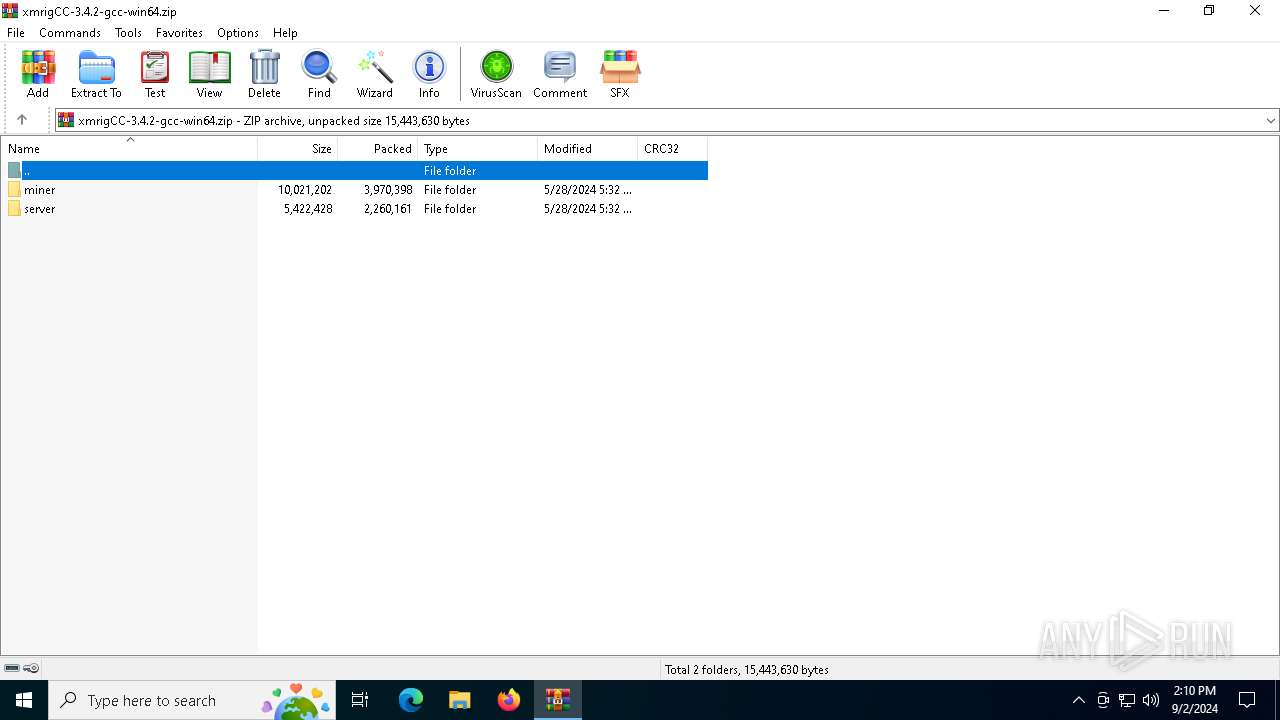
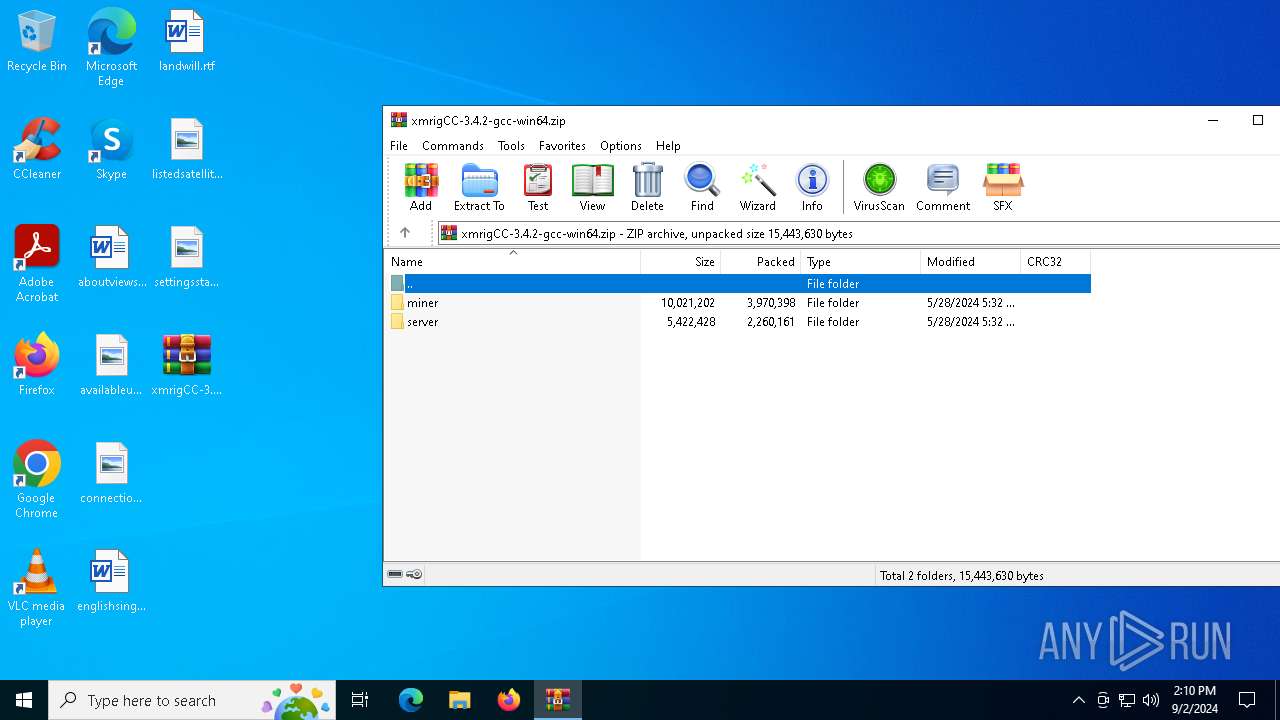
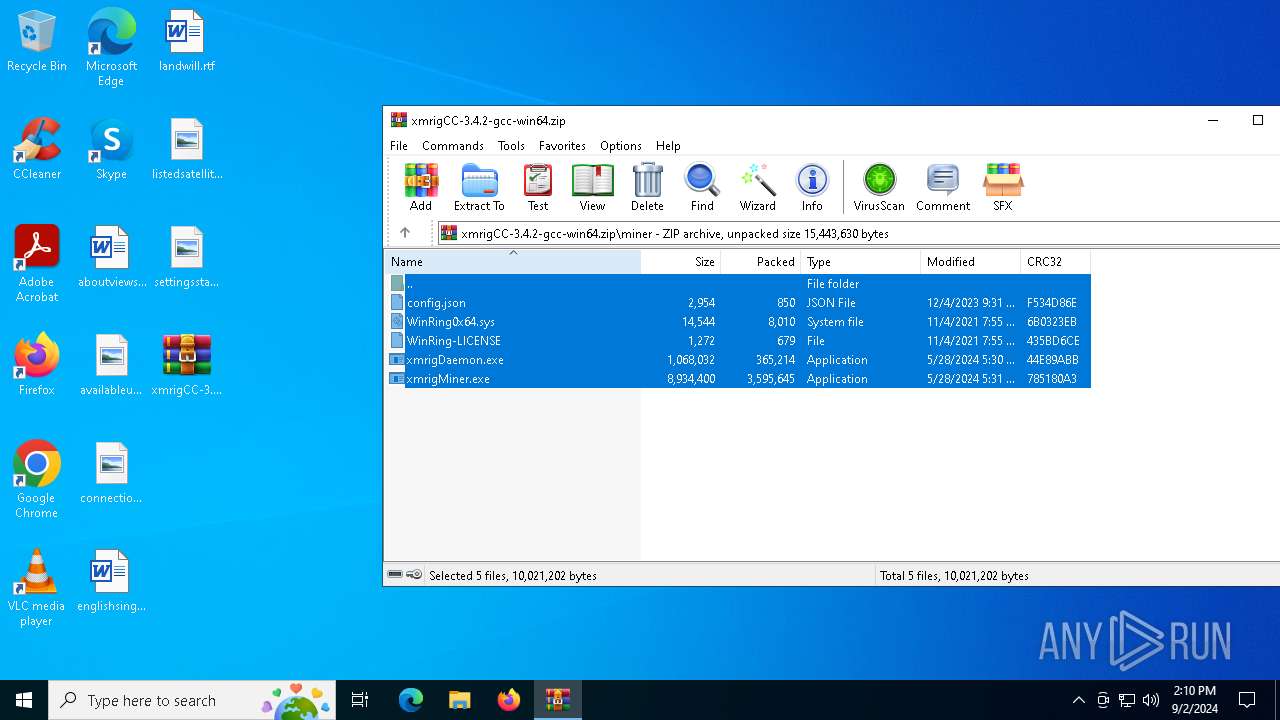
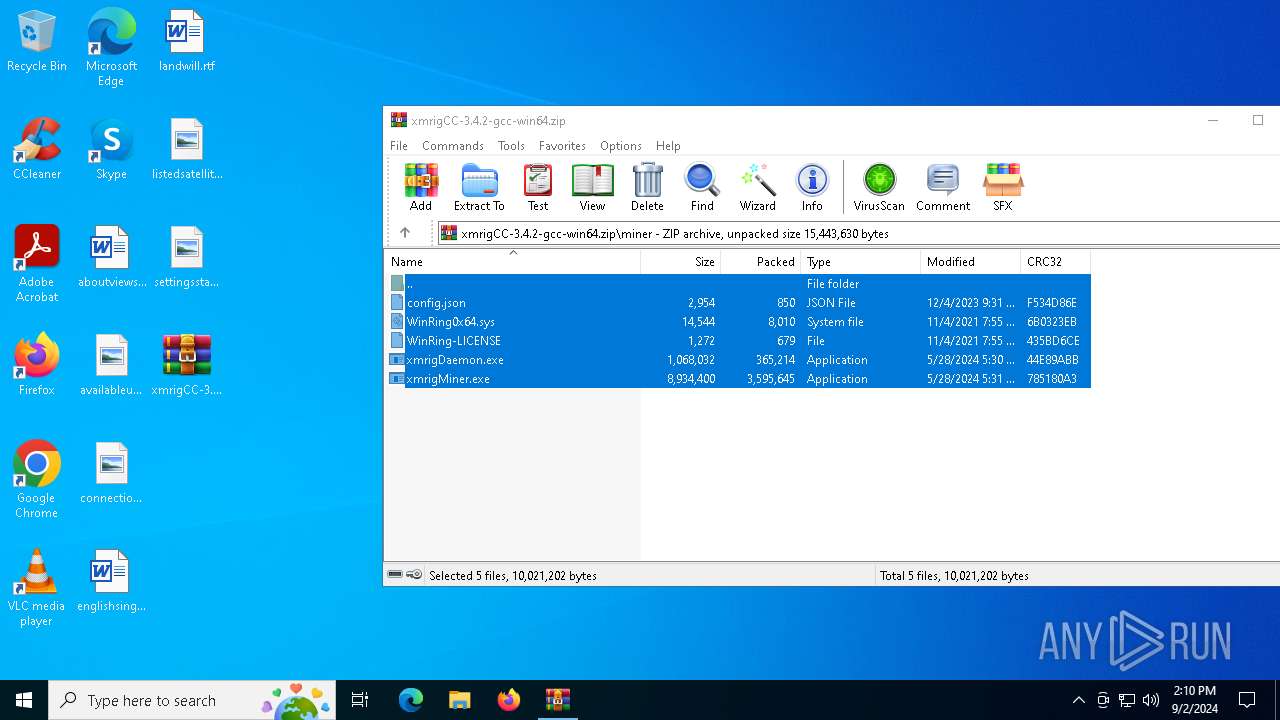
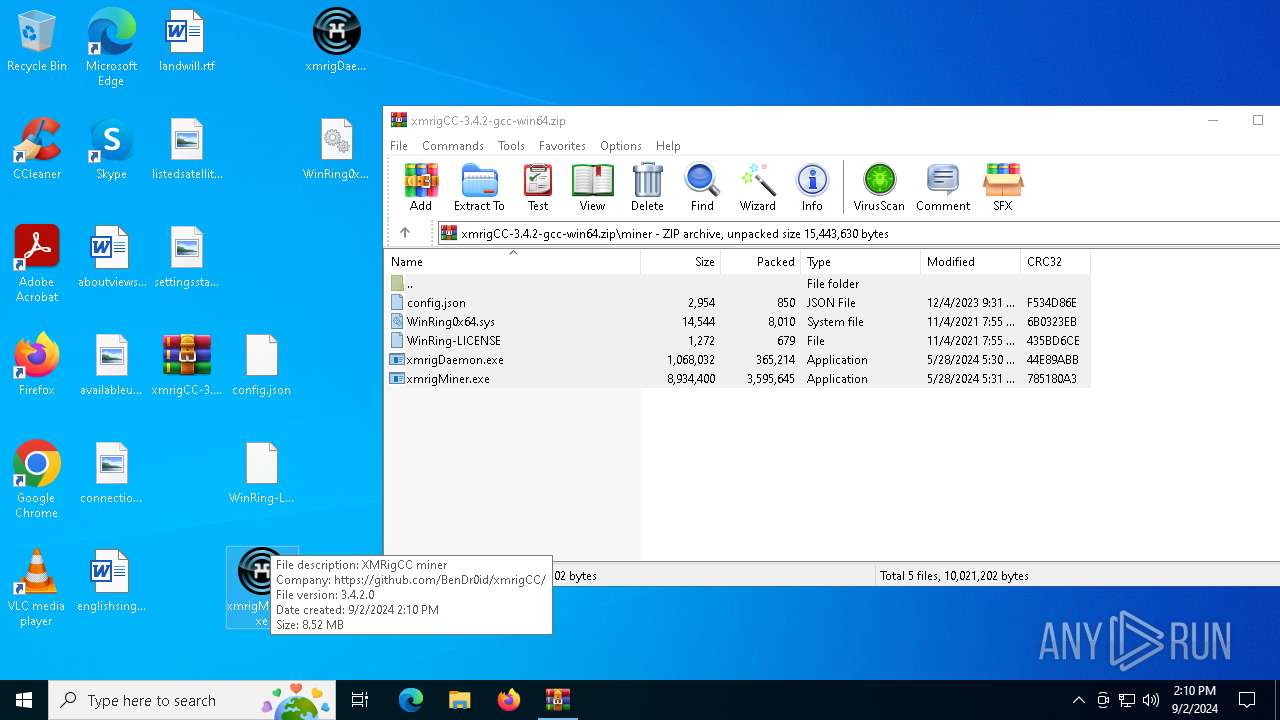
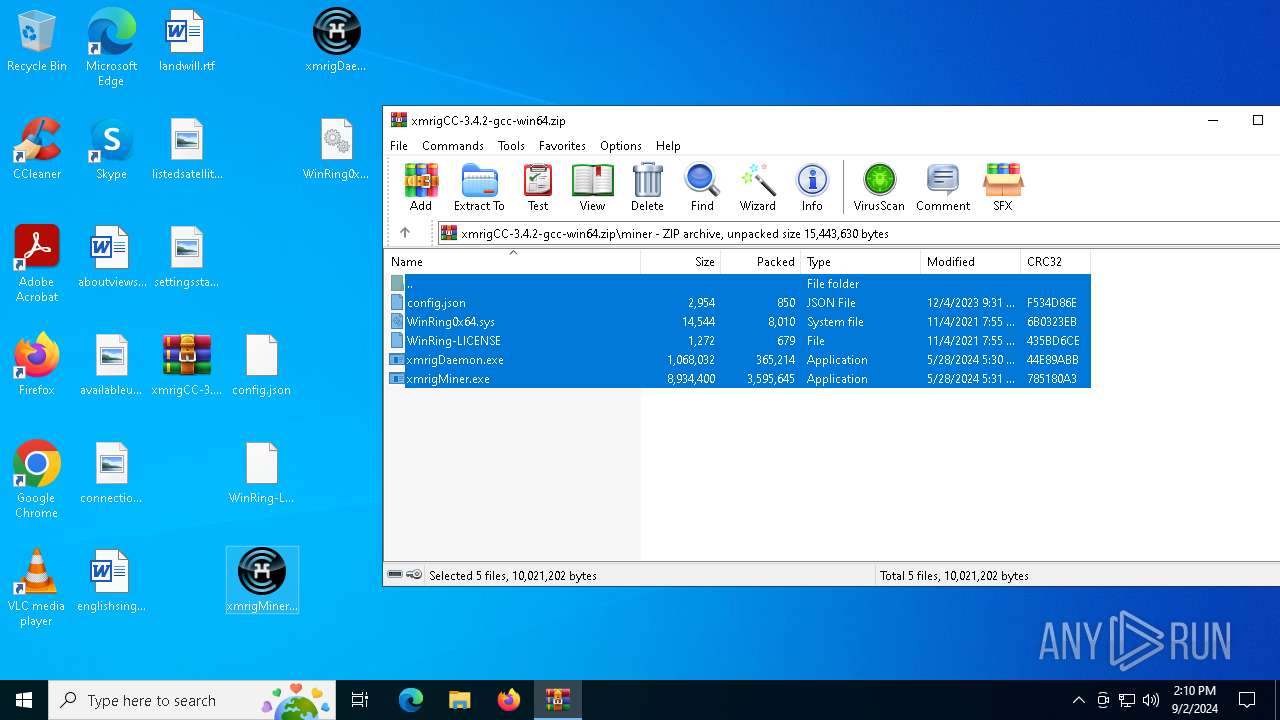
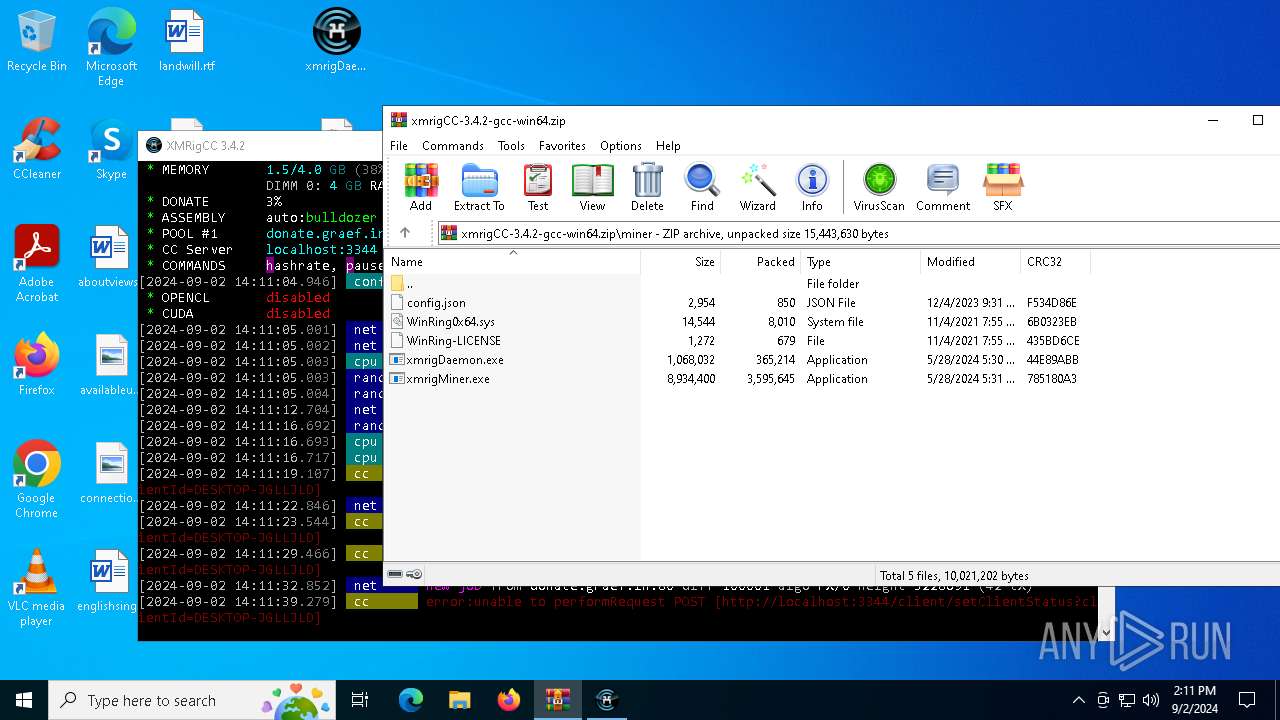
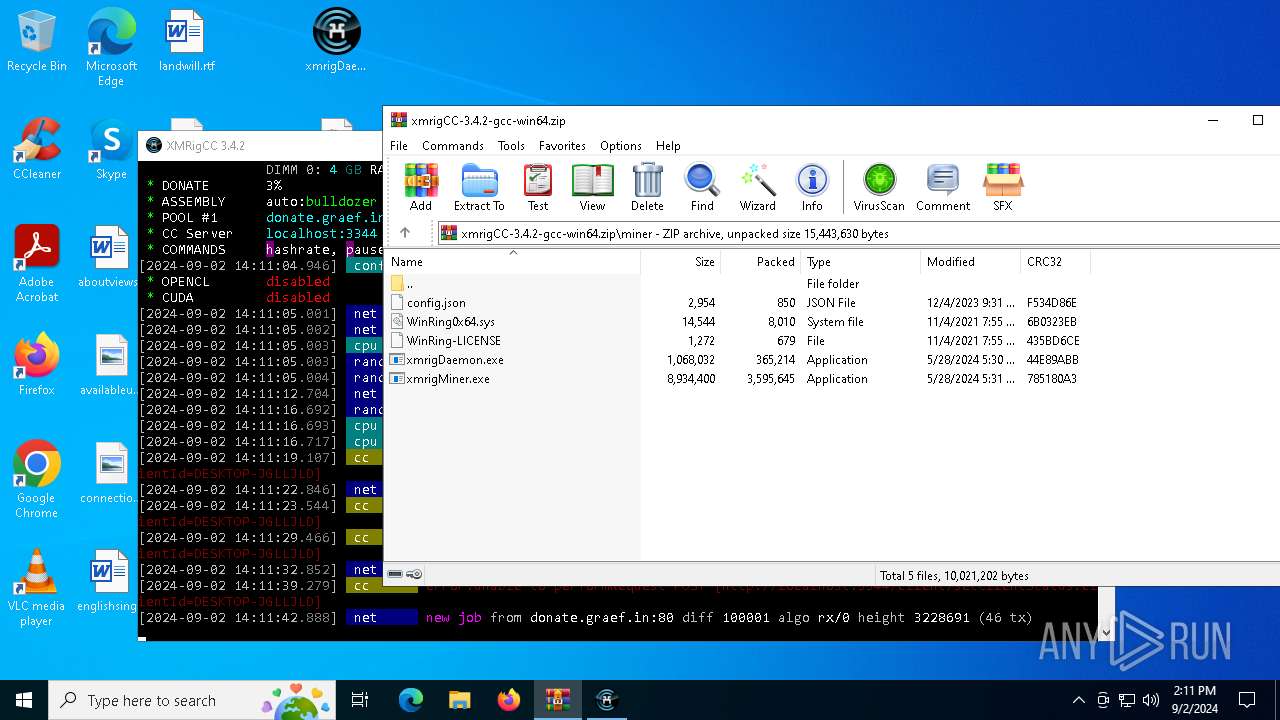
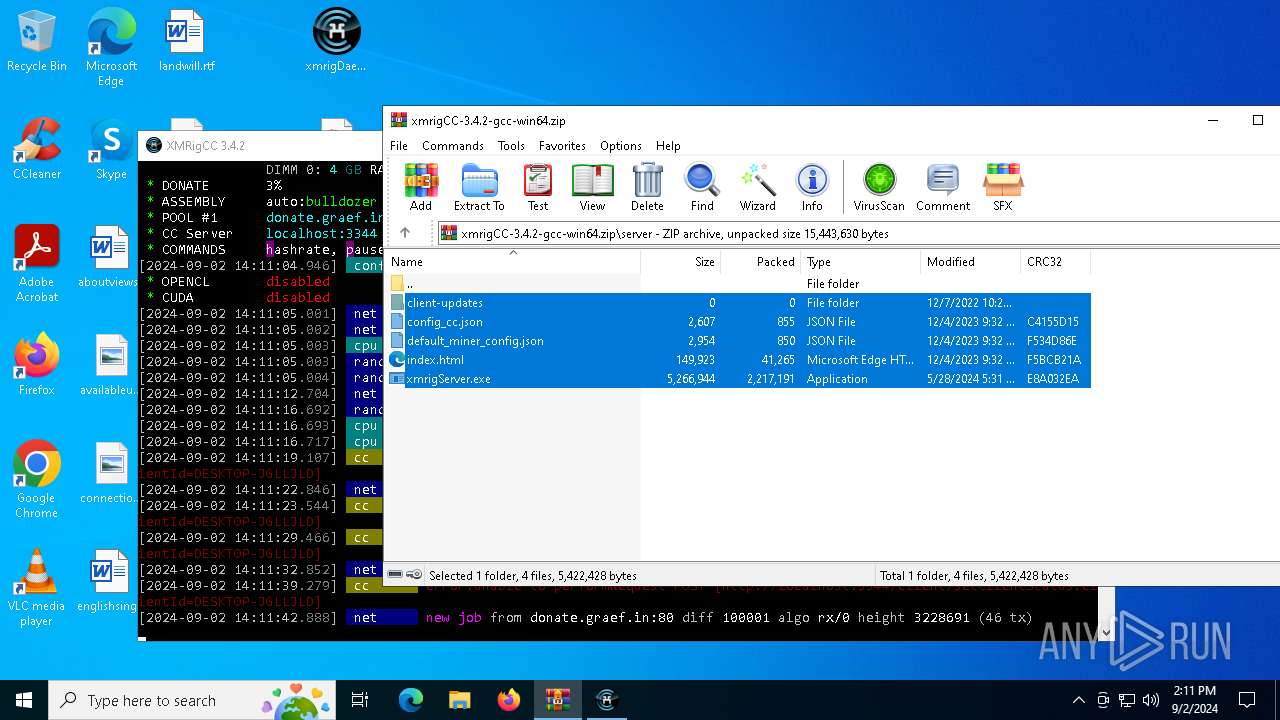
| File name: | xmrigCC-3.4.2-gcc-win64.zip |
| Full analysis: | https://app.any.run/tasks/f15cea70-7572-4148-bc26-b79034e83b08 |
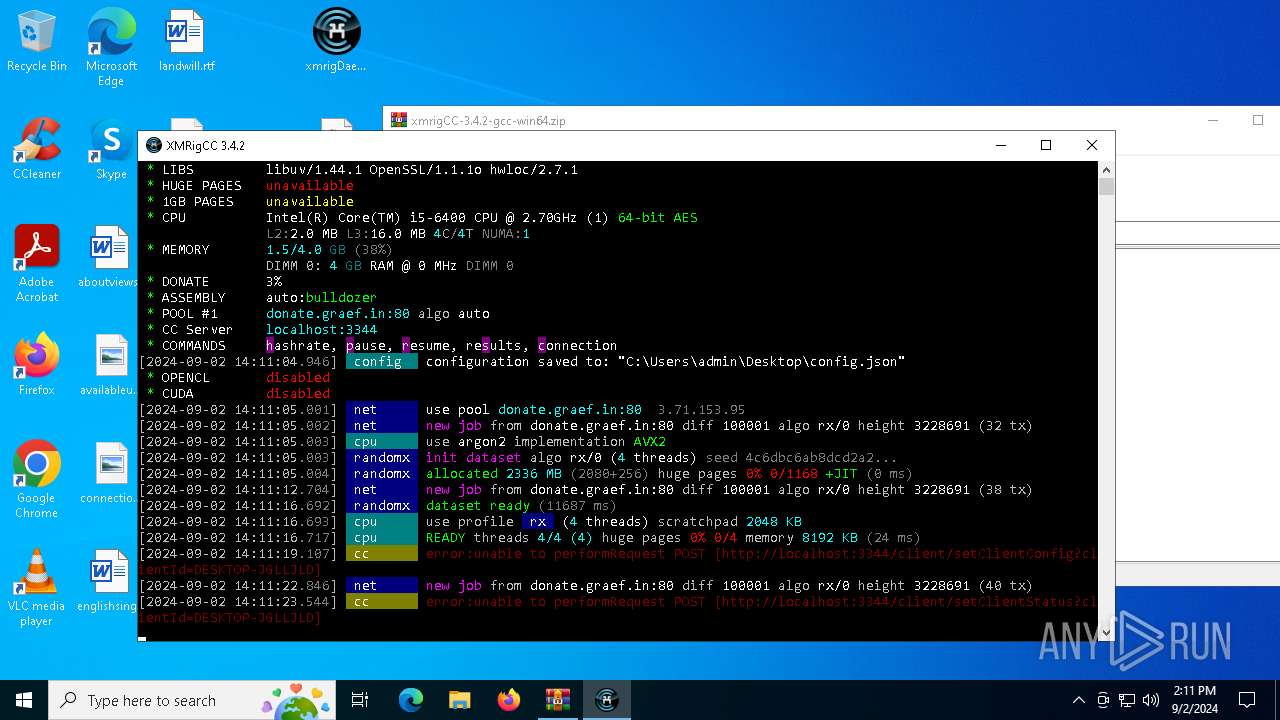
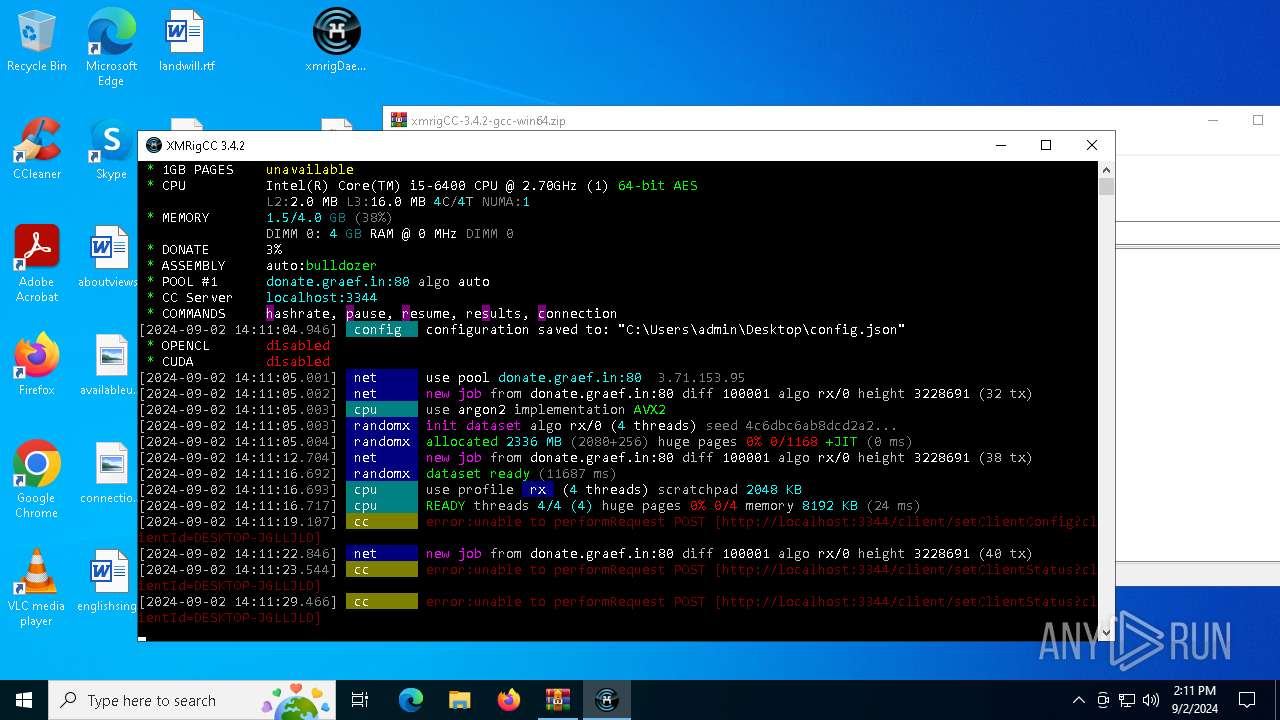
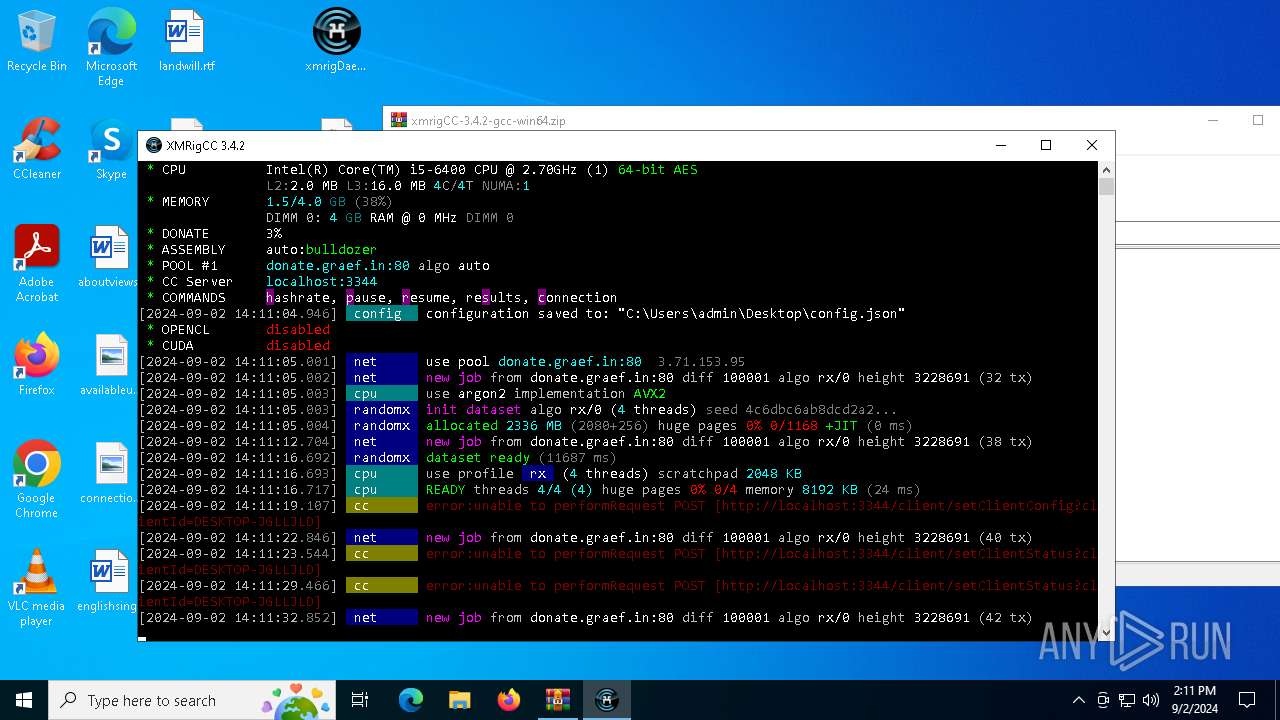
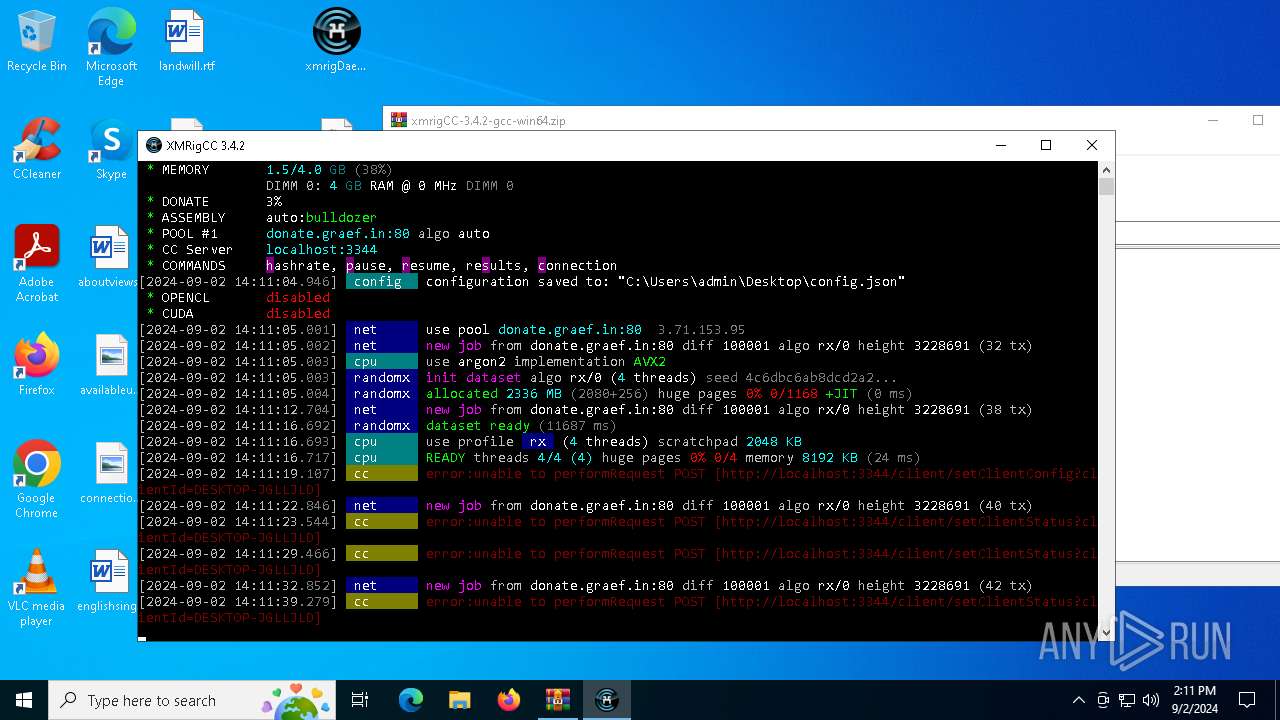
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | September 02, 2024, 14:10:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 35EEA89F28D613640737E798DFC54C86 |
| SHA1: | 47E28EC08B4429A0A6025083D133A9F08805C383 |
| SHA256: | 0F6A044933480ABC8F71DBEB8331B518ED5ED6DB1D8F7939C1590D195623BE2F |
| SSDEEP: | 98304:PZIsfvK1MkohBvDL6saGdyBqghljvdzP0nCCEmKiUMI8a5ET7c0HZgQNxNqFvY7/:dGn6m42Hu7E+ue9WM |
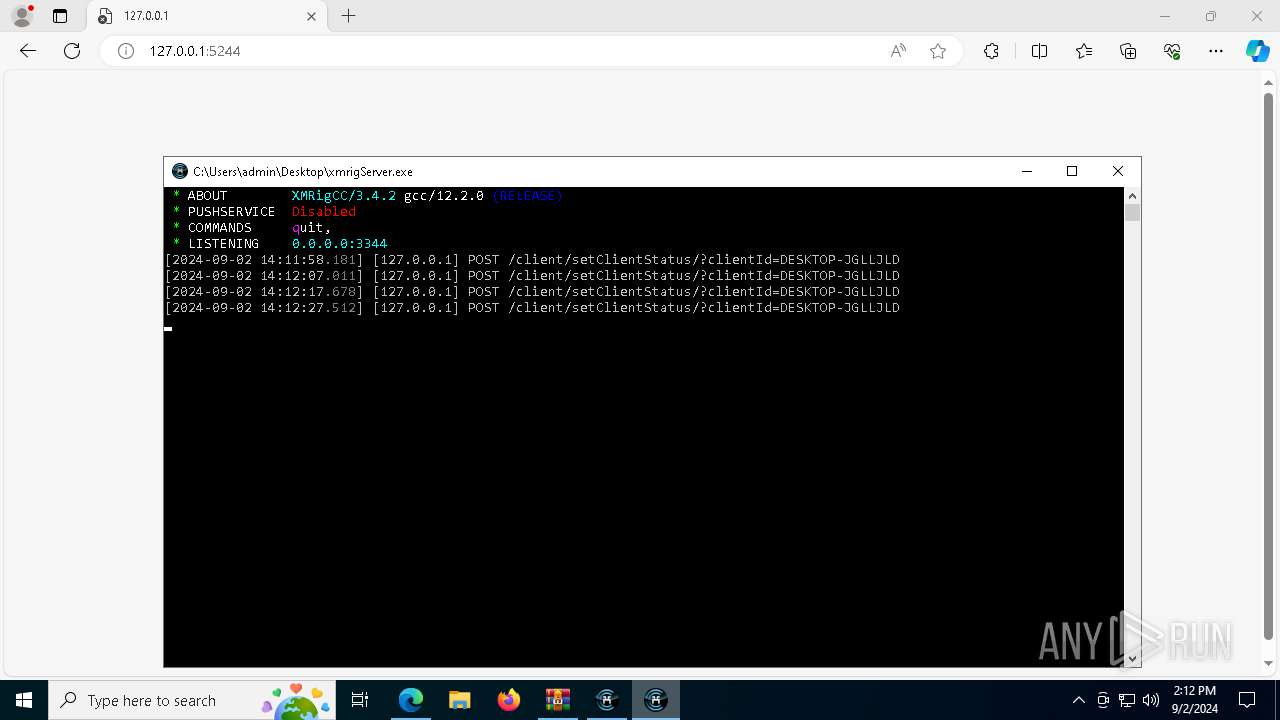
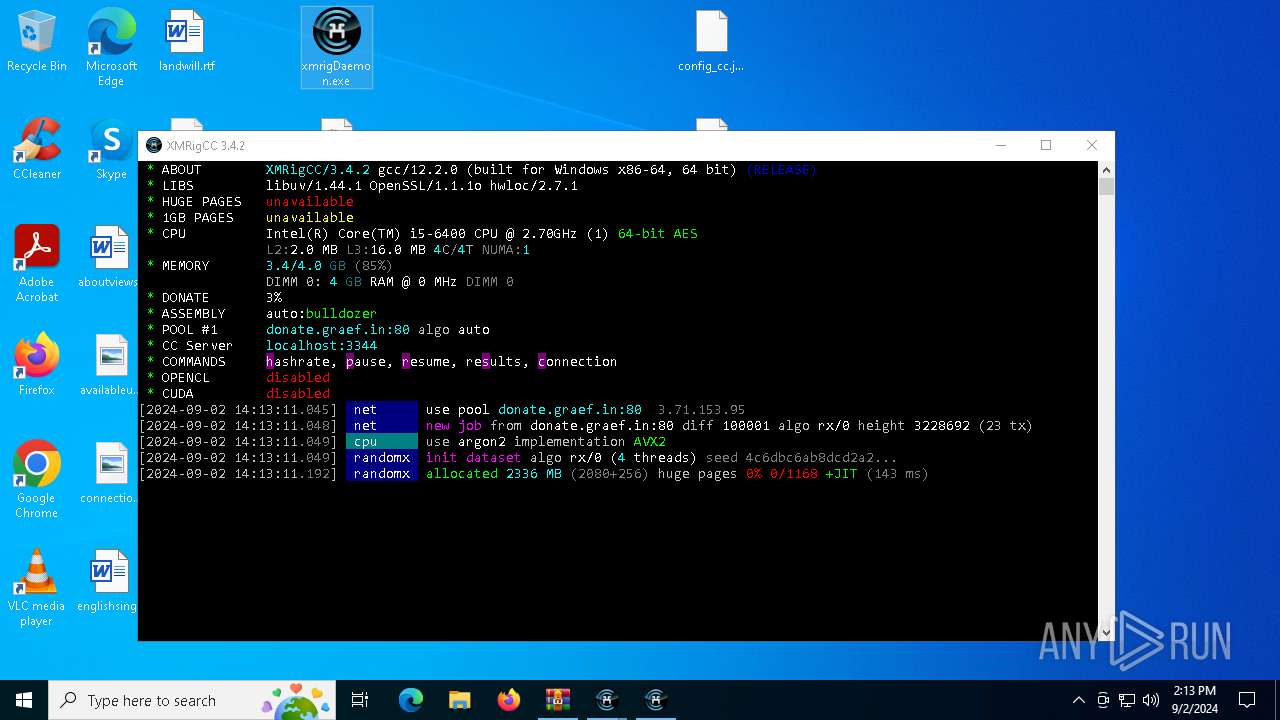
MALICIOUS
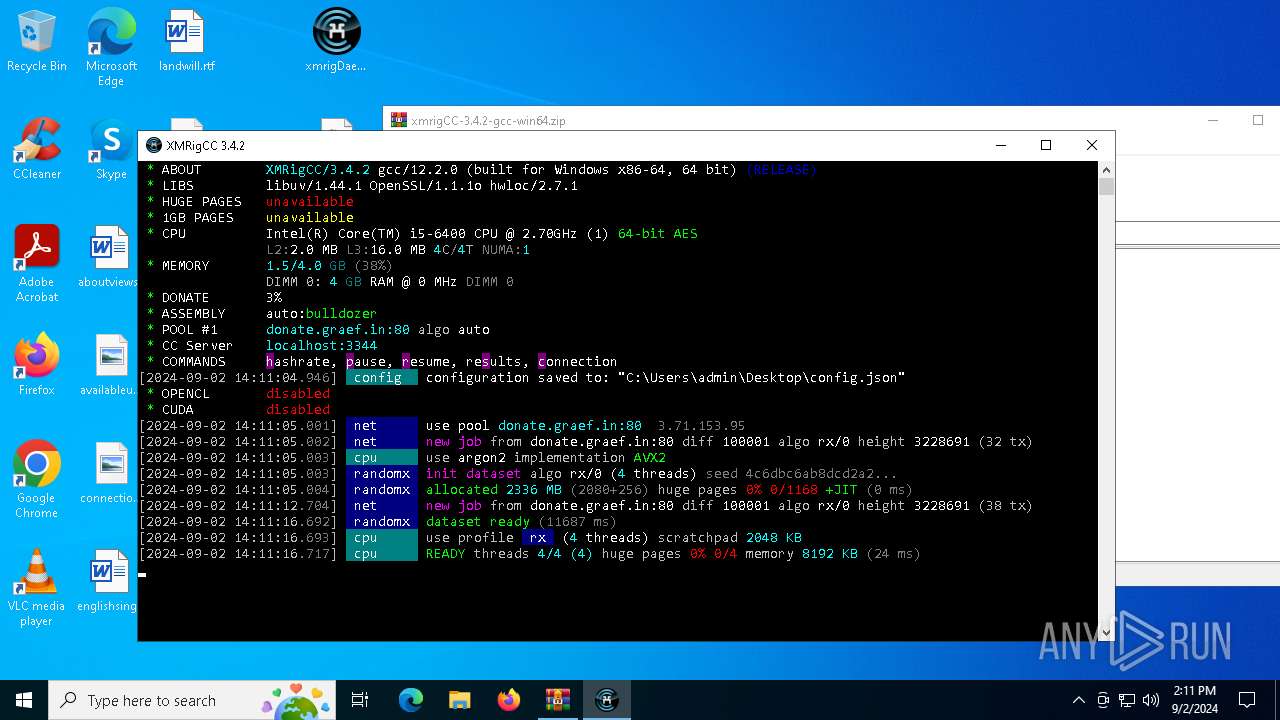
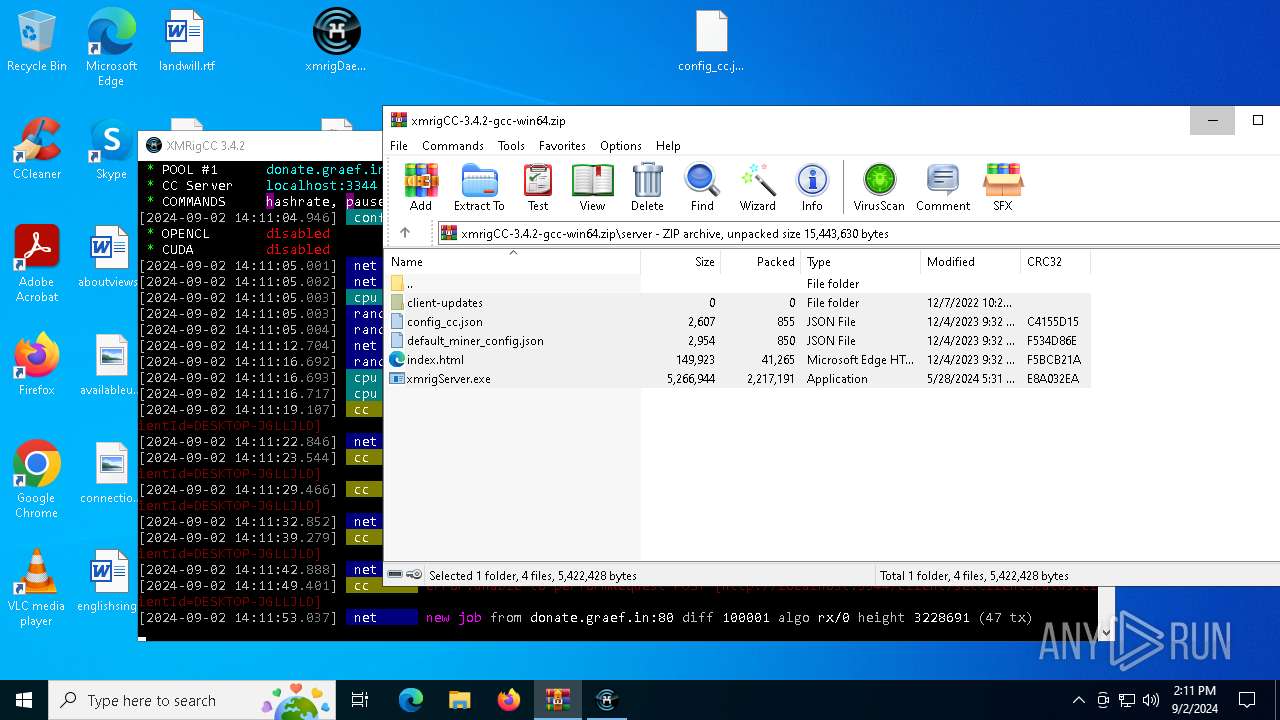
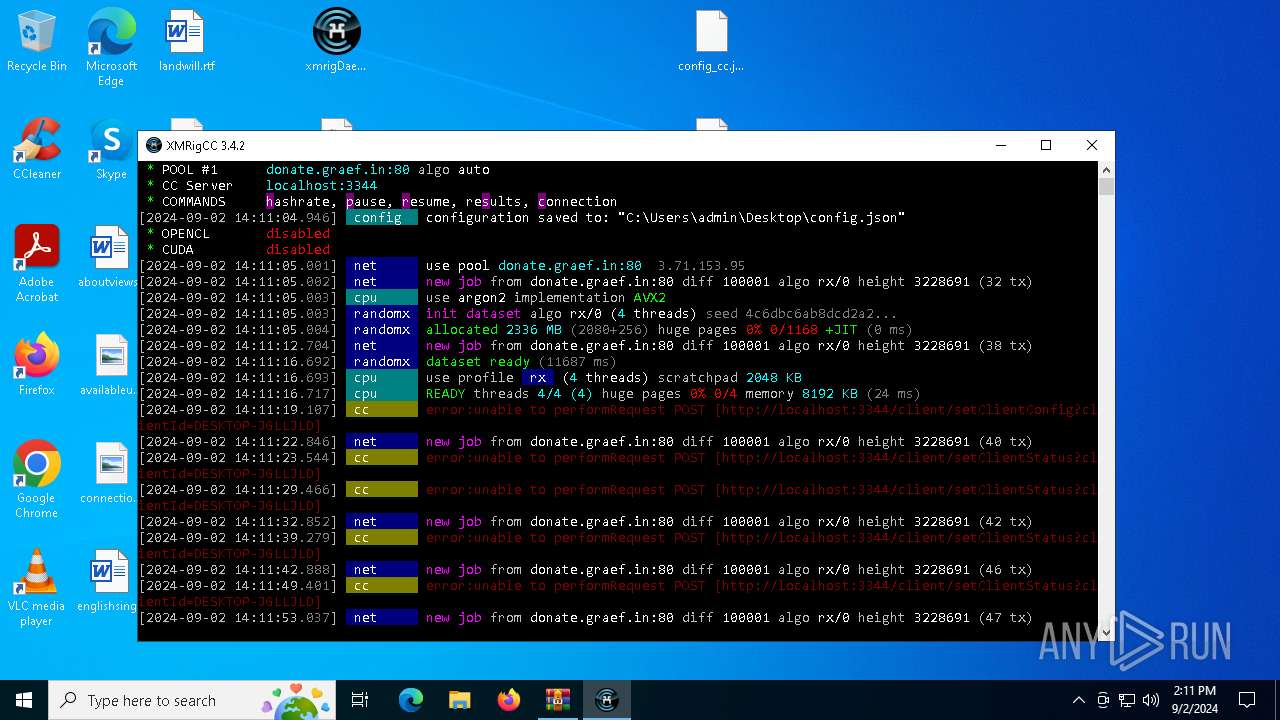
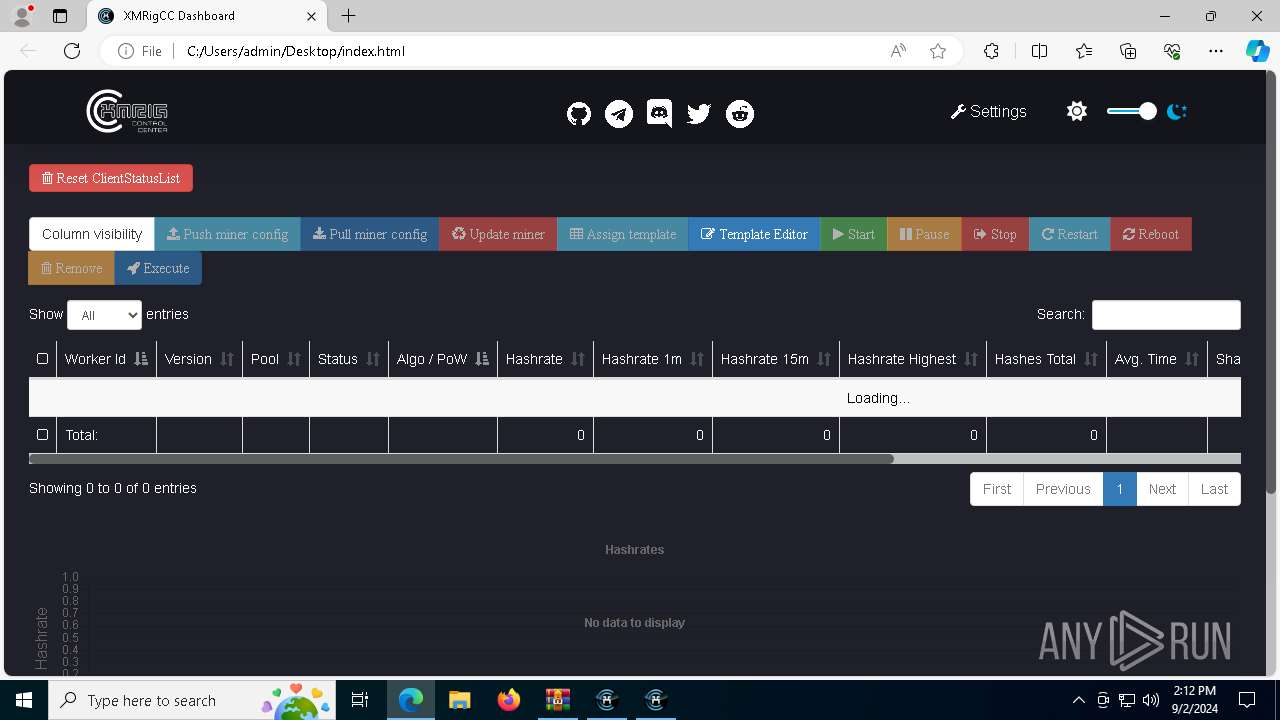
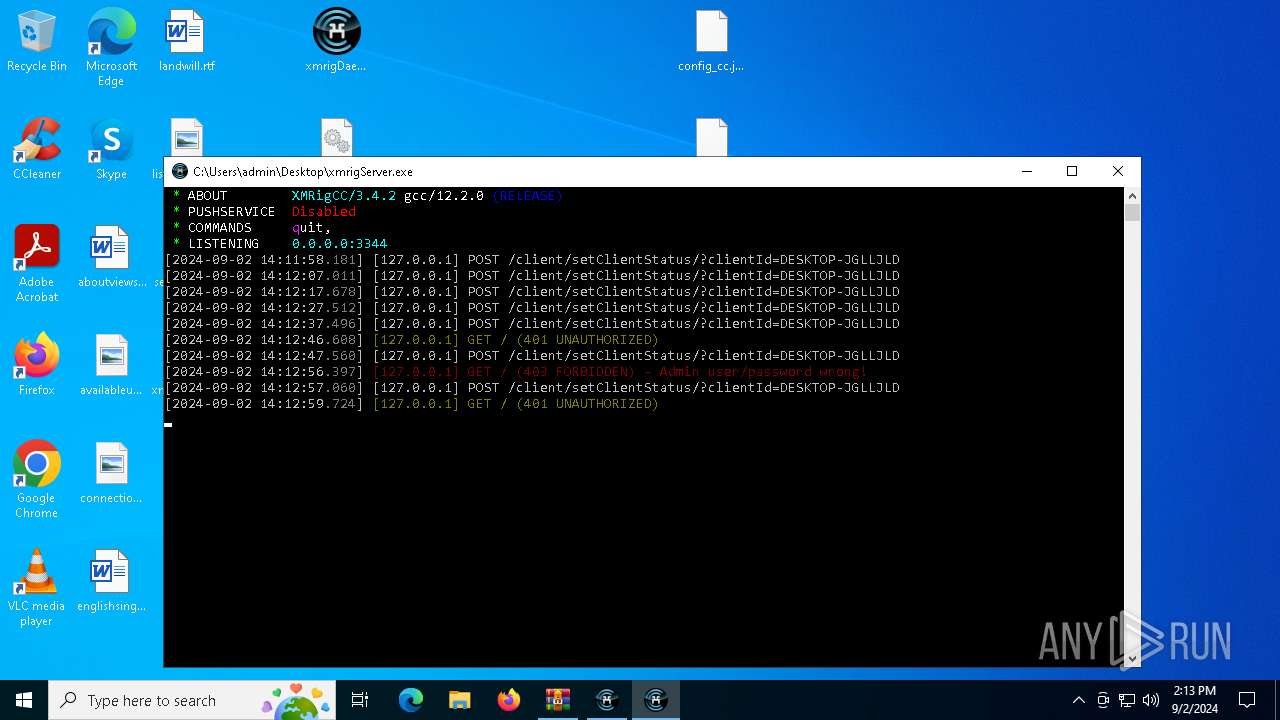
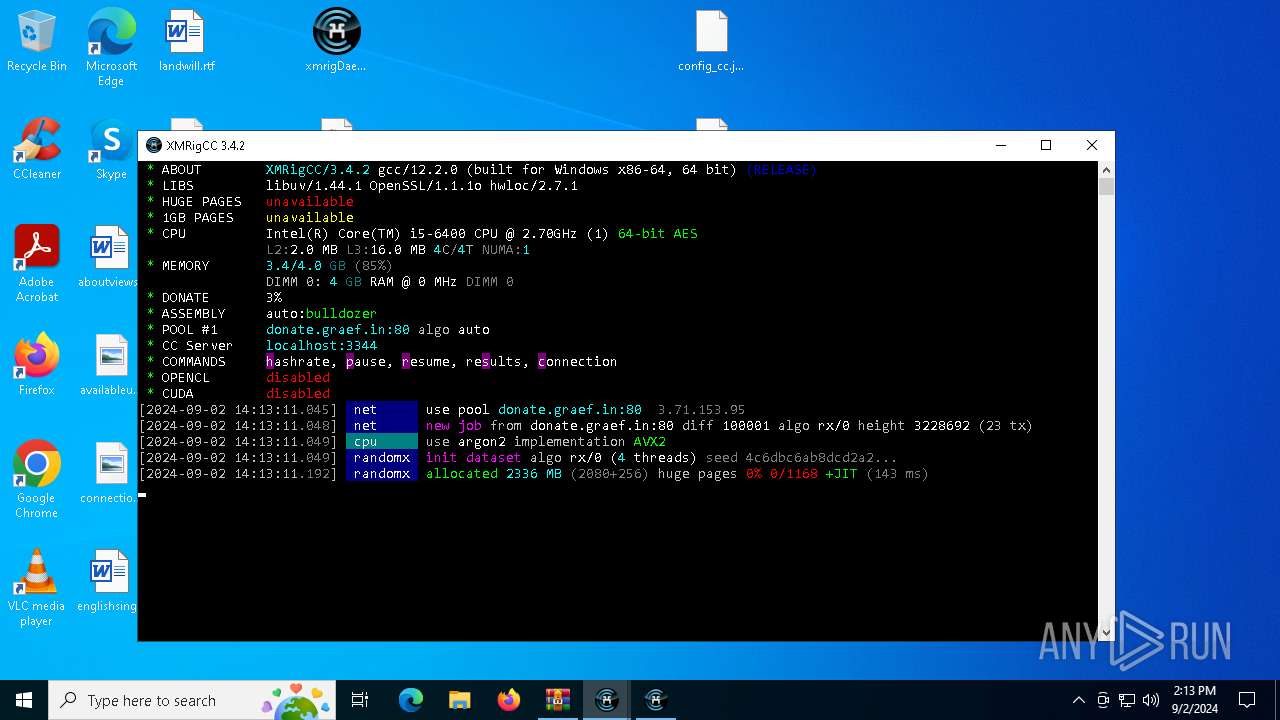
MINER has been detected (SURICATA)
- xmrigMiner.exe (PID: 5888)
- xmrigMiner.exe (PID: 6872)
Connects to the CnC server
- xmrigMiner.exe (PID: 5888)
- xmrigMiner.exe (PID: 6872)
SUSPICIOUS
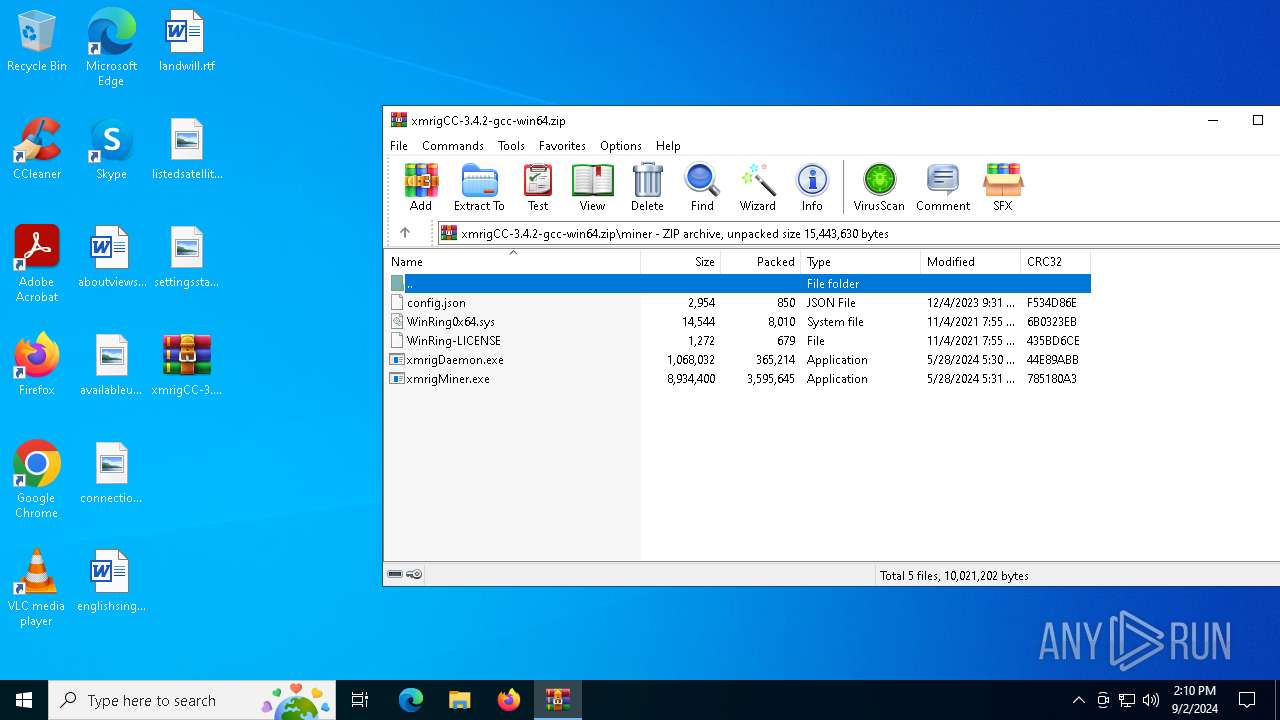
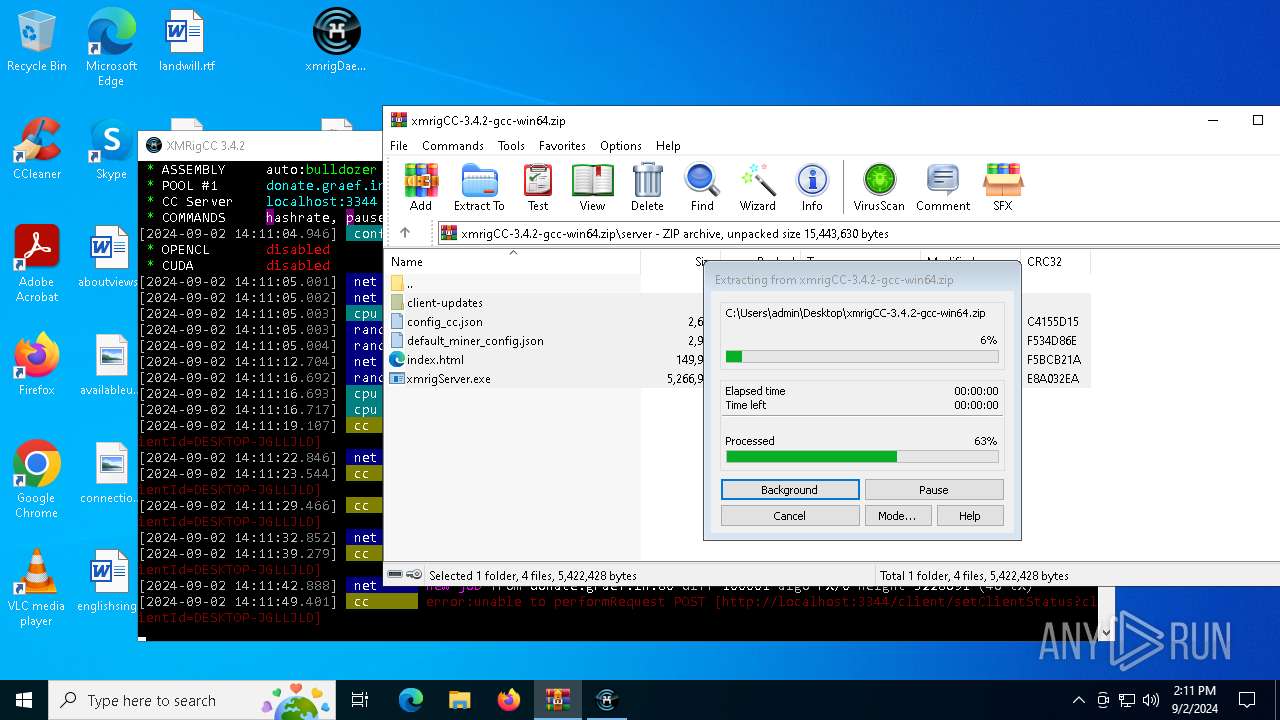
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 2112)
Starts CMD.EXE for commands execution
- xmrigDaemon.exe (PID: 2388)
- xmrigDaemon.exe (PID: 7316)
- xmrigDaemon.exe (PID: 7560)
- xmrigDaemon.exe (PID: 1436)
- xmrigDaemon.exe (PID: 7836)
- xmrigDaemon.exe (PID: 1232)
- xmrigDaemon.exe (PID: 6960)
- xmrigDaemon.exe (PID: 4072)
- xmrigDaemon.exe (PID: 2568)
- xmrigDaemon.exe (PID: 3568)
- xmrigDaemon.exe (PID: 7528)
Potential Corporate Privacy Violation
- xmrigMiner.exe (PID: 5888)
- xmrigMiner.exe (PID: 6872)
INFO
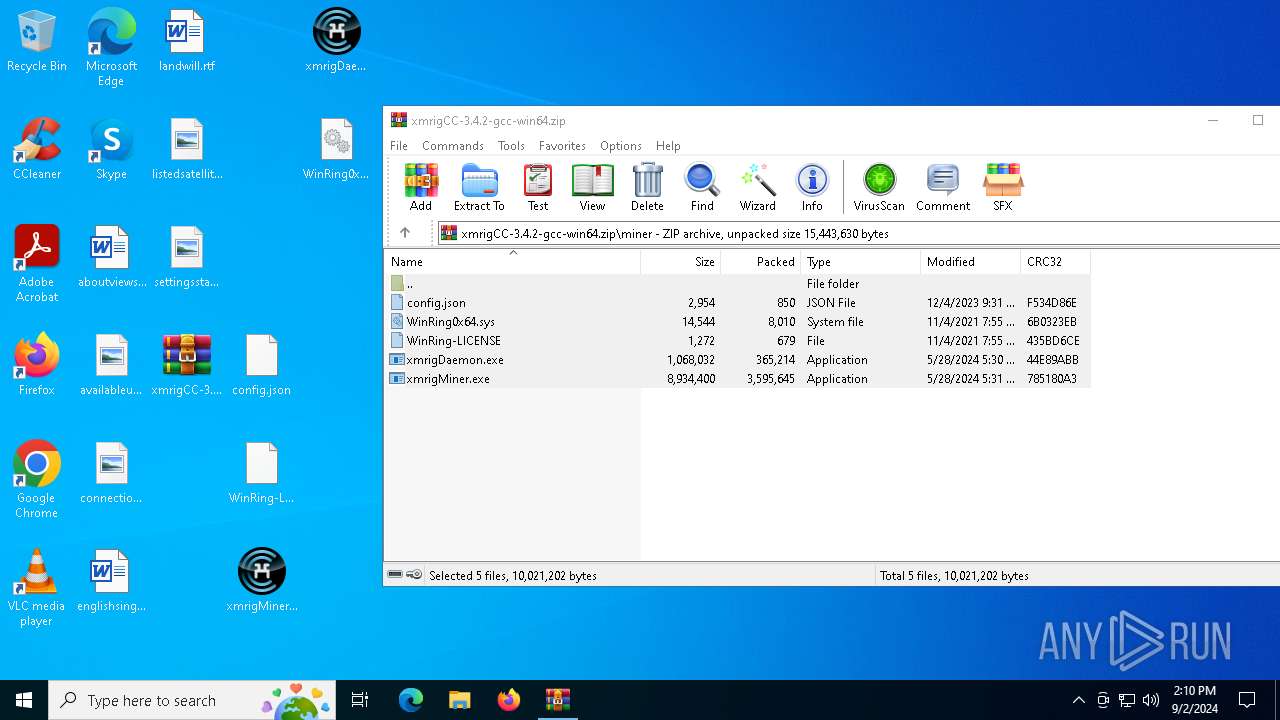
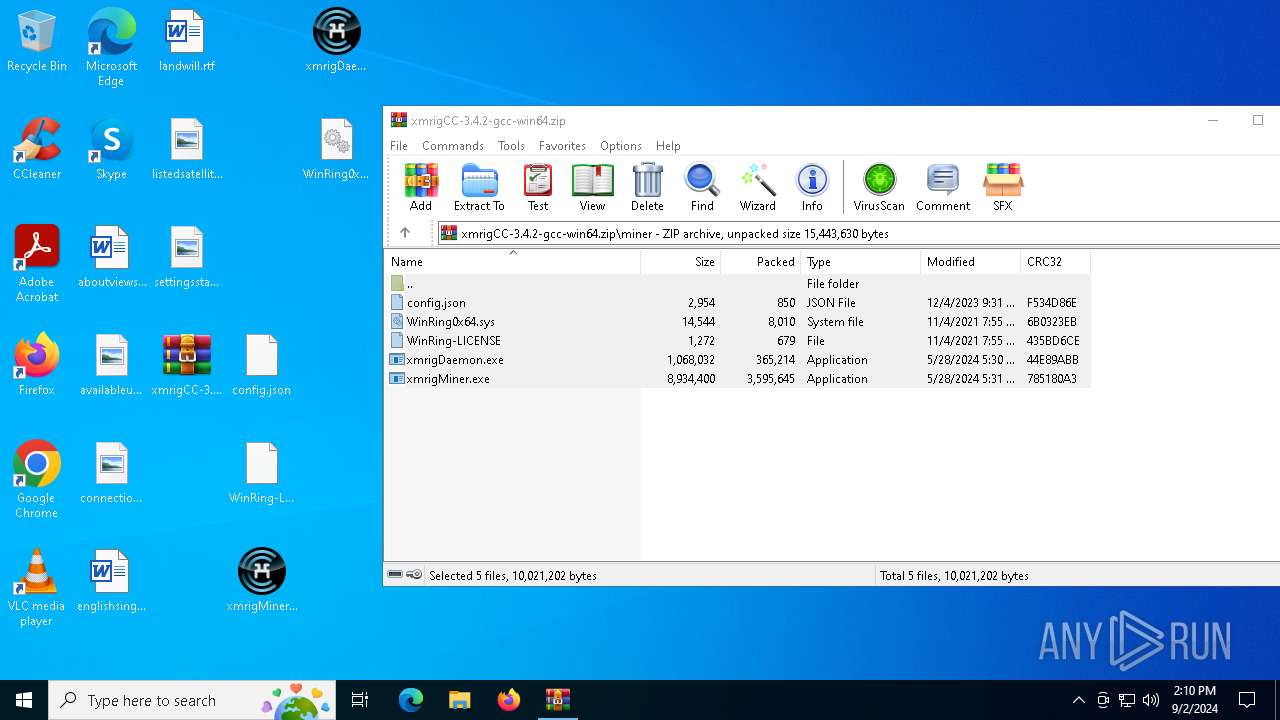
The process uses the downloaded file
- WinRAR.exe (PID: 2112)
Checks supported languages
- xmrigMiner.exe (PID: 1608)
- xmrigDaemon.exe (PID: 2388)
- xmrigMiner.exe (PID: 5888)
- xmrigServer.exe (PID: 6756)
- identity_helper.exe (PID: 8148)
- identity_helper.exe (PID: 7008)
- xmrigMiner.exe (PID: 6872)
- xmrigDaemon.exe (PID: 7316)
- xmrigDaemon.exe (PID: 4072)
- xmrigDaemon.exe (PID: 7560)
- xmrigDaemon.exe (PID: 1436)
- xmrigDaemon.exe (PID: 1232)
- xmrigDaemon.exe (PID: 7836)
- xmrigDaemon.exe (PID: 6960)
- xmrigDaemon.exe (PID: 2568)
- xmrigMiner.exe (PID: 8232)
- xmrigDaemon.exe (PID: 3568)
- xmrigMiner.exe (PID: 8344)
- xmrigMiner.exe (PID: 8360)
- xmrigMiner.exe (PID: 8392)
- xmrigMiner.exe (PID: 8408)
- xmrigMiner.exe (PID: 8416)
- xmrigMiner.exe (PID: 8436)
- xmrigMiner.exe (PID: 8400)
- xmrigDaemon.exe (PID: 7528)
- xmrigMiner.exe (PID: 8464)
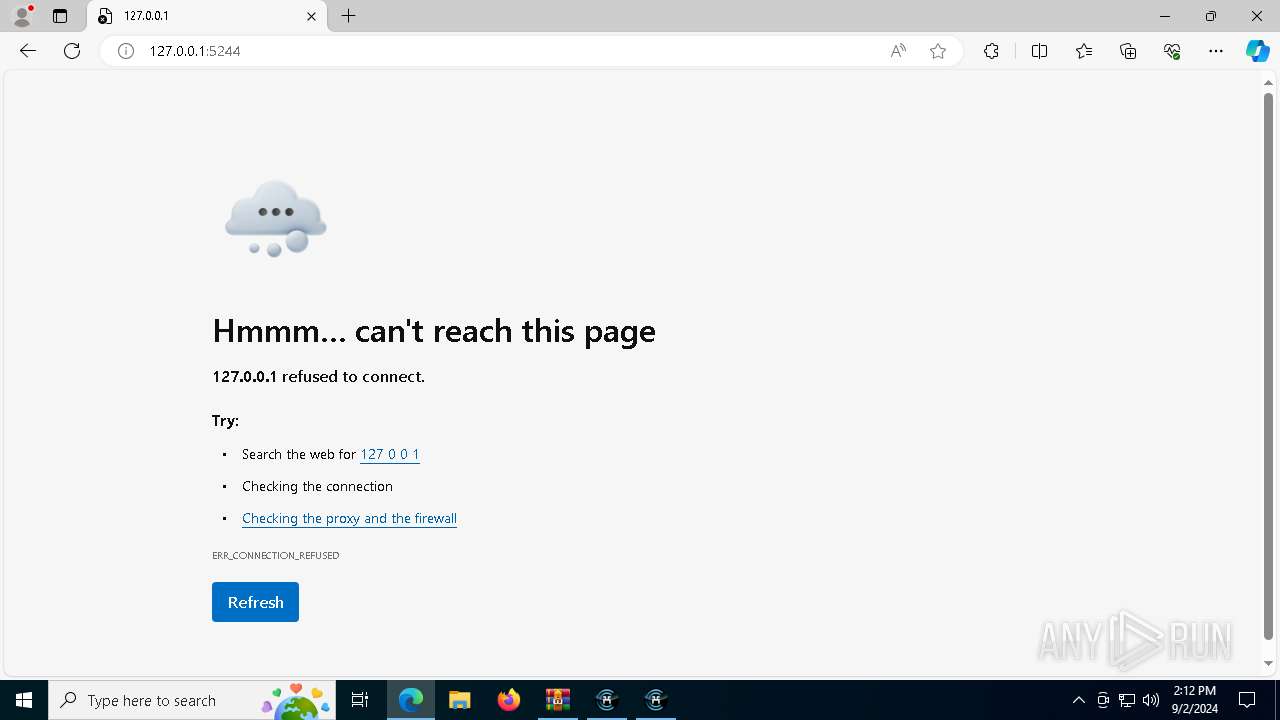
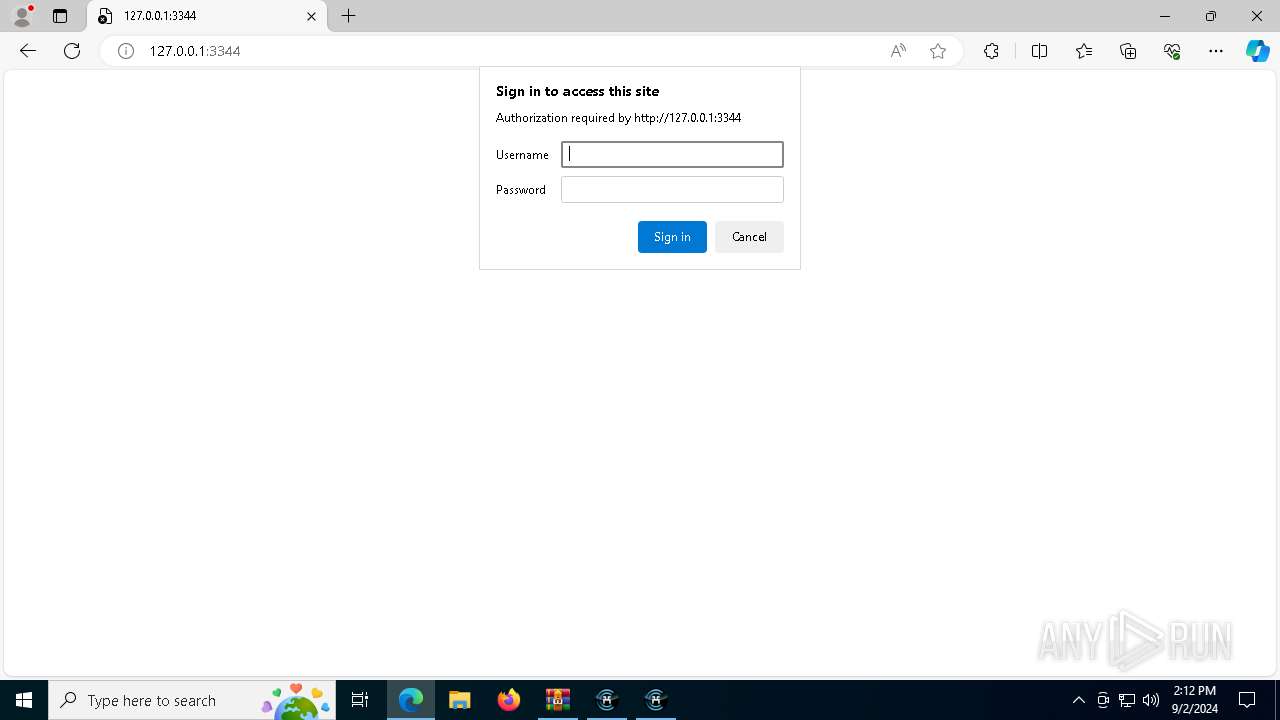
Manual execution by a user
- xmrigMiner.exe (PID: 1608)
- xmrigDaemon.exe (PID: 2388)
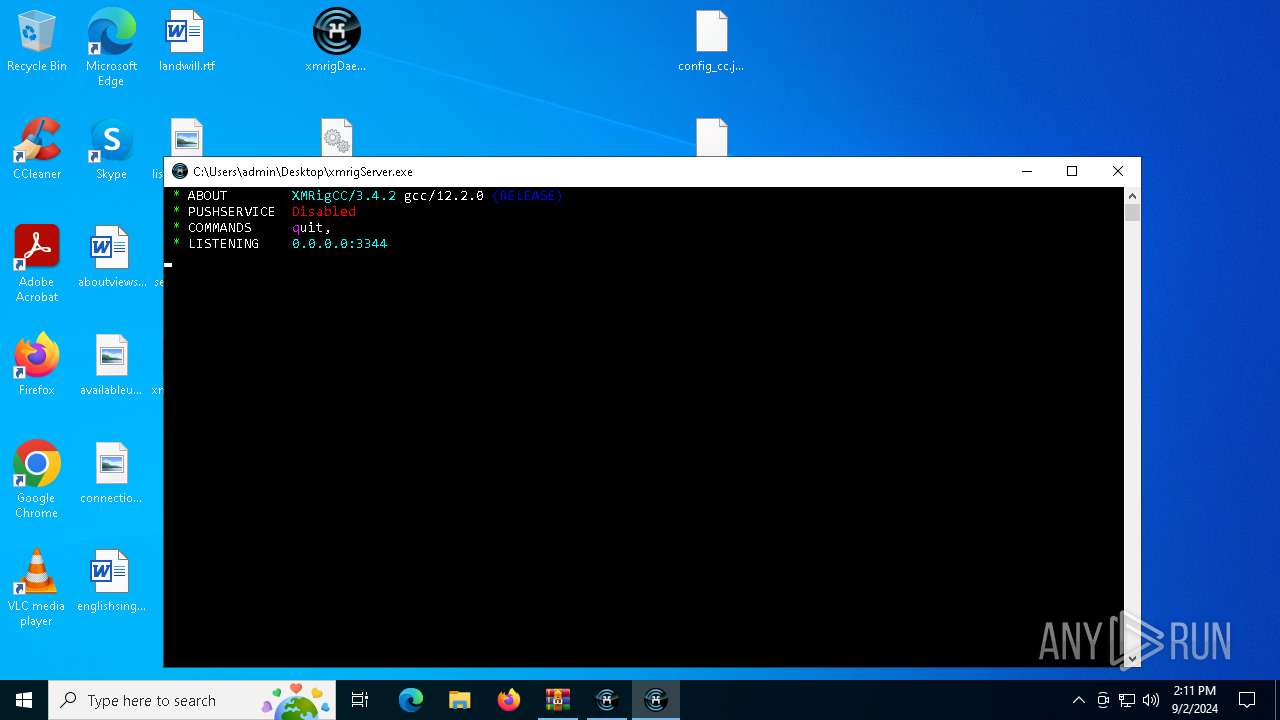
- xmrigServer.exe (PID: 6756)
- msedge.exe (PID: 5984)
- xmrigDaemon.exe (PID: 7316)
- xmrigDaemon.exe (PID: 7560)
- xmrigDaemon.exe (PID: 6960)
- xmrigDaemon.exe (PID: 4072)
- xmrigDaemon.exe (PID: 2568)
- xmrigDaemon.exe (PID: 1232)
- xmrigDaemon.exe (PID: 3568)
- xmrigDaemon.exe (PID: 7528)
- xmrigDaemon.exe (PID: 1436)
- xmrigDaemon.exe (PID: 7836)
Reads the computer name
- xmrigMiner.exe (PID: 1608)
- xmrigMiner.exe (PID: 5888)
- identity_helper.exe (PID: 8148)
- identity_helper.exe (PID: 7008)
- xmrigMiner.exe (PID: 6872)
- xmrigMiner.exe (PID: 8408)
- xmrigMiner.exe (PID: 8400)
- xmrigMiner.exe (PID: 8360)
- xmrigMiner.exe (PID: 8436)
- xmrigMiner.exe (PID: 8344)
- xmrigMiner.exe (PID: 8392)
- xmrigMiner.exe (PID: 8464)
- xmrigMiner.exe (PID: 8232)
- xmrigMiner.exe (PID: 8416)
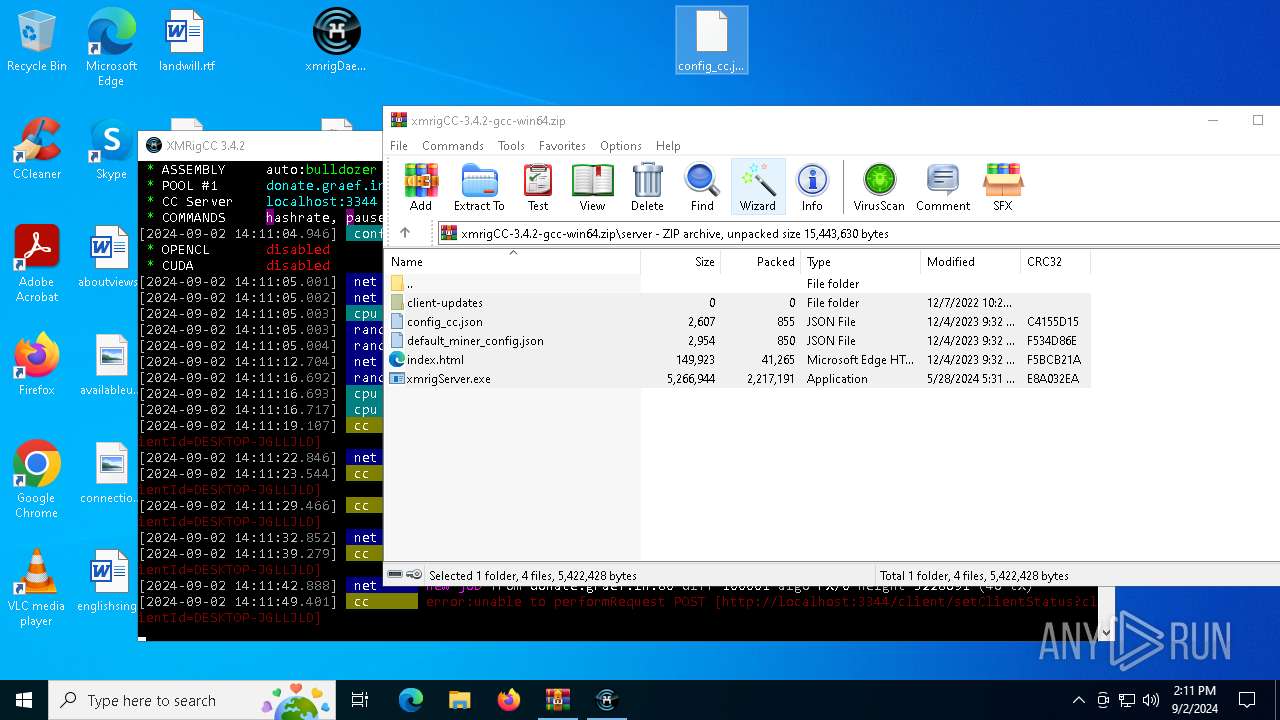
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2112)
Reads the software policy settings
- slui.exe (PID: 3352)
- slui.exe (PID: 3696)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5984)
- msedge.exe (PID: 8144)
Application launched itself
- msedge.exe (PID: 5984)
- msedge.exe (PID: 8144)
Reads Environment values
- identity_helper.exe (PID: 8148)
- identity_helper.exe (PID: 7008)
Checks proxy server information
- slui.exe (PID: 3696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
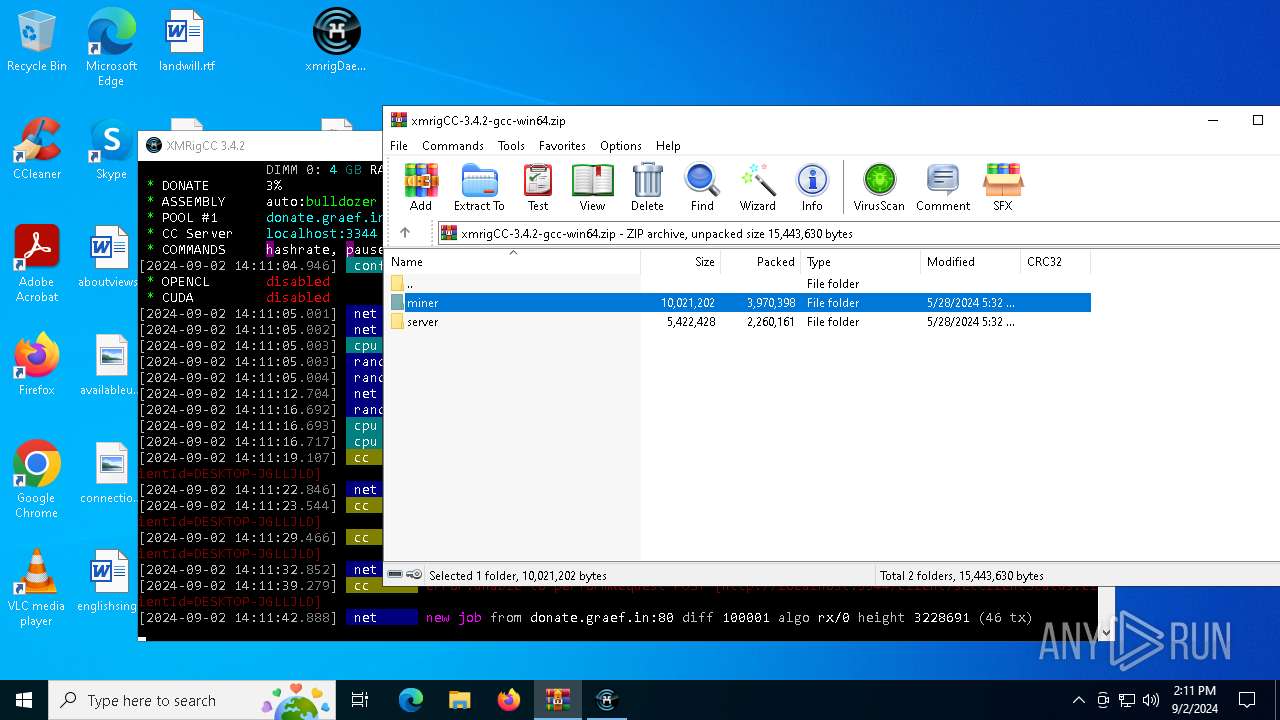
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:05:28 18:32:36 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | miner/ |
Total processes
230
Monitored processes
96
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
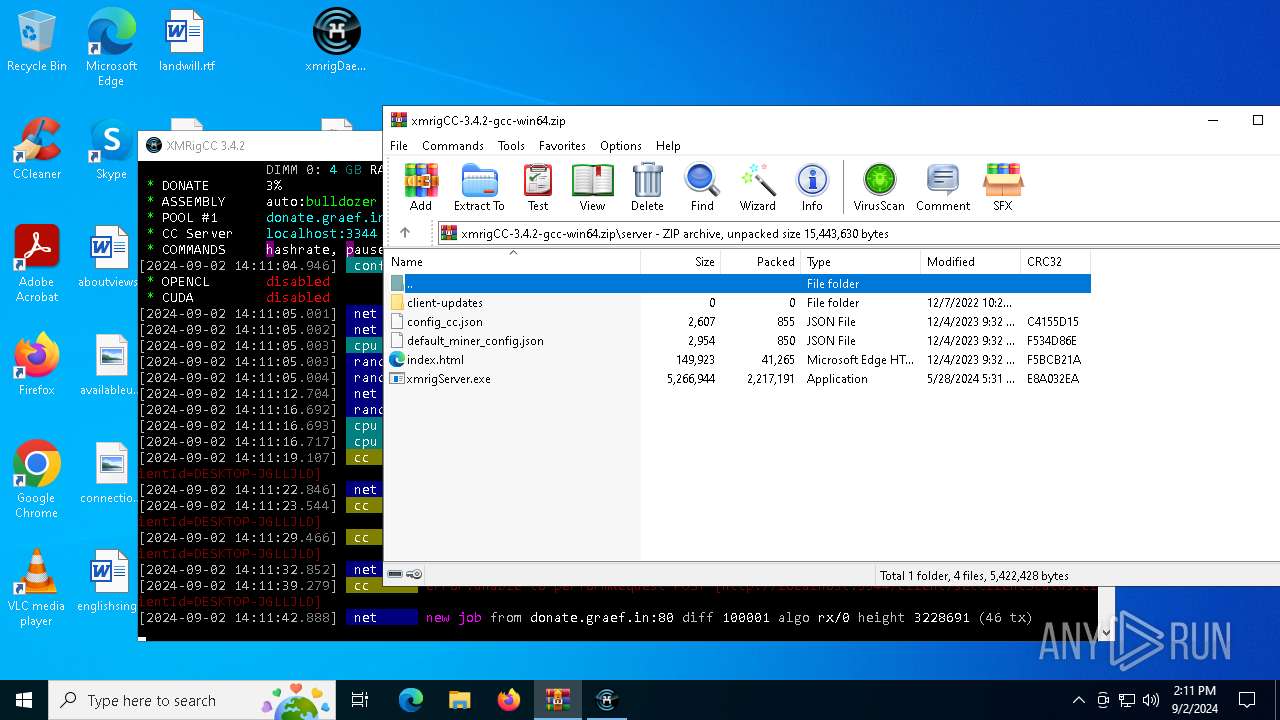
| 1168 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xmrigServer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\Desktop\xmrigDaemon.exe" | C:\Users\admin\Desktop\xmrigDaemon.exe | — | explorer.exe | |||||||||||
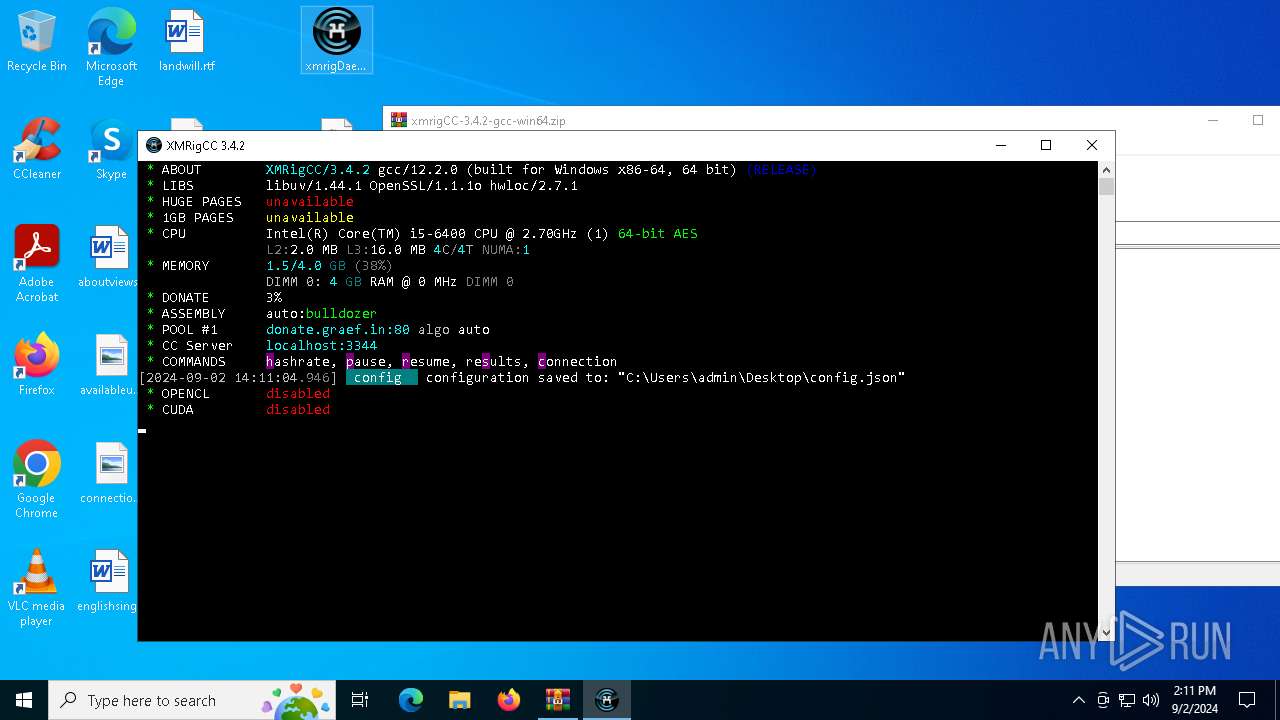
User: admin Company: https://github.com/BenDr0id/xmrigCC/ Integrity Level: MEDIUM Description: XMRigCC miner Version: 3.4.2 Modules
| |||||||||||||||
| 1436 | "C:\Users\admin\Desktop\xmrigDaemon.exe" | C:\Users\admin\Desktop\xmrigDaemon.exe | — | explorer.exe | |||||||||||
User: admin Company: https://github.com/BenDr0id/xmrigCC/ Integrity Level: MEDIUM Description: XMRigCC miner Version: 3.4.2 Modules
| |||||||||||||||
| 1448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xmrigDaemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1608 | "C:\Users\admin\Desktop\xmrigMiner.exe" | C:\Users\admin\Desktop\xmrigMiner.exe | — | explorer.exe | |||||||||||
User: admin Company: https://github.com/BenDr0id/xmrigCC/ Integrity Level: MEDIUM Description: XMRigCC miner Exit code: 2 Version: 3.4.2 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\xmrigCC-3.4.2-gcc-win64.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\Desktop\xmrigDaemon.exe" | C:\Users\admin\Desktop\xmrigDaemon.exe | — | explorer.exe | |||||||||||
User: admin Company: https://github.com/BenDr0id/xmrigCC/ Integrity Level: MEDIUM Description: XMRigCC miner Version: 3.4.2 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\Desktop\xmrigDaemon.exe" | C:\Users\admin\Desktop\xmrigDaemon.exe | — | explorer.exe | |||||||||||
User: admin Company: https://github.com/BenDr0id/xmrigCC/ Integrity Level: MEDIUM Description: XMRigCC miner Version: 3.4.2 Modules
| |||||||||||||||
| 3144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=3500 --field-trial-handle=2284,i,2893144108357622636,2479770191284513961,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3180 | C:\WINDOWS\system32\cmd.exe /c "C:\Users\admin\Desktop\xmrigMiner.exe" --daemonized | C:\Windows\System32\cmd.exe | — | xmrigDaemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 780
Read events
21 649
Write events
127
Delete events
4
Modification events
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\xmrigCC-3.4.2-gcc-win64.zip | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
5
Suspicious files
97
Text files
87
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2112 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2112.5791\miner\WinRing0x64.sys | executable | |
MD5:0C0195C48B6B8582FA6F6373032118DA | SHA256:11BD2C9F9E2397C9A16E0990E4ED2CF0679498FE0FD418A3DFDAC60B5C160EE5 | |||
| 2112 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2112.5791\miner\WinRing-LICENSE | text | |
MD5:557EF98AC47ACCD0B7010E62A838AB2E | SHA256:534DAD3827C7D381414566C29A374F375A83E320F7D31562C2B0386E3ABA86BC | |||
| 5984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF142b93.TMP | — | |
MD5:— | SHA256:— | |||
| 5984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF142ba2.TMP | — | |
MD5:— | SHA256:— | |||
| 5984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF142bb2.TMP | — | |
MD5:— | SHA256:— | |||
| 5984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF142b93.TMP | — | |
MD5:— | SHA256:— | |||
| 5984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
87
DNS requests
74
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3832 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3424 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6052 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7156 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7156 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3832 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3832 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
donate.graef.in |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5888 | xmrigMiner.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7204 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |