| File name: | Client-built.exe |
| Full analysis: | https://app.any.run/tasks/cbd3e2ba-96da-44a6-af83-f89cd56c5528 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | April 15, 2024, 16:53:23 |
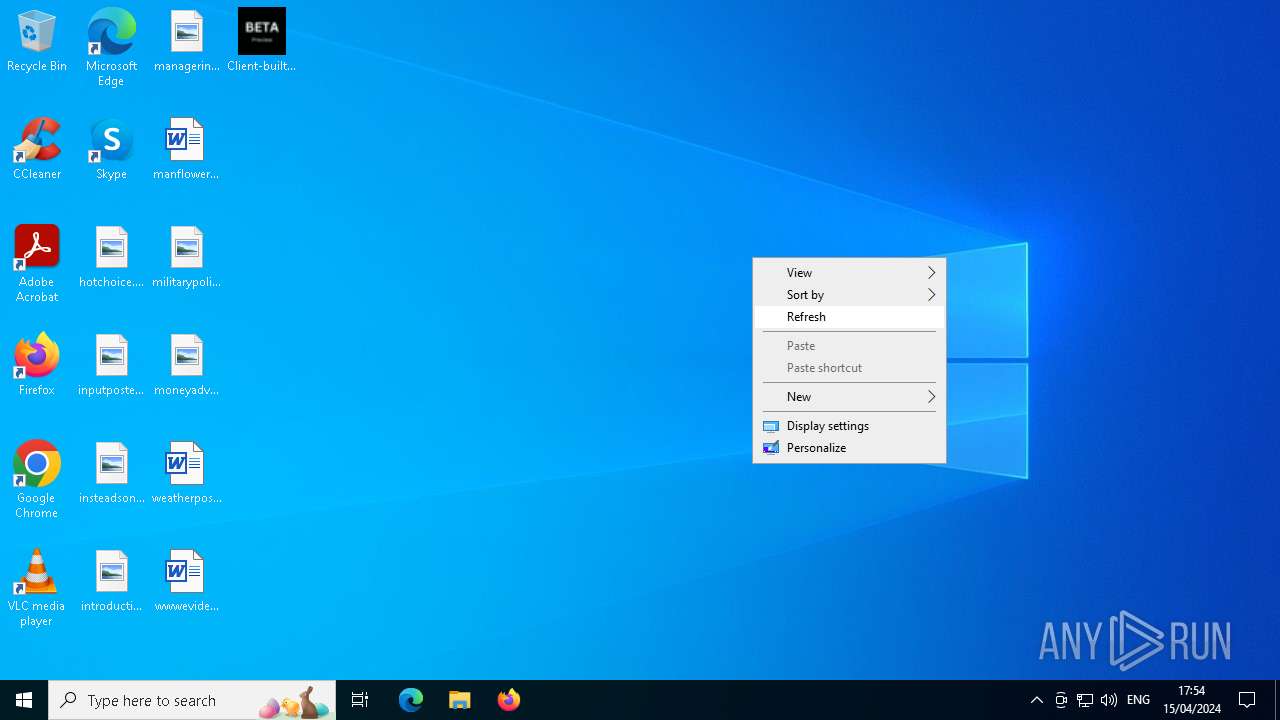
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9F2C9C8F1E227BFF7AAF17A8DFCC5E52 |
| SHA1: | 04D5D1CCDF36C64B6DBE4B3F0E144048065E3973 |
| SHA256: | 0F34B045728E701EC2A70EF07A38F00058C1679AA6E27B91BE65FF9C01D0F6CD |
| SSDEEP: | 49152:oVgGOhX02hD2nPiLq3A6770DODdl/rADxXhCk/3DgRjIh/0KiKgUOzQbVI3zvk11:f2nP6q3A6770DODdl/rADxRLDgyIa6E |
MALICIOUS
Drops the executable file immediately after the start
- Client-built.exe (PID: 3208)
Changes the autorun value in the registry
- Client-built.exe (PID: 3208)
- JavaUpdater.exe (PID: 6180)
QUASAR has been detected (YARA)
- JavaUpdater.exe (PID: 6180)
SUSPICIOUS
Executable content was dropped or overwritten
- Client-built.exe (PID: 3208)
Starts itself from another location
- Client-built.exe (PID: 3208)
Connects to unusual port
- JavaUpdater.exe (PID: 6180)
INFO
Reads the computer name
- Client-built.exe (PID: 3208)
- JavaUpdater.exe (PID: 6180)
Checks supported languages
- Client-built.exe (PID: 3208)
- JavaUpdater.exe (PID: 6180)
Reads Environment values
- Client-built.exe (PID: 3208)
- JavaUpdater.exe (PID: 6180)
Creates files or folders in the user directory
- Client-built.exe (PID: 3208)
Reads the machine GUID from the registry
- Client-built.exe (PID: 3208)
- JavaUpdater.exe (PID: 6180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(6180) JavaUpdater.exe
Version1.4.1
C2 (2)73.193.34.34:4782
Sub_DirSubDir
Install_NameJavaUpdater.exe
Mutex02ed8f6e-b4ab-48d4-b95b-fbefab7e770d
StartupJava Updater
Tagrat4
LogDirLogs
Signatureb9g8ZVHJ02jVQBlg5MR/iIFp+8EEbgLKM8VzHSBLknznsp708byJ3kOi9kpXqNCj7I6mpVQekf9nEONBaLj2+Fyca/R4baSooFrPhVeeArWJi0qwZnOJfNcd9mXLhB8bKJgguU2Nmd/UPM2+HP8lR7CrdGjAmgPNNZPTUuKCPnqr5oRJWidnNmrOkg9umf1LapnFEBQwlj7ELbWwSwmo3U60XRsR66niwWUXYNjUVdPYmiVT+VPXTPAbW7aC4zfvehHVmSd2JvhPLUGyK7ocljq27YivCSDquYCwy06ZNje1...
CertificateMIIE9DCCAtygAwIBAgIQAPR69zUy374PjJagM+NuOzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDQwODA2MzExOVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAzU89X173oIoMRcl8ZdN6AhkQ+oResz6sijeIobTMXqkSo11Ys7/DbJJoVzYn1Bm/QzI//5Id...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 16:16:39+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261440 |
| InitializedDataSize: | 7680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e3ee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.7.9 |
| ProductVersionNumber: | 1.1.7.9 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | StartUp |
| FileVersion: | 1.1.7.9 |
| InternalName: | Windows 2024 |
| LegalCopyright: | Microsoft 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Windows 2024 |
| ProductName: | WinUpdater |
| ProductVersion: | 1.1.7.9 |
| AssemblyVersion: | 1.1.7.9 |
Total processes
113
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2568 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 3208 | "C:\Users\admin\Desktop\Client-built.exe" | C:\Users\admin\Desktop\Client-built.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: StartUp Exit code: 3 Version: 1.1.7.9 Modules
| |||||||||||||||
| 6180 | "C:\Users\admin\AppData\Roaming\SubDir\JavaUpdater.exe" | C:\Users\admin\AppData\Roaming\SubDir\JavaUpdater.exe | Client-built.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: StartUp Version: 1.1.7.9 Modules
Quasar(PID) Process(6180) JavaUpdater.exe Version1.4.1 C2 (2)73.193.34.34:4782 Sub_DirSubDir Install_NameJavaUpdater.exe Mutex02ed8f6e-b4ab-48d4-b95b-fbefab7e770d StartupJava Updater Tagrat4 LogDirLogs Signatureb9g8ZVHJ02jVQBlg5MR/iIFp+8EEbgLKM8VzHSBLknznsp708byJ3kOi9kpXqNCj7I6mpVQekf9nEONBaLj2+Fyca/R4baSooFrPhVeeArWJi0qwZnOJfNcd9mXLhB8bKJgguU2Nmd/UPM2+HP8lR7CrdGjAmgPNNZPTUuKCPnqr5oRJWidnNmrOkg9umf1LapnFEBQwlj7ELbWwSwmo3U60XRsR66niwWUXYNjUVdPYmiVT+VPXTPAbW7aC4zfvehHVmSd2JvhPLUGyK7ocljq27YivCSDquYCwy06ZNje1... CertificateMIIE9DCCAtygAwIBAgIQAPR69zUy374PjJagM+NuOzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDQwODA2MzExOVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAzU89X173oIoMRcl8ZdN6AhkQ+oResz6sijeIobTMXqkSo11Ys7/DbJJoVzYn1Bm/QzI//5Id... | |||||||||||||||
Total events
1 065
Read events
1 063
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3208) Client-built.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Java Updater |
Value: "C:\Users\admin\AppData\Roaming\SubDir\JavaUpdater.exe" | |||
| (PID) Process: | (6180) JavaUpdater.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Java Updater |
Value: "C:\Users\admin\AppData\Roaming\SubDir\JavaUpdater.exe" | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3208 | Client-built.exe | C:\Users\admin\AppData\Roaming\SubDir\JavaUpdater.exe | executable | |
MD5:— | SHA256:— | |||
| 2568 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2024-04-15.1653.2568.1.aodl | binary | |
MD5:— | SHA256:— | |||
| 2568 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2024-04-15.1653.2568.1.odl | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
16
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | svchost.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
2980 | svchost.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
6180 | JavaUpdater.exe | 73.193.34.34:4782 | — | COMCAST-7922 | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2980 | svchost.exe | 72.246.169.155:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
2980 | svchost.exe | 2.16.164.81:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |