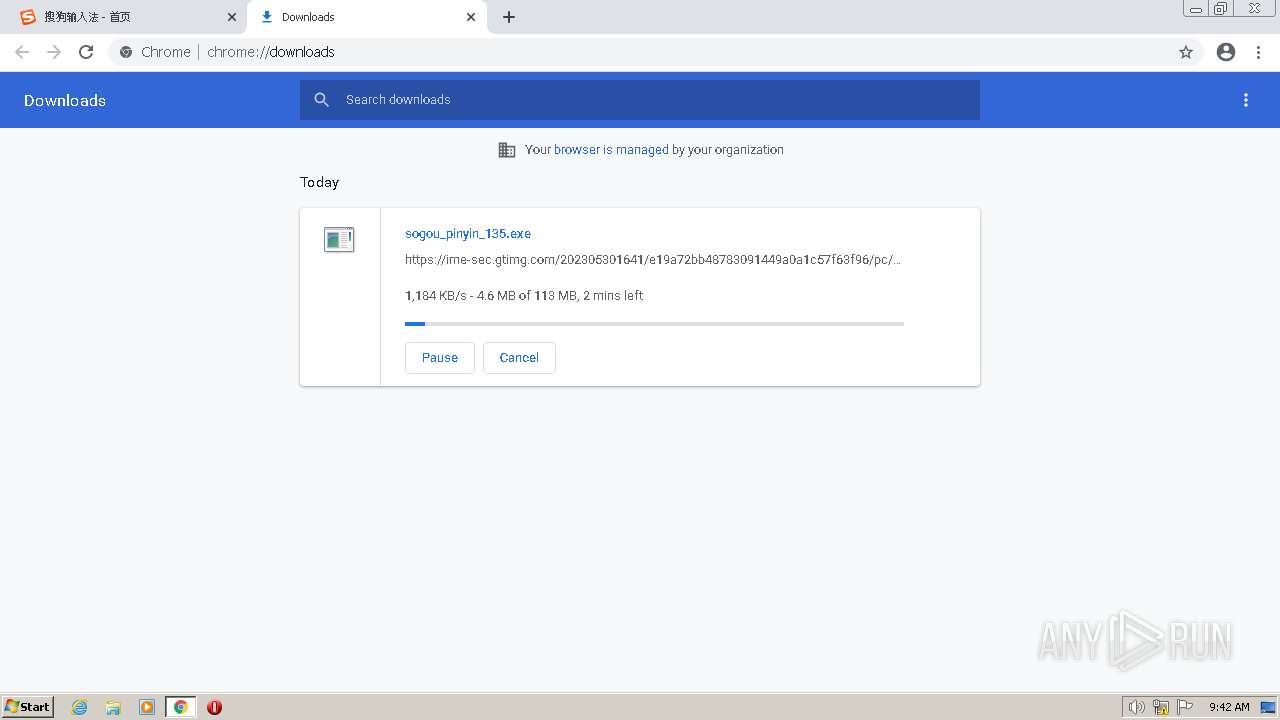
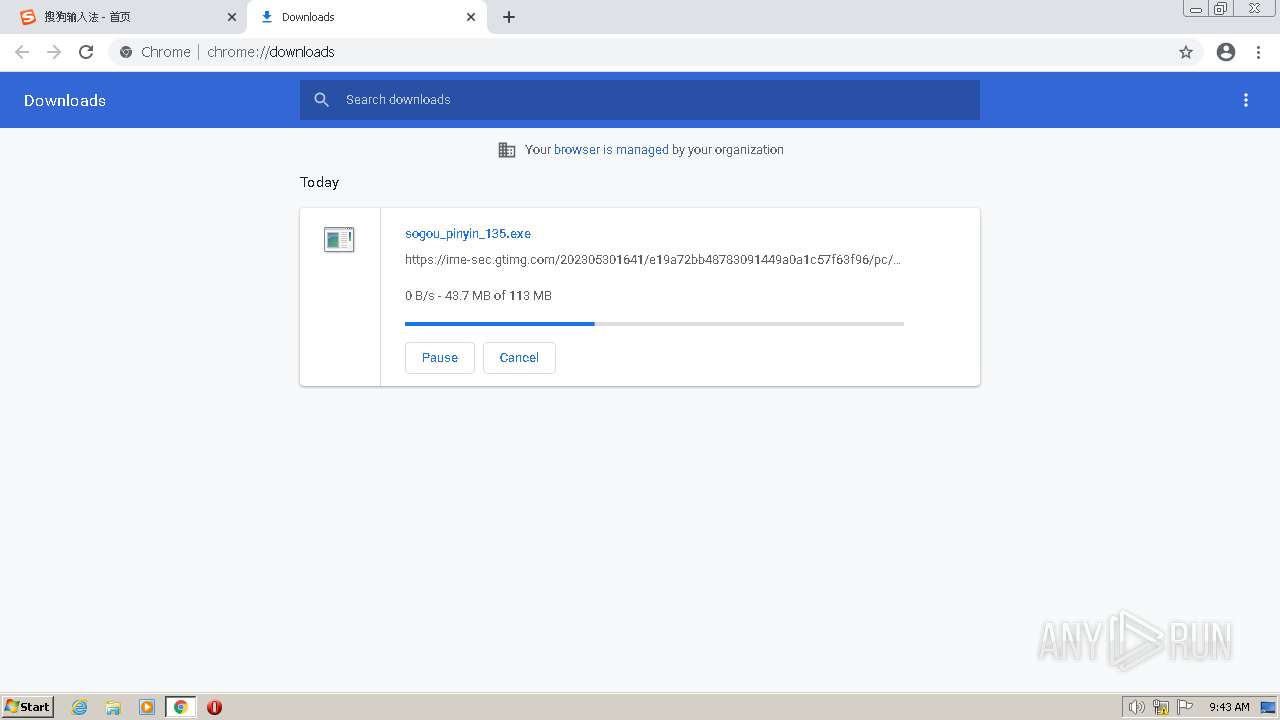
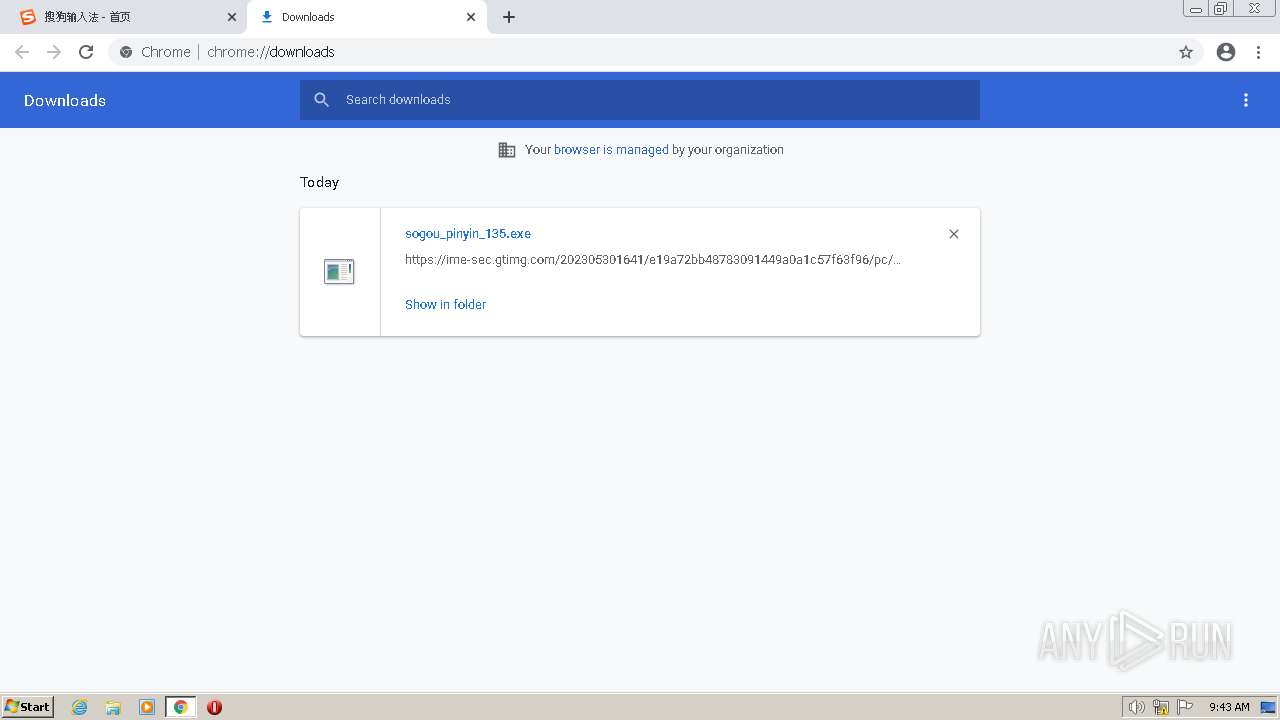
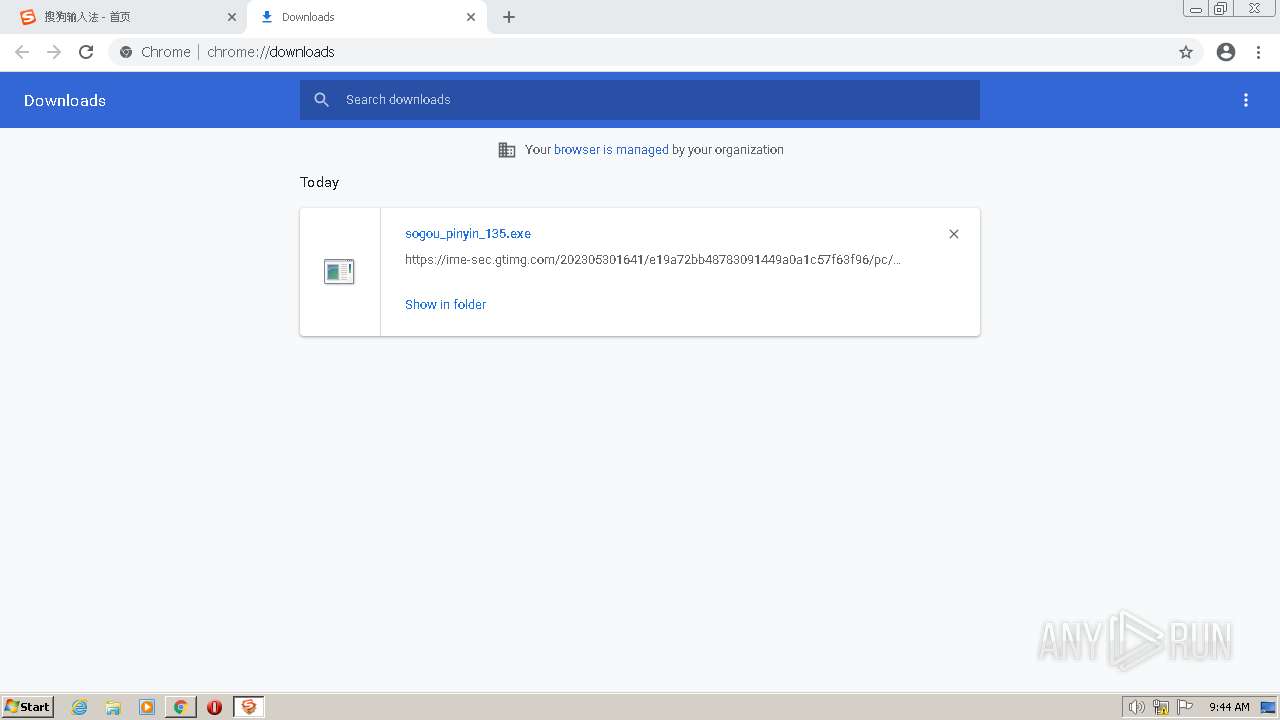
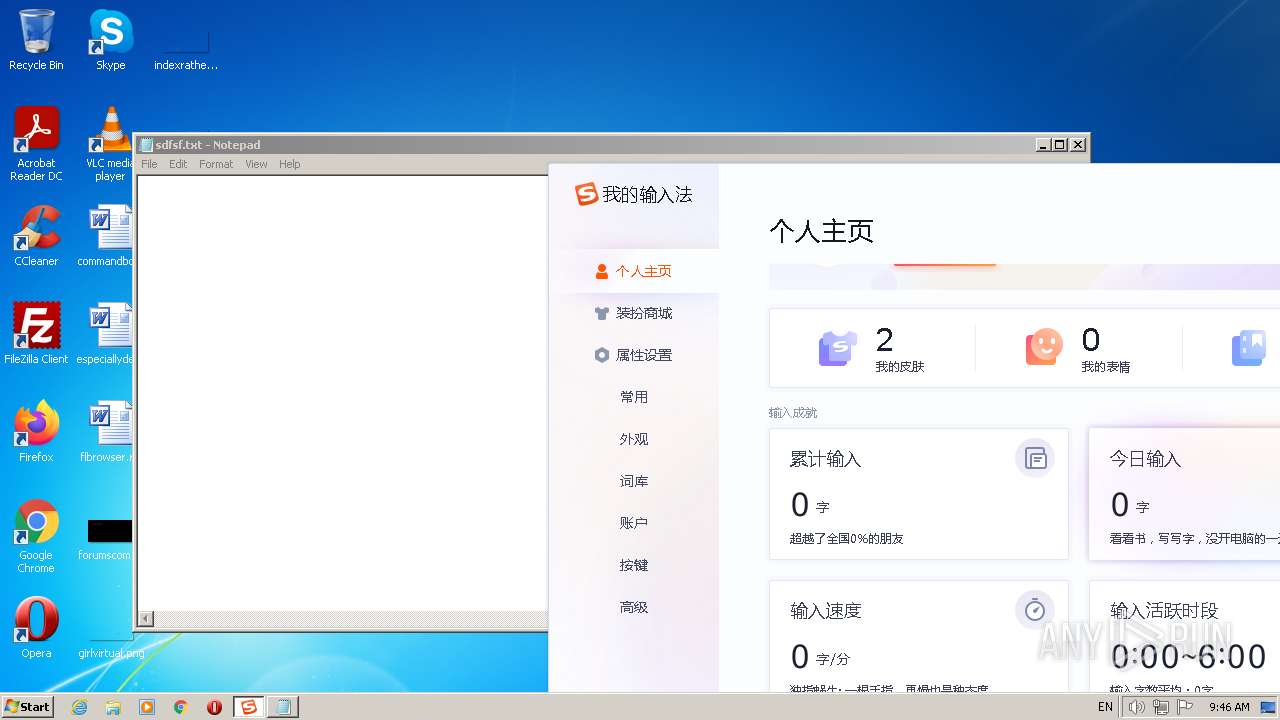
| URL: | https://pinyin.sogou.com/windows/?r=mac&t=pinyin |
| Full analysis: | https://app.any.run/tasks/d40f5fb9-5dcd-4d1e-92ed-a1f79fb4a019 |
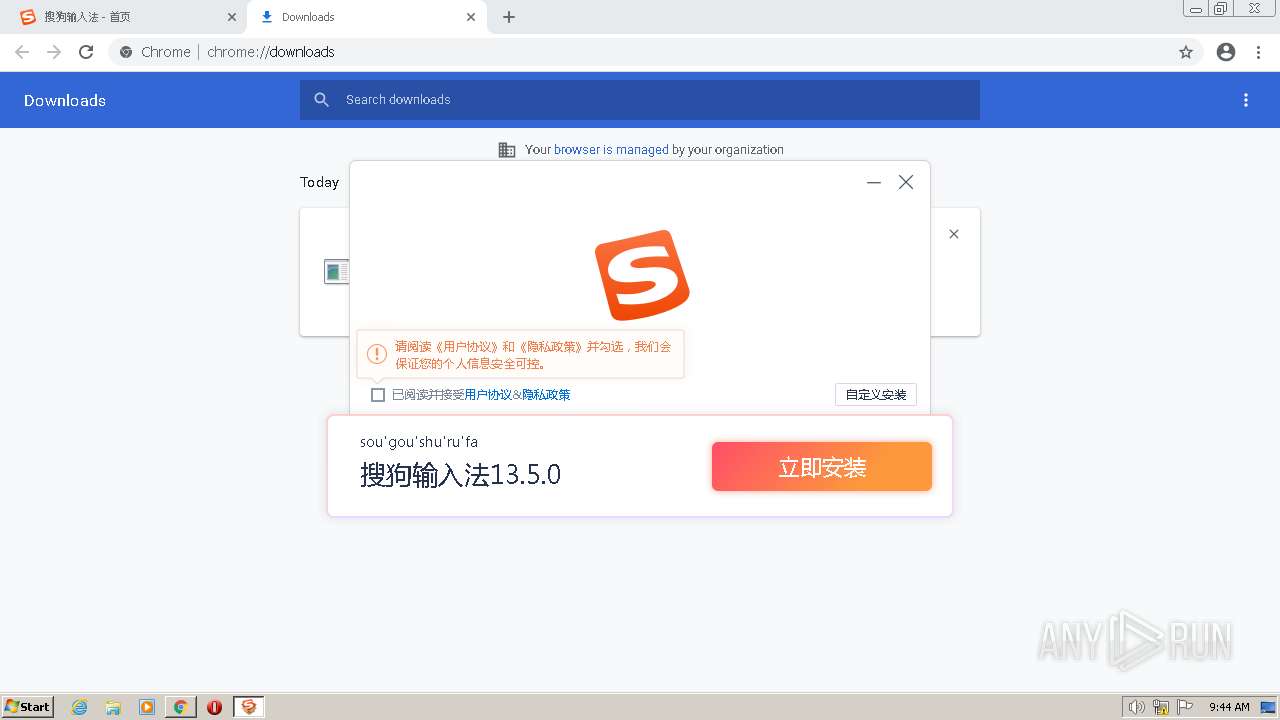
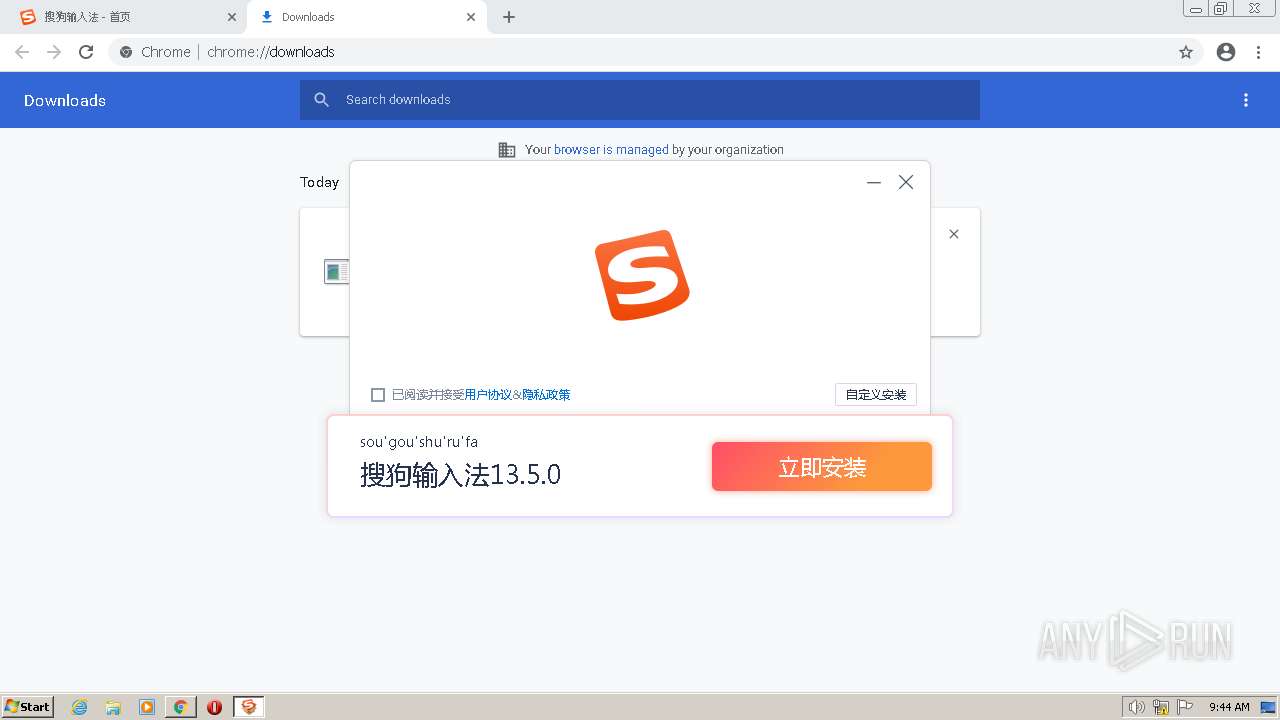
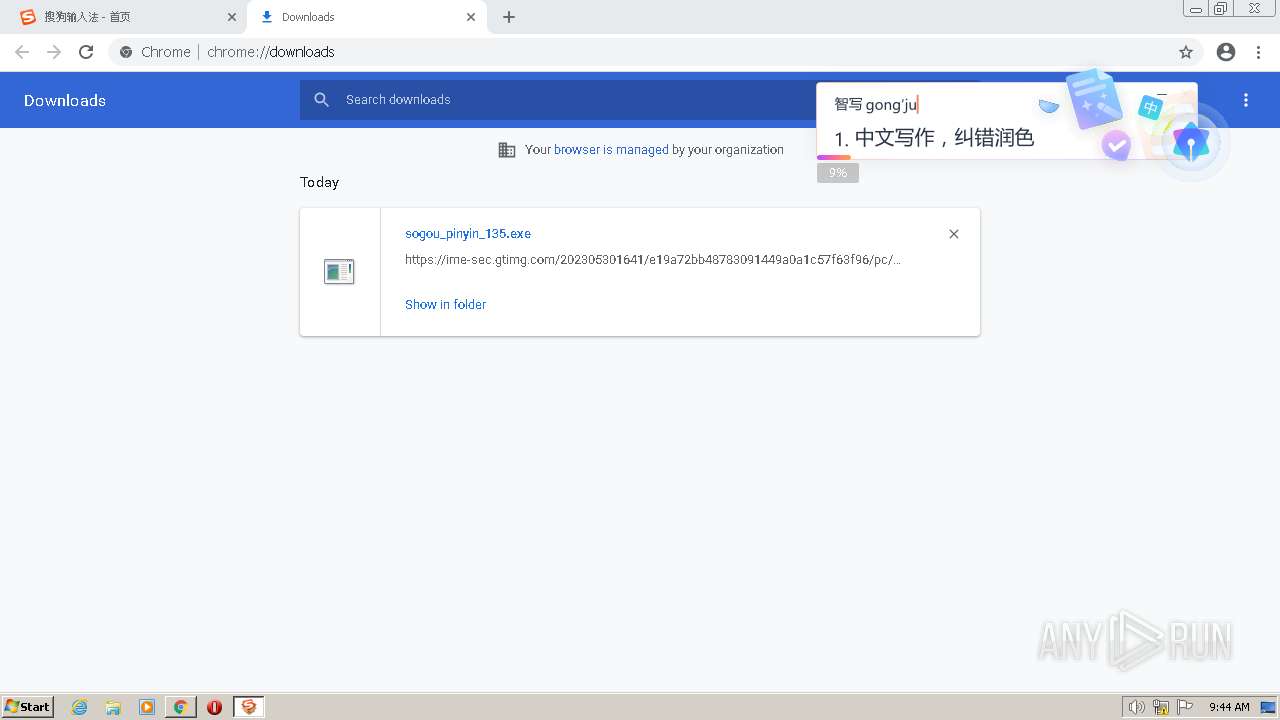
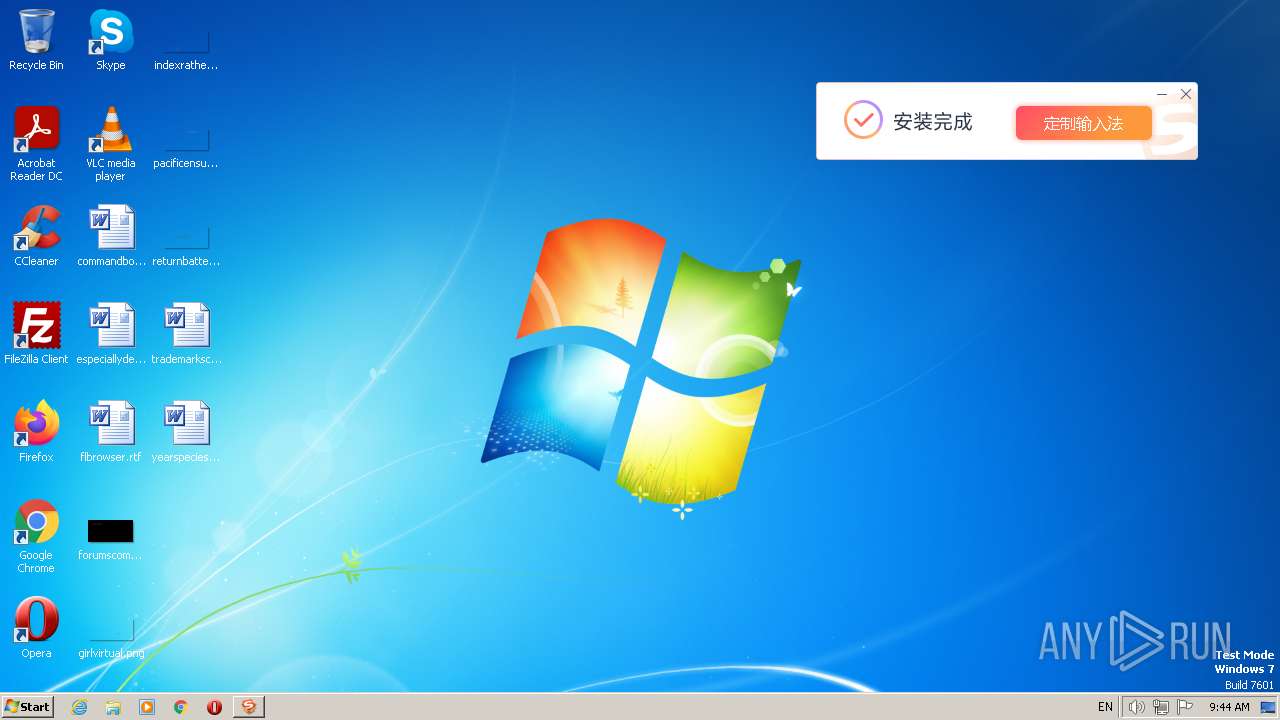
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | May 30, 2023, 08:41:38 |
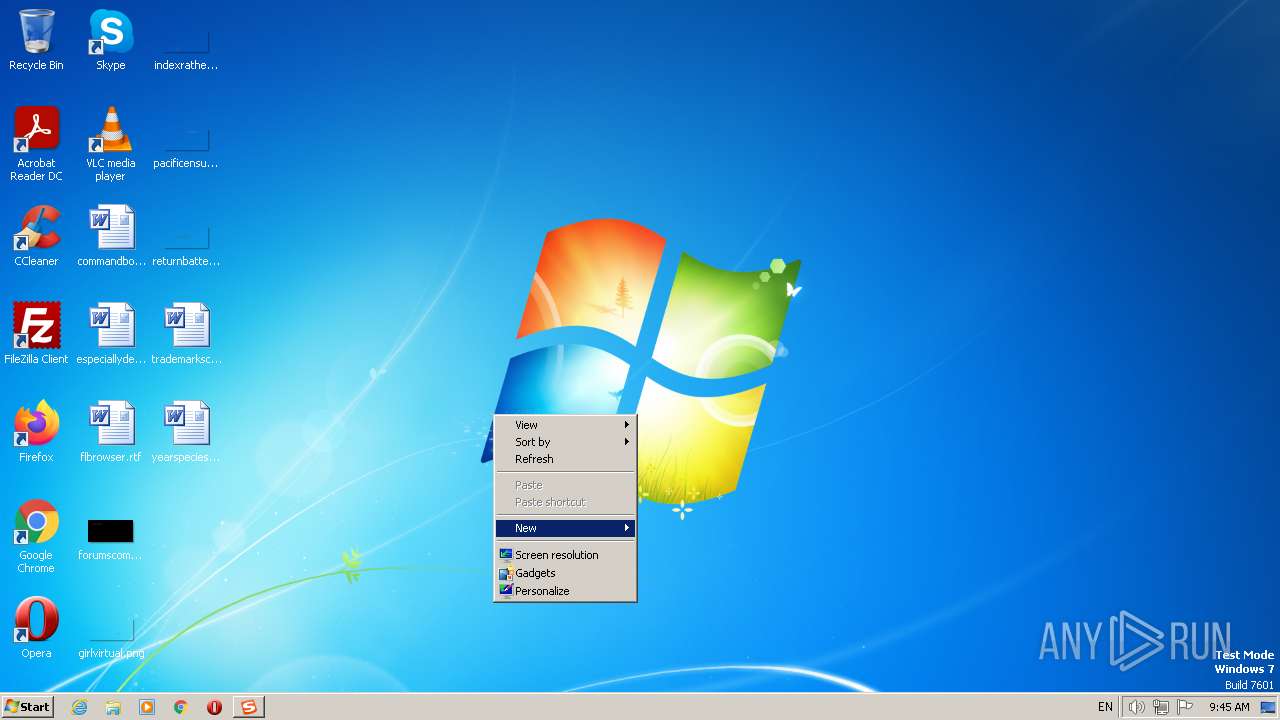
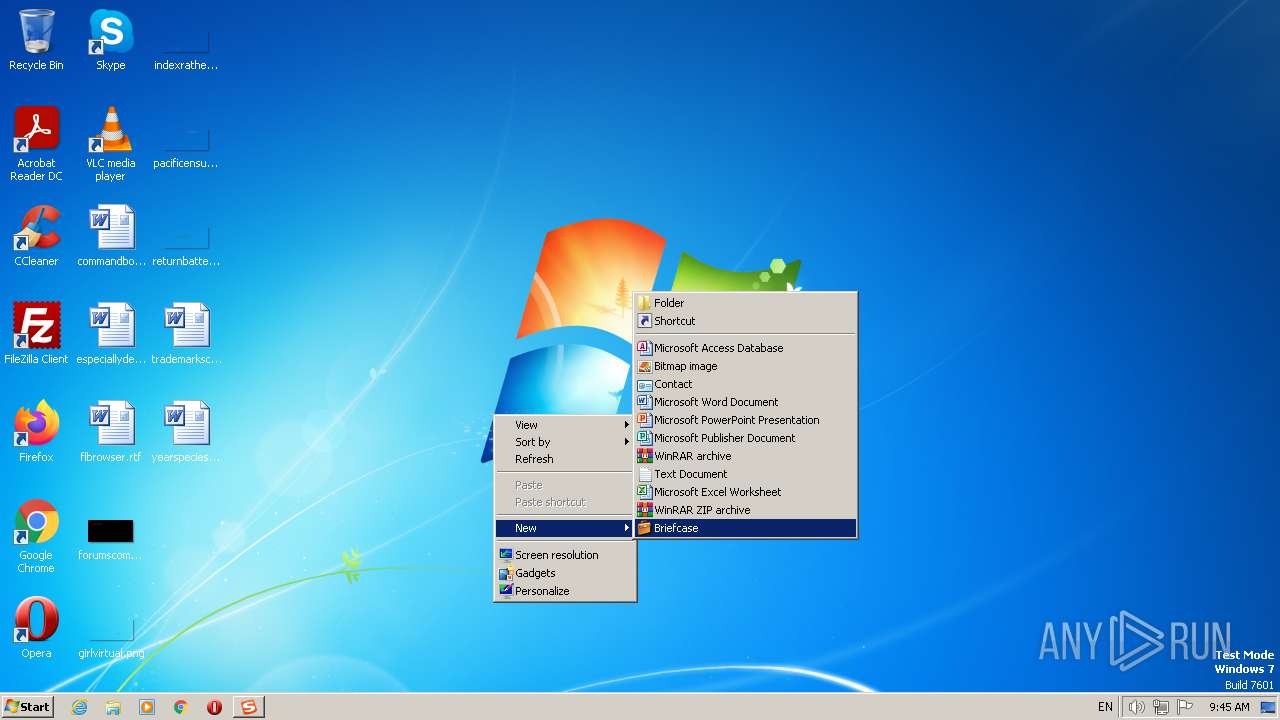
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AB12878B987F06AF12BB0E0F1E2B003E |
| SHA1: | A7E4EFB4D943D962F0F72F457621801829C7AFC6 |
| SHA256: | 0F41320C168D1755A34F788304B981F5AF8F15BE66E8774F0050356DB2C2B455 |
| SSDEEP: | 3:N8IoKLfeKK/TeYUn:2ItreK0HUn |
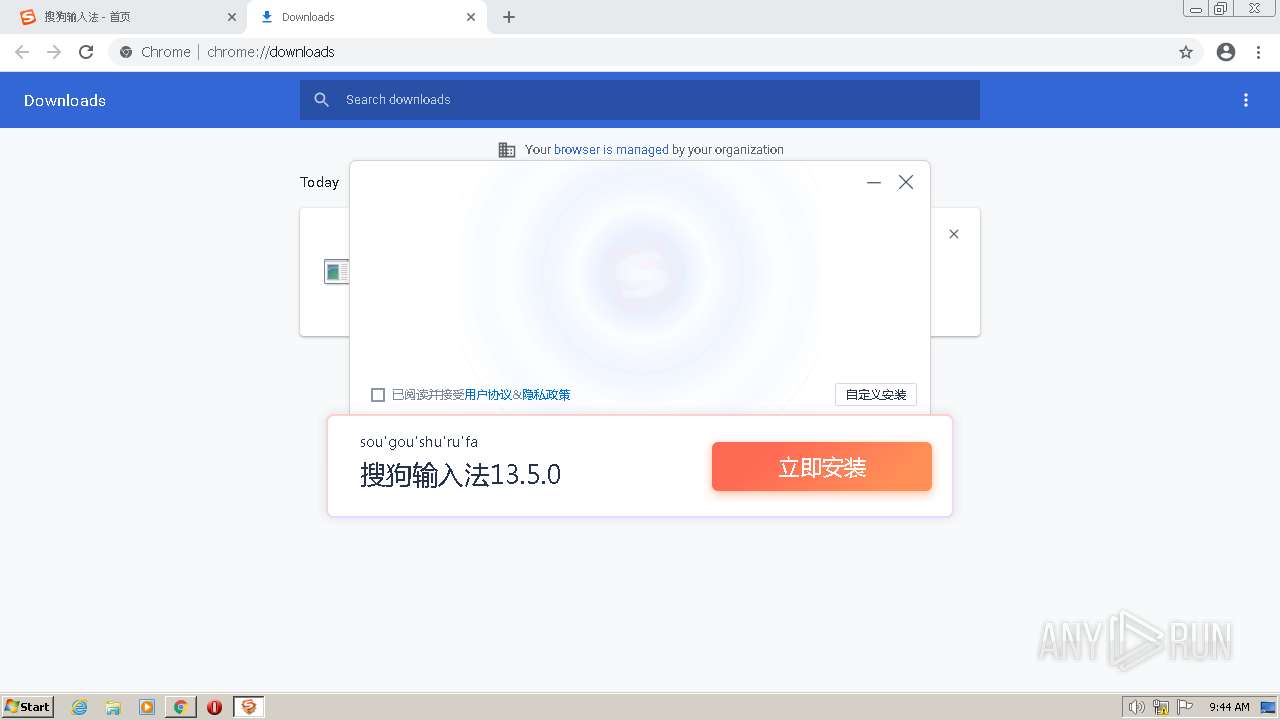
MALICIOUS
Application was dropped or rewritten from another process
- sogou_pinyin_135.exe (PID: 3940)
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 3524)
- SGTool.exe (PID: 2696)
- SGTool.exe (PID: 1156)
- SogouExe.exe (PID: 3924)
- SGTool.exe (PID: 3384)
- SogouExe.exe (PID: 3204)
- SogouExe.exe (PID: 1148)
- SogouSvc.exe (PID: 1960)
- SogouExe.exe (PID: 3552)
- SGTool.exe (PID: 768)
- SGTool.exe (PID: 3972)
- SogouExe.exe (PID: 1580)
- SGTool.exe (PID: 3100)
- SogouExe.exe (PID: 1616)
- userNetSchedule.exe (PID: 2828)
- SogouExe.exe (PID: 2680)
- SogouExe.exe (PID: 932)
- SGTool.exe (PID: 4064)
- SGTool.exe (PID: 2784)
- SGTool.exe (PID: 1544)
- SGTool.exe (PID: 3852)
- SGTool.exe (PID: 268)
- SogouImeBroker.exe (PID: 2264)
- SogouComMgr.exe (PID: 844)
- SGTool.exe (PID: 2044)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 2240)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 1348)
- userNetSchedule.exe (PID: 2704)
- SogouExe.exe (PID: 3600)
- SGTool.exe (PID: 3480)
- SGTool.exe (PID: 1820)
- SGTool.exe (PID: 2636)
- SGWangzai.exe (PID: 2840)
- SGTool.exe (PID: 2612)
- PinyinUp.exe (PID: 2632)
- SGDownload.exe (PID: 1360)
- SGTool.exe (PID: 2504)
- SGMyInput.exe (PID: 3216)
- userNetSchedule.exe (PID: 2640)
- SGWebRender.exe (PID: 2640)
- SGWebRender.exe (PID: 1300)
- SGWebRender.exe (PID: 2916)
- SGWebRender.exe (PID: 3868)
- SGWebRender.exe (PID: 3680)
Registers / Runs the DLL via REGSVR32.EXE
- sogou_pinyin_135.exe (PID: 2788)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3004)
- SGTool.exe (PID: 2696)
- SGTool.exe (PID: 1156)
- SogouExe.exe (PID: 3924)
- SGTool.exe (PID: 3384)
- SGTool.exe (PID: 768)
- SogouExe.exe (PID: 3204)
- SogouExe.exe (PID: 1148)
- SGTool.exe (PID: 3972)
- SGTool.exe (PID: 3100)
- SogouExe.exe (PID: 3552)
- userNetSchedule.exe (PID: 2828)
- SGTool.exe (PID: 4064)
- SogouExe.exe (PID: 1580)
- SGTool.exe (PID: 2784)
- SogouExe.exe (PID: 932)
- SGTool.exe (PID: 1544)
- SGTool.exe (PID: 3852)
- SogouExe.exe (PID: 2680)
- SGTool.exe (PID: 268)
- SogouExe.exe (PID: 1616)
- SGTool.exe (PID: 2044)
- SogouComMgr.exe (PID: 844)
- SGTool.exe (PID: 2240)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 1348)
- SGWizard.exe (PID: 308)
- userNetSchedule.exe (PID: 2704)
- SGTool.exe (PID: 3480)
- SGTool.exe (PID: 1820)
- SGTool.exe (PID: 2636)
- SGWangzai.exe (PID: 2840)
- SogouExe.exe (PID: 3600)
- SGTool.exe (PID: 2612)
- PinyinUp.exe (PID: 2632)
- SGTool.exe (PID: 2504)
- SGMyInput.exe (PID: 3216)
- userNetSchedule.exe (PID: 2640)
- SGWebRender.exe (PID: 3680)
- SGWebRender.exe (PID: 1300)
- SGWebRender.exe (PID: 2640)
- SGWebRender.exe (PID: 2916)
- SGWebRender.exe (PID: 3868)
Creates a writable file the system directory
- sogou_pinyin_135.exe (PID: 2788)
Uses Task Scheduler to run other applications
- sogou_pinyin_135.exe (PID: 2788)
SUSPICIOUS
Executable content was dropped or overwritten
- sogou_pinyin_135.exe (PID: 2788)
- SogouExe.exe (PID: 3924)
- SogouExe.exe (PID: 3204)
- SogouExe.exe (PID: 1148)
- SogouExe.exe (PID: 3552)
- SogouExe.exe (PID: 1580)
- SogouExe.exe (PID: 1616)
- SogouComMgr.exe (PID: 844)
- SogouExe.exe (PID: 3600)
- SGTool.exe (PID: 2044)
- SGMyInput.exe (PID: 3216)
The process creates files with name similar to system file names
- sogou_pinyin_135.exe (PID: 2788)
- SogouComMgr.exe (PID: 844)
Reads the Internet Settings
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 2696)
- SGTool.exe (PID: 1156)
- SGTool.exe (PID: 3384)
- SGTool.exe (PID: 768)
- SGTool.exe (PID: 3972)
- SGTool.exe (PID: 3100)
- userNetSchedule.exe (PID: 2828)
- SGTool.exe (PID: 4064)
- SogouComMgr.exe (PID: 844)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 1348)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 3480)
- SGTool.exe (PID: 2612)
- SGTool.exe (PID: 2044)
- PinyinUp.exe (PID: 2632)
- SGDownload.exe (PID: 1360)
- SGMyInput.exe (PID: 3216)
Process requests binary or script from the Internet
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 2044)
Checks Windows Trust Settings
- SogouExe.exe (PID: 3924)
- SogouExe.exe (PID: 3204)
- SogouExe.exe (PID: 1148)
- SogouExe.exe (PID: 3552)
- SogouExe.exe (PID: 1580)
- SogouExe.exe (PID: 1616)
- SogouComMgr.exe (PID: 2980)
- SogouExe.exe (PID: 3600)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 2612)
- SGMyInput.exe (PID: 3216)
Reads security settings of Internet Explorer
- SogouExe.exe (PID: 3924)
- SogouExe.exe (PID: 3204)
- SogouExe.exe (PID: 1148)
- SogouExe.exe (PID: 3552)
- SogouExe.exe (PID: 1580)
- SogouExe.exe (PID: 1616)
- SogouComMgr.exe (PID: 2980)
- SogouExe.exe (PID: 3600)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 2612)
- SGMyInput.exe (PID: 3216)
Reads settings of System Certificates
- SogouExe.exe (PID: 3924)
- SogouExe.exe (PID: 3204)
- SogouExe.exe (PID: 1148)
- SogouExe.exe (PID: 3552)
- SogouExe.exe (PID: 1580)
- SogouExe.exe (PID: 1616)
- SogouComMgr.exe (PID: 2980)
- SogouExe.exe (PID: 3600)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 2612)
- SGMyInput.exe (PID: 3216)
- SGWebRender.exe (PID: 2640)
Adds/modifies Windows certificates
- SGTool.exe (PID: 2696)
- sogou_pinyin_135.exe (PID: 2788)
- SGMyInput.exe (PID: 3216)
Application launched itself
- SGTool.exe (PID: 2044)
Reads Microsoft Outlook installation path
- SGMyInput.exe (PID: 3216)
Reads Internet Explorer settings
- SGMyInput.exe (PID: 3216)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 2032)
Create files in a temporary directory
- chrome.exe (PID: 2032)
- sogou_pinyin_135.exe (PID: 2788)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 2612)
- SGTool.exe (PID: 2044)
- SGDownload.exe (PID: 1360)
- SGMyInput.exe (PID: 3216)
The process uses the downloaded file
- chrome.exe (PID: 2068)
- chrome.exe (PID: 2032)
Checks supported languages
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 3524)
- SGTool.exe (PID: 2696)
- SogouExe.exe (PID: 3924)
- SGTool.exe (PID: 1156)
- SGTool.exe (PID: 3384)
- SogouExe.exe (PID: 1148)
- SogouSvc.exe (PID: 1960)
- SGTool.exe (PID: 768)
- SogouExe.exe (PID: 3552)
- SogouExe.exe (PID: 3204)
- SGTool.exe (PID: 3972)
- SogouExe.exe (PID: 1580)
- SGTool.exe (PID: 3100)
- SogouExe.exe (PID: 1616)
- userNetSchedule.exe (PID: 2828)
- SGTool.exe (PID: 4064)
- SogouExe.exe (PID: 932)
- SogouExe.exe (PID: 2680)
- SGTool.exe (PID: 2784)
- SGTool.exe (PID: 1544)
- SGTool.exe (PID: 3852)
- SGTool.exe (PID: 268)
- SogouImeBroker.exe (PID: 2264)
- SogouComMgr.exe (PID: 844)
- wmpnscfg.exe (PID: 1828)
- SGTool.exe (PID: 2044)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 2240)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 1348)
- userNetSchedule.exe (PID: 2704)
- SogouExe.exe (PID: 3600)
- SGTool.exe (PID: 3480)
- SGTool.exe (PID: 1820)
- SGWangzai.exe (PID: 2840)
- SGTool.exe (PID: 2612)
- SGDownload.exe (PID: 1360)
- PinyinUp.exe (PID: 2632)
- SGTool.exe (PID: 2504)
- SGMyInput.exe (PID: 3216)
- userNetSchedule.exe (PID: 2640)
- SGWebRender.exe (PID: 3680)
- SGWebRender.exe (PID: 2916)
