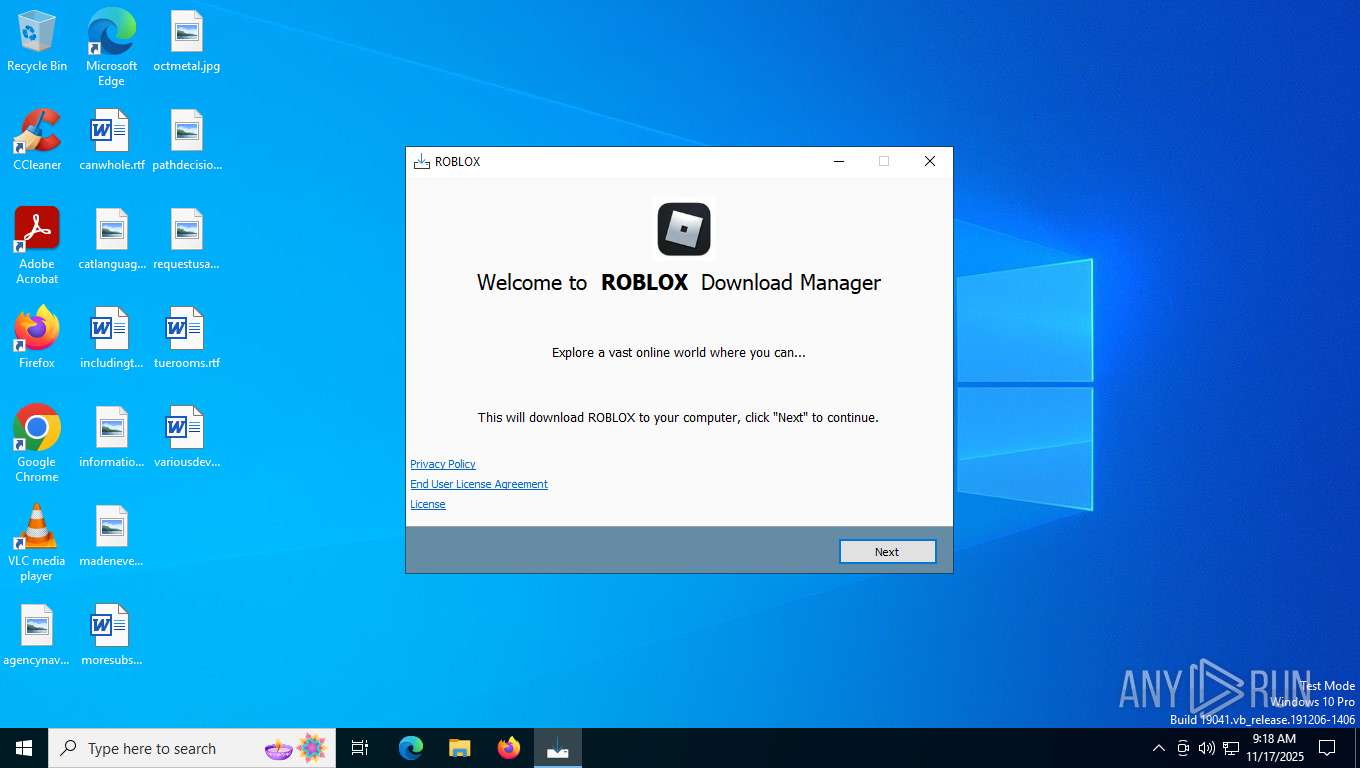
| File name: | roblox_lH8V-W1.exe |
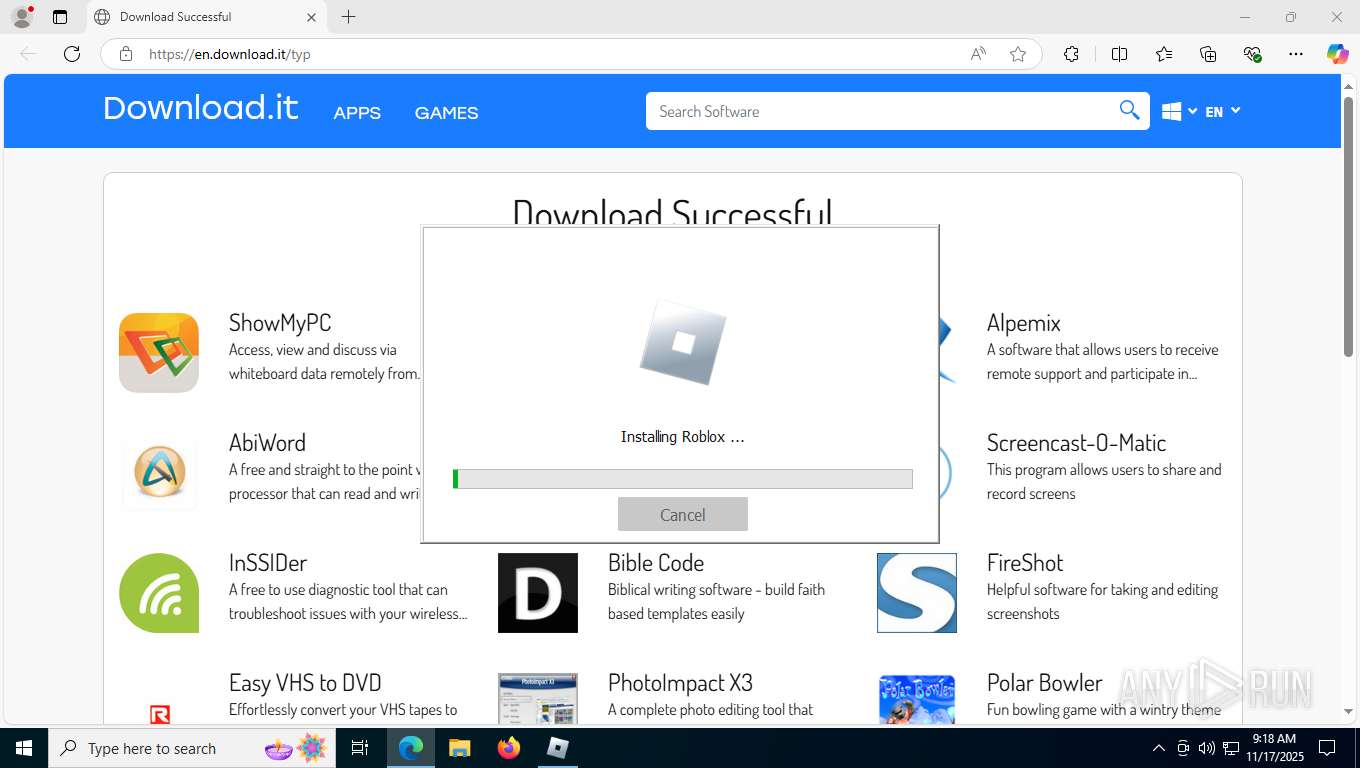
| Full analysis: | https://app.any.run/tasks/cd6c215e-5ab2-46ca-bdfd-37097f9c21fd |
| Verdict: | Malicious activity |
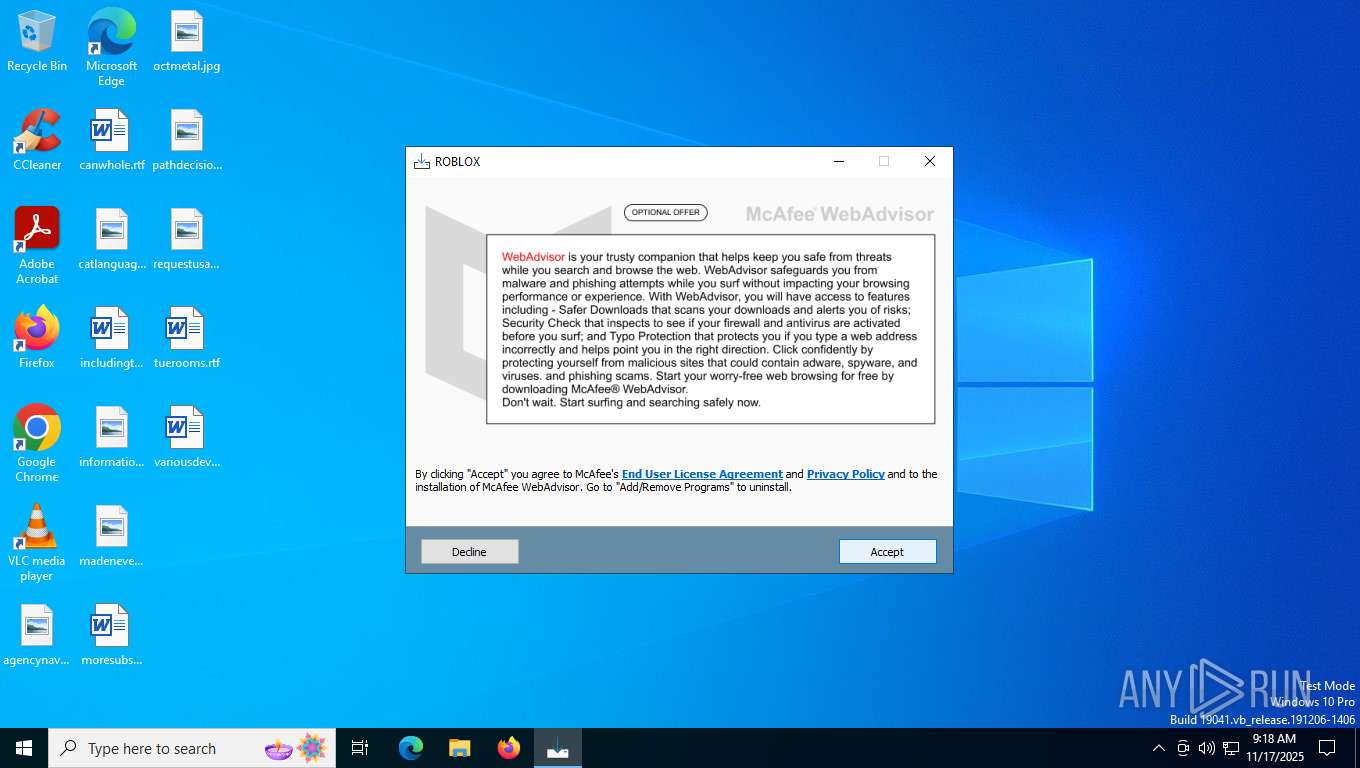
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | November 17, 2025, 09:18:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | FD98CF60DFE49D768A0870CEC2BFD4FE |
| SHA1: | 761B818AFE58FAD90F1F9B9C0C9818723C541A3D |
| SHA256: | 0F2B924E3CDB95E9334FFD5918D657CC94D1433473DC68FED4209B008E94692E |
| SSDEEP: | 98304:4LVIF8P3n1BLHxtD59KEKjSvDFLI7VTZgtT160NZbXQc98CyhWtAh8GLRokZWtKb:c/Yr3t/m7qoEJ+lmPN |
MALICIOUS
Bundleinstaller mutex has been found
- roblox_lH8V-W1.tmp (PID: 7620)
INNOSETUP has been detected (SURICATA)
- roblox_lH8V-W1.tmp (PID: 7620)
Changes settings of System certificates
- saBSI.exe (PID: 8116)
- servicehost.exe (PID: 8920)
SUSPICIOUS
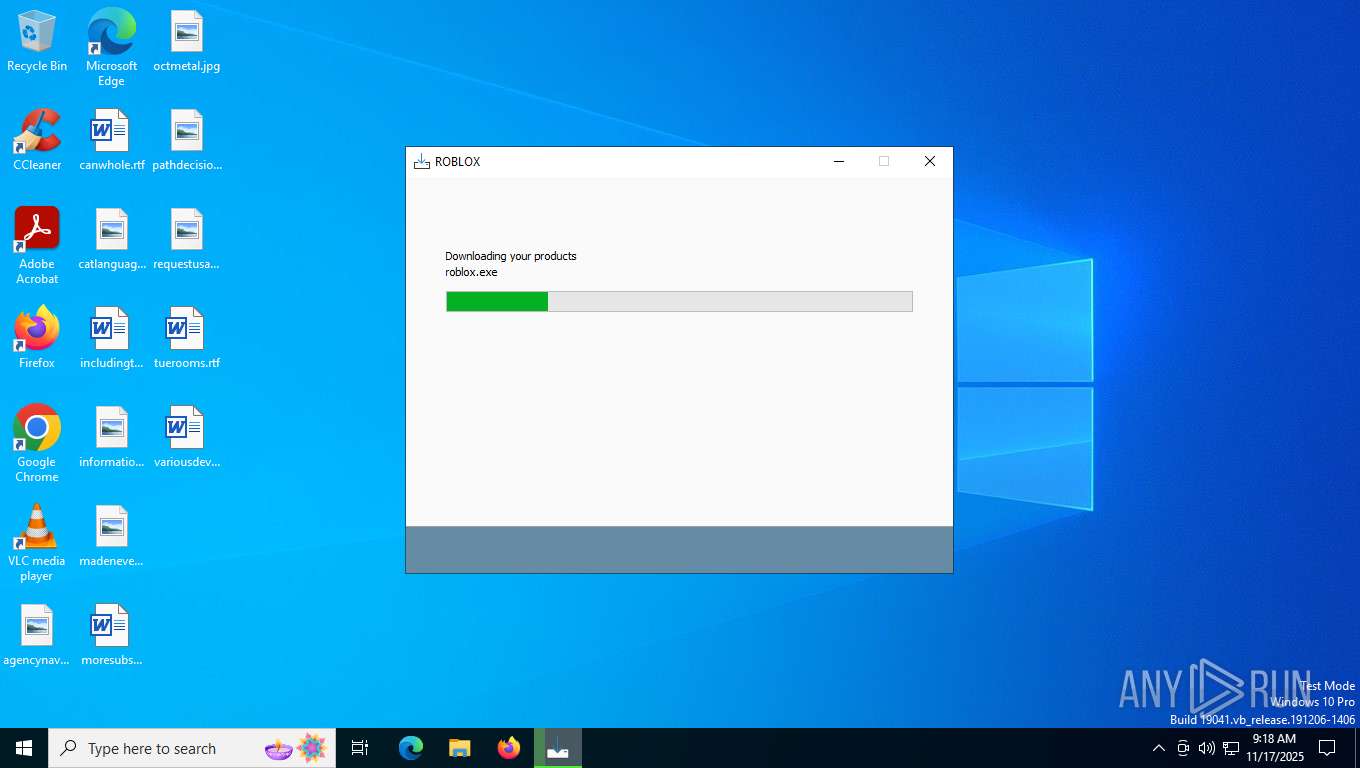
Executable content was dropped or overwritten
- roblox_lH8V-W1.exe (PID: 7364)
- roblox_lH8V-W1.exe (PID: 7572)
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 8116)
- saBSI.exe (PID: 7256)
- installer.exe (PID: 4644)
- roblox.exe (PID: 5576)
- installer.exe (PID: 1172)
- MicrosoftEdgeWebview2Setup.exe (PID: 8636)
Reads security settings of Internet Explorer
- roblox_lH8V-W1.tmp (PID: 7384)
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 7256)
- installer.exe (PID: 1172)
- MicrosoftEdgeUpdate.exe (PID: 8700)
- saBSI.exe (PID: 8116)
- uihost.exe (PID: 7588)
Reads the Windows owner or organization settings
- roblox_lH8V-W1.tmp (PID: 7620)
Access to an unwanted program domain was detected
- roblox_lH8V-W1.tmp (PID: 7620)
Potential Corporate Privacy Violation
- roblox_lH8V-W1.tmp (PID: 7620)
Adds/modifies Windows certificates
- saBSI.exe (PID: 8116)
- servicehost.exe (PID: 8920)
The process verifies whether the antivirus software is installed
- saBSI.exe (PID: 7256)
- installer.exe (PID: 4644)
- installer.exe (PID: 1172)
- servicehost.exe (PID: 8920)
- uihost.exe (PID: 7588)
- updater.exe (PID: 8576)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 8744)
Creates/Modifies COM task schedule object
- installer.exe (PID: 1172)
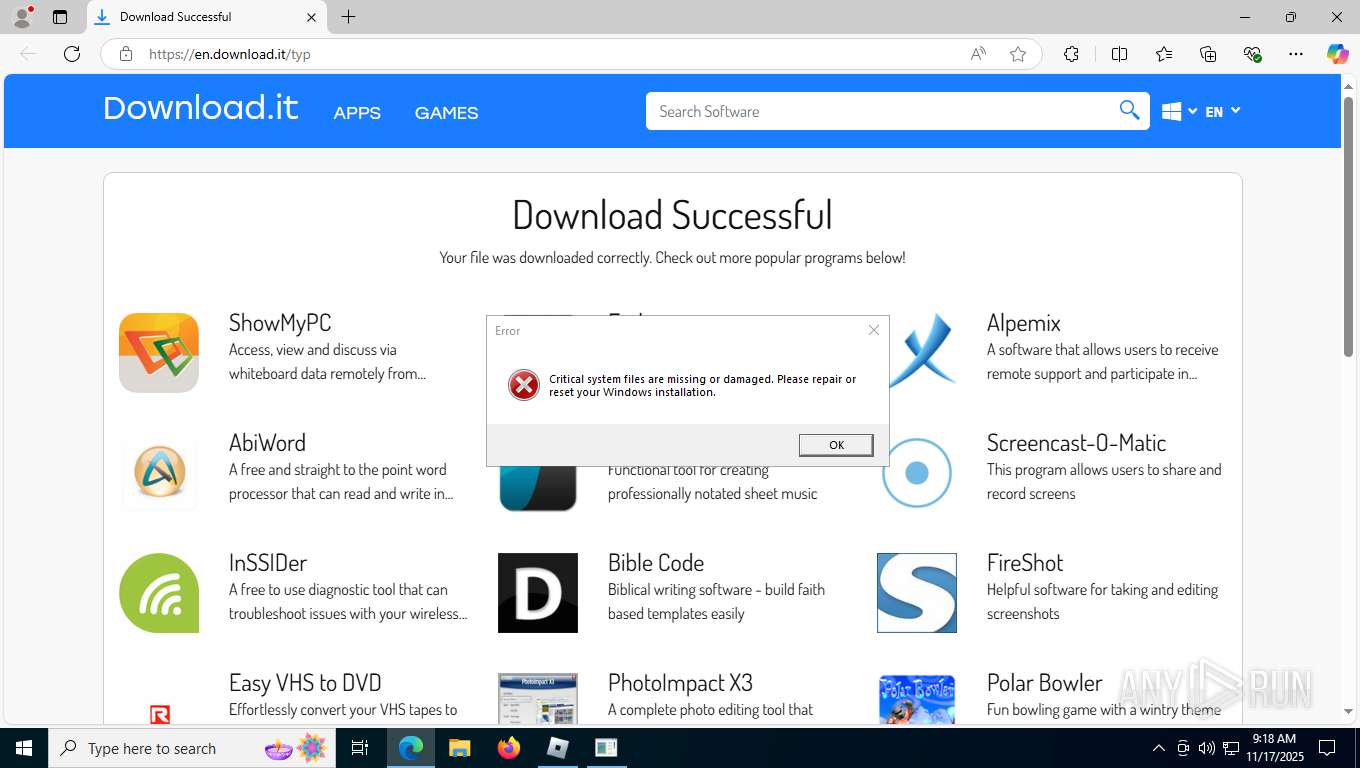
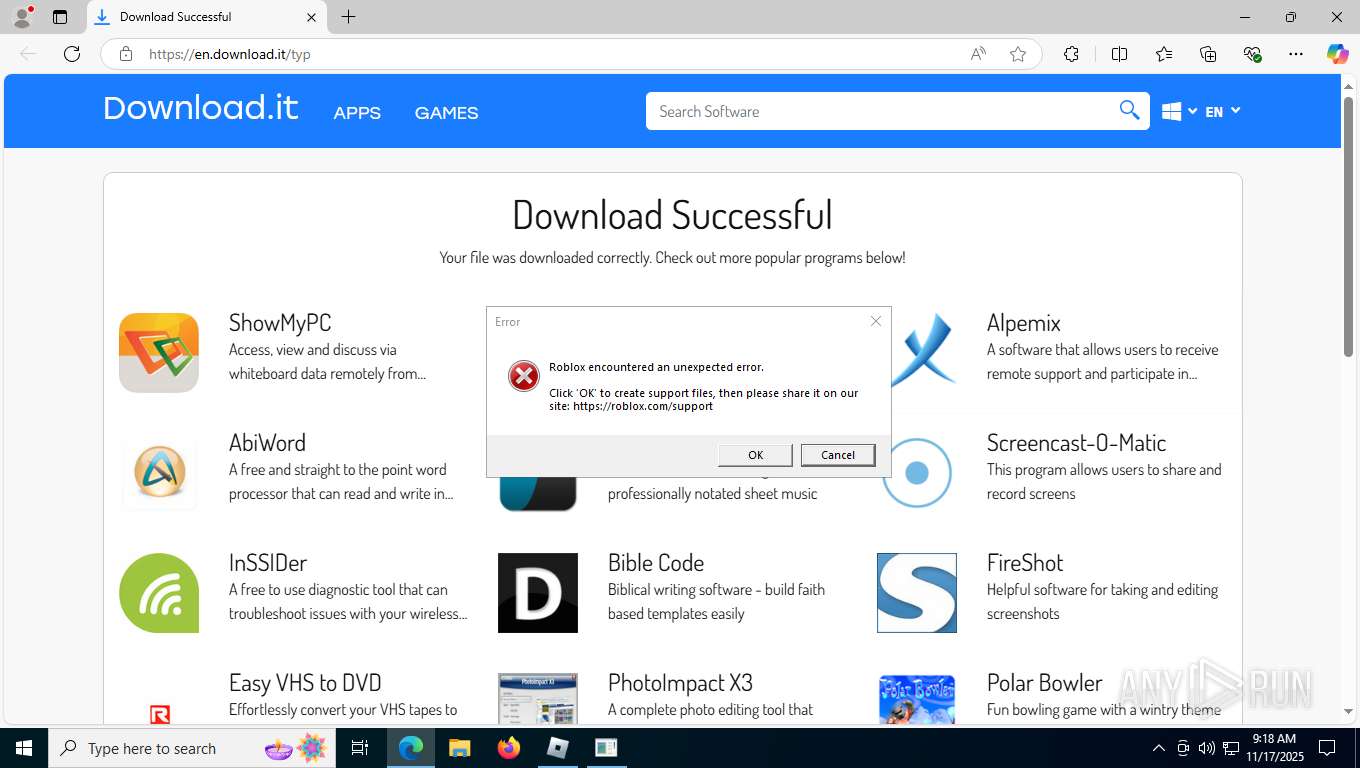
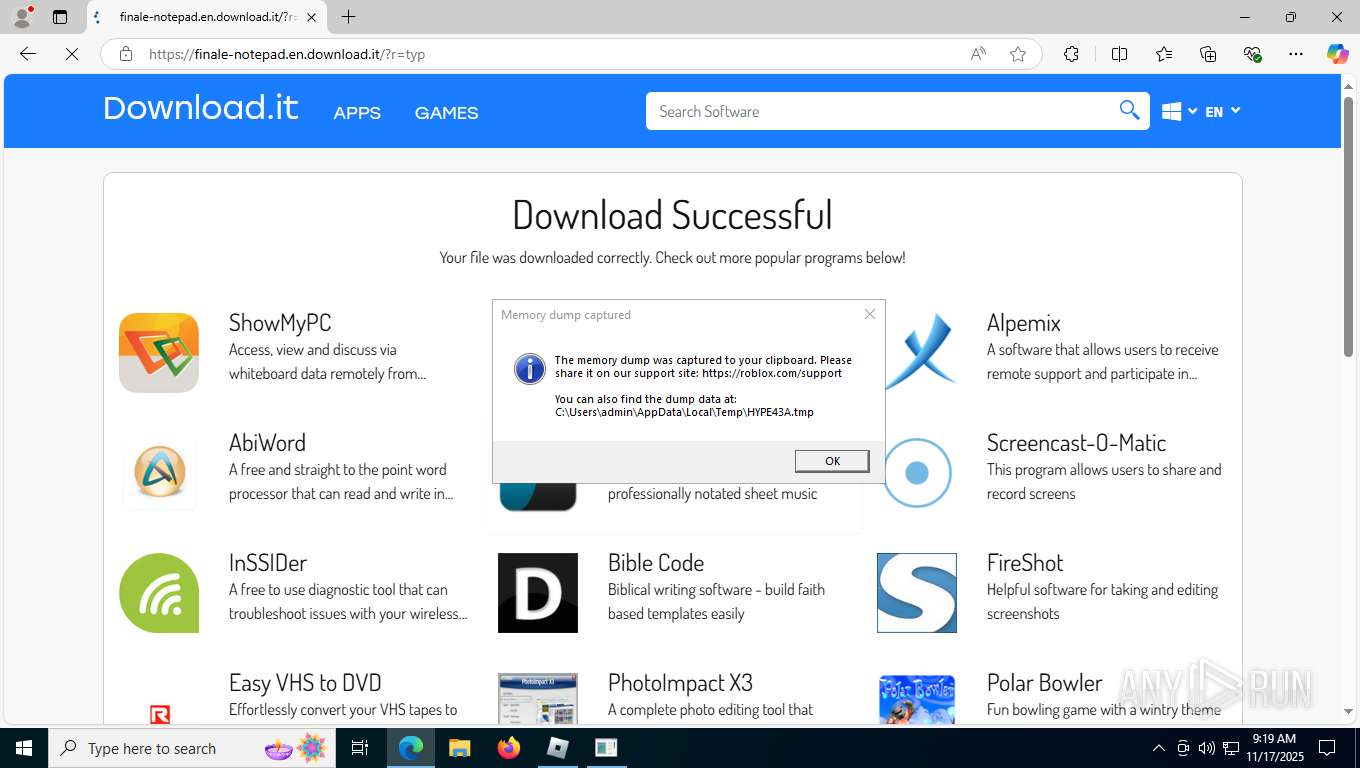
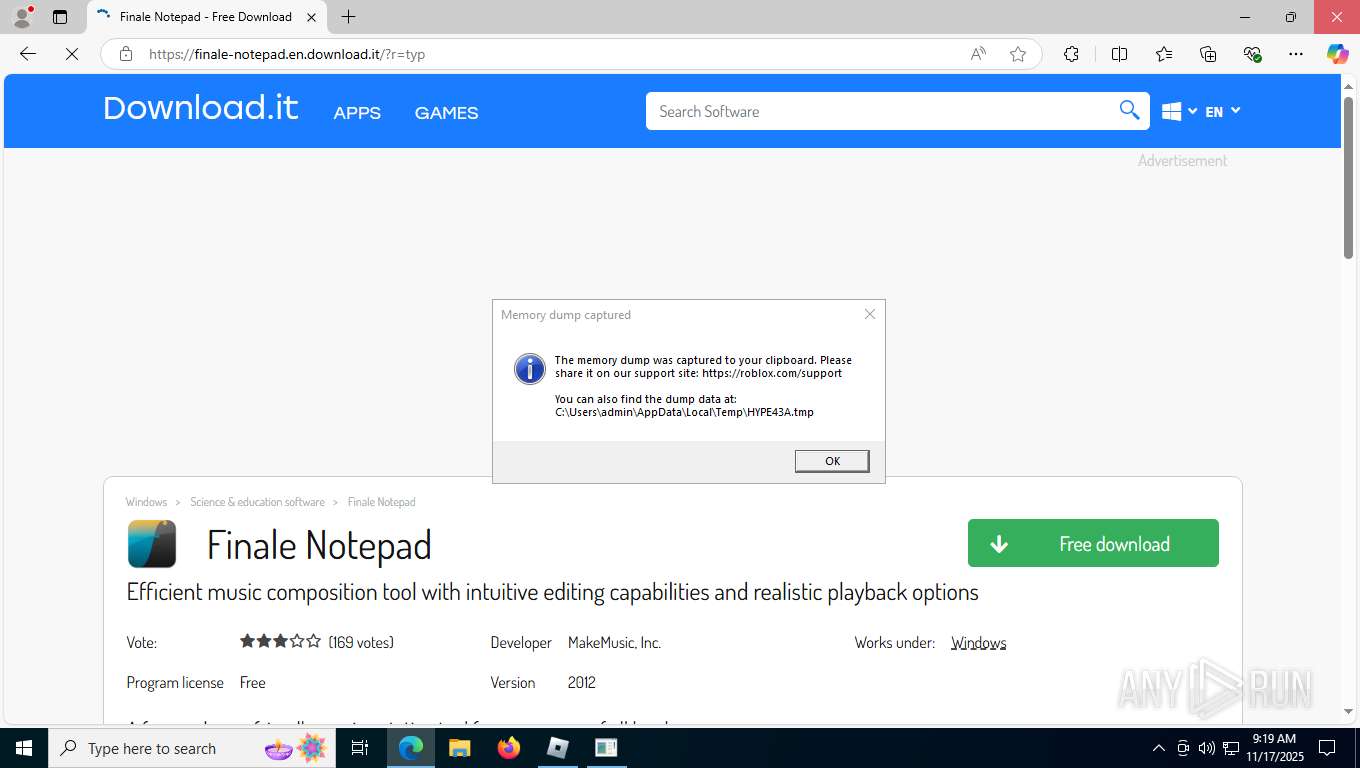
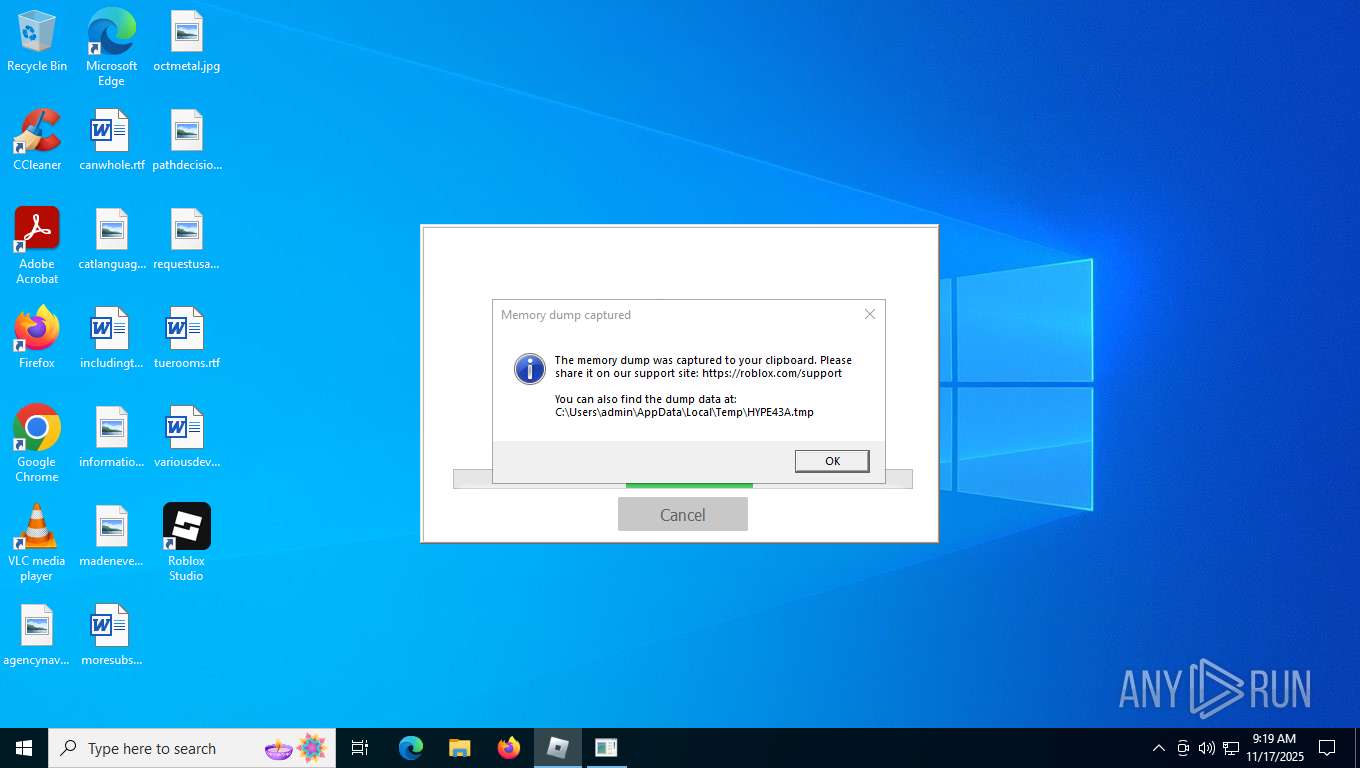
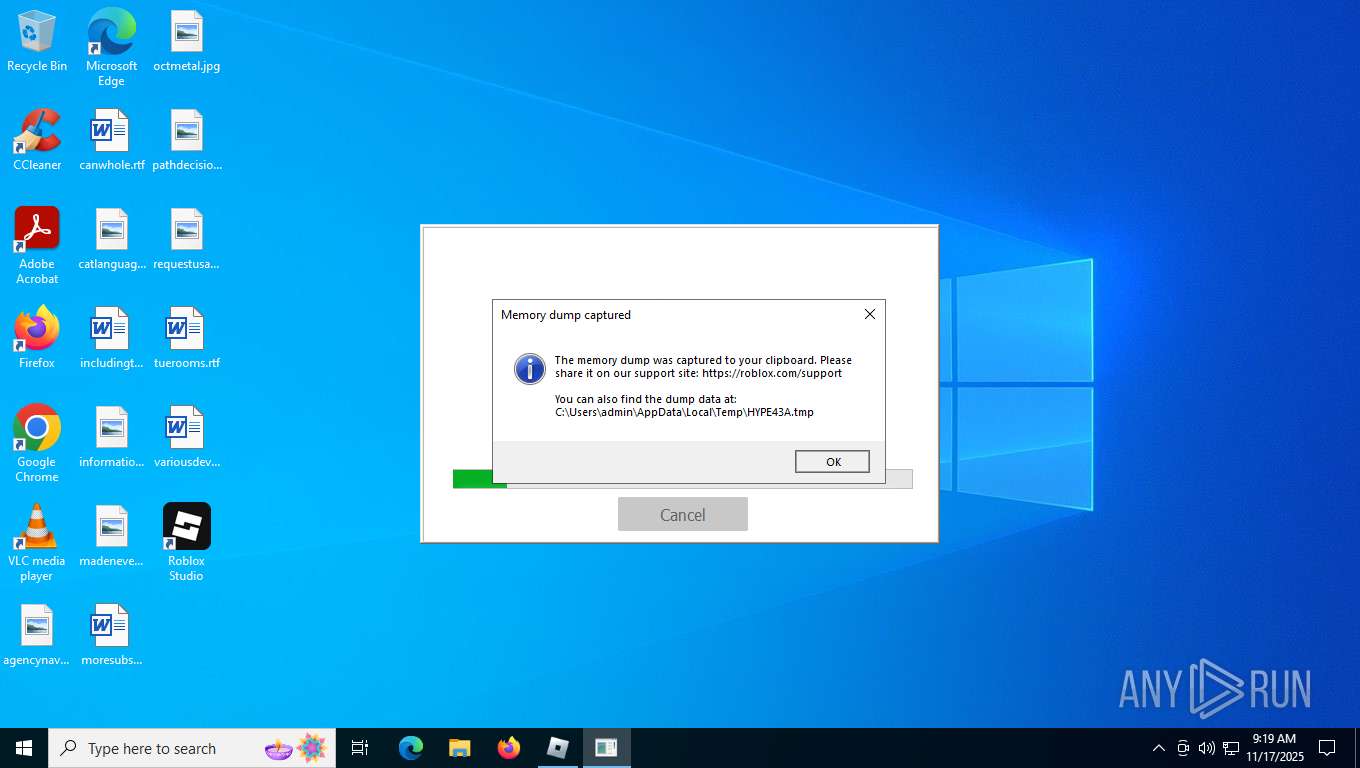
Executes application which crashes
- roblox_lH8V-W1.tmp (PID: 7620)
Changes default file association
- roblox.exe (PID: 5576)
The process creates files with name similar to system file names
- installer.exe (PID: 1172)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 8700)
Process drops legitimate windows executable
- MicrosoftEdgeUpdate.exe (PID: 8700)
- MicrosoftEdgeWebview2Setup.exe (PID: 8636)
- roblox.exe (PID: 5576)
- installer.exe (PID: 1172)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 8700)
Executes as Windows Service
- servicehost.exe (PID: 8920)
Non windows owned service launched
- servicehost.exe (PID: 8920)
Reads Mozilla Firefox installation path
- servicehost.exe (PID: 8920)
- uihost.exe (PID: 7588)
Searches for installed software
- updater.exe (PID: 8576)
Starts CMD.EXE for commands execution
- updater.exe (PID: 8576)
INFO
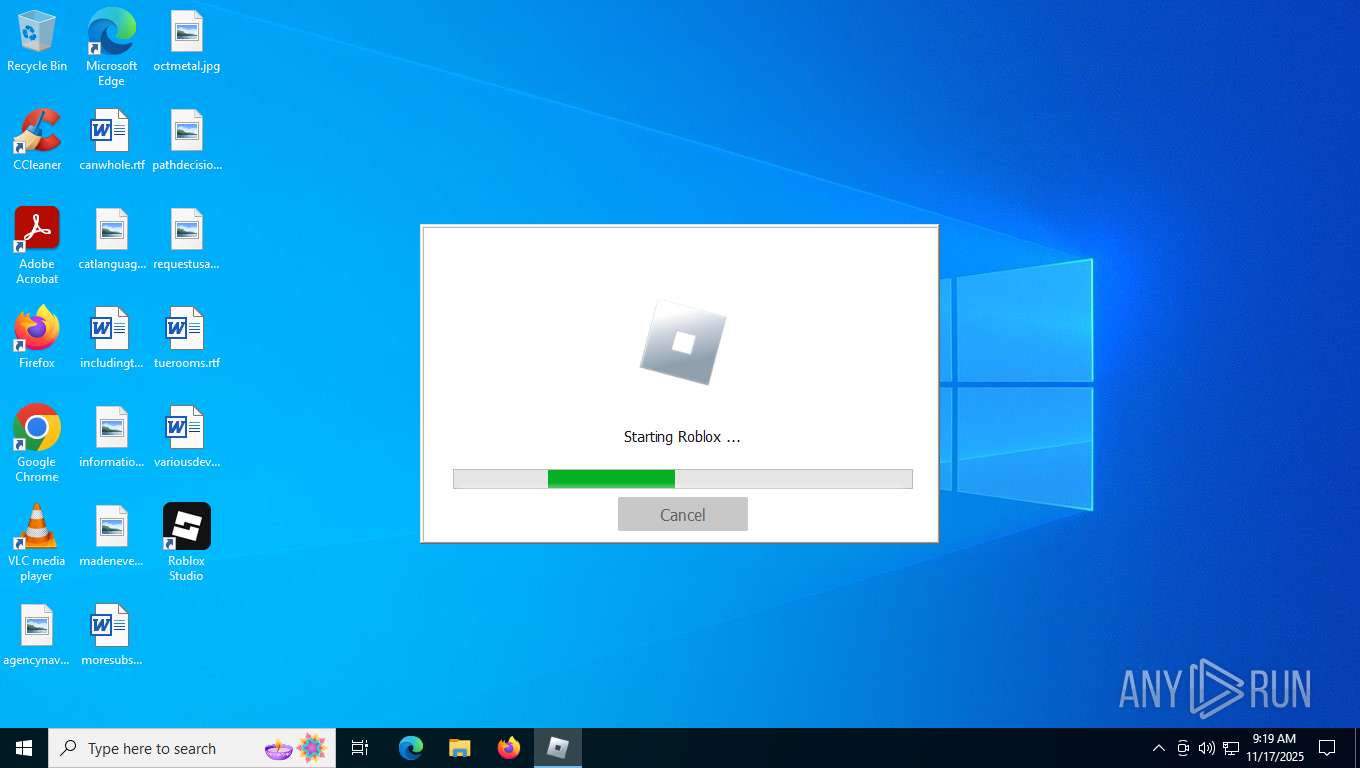
Create files in a temporary directory
- roblox_lH8V-W1.exe (PID: 7364)
- roblox_lH8V-W1.exe (PID: 7572)
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 7256)
- installer.exe (PID: 1172)
- roblox.exe (PID: 5576)
Reads Environment values
- roblox_lH8V-W1.exe (PID: 7364)
- roblox_lH8V-W1.tmp (PID: 7384)
- roblox_lH8V-W1.exe (PID: 7572)
- roblox_lH8V-W1.tmp (PID: 7620)
- identity_helper.exe (PID: 8224)
- MicrosoftEdgeUpdate.exe (PID: 8700)
- RobloxPlayerBeta.exe (PID: 8832)
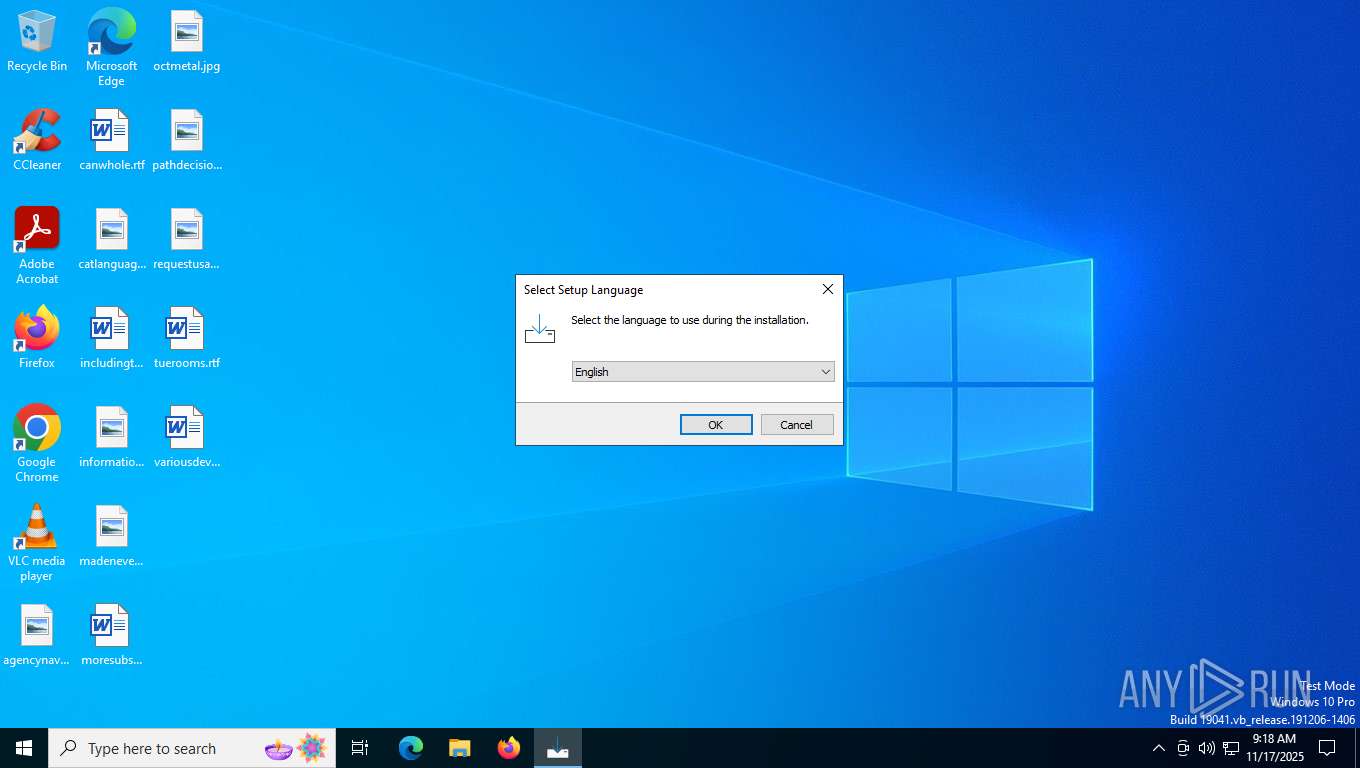
Checks supported languages
- roblox_lH8V-W1.exe (PID: 7364)
- roblox_lH8V-W1.tmp (PID: 7384)
- roblox_lH8V-W1.exe (PID: 7572)
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 8116)
- saBSI.exe (PID: 7256)
- roblox.exe (PID: 5576)
- installer.exe (PID: 4644)
- installer.exe (PID: 1172)
- identity_helper.exe (PID: 8224)
- MicrosoftEdgeUpdate.exe (PID: 8700)
- MicrosoftEdgeWebview2Setup.exe (PID: 8636)
- RobloxPlayerBeta.exe (PID: 8832)
- servicehost.exe (PID: 8920)
- uihost.exe (PID: 7588)
- updater.exe (PID: 8576)
Reads the computer name
- roblox_lH8V-W1.tmp (PID: 7384)
- roblox_lH8V-W1.exe (PID: 7572)
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 7256)
- saBSI.exe (PID: 8116)
- roblox.exe (PID: 5576)
- installer.exe (PID: 1172)
- identity_helper.exe (PID: 8224)
- MicrosoftEdgeUpdate.exe (PID: 8700)
- servicehost.exe (PID: 8920)
- uihost.exe (PID: 7588)
- updater.exe (PID: 8576)
Process checks computer location settings
- roblox_lH8V-W1.tmp (PID: 7384)
- roblox_lH8V-W1.tmp (PID: 7620)
- MicrosoftEdgeUpdate.exe (PID: 8700)
- servicehost.exe (PID: 8920)
Reads the software policy settings
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 7256)
- saBSI.exe (PID: 8116)
- installer.exe (PID: 1172)
- WerFault.exe (PID: 8480)
- WerFault.exe (PID: 2220)
- MicrosoftEdgeUpdate.exe (PID: 8700)
- wermgr.exe (PID: 8760)
- uihost.exe (PID: 7588)
- servicehost.exe (PID: 8920)
- updater.exe (PID: 8576)
Compiled with Borland Delphi (YARA)
- roblox_lH8V-W1.exe (PID: 7364)
- roblox_lH8V-W1.exe (PID: 7572)
- roblox_lH8V-W1.tmp (PID: 7384)
- roblox_lH8V-W1.tmp (PID: 7620)
Reads the machine GUID from the registry
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 7256)
- saBSI.exe (PID: 8116)
- roblox.exe (PID: 5576)
- installer.exe (PID: 1172)
- servicehost.exe (PID: 8920)
- uihost.exe (PID: 7588)
- updater.exe (PID: 8576)
Checks proxy server information
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 8116)
- saBSI.exe (PID: 7256)
- WerFault.exe (PID: 2220)
- WerFault.exe (PID: 8480)
- MicrosoftEdgeUpdate.exe (PID: 8700)
- wermgr.exe (PID: 8760)
Detects InnoSetup installer (YARA)
- roblox_lH8V-W1.exe (PID: 7364)
- roblox_lH8V-W1.tmp (PID: 7384)
- roblox_lH8V-W1.exe (PID: 7572)
- roblox_lH8V-W1.tmp (PID: 7620)
The sample compiled with english language support
- roblox_lH8V-W1.tmp (PID: 7620)
- saBSI.exe (PID: 8116)
- installer.exe (PID: 4644)
- roblox.exe (PID: 5576)
- installer.exe (PID: 1172)
- MicrosoftEdgeWebview2Setup.exe (PID: 8636)
- MicrosoftEdgeUpdate.exe (PID: 8700)
Creates files in the program directory
- saBSI.exe (PID: 8116)
- saBSI.exe (PID: 7256)
- installer.exe (PID: 4644)
- roblox.exe (PID: 5576)
- installer.exe (PID: 1172)
- MicrosoftEdgeWebview2Setup.exe (PID: 8636)
- servicehost.exe (PID: 8920)
- uihost.exe (PID: 7588)
Application launched itself
- msedge.exe (PID: 2588)
- msedge.exe (PID: 4064)
- msedge.exe (PID: 1632)
Creates files or folders in the user directory
- roblox.exe (PID: 5576)
- WerFault.exe (PID: 2220)
- WerFault.exe (PID: 8480)
Manual execution by a user
- msedge.exe (PID: 1632)
ROBLOX mutex has been found
- roblox.exe (PID: 5576)
Process checks whether UAC notifications are on
- roblox.exe (PID: 5576)
Creates a software uninstall entry
- installer.exe (PID: 1172)
- roblox.exe (PID: 5576)
- servicehost.exe (PID: 8920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:03 14:45:36+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 704512 |
| InitializedDataSize: | 162304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xacfe0 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.0.9298 |
| ProductVersionNumber: | 2.4.0.9298 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Portale delle applicazioni |
| FileVersion: | 2.4.0.9298 |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Applicazioni Windows |
| ProductVersion: | 2.4.0.9298 |
Total processes
192
Monitored processes
43
Malicious processes
5
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2232,i,8641521653221261344,4543680107784835906,262144 --variations-seed-version --mojo-platform-channel-handle=2128 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\McAfee\Temp2452046342\installer.exe" /setOem:Affid=91082 /s /thirdparty /upgrade | C:\Program Files\McAfee\Temp2452046342\installer.exe | installer.exe | ||||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee WebAdvisor(installer) Exit code: 0 Version: 4,1,1,1080 Modules
| |||||||||||||||
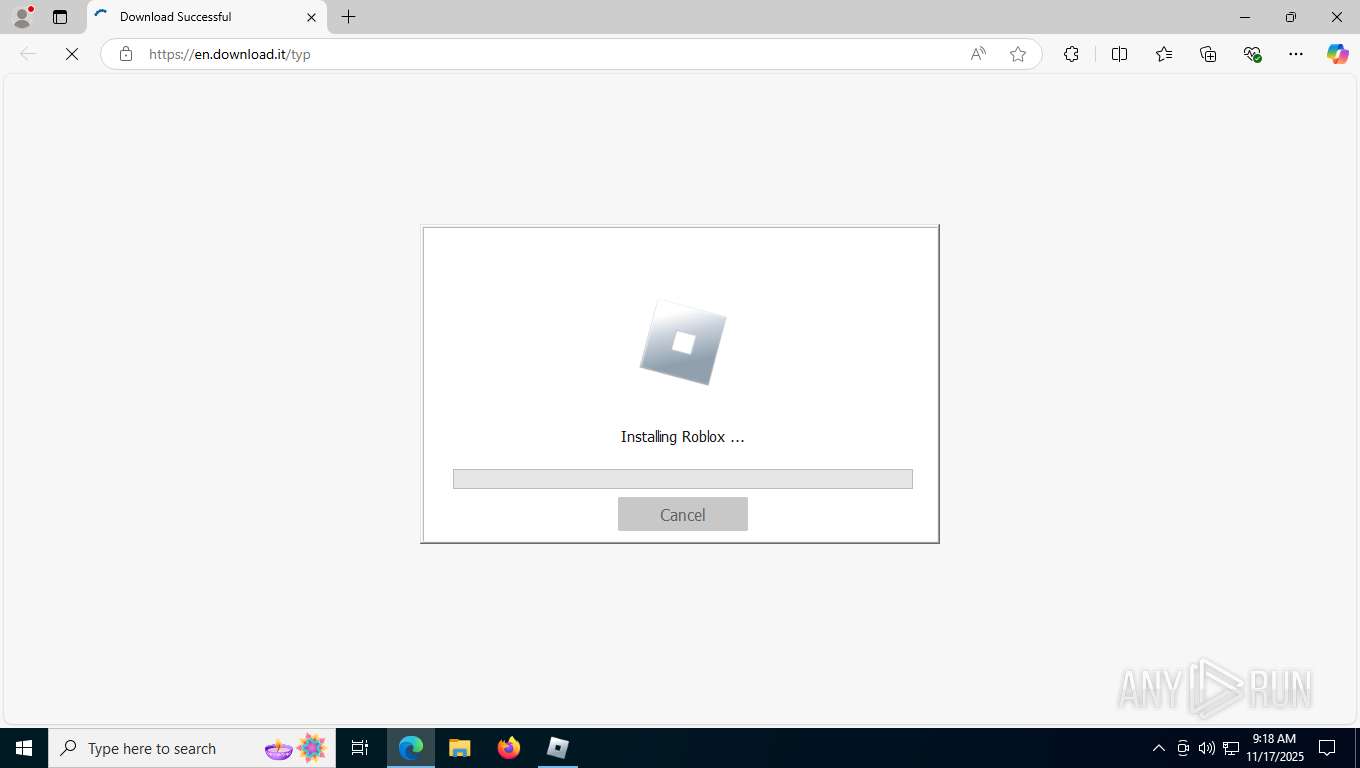
| 1632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --disable-quic --flag-switches-end --do-not-de-elevate --single-argument https://en.download.it/typ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3616,i,16405612796144707213,5770068247863258937,262144 --variations-seed-version --mojo-platform-channel-handle=3776 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2220 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7620 -s 2744 | C:\Windows\SysWOW64\WerFault.exe | roblox_lH8V-W1.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=3868,i,16405612796144707213,5770068247863258937,262144 --variations-seed-version --mojo-platform-channel-handle=5512 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2588 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch --single-argument https://en.download.it/typ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2764 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5544,i,16405612796144707213,5770068247863258937,262144 --variations-seed-version --mojo-platform-channel-handle=5588 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3000 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4952,i,16405612796144707213,5770068247863258937,262144 --variations-seed-version --mojo-platform-channel-handle=4956 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://en.download.it/typ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | roblox_lH8V-W1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
41 713
Read events
41 382
Write events
314
Delete events
17
Modification events
| (PID) Process: | (7620) roblox_lH8V-W1.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E9070B0001001100090012001F000303010000001E768127E028094199FEB9D127C57AFE | |||
| (PID) Process: | (7620) roblox_lH8V-W1.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E9070B0001001100090012001F001303010000001E768127E028094199FEB9D127C57AFE | |||
| (PID) Process: | (8116) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | UUID |
Value: {09B84935-5FC5-4C04-BAC3-9E2DE743919D} | |||
| (PID) Process: | (8116) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | InstallerFlags |
Value: 1 | |||
| (PID) Process: | (8116) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
Value: | |||
| (PID) Process: | (8116) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000E94FB54871208C00DF70F708AC47085B0F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C0300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B809000000010000000C000000300A06082B060105050703031D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD91400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B53000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C06200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF860B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000001900000001000000100000005D1B8FF2C30F63F5B536EDD400F7F9B4200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (8116) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000001900000001000000100000005D1B8FF2C30F63F5B536EDD400F7F9B40B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000006200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF8653000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C01400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B1D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD909000000010000000C000000300A06082B060105050703030300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B80F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C040000000100000010000000E94FB54871208C00DF70F708AC47085B200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (7256) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | InstallationStatus |
Value: PENDING | |||
| (PID) Process: | (7256) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | InstallationID |
Value: GnjW0tiGGzrccSnk2pj0zQPkeaZDUEc80SeGNIbMHiArYbwvcQsurMveXnP3t9guDszHH7huqKVCG3iRv4C | |||
| (PID) Process: | (7256) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | CountryCode |
Value: DE | |||
Executable files
238
Suspicious files
398
Text files
744
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7364 | roblox_lH8V-W1.exe | C:\Users\admin\AppData\Local\Temp\is-IODQB.tmp\roblox_lH8V-W1.tmp | executable | |
MD5:5ACF9F3B7D355C4D604691FF23423F2D | SHA256:988339C9378571DE0E501A3ACAAC46EB2C8200E10C0540843CAAC8AB7F43DDB2 | |||
| 7572 | roblox_lH8V-W1.exe | C:\Users\admin\AppData\Local\Temp\is-7D31E.tmp\roblox_lH8V-W1.tmp | executable | |
MD5:5ACF9F3B7D355C4D604691FF23423F2D | SHA256:988339C9378571DE0E501A3ACAAC46EB2C8200E10C0540843CAAC8AB7F43DDB2 | |||
| 7620 | roblox_lH8V-W1.tmp | C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\Helper.dll | executable | |
MD5:DE761970892FD126C0A130966215B363 | SHA256:3AA8BA187B846D05BED20E2F6E71F330E029D958E943DC9DD102DB4CFC6AEB38 | |||
| 7620 | roblox_lH8V-W1.tmp | C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7620 | roblox_lH8V-W1.tmp | C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\roblox.exe | executable | |
MD5:93CC28BFF51A677298618FA83BC6D3C0 | SHA256:ABE0149F9D65062AB9CF54B3B1AA68B563F136CC0BBA153C7C20DDC5AFADBD5C | |||
| 7620 | roblox_lH8V-W1.tmp | C:\Users\admin\Downloads\roblox.exe | executable | |
MD5:93CC28BFF51A677298618FA83BC6D3C0 | SHA256:ABE0149F9D65062AB9CF54B3B1AA68B563F136CC0BBA153C7C20DDC5AFADBD5C | |||
| 7620 | roblox_lH8V-W1.tmp | C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\prod0.zip | compressed | |
MD5:F68008B70822BD28C82D13A289DEB418 | SHA256:CC6F4FAF4E8A9F4D2269D1D69A69EA326F789620FB98078CC98597F3CB998589 | |||
| 8116 | saBSI.exe | C:\ProgramData\McAfee\WebAdvisor\saBSI\saBSI.exe | executable | |
MD5:7A1B6316D5D64A740B847D8261EA3E83 | SHA256:5EC42B168F2541DBB413D6F87AA5569470A2B0C6C574C3E655242461A4524763 | |||
| 7620 | roblox_lH8V-W1.tmp | C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\is-V87D7.tmp | executable | |
MD5:93CC28BFF51A677298618FA83BC6D3C0 | SHA256:ABE0149F9D65062AB9CF54B3B1AA68B563F136CC0BBA153C7C20DDC5AFADBD5C | |||
| 8116 | saBSI.exe | C:\ProgramData\McAfee\WebAdvisor\saBSI.exe\log_00000057003F001D0006.txt | text | |
MD5:18418D6D8C04401EDEC0DD7CE12402F6 | SHA256:6495428B032BB972E7F05E98D1F8B9F595F4D839BB98F84E3AB7A9AD9E03FE7D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
127
DNS requests
107
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2388 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
5052 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5724 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
2220 | WerFault.exe | GET | 200 | 95.101.78.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5724 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | DE | binary | 402 b | whitelisted |
5724 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
2220 | WerFault.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
5724 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | DE | binary | 813 b | whitelisted |
5724 | SIHClient.exe | GET | 200 | 95.101.78.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | NL | binary | 824 b | whitelisted |
7620 | roblox_lH8V-W1.tmp | GET | 200 | 95.168.168.24:80 | http://dl.jalecdn.com/US/roblox.exe | NL | executable | 4.56 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2388 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3100 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 2.16.241.205:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7620 | roblox_lH8V-W1.tmp | 18.64.16.25:443 | djloiq2ki6v9p.cloudfront.net | — | US | malicious |
7620 | roblox_lH8V-W1.tmp | 172.66.165.85:443 | static.download.it | — | US | suspicious |
2388 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2388 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
djloiq2ki6v9p.cloudfront.net |
| malicious |
static.download.it |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
dl.jalecdn.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET ADWARE_PUP Win32/OfferCore Checkin M1 |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | A Network Trojan was detected | ET ADWARE_PUP Win32/OfferCore Checkin M2 |
— | — | Possibly Unwanted Program Detected | ADWARE [ANY.RUN] InnoSetup Installer |
— | — | Possibly Unwanted Program Detected | ADWARE [ANY.RUN] InnoSetup Installer |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7620 | roblox_lH8V-W1.tmp | Possibly Unwanted Program Detected | ADWARE [ANY.RUN] InnoSetup Installer |
7620 | roblox_lH8V-W1.tmp | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Possibly Unwanted Program Detected | ADWARE [ANY.RUN] InnoSetup Installer |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
Process | Message |
|---|---|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-66UM3.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|