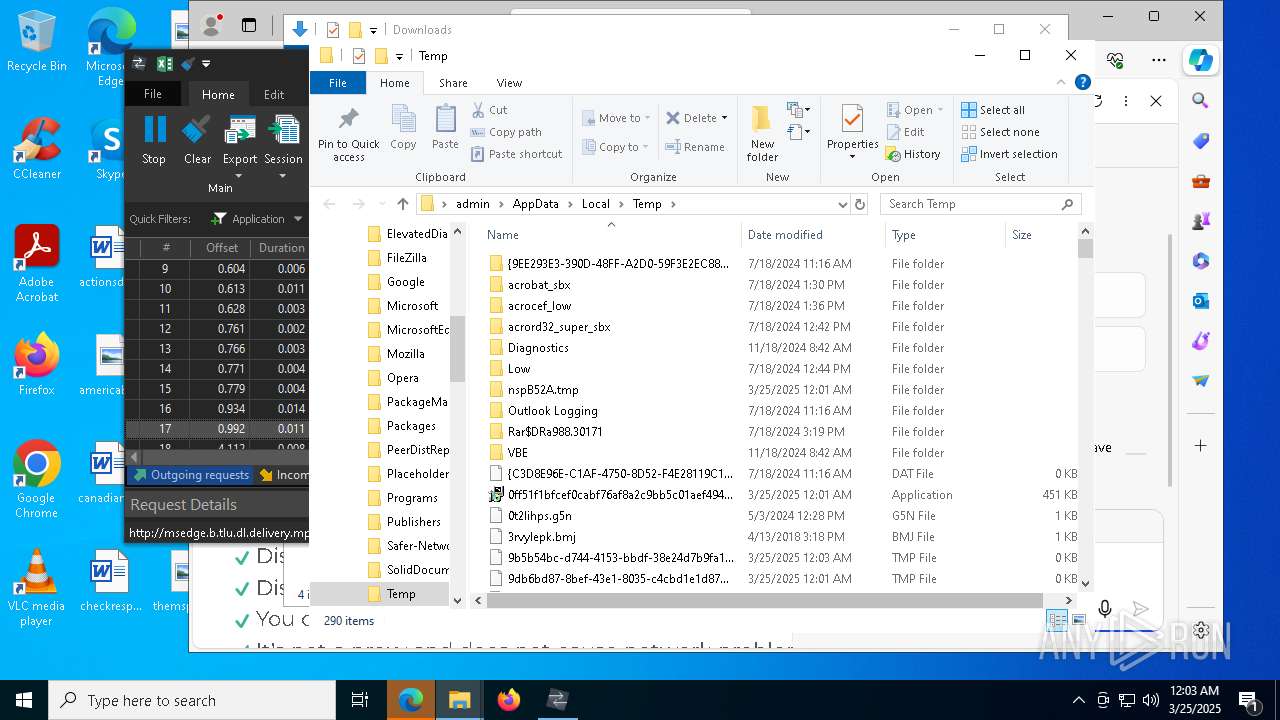
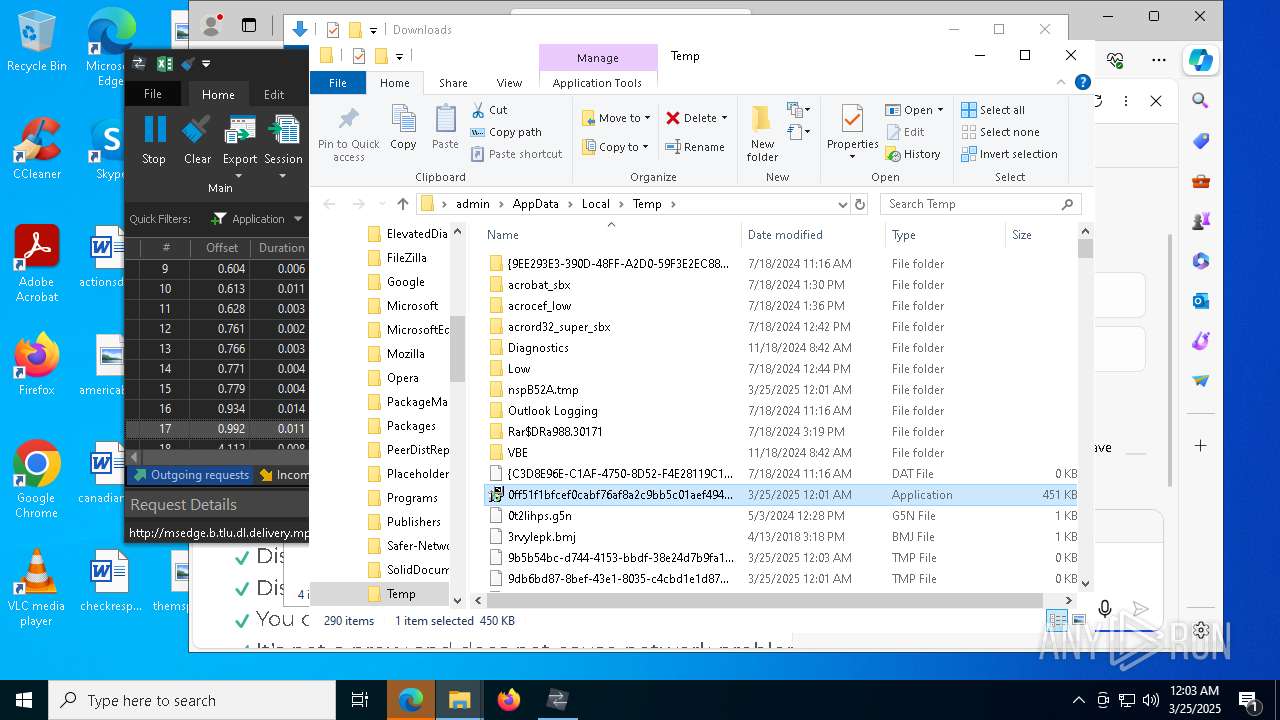
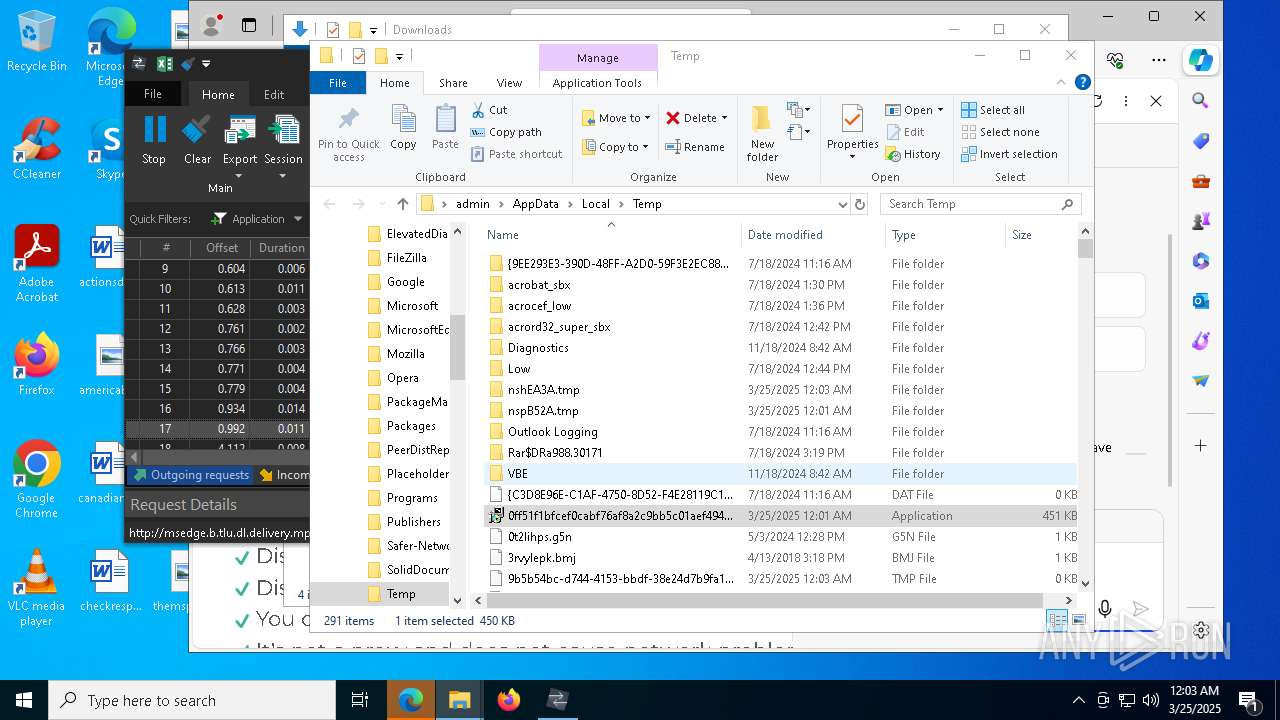
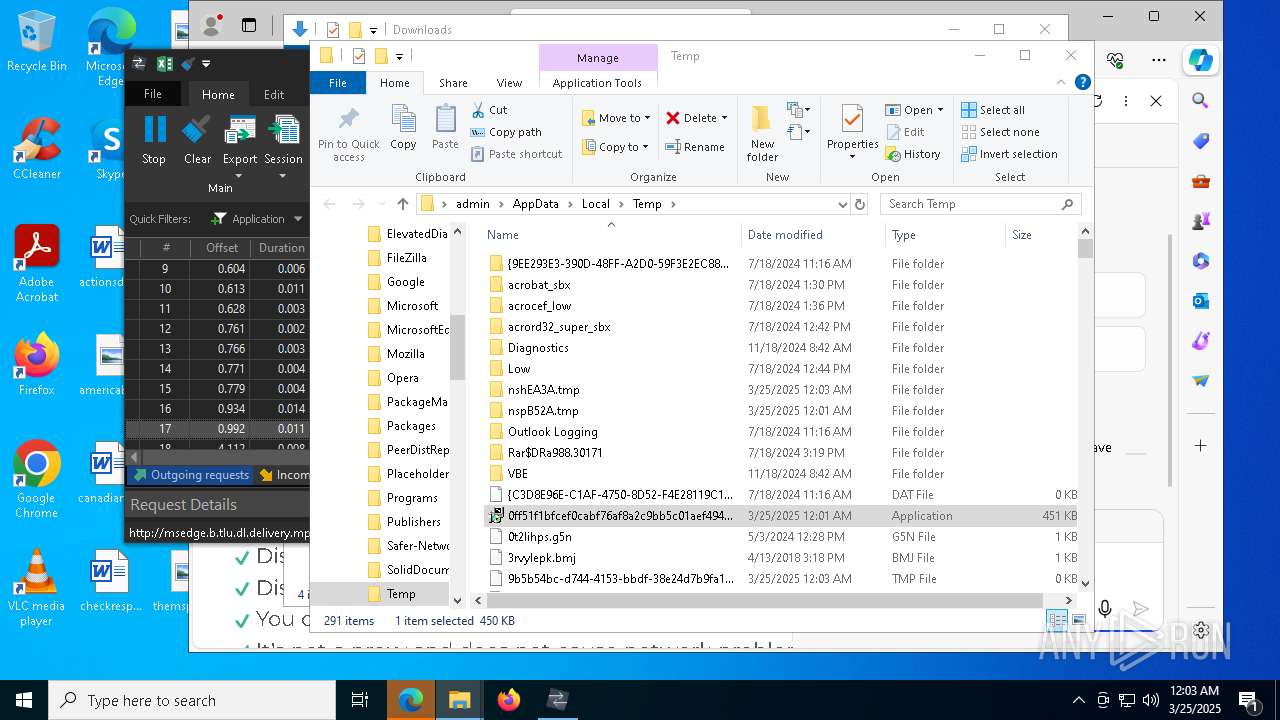
The process creates files with name similar to system file names
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
- msiexec.exe (PID: 8764)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6300)
Executable content was dropped or overwritten
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
- HTTPDebuggerSvc.exe (PID: 4880)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6300)
Malware-specific behavior (creating "System.dll" in Temp)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6300)
Application launched itself
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6300)
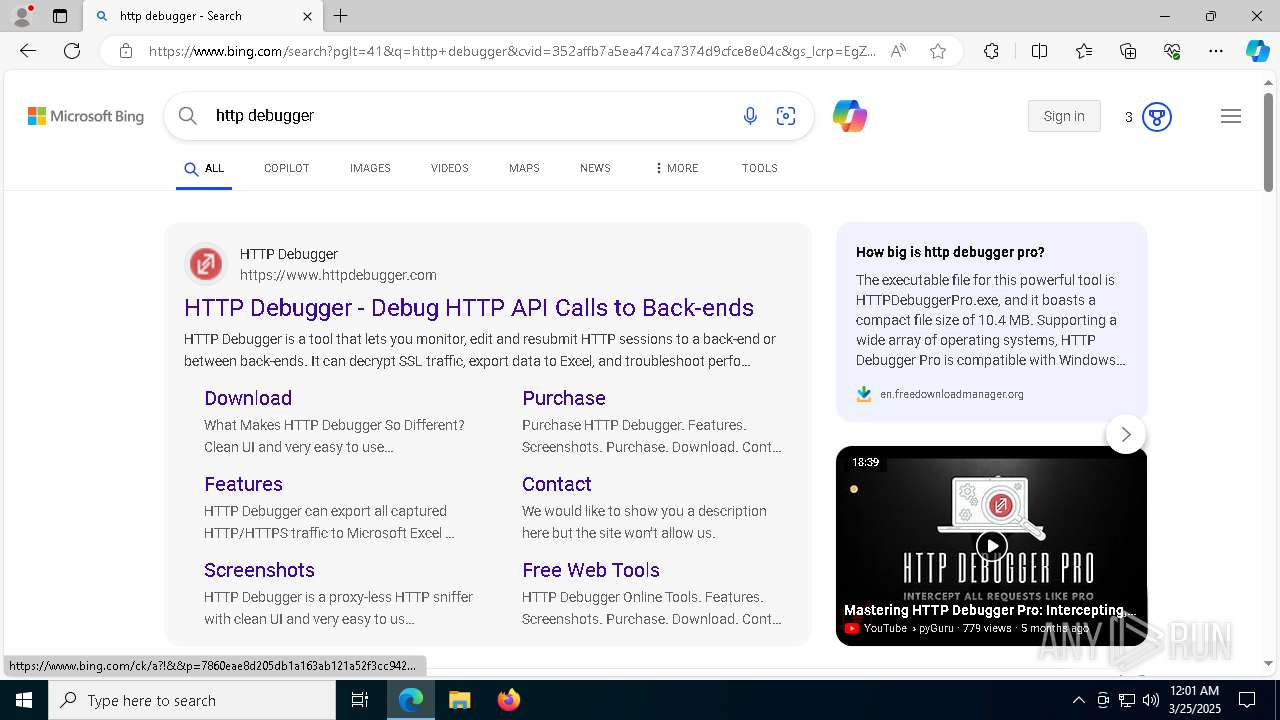
Reads security settings of Internet Explorer
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- HTTPDebuggerUI.exe (PID: 9124)
- ShellExperienceHost.exe (PID: 8244)
- msiexec.exe (PID: 8808)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
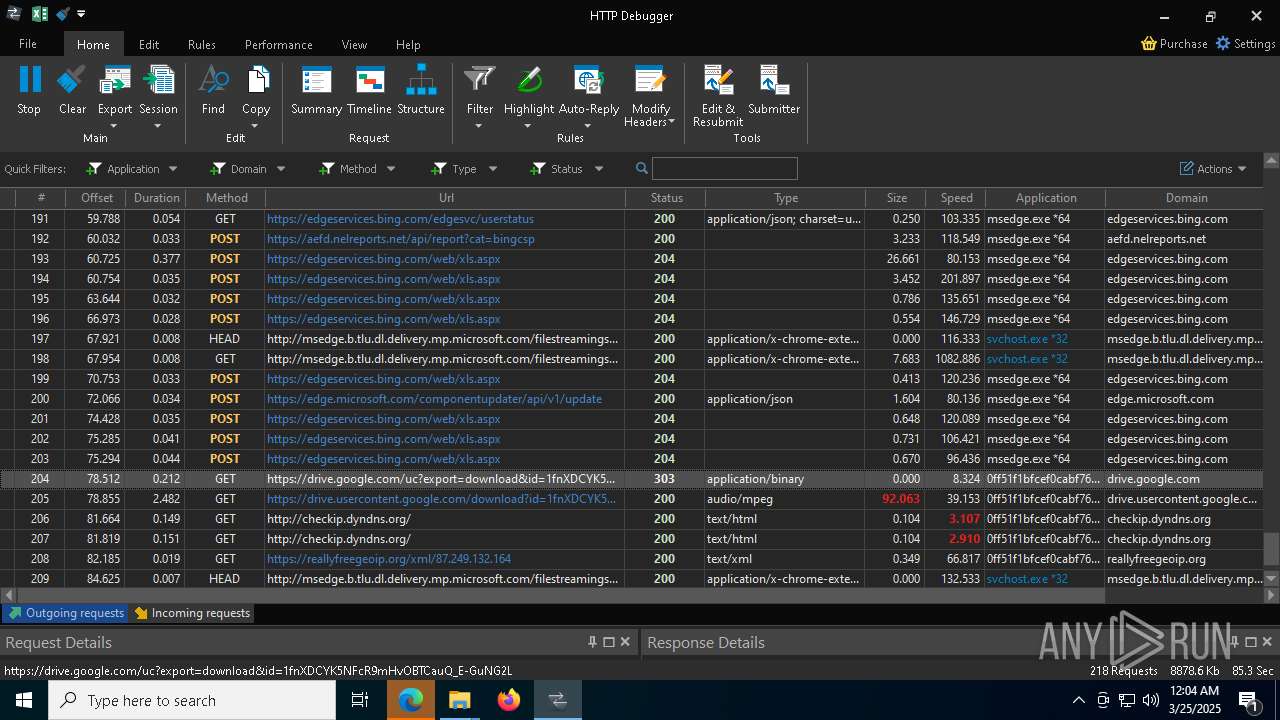
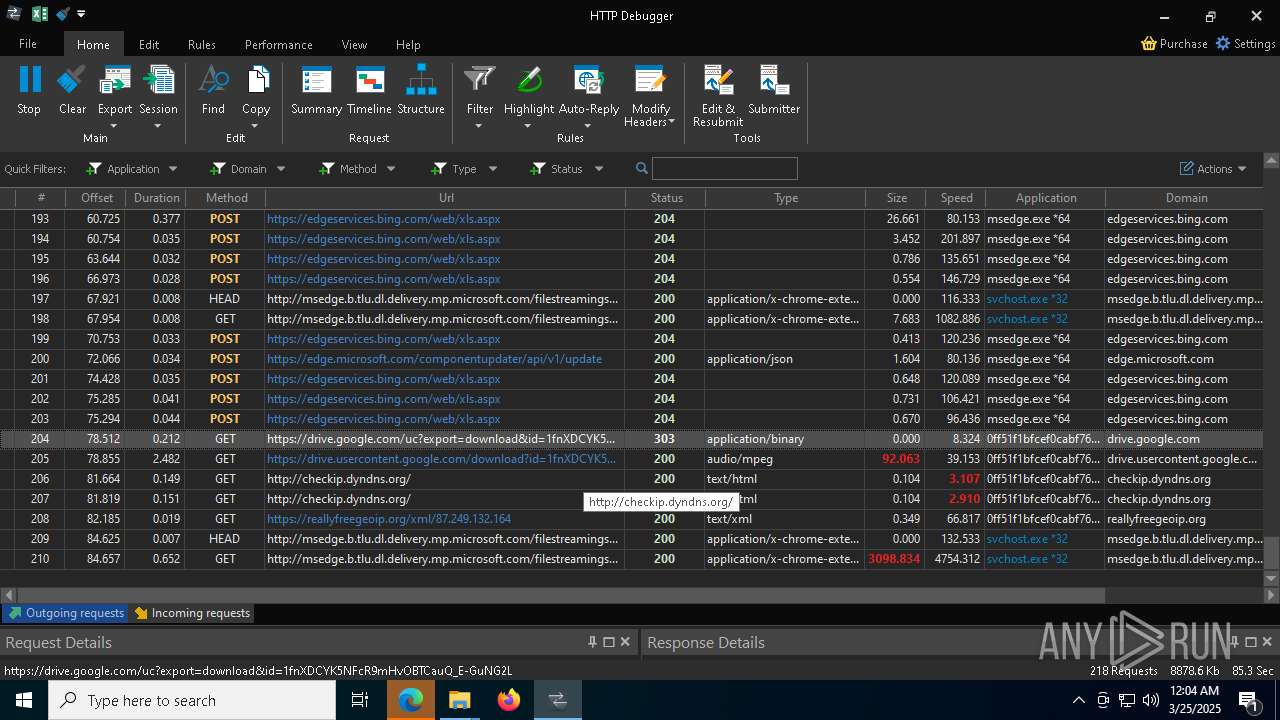
Checks for external IP
- svchost.exe (PID: 2196)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
There is functionality for taking screenshot (YARA)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
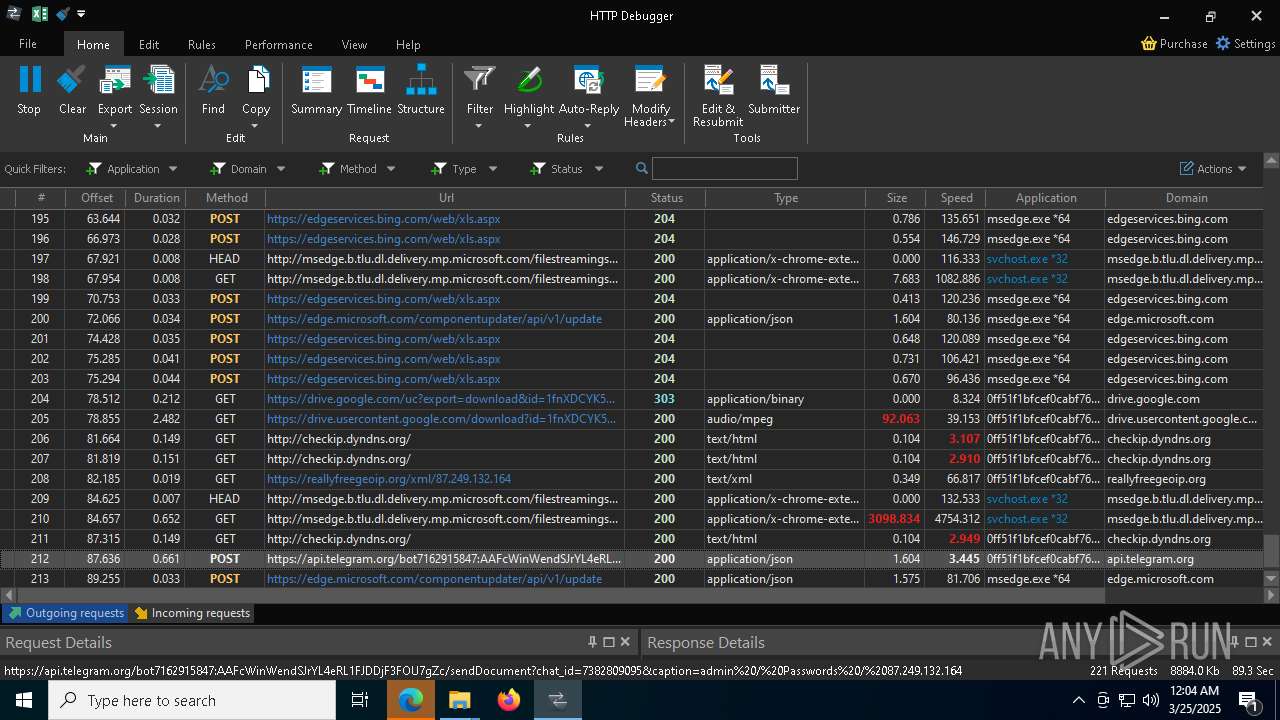
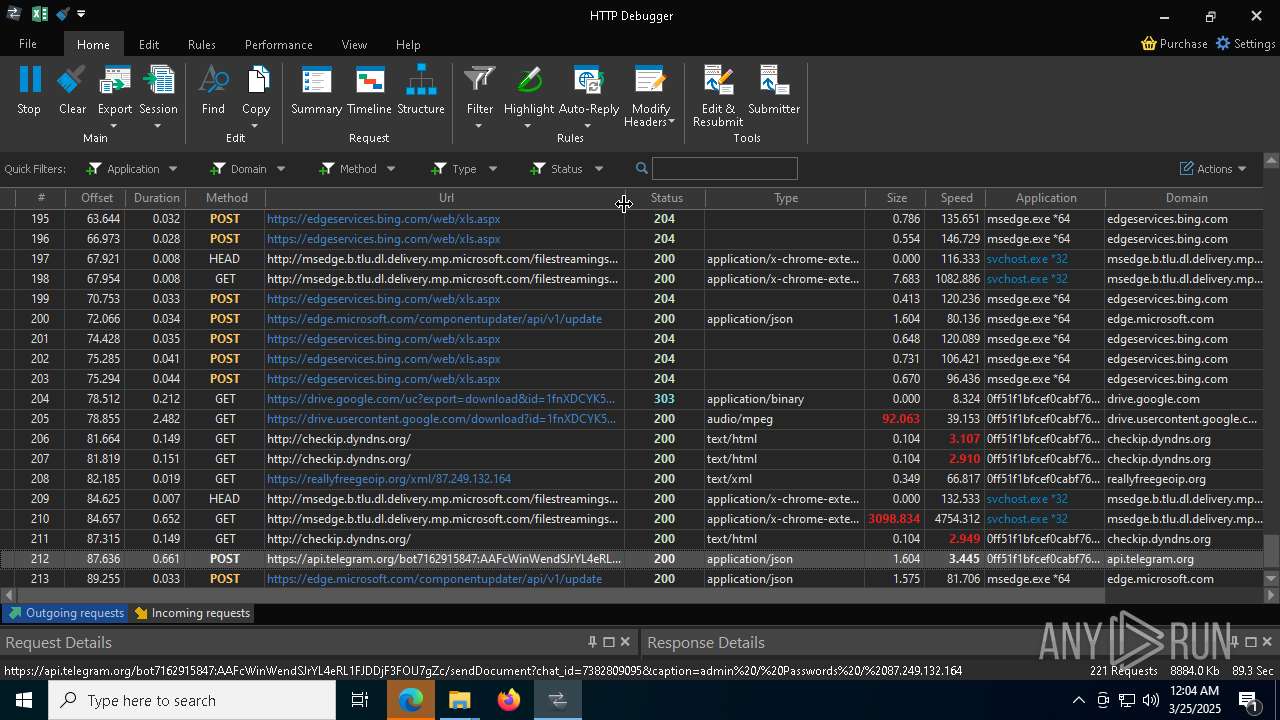
Possible usage of Discord/Telegram API has been detected (YARA)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
The process verifies whether the antivirus software is installed
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
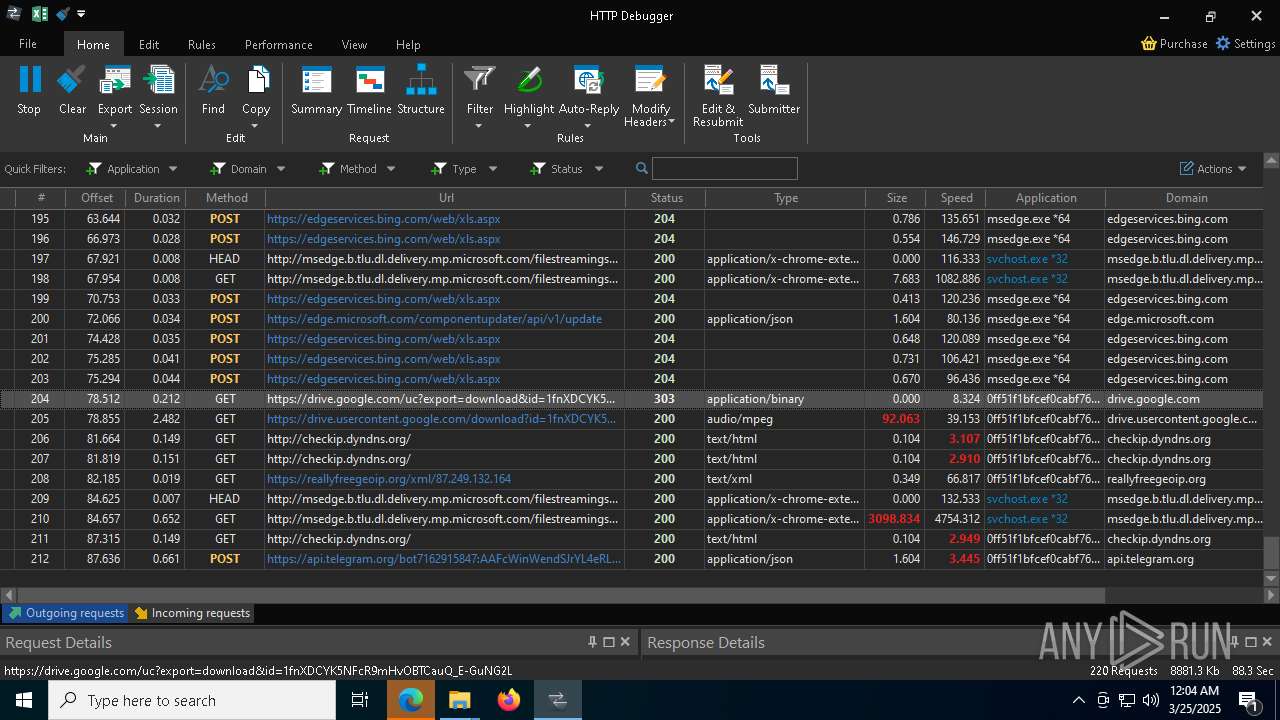
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
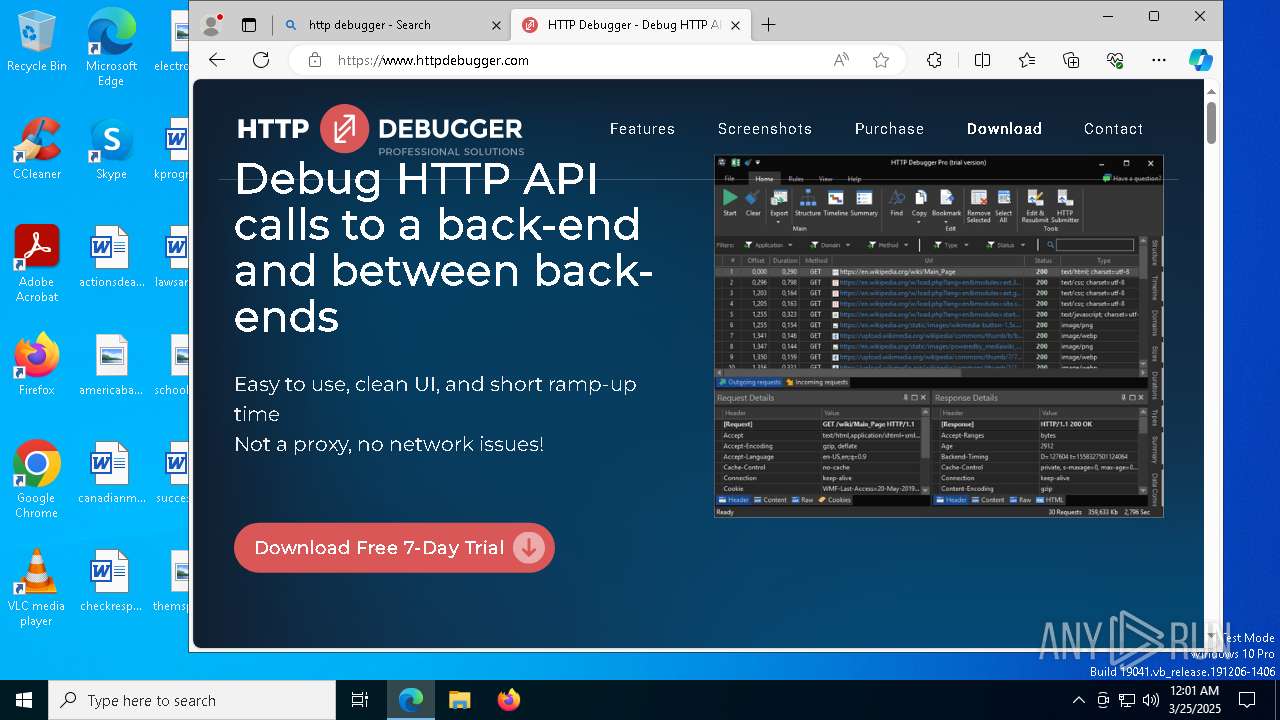
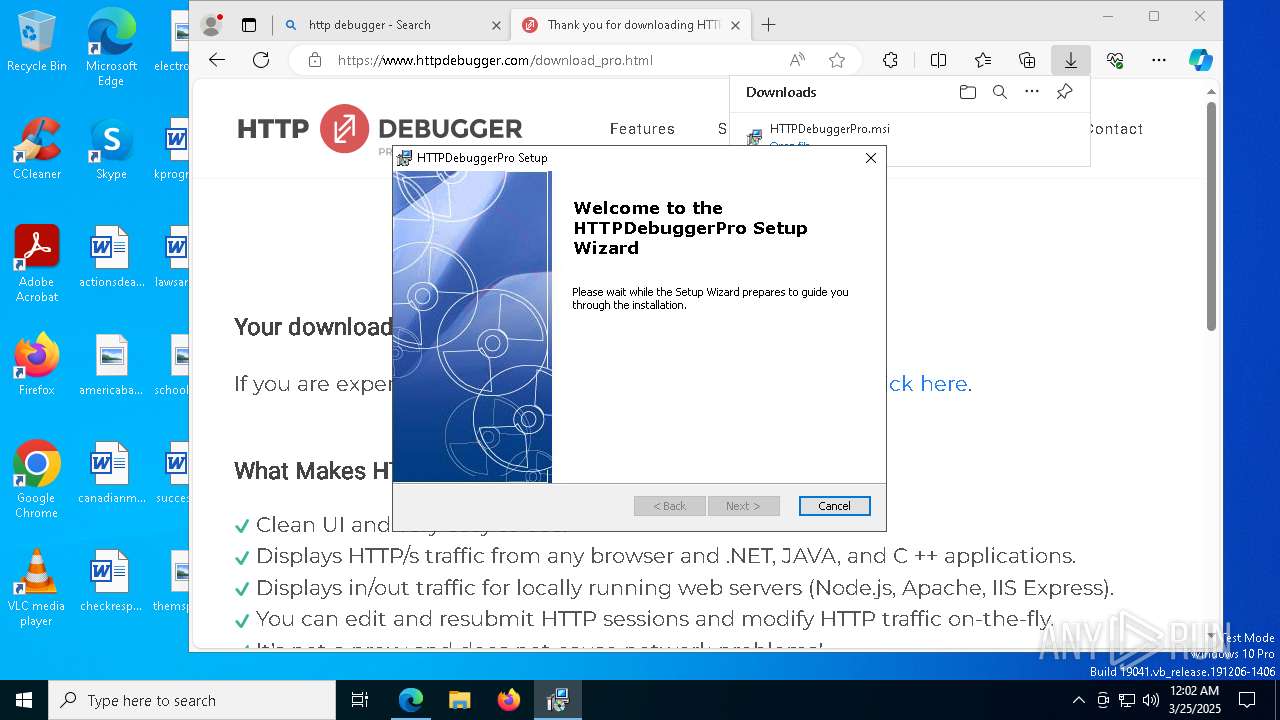
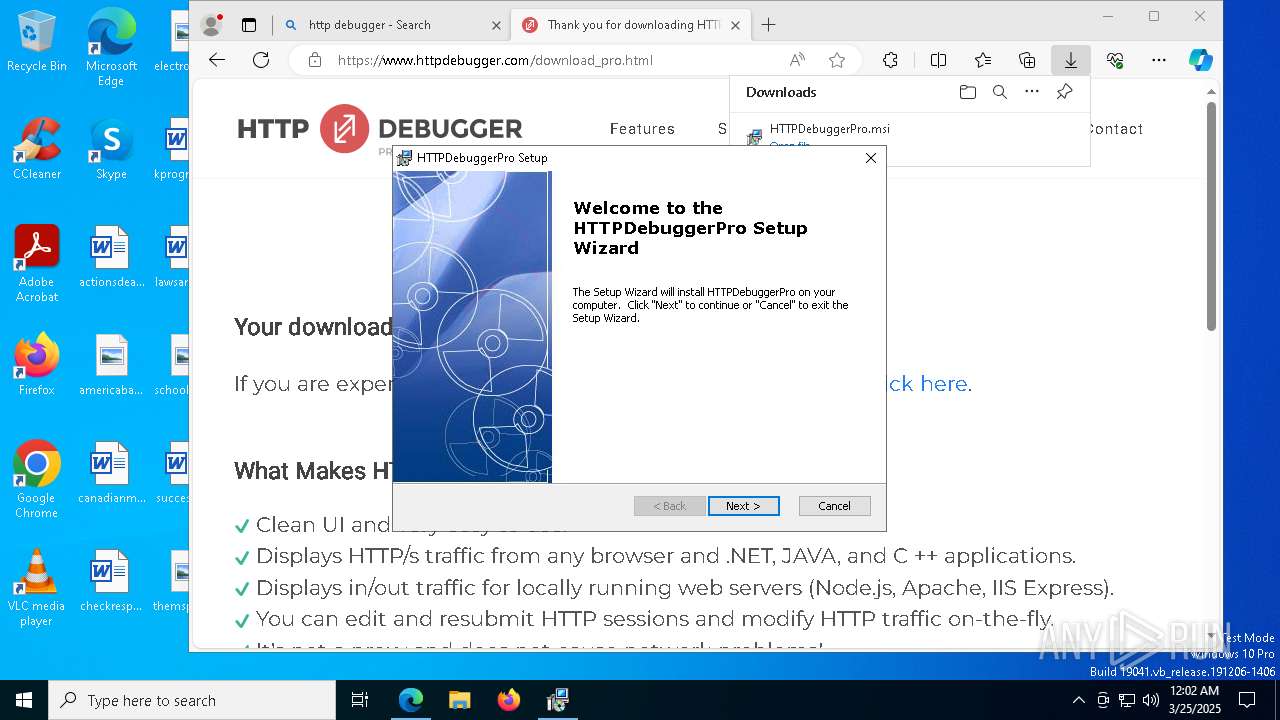
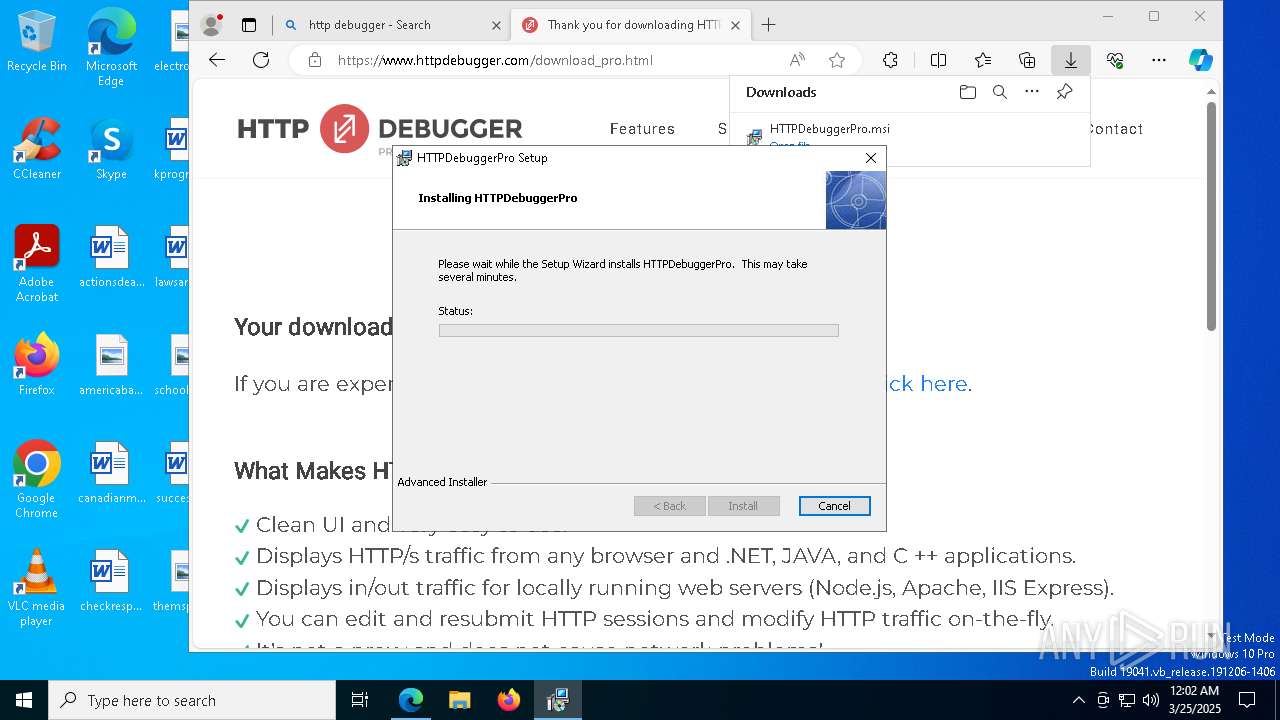
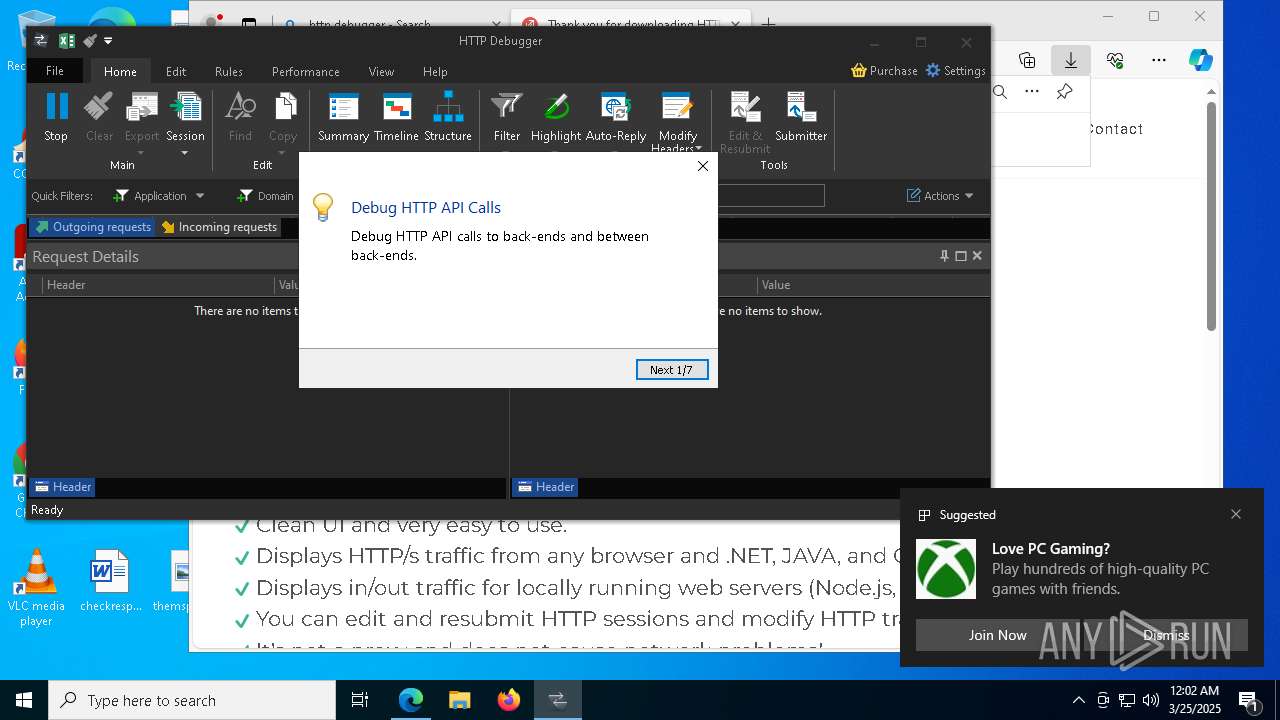
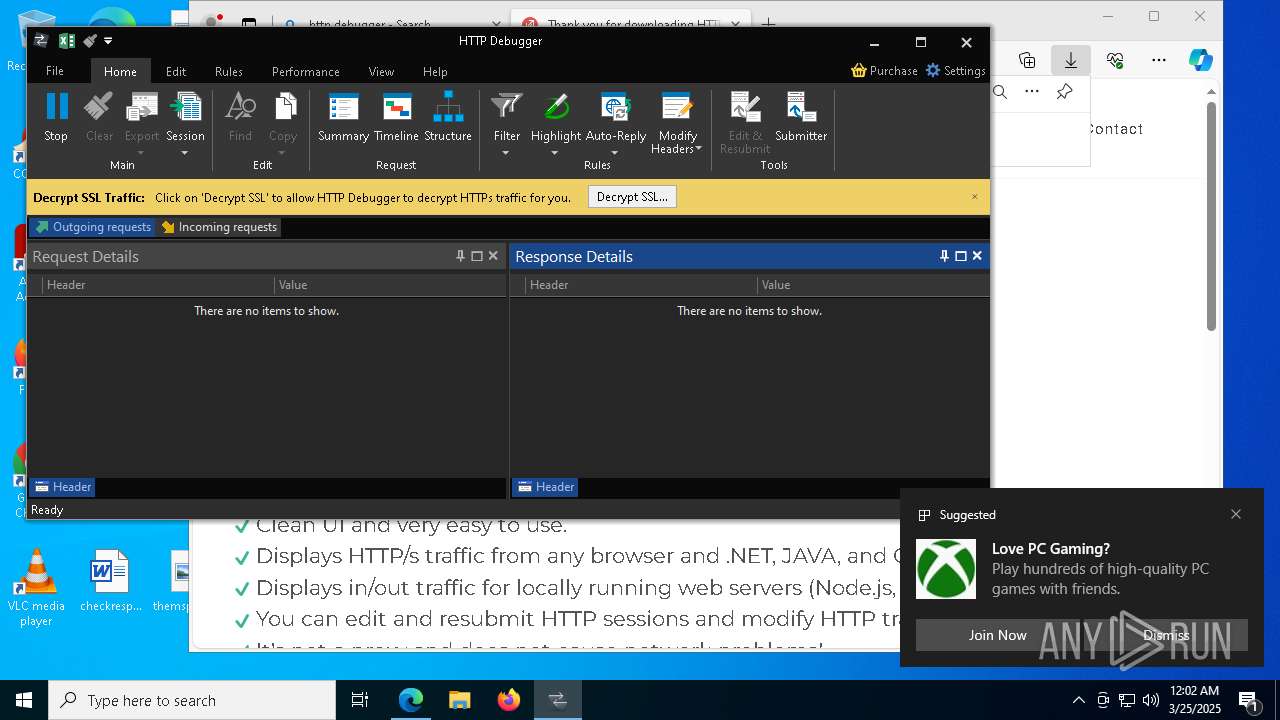
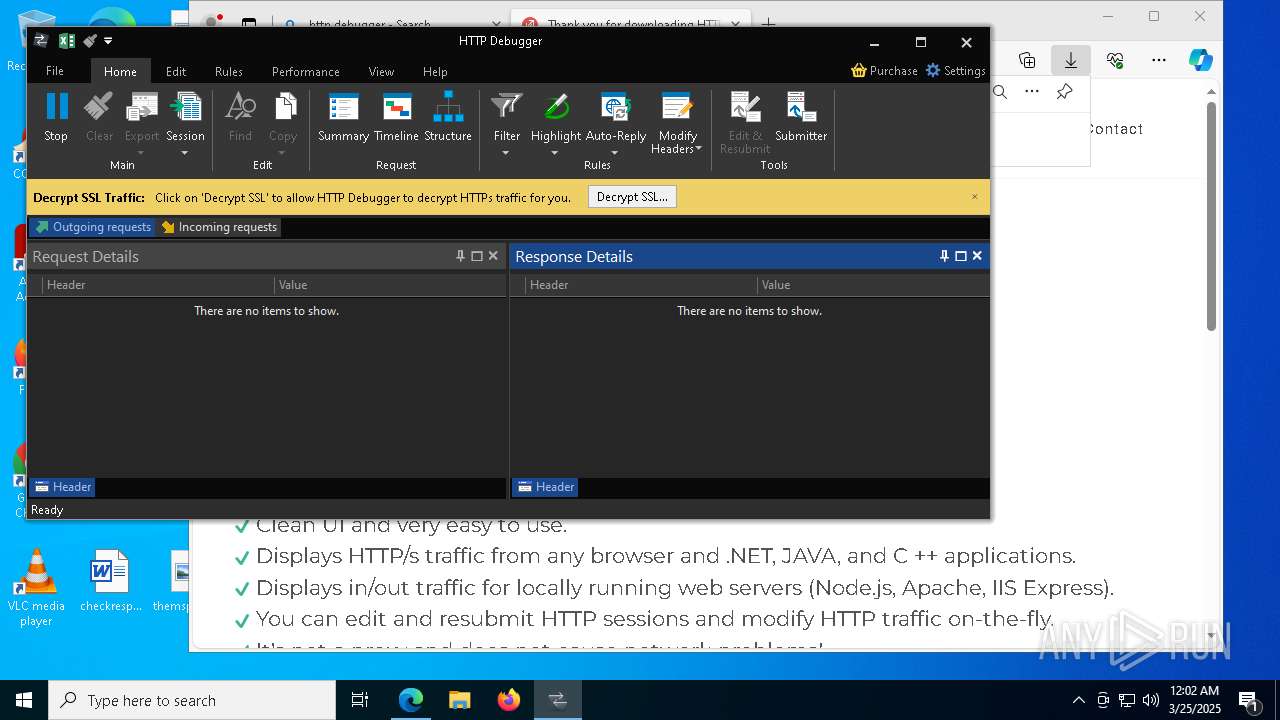
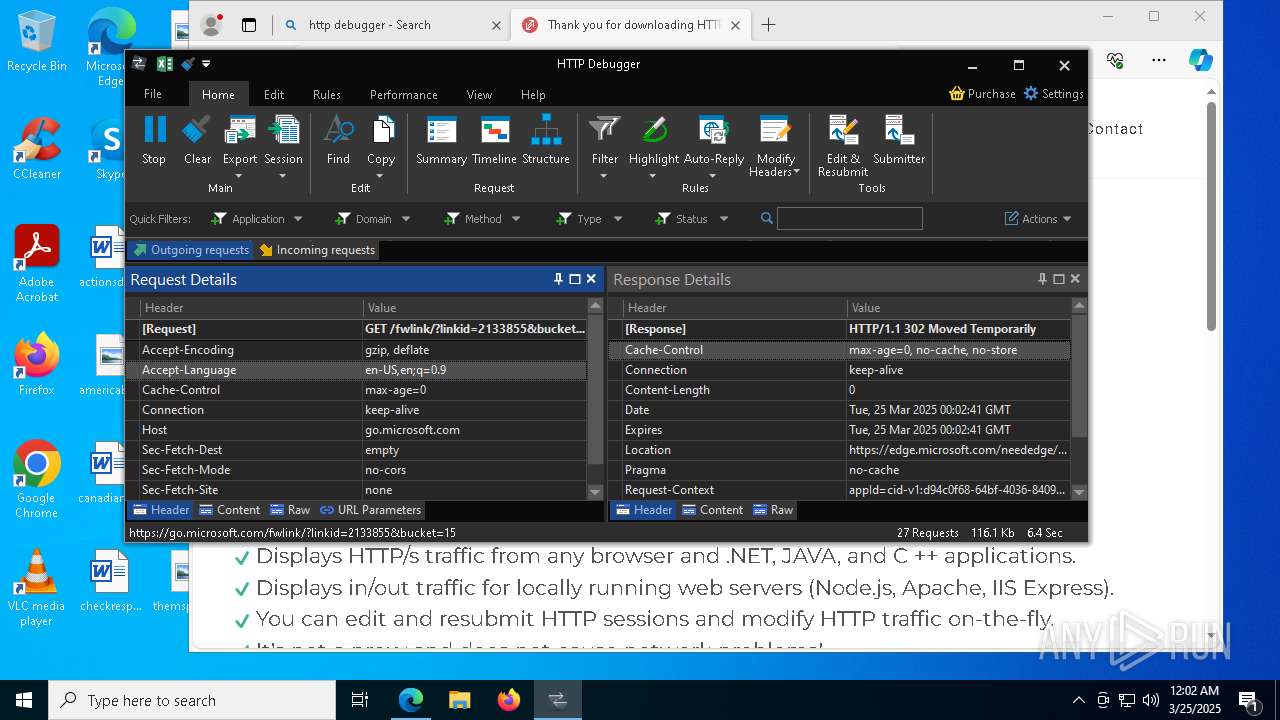
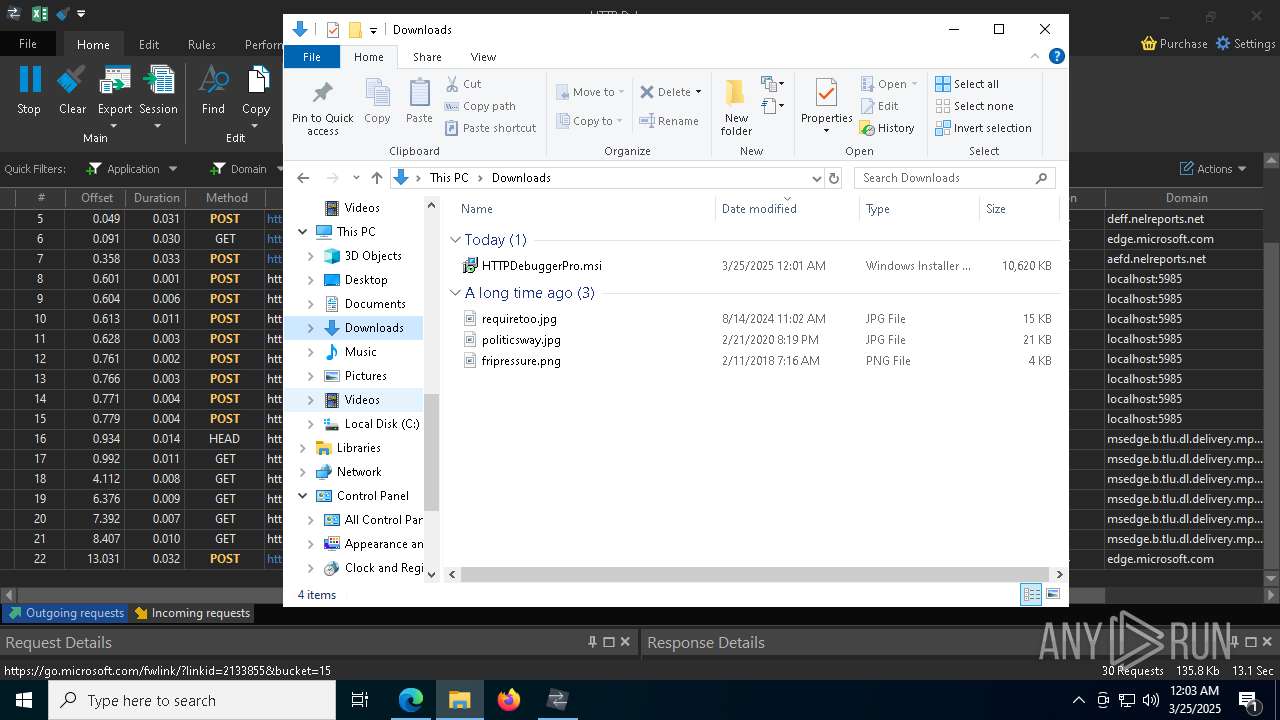
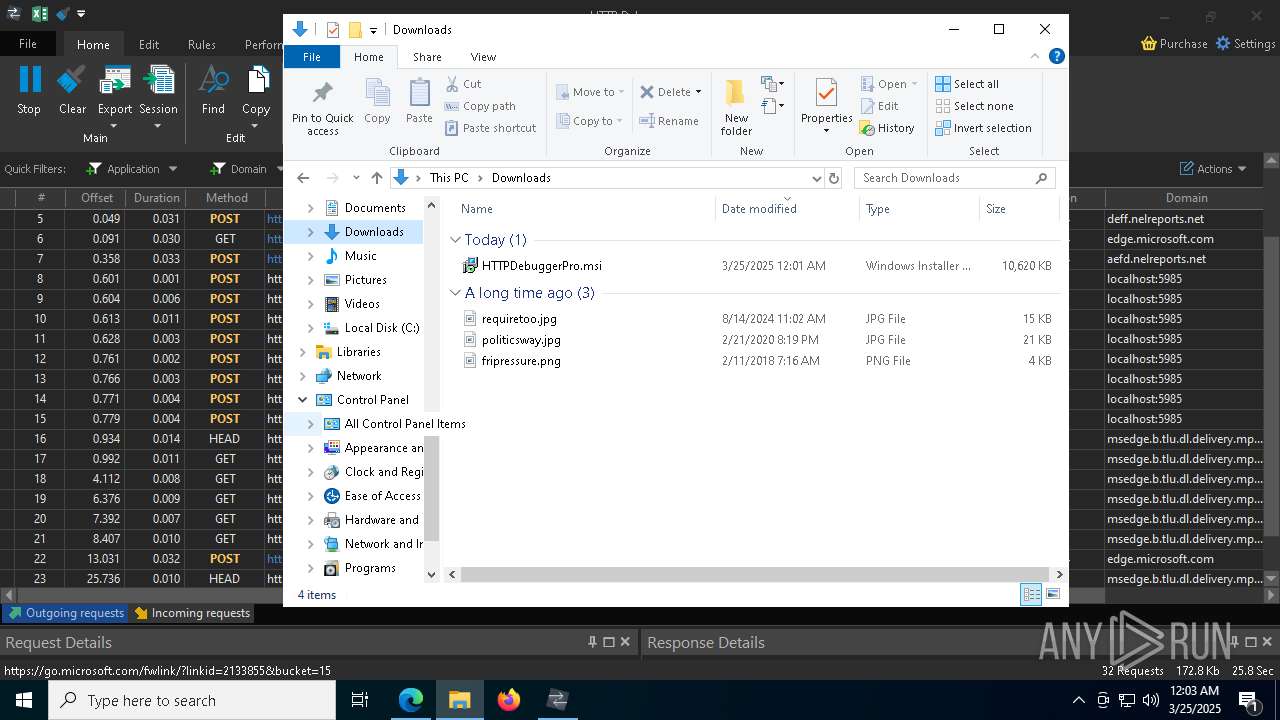
Executes as Windows Service
- VSSVC.exe (PID: 8928)
- HTTPDebuggerSvc.exe (PID: 4880)
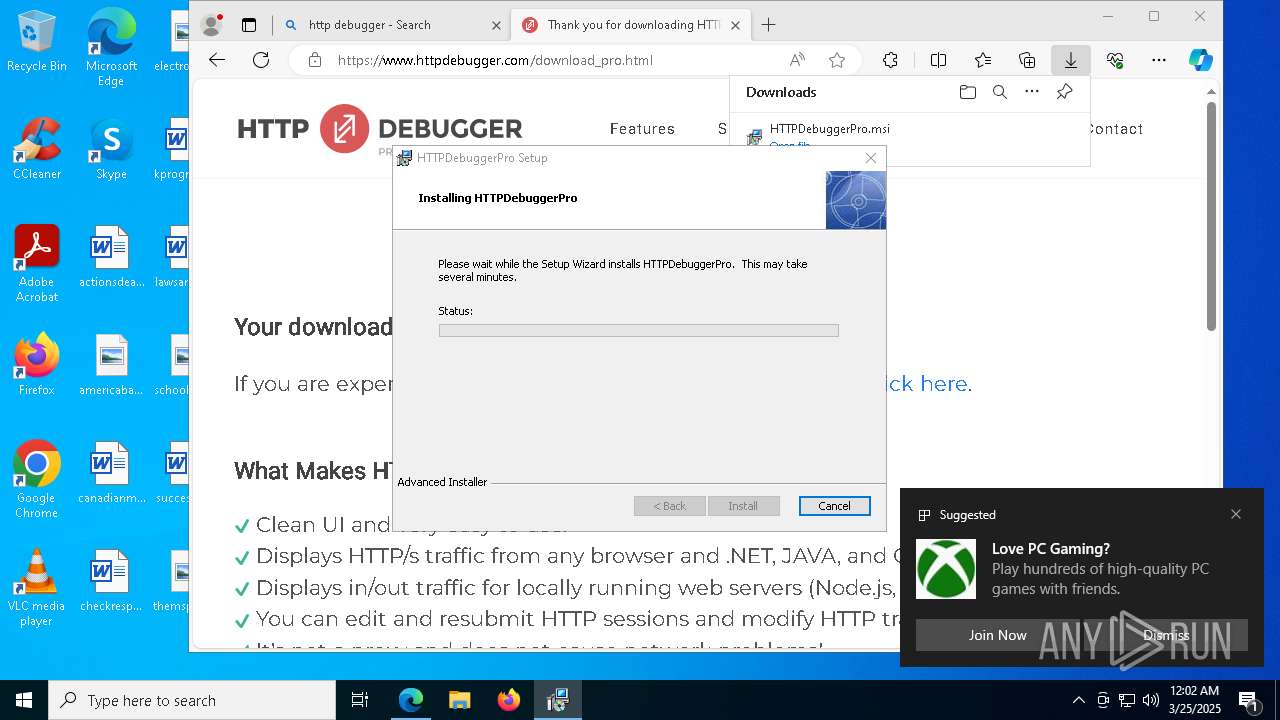
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 8716)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8764)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 8676)
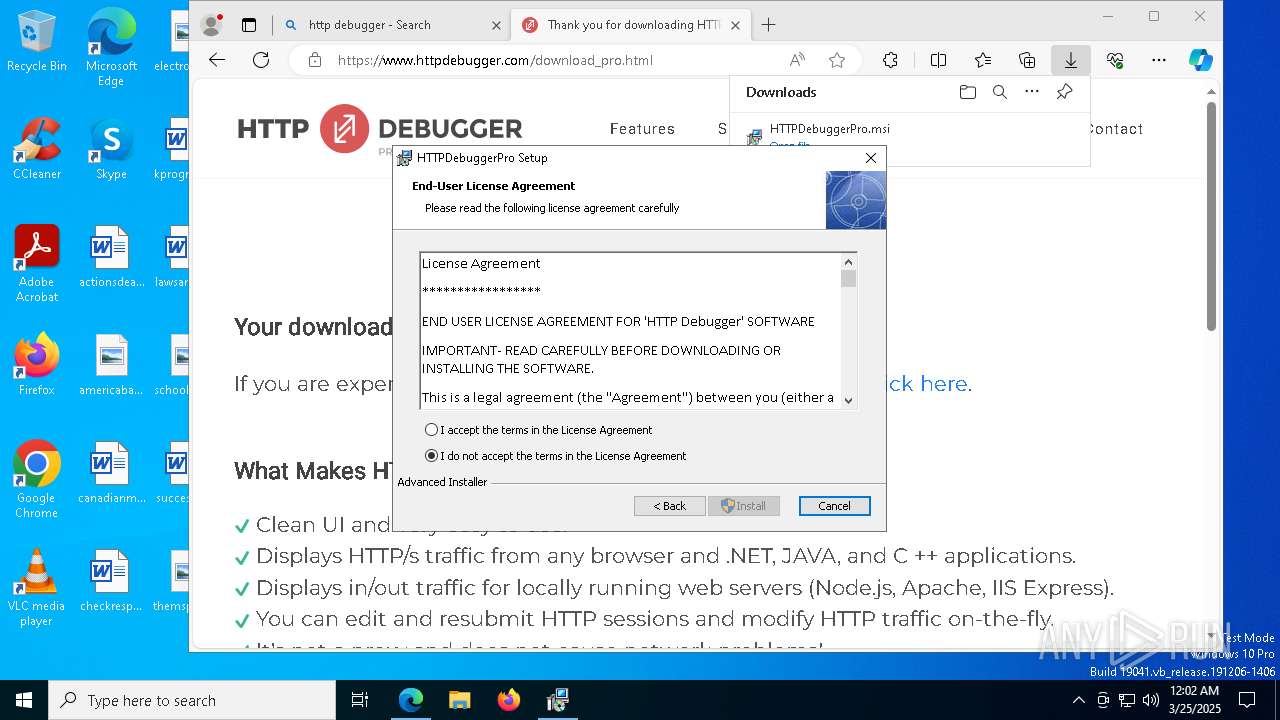
Drops a system driver (possible attempt to evade defenses)
- HTTPDebuggerSvc.exe (PID: 4880)
- msiexec.exe (PID: 8764)
Creates files in the driver directory
- HTTPDebuggerSvc.exe (PID: 4880)
Reads Microsoft Outlook installation path
- HTTPDebuggerUI.exe (PID: 9124)
Reads Internet Explorer settings
- HTTPDebuggerUI.exe (PID: 9124)
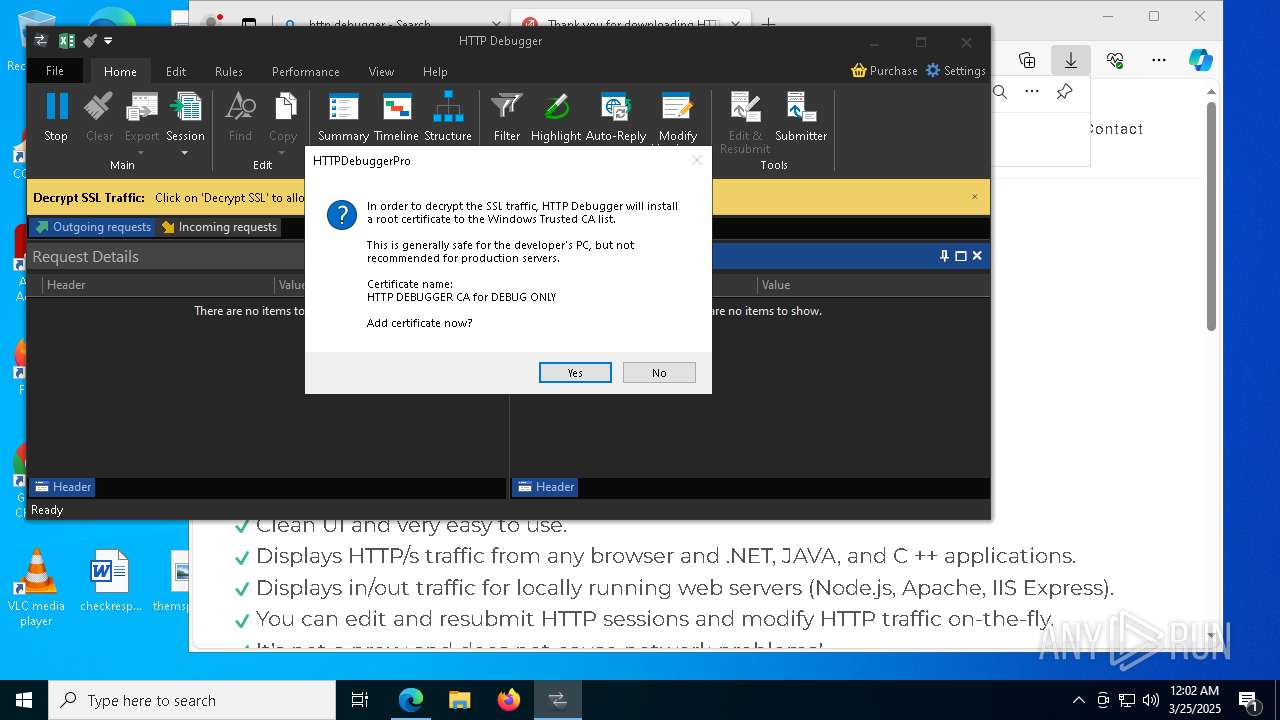
Adds/modifies Windows certificates
- HTTPDebuggerSvc.exe (PID: 4880)
INFO
Checks supported languages
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- identity_helper.exe (PID: 7764)
- msiexec.exe (PID: 8808)
- msiexec.exe (PID: 8764)
- msiexec.exe (PID: 7652)
- HTTPDebuggerSvc.exe (PID: 4880)
- HTTPDebuggerSvc.exe (PID: 924)
- ShellExperienceHost.exe (PID: 8244)
- certutil.exe (PID: 8444)
- HTTPDebuggerUI.exe (PID: 9124)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6300)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
Reads the computer name
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- identity_helper.exe (PID: 7764)
- msiexec.exe (PID: 8764)
- msiexec.exe (PID: 8808)
- HTTPDebuggerSvc.exe (PID: 4880)
- HTTPDebuggerSvc.exe (PID: 924)
- msiexec.exe (PID: 7652)
- ShellExperienceHost.exe (PID: 8244)
- HTTPDebuggerUI.exe (PID: 9124)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6300)
- certutil.exe (PID: 8444)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
Creates files or folders in the user directory
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- BackgroundTransferHost.exe (PID: 2420)
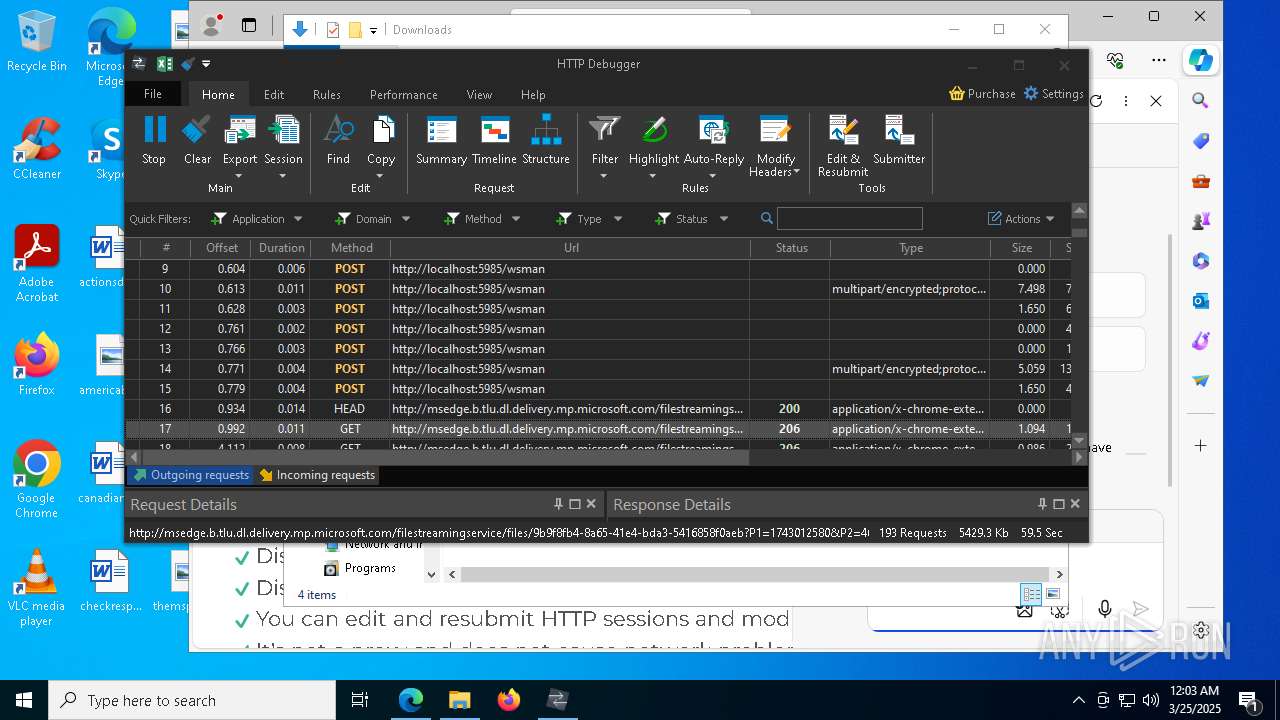
Create files in a temporary directory
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6044)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6300)
Checks proxy server information
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- BackgroundTransferHost.exe (PID: 2420)
- HTTPDebuggerUI.exe (PID: 9124)
- slui.exe (PID: 9112)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
Reads the machine GUID from the registry
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- msiexec.exe (PID: 8764)
- HTTPDebuggerSvc.exe (PID: 4880)
- HTTPDebuggerSvc.exe (PID: 924)
- HTTPDebuggerUI.exe (PID: 9124)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
Reads the software policy settings
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- BackgroundTransferHost.exe (PID: 2420)
- msiexec.exe (PID: 8764)
- msiexec.exe (PID: 8716)
- slui.exe (PID: 4812)
- HTTPDebuggerUI.exe (PID: 9124)
- slui.exe (PID: 9112)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1272)
- BackgroundTransferHost.exe (PID: 2420)
- BackgroundTransferHost.exe (PID: 3100)
- BackgroundTransferHost.exe (PID: 7508)
- BackgroundTransferHost.exe (PID: 8096)
- msiexec.exe (PID: 8716)
Disables trace logs
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 2980)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 4040)
Application launched itself
- msedge.exe (PID: 6132)
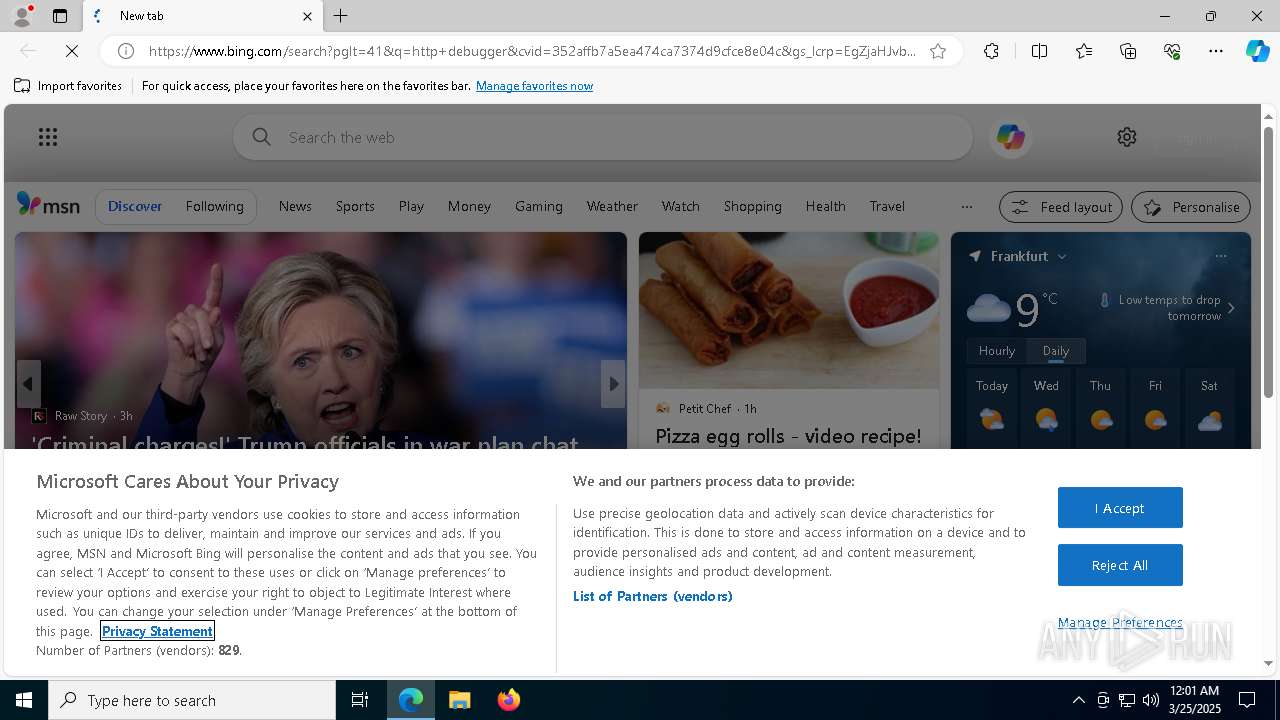
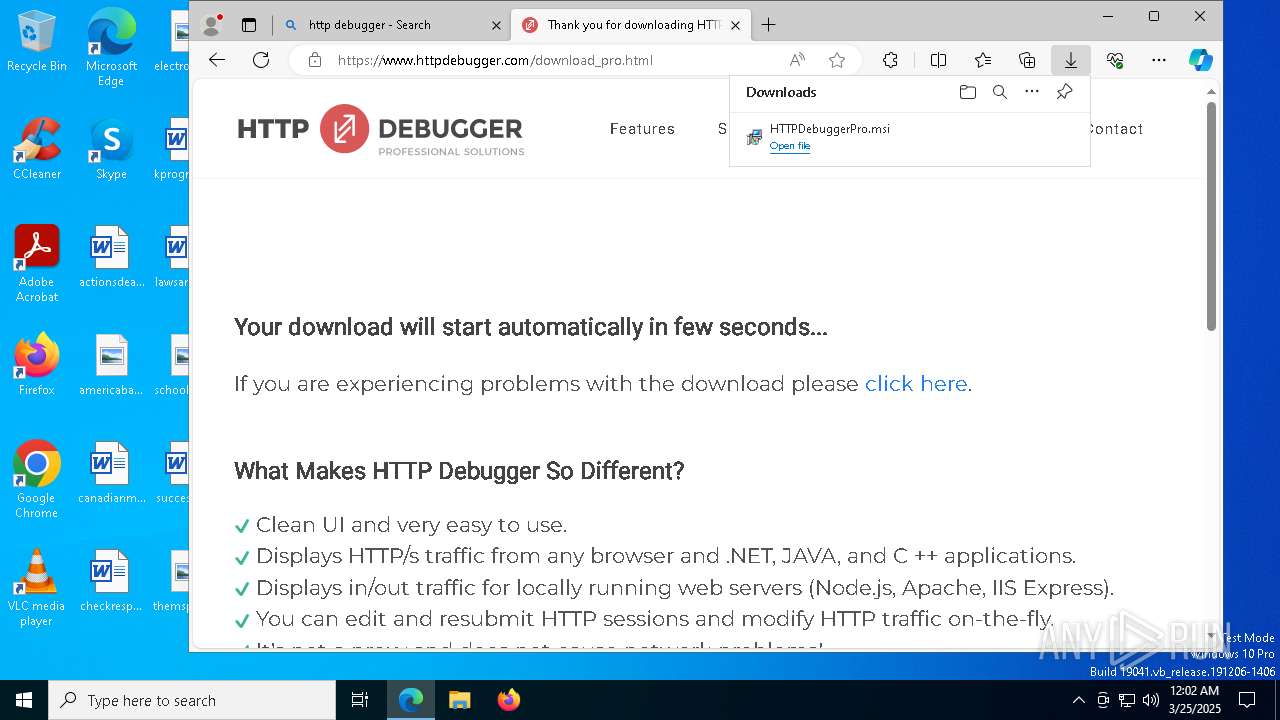
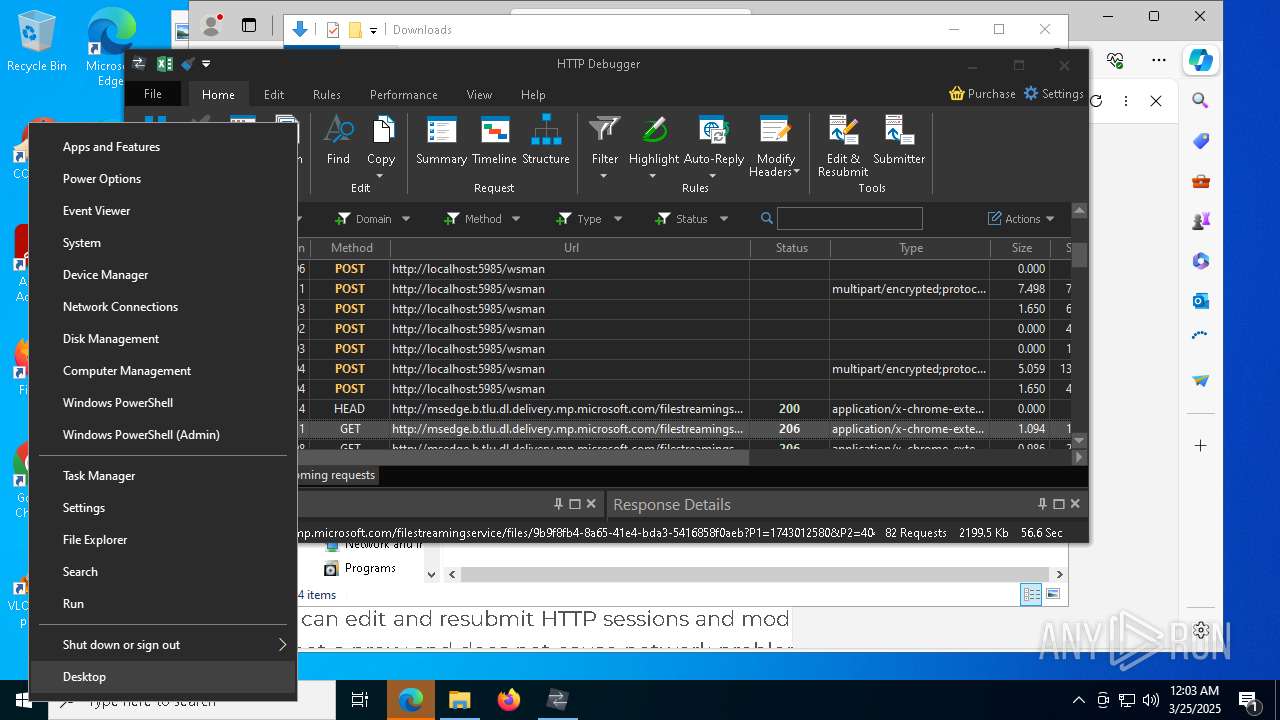
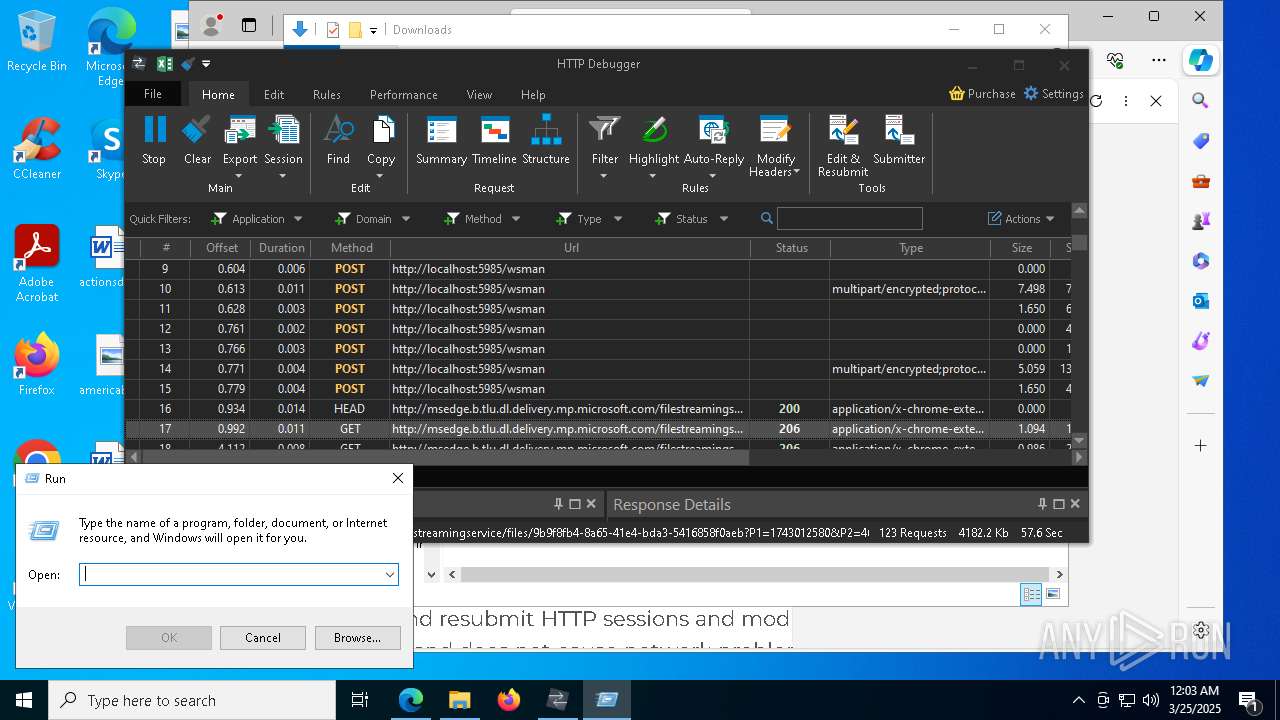
Manual execution by a user
- msedge.exe (PID: 6132)
- 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe (PID: 6300)
Reads Environment values
- identity_helper.exe (PID: 7764)
Manages system restore points
- SrTasks.exe (PID: 8628)
The sample compiled with english language support
- msiexec.exe (PID: 8716)
- msiexec.exe (PID: 8764)
- HTTPDebuggerSvc.exe (PID: 4880)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8716)
- msiexec.exe (PID: 8764)
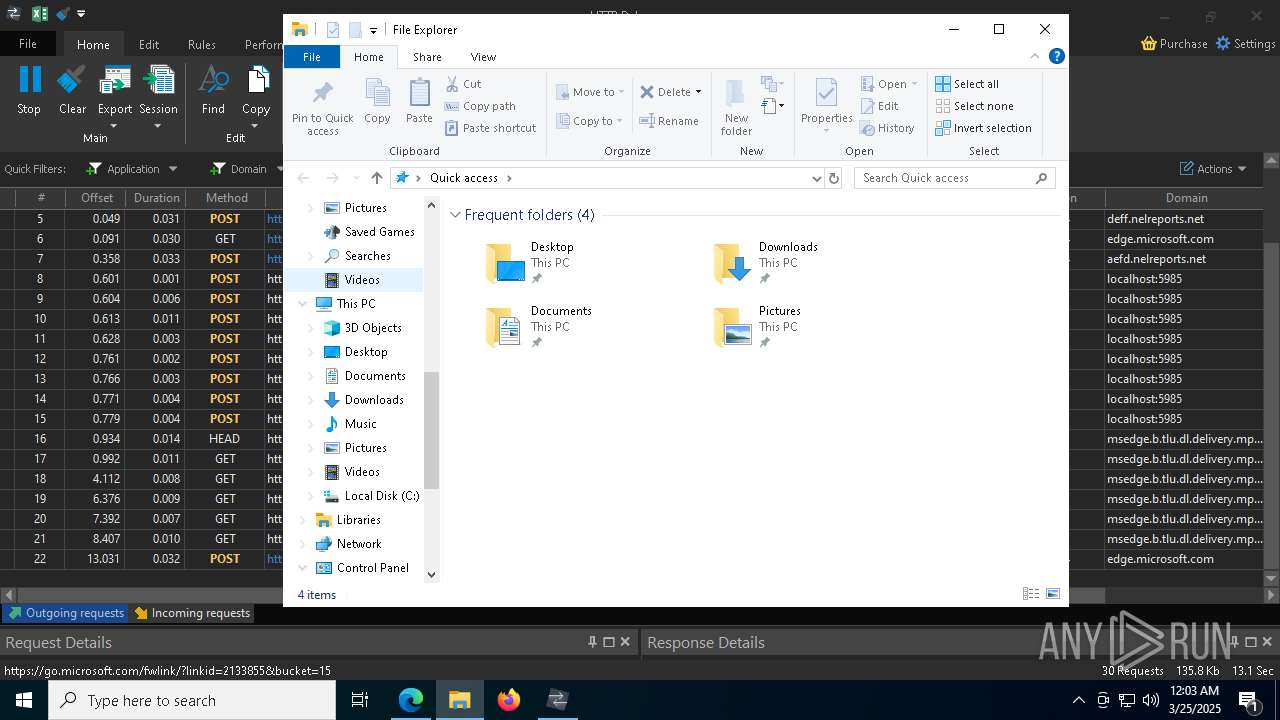
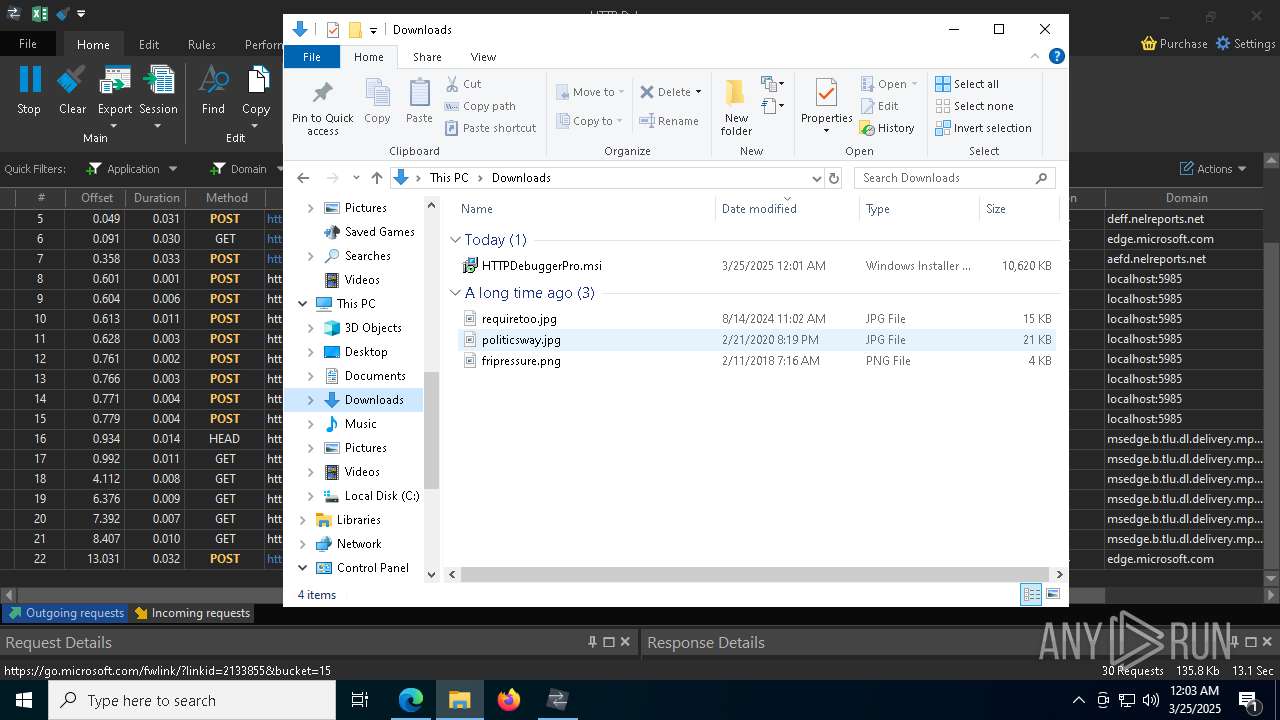
Autorun file from Downloads
- msedge.exe (PID: 8600)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6132)
Creates files in the program directory
- HTTPDebuggerSvc.exe (PID: 4880)
Creates a software uninstall entry
- msiexec.exe (PID: 8764)
Process checks computer location settings
- msiexec.exe (PID: 8808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 06:26:07+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x32a0 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
227
Monitored processes
84
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
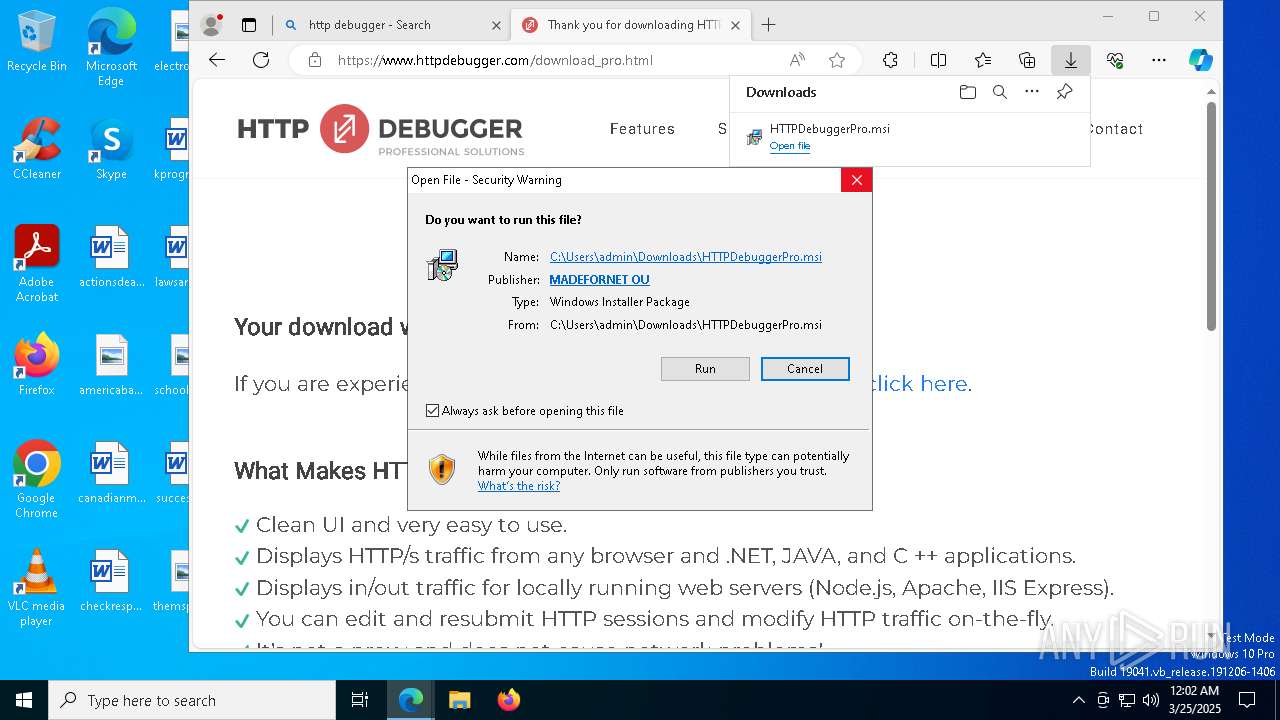
| 924 | "C:\Program Files (x86)\HTTPDebuggerPro\HTTPDebuggerSvc.exe" /install | C:\Program Files (x86)\HTTPDebuggerPro\HTTPDebuggerSvc.exe | — | msiexec.exe | |||||||||||
User: admin Company: HttpDebugger.com Integrity Level: MEDIUM Description: HTTP Debugger Windows Service Exit code: 0 Version: 9.0.0.12 Modules
| |||||||||||||||