- SGWebRender.exe (PID: 1300)
- SGWebRender.exe (PID: 2640)
- SGWebRender.exe (PID: 3868)
- SGTool.exe (PID: 2636)
Application launched itself
- chrome.exe (PID: 2032)
The process checks LSA protection
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 2696)
- SogouExe.exe (PID: 3924)
- SogouExe.exe (PID: 3204)
- SGTool.exe (PID: 1156)
- SGTool.exe (PID: 3384)
- SogouExe.exe (PID: 1148)
- SGTool.exe (PID: 768)
- SogouExe.exe (PID: 3552)
- SGTool.exe (PID: 3100)
- SGTool.exe (PID: 3972)
- SogouExe.exe (PID: 1580)
- SogouExe.exe (PID: 1616)
- userNetSchedule.exe (PID: 2828)
- SGTool.exe (PID: 4064)
- SogouExe.exe (PID: 932)
- SogouExe.exe (PID: 2680)
- SGTool.exe (PID: 2784)
- SGTool.exe (PID: 268)
- SogouComMgr.exe (PID: 844)
- wmpnscfg.exe (PID: 1828)
- SGTool.exe (PID: 2044)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 2240)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 1348)
- userNetSchedule.exe (PID: 2704)
- SogouExe.exe (PID: 3600)
- SGTool.exe (PID: 3480)
- SGTool.exe (PID: 1820)
- SGWangzai.exe (PID: 2840)
- SGTool.exe (PID: 2612)
- PinyinUp.exe (PID: 2632)
- SGDownload.exe (PID: 1360)
- SGTool.exe (PID: 2504)
- SGMyInput.exe (PID: 3216)
- userNetSchedule.exe (PID: 2640)
- SGWebRender.exe (PID: 2640)
Reads the machine GUID from the registry
- sogou_pinyin_135.exe (PID: 2788)
- SogouExe.exe (PID: 3924)
- SogouExe.exe (PID: 3204)
- SGTool.exe (PID: 3384)
- SogouExe.exe (PID: 1148)
- SogouExe.exe (PID: 3552)
- SogouExe.exe (PID: 1616)
- SogouExe.exe (PID: 1580)
- wmpnscfg.exe (PID: 1828)
- SogouComMgr.exe (PID: 844)
- SogouComMgr.exe (PID: 2980)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 1348)
- SogouExe.exe (PID: 3600)
- SGTool.exe (PID: 3480)
- SGTool.exe (PID: 2612)
- PinyinUp.exe (PID: 2632)
- SGDownload.exe (PID: 1360)
- SGMyInput.exe (PID: 3216)
- SGTool.exe (PID: 2044)
- SGWebRender.exe (PID: 2640)
Reads the computer name
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 2696)
- SogouExe.exe (PID: 3924)
- SGTool.exe (PID: 1156)
- SogouExe.exe (PID: 3204)
- SGTool.exe (PID: 3384)
- SogouExe.exe (PID: 1148)
- SogouSvc.exe (PID: 1960)
- SGTool.exe (PID: 768)
- SogouExe.exe (PID: 3552)
- SogouExe.exe (PID: 1580)
- SGTool.exe (PID: 3972)
- SGTool.exe (PID: 3100)
- SogouExe.exe (PID: 1616)
- SGTool.exe (PID: 4064)
- userNetSchedule.exe (PID: 2828)
- SogouExe.exe (PID: 932)
- SogouExe.exe (PID: 2680)
- SGTool.exe (PID: 2784)
- SGTool.exe (PID: 268)
- SogouComMgr.exe (PID: 844)
- wmpnscfg.exe (PID: 1828)
- SGTool.exe (PID: 2044)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 2240)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 1348)
- userNetSchedule.exe (PID: 2704)
- SogouExe.exe (PID: 3600)
- SGTool.exe (PID: 3480)
- SGTool.exe (PID: 1820)
- SGWangzai.exe (PID: 2840)
- SGTool.exe (PID: 2612)
- PinyinUp.exe (PID: 2632)
- SGDownload.exe (PID: 1360)
- SGTool.exe (PID: 2504)
- SGMyInput.exe (PID: 3216)
- userNetSchedule.exe (PID: 2640)
- SGWebRender.exe (PID: 3680)
- SGWebRender.exe (PID: 2640)
- SGWebRender.exe (PID: 3868)
Checks proxy server information
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 3384)
- SogouComMgr.exe (PID: 844)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 1348)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 3480)
- SGTool.exe (PID: 2612)
- SGTool.exe (PID: 2044)
- PinyinUp.exe (PID: 2632)
- SGDownload.exe (PID: 1360)
- SGMyInput.exe (PID: 3216)
Creates files in the program directory
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 2696)
- SogouExe.exe (PID: 932)
- SogouComMgr.exe (PID: 844)
- SGTool.exe (PID: 2044)
- SGTool.exe (PID: 2240)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 3480)
- SGWangzai.exe (PID: 2840)
- SGMyInput.exe (PID: 3216)
Creates files or folders in the user directory
- sogou_pinyin_135.exe (PID: 2788)
- SGTool.exe (PID: 2696)
- SogouExe.exe (PID: 3924)
- SGTool.exe (PID: 1156)
- SogouExe.exe (PID: 3204)
- SGTool.exe (PID: 3384)
- SogouExe.exe (PID: 1148)
- SogouExe.exe (PID: 3552)
- SGTool.exe (PID: 768)
- SogouExe.exe (PID: 1580)
- SGTool.exe (PID: 3972)
- SogouExe.exe (PID: 1616)
- SGTool.exe (PID: 3100)
- userNetSchedule.exe (PID: 2828)
- SGTool.exe (PID: 4064)
- SogouExe.exe (PID: 932)
- SGTool.exe (PID: 2784)
- SGTool.exe (PID: 1544)
- SGTool.exe (PID: 3852)
- SGTool.exe (PID: 268)
- SogouComMgr.exe (PID: 844)
- SGTool.exe (PID: 2044)
- SogouComMgr.exe (PID: 2980)
- SGTool.exe (PID: 2240)
- SGTool.exe (PID: 1348)
- userNetSchedule.exe (PID: 2704)
- SogouExe.exe (PID: 3600)
- SGTool.exe (PID: 3480)
- SGWizard.exe (PID: 308)
- SGTool.exe (PID: 1820)
- SGTool.exe (PID: 2636)
- SGTool.exe (PID: 2612)
- PinyinUp.exe (PID: 2632)
- SGTool.exe (PID: 2504)
- SGDownload.exe (PID: 1360)
- SGMyInput.exe (PID: 3216)
- userNetSchedule.exe (PID: 2640)
Dropped object may contain TOR URL's
- sogou_pinyin_135.exe (PID: 2788)
Loads dropped or rewritten executable
- sogou_pinyin_135.exe (PID: 2788)
Manual execution by a user
- wmpnscfg.exe (PID: 1828)
- notepad.exe (PID: 1620)
Process checks computer location settings
- SGWebRender.exe (PID: 1300)
- SGWebRender.exe (PID: 2916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
125
Monitored processes
74
Malicious processes
51
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\SogouInput\13.5.0.7715\SGTool.exe" --appid=dictconv | C:\Program Files\SogouInput\13.5.0.7715\SGTool.exe | — | sogou_pinyin_135.exe | |||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: HIGH Description: 搜狗输入法 工具 Exit code: 0 Version: 13.5.0.7715 Modules
| |||||||||||||||
| 308 | "C:\Program Files\SogouInput\13.5.0.7715\SGWizard.exe" --appid=wizard -n | C:\Program Files\SogouInput\13.5.0.7715\SGWizard.exe | sogou_pinyin_135.exe | ||||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: HIGH Description: 搜狗输入法 设置向导 Exit code: 0 Version: 13.5.0.7715 Modules
| |||||||||||||||
| 768 | "C:\Program Files\SogouInput\13.5.0.7715\SGTool.exe" --appid=scdreg -ConvV1toV2InstPath "C:\Program Files\SogouInput\13.5.0.7715" | C:\Program Files\SogouInput\13.5.0.7715\SGTool.exe | — | sogou_pinyin_135.exe | |||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: HIGH Description: 搜狗输入法 工具 Exit code: 0 Version: 13.5.0.7715 Modules
| |||||||||||||||
| 844 | "C:\Program Files\SogouInput\Components\SogouComMgr.exe" -installdoall "C:\Program Files\SogouInput\Components\TempComponents" -param "-setup -rdele -pluginlist HandInput#MouseGesture#ScreenCapture -installplu 0 -removelist SearchSuggestionBundle#WonderfulWriteBundle#SmartInfoBundle" -silent -overwrite | C:\Program Files\SogouInput\Components\SogouComMgr.exe | sogou_pinyin_135.exe | ||||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: HIGH Description: 搜狗输入法 扩展功能管理器 Exit code: 0 Version: 13.5.0.7715 Modules
| |||||||||||||||
| 932 | "C:\Program Files\SogouInput\SogouExe\SogouExe.exe" /check | C:\Program Files\SogouInput\SogouExe\SogouExe.exe | — | userNetSchedule.exe | |||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: HIGH Description: 搜狗输入法 安全启动程序 Exit code: 0 Version: 13.5.0.7715 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\SogouInput\SogouExe\SogouExe.exe" /check | C:\Program Files\SogouInput\SogouExe\SogouExe.exe | SGTool.exe | ||||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: HIGH Description: 搜狗输入法 安全启动程序 Exit code: 0 Version: 13.5.0.7715 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,2089053335296603350,13708172923716126852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\SogouInput\13.5.0.7715\SGTool.exe" --appid=ucfont -yahei -extb6 "\" | C:\Program Files\SogouInput\13.5.0.7715\SGTool.exe | — | sogou_pinyin_135.exe | |||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: HIGH Description: 搜狗输入法 工具 Exit code: 4294967295 Version: 13.5.0.7715 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1036,2089053335296603350,13708172923716126852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2940 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1300 | SGWebRender.exe --type=renderer --no-sandbox --log-file="C:\ProgramData\SogouInput\cef.log" --field-trial-handle=4680,6873486459714340303,11209818928241255247,131072 --enable-features=CastMediaRouteProvider --lang=zh-CN --log-file="C:\ProgramData\SogouInput\cef.log" --log-severity=error --disable-spell-checking --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4936 /prefetch:1 | C:\Program Files\SogouInput\13.5.0.7715\SGWebRender.exe | SGMyInput.exe | ||||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: HIGH Description: 搜狗输入法 渲染进程 Exit code: 0 Version: 13.5.0.7715 Modules
| |||||||||||||||
Total events
118 526
Read events
117 786
Write events
717
Delete events
23
Modification events
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
89
Suspicious files
250
Text files
424
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6475B6C9-7F0.pma | — | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10e272.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10e282.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF10e282.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
105
TCP/UDP connections
135
DNS requests
66
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2336 | chrome.exe | GET | — | 125.37.205.240:80 | http://imedl.sogoucdn.com/index/download.png | CN | — | — | suspicious |
2336 | chrome.exe | GET | 200 | 125.37.205.240:80 | http://imedl.sogoucdn.com/index/download_hover.png | CN | image | 4.08 Kb | suspicious |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/eua6zlfhpj3roq46nymxtbz4zq_2022.10.19.1145/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.10.19.1145_all_ac7cecrzrmfngskhgmtk6zmhfjoa.crx3 | US | binary | 5.88 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/eua6zlfhpj3roq46nymxtbz4zq_2022.10.19.1145/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.10.19.1145_all_ac7cecrzrmfngskhgmtk6zmhfjoa.crx3 | US | binary | 4.36 Kb | whitelisted |
852 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/eua6zlfhpj3roq46nymxtbz4zq_2022.10.19.1145/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.10.19.1145_all_ac7cecrzrmfngskhgmtk6zmhfjoa.crx3 | US | — | — | whitelisted |
852 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 2.81 Kb | whitelisted |
852 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 4.36 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 9.16 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 59.4 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 83.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2336 | chrome.exe | 125.37.205.240:80 | imedl.sogoucdn.com | CHINA UNICOM China169 Backbone | CN | unknown |
2336 | chrome.exe | 39.156.166.44:443 | pinyin.sogou.com | China Mobile Communications Group Co., Ltd. | CN | suspicious |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3692 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2032 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | chrome.exe | 39.156.166.45:443 | pinyin.sogou.com | China Mobile Communications Group Co., Ltd. | CN | unknown |
2336 | chrome.exe | 142.250.185.238:443 | clients2.google.com | GOOGLE | US | whitelisted |
2336 | chrome.exe | 142.250.185.109:443 | accounts.google.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
pinyin.sogou.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
ife.gtimg.com |
| suspicious |
ssl.gstatic.com |
| whitelisted |
s11.cnzz.com |
| whitelisted |
imedl.sogoucdn.com |
| suspicious |
img03.sogoucdn.com |
| suspicious |
img04.sogoucdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2336 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2788 | sogou_pinyin_135.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
308 | SGWizard.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
2044 | SGTool.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
1360 | SGDownload.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
1360 | SGDownload.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
1360 | SGDownload.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
1360 | SGDownload.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
1360 | SGDownload.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
2044 | SGTool.exe | A Network Trojan was detected | ET POLICY Win32/Sogou User-Agent (SOGOU_UPDATER) |
Process | Message |
|---|---|
SGMyInput.exe | [0530/094601.562:ERROR:main_delegate.cc(951)] Could not load cef_100_percent.pak
|
SGMyInput.exe | [0530/094601.563:ERROR:main_delegate.cc(960)] Could not load cef_200_percent.pak
|
SGMyInput.exe | [0530/094601.563:ERROR:main_delegate.cc(970)] Could not load cef_extensions.pak
|
SGWebRender.exe | [0530/094601.623:ERROR:main_delegate.cc(951)] Could not load cef_100_percent.pak
|
SGWebRender.exe | [0530/094601.623:ERROR:main_delegate.cc(960)] Could not load cef_200_percent.pak
|
SGWebRender.exe | [0530/094601.624:ERROR:main_delegate.cc(970)] Could not load cef_extensions.pak
|
SGWebRender.exe | [0530/094601.654:ERROR:viz_main_impl.cc(161)] Exiting GPU process due to errors during initialization
|
SGWebRender.exe | [0530/094601.701:ERROR:main_delegate.cc(951)] Could not load cef_100_percent.pak
|
SGWebRender.exe | [0530/094601.701:ERROR:main_delegate.cc(960)] Could not load cef_200_percent.pak
|
SGWebRender.exe | [0530/094601.701:ERROR:main_delegate.cc(970)] Could not load cef_extensions.pak
|