| 1272 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2580 --field-trial-handle=2556,i,4864323995299725705,17095505902595797698,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\AppData\Local\Temp\0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe" | C:\Users\admin\AppData\Local\Temp\0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3100 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc89905fd8,0x7ffc89905fe4,0x7ffc89905ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5708 --field-trial-handle=2556,i,4864323995299725705,17095505902595797698,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\AppData\Local\Temp\0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe" | C:\Users\admin\AppData\Local\Temp\0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
38 237
Read events
37 813
Write events
406
Delete events
18
Modification events
| (PID) Process: | (6044) 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Service |
| Operation: | write | Name: | System_Check |
Value: kernel32::CreateFileA(m r4 , i 0x80000000, i 0, p 0, i 4, i 0x80, i 0)i.r5 | |||
| (PID) Process: | (6044) 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Service |
| Operation: | write | Name: | System_Check |
Value: kernel32::SetFilePointer(i r5, i 13101 , i 0,i 0) | |||
| (PID) Process: | (6044) 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Service |
| Operation: | write | Name: | System_Check |
Value: kernel32::VirtualAlloc(i 0,i 48783360, i 0x3000, i 0x40)p.r2 | |||
| (PID) Process: | (6044) 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Service |
| Operation: | write | Name: | System_Check |
Value: kernel32::ReadFile(i r5, i r2, i 48783360,*i 0, i 0) | |||
| (PID) Process: | (6044) 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Service |
| Operation: | write | Name: | System_Check |
Value: user32::EnumWindows(i r2 ,i 0) | |||
| (PID) Process: | (6044) 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\CLI\Start |
| Operation: | write | Name: | CLI start |
Value: 2 | |||
| (PID) Process: | (1272) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1272) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1272) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2420) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
76
Suspicious files
797
Text files
110
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\7774ba60-4fab-4ddc-97e0-c01ef38be83f.down_data | — | |
MD5:— | SHA256:— | |||
| 2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7B5FC60CCA5D8CF767A7572C65728CD6_F0452699D4257125F6D867DFDE8372A2 | binary | |
MD5:13735785542D18D5704E0AE537BEC2F5 | SHA256:86DF9DA9A63E1C0A2706AF293297BB582C247201F8519134969A307EB469185F | |||
| 6044 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | C:\Users\admin\AppData\Local\Temp\nspB52A.tmp\System.dll | executable | |
MD5:EE260C45E97B62A5E42F17460D406068 | SHA256:E94A1F7BCD7E0D532B660D0AF468EB3321536C3EFDCA265E61F9EC174B1AEF27 | |||
| 2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:E117C3342F046AB52553F9B660B503D3 | SHA256:A4C7549FD5F83C311982CB1CEB7D33F8D5EDD98F307F0C1AAB8A019AB2FE9A24 | |||
| 2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9E62DD75009A293E0AF9565AE544F23E_6465F3778A77E94C1A0900A28FE8CBDE | binary | |
MD5:5A18FB8A82D60D7A0053C4EBE9A101B4 | SHA256:36C6DA66510C0371D943B4D6E221BBD3B062F773EA6B4DB9A39E3CF0432DDF73 | |||
| 6044 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Printer Shortcuts\Benchership141.lnk | binary | |
MD5:BF9CC6B5857258FEA4B48BB766A90893 | SHA256:94774DC897B368347052D00311D80A00D2620757C25A9B1BF426CFA4083B2109 | |||
| 2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9E62DD75009A293E0AF9565AE544F23E_6465F3778A77E94C1A0900A28FE8CBDE | binary | |
MD5:E603F8D8F84C64FCBBE3696DADFFAC8E | SHA256:92439C7CE0E04856AEC8B453261DECB2E631814C9F5AC502C30279E0CC439C4F | |||
| 2420 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 6044 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\rapiditetens\fremtving\Beclamor\wildwestfilm.sto | binary | |
MD5:BFEA15C03AB295424981A73637A19491 | SHA256:83E9CE74259889DCABD39D41131F286882B224698DCDEB8D0B4074069AAA687B | |||
| 2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7B5FC60CCA5D8CF767A7572C65728CD6_F0452699D4257125F6D867DFDE8372A2 | binary | |
MD5:50C20B93958386BF78BDFA252ED51B1F | SHA256:D78E87BF99D0AA8122BFADC1CD7C3BD44B740A3566CA9397CD52FF5FA8AF227C | |||
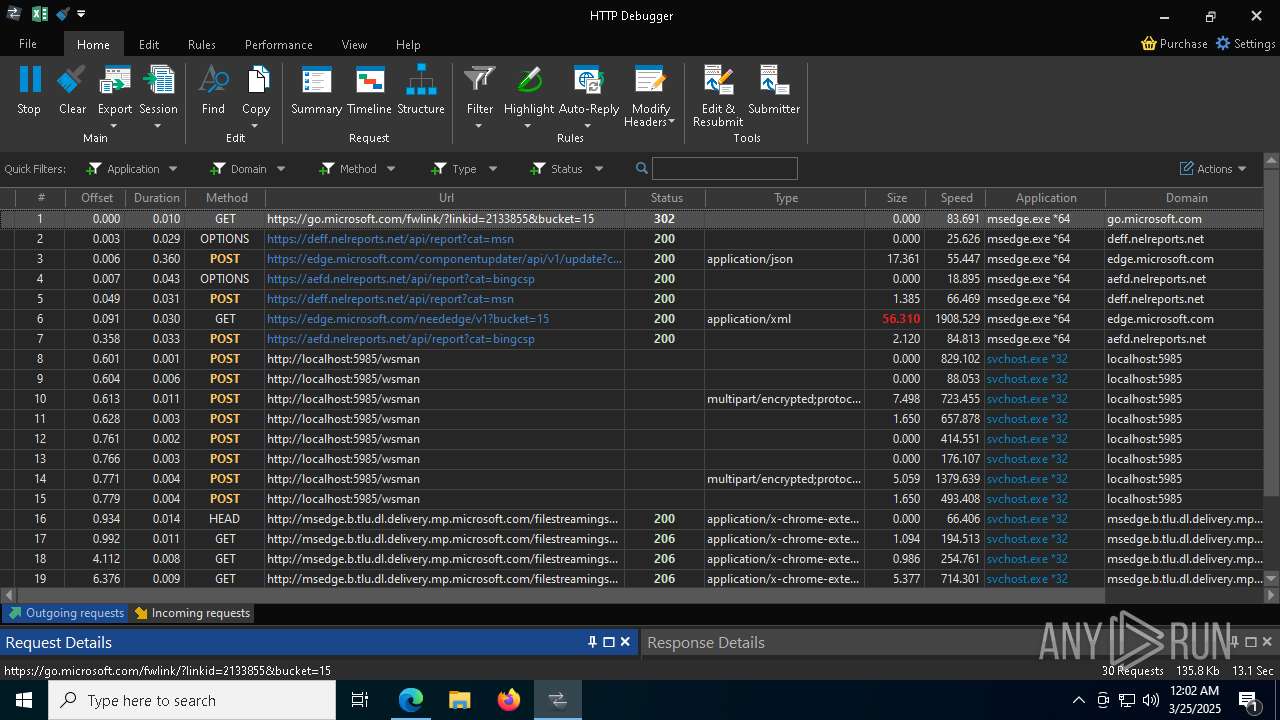
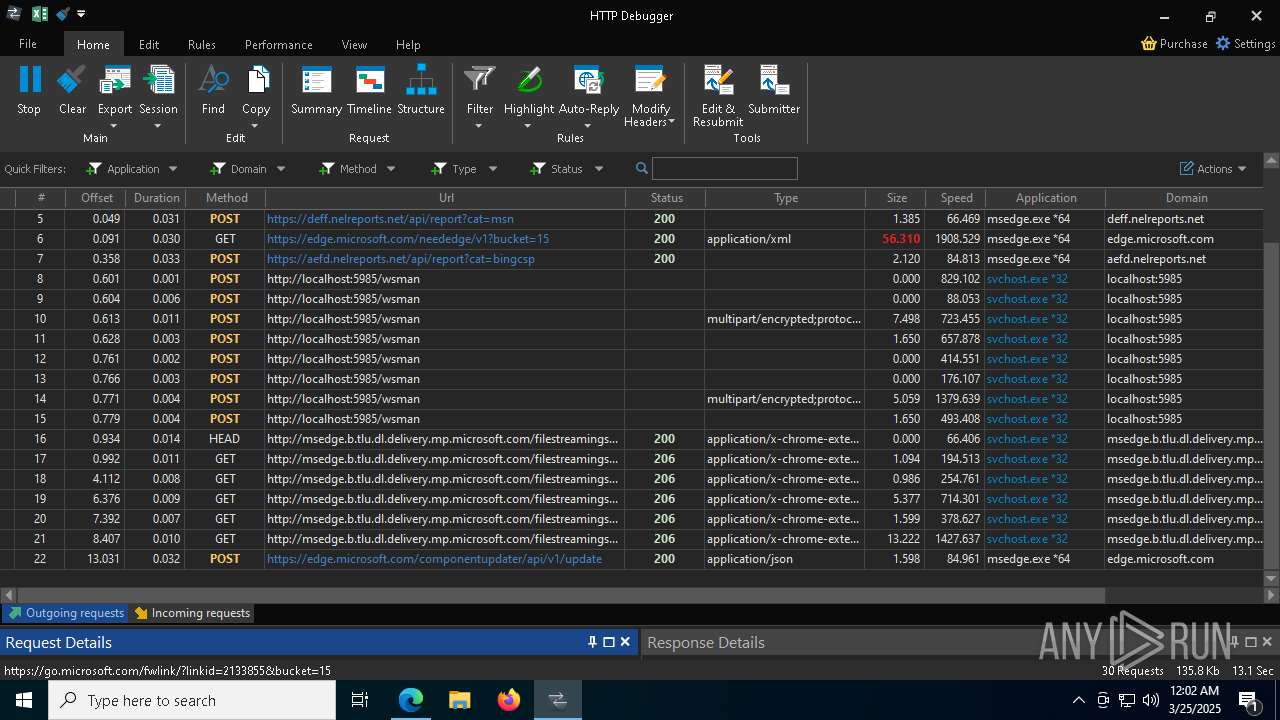
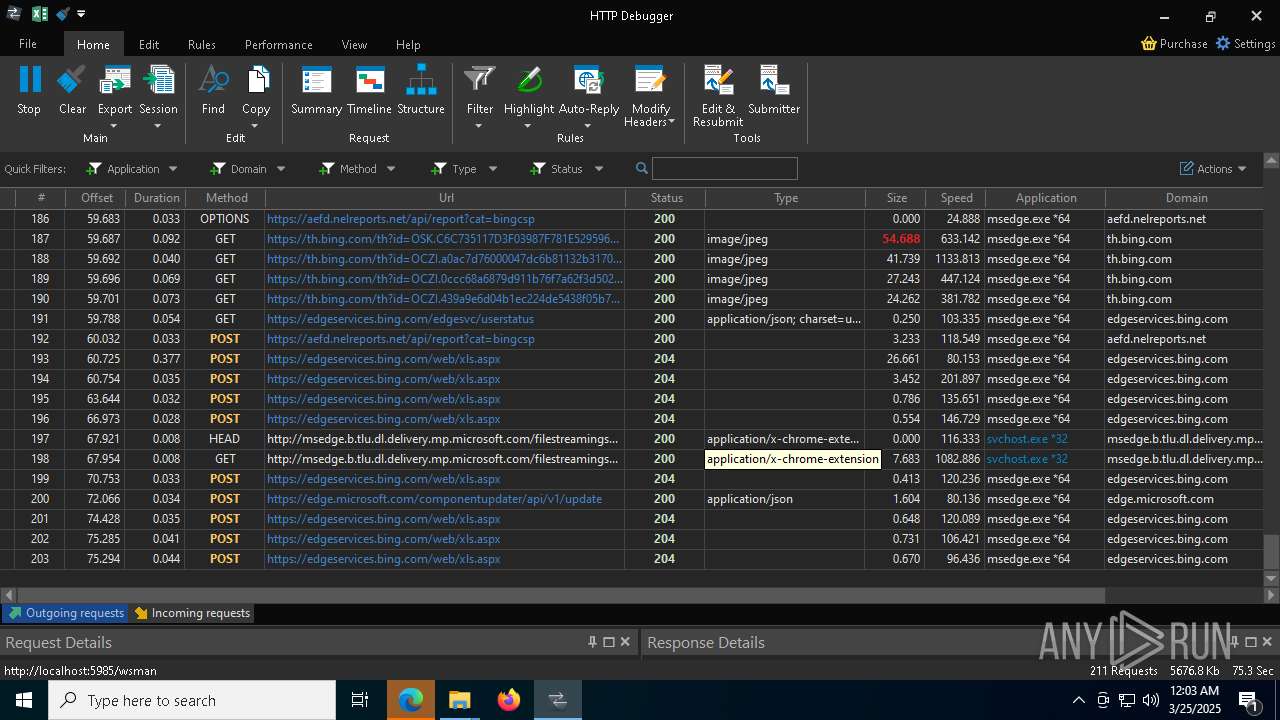
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
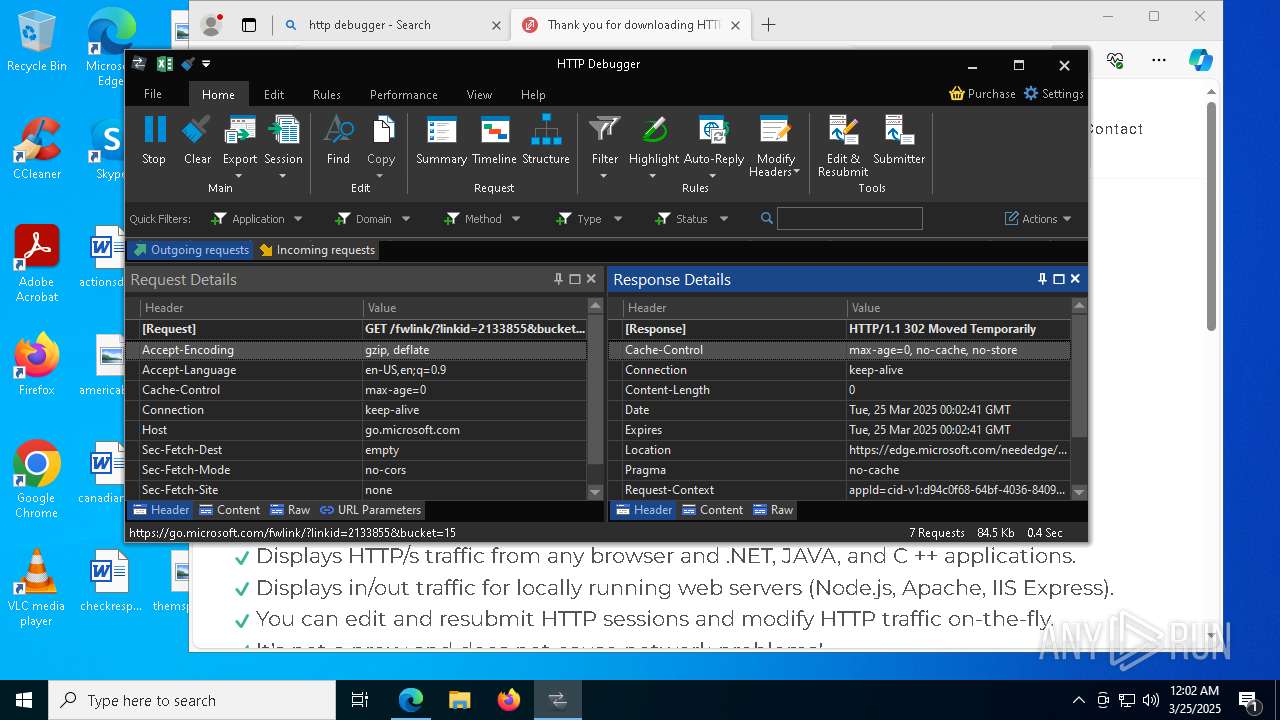
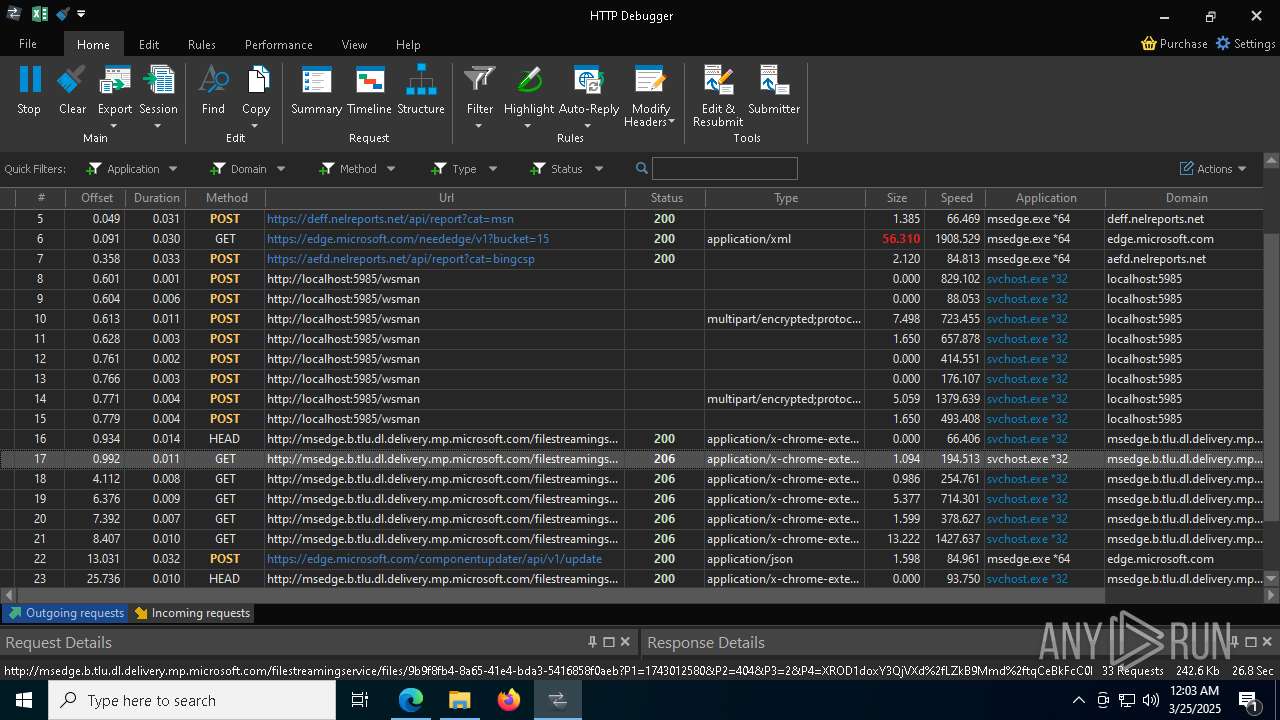
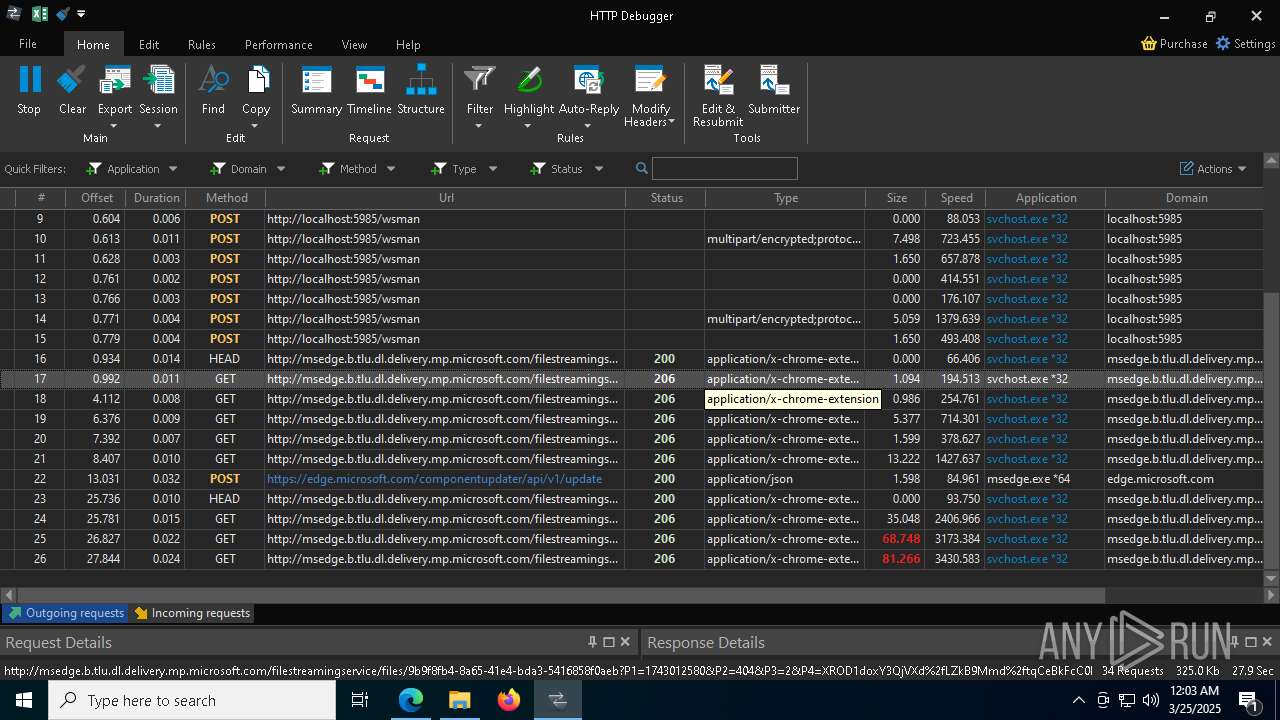
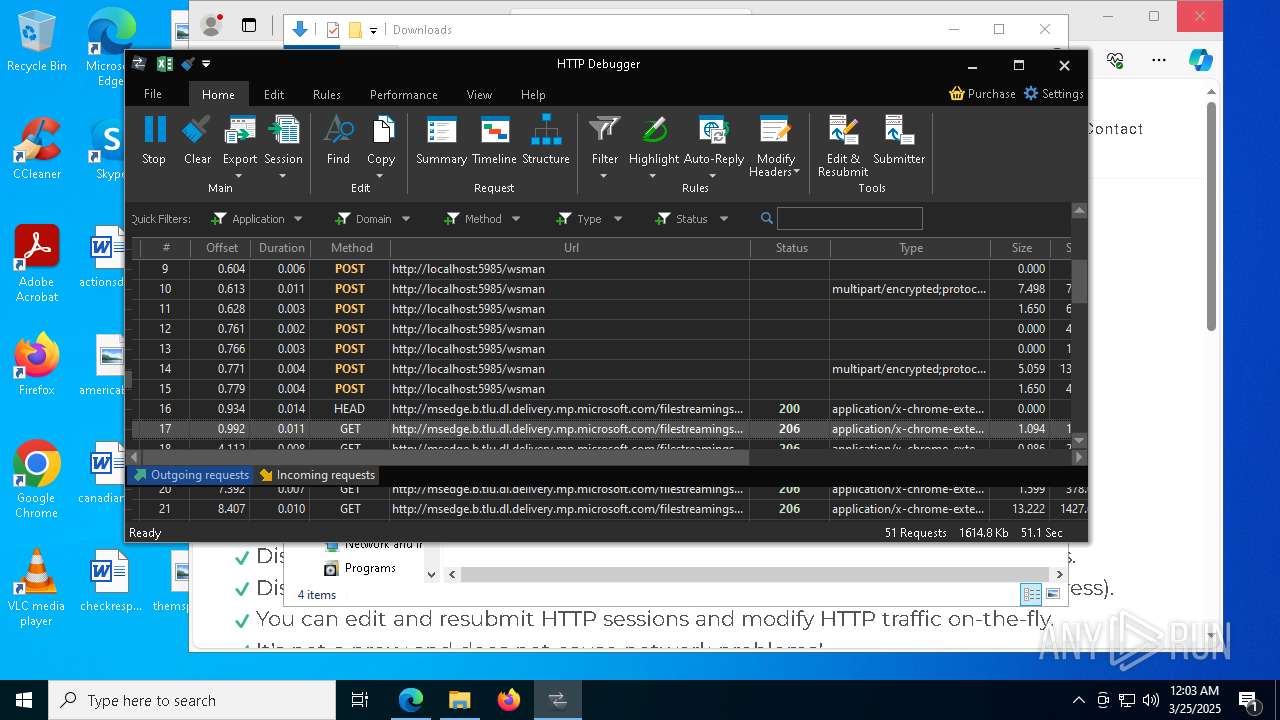
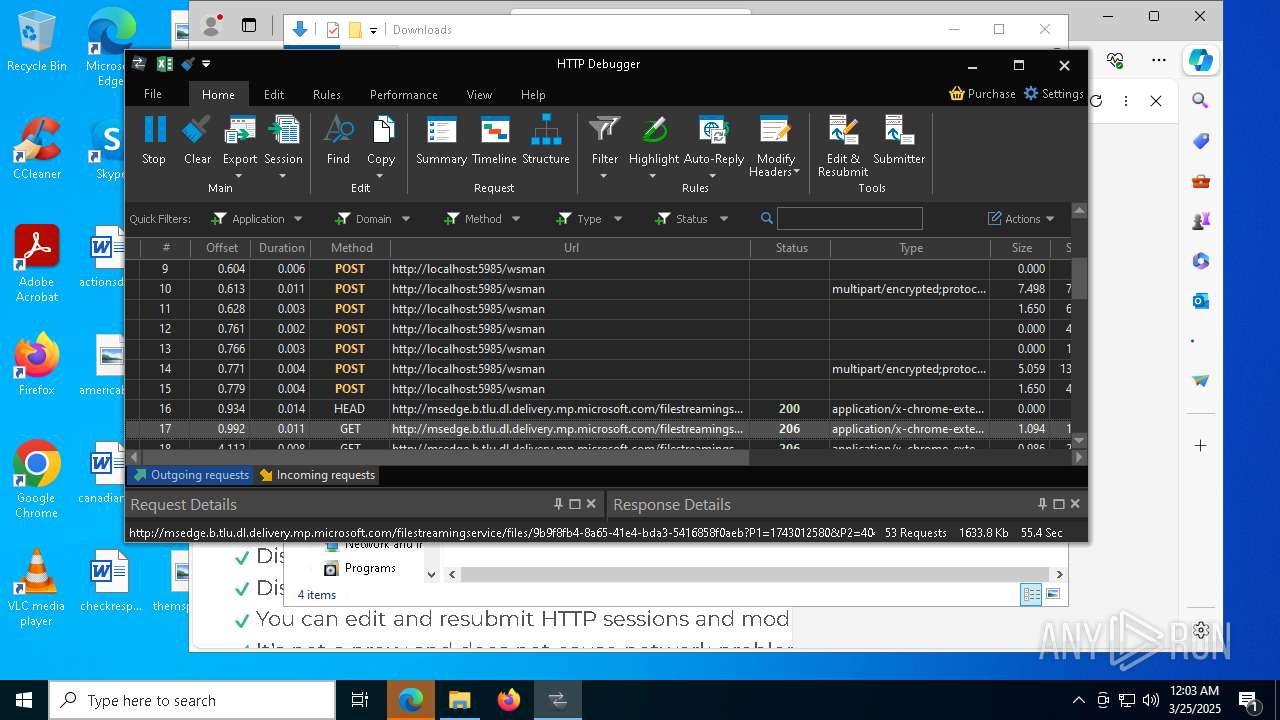
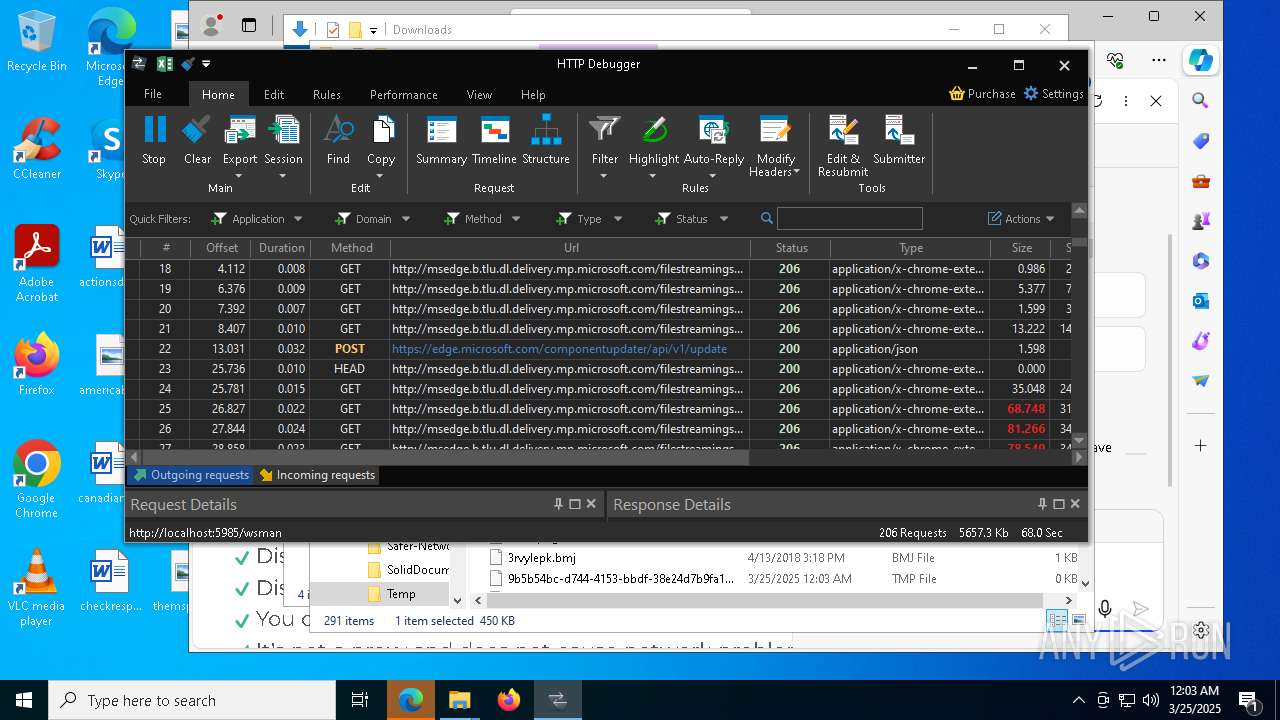
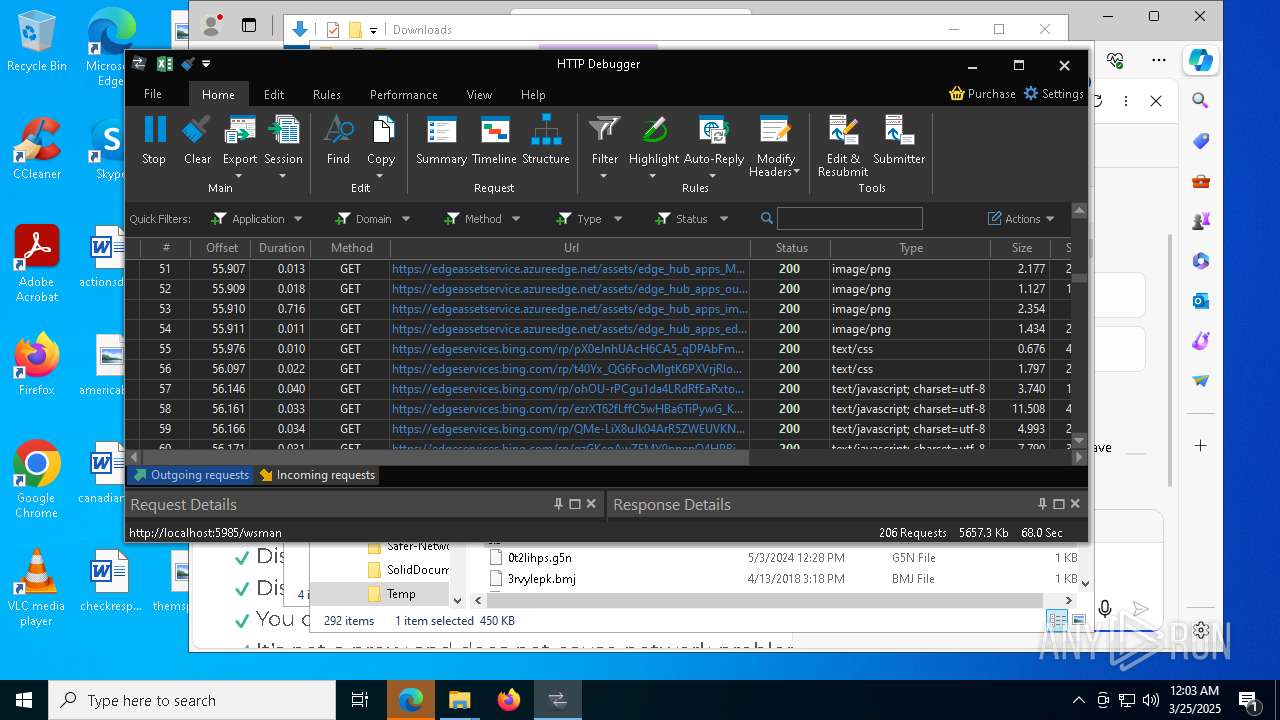
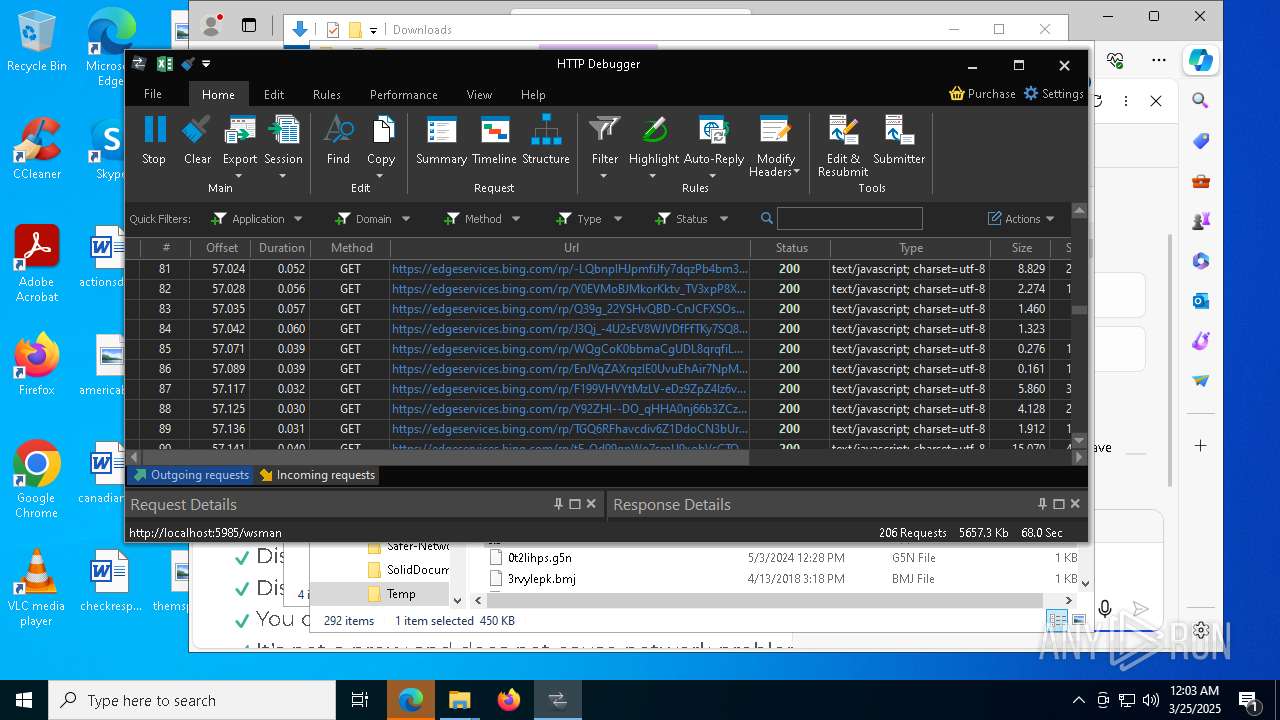
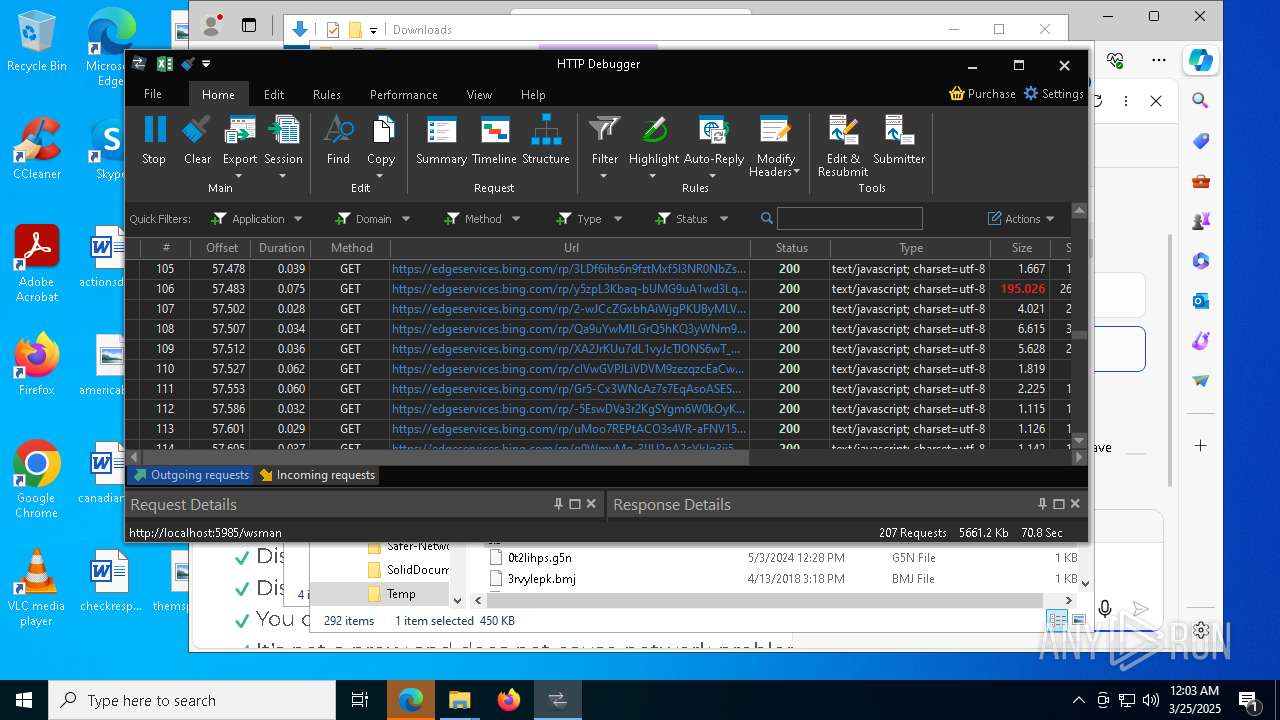
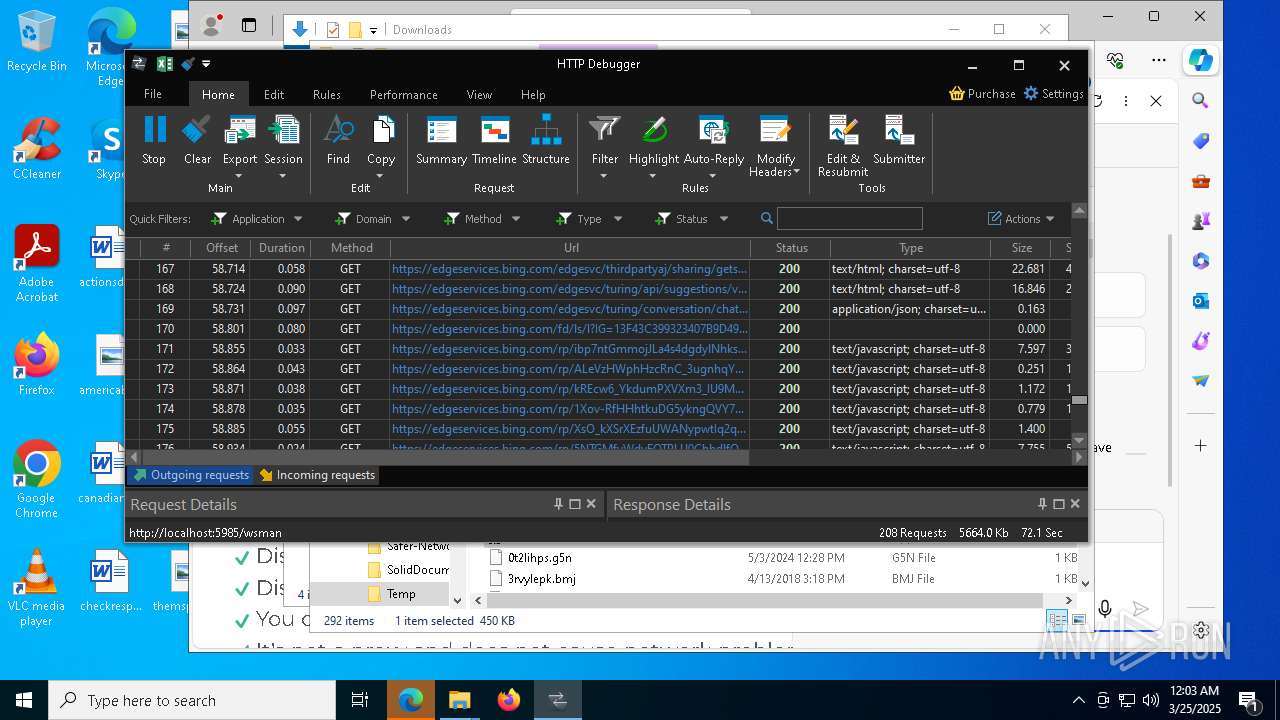
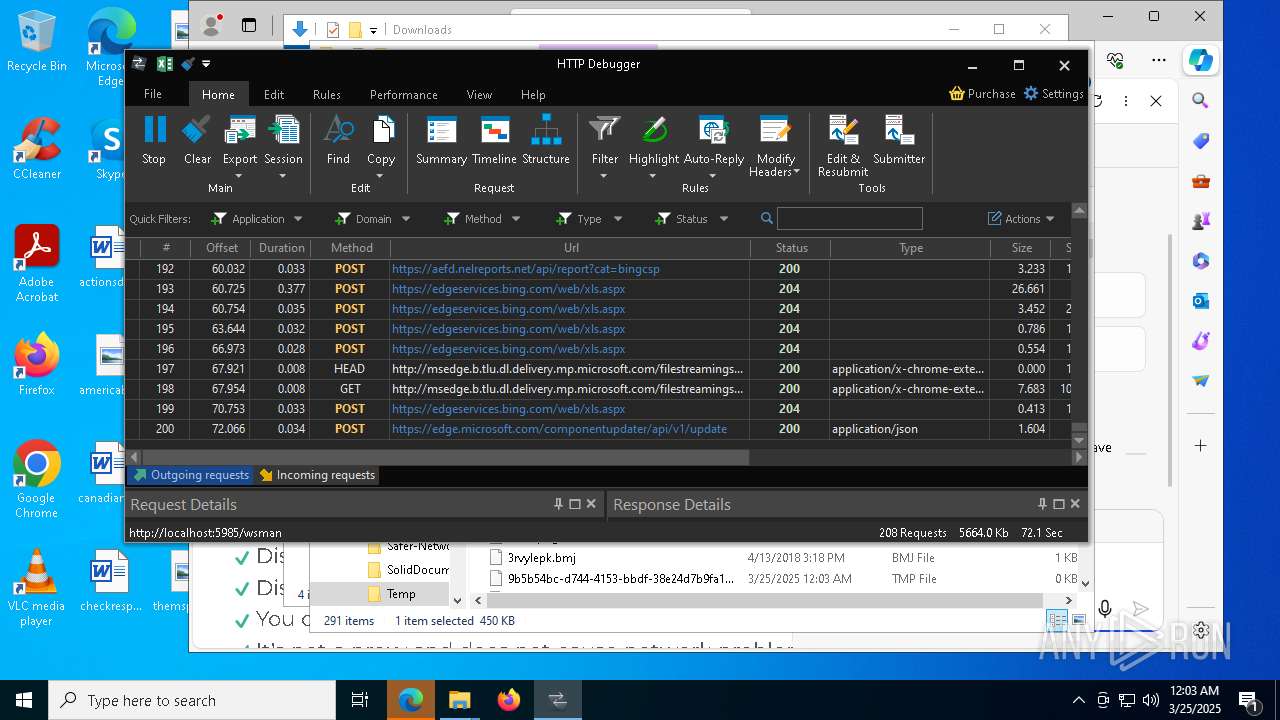
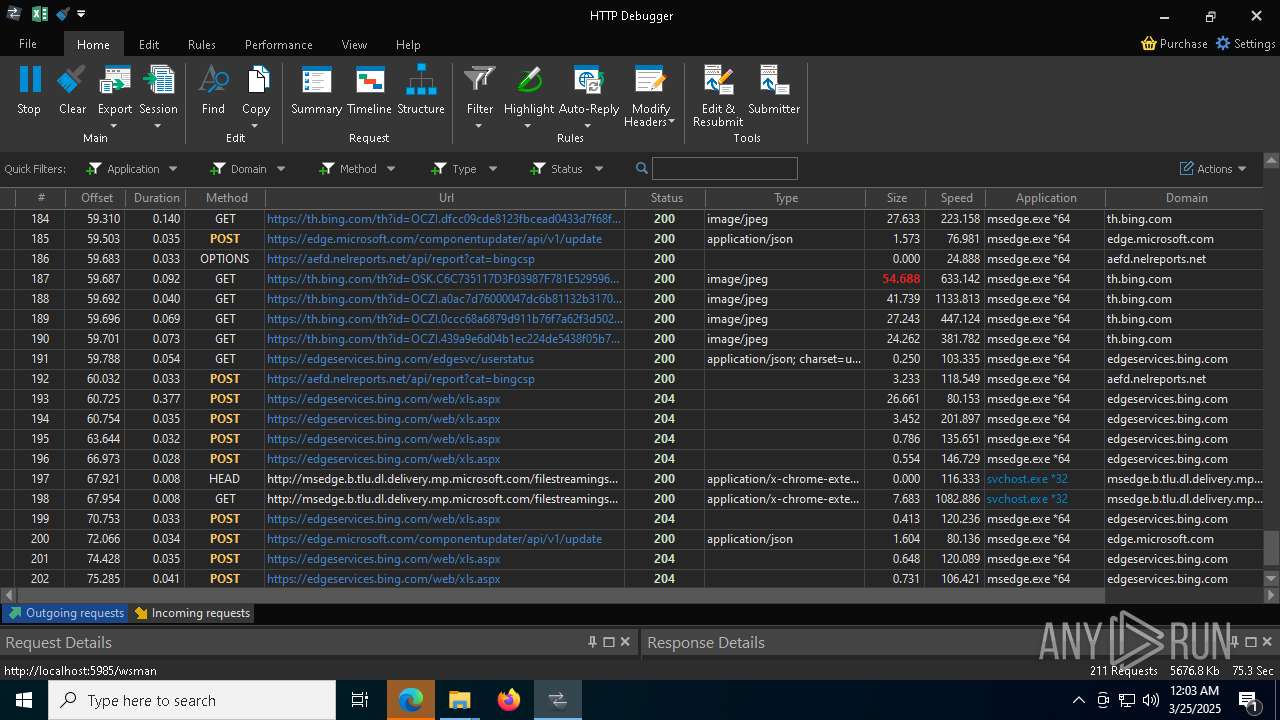
HTTP(S) requests
48
TCP/UDP connections
217
DNS requests
198
Threats
24
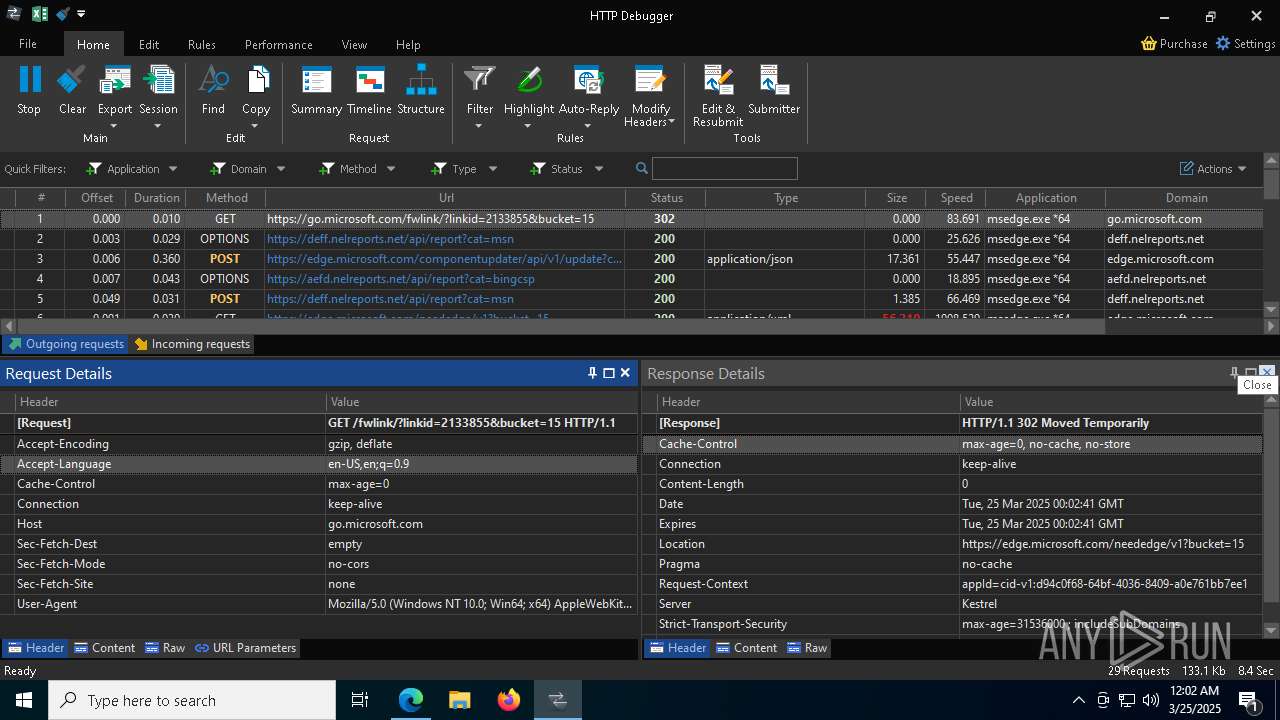
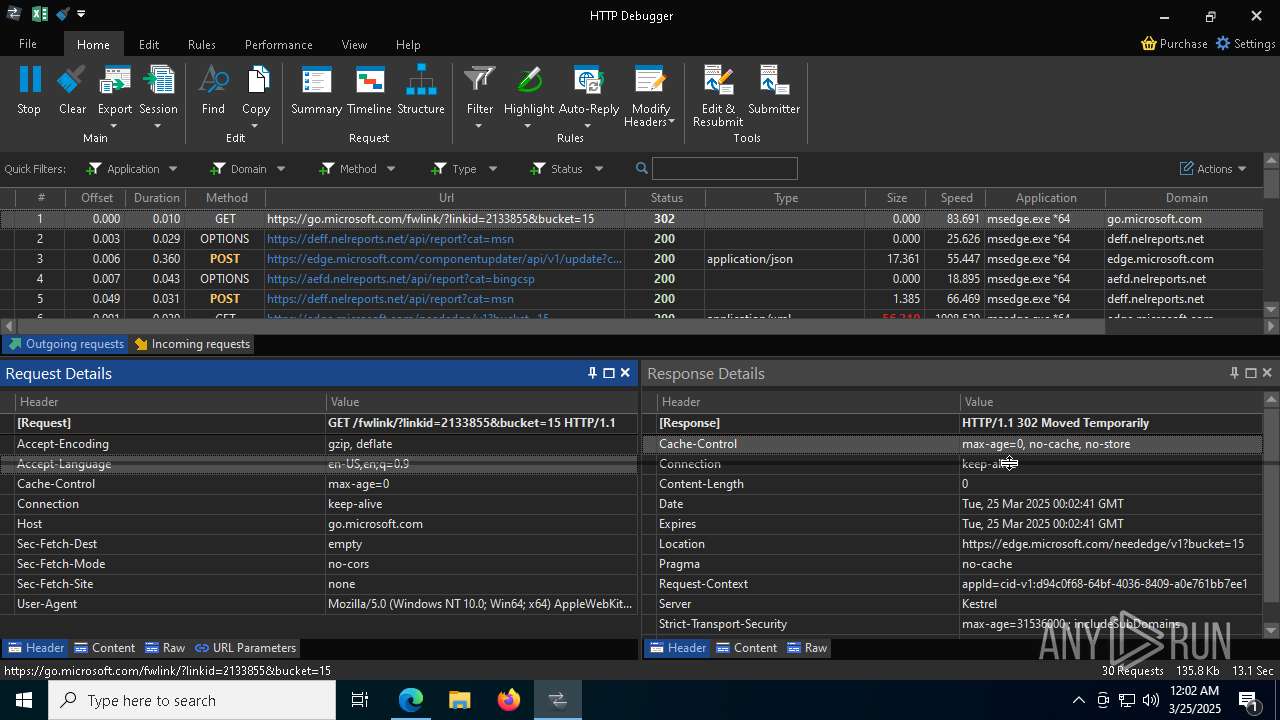
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6112 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | GET | 200 | 142.250.74.195:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | GET | 200 | 142.250.74.195:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | GET | 200 | 142.250.186.99:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEG%2BorlfPZWf5CeqNw%2Flf3jE%3D | unknown | — | — | whitelisted |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | GET | 200 | 142.250.186.99:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEEMozOhYl9J2Ctz332xAY9c%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2420 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | GET | 200 | 132.226.247.73:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | GET | 200 | 132.226.247.73:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6112 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6112 | backgroundTaskHost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
drive.google.com |
| whitelisted |
c.pki.goog |
| whitelisted |
o.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET DYN_DNS External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Device Retrieving External IP Address Detected | ET INFO 404/Snake/Matiex Keylogger Style External IP Check |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Address Lookup Domain (reallyfreegeoip .org) |
2980 | 0ff51f1bfcef0cabf76af8a2c9bb5c01aef4940a97c9b5cebe83cddf62d5be77.exe | Misc activity | ET INFO External IP Lookup Service Domain (reallyfreegeoip .org) in TLS SNI |
2196 | svchost.exe | Misc activity | ET INFO External IP Address Lookup Domain in DNS Lookup (reallyfreegeoip .org) |
2420 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2420 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
2420 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |